Submitted:
12 August 2025
Posted:
14 August 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Examination of GenAI agent architectures, emphasizing the security problems arising from tool use, autonomy, reasoning, and memory.
- A list of nine main threats that target these agentic capabilities.
- A review of pertinent attack avenues, including untested exploitation methods.
- Identifying risks to the STRIDE framework and developing customized mitigation techniques for SHIELD.
2. Literature Review
2.1. AI Applications in Cybersecurity
2.2. Cybersecurity risks and vulnerabilities: impact on software coding
2.3. Secure Software Coding Practices
2.4. Integration of AI Frameworks with Maturity Models
- Proactive threat identification and prevention: The ANN-ISM paradigm’s primary strength is its ability to forecast using Artificial Neural Networks (ANN). An ANN learns from each new piece of historical or real-time data and anticipates potential dangers before they become problems. Compared to traditional approaches, it has the advantage of early intervention and prevention because it proactively detects new cyber security threats.
- The NIST Cybersecurity Framework and Capability Maturity Model Integration (CMMI) are excellent for risk management, compliance, and process improvement, but what is reactive? In contrast, the framework emphasizes organized methods for addressing cybersecurity threats and weaknesses. However, they do not have the real-time predictive capabilities necessary to proactively mitigate the unknown and dynamic risks at play.
- Adaptability to emerging threats: Your model’s ANN component enables continuous learning in the ANN-ISM Paradigm. The framework thus combines ISM and AI threat detection to generate real-time alerts and countermeasures. As fresh data are collected, this system adjusts to the new attack signals and changes to keep up with the speed of cyberthreats. Security policies are further improved by integrating the ISM framework, which increases the system’s adaptability and flexibility in changing contexts.
- The CMMI and NIST approaches have static frameworks that are Even while they offer good suggestions for future cybersecurity best practices, they are unable to respond automatically to novel threats or environmental changes without human oversight. For instance, the NIST requires constant human oversight to adapt controls and processes to newly obtained threat intelligence, even though it depends on a risk-based management approach and associated best practices.
- Real-time threat detection and response: Our model detects the same cybersecurity problem in real-time and responds to it automatically by taking the necessary action immediately. The framework thus combines ISM and AI threat detection to generate real-time alerts and countermeasures.
- Real-time threat detection and response are not supported by the NIST and CMMI frameworks, although they facilitate the creation of detailed security processes. Although the NIST emphasizes monitoring for continual development, it lacks the capability to respond quickly to threats, as exemplified by the ANN-ISM model. Similarly, CMMI is more suited to organizational capability and process maturity than to immediate cybersecurity incident response.
- Flexibility and Scalability: When neural networks and ISM are combined (ANN-ISM paradigm), the framework is incredibly scalable. Without compromising its functionality, it can be developed over time to accommodate ever-increasing data volumes and security requirements. With the amount of data, machine learning is used in the framework to enhance the system and detect intricate and unknown dangers more accurately.
- The CMMI and NIST frameworks are both excellent tools for offering an organized method of approaching the concept of cybersecurity maturity. They are typically less adaptable to resolving novel, intricate, or expanding issues. The security procedure may be enhanced, and a baseline established with the aid of these models. However, they do not scale effectively by nature to accommodate growing data, complexity, and threats without manual updates or modifications.
- It facilitates the management and continuous improvement of automated process: The model’s ISM component incorporates the ANN-ISM Paradigm, a continuous improvement cycle, into the framework. Through the use of machine learning and security management procedures, the system continuously assesses its operations and makes the necessary adjustments in response. Consequently, the system can use new information and shifts in the threat landscape to continuously improve its cybersecurity protocols.
- The CMMI Framework focuses more on continuous process improvement and emphasizes organizational procedures and capability maturity. It doesn’t take into 7 account the fact that data-driven learning is automated. The NIST framework provides guidelines for improved security postures. Nevertheless, it lacks an automated upgrading procedure that would enable constant security posture improvement and relies on sporadic manual upgrades.
- Cost-effectiveness over time: The initial expenditure may be higher due to the blend of AI and continuous learning capabilities in the ANN-ISM technique. However, by reducing incident response expenses, improving the security posture, and eliminating manual intervention, this becomes less costly over time. The cost of cybersecurity management is low because it does not include the cost of stopping attacks before they occur.
- More substantial operational costs are associated with frameworks such as the NIST and CMMI frameworks, which use manual procedures, frequent upgrades, and frequent process monitoring and alignment for improvement. Although these procedures are useful for managing cybersecurity, they are not autonomous threat detection systems or constantly changing without human assistance.
- Holistic security approach: The ANN-ISM paradigm offers a comprehensive perspective on cybersecurity by combining structured security management with AI-based predictive analytics. This guarantees that every aspect of cybersecurity, from policy administration to threat detection, functions in unison to provide a comprehensive solution that addresses both managerial and technical aspects of cybersecurity.
- Although both the CMMI and NIST Cybersecurity Frameworks offer helpful advice for organizations to strengthen their cybersecurity practices, their positions are more dispersed. While CMMI covers process maturity to a considerable extent without fully including predictive technology (CTIS) and continuous learning of security architecture, NIST deals with risk management and control setups.
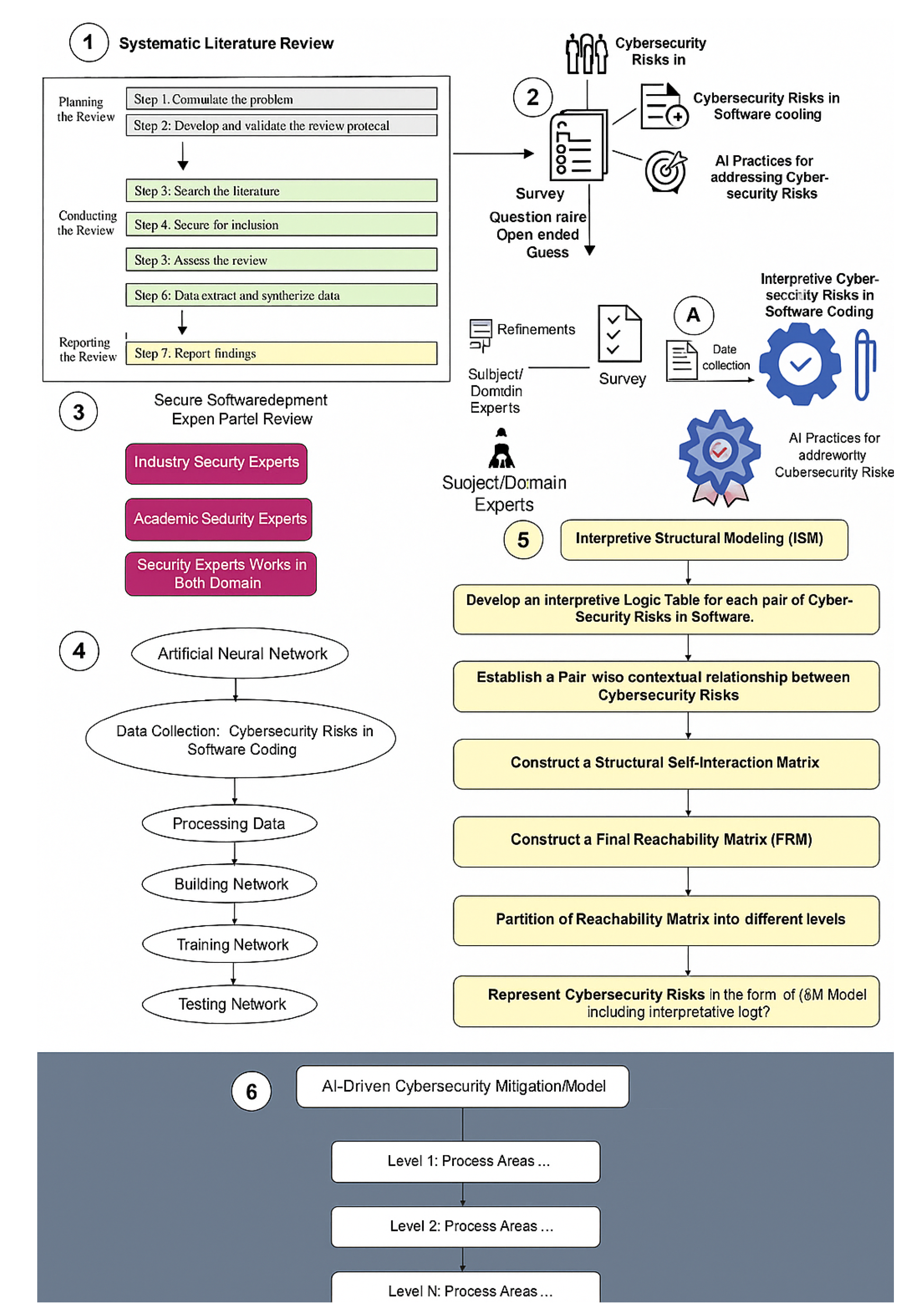
3. Methodology
3.1. Phase 1: Systematic Literature Review (SLR)
3.2. Search Strategy
| Digital libraries | Search string findings | Initial selection | Final selection |
| IEEE Xplore | 98 | 28 | 19 |
| ScienceDirect | 150 | 33 | 18 |
| ACM | 135 | 39 | 15 |
| Wiley Online Library | 60 | 10 | 8 |
| SpringerLink | 230 | 50 | 16 |
| Google Scholar | 2021 | 60 | 14 |
| Total | 2694 | 220 | 90 |
3.3. Data Extraction
3.4. The Findings
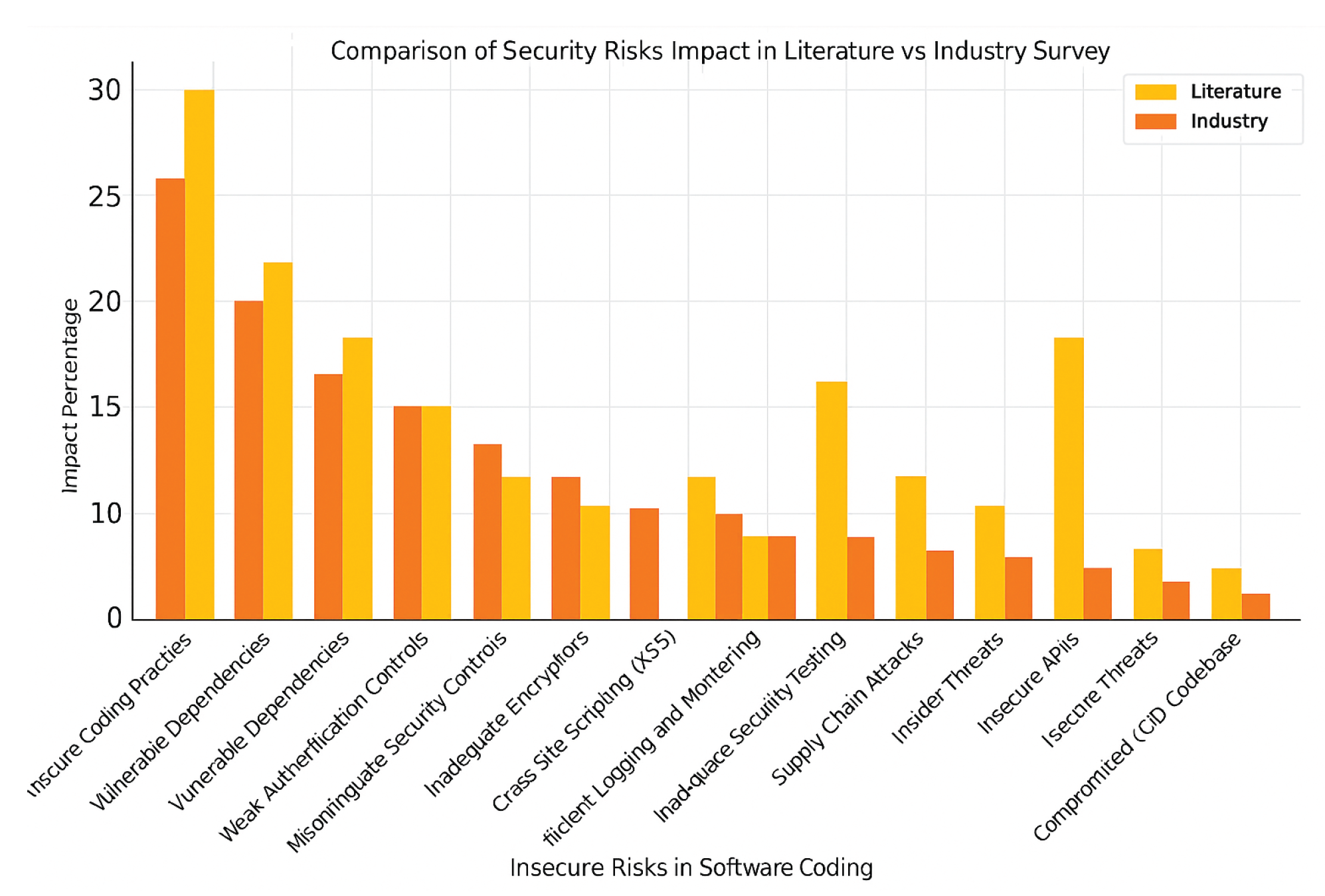
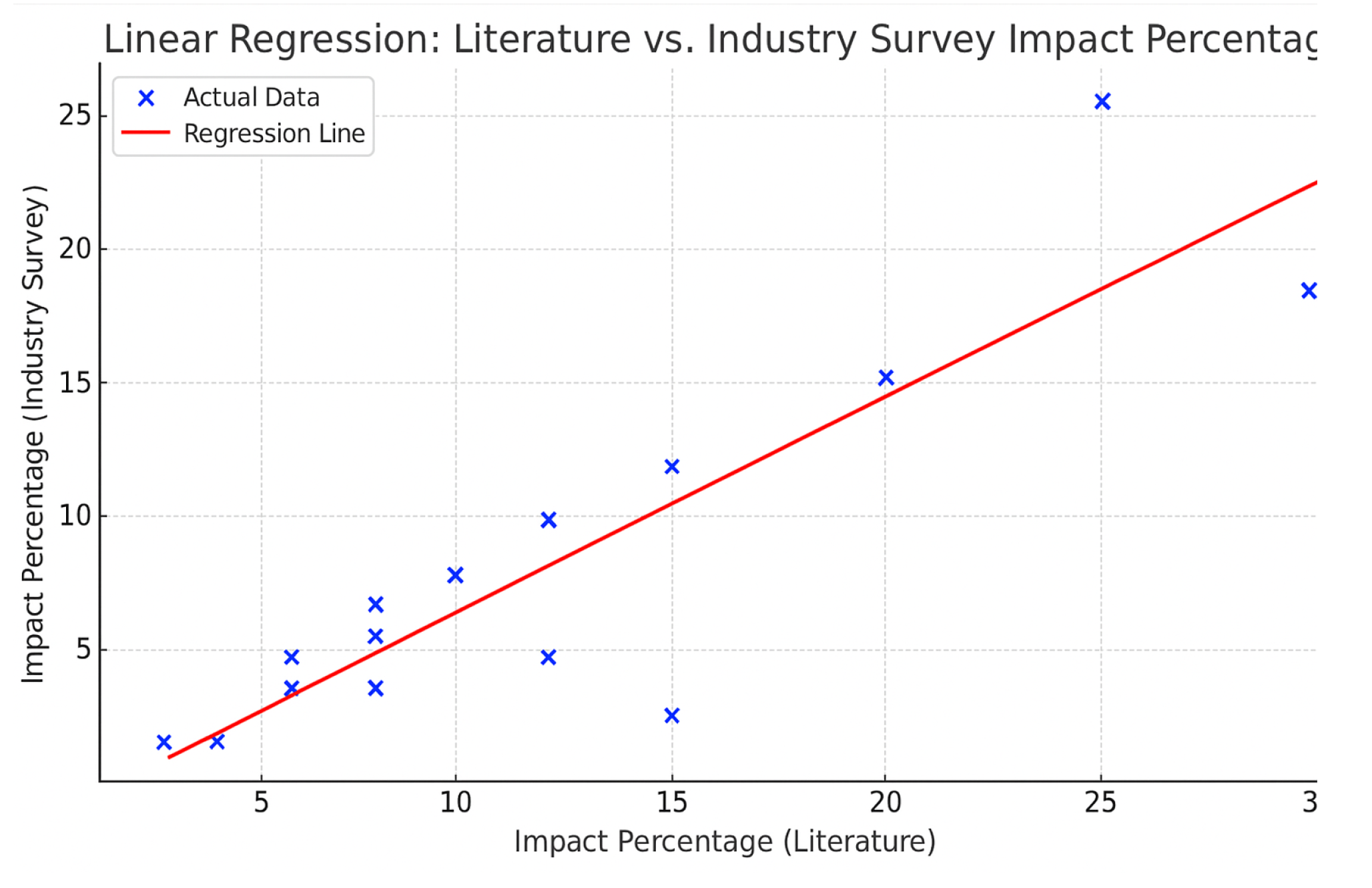
4. Findings and Conversations
Potential Cybersecurity Risks and Vulnerabilities in Software Coding
5. Development of AI-Driven Cybersecurity Mitigation Model for Secure Software Coding: Using ANN-ISM Approach
- ANN Data: We combine data from a survey of academic sources plus real-world studies to create a strong database to train the ANN system. We normalize and prepare our data to make it consistent and exact in its measurement.
- ISM Data: Through online interviews with professionals, we performed focus groups and surveys to learn how cybersecurity threats impact software coding.
- Training of the ANN: The model’s ability to process qualitative data is essential to the trained ANN. In order to forecast cybersecurity risk situations that are advantageous to each software coding system, the neural network system makes use of input data relationships.
- Constructing ISM: Qualitative data becomes the foundation for designing an ISM chart that depicts all security risk influences on software coding security.
- Hybrid Framework: Our group develops a single, cohesive strategy that blends ISM and ANN results. While ANN aids in threat prediction and secure setting identification, ISM demonstrates how various cybersecurity hazards interact with their fundamental elements.
- Model Validation: Our integrated model is put through a number of tests using a variety of datasets and security professionals to demonstrate that it can identify and address coding security issues in software.
- Implementation: By combining ANN forecasts with ISM analysis, the validated model creates comprehensive security protection techniques for coding projects, thereby preventing software coding issues.
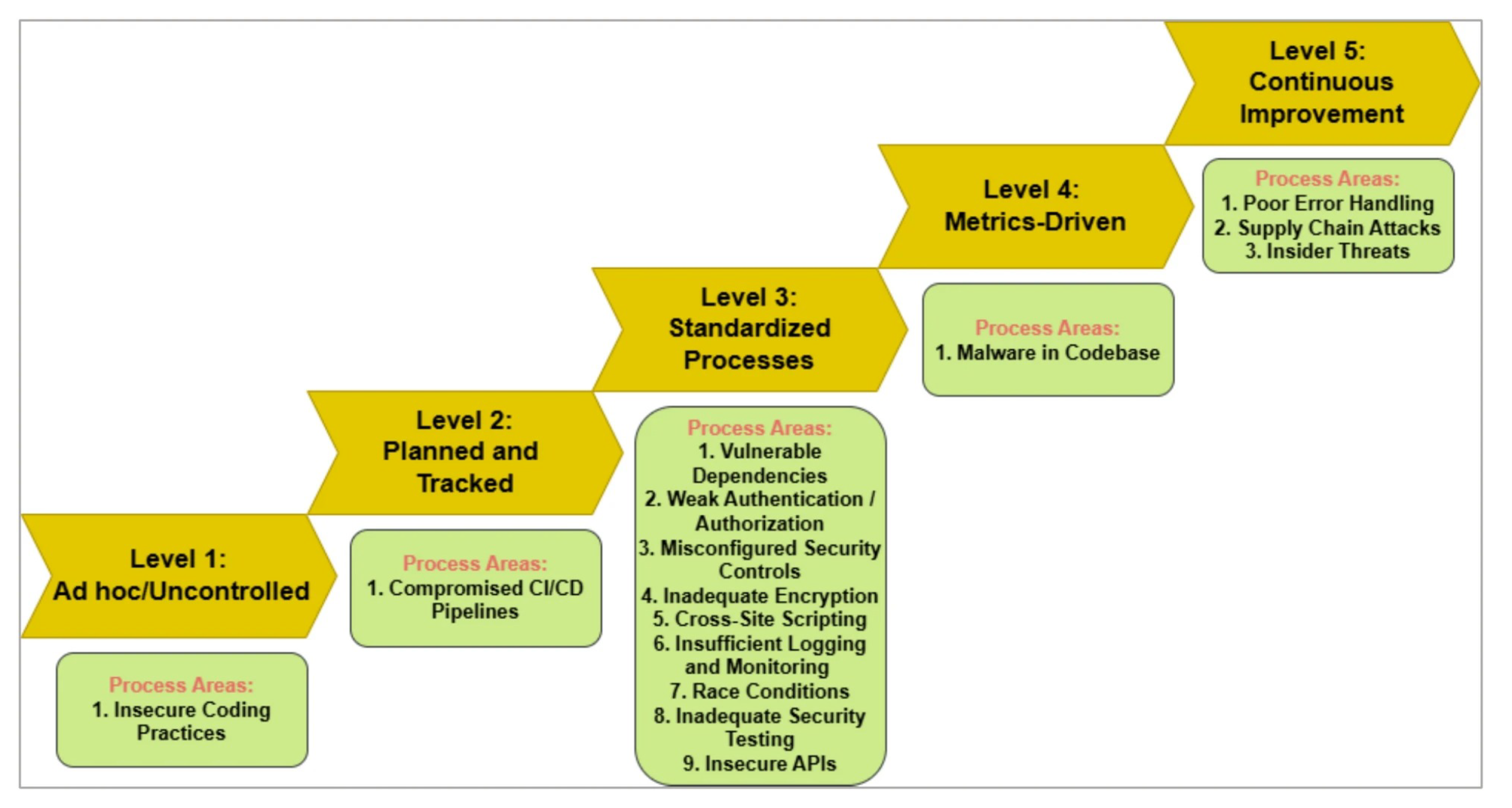
5.1. Levels Overview
-
Level-1: Ad hoc/Uncontrolled
- -
- Median Score:3
- -
- Appraisal: Advanced
- -
- Analysis: The software development organization received an Advanced appraisal, demonstrating the successful implementation of fundamental security measures, even though it falls into an early-stage category. AI technologies are used by 13 organizations to identify coding security flaws and prioritize taking the necessary corrective action. Because the strategies lack defined principles and effective distribution methods, they rely on informal tactics.
-
Level-2: Planned and Tracked
- -
- Median Score: 3
- -
- Appraisal: Advanced
- -
- Analysis: At this level, the secure software development businesses showed that their software security measures were planned and monitored. Organizations at the advanced level concentrate on allowing AI systems to identify anomalous system behavior and dangers. Installing security measures lays the groundwork for continued increased development phases.
-
Level-3: Standardized Processes
- -
- Median Score: 3
- -
- Appraisal: Advanced
- -
-
Analysis: The core focus is keeping all business systems uniform across all units. This phase shows that our organization uses AI correctly through established industry techniques:
- *
- Dependency Scanning
- *
- Vulnerability management
- *
- Secure Frameworks: This consistency ensures scalability and fosters long-term security resilience.
-
Level-4: Metrics Driven
- -
- Median Score- 3
- -
- Appraisal- Advanced
- -
-
Analysis: Measurable criteria help the association ameliorate, but an appraisal reveals performance pretensions that need adaptation:
- *
- AI is not being used enough for incident response and sophisticated monitoring.
- *
- Lack of established marks to measure and optimize AI-driven security sweeps. fastening on enriching criteria and using data perceptivity can elevate this position to advanced maturity.
-
Level-5: Nonstop enhancement
- -
- Median Score- 3
- -
- Appraisal: Advanced
- -
-
Analysis: The company exhibits early appreciation of nonstop enhancement as it begins to use performance pointers, but it also has difficulties when using AI advancements on a large scale. Choosing realistic path conditioning is difficult for the association since performance measures punctuate performance weaknesses:
- *
- Limited AI relinquishment in dynamic trouble modeling or real-time trouble responses.
- *
- There’s a straightforward procedure to ameliorate security measures. Cutting-edge AI tools and training will help the company turn its core moxie into comprehensive security advancements.
- Advanced Security at original situations. The association’s high appraisals in the first three situations indicate strong foundational and standardized practices.
- Decline in After situations. The major drop in conditions at the enhancement and Understanding situations shows that our association needs to strengthen its investment in security criteria while streamlining its systems continuously.
- AI as a Differentiator Beforehand-level success pointers show how well AI tools support secure programming while collecting trouble data and constantly covering.
-
Refine Metrics and KPIs( Level 4): apply measurable security criteria for assessing AI effectiveness, similar as:
- -
- Time to descry respond to pitfalls.
- -
- The number of vulnerabilities renovated through AI robotization.
-
Expand nonstop enhancement Efforts( Level 5):
- -
- Incorporate adaptive AI systems for real-time monitoring and predictive trouble modeling.
- -
- Establishing a feedback medium to learn from once security incidents and acclimate AI-driven processes consequently.
- Enhance Training and mindfulness: Investment in training inventors to align their practices with AI tools, especially at situations 4 and 5.
| Levels | Five orders of AI-driven cybersecurity mitigation model for secure software rendering | Median | Appraisal of software development association |
| Level 1 | Ad hoc/ unbridled | 3 | Advanced |
| Level 2 | Planned and tracked | 3 | Advanced |
| Level 3 | Formalized processes | 3 | Advanced |
| Level 4 | Metrics driven | 2 | Enhancement |
| Level 5 | Nonstop Enhancement | 1 | Understanding |
6. Conclusions
- Probing the possibility of combining ANN with different AI fabrics, similar underpinning literacy and inheritable algorithms, in order to ameliorate cybersecurity features could be the focus of future exploration.
- Operations across different disciplines: The ANN-ISM approach might be applicable to other areas, including pall computing protection, IoT security, and cybersecurity fabrics grounded on Blockchain technology.
- Perpetration and confirmation in practice unborn work needs to acclimatize and estimate this frame in practice, integrated into software development workflows.
References
- Admass, Wasyihun Sema, Yirga Yayeh Munaye, and Abebe Abeshu Diro. 2024. Cyber security: State of the art, challenges and future directions. Cyber Security and Applications 2, 100031.
- AI, NIST. 2023. Artificial intelligence risk management framework (ai rmf 1.0). https://nvlpubs. nist. gov/nistpubs/ai/nist. ai, 100–1.
- Al-Mhiqani, Mohammed Nasser, Tariq Alsboui, Taher Al-Shehari, Karrar hameed Abdulkareem, Rabiah Ahmad, and Mazin Abed Mohammed. 2024. Insider threat detection in cyber-physical systems: a systematic literature review. Computers and Electrical Engineering 119, 109489.
- Alliance, Cloud Security. 2025. “Agentic AI threat modeling framework: MAESTRO,”. Ph. D. thesis, OWASP. CSA blog: https://cloudsecurityalliance.org/blog/2025/02/06/agentic-ai-threat-modeling-framework-maestro.
- Chang, Younghoon, Siew Fan Wong, Christian Fernando Libaque-Saenz, and Hwansoo Lee. 2018. The role of privacy policy on consumers’ perceived privacy. Government Information Quarterly 35(3), 445–459.
- Domkundwar, Ishaan, Ishaan Bhola, Riddhik Kochhar, et al. 2024. Safeguarding ai agents: Developing and analyzing safety architectures. arXiv preprint arXiv:2409.03793.
- Gurtu, Anurag and Damien Lim. 2025. Use of artificial intelligence (ai) in cybersecurity. In Computer and information security handbook, pp. 1617–1624. Elsevier.
- Hasan, Mohammad Kamrul, Muhammad Shafiq, Shayla Islam, Bishwajeet Pandey, Yousef A Baker El-Ebiary, Nazmus Shaker Nafi, R Ciro Rodriguez, and Doris Esenarro Vargas. 2021. Lightweight cryptographic algorithms for guessing attack protection in complex internet of things applications. Complexity 2021(1), 5540296.
- Ilyas, Muhammad, Siffat Ullah Khan, Habib Ullah Khan, and Nasir Rashid. 2024. Software integration model: An assessment tool for global software development vendors. Journal of Software: Evolution and Process 36(4), e2540.
- Isabirye, Edward. 2024. Securing the ai supply chain: Mitigating vulnerabilities in ai model development and deployment. World Journal of Advanced Research and Reviews 22(2), 2336–2346.
- Itodo, Cornelius and Murat Ozer. 2024. Multivocal literature review on zero-trust security implementation. Computers & Security, 103827.
- Jaatun, Martin Gilje, Daniela S Cruzes, Karin Bernsmed, Inger Anne Tøndel, and Lillian Røstad. 2015. Software security maturity in public organisations. In International Conference on Information Security, pp. 120–138. Springer.
- Jedrzejewski, Felix Viktor, Davide Fucci, and Oleksandr Adamov. 2025. Threat modeling of large language model-integrated applications. arXiv preprint arXiv:2504.18369.
- Kaur, Ramanpreet, Dušan Gabrijelčič, and Tomaž Klobučar. 2023. Artificial intelligence for cybersecurity: Literature review and future research directions. Information Fusion 97, 101804.
- Khan, Rafiq Ahmad and Siffat Ullah Khan. 2018. A preliminary structure of software security assurance model. In Proceedings of the 13th International Conference on Global Software Engineering, pp. 137–140.
- Khan, Rafiq Ahmad, Siffat Ullah Khan, Muhammad Azeem Akbar, and Musaad Alzahrani. 2024. Security risks of global software development life cycle: Industry practitioner’s perspective. Journal of Software: Evolution and Process 36(3), e2521.
- Khan, Rafiq Ahmad, Siffat Ullah Khan, Habib Ullah Khan, and Muhammad Ilyas. 2022. Systematic literature review on security risks and its practices in secure software development. ieee Access 10, 5456–5481.
- Kitchenham, Barbara, O Pearl Brereton, David Budgen, Mark Turner, John Bailey, and Stephen Linkman. 2009. Systematic literature reviews in software engineering–a systematic literature review. Information and software technology 51(1), 7–15.
- Kuhail, Mohammad Amin, Sujith Samuel Mathew, Ashraf Khalil, Jose Berengueres, and Syed Jawad Hussain Shah. 2024. “will i be replaced?” assessing chatgpt’s effect on software development and programmer perceptions of ai tools. Science of Computer Programming 235, 103111.
- Manjunath, Vignesh and Marcel Baunach. 2024. A framework for static analysis and verification of low-level rtos code. Journal of Systems Architecture 154, 103220.
- Nanda, Manika, Mala Saraswat, and Pankaj Kumar Sharma. 2024. Enhancing cybersecurity: A review and comparative analysis of convolutional neural network approaches for detecting url-based phishing attacks. e-Prime-Advances in Electrical Engineering, Electronics and Energy, 100533.
- OWASP, Top. 2023. Owasp top 10 for large language model applications.
- Patel, Soham, Kailas Patil, and Prawit Chumchu. 2024. Bhramari: Bug driven highly reusable automated model for automated test bed generation and integration. Software Impacts 21, 100687.
- Pawlicki, Marek, Aleksandra Pawlicka, Rafał Kozik, and Michał Choraś. 2024. Advanced insights through systematic analysis: Mapping future research directions and opportunities for xai in deep learning and artificial intelligence used in cybersecurity. Neurocomputing, 127759.
- Shu, Raphael, Nilaksh Das, Michelle Yuan, Monica Sunkara, and Yi Zhang. 2024. Towards effective genai multi-agent collaboration: Design and evaluation for enterprise applications.
- Vouvoutsis, Vasilis, Fran Casino, and Constantinos Patsakis. 2025. Beyond the sandbox: Leveraging symbolic execution for evasive malware classification. Computers & Security 149, 104193.
- Wang, Pingyan, Shaoying Liu, Ai Liu, and Wen Jiang. 2024. Detecting security vulnerabilities with vulnerability nets. Journal of Systems and Software 208, 111902.
- Yeoh, William, Marina Liu, Malcolm Shore, and Frank Jiang. 2023. Zero trust cybersecurity: Critical success factors and a maturity assessment framework. Computers & Security 133, 103412.
- Zhou, Xiyu, Peng Liang, Beiqi Zhang, Zengyang Li, Aakash Ahmad, Mojtaba Shahin, and Muhammad Waseem. 2025. Exploring the problems, their causes and solutions of ai pair programming: A study on github and stack overflow. Journal of Systems and Software 219, 112204.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



