3. Proposed Method
In this part, we discuss the architectural layout and the optimization techniques of Quantum AIO-ChameleonGAN, which is a devised cybersecurity framework for the detection of camouflaged and mutating cyber attacks. This framework incorporates quantum learning principles, adaptive perception mechanisms, and angle-based detection alignment. In this case, the quantum portion is associated with quantum-inspired concepts, which includes superposition and entanglement.
The AIO applies adaptive optimization strategies, tracking the detection and mitigation of threat vectors as the adaptive optimization processes the angle to the threat [
21,
22,
23,
24,
25]. The chameleon paradigm reflects the form and manner of the system’s real-time detection modulation as driven by changing data behavior, thus, dynamic concealment, context-sensitive adaptability.
The framework is based on the GAN, which serves the dual purpose for generation of synthetic attack traffic as well as the discrimination of legitimate and anomalous traffic. These paradigms are integrated so that the AIO improves the operation of the quantum generator and the discriminator, responsive chameleon, developing adaptability and enhancing contextual detection precision.
Incorporating all three synergistic components makes up the proposed method:
Simulating polymorphic and stealthy attack patterns enabled by the Quantum Enhanced Generator.
Threat signature deviations detection by Quantum Discriminator integrated with AIO logic modules.
The Responsive Anomaly Alignment Regularization AIO Engine: An AIO Regularization Engine adjusting detection vectors and framework responsively to observed anomaly trajectories and angles.
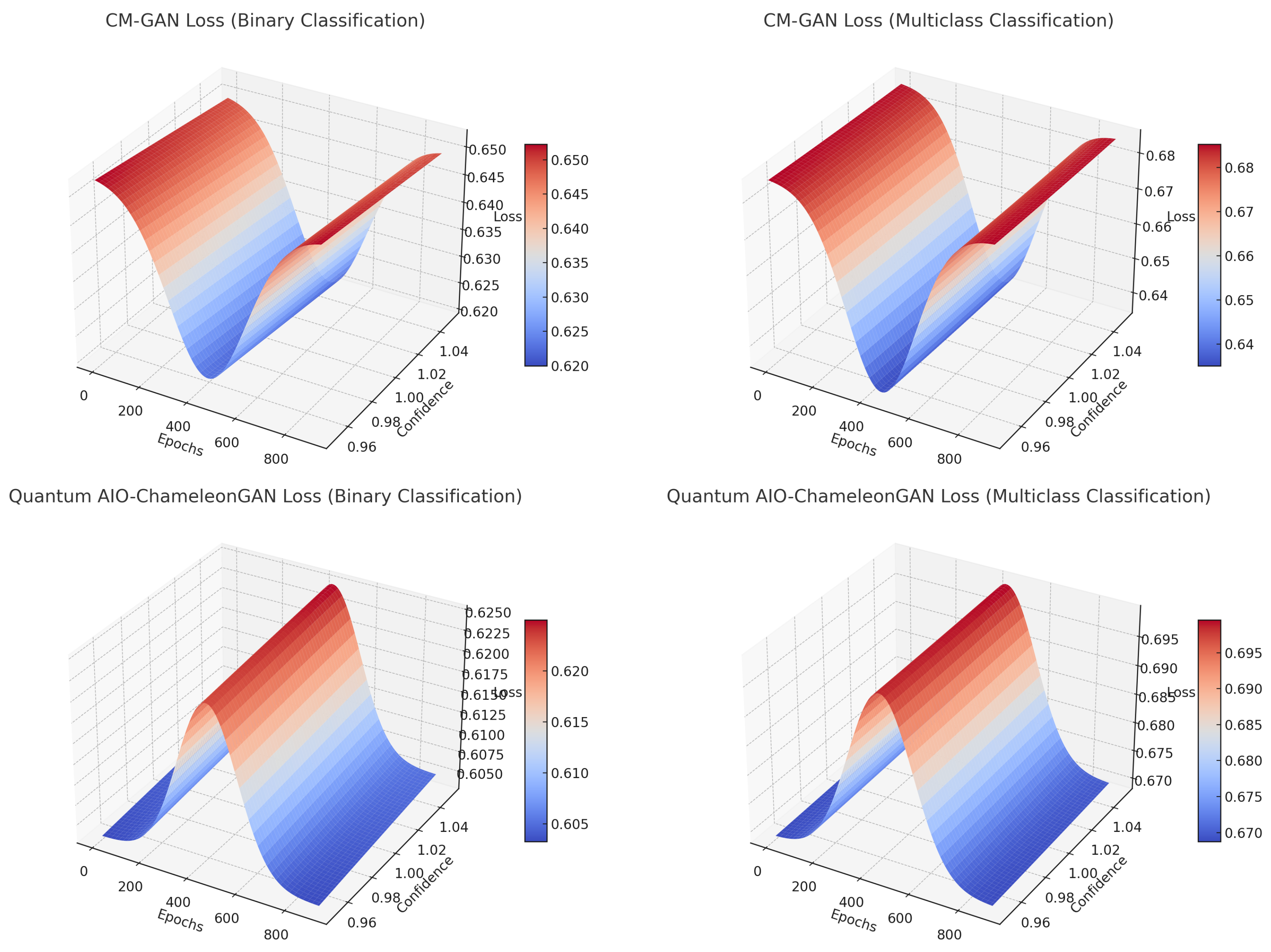
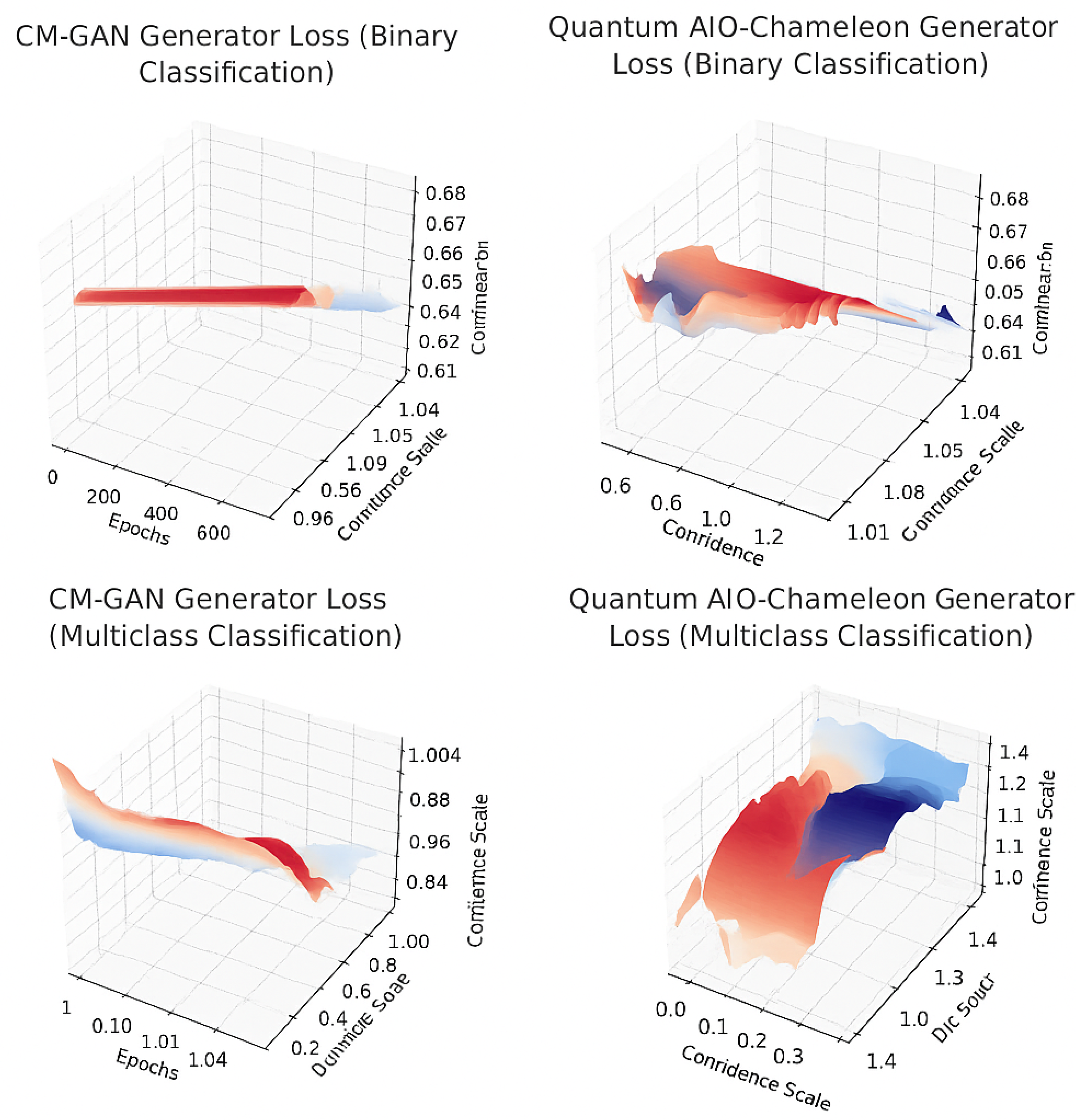
Using the CIC-UNSW-NB15- Augmented Dataset, the model is trained to extract features of different cyber threats, normal behaviors and network activities. Validation of the approach is done using the CM-GAN framework to measure robustness and stability in detection, provocation under adversarial variation, and adaptability under changing conditions of threats.
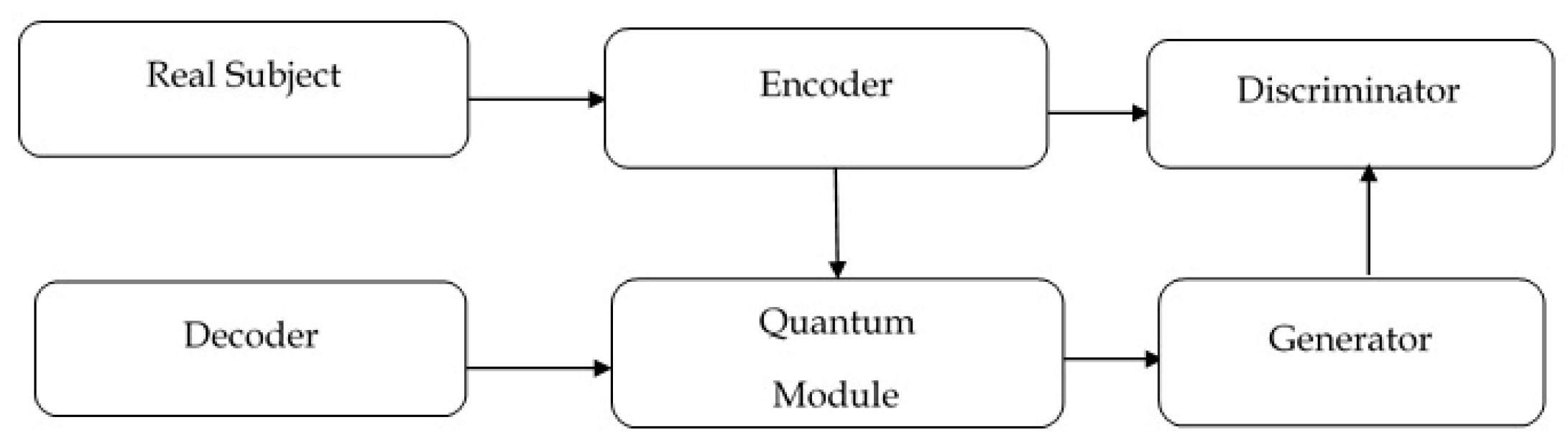
As seen in
Figure 1, the Quantum AIO-ChameleonGAN model’s operational workflow illustrates how cyber traffic is ingested and subsequently goes through feature extraction from relevant indicators to behavior the system captures and processes through the quantum GAN (generator and discriminator) to model complex threat dynamics.
An important part of the workflow is to calculate the angle of incidence () which captures the distance between the observation and the behavior that is considered normal (baseline profiles). This geometric measure assists the model in making decisions such as in accurately identifying anomalies and triggering the context-sensitive adaptive changes.
The system contains a feedback loop model that allows for the refining of the model in real time as well as learning continuously. This loop ensures that the accuracy of detection improves over time with the introduction of new traffic or patterns and even new threat behaviors and activities. The process is completed once a set threshold is achieved or is reset based on the traffic being analyzed continuously.
3.1. Adversarial Learning Objective for the Validating Method
The complex and camouflaged cyber threats are detected using the CM-GAN model which uses an adversarial learning framework to generate coherent synthetic attack patterns. It Usess a generator
G and a discriminator
D, which are trained using real samples
and latent inputs
, which are taken from a prior distribution.The main goal is to address the conflict of realism versus structural fidelity and generate data, with the following given objective:
Here, represents the generator’s output and M, denotes the attack matrix, where the attack matrix is concavely mapped, latent structural patterns represented by , and system reactions represented by . The discriminator evaluates realism of the structural norms in M, relative to the inputs, while the regularization function applies penalties for loss of matrix coherence. The scalar governs the intensity of this penalty, enforcing a balance between generative precision and structural fidelity. This is how CM-GAN is able to model adversarial behavior in a data-driven fashion and in a contextually system-structured manner.
3.2. Detection Mapping and Structural Encoding
Through, CM-GAN,
and
M refer to input and output perceptions of detection awareness, respectively.
where
is a non-linear transformation function (e.g., ReLU or (sigmoid)to influence detection within a system.
3.3. Cybersecurity Camouflaging Threats
Such threats to cybersecurity represent a class of sophisticated attacks constructed to avoid detection by merging with seamless layers of legitimate digital activity. Camouflaging threats exploit the gaps found within conventional security measures like those based on fixed rules or reliant on signatures. One of the most common examples is polymorphic malware, which changes its signature or code structure continuously. relying solely on tools like PowerShell or WMI (Windows Management Instrumentation) to execute its functions without ever saving anything on the disk to aid in detection.
Advanced Persistent Threats (APTs), expands the scope of the previous ones by being more dangerous. They are defined by observed persistent stealthy long-term intrusions by expert malicious actors. These are often executed in multi-stage processes that require silence to sustain access to vital resources.
Other avoidance techniques involve the use of encrypted or obfuscation, where malicious content delivers payloads beneath the content inspection mechanisms and hidden from the scrutiny of content inspection mechanisms. Steganographic malware extends this by embedding the malicious payloads in files perceived to be harmless, like images or videos, making it impossible for file-based scanners. Furthermore, the risk posed by zero-day exploits also greatly concerns absolutely identifying these vulnerabilities as their exploits are unknown.
The insider threat’s taciturn nature greatly poses a risk, particularly because the user has the privilege of being a legitimate user and therefore, works with his given access, often exhibiting behavior that mimics performing routine activity. Another notable form is Living off the Land (LotL) attacks that use pre-installed administrative tools to perform malicious activities without the use of external software. Also, Domain Generation Algorithms (DGAs) create domain names for command-and-control communications in a resilient manner, effectively bypassing blacklist filter-based blockers.
Finally, supply chain attacks introduced threats by compromised third-party software or hardware components, often hidden in updates or trusted integrations. These different threat vectors depend on concealment, adaptability, and the mimicry of the environment which makes it necessary to use advanced detection frameworks such as Quantum AIO-ChameleonGAN.
3.4. Quantum AIO-ChameleonGAN Detection Mechanism and Anomaly Trigger Mechanism
The quantum AIO-chameleonGAN detection mechanism incorporates the quantum computing and stealth behavior disguise principles to enhance the detection of stealthy cybersecurity breaches. The core of the mechanism the Discriminator learns to distinguish real traffic samples from synthetic ones using quantum optimized parameters to encode interactions of complex features like entropy patterns, timing deviations, and protocol anomalies. These settings give the model the capability to detect camouflaged threats that blend into normal traffic, similar to the way a chameleon perceives its surroundings.
The Generator simulates the corresponding attack behavior using the same parameters , producing highly realistic attack simulations, which allows the model to evolve its attack patterns to mimic benign behavior. A critical component is the Angle of Incidence Optimization function , which punishes the generator when the camouflaging features become too complex. This regularization guarantees that the generator does not produce traffic which is utterly unobtainable to even the most advanced systems.
An anomaly occurs when the confidence of the discriminator for a real input drops below a confidence threshold . With the same behavior, if the discriminator accepts as a threat crafted by a generator with too much confidence (greater than ), the model shows a gap in its detection capability. Besides, if the surpasses a set threshold of , this means that the threat generated has too much camouflage which should raise an alarm.
The self-calibrating cyber-security framework is created using quantum-boosted feature detection, adversarial learning, and camouflage modeling by the Quantum AIO-ChameleonGAN model. This makes it capable of identifying both previously documented and undocumented threats, especially those which use concealment, privilege abuse or legitimate system tools to bypass detection. This makes it a critical development in next generation intrusion detection systems.
3.5. Angle of Incidence Optimization Strategy
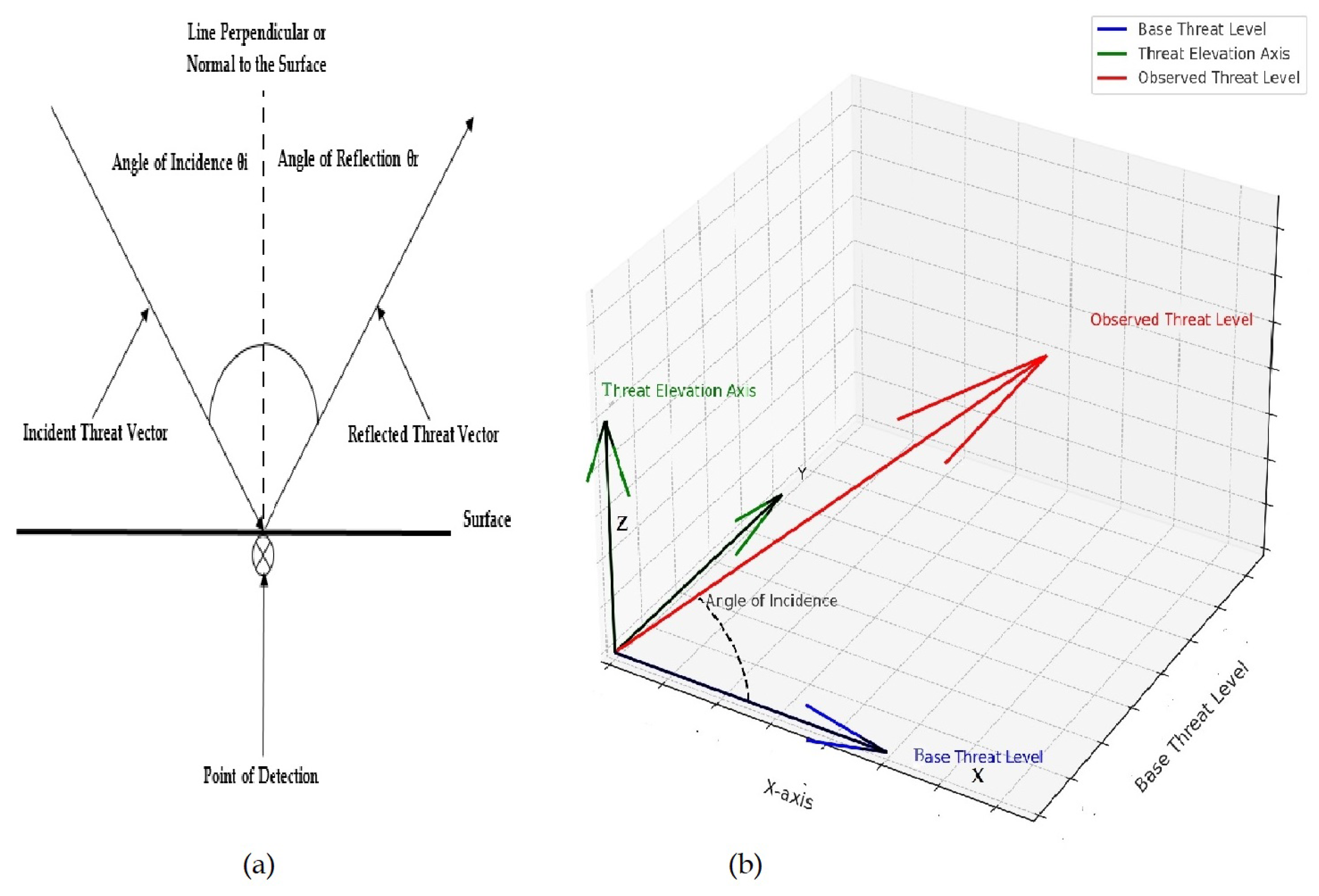
From its name, the ChameleonGAN model, draws its core concept from the classical Law of Reflection. It claims that the angle of incidence is equal to the angle of reflection. Cyber threats can be thought of as incident rays, and baseline threat behavior as the normal vector to a reflective surface. Thus, the deviation from the baseline threat behavior is the reflected vector which analogously is the system’s perception of threat intensity.
In this formulation, the angle of incidence
is used to quantify how significantly an observed threat vector
deviates from the baseline threat vector
. This is calculated using the inverse cosine of the dot product between the two vectors, expressed mathematically as:
The excerpt describes a system that recognizes and mimics observing behavior which helps in avoiding detection. On the contrary, a greater angle signifies much deviation, which could signify some abnormal or malicious behavior.
In Figure (2 a), the classical reflection concept is illustrated, depicting rays as different types of threats. The incident ray is the incoming cyber threat, the normal vector is the expected baseline behavior, and the reflected ray is the observed anomaly. In Figure (2 b), the same concept is modified and applied in visualization of threat detection. The vertical axis shows the Observed Threat Level and the horizontal axis shows the Baseline Threat Level, with the angle as the most important detection metric.
Figure 2.
Calculating the angle of incidence.
Figure 2.
Calculating the angle of incidence.
If the computed angle is less than , the threat is classified as camouflaged. This means the activity is very close to normal activity, which means detection is sensitive. If ranges between and , the activity is classified as stealthy and shows moderate drift. Angles greater than suggests behavior deviation is erratic give rise to mutating threats and becomes easier to detect through standard anomaly detection algorithms. This approach is useful because it allows adaptive optimization of threat perception thresholds. As increases, the system automatically lowers the detection sensitivity thresholds, reducing the chances of false negatives. This enhances detection accuracy, and allows for more intelligent and context-aware responses. Essentially, the model emulates a reflective surface which accentuates anomalies of threats by quantifying behavioral deviations from the set baselines and norms.
The introduction of physical constraints alongside intelligent systems gives rise to the QuantumAIO-ChameleonGAN, a new paradigm for cybersecurity. Instead of static classification, it approaches threat detection with active and intelligent systems viewing the threat as a dynamically changing geometry of behavior. This geometry of behavior allows for the optimization to be angle-based which aids in the efficient identification of camouflaged, stealthy, or mutating threats and improves accuracy and resilience in adversarial detection environments.
|
Algorithm 1:Quantum AIO-ChameleonGAN Optimization. |
- 1:
Input: CIC-UNSW-NB15 Augmented Dataset (benign and attack samples) - 2:
Output: Trained Generator G, Discriminator D, and optimized angle-aligned detection pipeline - 3:
Initialize Quantum Generator G and Quantum Discriminator D
- 4:
Extract independent variables from packet metadata and system attributes - 5:
Calculate intervening variables : Camouflage Confidence, Mutation Entropy, Quantum Latent Angle - 6:
Compute the angle of incidence
- 7:
Generate synthetic threat instance
- 8:
Evaluate discriminator confidence score
- 9:
Formulate AIO-based adversarial loss and update parameters of G and D
- 10:
Repeat until convergence or early stopping based on F1-score - 11:
return Trained G, D, and optimized angle-aligned detection pipeline |
This algorithm starts by configuring quantum generator and discriminator components. As a first step, it obtains the input features, then computes the angle of incidence (
). Finally, the synthetic threats go through the discriminator to be assessed for the likelihood of being anomalies. Computation of the AIO-based loss enables the model’s parameters to be iteratively optimized until the detection accuracy targets the predefined goals.
|
Algorithm 2:AIO-Based Anomaly Detection and Response. |
- 1:
Input: Test sample x, AIO-threshold , and AIO response map
- 2:
Output: Anomaly classification and corresponding automated response - 3:
Compute angle of incidence from current feature vector and benign baseline - 4:
Pass x through discriminator:
- 5:
ifthen
- 6:
Classify as anomaly - 7:
Trigger AIO-aligned response: - 8:
if then
- 9:
Send silent alert (high camouflage risk)
- 10:
Isolate software and notify admin - 11:
else
- 12:
Disable access, log event, and retrain - 13:
end if
- 14:
else - 15:
Classify as normal and log timestamp - 16:
end if - 17:
return Anomaly status and executed response |
The flow starts by calculating
for a test input and passes the sample through the trained discriminator to get a confidence score. If the score is below a threshold, the system classifies it as an anomaly and applies angle-specific automated responses ranging from silent alerts to full system lockdowns. Normal traffic is logged without response.
|
Algorithm 3:Validation Using CM-GAN. |
- 1:
Input: CIC-UNSW-NB15 Augmented Dataset, CM-GAN baseline metrics - 2:
Output: Validation of detection performance - 3:
Train CM-GAN using the same dataset and extracted variable matrices
- 4:
Evaluate CM-GAN detection accuracy, precision, recall, and loss convergence - 5:
Train Quantum AIO-ChameleonGAN under identical conditions - 6:
Compare both models on: - 6:
F1-score - 6:
Generator and Discriminator Loss Stability - 6:
Anomaly Detection Rate - 6:
Camouflage and Mutation Sensitivity - 7:
Validate if AIO-ChameleonGAN outperforms CM-GAN in detecting subtle, adaptive threats - 8:
Return: Detection validation comparison results |
This algorithm trains a baseline CM-GAN using the same dataset and matrix structure as the proposed model. It then compares performance metrics (F1-score, loss, anomaly rate) between CM-GAN and Quantum AIO-ChameleonGAN. The goal is to validate that AIO-ChameleonGAN outperforms CM-GAN in detecting subtle, mutating threats.
3.6. Advantages of Proposed Method
The AIO-ChameleonGAN incorporates quantum superposition and entanglement for enhanced polymorphic threat simulation, introduces AIO loss to encode context-aware detection aligned with the behavior of evolving attacks, demonstrates superior anomaly sensitivity on camouflaged and mutating threats, validated against CM-GAN and enables automated, angle-aligned mitigation strategies based on the nature and confidence of the detected anomaly.