Submitted:
29 July 2025
Posted:
30 July 2025
You are already at the latest version
Abstract
Keywords:
1. Dedication
2. Main Results
3. Introduction
- Exodus to the Digital Renaissance — a strategic introduction summarizing the imperative, philosophical foundations, and social backdrop of Exodus 2.0.
- The Exodus 2.0 Law: A New Paradigm in Sociology and Graph Theory describing the mathematical and theoretical underpinnings for the Law of Autocatalytic Inevitability.
Related Work
Our Contribution.
Positioning Among Existing Decentralized Systems
Decentralized Autonomous Organizations (DAO)
Decentralized Finance (DeFi)
Trust Networks
Glossary of Key Terms
Theoretical Framework
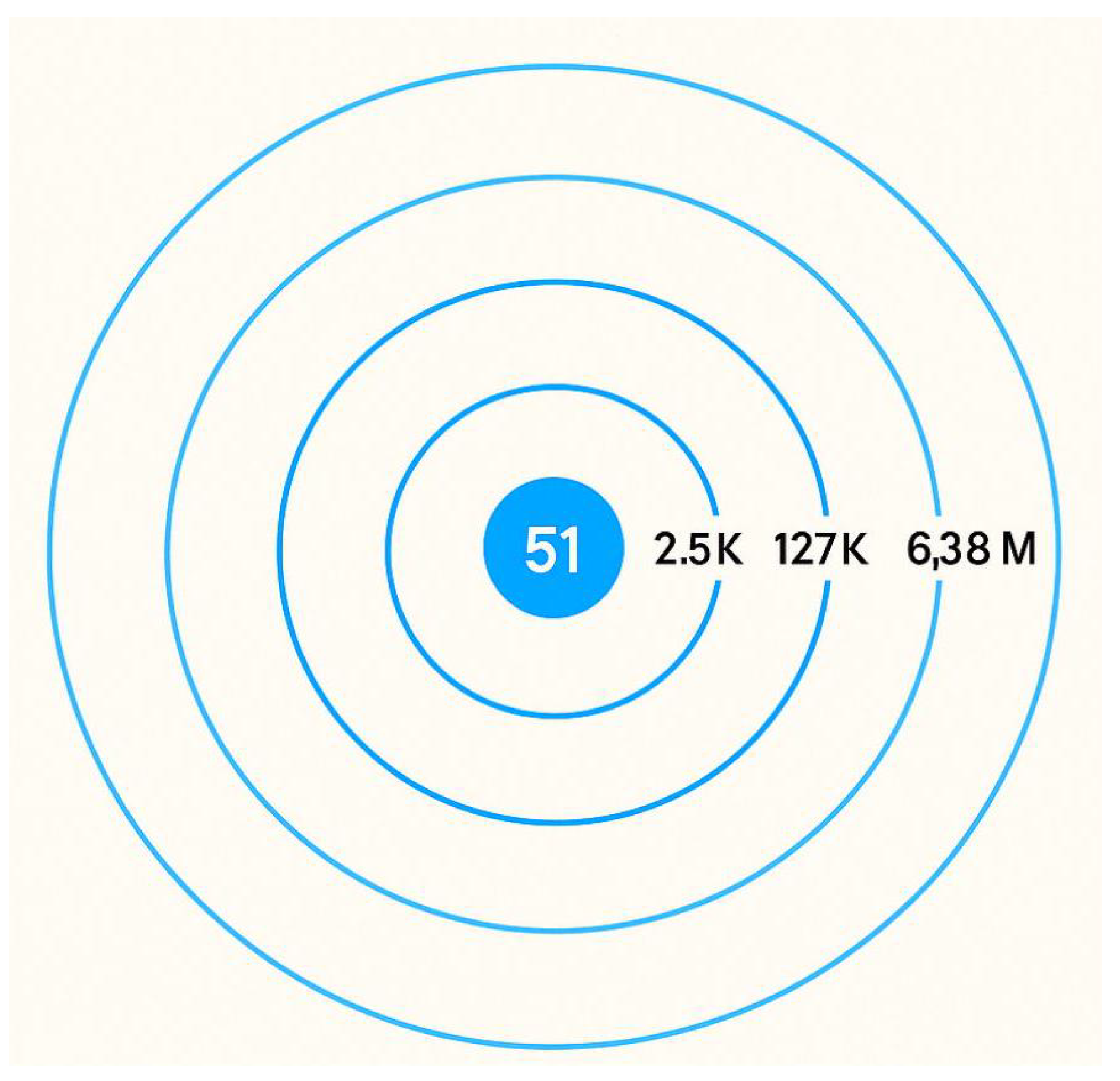
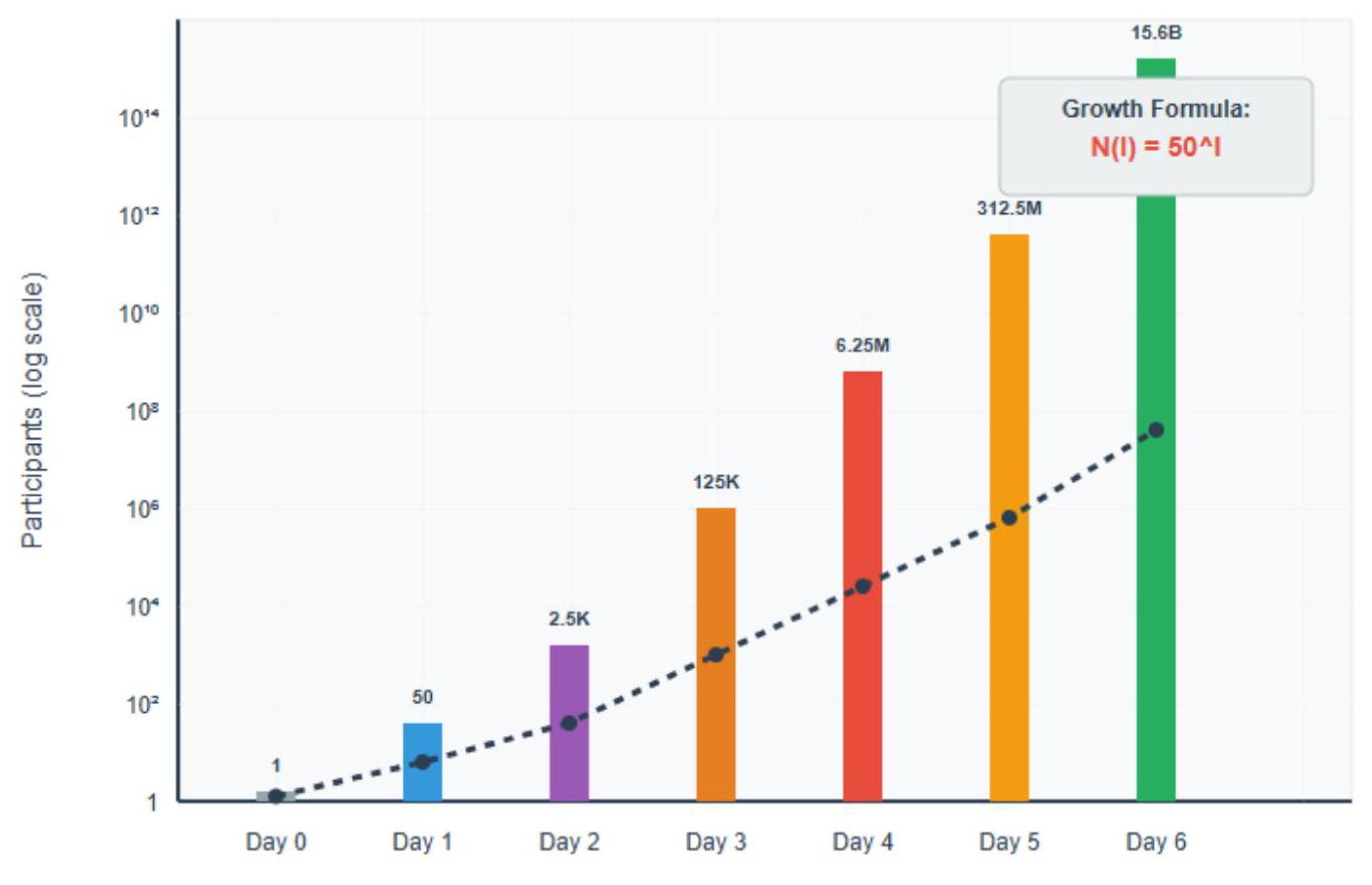
2.1 The Law of Autocatalytic Inevitability
- is the number of participants at level I
- is the average number of empathic, non-overlapping connections per participant (approximately 50, consistent with Dunbar’s research)
- I represents the levels of "handshakes" or degrees of separation
- Harm Prevention: for all actions a and participants v
- Connection Inheritance: new parent parent }
- Empathic Foundation: All connections are based on pre-existing relationships of genuine mutual care, active support, and reciprocal concern within participants’ Dunbar circles
Mathematical Formalization of Empathic Connections:
- (Dunbar constraint based on cognitive limitations)
- : mutual_care(v,u) = true (verified through personal invitation)
- : active_support(v,u) = true (demonstrated willingness to assist)
- : reciprocal_concern(v,u) = true (bidirectional empathic bond)
- E(v_new) = E(v_parent) U {v_parent}
- v_new v_parent
- trust_propagation(v_new, u) = trust_inheritance(v_parent, u) parent )
4. Mathematical Proof by Induction:
- Base Case ( ): The initial node has connections. Thus,
- Inductive Step ( ): Each node at level connects new nodes, creating participants at level
- This deterministic pattern continues indefinitely, proving global network expansion is mathematically inevitable once initiated.
4.1. Structural Irrelevance of Trust ( )
- No Internal Monetary Transactions: All financial transactions occur externally, eliminating possibilities of fraud, unauthorized access, or internal financial breaches.
- No Built-in Communication Channels: Coordination occurs exclusively via external trusted channels, preventing manipulation, spam, or phishing attacks.
- Complete Transparency of Actions: All obligations and actions are openly visible, preventing hidden abuses or covert manipulations.
- Complete Voluntary Participation: Participants retain total autonomy in their actions and interactions, eliminating coercion or enforced participation.
- Financial-related actions {fraud, data_theft, unauthorized_access} are structurally impossible due to No Internal Monetary Transactions
- Communication-related actions (manipulation, impersonation, spam) are structurally impossible due to No Built-in Communication Channels
- Hidden abuses {abuse, covert_manipulation} are structurally impossible due to Full Transparency
| Aspect | Traditional Decentralized Systems | DSI Exodus 2.0 |
|---|---|---|
| Trust Verification | Required through cryptographic proofs, consensus mechanisms, reputation scores, smart contracts | Structurally irrelevant due to |
| System Complexity | Energy-intensive verification, technical barriers to entry, scalability limitations, new attack vectors | Elegant simplicity with natural participation, unlimited scalability, zero attack vectors |
| Core Problem | How to verify strangers? | Trust verification unnecessary |
| Harm Prevention | Complex security systems and verification protocols | Architectural impossibility of harmful actions |
| Scalability | Limited by consensus mechanisms and verification overhead | Unlimited through mathematical inevitability |
| Participation Barriers | Technical knowledge, financial resources, verification processes | None – based on existing empathic connections |
| Network Foundation | Technology-first approach with cryptographic guarantees | Human empathy formalized through existing relationships |
| Economic Model | Transaction fees, mining costs, verification expenses | Zero transaction costs, reputation-based value |
| Governance | Complex consensus protocols, potential for centralization | Self-regulating through structural incentives |
| Implementation | Requires new infrastructure and behavioral adoption | Activates existing social architecture |
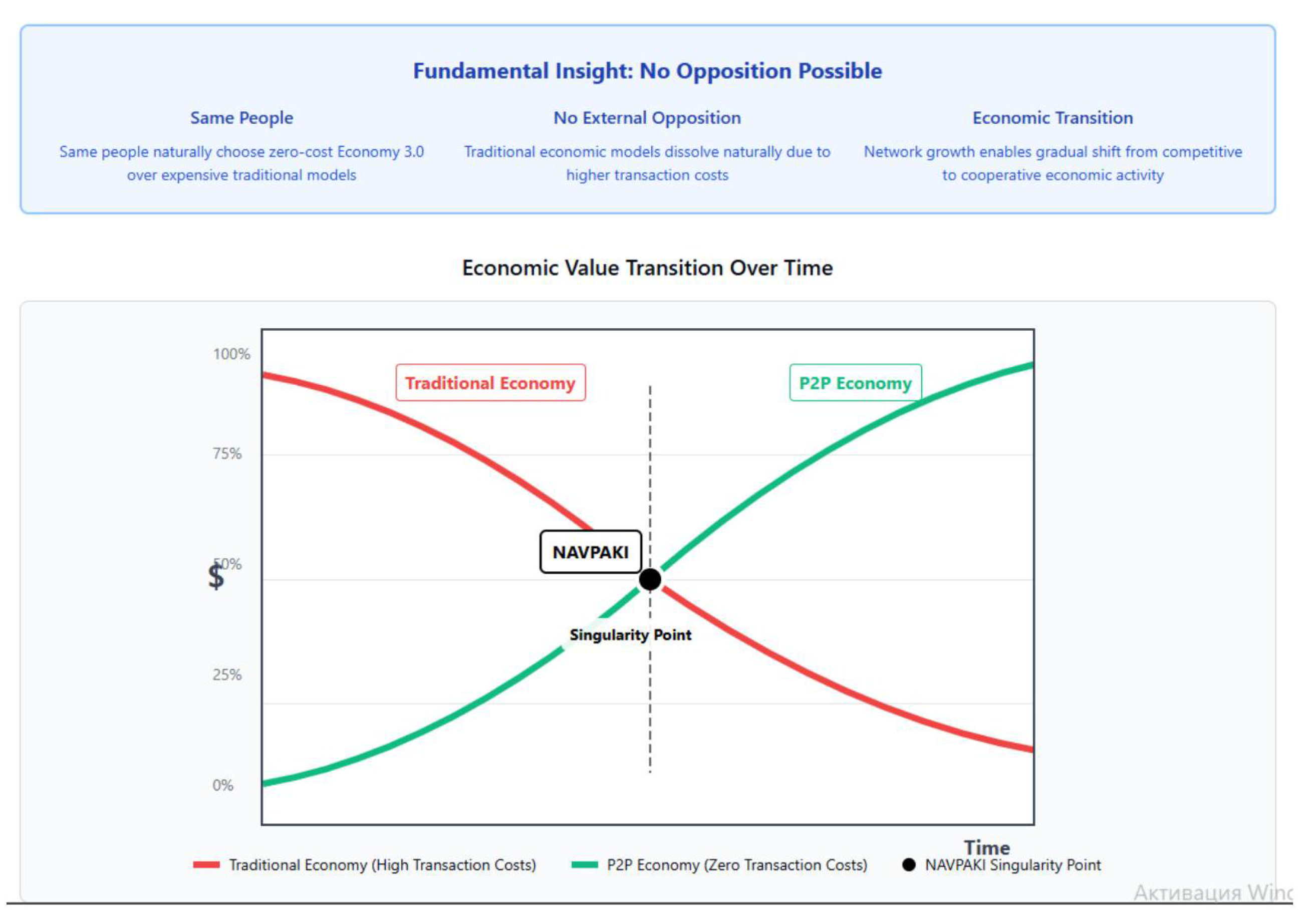
4.2. The NAVPAKI Threshold: When the Empathic Economy Becomes Dominant
- is the economic activity in the traditional (centralized) system;
- represents activity in the emerging empathic network;
- and influence the interdependence of the systems;
- gathers the natural inefficiencies present in the hierarchy;
- captures the network growth self-generated momentum;
- is the number of members of the empathic network with bounded exponential growth, satisfying , where and accounts for invitation redundancy in social connections.
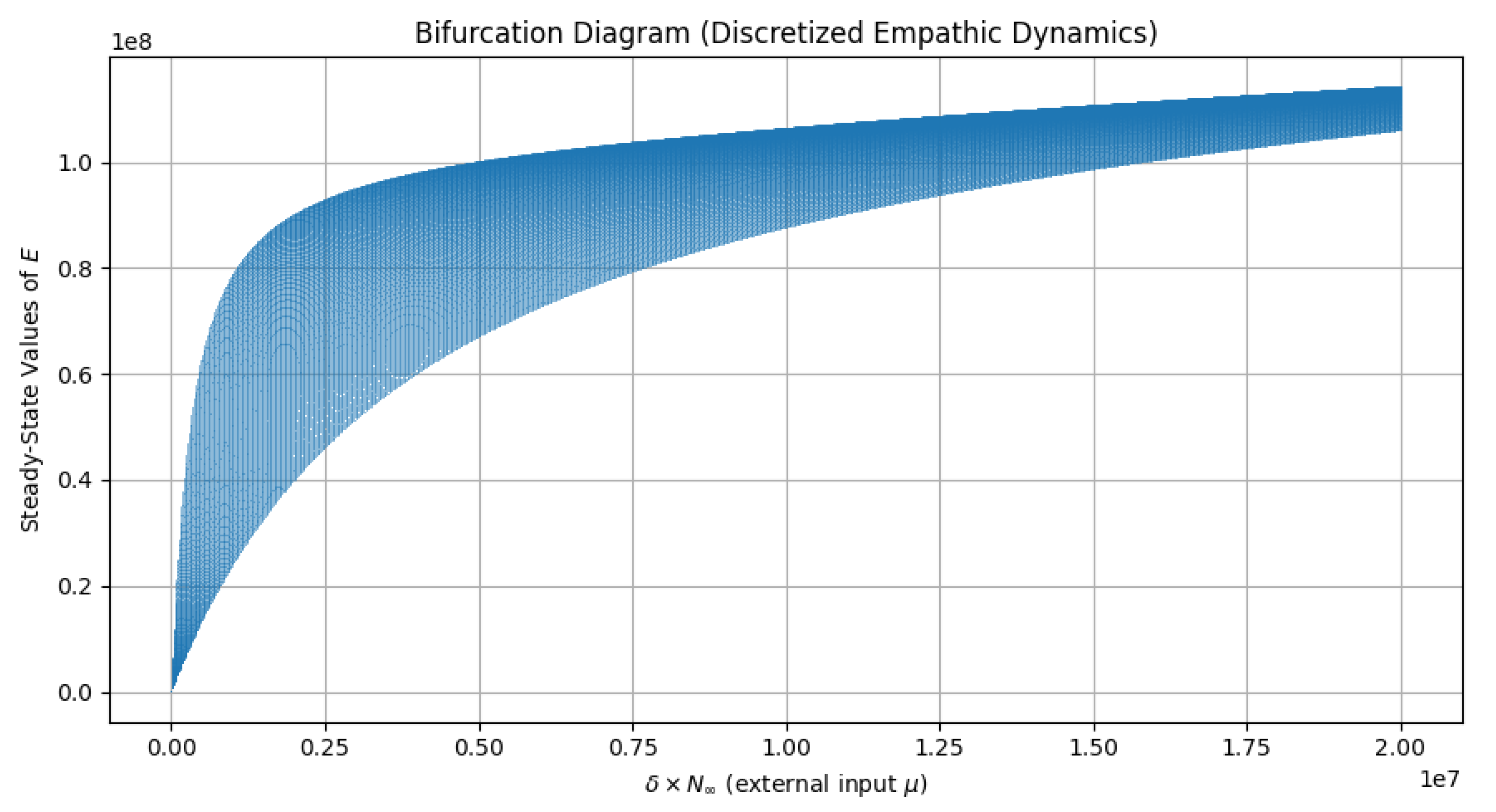
4.3. 4.7 Discrete-Time Bifurcation Analysis of Empathic Dynamics
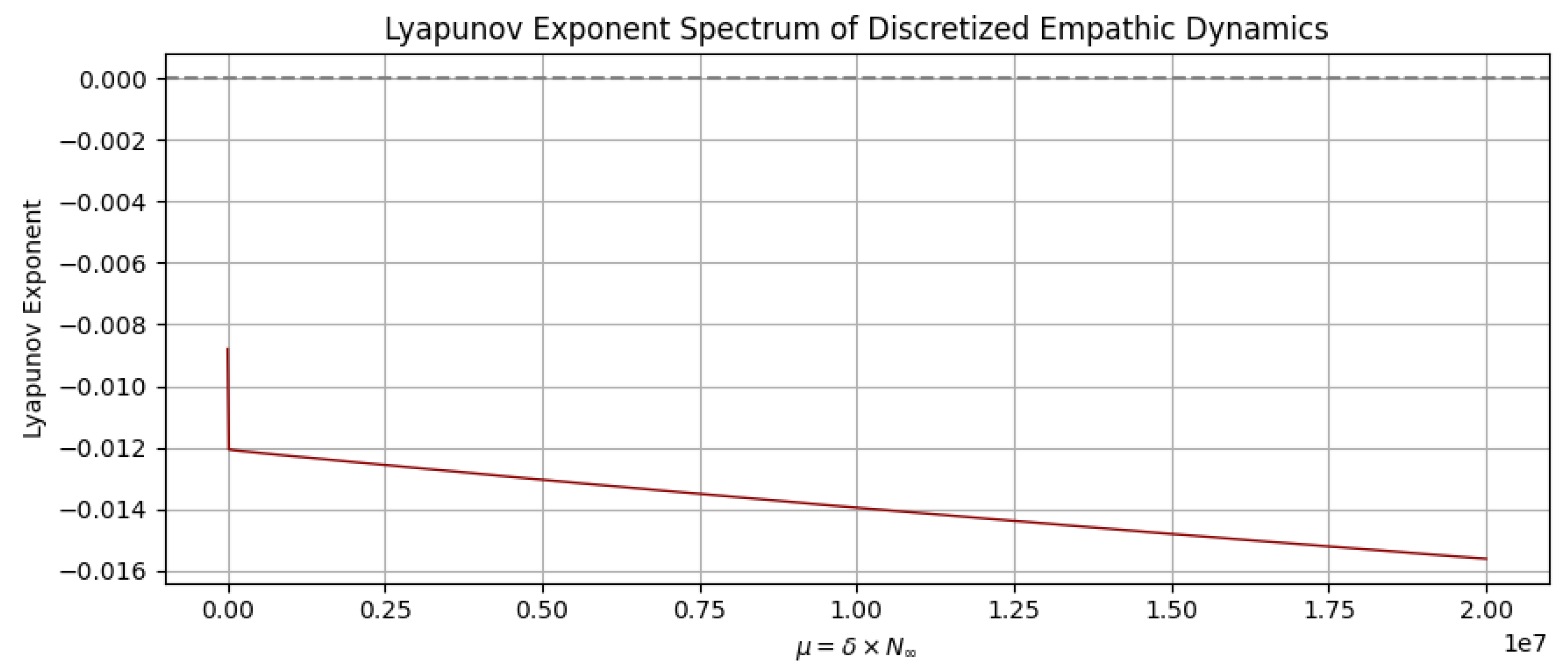
4.4. 4.8 Lyapunov Stability Analysis and Network Resilience
Architectural Implementation via the Social Organizer
Empathic Foundation with Structural Inheritance
- Transparent Mutual Risk Reinsurance
Harm Prevention Through Architectural Constraints
Self-Regulation Through Structural Incentives
3. Methodology
3.1 The Social Organizer Architecture
Design Philosophy: Neutrality and Non-Interference
Scalability Through Simplicity
| Function | Components | Implementation | Design Principle |
|---|---|---|---|
| RECORD | - Member data - Commitments - Initiatives - P2P registry maintenance | Decentralized ledger documenting voluntary social contracts | Purely neutral recording without enforcement |
| NOTIFICATION | - Emergency aid allocation - Minimum 1 request unit - Instant & dynamic - AI-assisted donor matching | Proportional distribution to confirmed connections with intelligent participant identification | Non-interference in human coordination |
| FACILITATION | - Self-regulated dynamic crowdfunding - AI-assisted donor search - User-requested collaborations - Database-integrated matching | Opportunity discovery and collaboration support without central curation | Facilitation without control |
| Constraint | Implementation | Eliminated Risks | Mathematical Guarantee |
|---|---|---|---|
| Financial Isolation | Records only voluntary commitments; no monetary transactions within system; external payment channels only | Fraud, unauthorized access, payment processing vulnerabilities | |
| Communication Externalization | No built-in messaging features; all coordination through external trusted channels | Manipulation, spam, phishing, impersonation attacks | |
| Complete Transparency | All actions visible to relevant network participants; open obligations and fulfillments | Secret negotiations, backdoor abuse, undisclosed conflicts | |
| Individual Autonomy | Complete participant control over commitment levels and connection choices | Coercion, forced participation, external control mechanisms |
| Principle | Mechanism | Outcome |
|---|---|---|
| Empathic Foundation with Structural Inheritance | Participants invite only known individuals within empathic circles | Complete local graphs that scale globally through connection inheritance |
| Transparent Mutual Risk Reinsurance | All obligations recorded in transparent P2P registry | Collective risk distribution with full auditability |
| Harm Prevention Through Constraints | Implementation of four architectural constraints | Mathematical guarantee for all participants |
| Self-Regulated AI-Assisted Matching | Dynamic crowdfunding and donor search, AI-supported cooperation | Human-controlled interaction without algorithmic dominance |
Core Functions of the Social Organizer:
- Record
- Notification
- Facilitation
3.2 Mathematical Model of Economic Transition
3.2.1 Network Growth Dynamics
3.2.2 Economic Transition Dynamics
Parameter explanations:
- (Empathic Conversion Rate, approx. 0.8) - based on observed behavior in Chinese mutual aid platforms.
- (Network Effect Amplification, approx. 1.2) - derived from Metcalfe’s Law, adapted for "empathic network", reflecting how each new connection increases total network value.
- y (Hierarchical Entropy, approx. 0.1) - represents natural losses due to inefficiencies in traditional structures.
- (Empathic Momentum, approx. 0.3) - estimated from Dunbar number dynamics and trust inheritance rates, reflecting the network’s intrinsic growth power.
Note on Parameters:
3.2.3 The NAVPAKI Point: Critical Threshold Analysis
- becomes greater than
- The growth rate of also surpasses that of
Threshold approximation:
3.2.4 Parameter Estimation and Data Sources
- Primary source: Efficiency analysis of Chinese mutual aid platforms (2016-2019)
- Supporting data: Xiang Hu Bao participation rates (Ant Group, 2018-2021)
- Validation: Comparative study of traditional vs. peer-to-peer insurance uptake rates
- Confidence interval: based on cross-platform variance
(Network Effect Amplification ):
- Derived from: Modified Metcalfe’s Law for empathic networks
- Calculation: Value_increase Connection_increase ) from Facebook connectivity data (Boldi et al., 2012)
- Adjustment factor: standard Metcalfe coefficient to account for trust overhead reduction
- Range: [1.1, 1.3] depending on network density
Y (Hierarchical Entropy ):
- Based on: Transaction cost analysis in traditional hierarchical systems (Coase, 1937)
- Empirical foundation: Administrative overhead rates in conventional insurance (8-35%)
- Normalized value: Average friction coefficient across multiple institutional studies
- Literature range: [0.08, 0.15] across different organizational structures
Empathic Momentum :
- Theoretical basis: Dunbar number propagation dynamics active connections)
- Simulation data: Monte Carlo modeling of invitation cascades (10,000 iterations)
- Historical validation: Viral coefficient analysis from successful peer-to-peer platforms
- Sensitivity analysis: variation does not affect qualitative model behavior
3.3 Empirical Validation
3.3.1 Large-Scale Network Connectivity: Facebook Global Analysis
- Scale: 721 million active users connected through 69 billion friendship links
- Average Path Length: 4.74 degrees of separation (3.74 intermediaries)
- Connectivity Density: of all reachable pairs connected within 5 degrees
- Geographic Validation: Consistent small-world properties across diverse regions Italy (3.89), Sweden (3.90), USA (4.32)
3.3.2 Economic Precedent: Chinese Mutual Aid Platforms
- Scale: Tens of millions of active participants across multiple platforms
- Cost Efficiency: Annual contribution of approximately per participant per year
- Coverage Magnitude: Up to in medical coverage per person
- Risk-Benefit Ratio: 1:333,333 return on contribution
- Administrative Overhead: vs. in traditional insurance systems
| Aspect | Traditional Insurance | Chinese Platforms | DSI Exodus 2.0 |
|---|---|---|---|
| Cost for Participants | euros/month | 15 cents/year | No payments, voluntary commitments |
| Transparency | Low | Moderate | Complete ( ) |
| Centralization | Fully centralized | Centralized | Fully decentralized |
| Administrative Overhead | 25-35% | 8% | Zero |
| Resilience to External Pressure | Vulnerable | Vulnerable | Resistant (formless) |
| Accessibility | Bureaucratic, selective | Simple | Universal |
| Innovation Potential | Low | Moderate | Unlimited (Economy 3.0) |

3.3.3 Historical Parallel: Arvut Hadadit Principles
- Duration: Practiced for centuries across diasporic Jewish communities
- Resilience: Maintained cohesion despite political upheaval and geographic dispersion
- Scalability: Support networks extended across continents
- Trust Mechanism: Based on mutual guarantees rather than institutional enforcement
4. Results
4.1 Exponential Growth Recap and Real-World Constraints
4.2 Structural Properties of the Emerging Network
- Formless Architecture
- Inherent Universality
- Architectural Inclusivity
- Neutralization of Authority
4.3 Mathematical Inevitability and the Non-Empirical Nature of the Law
Why Empirical Validation Is Not Applicable
Engineering vs. Discovery
5. Discussion
5.1. Paradigmatic Implications
5.2. Transcendence of Traditional Constraints
-
No Cold Start Problem: High perceived value (mutual aid and reinsurance) naturally initiates adoption within empathic circles.
- -
- No Scaling Friction: Network growth is exponential and deterministic——requiring no centralized coordination.
- -
- No Trust Burden: Trust is structurally irrelevant; guarantees safety without verification.
- -
- No Governance Overhead: Incentives emerge naturally from participant benefit; no enforcement or arbitration required.
5.3. The NAVPAKI Point: Economic Singularity
5.4. Regulatory Irrelevance and Formless Design
5.5. Implementation Readiness
5.6. Implementation Challenges and Engineering Solutions
Technical Challenges:
- Infrastructure Requirements: Basic internet connectivity and mobile device access across diverse populations
- Interface Design: Creating intuitive user experiences that maintain architectural constraints $H(a,v) = 0$
- Scalability Engineering: Supporting millions of simultaneous participants without performance degradation
Social Adoption Factors:
- Cultural Adaptation: Varying rates of technology adoption across different societies and age groups
- Language Localization: Ensuring accessibility across linguistic and cultural boundaries
- Digital Literacy: Supporting users with diverse technical competencies
Regulatory Considerations:
- Compliance Frameworks: Operating within existing legal structures while maintaining a decentralized architecture
- Data Protection: Ensuring privacy compliance (GDPR, CCPA) within a transparent obligation registry
- Cross-Border Coordination: Managing international participants across different jurisdictions
Implementation Timeline:
5.7. Mathematical Laws Require Activation, Not Validation
The Category Error of Empirical Testing
Mathematical Laws vs. Behavioral Models
| Mathematical Laws | Behavioral Models |
| (Autocatalytic Inevitability) | “Will people adopt this technology?” |
| (Pythagorean Theorem) | “Do users prefer interface A or B?” |
| (Newton’s Second Law) | “Will trust emerge in communities?” |
| Logically derived certainty | Empirically tested hypothesis |
| Requires proper activation | Requires behavioral validation |
What DSI Exodus 2.0 Requires
Technical Requirements:
- Infrastructure capable of supporting billions of simultaneous participants
- Architectural implementation of constraints
- Connection inheritance mechanisms:
- Empathic foundation formalization within Dunbar-limited networks
Not Required:
- Behavioral testing or user acceptance studies
- Gradual adoption curves or market validation
- Proof-of-concept pilots or controlled experiments
- Empirical verification of mathematical relationships
Self-Organization as a Living System
- Activate the three architectural conditions
- Enable connection inheritance and empathic formalization
- Withdraw as the network becomes self-sustaining
Engineering Implementation, Not Experimental Validation
6. Conclusions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Bacharach, M., Guerra, G., & Zizzo, D. J. (2007). The self-fulfilling nature of trust in risky coordination. Theory and Decision, 63(4), 349–389.
- Barabási, A.-L. (2002). Linked: The New Science of Networks. Perseus Publishing.
- Barabási, A.-L., & Albert, R. (1999). Emergence of scaling in random networks. Science, 286(5439), 509–512. [CrossRef]
- Boldi, P., Rosa, M., & Vigna, S. (2012). Four degrees of separation. In Proceedings of the 4th Annual ACM Web Science Conference (pp. 33–42).
- Buterin, V. (2020). The meaning of decentralization. Ethereum Foundation. https://ethereum.org/en/developers/docs/decentralization/.
- Chen, L., & Wang, H. (2020). Mutual aid platforms in China’s digital economy: Innovation and regulatory challenges. Journal of Financial Innovation, 6(1), 1–18.
- China Banking and Insurance Regulatory Commission (2020). Guidelines on the regulation of mutual aid platforms. Official CBIRC Document.
- Coase, R. H. (1937). The nature of the firm. Economica, 4(16), 386–405.
- Dunbar, R. I. M. (1992). Neocortex size as a constraint on group size in primates. Journal of Human Evolution, 22(6), 469–493. [CrossRef]
- Eigen, M. (1971). Self-organization of matter and the evolution of biological macromolecules. Naturwissenschaften, 58(10), 465–523.
- Graeber, D. (2011). Debt: The First 5,000 Years. Melville House.
- Greco, T. H. (2001). Money: Understanding and Creating Alternatives to Legal Tender. Chelsea Green Publishing.
- Hardin, R. (2002). Trust and Trustworthiness. Russell Sage Foundation.
- Hill, R. A., & Dunbar, R. I. M. (2003). Social network size in humans. Human Nature, 14(1), 53–72. [CrossRef]
- Holland, J. H. (1992). Complex adaptive systems. Daedalus, 121(1), 17–30.
- Kauffman, S. A. (1993). The Origins of Order: Self-Organization and Selection in Evolution. Oxford University Press.
- Kropotkin, P. (1902). Mutual Aid: A Factor of Evolution. McClure Phillips & Co.
- Li, H., Ma, Y., & Sun, T. (2021). From innovation to regulation: The lifecycle of Chinese mutual aid platforms. China Economic Review, 67, 101–115.
- Liu, M., Zhang, Y., & Li, X. (2021). The rise and fall of mutual aid insurance platforms in China: A case study of regulatory intervention. Asia Pacific Journal of Management, 38(2), 445–467.
- Mauss, M. (1925). The Gift: Forms and Functions of Exchange in Archaic Societies. Cohen & West. [CrossRef]
- Maymounkov, P., & Mazières, D. (2002). Kademlia: A peer-to-peer information system based on the XOR metric. In International Workshop on Peer-to-Peer Systems (pp. 53–65). Springer.
- McKinsey & Company (2020). China’s mutual aid platforms: Lessons for global fintech. McKinsey Global Institute.
- Milgram, S. (1967). The small-world problem. Psychology Today, 2(1), 60–67. [CrossRef]
- Nakamoto, S. (2008). Bitcoin: A peer-to-peer electronic cash system. https://bitcoin.org/bitcoin.pdf.
- Nowak, M. A. (2006). Five rules for the evolution of cooperation. Science, 314(5805), 1560–1563. [CrossRef]
- Ostrom, E. (1990). Governing the Commons: The Evolution of Institutions for Collective Action. Cambridge University Press.
- Putnam, R. D. (2000). Bowling Alone: The Collapse and Revival of American Community. Simon & Schuster.
- PwC China (2020). Mutual aid platforms in China: Market dynamics and regulatory landscape. PricewaterhouseCoopers Financial Services.
- Shmidel, F. (1999). The Metaphysics of Meaning. Moscow: CARTE BLANCHE.
- Shmidel, F. (2012). Will to Joy. Moscow: New Literary Review.
- Shmidel, F. (2019). Power. Kyiv: ArtHuss.
- Simon, H. A. (1962). The architecture of complexity. Proceedings of the American Philosophical Society, 106(6), 467–482.
- Tomasello, M. (2009). Why We Cooperate. MIT Press.
- Vicsek, T., Czirók, A., Ben-Jacob, E., Cohen, I., & Shochet, O. (1995). Novel type of phase transition in a system of self-driven particles. Physical Review Letters, 75(6), 1226–1229. [CrossRef]
- Wang, J., Chen, S., & Zhao, L. (2019). Digital mutual aid: How technology reshapes social insurance in China. Technology in Society, 58, 101–112.
- Watts, D. J. (2004). Six Degrees: The Science of a Connected Age. W. W. Norton & Company.
- Watts, D. J., & Strogatz, S. H. (1998). Collective dynamics of ’small-world’ networks. Nature, 393(6684), 440–442. [CrossRef]
- Yang, F., & Chen, R. (2021). Regulatory challenges of mutual aid platforms: Evidence from China’s market intervention. Journal of Financial Regulation and Compliance, 29(4), 445–461.
- Zhang, K., & Wu, D. (2020). Waterdrop and the evolution of peer-to-peer mutual aid in China. Harvard Business Review China, 15(3), 34–42.
- Simon, H. A. (1962). The architecture of complexity. Proceedings of the American Philosophical Society, 106(6), 467–482. Retrieved from http://links.jstor.org/sici?sici=0003-049X%2819621212%29106%3A6%3C467%3ATAOC%3E2.0.CO%3B2-1.
- Vicsek, T., Czirók, A., Ben-Jacob, E., Cohen, I., & Shochet, O. (1995). Novel type of phase transition in a system of self-driven particles. Physical Review Letters, 75(6), 1226–1229. [CrossRef]
- Watts, D. J. (2004). Six Degrees: The Science of a Connected Age. W. W. Norton & Company.
- Rafik, Z., & Salas, A. H. (2024). Chaotic dynamics and zero distribution: implications and applications in control theory for Yitang Zhang’s Landau Siegel zero theorem. European Physical Journal Plus, 139, 217. [CrossRef]
- Lubalin, A. (2025). Discovery of the Law of Autocatalytic Inevitability: A New Natural Law Governing Network Self-Organization (Version 2.0) [Preprint]. Zenodo. https://zenodo.org/records/15778286.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




