Submitted:
12 July 2025
Posted:
14 July 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
II. Literature Review
II.A Gaps in the Literature:
- Many systems depend a lot on rules set by people. This means they need regular help from experts to remain effective.
- Few studies offer clear implementation examples or guides for beginners in the field.
- There is little discussion on how to design and extend rule-based systems for educational or hybrid use cases.
II.B Transition to Proposed System
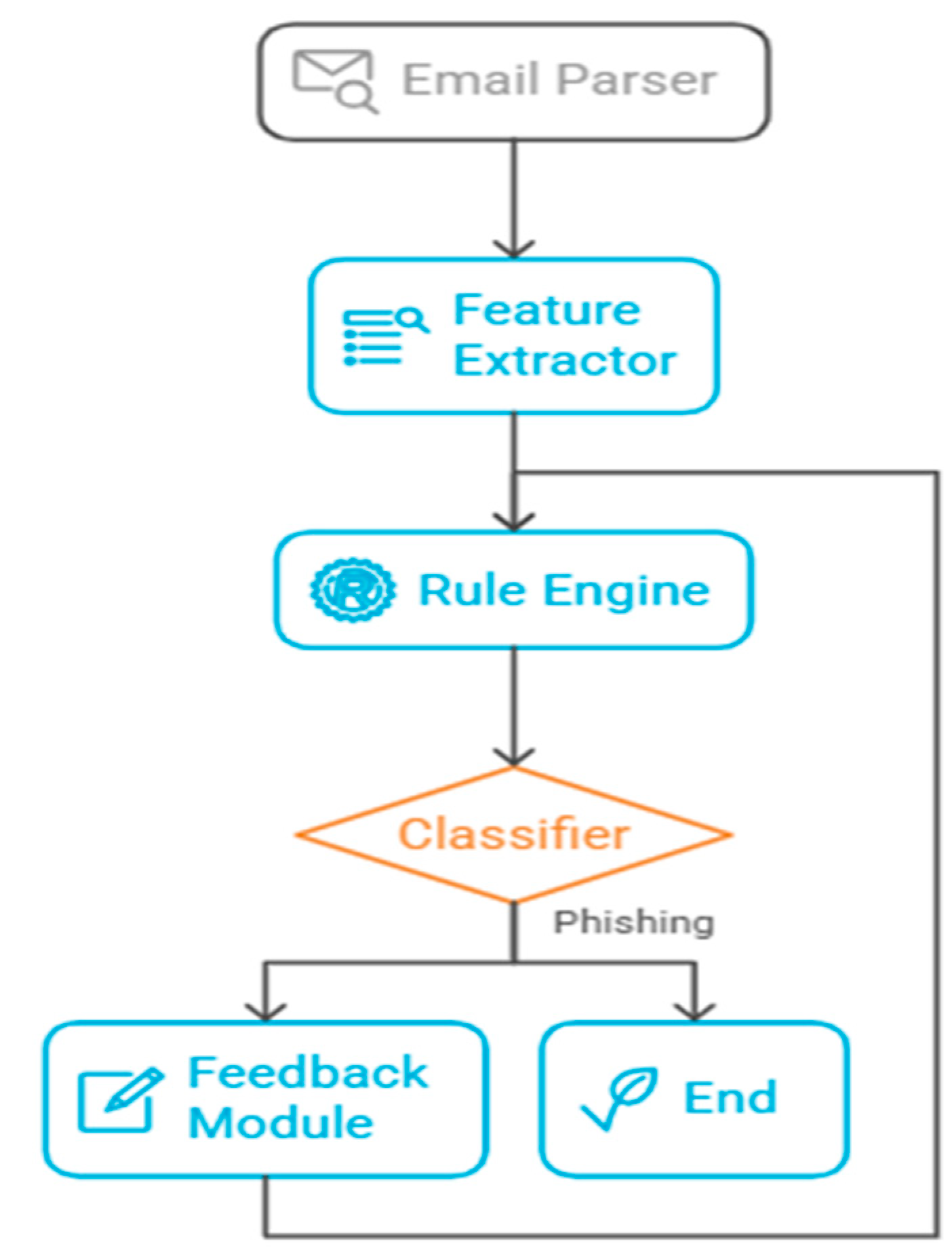
III. Proposed Rule-Based AI Agent Architecture
- Email Parser: Extracts headers, body text, links, and metadata.
- Feature Extractor: Identifies key phishing signs like mismatched sender domains, suspicious URLs, and urgent language.
- Rule Engine: Uses a set of predefined rules to assess the likelihood of phishing.
- Classifier: Decides if the email is phishing or legitimate.
- Feedback Module: Allows manual overrides and updates to the rule base.
III.A Feedback Module
- Manual Rule Updates by Experts: Cybersecurity professionals or system administrators can review misclassified emails, such as false positives and negatives, and update the rule set as needed. For example, if a new phishing campaign uses a previously unseen tactic, like domain spoofing with subdomains, an expert can create a new rule to spot these patterns.
- User Reporting Integration: End users usually notice suspicious emails before anyone else. The system lets users report suspected phishing emails directly. These reports are recorded and examined to find common traits that might lead to new rules or improvements to current ones.
- Semi-Automated Rule Suggestions: The system does not learn automatically like machine learning models, but it can track common patterns from flagged or reported emails. Using these logs, the system can propose new rules, such as “New pattern detected: shortened URL + brand name + no prior contact.” Experts review these suggestions before they are added to the active rule set.
- IF sender domain ≠ brand name in email THEN classify as phishing
- IF contains shortened URL AND no contact history THEN classify as phishing
- IF subject line includes "Urgent" OR "Action Required" AND contains attachments THEN flag for review
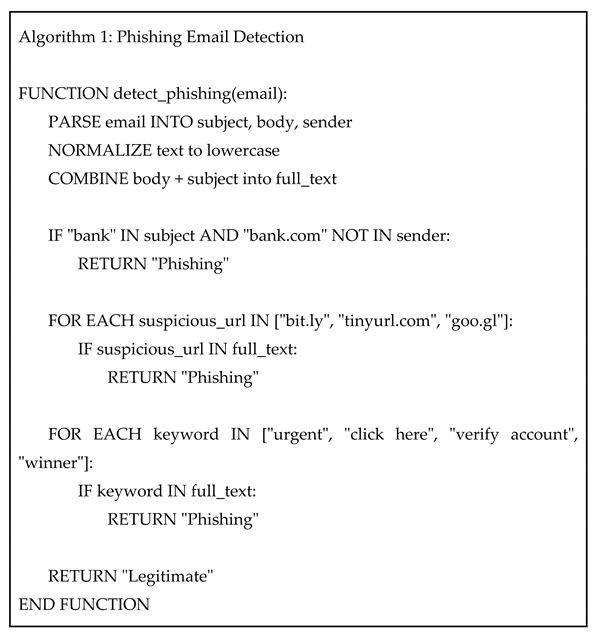
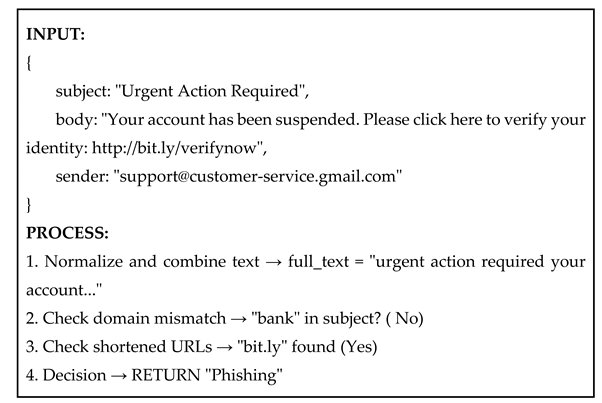
IV. Implementation of a Rule-Based AI Agent (Instructional Example)
V. Discussion
VI. Conclusion
References
- J. Smith and R. Patel, “Rule-Based Detection of Email Phishing,” Journal of Cybersecurity, vol. 12, no. 3, pp. 45-58, 2020.
- H. Lee and S. Kim, “Hybrid Approaches for Phishing Detection Using NLP and Heuristics,” in Proc. Int. Conf. Cybersecurity and AI, Cham, Switzerland, 2021, pp. 112-125.
- M. Johnson, “Artificial Intelligence in Email Security: A Comparative Study,” ACM Comput. Surv., vol. 52, no. 4, pp. 1-35, 2019.
- R. Gupta, G. R. Gupta, G. Somani, and M. S. Gaur, “PhishStorm: Detecting Phishing With Streaming Analytics,” in Proc. ACM Int. Conf. Advances in Computing, New York, NY, USA, 2012, pp. 1-7.
- K. Anderson, Understanding Phishing Techniques: A Guide for Beginners. Berlin, Germany: Springer, 2018.
- Cybersecurity Research Group. (2023). [Online]. Available: https://www.cybersec-research.org/phishing-stats-2023. ,: [Accessed, 10 May 2024.
- Alseadoon, N. B. Anuar, R. Razib, and A. Gani, “Phishing Email Detection Based Filtering Techniques: A Survey,” Int. J. Adv. Comput. Sci. Appl., vol. 8, no. 6, pp. 379-388, 2017.
- D. Wilson, “User Awareness and Its Impact on Phishing Susceptibility,” IEEE Trans. Inf. Forensics Secur., vol. 16, pp. 1234-1245, 2021.
- E. Martin, “Transparency in AI Systems: Why It Matters,” AI Ethics J., vol. 2, no. 1, pp. 45-60, 2020.
- F. Roberts, “Explainable AI for Cybersecurity Applications,” IEEE Access, vol. 8, pp. 123456-123467, 2020.
- G. Foster, “Rule-Based vs. ML-Based Email Filtering: A Comparative Study,” Comput. Secur., vol. 99, p. 102012, 2020.
- Ahmed, “Machine Learning for Phishing Detection: Challenges and Opportunities,” Knowl.-Based Syst., vol. 193, p. 105421, 2020.
- J. Lin, “Rule-Based Systems in Threat Detection: A Review,” Eng. Appl. Artif. Intell., vol. 92, p. 103645, 2020.
- K. Tanaka, “Natural Language Processing for Email Analysis,” Inf. Process. Manage., vol. 57, no. 6, p. 102034, 2020.
- L. Zhang, “Behavioral Factors in Phishing Attacks,” J. Inf. Secur. Educ., vol. 15, no. 1, pp. 22-35, 2020.
- M. Okafor, “Challenges in Real-Time Phishing Detection,” IEEE Trans. Dependable Secure Comput., vol. 18, no. 3, pp. 111-123, 2021.
- P. Sharma and H. Gupta, “Rule-Based Detection of Email Phishing,” Int. J. Comput. Appl., vol. 120, no. 10, pp. 1-6, 2015.
- S. Ali, “Human Behavior and Phishing Vulnerability,” Hum. Factors Cybersecurity, vol. 2, no. 1, pp. 45-58, 2021.
- U. Roy, “Automated Rule Updating in Phishing Detection Systems,” IEEE Trans. Inf. Forensics Secur., vol. 17, pp. 2345-2356, 2022.
- Y. Zhao, “Hybrid Frameworks for Phishing Detection: Combining Rules and ML,” Neural Comput. Appl., vol. 34, no. 10, pp. 7891-7903, 2022.
- Kumar and, T. Singh, “A Rule-Based Phishing Detection System Using Machine Learning Approach,” in Proc. IEEE Conf. Cybersecurity, pp. 45-50, 2020.
- Li and, W. Chen, “Phishing Detection Using Rule-Based and Signature Matching Methods,” Int. J. Digit. Crime Forensics, vol. 13, no. 2, pp. 45-60, 2021.
- R. Deshmukh and S. Shah, “Email Phishing Detection Using Feature Extraction and Rule Matching,” J. Netw. Comput. Appl., vol. 178, p. 102891, 2021.
- Z. Khan, “Social Engineering Tactics in Modern Phishing Attacks,” IEEE Security & Privacy, vol. 19, no. 4, pp. 55-62, 2021.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



