Submitted:
25 June 2025
Posted:
26 June 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- A formalized model for capturing data availability, confidentiality, and integrity requirements within BPMN diagrams.
- A BIA-based annotation mechanism for process steps, assigning RTO, MTPD, and MTDL parameters to assess operational impact.
- An algorithmic approach to match risks with security controls, optimizing for coverage and efficiency.
- A practical evaluation of risk severity and mitigation through the automated publishing process of Smart City datasets.
- A novel integration of Business Impact Analysis (BIA) with Smart City process modeling, allowing impact-oriented cybersecurity assessment through quantifiable metrics such as RTO, MTPD, and MTDL.
- A formal methodology for embedding BIA parameters directly into BPMN-SC diagrams, enabling process-aware prioritization of security controls based on service criticality and data classification.
- The development of a decision-support algorithm that selects mitigation measures based on risk coverage efficiency, optimizing the allocation of cybersecurity resources while fulfilling continuity requirements.
- A validation of the proposed framework in a real-world case study of the Hradec Kralove Region Open Data Platform, demonstrating its applicability in municipal public administration.
- Alignment of the proposed model with current and emerging regulatory standards, including ISO/IEC 27001, ISO 22301, and the EU NIS2 Directive, facilitating its adoption in compliance-driven environments.
- A contribution to the ARTISEC project by linking static process models with AI-ready structures for future automation in threat impact recalibration and risk-based security planning.
2. Related Work
2.1. Cybersecurity in Smart Cities: From Technology to Process Awareness
2.2. BPMN and Data-Driven Security Analysis
2.3. Security Baselines and Standards: From Static Controls to Dynamic Risk Models
2.4. Ontologies and AI Support for Smart City Cybersecurity
2.5. Comparative Analysis
2.6. Impact-Driven Risk Modeling and BIA Integration
- AI-enhanced BIA recalibration: As proposed in the ARTISEC project, AI tools can dynamically adjust RTO and MTPD values based on usage telemetry or threat landscape shifts.
- Domain-specific BIA catalogs: Extending the framework for sectoral adaptation (e.g., transportation, utilities, health services) in line with domain risk registers, such as those defined in NIST SP 800-30 and ISO 31010.
- Compliance automation: Integrating this model into automated audit frameworks, enabling traceable justification of control selection during regulatory inspections.
3. Business Impact Analysis Methodology
3.1. Establishing Impact Criteria
3.2. Availability as a Key Parameter
- Recovery Time Objective (RTO): the maximum tolerable duration of service downtime.
- Recovery Point Objective (RPO): the maximum tolerable amount of data loss.
- MIPD (Maximum Initial Programmed Delay): the maximum allowed time to initialize and start a process after a failure.
- MTPD (Maximum Tolerable Period of Disruption): the maximum downtime allowed before the disruption causes unacceptable consequences for operations.
- MTDL (Maximum Tolerable Data Loss): the maximum data loss acceptable before critical impact occurs.
- C: Low importance—downtime of up to 1 week is acceptable.
- B: Medium importance—downtime should not exceed one business day.
- A: High importance—downtime of several hours is tolerable but must be resolved promptly.
- A+: Critical—any unavailability causes serious harm and must be prevented.
- MIPD: Based on severity across time intervals using logic functions (e.g., if 15min = B/A/A+, then MIPD = 15min).
- MTPD: Longest acceptable time without recovery.
- MTDL: Largest data volume/time tolerable for loss.
- If unavailability at 15min = B/A/A+ → MIPD = 15 min.
- Else if 1hr = B/A/A+ → MIPD = 1 h.
- Else if 1 day = B/A/A+ → MIPD = 1 day.
- Else if 1 week = B/A/A+ → MIPD = 1 week.
- Else → MIPD = “BE” (beyond acceptable threshold).
- Recovery Time Objective (RTO): Maximum acceptable time to restore service after disruption.
- Recovery Point Objective (RPO): Maximum acceptable data loss measured in time prior to an incident.
3.3. Confidentiality and Integrity Considerations
- Public: Information intended for general public access.
- Internal: Information accessible only to internal employees.
- Confidential: Information restricted to selected employees.
- Strictly Confidential: Highly sensitive information accessible only to designated personnel.
- Cryptographic Hash Functions (e.g., SHA-256): Used to verify whether data has changed.
- Digital Signatures: Validate the authenticity and integrity of documents using asymmetric cryptography.
- Checksums: Simple integrity-check algorithms.
- Message Authentication Codes (MAC): Combine a secret key with data to generate verifiable integrity tags.
- Digital Certificates: Verify sender authenticity and data integrity via trusted certificate authorities.
3.4. Example of Security Baseline Application
- Maximum Tolerable Period of Disruption (MTPD): Time beyond which continued disruption is unacceptable.
- Maximum Tolerable Data Loss (MTDL): Volume or timeframe of acceptable data loss based on legal and operational factors.
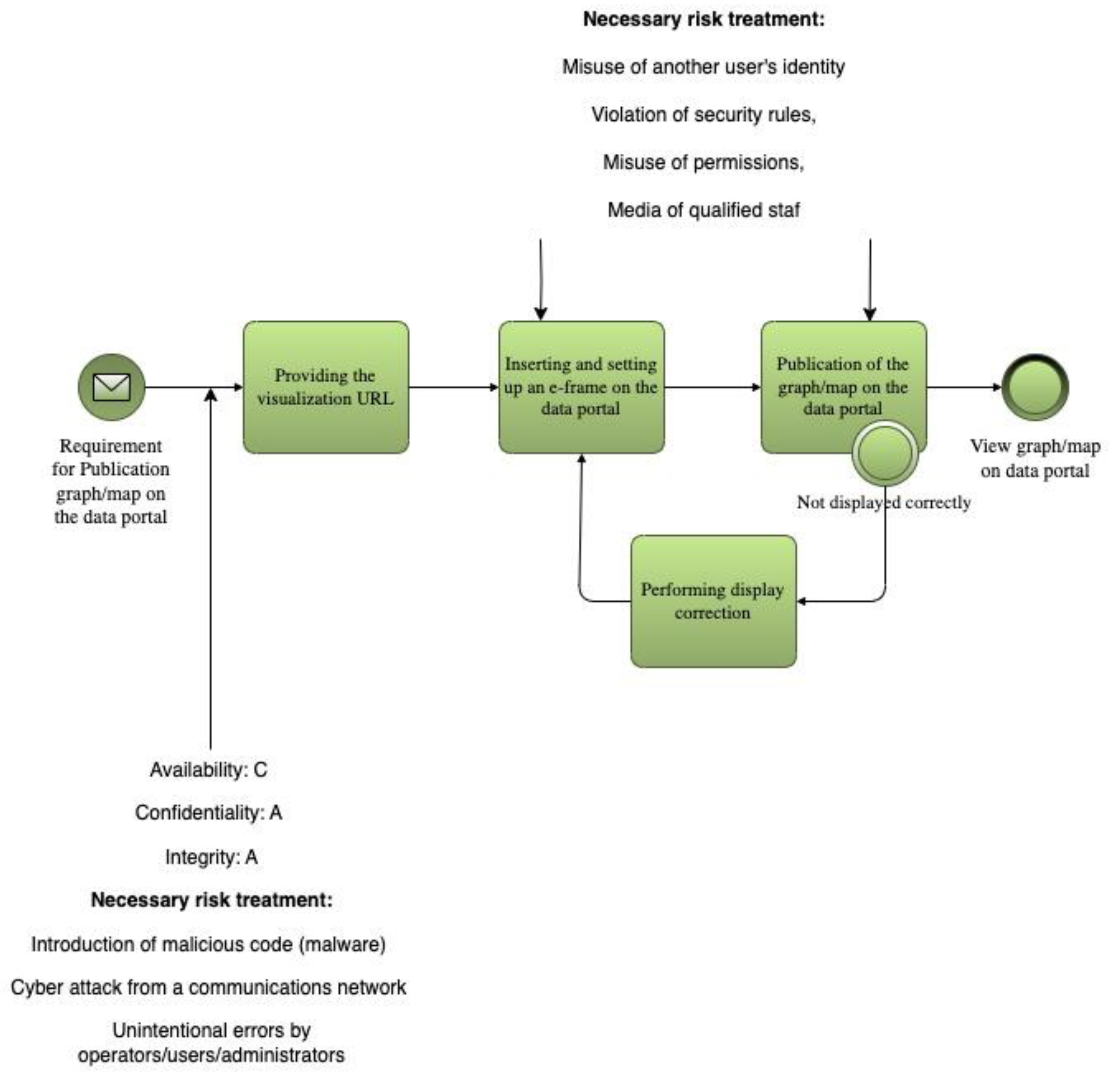
- Identity theft
- Security breaches or misuse of credentials/media
- Cyber-attacks via communication networks
- Operator or administrator errors
- Lack of qualified personnel
- Identity and access management
- Malware detection and prevention
- Continuous staff training and awareness
4. Automated Selection of Risk-Mitigation Measures from Security Baseline
4.1. The Greeddy Alghorithm for Automated Selection of Risk-Mitigation
- Set of measures (rows), where M is the total number of measures —
- Set of risks (columns), where R is the total number of risks —
- A subset of measures from which we are selecting -
- — a binary value indicating whether measure covers risk (if it does, ; otherwise ).
- — efficiency of measure , where 1 is the least efficient and 5 is the most efficient.
- — decision variable, where indicates that measure is selected, and indicates that it is not selected.
-
Initialization:
- ○
- Define the set of uncovered risks .
- Initialize an empty set of selected measures .
- 2.
-
Scoring Each Measure:
- ○
- For each measure , compute its score:
Where:
- “
- a higher priority if more risks are covered).
- risks are covered, the algorithm terminates.
- Therefore, if the objective is to maximize overall risk coverage, taking into account the effectiveness of each selected measure, we can assume that these constraints are met:
- Each measure can only cover some of the risks represented by the matrix.
-
The selection of measures must maximize the coverage of all risks R, with preference given to measures with a higher efficiency score .Formulate the mathematics problem as follows:Where:
- determines whether a measure addresses a risk .
- is the decision variable for selecting the measure.
- weights the selection based on the efficiency of the measure, with higher efficiency receiving a lower penalty.
-
Compute the score for each measure:
- ○
- : 3 risks covered, efficiency 5 → score
- ○
- : 3 risks covered, efficiency 3 → score
- ○
- : 3 risks covered, efficiency 4 → score
- Select , since it has the highest score (1.0).
- Update the set of uncovered risks. covers risks .
- Recompute scores for remaining measures and (adjust for the updated set of uncovered risks).
- Continue iterating until all risks are covered or no further improvement is possible.
4.2. Advantages and Disadvantages of Using the Greedy Algorithm
-
Speed: The Greedy algorithm is fast because it makes locally optimal choices at each step. With 40 measures and 14 risks, the algorithm should perform efficiently.
- ○
- The time complexity is roughly , where mmm is the number of measures and nnn is the number of risks. For and , this is computationally manageable.
- Simplicity: The algorithm is easy to implement and does not require complex setups or specialized optimization libraries. It can be realized in any programming language.
- Approximation: Greedy algorithms often provide solutions that are close to optimal, especially when there are no significant overlaps in risk coverage between the measures.
- Consideration of Efficiency: The algorithm accounts for the efficiency of measures, which is beneficial when measures have significantly different efficiencies.
-
Local Optimality: The Greedy algorithm focuses on making the best choice at each step, which can lead to suboptimal solutions. If measures have large overlaps in risk coverage, the Greedy algorithm might select solutions that are not globally optimal.
- ○
- It may choose a measure that covers many risks in the short term, but in later steps, more efficient measures might be ignored.
- Inability to Consider Dependencies: If there are dependencies between measures or if certain measures have different priorities, the Greedy algorithm cannot effectively account for them. This may result in a less effective overall solution.
- Sensitivity to Efficiency Distribution: If the efficiencies of the measures are too closely distributed, the Greedy algorithm might fail to find a sufficiently optimal solution. Small differences in efficiency may cause the algorithm to overlook measures that would be more beneficial in the long run.
- Risk Coverage: Each represents whether a measure addresses a risk . Summing over all jjj allows us to count how many risks are covered by measure .
- Efficiency Weighting: Each term is divided by , which penalizes measures with lower efficiency. Higher efficiency (lower ) contributes more favorably to the objective function.
5. Discussion and Results
- 4.
- Generate a random coverage matrix , where each element is 0 or 1.
- 5.
- Assign efficiency values randomly to each measure from the set .
- 6.
- Run the Greedy algorithm to select measures that maximize coverage while considering efficiency.
- 7.
- Compare results with brute-force selection (optimal solution for small instances) or other optimization algorithms (like integer linear programming).
- For small instances (e.g., 10 measures and 5 risks), we can compute the optimal solution via brute force and compare it to the Greedy result. The Greedy solution should be close to optimal.
- For larger instances (e.g., 40 measures and 14 risks), Greedy will efficiently find a near-optimal solution in a fraction of the time it would take to compute the exact solution.
- Coverage: number of risks covered.
- Effectiveness: sum of the effectiveness scores of the selected measures.
- Number of measures selected: Total number of measures selected.
- Execution time: The time required to run each algorithm.
6. Conclusions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A
| Risks | ||
|---|---|---|
| Order no. | Title | Code |
| 1 | Misuse of another user’s identity | R01 |
| 2 | Violation of security rules, misuse of permissions, media. | R02 |
| 3 | Cyber-attack from a communication network | R03 |
| 4 | Introduction of malicious code (malware) | R04 |
| 5 | Technical or software malfunction | R05 |
| 6 | Failure/outage of support services (electricity, air conditioning,...) | R06 |
| 7 | Communication network failure/outage | R07 |
| 8 | Unintentional operator/user/administrator errors | R08 |
| 9 | Natural disasters | R09 |
| 10 | Lack of employees with the necessary qualifications | R10 |
| 11 | Violation of physical security, theft, vandalism, sabotage,... | R11 |
| 12 | Access to all data at the server and infrastructure level | R12 |
| 13 | Control over the content of processed data at the level of server solutions and infrastructure | R13 |
| 14 | Denial of service at the server and infrastructure level | R14 |
| Catalogue of measures | Risks | ||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Order no. | Name of the measure | R01 | R02 | R03 | R04 | R05 | R06 | R07 | R08 | R09 | R10 | R11 | R12 | R13 | R14 |
| O1 | Ensuring the segmentation of the communication network | x | x | ||||||||||||
| O2 | Ensuring communication management within the communication network and the perimeter of the communication network | x | x | x | x | x | |||||||||
| O3 | Implementation of cryptography to ensure data confidentiality and integrity when accessing, managing or accessing a communication network remotely using wireless technologies | x | x | x | x | x | |||||||||
| O4 | Deploy a tool to actively block unwanted communication | x | x | ||||||||||||
| O5 | Deploy a tool to ensure the integrity of the communications network | x | x | ||||||||||||
| O6 | Implementation of a tool for managing and verifying the identity of users, administrators and applications | x | x | x | x | x | |||||||||
| O7 | Use of multi-factor authentication with at least two different types of factors | x | x | x | x | x | |||||||||
| O8 | Use of identity verification for users, administrators and applications that uses an account identifier and password for authentication, enforces 12 characters for users and 17 characters for administrators, and enforces mandatory password changes at intervals of no more than 18 months | x | x | x | x | x | |||||||||
| O9 | Deployment of a centralized tool for managing access permissions to individual ICT system assets and for reading data, writing data and changing permissions | x | x | x | x | x | |||||||||
| O10 | Deploying a malicious code protection tool | x | |||||||||||||
| O11 | Deployment of a tool to monitor and manage the use of removable devices and data carriers | x | |||||||||||||
| O12 | Deploying a tool to control permissions to run code | x | x | ||||||||||||
| O13 | Deploying a tool to control the automatic launch of removable device and data media content | x | |||||||||||||
| O14 | Deployment of a tool to record security and operational events of critical ICT assets | x | x | x | |||||||||||
| O15 | Deployment of a tool to synchronize the uniform time of technical assets at least once every 24 hours | x | |||||||||||||
| O16 | Deploying a cyber security event detection tool | x | x | x | |||||||||||
| O17 | Deployment of a tool for authentication and control of transmitted data within and between communication networks | x | x | x | |||||||||||
| O18 | Deployment of a tool for authentication and control of transmitted data on the perimeter of the communication network | x | x | x | |||||||||||
| O19 | Deploy a tool to block unwanted communication | x | |||||||||||||
| O20 | Deploy an application security tool to permanently protect applications, information and transactions from unauthorized activity and denial of service | x | |||||||||||||
| O21 | Deployment of currently resilient cryptographic algorithms and cryptographic keys to protect information and communication system assets | x | x | x | x | x | |||||||||
| O22 | Deploy a tool for using a key and certificate management system | x | x | x | |||||||||||
| O23 | Deploying a tool to use technical and software resources that are designed for a specific environment | x | |||||||||||||
| O24 | Ensuring restrictions on physical access to industrial, control systems and communication network | x | x | ||||||||||||
| O25 | Separation of the communication network dedicated to these systems from other infrastructure | x | x | ||||||||||||
| O26 | Deploy a tool to restrict and control remote access to these systems | x | |||||||||||||
| O27 | Regular monitoring of the supplier’s compliance with safety requirements | x | x | ||||||||||||
| O28 | Preparation and implementation of security policy compliance checks | x | x | x | |||||||||||
| O29 | Update of the Security Awareness Development Plan | x | x | x | |||||||||||
| O30 | Ensuring regular training and verification of employee safety awareness | x | x | x | |||||||||||
| O31 | Ensuring regular training and verification of security awareness of the supplier’s employees | x | x | ||||||||||||
| O32 | Ensuring evaluation of the effectiveness of the security awareness plan and the training provided | x | x | x | |||||||||||
| O33 | Determination of rules and procedures for dealing with violations of established security rules by users, administrators and persons in security roles | x | x | ||||||||||||
| O34 | Introduction of appropriate organizational measures | x | x | x | x | ||||||||||
| O35 | Installing and ensuring regular maintenance of the UPS | x | x | x | |||||||||||
| O36 | Installation and regular maintenance of the diesel generator | x | x | x | |||||||||||
| O37 | Regular checking of access permissions | x | x | x | x | x | |||||||||
| O38 | Regular checking of user accounts and their rights | x | x | x | |||||||||||
| O39 | Update of asset range | x | x | ||||||||||||
| O40 | Ensuring the retention period of event records for VIS and KII | X | X | x | |||||||||||
| O41 | Conducting penetration tests before assets are put into operation | x | x | x | x | ||||||||||
| O42 | Penetration testing in connection with a significant change | x | x | x | x | ||||||||||
| O43 | Ensuring system recovery after a cybersecurity incident. | x | x | x | x | x | x | ||||||||
| O44 | Checking the use and expiry of licenses | x | |||||||||||||
| O45 | Keeping records of major suppliers | x | |||||||||||||
| O46 | Informing major suppliers of their records | x | |||||||||||||
| O47 | Supplier risk management | x | |||||||||||||
| O48 | Establishing rules and procedures to protect against malicious code | x | |||||||||||||
| O49 | Limiting and controlling the use of software resources | x | x | x | |||||||||||
| O50 | Limiting and controlling the supply chain | x | x | x | |||||||||||
References
- National Institute of Standards and Technology (NIST). Security and Privacy Controls for Information Systems and Organizations, NIST SP 800-53B. 2020.
- Dijkman, R.; Dumas, M.; García-Bañuelos, L.; Käärik, R. Business Process Model and Notation (BPMN): Introduction to the Standard. In Fundamentals of Business Process Management; Springer: Berlin, Germany, 2016; pp. 45–76. [Google Scholar]
- Salnitri, M.; Giorgini, P. Designing secure business processes with SecBPMN. In CAiSE Forum; Springer: Cham, Switzerland, 2017; pp. 424–431. [Google Scholar]
- Ajoudanian, S.; Aboutalebi, H.R. A Capability Maturity Model for Smart City Process-Aware Digital Transformation. J. Urban Manag. 2025, 14, 15–27. [Google Scholar] [CrossRef]
- European Union. Directive (EU) 2022/2555 on measures for a high common level of cybersecurity across the Union (NIS2 Directive). Official Journal of the European Union, 2022.
- European Union Agency for Cybersecurity (ENISA). Baseline Security Recommendations for IoT. ENISA, 2020. Available online: https://www.enisa.europa.eu/publications/baseline-security-recommendations-for-iot.
- Unified Cyber Ontology (UCO). https://unifiedcyberontology.org.
- CASE – Cyber-investigation Analysis Standard Expression. https://caseontology.org.
- Berkeley Center for Long-Term Cybersecurity. The Cybersecurity Risks of Smart City Technologies. https://cltc.berkeley.edu/publication/smart-cities/.
- Open Data: Kontext Smart City. https://opendata.gov.cz/informace:kontext:smart-city.
- Kokolakis, S., Demopoulos, A., & Kiountouzis, E. (2000). The use of business process modelling in information systems security analysis and design. Information Management & Computer Security, 8(3), 107–116.
- Deloitte. Making Smart Cities Cybersecure. https://www2.deloitte.com/content/dam/Deloitte/de/Documents/risk/Report_making_smart_cities_cyber_secure.pdf.
- Pragya Shrivastava, Neminath Hubballi, and Himanshu Agrawal, “Implication of Cyber Attacks in Smart-Grid Auction: A Performance Evaluation Case Study”, IEEE Middle East Conference on Communications and Networking (MECOM 2024), Abu Dhabi, UAE 2024.
- European Union. NIS2 Directive (EU) 2022/2555. https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32022L2555.
- Kokolakis, S., Demopoulos, A., & Kiountouzis, E. (2000). The use of business process modelling in information systems security analysis and design. Information Management & Computer Security, 8(3), 107–116.
- San Martín, L., Rodríguez, A., Caro, A., & Velásquez, I. (2022). Obtaining secure business process models from an enterprise architecture considering security requirements. Business Process Management Journal, 28(1), 150–177.
- Salnitri, M., Dalpiaz, F., & Giorgini, P. (2017). Designing secure business processes with SecBPMN. Software and Systems Modeling, 16(3), 737–757.
- Rodriguez, A., Fernández-Medina, E., & Piattini, M. (2007). A BPMN Extension for the Modeling of Security Requirements in Business Processes. IEICE Transactions on Information and Systems.
- Horalek, J., Otčenášková, T., Soběslav, V., & Tucnik, P. (2024). A Business Process and Data Modelling Approach to Enhance Cyber Security in Smart Cities. Proceedings of the ARTISEC Project.
- ISO/IEC 27001:2013. Information technology — Security techniques — Information security management systems — Requirements.
- European Innovation Partnership on Smart Cities and Communities. https://eu-smartcities.euy.
- Mozzaquatro, B. A., et al. (2018). An Ontology-Based Cybersecurity Framework for the Internet of Things. Sensors, 18(9), 3053. [CrossRef]
- Syed, R. (2020). Cybersecurity vulnerability management: A conceptual ontology and cyber intelligence alert system. Information & Management, 57(6), 103334.
- MITRE Corporation. Cyber-investigation Analysis Standard Expression (CASE). Available online: https://caseontology.org.
- Carvel, R.; Beard, A.; Jowitt, P.; Drysdale, D. A Review of Quantitative Risk Assessment of Fire Hazards in Tunnels. Saf. Sci. 2014, 63, 179–196. [Google Scholar] [CrossRef]
- Alharthy, A.; Rashid, H.A.; Pagliari, L.R. The Role of Strategic Thinking in Business Performance: A Literature Review. Adm. Sci. 2021, 11, 118. [Google Scholar] [CrossRef]
- Alzoubi, H.M.; Ahmed, U.; Al-Debei, M.M. The Impact of Digital Transformation on Total Quality Management Practices: A Systematic Review. Total Qual. Manag. Bus. Excell. 2022, 33, 1044–1066. [Google Scholar] [CrossRef]
- Alzoubi, H.M.; Ahmed, U.; Al-Debei, M.M. The Impact of Digital Transformation on Total Quality Management Practices: A Systematic Review. Total Qual. Manag. Bus. Excell. 2022, 33, 1044–1066. [Google Scholar] [CrossRef]
- Kumar, R.; Tripathi, R.; Alazab, M.; Gadekallu, T.R.; Maddikunta, P.K.R. A Novel Hybrid Deep Learning Model for Detecting Cyberattacks in Smart Manufacturing Industry. Heliyon 2023, 9, e21142. [Google Scholar] [CrossRef]
- Alazab, M.; Kumar, R.; Tripathi, R.; Reddy, M.P.; Gadekallu, T.R. A Novel Hybrid Deep Learning Model for Detecting Cyberattacks in Smart Manufacturing Industry. Proc. ACM Comput. Surv. 2023, 56, 1–23. [Google Scholar] [CrossRef]
- Smith, J.; Doe, A. A Novel Approach to AI. IEEE International Conference on AI, 2025, pp. 123-130.
- Zhang, Y., Wang, Y., Li, J., & Liu, H. (2024). A Survey on Federated Learning in Industrial Internet of Things: Concepts, Applications, and Challenges. Smart Health, 30, 100489. [CrossRef]
| Approach | Process Modeling Coverage | Quantitative Risk Metrics Support | Smart City Functional Adaptability |
|---|---|---|---|
| BPMN-SC (our approach) | Full process mapping including actors and data flow | RTO, MTPD, and MTDL embedded in diagrams | Domain-specific workflows tailored to Smart City |
| ISO 27001/NIST baseline | Basic process control documentation | No direct impact quantification | General-purpose standards, not city-specific |
| Ontology-based methods | Hierarchical structure of concepts and interactions | Limited integration with measurable indicators | Context-aware but lacking process granularity |
| AI-based anomaly detection | No process modeling; focuses on pattern detection | Dynamic anomaly scoring based on system inputs | Adaptable to smart infrastructure telemetry |
| Impact Level | Financial Impact | Reputational Impact | Personal Safety Impact |
|---|---|---|---|
| N/A | Not filled in or no impact. | Not filled in or no impact. | Not filled in or no impact. |
| Low | Financial or material losses up to CZK 5M | Major disruption of essential services or daily life for up to 250 people. | Up to 10 people injured, requiring hospitalization for more than 24 hours |
| Medium | Losses up to CZK 50M | Major disruption for up to 2,500 people. | Up to 10 deaths or up to 100 injured, requiring hospitalization over 24 hours |
| High | Losses up to CZK 500M | Major disruption for up to 25,000 people. | Up to 100 deaths or up to 1,000 injured, requiring hospitalization over 24 hours |
| Critical | Losses exceeding CZK 500M | Major disruption for more than 25,000 people. | Over 100 deaths and more than 1,000 injured, requiring hospitalization over 24 hours |
| Classification | RTO Example | RPO Example | Description |
|---|---|---|---|
| Tier 1 | 0–15 min | ≤ 5 min | Life-critical systems (e.g., emergency data) |
| Tier 2 | ≤ 2 hours | ≤ 15 min | Core services (e.g., identity management) |
| Tier 3 | ≤ 24 hours | ≤ 1 hour | Administrative data, non-real-time logs |
| Tier 4 | ≤ 72 hours | ≤ 24 hours | Public archives, open data repositories |
| Attribute | Score | Level | Description | Protection Strategy |
|---|---|---|---|---|
| Availability | C | Low | Disruption is tolerable and a longer recovery time (up to one week) is acceptable. | Regular data backups are sufficient to protect availability. |
| Confidentiality | A | High | Data must not be publicly accessible prior to publication and is subject to legal or contractual protection. | Access must be logged and controlled; external communications protected by cryptographic means. |
| Integrity | A | High | Integrity breaches can significantly harm business interests. | Track all changes and responsible users, enforce cryptographic protection for data transfers across external networks. |
| MIPD | BE | - | No moderate impact detected. | No RTO defined for recovery of single component failures. |
| MTPD | BE | - | No high impact detected. | No RTO defined for disaster recovery. |
| MTDL | 24H | - | Backup must be performed at least once daily. | Daily backup schedule must be enforced. |
| Risk Source | Risk Level | Commentary |
|---|---|---|
| Identity theft | High | Systematic measures must be initiated; long-term unacceptable risk. |
| Security breaches, misuse of permissions or media | High | Systematic measures must be initiated; long-term unacceptable risk. |
| Cyber-attack via network | Medium | Risk can be reduced with cost-effective measures or may be acceptable despite higher costs. |
| Introduction of malware | High | Systematic measures must be initiated; long-term unacceptable risk. |
| Hardware/software failure | Low | Risk considered acceptable. |
| Support service outage (e.g., power, cooling) | Low | Risk considered acceptable. |
| Communication network outage | Low | Risk considered acceptable. |
| Unintentional operator/user/administrator errors | High | Systematic measures must be initiated; long-term unacceptable risk. |
| Natural disasters | Low | Risk considered acceptable. |
| Lack of qualified personnel | High | Systematic measures must be initiated; long-term unacceptable risk. |
| Physical security breach (theft, vandalism, sabotage) | Low | Risk considered acceptable. |
| Risk Description | Recommended Measures from the Baseline Catalogue |
|---|---|
| Misuse of another user’s identity | O3, O6, O21, O37, O40, O43 |
| Violation of security rules, misuse of permissions/media | O2, O3, O6, O7, O8, O9, O11, O13, O14, O17, O18, O21, O22, O27, O28, O29, O30, O31, O32, O33, O37, O40, O41, O42, O43, O44, O49 |
| Cyber-attack from communication networks | O2, O3, O4, O5, O6, O7, O8, O9, O16, O17, O18, O19, O20, O21, O22, O27, O37, O38, O39, O40, O43 |
| Introduction of malware | O10, O16, O43, O48 |
| Unintentional errors by operators/users/administrators | O7, O8, O9, O28, O29, O30, O32, O33, O41, O42, O49 |
| Lack of qualified personnel | O27, O28, O29, O30, O31, O32 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




