Submitted:
15 June 2025
Posted:
17 June 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
A. Limitations of Traditional Security Auditing
B. Evolution Towards Intelligent Automation
C. Focus on Key Vulnerabilities and Bug Bounties
D. Survey Scope and Purpose
II. Literature Review: Advances and Drawbacks
A. Hybrid and Automated Scanning Techniques
B. AI/ML in Vulnerability Detection and Cybersecurity
C. Large Language Models (LLMs) in Penetration Testing
D. Bug Bounty Programs and IoT Security
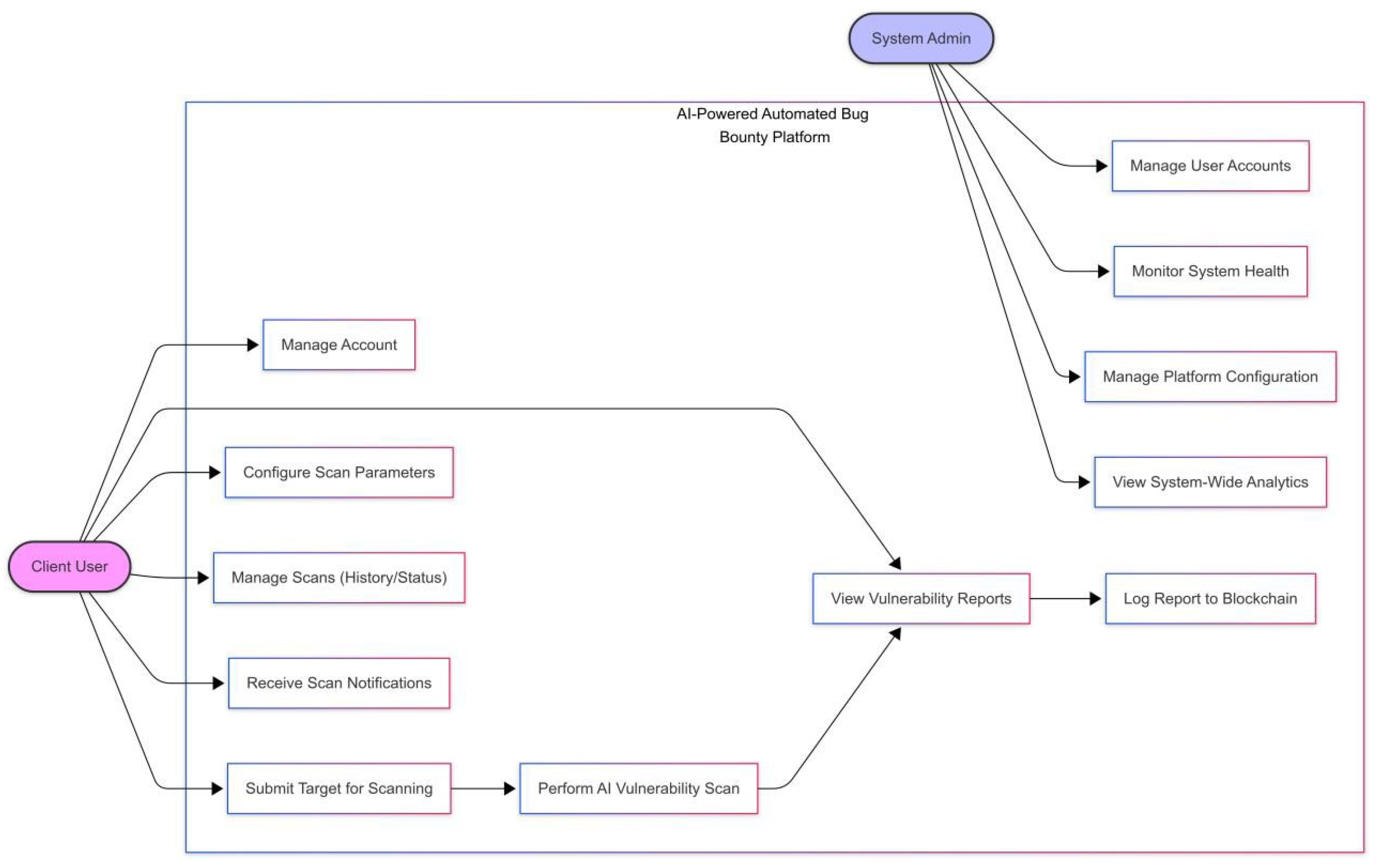
III. Proposed System
IV. Comparative Analysis of Surveyed Approaches
V. Synthesis and Motivation for Future Directions
A. Key Advancements Observed
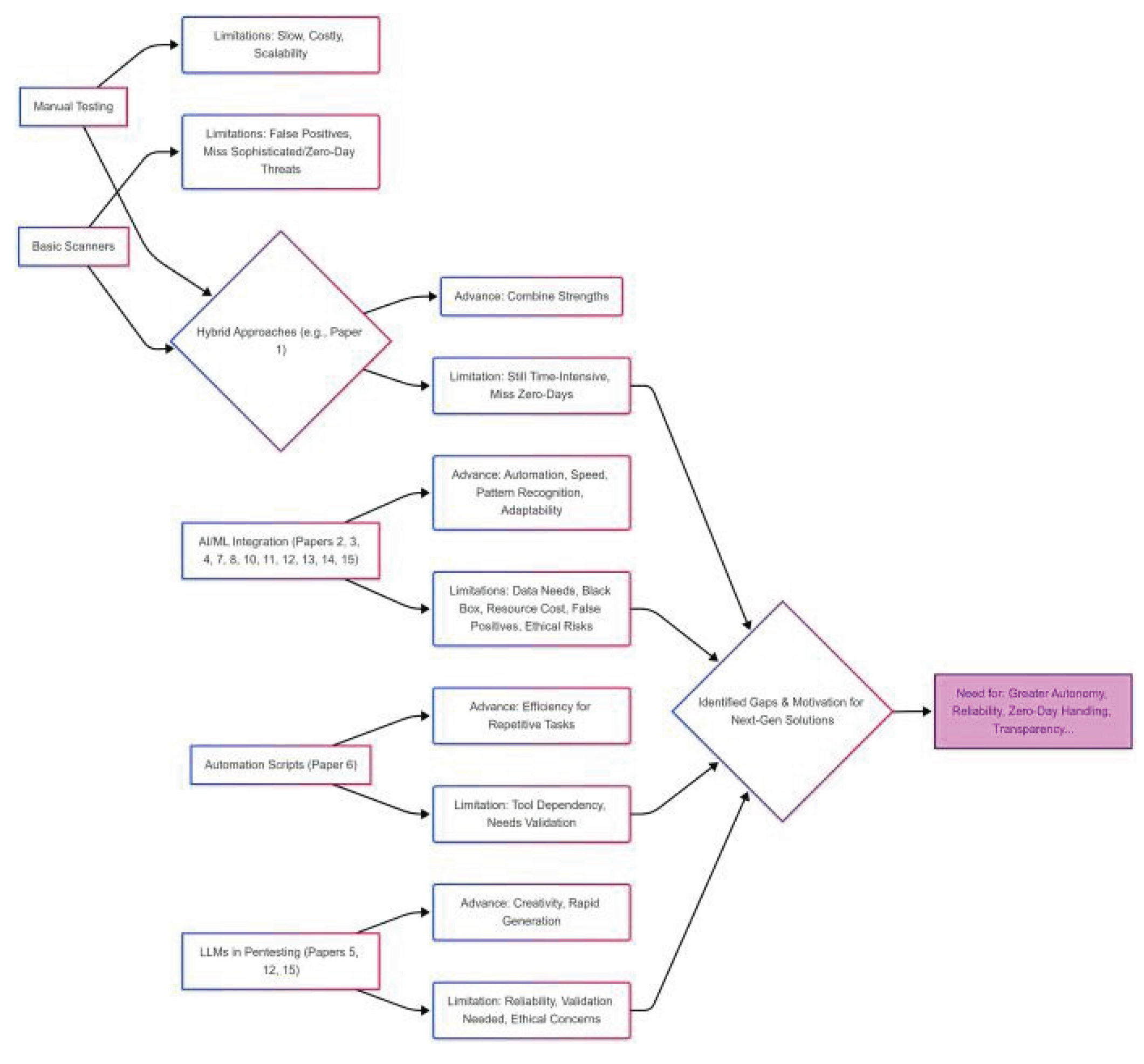
B. Persistent Limitations and Challenges
| Ref | Primary Focus | Technique(s) Used | Target Area | Key Advance(s) | Key Limitation(s) |
|---|---|---|---|---|---|
| 1 | Hybrid Testing | OWASP ZAP + Manual | Web App S | Covers common flaws | Time-intensive, No zero-days (Summary) |
| 2 | AI in Security (Survey) | Anomaly Det., Pred. Analytics |
General Cybersecurity | Real-time, Adaptability |
Data needs, Black-box, Ethics |
| 3 4 |
SQLI Detection | SVM, RF, LSTM, Anomaly Det. |
Web App S (SQLi) C/C++ Source Code |
High accuracy (95%+), Adapts |
Data needs, False Positives (Unsup.), Resources (LSTM) |
| Code Vuln. (C/C++) | ML (LGBM) + DL (CodeBERT Multi-Task) |
DL high accuracy (8-22% MCC improvement), ML efficient |
Labeled data needed, Resources (DL) |
||
| 5 | LLM Pentesting | ChatGPT 3.5 + CLI Tools | Pentest Automation | Efficiency, Creativity (Assistive, 95% valid) |
Needs validation, Ethics, Reliability |
| 6 | Recon Automation | Bash Script + OSINT Tools | Bug Bounty Recon | Time saving (70%), Coverage (92% subs) |
Tool dependency, False positives, Ethics |
| 7 | Defect Prediction | MLP Neural Network | Cloud Bug Tracking | Automation (78.21% acc.), Handle imbalance |
Dataset bias, Complexity, Resources, Interpretability |
| 8 | ML/DL Vuln. Det. (Survey) |
Survey (RNN, GNN, etc.) | Source Code / Repos |
DL > ML, LSTM/GGNN top performers |
Excludes Web/Android, Filter bias risk |
| 9 | Bug Bounty Analysis | Literature, Case Studies |
Bug Bounty Programs | Proactive, Cost-effective |
Needs more automation, clearer ethics |
| 10 | ML for IoT Sec. (Survey) |
Survey (ML/DL) | IoT Vulnerabilities | Handle IoT diversity | Needs more research, Maturity low |
|
11 |
DL Library Bugs | Technique(s) Used | TF/PyTorch Code | High recall detection (94.51%) | Low patch accuracy (10 correct out of 90 generated), Generalization |
| 12 | LLM Pentest Benchmarking |
LLMS (GPT-4o, Llama 3.1) + PentestGPT |
Pentest Automation | Benchmark creation, Insights (Llama edge) |
LLMs fail end-to-end autonomy |
| 13 | AI for Cybersec (Survey) |
SLR + NIST Framework | General Cybersecurity | Comprehensive overview (NIST) |
Pre-Feb 2022 scope |
| 14 | SQLI Detection (DL) | TextCNN, LSTM, Attention, BERT |
Web App S (SQLi) | Aims for high accuracy/low FP/FN |
Overfitting risk, Feature quality, Data scarcity |
| 15 | Python Vuln. Det. | BILSTM + ChatGPT (SafePyScript) |
Python Source Code | Accessible tool, LLM suggestions |
Focus on tool; model limits less explored |
C. Impact of Identified Limitations
D. Specific Future Research Avenues
- Hybrid AI-Human Systems: Research into optimally combining AI strengths (speed, pattern matching) with human expertise (contextual understanding, complex reasoning), moving beyond simple validation towards collaborative analysis.
- Explainable AI (XAI) for Security Contexts: Developing and applying XAI techniques (e.g., SHAP, LIME) specifically for vulnerability detection models to overcome the ’black-box’ problem, build trust, and aid debugging.
- Adversarial Robustness: Investigating the susceptibility of AI-based detection models to adversarial manipulation and developing defenses.
- Data Augmentation and Efficient Learning: Exploring few-shot learning, transfer learning, or semi-supervised methods to reduce the dependency on large labeled datasets. Techniques for learning effectively from imbalanced security datasets also need refinement.
- Lightweight and Efficient AI Models: Researching more computationally efficient model architectures (e.g., model pruning, quantization) suitable for resourceconstrained environments (relevant for IoT) or high-speed scenarios.
- Context-Aware Zero-Day Detection: Improving unsupervised and anomaly detection methods to reduce false positives while maintaining sensitivity to novel threats by incorporating richer context.
- Blockchain for Verifiable Reporting: Investigating the application of blockchain or other distributed ledger technologies to create secure, immutable, timestamped, and potentially access-controlled records of vulnerability discovery, reporting, and remediation processes. This could enhance transparency and trust in automated platforms and bug bounty ecosystems by providing a verifiable audit trail, addressing gaps highlighted by and trust issues in. Research is needed on suitable consensus mechanisms, data privacy considerations, and integration with scanning tools.
E. Concluding Synthesis
VI. Conclusion
References
- S. B. Swetha, V. M. Sridhar, and G. S. Kavya, ”Web application security assessment using OWASP ZAP and BWAPP,” Materials Today: Proceedings, vol. 80, pp. 1922-1927, 2023.
- P. S. Rao, N. M. Babu, and T. V. Ramana, ”Artificial Intelligence in Cybersecurity: A Survey,” Materials Today: Proceedings, vol. 80, pp. 1983-1987, 2023.
- M. C. Danilla, R. Ravi, and N. Jeyakumar, ”SQL injection detection using supervised and unsupervised machine learning,” Materials Today: Proceedings, vol. 80, pp. 1787-1791, 2023.
- T. Nguyen, H. V. Pham, and T. T. Nguyen, ”Code-centric vulnerability assessment in C/C++ using ML and DL,” IEEE Access, vol. 10, pp. 123456-123470, 2022.
- E. Hilario, L. Al-Adhaileh, and M. A. Alzain, ”The Good, the Bad, and the Ugly of Generative AI in Penetration Testing,” in Proc. IEEE Int. Conf. Computing, 2024, pp. 88-94.
- K. Kaur, P. Singh, and M. Vashisht, ”Automated bug bounty reconnaissance using bash scripting,” International Journal of Computer Applications, vol. 182, no. 2, pp. 25-29, 2023.
- T. V. Hai, H. P. Linh, and N. Q. Hien, ”Cloud-based bug tracking and defect prediction using deep learning,” Journal of Computer Virology and Hacking Techniques, vol. 19, pp. 115-126, 2022.
- N. S. Harzevili, A. Ghaffarian, and M. H. Ghaffari, ”A survey on automated software vulnerability detection using ML/DL,” IEEE Access, vol. 10, pp. 64532-64552, 2022.
- S. Sharma and A. Rathi, ”A Study of Bug Bounty Programs: Challenges and Future Directions,” in Proc. Int. Conf. on Cyber Security, 2021, pp. 91-96.
- V. R. Anala, K. H. Ram, and R. Kumar, ”ML-Based Vulnerability Detection and Classification in IoT Device Security,” Materials Today: Proceedings, vol. 80, pp. 1800-1804, 2023.
- Y. T. Chen, Z. Lin, and H. Lin, ”Checker bug detection and repair in deep learning libraries,” ACM Trans. Software Engineering and Methodology, vol. 32, no. 2, pp. 15:1-15:27, 2023.
- F. Rezaei and M. Hadian, ”Towards Automated Penetration Testing: Introducing LLM Benchmark, Analysis and Improvements,” arXiv preprint arXiv:2401.00223, 2024.
- Wang and J. Zhang, ”Artificial intelligence for cybersecurity: Literature review and future research directions,” Computer Science Review, vol. 45, pp. 100491, 2022.
- Y. X. Wang, Z. Y. Li, and L. H. Liu, ”Deep learning-based detection technology for SQL injection: Research and implementation,” Computer Applications and Software, vol. 40, no. 7, pp. 53-60, 2023.
- K. Sharma, S. R. Mishra, and M. S. Khan, ”SafePyScript: A WebBased Solution for ML-Driven Vulnerability Detection in Python,” in Proc. Int. Conf. Intelligent Computing and Networking, 2023, pp. 205212.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




