Submitted:
19 May 2025
Posted:
20 May 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Methodology
- Subnetting to efficiently organize devices and bolster security
- VLANs to separate departmental traffic and safeguard sensitive data
- Planning for employee and visitor wireless networks, each with distinct SSIDs and WPA2 encryption
3. Physical Workspace
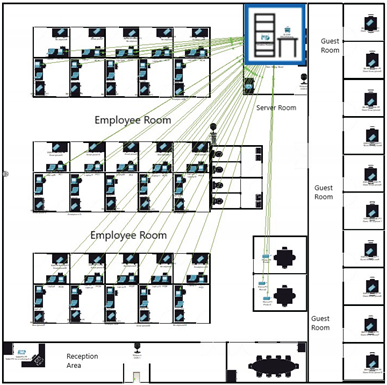
3.1. Build a Simple Network in the Logical Topology Workspace
| Explanation | Screenshot |
| The image shows multiple smartphones connected wirelessly to the network. These are the required 30 smartphones that the employees will be using. It is also worth noting that the connection is wired. |
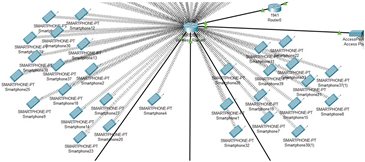 |
| The second image highlights the wireless connections for employee laptops. Each laptop is linked to the network, to make sure they are all connected and Ready to use. The connection is also wireless, so it is more convenient. |
 |
| This picture displays the wired connections of PCs and printers to switches. Each employee has a PC connected via Ethernet. Notice how This setup has a wired connection for reliability and a faster connection. Printers are also wired to the switch. |  |
| This occupied area is the guest room, where a maximum of 10 people can fit inside. The phone connections are all wireless. All the devices get their connection from access point directly connected to the wireless router. |
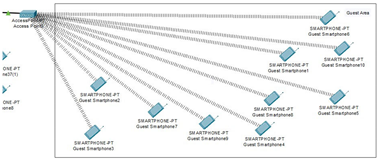 |
| For providing the wireless connection to 10 guest devices. access point is used, and inside the configuration of port 1 of the access point, the SSID is set as Guest and in authentication, WPA2-PSK is selected, which assigns login information for each device for them to connect to the network as an added security measure. | 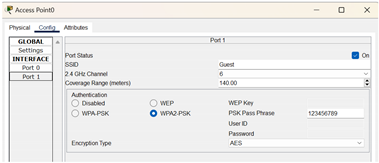 |
| The IoT devices section contains 3 webcams (one for the main door, one for employee space, and one for the server room), a smart door that can be opened and closed, and a tablet PC to monitor these devices. All the IoT devices are connected to a home gateway (renamed to OfficeGateway) while the gateway is connected to the wireless router via a copper straight-through wire. |
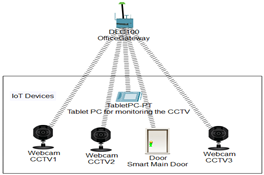 |
| The tablet PC is used to monitor the IOT devices. Inside the desktop, click on the IOT monitor, and you will be able to check all the IOT devices. | 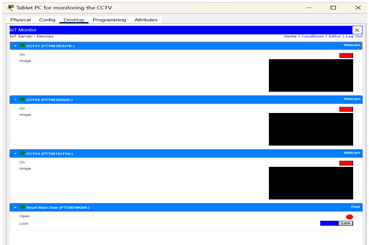 |
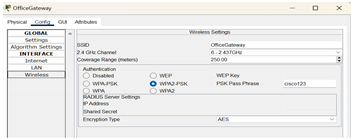
| Inside the config of HomeGateway, the SSID is changed to OfficeGateway and for extra security measures in authentication, WPA2-PSK is selected, which assigns login information for each IOT device and connects them to the network. |
 |
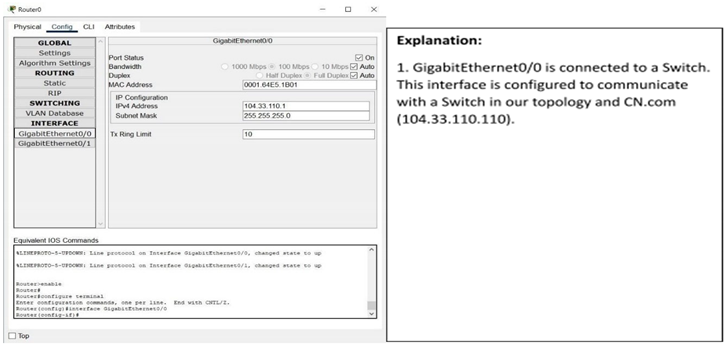
| The WRT300N wireless router is connected to the server through a 1941 router, which gets its connection from a switch. The reason for choosing a 1941 router is that it is specifically designed for small-to-medium-sized businesses and can handle multiple connections all at once, all while having a wired connection option as well. As for the WRT300N wireless router, it is used for mobile devices, computers, and laptops on most occasions, all while being affordable and having a decent range. |
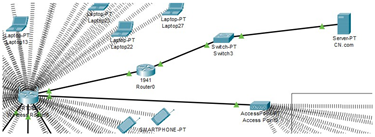 |
| Inside the config of wireless router, the SSID is set as OfficeNetwork and for security in the authentication, we selected WPA2-Enterprise (WiFi Protected Access 2), which assigns login information for each device for them to connect to the network. | 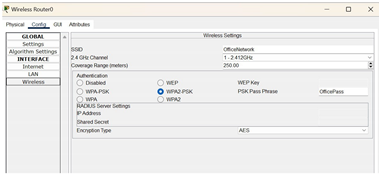 |
- 1)
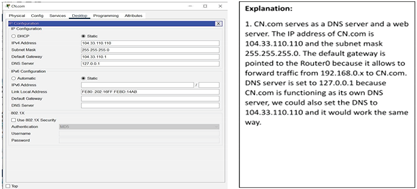
- Configuration for Wireless_Router0
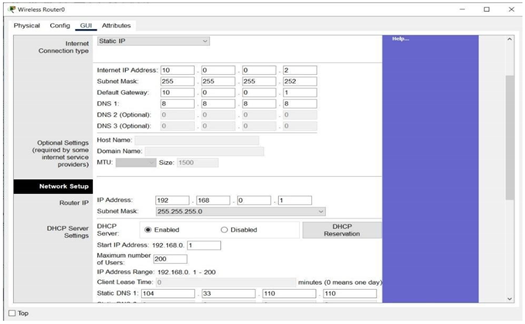
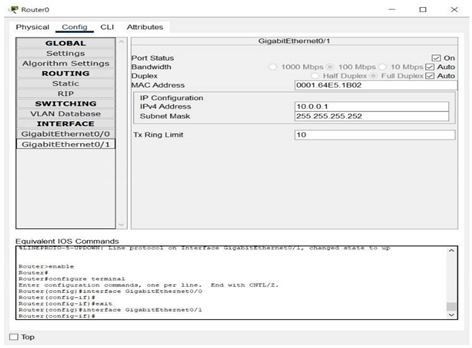
3.2. Interface GigabitEthernet0/1
- 3)
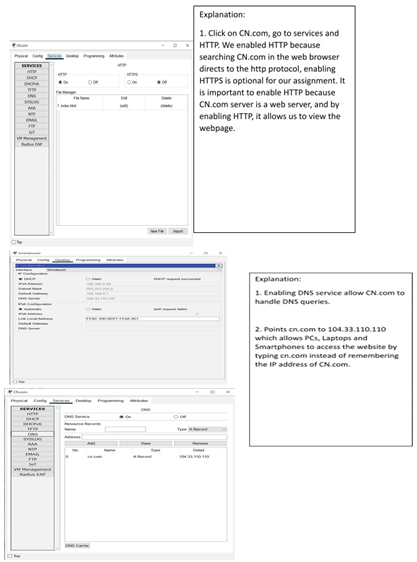
- Configure CN.com
- 4)
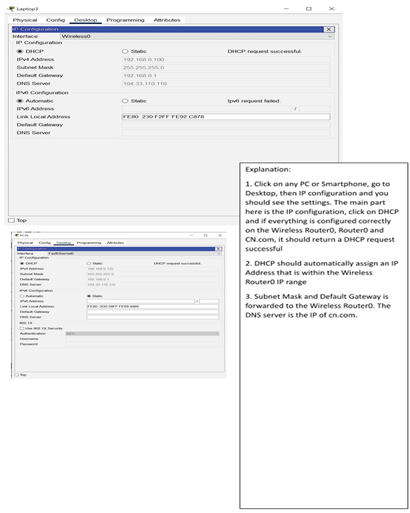
- Configuring Client Devices
3.3. Verify Connectivity
| Steps | Explanation | Screenshot |
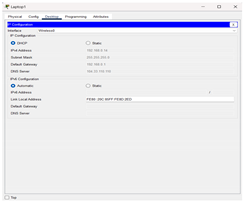
| Step 1: Refresh the IPv4 | We have opened the PC | 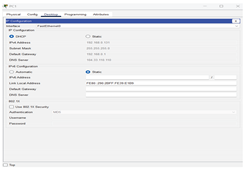 |
| settings on the PCs | window and selected Desktop | |
| from the menu. Then we | ||
| opened the IP Configuration | ||
| window and chose DHCP | ||
| instead of Static. We made | ||
| sure that the computer had an | ||
| IP address, Subnet Mask, and | ||
| Default Gateway. | ||
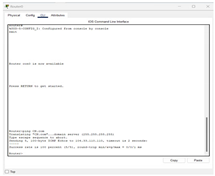
| In this step we tested connecting to a CN.com server Open the Command Prompt window from the Desktop menu, choose Command Prompt. Then we wrote the ping code CN.com to test it and it was working and there are no problems |
 |
|
| Step 2: Refresh the IPv4 settings on the Laptops | We have opened the laptops window and selected Desktop from the menu. Then we opened the IP Configuration window and chose DHCP instead of Static. We made sure that the computer had an IP address, Subnet Mask, and Default Gateway |
 |
| In this step we tested connecting to a CN.com server Open the web Browser window from the Desktop menu, we type CN.com in the search bar to make sure that the site is working well |
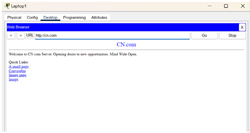 |
|
| Step 3: Refresh the IPv4 settings on the Mobile Phones |
We have opened the Smartphones window and selected Config from the menu. Then we chose DHCP instead of Static. We made sure that the computer had an IP address, Subnet Mask, and Default Gateway | 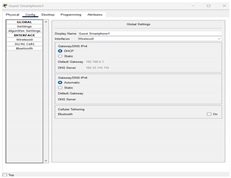 |
| In this step we tested connecting to a CN.com server Open the web Browser window from the Desktop menu inside the smartphone, we type CN.com in the search bar to make sure that the site is working well |
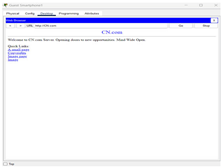 |
|
| Step 4: Refresh the IPv4 settings on the Router | It seems that the router does not have an explicitly dedicated WAN interface, but only GigabitEthernet0/0 and GigabitEthernet0/1 interfaces. Any Ethernet interface can be used as a WAN interface by configuring it correctly. |  |
| In this step, configure the GigabitEthernet interface as a WAN interface Choose CLI from the router window Enter the settings mode Type the enable code configure terminal Select GigabitEthernet0/1 as external interface (WAN) Type the code interface GigabitEthernet0/0 IP address 104.33.110.1 255.255.255.0 no shutdown Set NAT on this interface as external interface Type the code ip nat outside Check the connection to the DHCP server Type the code ip address dhcp |
 |
|
| Then make sure the default route ip route 0.0.0.0 0.0.0.0 10.0.0.1 make sure the GigabitEthernet0/1 interface (internal) has the ip nat inside command |
||
| We made sure that the CN.com works correctly and there are no problems by writing the code in the CLI interface |
 |
4. Challenges
5. Conclusions
References
- Kurose, J. F., & Ross, K. W. (2021). Computer networking: A top-down approach. Pearson.
- Cisco Systems. (n.d.). Cisco Packet Tracer – Networking simulation tool. https://www.cisco.com.
- li, S. A. M., & Mustafa, A. S. (2015). Designing and implementing a simple and secure network by using Cisco Packet Tracer. International Journal of Computer Applications, 129(5), 1–8.
- Qu, H., Zhang, Y., Chen, X., & Wu, B. (2020). Network simulation and implementation using Cisco Packet Tracer. International Journal of Computer Science and Network Security, 20(1), 150–158.
- Cai, J., & Chen, T. (2015). Enterprise network design and simulation with Packet Tracer. International Journal of Science and Technology, 5(6), 23–28.
- Saeed, S. (2016). Surveillance system concept due to the uses of face recognition application. Journal of Information Communication Technologies and Robotic Applications, 7(1), 17–22.
- Saeed, S. (2019). A conceptual system on ubiquitous cardiovascular health-care system (UCHS). SSUET, 9(1), 15–19.
- Saeed, S. (2018). Performance analysis of quality assurance due to the usage of two enterprise resource planning systems: Microsoft Dynamics AX and SAP. Mehran University of Engineering and Technology Journal (MUET), 37(2), 337–350.
- Saeed, S., Jhanjhi, N. Z., Naqvi, S. M. R., & Khan, A. (2022). Cost optimization of software quality assurance. In Deep learning in data analytics: Recent techniques, practices and applications (pp. 241–255).
- Saeed, S., Jhanjhi, N. Z., Naqvi, S. M. R., & Khan, A. (2022). Analytical approach for security of sensitive business cloud. In Deep learning in data analytics: Recent techniques, practices and applications (pp. 257–266).
- Dogra, V., Singh, A., Verma, S., Kavita, Jhanjhi, N. Z., & Talib, M. N. (2021). Analyzing DistilBERT for sentiment classification of banking financial news. In S. L. Peng, S. Y. Hsieh, S. Gopalakrishnan, & B. Duraisamy (Eds.), Intelligent computing and innovation on data science (Vol. 248, pp. 665–675). Springer. [CrossRef]
- Gopi, R., Sathiyamoorthi, V., Selvakumar, S., et al. (2022). Enhanced method of ANN based model for detection of DDoS attacks on multimedia Internet of Things. Multimedia Tools and Applications, 81(36), 26739–26757. [CrossRef]
- Chesti, I. A., Humayun, M., Sama, N. U., & Jhanjhi, N. Z. (2020, October). Evolution, mitigation, and prevention of ransomware. In 2020 2nd International Conference on Computer and Information Sciences (ICCIS) (pp. 1–6). IEEE.
- Alkinani, M. H., Almazroi, A. A., Jhanjhi, N. Z., & Khan, N. A. (2021). 5G and IoT based reporting and accident detection (RAD) system to deliver first aid box using unmanned aerial vehicle. Sensors, 21(20), 6905. [CrossRef]
- Babbar, H., Rani, S., Masud, M., Verma, S., Anand, D., & Jhanjhi, N. (2021). Load balancing algorithm for migrating switches in software-defined vehicular networks. Computational Materials and Continua, 67(1), 1301–1316. [CrossRef]
- Javed, D., Jhanjhi, N. Z., Khan, N. A., Ray, S. K., Al Mazroa, A., Ashfaq, F., & Das, S. R. (2024). Towards the future of bot detection: A comprehensive taxonomical review and challenges on Twitter/X. Computer Networks, 254, 110808. [CrossRef]
- Jhanjhi, N. Z., & Shah, I. A. (Eds.). (2024). Navigating Cyber Threats and Cybersecurity in the Logistics Industry. IGI Global.
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., ... & Murugesan, R. K. (2024). Industry 4.0: Future Trends and Research Directions. Convergence of Industry 4.0 and Supply Chain Sustainability, 342-405.
- Das, S. R., Jhanjhi, N. Z., Asirvatham, D., Ashfaq, F., & Abdulhussain, Z. N. (2023, February). Proposing a model to enhance the IoMT-based EHR storage system security. In International Conference on Mathematical Modeling and Computational Science (pp. 503-512). Singapore: Springer Nature Singapore.
- Humayun, M., Sujatha, R., Almuayqil, S. N., & Jhanjhi, N. Z. (2022, June). A transfer learning approach with a convolutional neural network for the classification of lung carcinoma. In Healthcare (Vol. 10, No. 6, p. 1058). MDPI. [CrossRef]
- Khan, N., Hamid, B., Humayun, M., Jhanjhi, N. Z., & Tahir, S. (2024). Information Retrieval from Healthcare Information System. In Computational Intelligence in Healthcare Informatics (pp. 107-125). Singapore: Springer Nature Singapore.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



