Submitted:
05 May 2025
Posted:
06 May 2025
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
- A novel hybrid trust management architecture tailored for VANETs’ dynamic conditions,
- Lightweight and decentralized trust storage using the IOTA Tangle,
- Adaptive trust evaluation using probabilistic and anomaly-based methods,
- Large-scale simulations evaluating detection accuracy, latency, and system scalability.
2. Literature Review
2.1. Reputation-Based Trust Management Systems
2.2. Entropy-Based Trust Management System
2.3. Bayesian Inference-Based Trust Management Systems
2.4. Blockchain-Based Trust Management Systems
2.5. Hybrid Trust Management Systems
2.6. Research Gap and Motivation
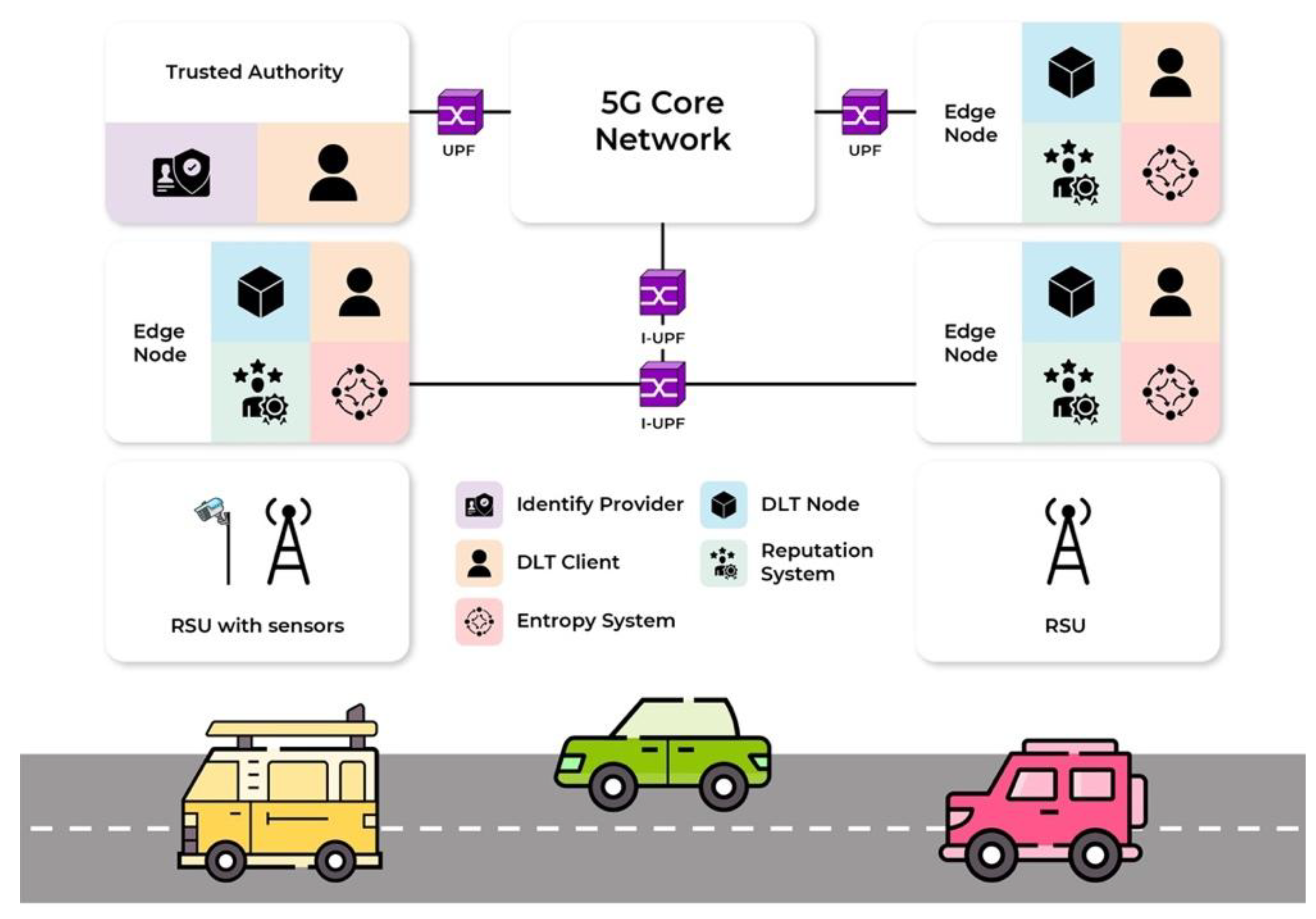
3. System Design
- Edge Nodes: Act as local computing units that collect vehicle messages, authenticate them, and calculate reputation scores. These nodes use entropy-based anomaly detection and Bayesian inference to detect suspicious activity. If anomalies are found, Edge Nodes update the DLT node.
- Road-Side Units (RSUs): Positioned along the roads to relay messages, extend communication range, and validate the consistency of vehicle-reported information. RSUs collect environmental and traffic data to assist in message verification.
- Trusted Authority (TA): A centralized entity that manages vehicle identities. It assigns Decentralized Identifiers (DIDs), authenticates vehicles, and conducts periodic audits to ensure trust and compliance.
- Entropy System: Detects irregular message transmission patterns by monitoring message frequency and coherence. A high entropy value indicates potential attacks, such as DoS, Sybil, or replay attacks.
- Reputation System: Uses Bayesian inference to dynamically update vehicle reputation scores based on historical trust data and current behavior.
- DLT Node: Stores trust scores securely in the IOTA Tangle, ensuring tamper-proof and decentralized record-keeping. It prevents data manipulation and ensures secure retrieval of trust scores.
- Message Exchange: Vehicles periodically transmit Cooperative Awareness Messages (CAMs) and Decentralized Environmental Notification Messages (DENMs), which RSUs and Edge Nodes intercept for validation.
- Integrity Verification: Upon receiving a message, an Edge Node verifies its authenticity using the vehicle’s Decentralized Identifier (DID) issued by the Trusted Authority (TA).
- Reputation Evaluation: Messages are compared against RSU-collected sensor data to ensure accuracy and consistency.
- Anomaly Detection (Entropy-Based): The Entropy System analyzes message timing fluctuations. If entropy is above a threshold, the vehicle is flagged as suspicious.
-
Trust Score Update (Bayesian Reputation System): Bayesian inference updates reputation scores dynamically, incorporating:
- ▪
- Historical interactions (long-term trust)
- ▪
- Real-time message consistency (short-term trust)
- ▪
- Entropy-based anomaly detection (behavior deviation)
- Tamper-Proof Storage on DLT: Updated trust scores are securely stored on the IOTA Tangle, ensuring decentralized reputation management.
- Reputation Query: Vehicles can request reputation scores from Edge Nodes, which fetch the latest verified scores from the DLT Node.
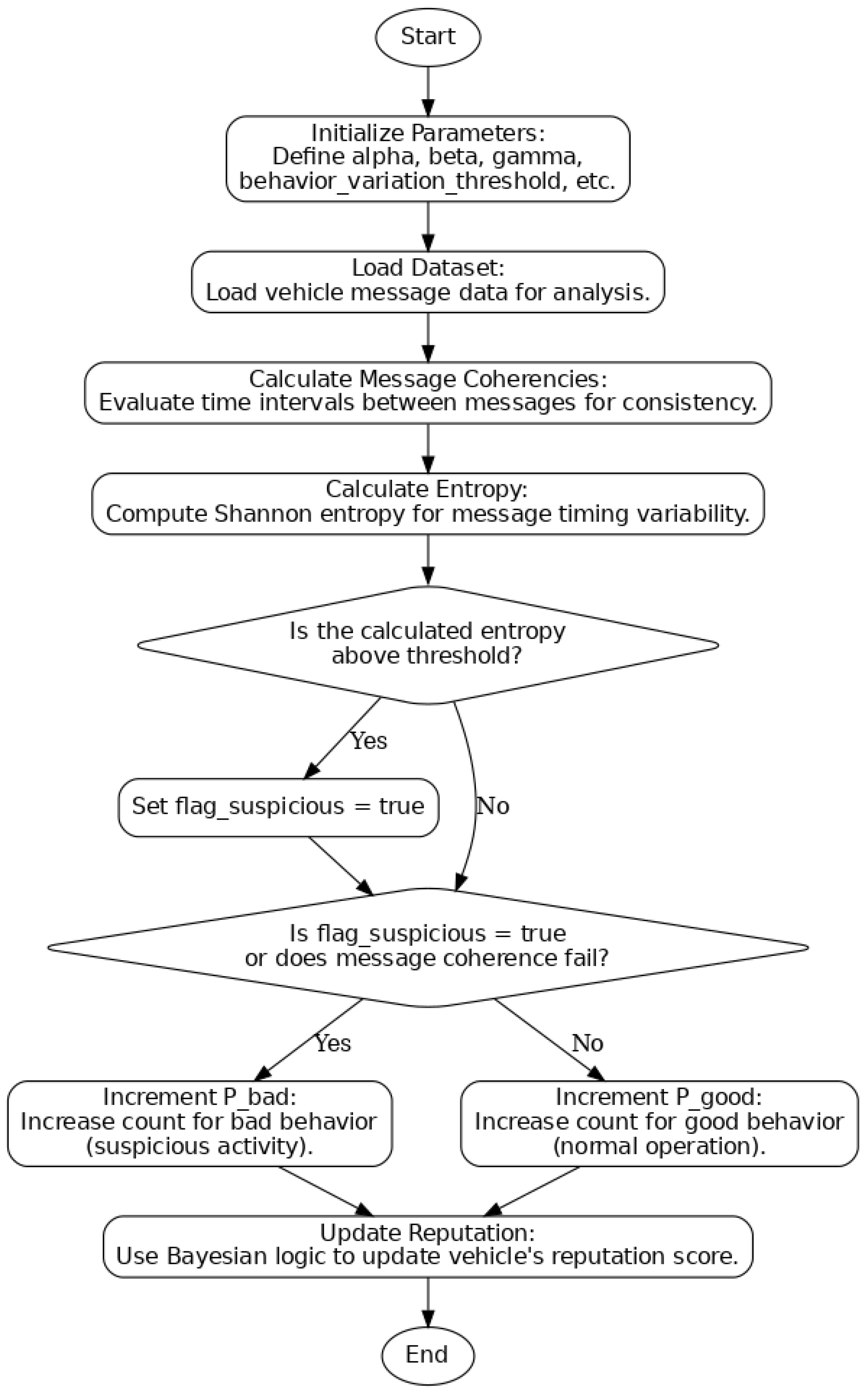
- Step 1: Initialize Parameters
- ○
- alfa (α): A weight assigned to the vehicle’s previous reputation, representing its historical behaviour.
- ○
- beta (β): A weight that measures the impact of the current message’s consistency on the updated reputation score.
- ○
- gamma (γ): A weight that considers detected anomalies, particularly variations indicated by high entropy values.
- ○
- behaviour_variation_threshold: A predefined cut-off value used to distinguish between normal and abnormal vehicle behaviour based on entropy calculations.
- Step 2: Load Dataset
- Step 3: Calculate Message Coherencies
- Step 4: Calculate Entropy
- Step 5: Check for High Entropy
- Step 6: Calculate Evidence Probability
- ○
- If the entropy is high or message coherencies fail, the probability count for bad behaviour (P_bad) is incremented, indicating accumulating evidence of suspicious activity.
- ○
- Conversely, if the messages are consistent and entropy is low, the probability count for good behaviour (P_good) increases, signalling evidence of normal operation.
- Step 7: Update Reputation Using Bayesian Formula
- ○
- Historical reputation: The vehicle’s previous reputation score .
- ○
- Current message integrity: The quality and consistency of the current message based on coherency checks .
- ○
- Detected anomalies: Any inconsistencies or randomness detected in message timing (represented by the entropy score) .
4. Evaluation Methodology
4.1. Adversarial Models
-
Dolev–Yao Model: This model provides a comprehensive framework for assessing how the system handles various attacks. It assumes that an attacker can intercept any message in the network, initiate communication with any participant, and even impersonate legitimate recipients. The following attacks are considered:
- ○
- Eavesdropping Attack: An attacker gains unauthorised access to sensitive data, such as vehicle locations, personal information, or messages between vehicles and Road Side Units (RSUs), compromising communication confidentiality.
- ○
- Replay Attack: The attacker intercepts and retransmits previously recorded messages to deceive vehicles, disrupting traffic management, collision prevention, and cooperative driving systems.
- ○
- Forgery Attack: The attacker impersonates legitimate users or entities to forge messages, misleading other vehicles and potentially causing unsafe or unintended outcomes.
- ○
- Sybil Attack: The attacker creates multiple fake identities or vehicles to deceive network participants, disrupting routing protocols, manipulating traffic flow, and spreading false information [35].
-
Network Adversary Model: This model comprehensively analyses network traffic behaviour under real-world attack scenarios, such as DoS and DDoS, at the network level. It effectively simulates how the system handles high traffic loads and evaluates the resilience of the network infrastructure under stress. Key aspects include:
- ○
- DoS Attack: The attacker overwhelms the network or specific nodes with excessive requests or messages, leading to resource exhaustion and reduced availability of communication services.
- ○
- DDoS Attack: A more severe version where multiple sources coordinate to send high volumes of traffic to a target, exhausting bandwidth and processing power and crippling communication [41].
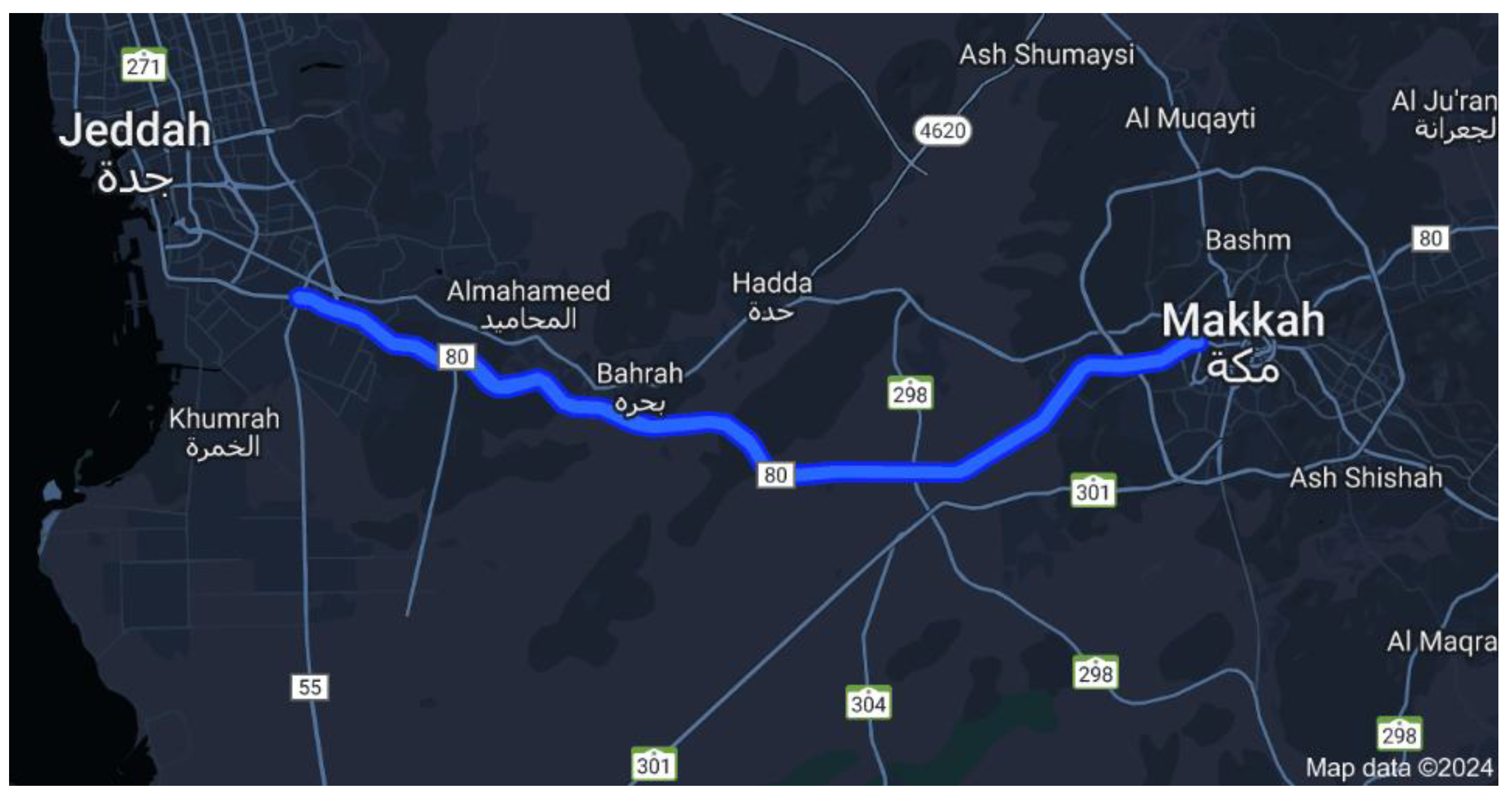
4.2. Simulation Setup and Dataset
4.3. V2V Communications Dataset
5. Results & Discussions
5.1. Effect of Vehicle Count
5.2. Effect of Malicious Percentage
5.3. System Robustness Against Attack Models
- DoS and DDoS Resistance: Entropy-based detection identifies message flooding attacks in real-time, ensuring that DoS attackers cannot manipulate vehicle communications. Unlike DIVA [18], which lacks strong DoS detection, our system flags anomalous frequency spikes and adjusts entropy thresholds dynamically.
- Sybil Attack Mitigation: The system ensures unique trust scores per vehicle, preventing identity spoofing. If multiple messages from a single entity exceed entropy variation limits, the system flags them as suspicious, reducing the risk of Sybil-based disruptions.
- Replay Attack Prevention: Timestamp-based message validation ensures that replayed messages are not treated as legitimate communications. The Bayesian update mechanism penalizes vehicles that repeatedly transmit outdated information, effectively neutralizing replay attacks.
- Forgery Attack Detection: The combination of entropy variations and Bayesian consistency checks enables the system to detect falsified messages, ensuring that only genuine, consistent data contributes to reputation scores.
5.4. Computational Efficiency and Scalability
- Real-Time Entropy Evaluation: The system employs lightweight Shannon entropy calculations to analyze message timing and behavioral variance. These calculations are computationally inexpensive, enabling continuous anomaly detection even in dense network conditions with hundreds of participating vehicles.
- Optimized Bayesian Inference: Bayesian trust score updates are selectively triggered based on entropy thresholds and behavioral deviations. This design significantly reduces the number of redundant trust updates, thus minimizing computational overhead while maintaining accurate reputation tracking.
- Low-Latency Detection Performance: Empirical results from simulation show that the end-to-end latency for trust evaluation, including entropy scoring and Bayesian inference, consistently remains under 1.5 seconds, even in scenarios with up to 400 vehicles and 40% malicious participation. This latency is well within the operational thresholds required for real-time vehicular decision-making, such as message forwarding, event reaction, or route selection.
5.5. Benchmarking with Existing Trust Management Models
| Metric | VANETGuard | DIVA [18] (Mode Threshold) | AATMS [12] | HTMS-V [13] | ART [16] | HDRS [14] |
|---|---|---|---|---|---|---|
| Detection Accuracy (%) | 99.925 | 99.9 | ~98.5 (derived from TPR/TNR) | >95 under most attacks | 96.8 (estimated from robustness section) | >97% across conditions (dynamic) |
| TPR (%) | 99.85 | 99.8 | ≥97.8 (at 20–30% collusion) | 96%+ (for malicious node identification) | ~95.9 (collusion scenarios) | 100% (≤40% malicious); drops after |
| TNR (%) | 100.0 | 100.0 | ~99 (stable across conditions) | >95–97% | 97.6 | High; contextually adaptive |
| FPR (%) | 0.0 | 0.0 | 1.0% or less (verified) | <4%, even under hybrid attacks | ~2.4 | Low, adaptive to context |
| FNR (%) | 0.15 | 0.2 | ~2.2% (drops at high collusion) | <4–5%, drops when malicious rate >40% | ~4.1% | Slight rise >40% malicious, stays low |
| Performance in High Malicious (50%) | Maintains ~98% | Drops significantly | Drops moderately (~94%) | Moderate drop (~90%) | Severe drop (~88%) | Can’t detect all at 50%, but stable below |
| Execution Latency | ms (Bayesian + IOTA) | µs (Tangle) | Seconds (cloud sync + Bayesian) | Milliseconds (local-only) | Milliseconds (lightweight) | ms range, dynamic interval |
| DDoS Mitigation | Effective (entropy analysis) | Not addressed | Limited (weighted filtering) | Not explicitly addressed | Basic thresholds | Effective (entropy + reliability filters) |
| Trust Update Mechanism | Entropy + Bayesian + DLT | DLT only | TrustRank + Forgetting + Feedback filters | Subjective logic + indirect decay | History + weighted scoring | Hybrid V2V/RSU + Reliability eval + AHP weights |
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| VANETs | Vehicular Ad Hoc Networks |
| V2V | Vehicle-to-Vehicle |
| V2I | Vehicle-to-Infrastructure |
| HTMS | Hybrid Trust Management System |
| DLT | Distributed Ledger Technology |
| DoS | Denial-of-Service |
| DDoS | Distributed Denial-of-Service |
| TPR | True Positive Rate |
| FPR | False Positive Rate |
| ITS | Intelligent Transportation Systems |
| V2X | Vehicle-to-Everything |
| IRS | Intelligent Reputation System |
| TA | Trusted Authority |
| DIDs | Decentralized Identifiers |
| RSUs | Road-Side Units |
| CAMs | Cooperative Awareness Messages |
| DENMs | Decentralized Environmental Notification Messages |
| FNR | False Negative Rate |
| TNR | True Negative Rate |
| IOTA | A type of Distributed Ledger Technology (DLT) |
| ML | Machine Learning |
| 5G | Fifth Generation Mobile Network |
| OMNeT++ | Objective Modular Network Testbed in C++ |
| SUMO | Simulation of Urban MObility |
| Simu5G | 5G Network Simulation Tool |
| ETS-G5 | European Telecommunications Standards Institute Intelligent Transport Systems G5 |
| DIVA | Decentralized Identification-Based Vehicular Authentication |
| MDPI | Multidisciplinary Digital Publishing Institute |
| DOAJ | Directory of Open Access Journals |
| TLA | Three Letter Acronym |
| LD | Linear Dichroism |
References
- Raya, M. , et al., “Early Reputation-Based Trust Models for VANETs,” IEEE Transactions on Vehicular Technology, vol. 56, no. 6, pp. 2562-2575, 2007.
- Dahiya, M. , et al., “Simulation-Based Reputation Management in VANETs Using NS-3,” Journal of Network Security, vol. 5, no. 2, pp. 112-123, 2018.
- Zhang, X. , et al., “Machine Learning-Integrated Reputation Systems for VANETs,” IEEE Transactions on Intelligent Transport Systems, vol. 20, no. 4, pp. 1552-1565, 2019.
- Kumar, P. , et al., “Secure Data Dissemination and Trust in VANETs,” Elsevier Vehicular Communications, vol. 24, pp. 67-78, 2020.
- Mahmood, A. , et al., “Distributed Reputation-Based Security in VANETs,” Springer Journal of Computer Science, vol. 15, no. 3, pp. 145-160, 2021.
- Sheikh, F. , et al., “Blockchain-Based Reputation Integrity in VANETs,” IEEE Transactions on Blockchain Technology, vol. 6, no. 4, pp. 745-759, 2022.
- Feraudo, D. , et al., “DIVA: A Decentralized Trust Model for VANETs Using IOTA Tangle,” MDPI Sensors, vol. 23, no. 5, pp. 2012-2025, 2023.
- Mejri, M.; Ben-Othman, J. , “Packets Entropy for Detecting DoS Attacks in VANETs,” IEEE Wireless Communications, vol. 19, no. 3, pp. 45-52, 2017.
- Ahmed, R.; Tepe, K. , “Adaptive Trust Models for VANETs Using Entropy Analysis,” IEEE Internet of Things Journal, vol. 7, no. 8, pp. 6891-6902, 2020.
- Kumar, S.; Mann, V. , “Entropy-Based DoS Attack Mitigation in VANETs,” Springer Journal of Cyber Security, vol. 12, pp. 301-317, 2021.
- Yin, L.; Li, J. , “Real-Time Trust Assessment in VANETs Using Entropy Weighting,” Elsevier Vehicular Networks Journal, vol. 8, pp. 89-102, 2022.
- Zhang, H. , et al., “AATMS: Bayesian Inference and TrustRank for VANETs,” IEEE Transactions on Smart Cities, vol. 5, no. 2, pp. 567-580, 2023.
- Xiang, Z.; Chen, X. , “HTMS-V: Hybrid Trust Evaluation for VANETs,” MDPI Electronics, vol. 11, no. 9, pp. 1256-1272, 2023.
- Liu, Y. , et al., “HDRS: Reputation-Based Trust System for VANETs,” IEEE Transactions on Mobile Computing, vol. 22, no. 5, pp. 1345-1360, 2022.
- Mahmood, A. , et al., “Scalable Trust Systems in VANETs,” MDPI Future Internet, vol. 14, no. 6, pp. 98-115, 2023.
- Mehra, R.; Patidar, S. , “ART: Attack-Resistant Trust Model for VANETs,” Elsevier Computers & Security, vol. 25, no. 3, pp. 333-347, 2023.
- He, X. , et al., “Bayesian Trust Models for Cognitive Radio-Based VANETs,” IEEE Communications Letters, vol. 25, no. 8, pp. 2103-2117, 2021.
- Fang, T. , et al., “Mitigating On-Off Attacks Using Bayesian Networks,” IEEE Transactions on Vehicular Technology, vol. 69, no. 7, pp. 7855-7868, 2020.
- Li, J. , et al., “Bayesian Inference and Game Theory for Secure Content Delivery in VANETs,” MDPI Sensors, vol. 20, no. 14, pp. 4158-4172, 2022.
- Talal, A. , et al., “A Decentralized Bayesian Trust Model for VANETs,” IEEE Transactions on Dependable and Secure Computing, vol. 19, no. 3, pp. 745-759, 2023.
- Ahmed, S. , et al., “Privacy-Preserving Authentication and Trust in Blockchain-Based VANETs,” IEEE Blockchain Transactions, vol. 4, no. 1, pp. 65-78, 2023.
- Yang, X. , et al., “Blockchain-Based Reputation Systems for Secure VANETs,” Elsevier Vehicular Communications, vol. 19, pp. 89-102, 2021.
- Lu, Y. , et al., “BARS: Blockchain-Based Anonymous Reputation System for VANETs,” IEEE Internet of Things Journal, vol. 8, no. 5, pp. 1983-1995, 2020.
- Zhao, C. , et al., “Machine Learning Integration in Blockchain Trust Models for VANETs,” MDPI Electronics, vol. 24, no. 9, pp. 875-890, 2023.
- Zhang, K. , et al., “Deep Learning and Blockchain for Trust Management in VANETs,” Elsevier Journal of Intelligent Transport Systems, vol. 27, no. 2, pp. 345-360, 2022.
- Kudva, A. , et al., “A Decentralized Trust Framework for Blacklisting Insider Attacks in VANETs,” IEEE Transactions on Information Forensics and Security, vol. 18, no. 1, pp. 210-225, 2023.
- Liu, H. , et al., “Hidden Markov Model-Based Blockchain Trust for VANETs,” IEEE Transactions on Intelligent Vehicles, vol. 6, no. 2, pp. 875-889, 2022.
- Alhatrhi, A. , et al., “Biometric Blockchain Framework for Trust Classification in VANETs,” Springer Journal of Cyber Security, vol. 31, no. 4, pp. 332-349, 2023.
| Threshold | α = 0.4, β = 0.4, γ = 0.2 | TPR (%) | TNR (%) | FPR (%) | FNR (%) |
|---|---|---|---|---|---|
| Mode | 0.5 | 99.9 | 79.80 | 20.20 | 0.04 |
| Median | 0.5 | 99.95 | 79.60 | 20.40 | 0.08 |
| Mean | 0.5 | 99.91 | 100 | 0 | 0.2 |
| Vehicles | Malicious (%) | TPR (%) | TNR (%) | Detection Accuracy (%) | FPR (%) | FNR (%) |
|---|---|---|---|---|---|---|
| 20 | 5 | 99.98 | 100 | 99.99 | 0.0 | 0.13 |
| 10 | 99.98 | 100 | 99.98 | 0.0 | 0.28 | |
| 20 | 99.93 | 100 | 99.94 | 0.3 | 0.55 | |
| 40 | 99.85 | 100 | 99.93 | 0.0 | 0.15 | |
| 40 | 5 | 99.94 | 100 | 99.97 | 0.15 | 0.3 |
| 10 | 99.94 | 100 | 99.97 | 0.4 | 0.7 | |
| 20 | 99.91 | 100 | 99.93 | 0.0 | 0.2 | |
| 40 | 99.85 | 99.95 | 99.9 | 0.25 | 0.5 | |
| 80 | 5 | 99.64 | 99.95 | 99.80 | 0.5 | 0.9 |
| 10 | 99.64 | 99.95 | 99.80 | 0.0 | 0.13 | |
| 20 | 99.57 | 99.85 | 99.71 | 0.1 | 0.28 | |
| 40 | 99.51 | 99.65 | 99.58 | 0.3 | 0.55 | |
| 160 | 5 | 98.20 | 100.0 | 99.1 | 0.0 | 0.15 |
| 10 | 97.74 | 99.92 | 98.83 | 0.15 | 0.3 | |
| 20 | 97.7 | 99.8 | 98.75 | 0.4 | 0.7 | |
| 40 | 97.4 | 99.6 | 98.5 | 0.0 | 0.2 | |
| 320 | 5 | 97.0 | 100.0 | 98.5 | 0.25 | 0.5 |
| 10 | 96.9 | 99.9 | 98.4 | 0.5 | 0.9 | |
| 20 | 97 | 99.75 | 98.4 | 0.0 | 0.13 | |
| 40 | 96.5 | 99.5 | 98.0 | 0.1 | 0.28 | |
| 400 | 5 | 97.6 | 100.0 | 98.8 | 0.3 | 0.55 |
| 10 | 96.75 | 99.85 | 98.3 | 0.0 | 0.15 | |
| 20 | 96.5 | 99.7 | 98.1 | 0.15 | 0.3 | |
| 40 | 96.4 | 99.4 | 97.9 | 0.4 | 0.7 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




