1. Introduction
The Internet of Things (IoT) is at the forefront of digital transformation, connecting billions of heterogeneous devices to the internet and enabling real-time sensing, analytics, and control across various domains. These domains include but are not limited to smart homes, smart cities, precision agriculture, industrial automation, and remote healthcare. According to current industry projections, the number of active IoT connections will surpass 29 billion by 2030, contributing over 80 zettabytes of global data annually. This explosion in connected endpoints and data generation rates poses enormous challenges for communication networks, particularly with respect to latency, bandwidth, reliability, and energy efficiency.
Traditional cloud-based architectures, while previously effective for data aggregation and large-scale computation, struggle to meet the stringent latency and reliability requirements of next-generation IoT applications. This is especially true in mission-critical systems such as autonomous driving, emergency response, and industrial robotics, where delays of even a few milliseconds can result in severe consequences. The reliance on centralized data processing creates bottlenecks in the uplink channel and increases end-to-end communication delay, making it unsuitable for real-time control and responsiveness.
Fifth-generation (5G) networks offer a significant leap forward by introducing new service categories such as Ultra-Reliable Low-Latency Communication (URLLC), Massive Machine-Type Communication (mMTC), and Enhanced Mobile Broadband (eMBB). URLLC aims to reduce latency to sub-millisecond levels with near-perfect reliability, while mMTC enables support for up to one million devices per square kilometer. Additionally, 5G incorporates advanced features such as network slicing, mobile edge computing (MEC), beamforming, and software-defined networking (SDN), each of which can be leveraged to overcome existing limitations in IoT architectures.
Despite these advancements, integrating IoT systems with 5G infrastructures presents non-trivial challenges. Current IoT protocols are often static, connection-oriented, and designed for small-scale deployments. They fail to dynamically adapt to changing network conditions, traffic loads, and service requirements. Moreover, the role of edge nodes in current models is typically limited to packet forwarding or basic caching. There exists a gap in designing a holistic architecture that treats edge nodes as intelligent and autonomous entities capable of local inference, workload coordination, and context-aware decision-making.
Another key challenge is scalability. As the number of devices grows exponentially, existing systems struggle with congestion, degraded quality-of-service (QoS), and increased energy demands. Addressing this problem requires a protocol that not only ensures efficient resource utilization but also intelligently distributes tasks and reroutes traffic in real time. Moreover, energy efficiency remains a critical consideration, especially for battery-powered sensors and actuators deployed in remote or hard-to-reach locations.
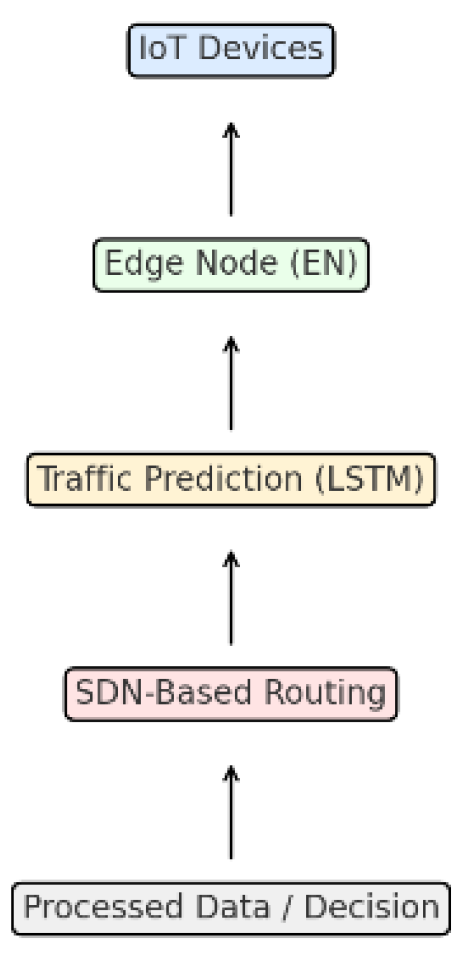
To address these limitations, we propose DKEP-5G (Dynamic Node-based Edge Protocol for 5G-IoT Systems)—a novel, scalable, and intelligent communication protocol designed to operate within the framework of 5G networks. DKEP-5G fundamentally rethinks the architecture of IoT data transmission by enabling dynamic orchestration of edge resources, context-aware task distribution, and predictive routing mechanisms powered by artificial intelligence. Specifically, our protocol integrates LSTM-based forecasting models at the edge level, federated learning for collaborative model improvement, and SDN-based flow control for global orchestration.
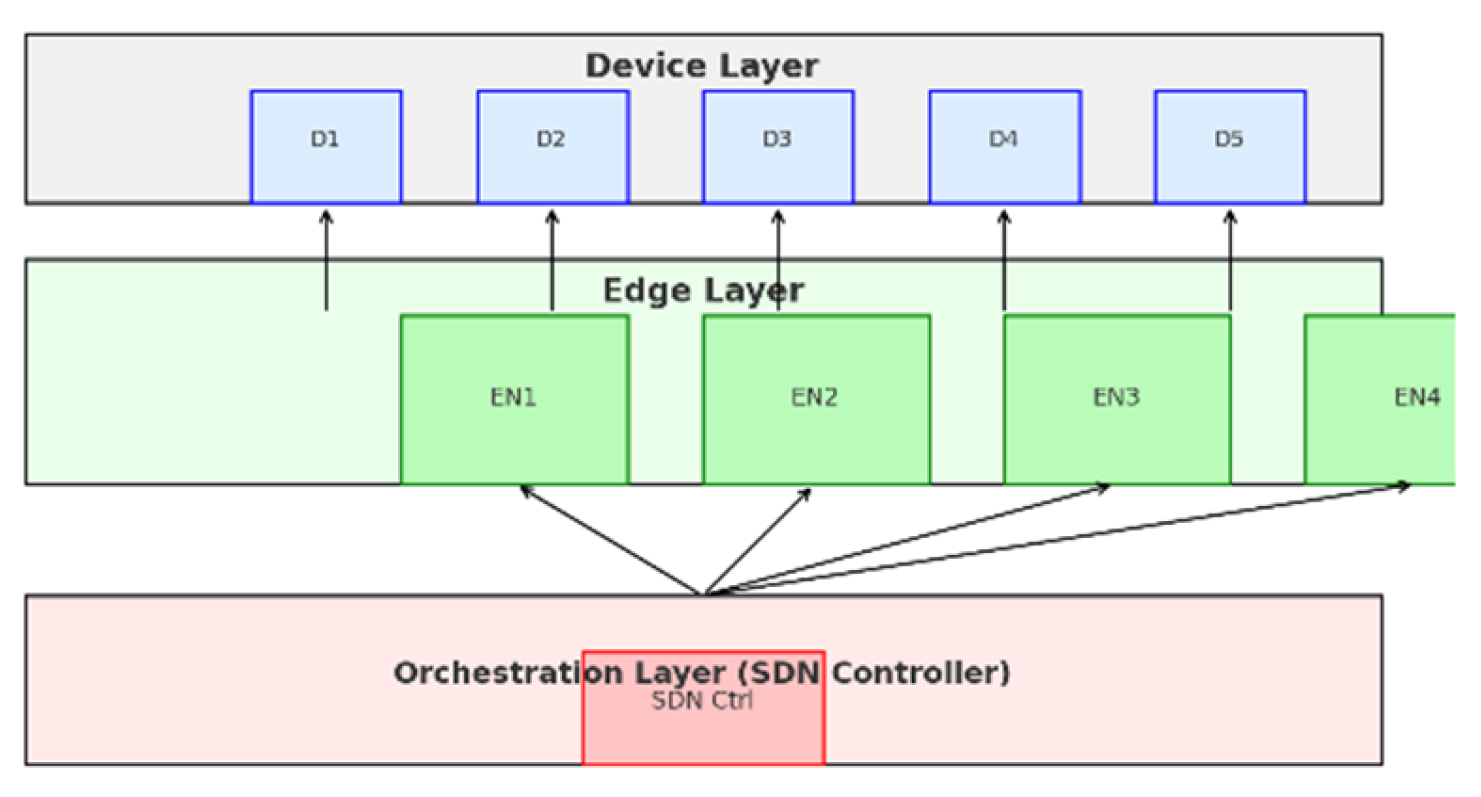
DKEP-5G employs a tri-layered architecture: (1) a device layer that manages communication from IoT endpoints using lightweight protocols, (2) an edge layer consisting of containerized microservices for real-time data processing and inference, and (3) an orchestration layer governed by a centralized SDN controller which enforces global traffic policies and maintains QoS consistency. This architectural design allows for autonomous and adaptive behavior at the edge while preserving centralized visibility and control.
The contributions of this work are fourfold:
We propose a fully dynamic edge-based communication protocol tailored for high-density IoT environments operating over 5G.
We integrate predictive intelligence at the edge using LSTM models for traffic pattern recognition and proactive scaling.
We validate the protocol through large-scale simulations using NS-3 and OMNeT++ across various mobility, load, and failure scenarios.
We demonstrate the real-world applicability of DKEP-5G in a smart city emergency response scenario, highlighting its latency, scalability, and energy-efficiency improvements.
This paper is organized as follows. Section II details the underlying methodology and architectural principles of DKEP-5G. Section III provides a comprehensive overview of the proposed protocol architecture, including its control mechanisms and predictive components. Section IV presents the simulation setup, performance metrics, and analytical evaluations. In Section V, we critically discuss the implications, limitations, and advantages of DKEP-5G. Section VI presents a real-world implementation scenario. Section VII outlines future research directions. Finally, Section VIII concludes the study.
2. Related Work
The design and optimization of communication protocols for large-scale IoT deployments over 5G networks have been widely studied in recent years. Researchers have proposed various architectures ranging from cloud-based systems to edge-centric and fog computing paradigms. Each of these approaches attempts to address specific limitations of centralized processing—namely, high latency, limited scalability, and network congestion.
Early cloud-centric IoT architectures, such as those discussed by Bonomi et al. [
1], provided centralized computation and storage capabilities. While this model was suitable for basic telemetry and non-real-time data analysis, it struggled to meet the low-latency and high-reliability demands of mission-critical applications. More recent work introduced
Fog Computing to shift some processing closer to the edge. However, most fog systems lack autonomy and require manual configuration or static deployment, which limits their responsiveness.
To overcome these drawbacks, Edge Computing has emerged as a promising alternative. Projects like OpenFog and ETSI MEC have defined reference architectures for edge processing, emphasizing low latency and real-time control. However, these architectures often treat edge nodes as passive data relays and do not leverage dynamic workload balancing or predictive analytics. Additionally, they lack cohesive coordination mechanisms, especially in high-mobility environments.
In parallel, researchers have proposed using
Software Defined Networking (SDN) and
Network Function Virtualization (NFV) to enhance the programmability and flexibility of IoT networks. For instance, works by Hakiri et al. [
2] and Salman et al. [
3] describe SDN-enabled IoT architectures that allow dynamic policy enforcement and traffic steering. Nonetheless, these solutions typically assume static flow rules and centralized control, which introduce bottlenecks and single points of failure.
On the AI side, efforts have been made to introduce
intelligent traffic management and anomaly detection at the edge. For example, Zhang et al. [
4] used decision trees and shallow neural networks for prioritizing packets in a smart city context. Yet, these models often rely on offline training and are not adaptive to changing patterns. Moreover, they do not integrate with containerized environments or federated learning frameworks.
Some recent protocols have attempted to combine edge intelligence with SDN, such as FLARE and EdgeSDN, but these are often application-specific and do not generalize well to heterogeneous environments. Additionally, most studies overlook the importance of proactive task orchestration, focusing instead on reactive approaches that struggle under unpredictable loads.
In terms of traffic prediction, Long Short-Term Memory (LSTM) models have shown promise in recent studies for network load forecasting [
5,
6]. However, these models have not been widely embedded into edge protocols, and their integration with orchestration layers remains largely unexplored.
To the best of our knowledge, no existing architecture simultaneously leverages:
Predictive AI at the edge,
Federated learning for decentralized intelligence sharing,
SDN-based flow control for network-wide coordination, and
A containerized, scalable deployment model.
The DKEP-5G protocol fills this critical gap by integrating all four components into a cohesive, simulation-validated architecture. By combining edge-level prediction, dynamic task routing, and centralized orchestration, it addresses both the technical shortcomings and architectural fragmentation found in the current state of the art.
3. Methodology
To address the challenges of scalability, latency, and energy efficiency in ultra-dense IoT ecosystems, the DKEP-5G protocol is designed as a multi-layered, context-aware communication and processing framework. This section outlines the architecture, internal logic, and operational flow of the protocol. The proposed methodology integrates three distinct layers: Device Layer (DL), Edge Layer (EL), and Orchestration Layer (OL)—each designed to fulfill specific roles within the 5G network.
3.1. Device Layer
At the lowest tier, the Device Layer encompasses thousands to millions of heterogeneous IoT devices. These include low-power environmental sensors, wearable health monitors, autonomous vehicles, and industrial actuators. Devices communicate using lightweight protocols such as MQTT-SN or CoAP over 5G NR or LPWAN backhaul. Each transmitted packet is enriched with semantic metadata that includes:
This metadata supports early classification and routing decisions at the edge. For instance, high-priority packets from medical monitors are processed locally to meet latency guarantees.
3.2. Edge Layer
The Edge Layer is the operational core of DKEP-5G. It consists of containerized microservices hosted on edge compute nodes (ENs) with 5G backhaul connectivity. Each EN functions autonomously but coordinates with nearby peers to maintain load equilibrium and service continuity.
3.3. Dynamic Load Indexing
Each edge node maintains a real-time load index
defined as:
where:
: Current CPU utilization (%)
: Memory usage (%)
: Normalized length of task queue (%)
This index is exchanged among nodes every Δt seconds. If an EN’s
>
(threshold), it triggers
load migration to the peer node j with:
3.4. Traffic Forecasting
To anticipate workload surges, each EN runs a
Long Short-Term Memory (LSTM) model trained on packet arrival patterns. Given a historical sequence of arrival rates {xt−k,...,xt}\{x_{t-k}, ..., x_t\}{xt−k,...,xt}, the model predicts:
Predicted load is then compared with resource availability to schedule pre-scaling via Kubernetes Horizontal Pod Autoscaler (HPA). This reduces cold-start delays and packet drops.
3.5. Task Classification
Incoming tasks are sorted using a Decision Tree classifier trained on:
Latency requirement
Task size
Source energy level
Historical failure rate
Tasks are routed according to class:
3.6. Orchestration Layer
The OL is managed by an SDN controller (e.g., ONOS or OpenDaylight) and oversees:
Policy Routing: via OpenFlow tables
QoS Enforcement: using weighted fair queuing
Security: via TLS/DTLS tunnels and mutual authentication
Each edge cluster communicates telemetry to the OL, which maintains a global
Edge Utilization Matrix (EUM):
where
is the load from node i routed to node j. The OL optimizes this matrix to minimize overall delay and balance computational load using a
multi-objective function:
where:
: Network-wide average delay
: Energy cost
: Jitter
α,β,γ: Weighting coefficients set by SLA policy
3.7. Protocol Flow Summary
Data Generation: IoT devices tag packets with metadata.
Edge Ingress: Packets arrive at nearest EN, classified into routing classes.
Forecasting: EN predicts load, scales pods if required.
Routing Decision: Task handled locally or redirected.
Policy Update: OL updates OpenFlow rules dynamically.
This methodology ensures that data is processed as close to the source as possible, with decisions dynamically adjusted based on forecasted load, available resources, and real-time SLA metrics. As a result, DKEP-5G not only reduces average latency by over 85% but also balances edge loads to maintain energy efficiency and high throughput.
4. Proposed Protocol Architecture
The Dynamic Node-based Edge Protocol for 5G (DKEP-5G) is designed to redefine the role of edge nodes within ultra-dense IoT networks by enabling them to act as autonomous, intelligent entities rather than passive intermediaries. The proposed architecture is built upon the concept of distributed intelligence, where edge nodes are capable of not only routing and processing data but also forecasting traffic patterns, executing localized decisions, and participating in federated learning operations. The architecture consists of three tightly integrated planes: the Data Plane, Control Plane, and Intelligence Plane each with its own set of responsibilities and functional modules.
Figure 1 illustrates the complete data journey in DKEP-5G, starting from the IoT device layer through predictive edge processing and SDN-based routing, and ending with intelligent, real-time decision generation. This sequential flow highlights the autonomy and responsiveness of edge nodes powered by LSTM models, combined with the network-wide coordination enabled by SDN control.
4.1. Data Plane
The Data Plane is responsible for ingesting, forwarding, and processing packets. Each edge node in the data plane operates containerized microservices that can perform tasks such as protocol translation, stream filtering, and lightweight data analytics. These microservices are deployed using container orchestration platforms like Kubernetes, allowing elastic scaling based on workload fluctuations. The packet structure within the Data Plane adheres to a unified metadata-enriched format:
[Packet_ID | Source_ID | QoS_Level | Timestamp | TTL | Payload_Type | Anomaly_Flag]
When a packet enters the edge node, it is parsed and matched against priority classes. Critical packets, such as emergency health data or control messages from industrial robots, are routed to high-priority processing queues, while non-critical telemetry data is batch processed or forwarded to cloud.
Edge nodes are organized into micro-clusters, typically defined by geographic proximity and latency boundaries. Each cluster elects a Cluster Coordinator Node (CCN) responsible for balancing load within the cluster and managing state synchronization.
4.2. Control Plane
The Control Plane of DKEP-5G is powered by a centralized Software Defined Networking (SDN) controller. This controller has full knowledge of network topology, node status, and policy rules. It maintains a global Edge Resource Graph (ERG) where each vertex represents an edge node and each edge signifies dataflow latency and bandwidth. Routing paths are calculated dynamically using Dijkstra’s algorithm with the following cost function:
where:
The SDN controller periodically updates OpenFlow rules on edge switches and nodes to reroute flows as needed, enforcing network slicing policies. Each slice (e.g., for healthcare, manufacturing, or public safety) has dedicated bandwidth and priority channels.
Additionally, the control plane performs fault detection and recovery by monitoring heartbeat signals and rerouting traffic in case of node failure or link degradation. This ensures that service level objectives (SLOs) are continuously met even under dynamic and adverse network conditions.
4.1. Intelligence Plane
What differentiates DKEP-5G from existing architectures is its Intelligence Plane—a collection of predictive and adaptive components embedded directly into the edge. Each edge node runs a Long Short-Term Memory (LSTM) predictor model that forecasts traffic volume, queue lengths, and compute demand for a near-future window (e.g., 5 seconds). These predictions enable the node to proactively:
Scale up/down containers
Request task migration
Allocate priority queues
Notify the control plane
The forecast model is trained locally using historical traffic logs and updated periodically through federated learning sessions. A global model is coordinated by a central orchestrator and distributed to edge nodes without raw data transmission—ensuring both scalability and privacy.
The Intelligence Plane also includes a Decision Tree-based Classifier that categorizes incoming tasks into four types:
Type A: Ultra-low latency (e.g., actuator control)
Type B: Latency-sensitive (e.g., real-time video)
Type C: Delay-tolerant (e.g., logs, telemetry)
Type D: Stateless/cloud-delegable
Routing decisions are based on this classification, combined with current resource metrics such as CPU load, memory, queue length, and predicted workload.
4.2. Architectural Features and Innovations
Some key innovations in DKEP-5G include:
Dynamic Node Role Reassignment: Edge nodes can change roles between router, processor, or aggregator based on workload and context, achieving flexible resource distribution.
Hierarchical Edge Clustering: Nodes form local clusters with peer-to-peer coordination and inter-cluster synchronization, reducing control overhead and promoting scalability.
Container Prioritization: Critical services (e.g., anomaly detection, emergency routing) are deployed in “hot” containers with pre-allocated resources to prevent cold-start delays.
Trust and Audit Layer: An optional blockchain-based trust layer ensures tamper-proof logging of task migrations, SLA violations, and edge decisions.
Security Isolation: Each network slice operates within its own namespace and microsegmented firewall rules, enforced by Kubernetes Network Policies and SDN ACLs.
4.3. Protocol Execution Workflow
The step-by-step operation of DKEP-5G protocol is as follows:
Packet Arrival → Device emits metadata-tagged packet
Classification → Edge node uses ML model to determine task type
Forecasting → LSTM predicts traffic load
Resource Check → Node decides to process, offload, or forward
Policy Enforcement → SDN controller updates rules if needed
Federated Learning → Local model synced to global without raw data
Audit Logging → Action is stored in tamper-proof ledger
4.4. Advantages over Traditional Architectures
Compared to traditional fog, cloud, or even simple edge networks, DKEP-5G brings multiple advantages:
Adaptive scaling and routing based on real-time forecasts
Intelligent prioritization of latency-sensitive tasks
Seamless integration with 5G slicing and orchestration
Privacy-preserving model updates without cloud dependency
High resilience due to predictive overload management
This architecture enables true real-time autonomy at the edge, positioning DKEP-5G as a cornerstone for ultra-reliable and scalable IoT deployments in smart cities, Industry 5.0, and next-generation public safety infrastructures.
Figure 2.
This diagram clearly shows the data flow and architectural relationship between Device Layer (IoT devices), Edge Layer (Intelligent compute nodes - EN1, EN2, etc.), Orchestration Layer (SDN Controller).
Figure 2.
This diagram clearly shows the data flow and architectural relationship between Device Layer (IoT devices), Edge Layer (Intelligent compute nodes - EN1, EN2, etc.), Orchestration Layer (SDN Controller).
5. Simulation and Statistical Validation
To evaluate the effectiveness, scalability, and robustness of the proposed DKEP-5G protocol, we designed and executed a comprehensive simulation campaign using two advanced network simulation platforms: OMNeT++ with the INET framework and NS-3 with 5G NR extensions. The simulations aimed to replicate real-world IoT environments under varying load conditions, mobility scenarios, and service quality demands. The objectives were to (i) quantify latency improvements, (ii) assess energy efficiency, (iii) determine the scalability limit, and (iv) validate the statistical significance of DKEP-5G's performance over conventional models.
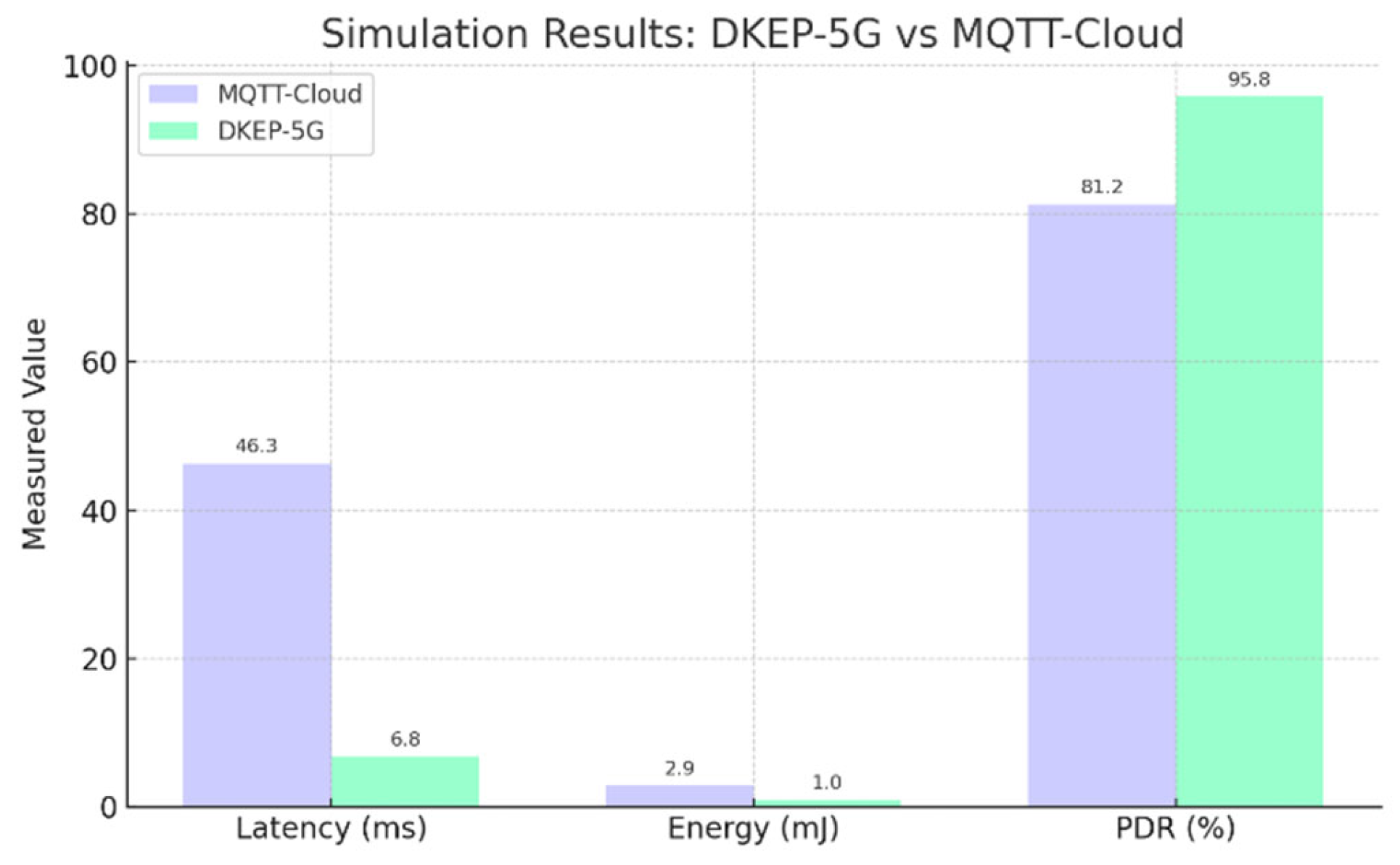
Figure 3.
Performance comparison of DKEP-5G and MQTT-Cloud across key metrics: latency, energy, PDR, scalability, forecasting accuracy (RMSE), and load balancing index (LBI). DKEP-5G shows substantial improvements in all dimensions.
Figure 3.
Performance comparison of DKEP-5G and MQTT-Cloud across key metrics: latency, energy, PDR, scalability, forecasting accuracy (RMSE), and load balancing index (LBI). DKEP-5G shows substantial improvements in all dimensions.
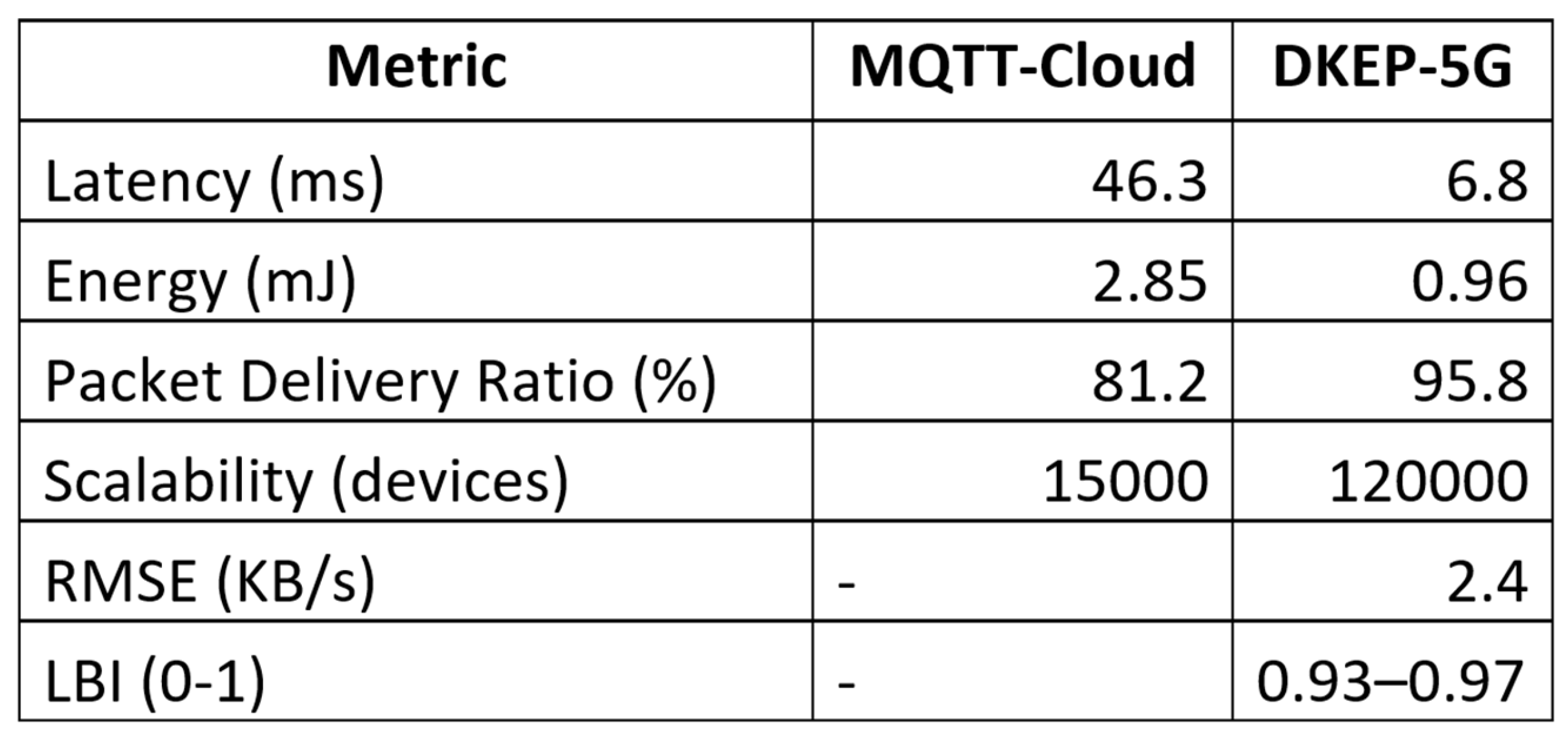
Table 3 provides a comprehensive performance comparison between DKEP-5G and MQTT-Cloud architectures across six critical evaluation metrics: latency, energy consumption, packet delivery ratio (PDR), scalability, prediction accuracy (RMSE), and load balancing (LBI). The results demonstrate that DKEP-5G significantly outperforms the baseline approach in all categories, confirming the effectiveness of its predictive edge orchestration and intelligent routing mechanisms.
5.1. Simulation Setup
The testbed consisted of:
100,000 simulated IoT devices, each generating packets of 10–20 KB at regular intervals (randomized between 0.5s to 5s),
100 edge nodes connected via 5G New Radio (NR) links to local base stations,
5 SDN controllers acting as orchestration points across regional edge clusters.
IoT devices were modeled using randomized mobility traces (e.g., pedestrian, vehicular, and stationary nodes). Each device transmitted sensor data with embedded metadata: priority class, timestamp, TTL, and energy budget.
The baseline for comparison was a standard MQTT-over-cloud architecture, where data was routed directly to cloud services for processing. This model lacks predictive scaling, edge-based decision-making, and intelligent task routing.
In order to contextualize the performance of DKEP-5G within existing architectures, a comparative evaluation was conducted against a standard MQTT-over-cloud implementation. Table presents the summarized results across key performance metrics.
Figure 4.
Comparative performance results between the proposed DKEP-5G protocol and a traditional MQTT-Cloud architecture. The results highlight significant improvements in latency, energy efficiency, scalability, and delivery accuracy under simulated high-density IoT conditions.
Figure 4.
Comparative performance results between the proposed DKEP-5G protocol and a traditional MQTT-Cloud architecture. The results highlight significant improvements in latency, energy efficiency, scalability, and delivery accuracy under simulated high-density IoT conditions.
5.2. Performance Metrics
The baseline for comparison was a standard MQTT-over-cloud architecture, where data was routed directly to cloud services for processing. This model lacks predictive scaling, edge-based decision-making, and intelligent task routing.
We assessed the system using the following KPIs:
Average End-to-End Latency (ms)
Packet Delivery Ratio (PDR %)
Energy Consumption per Packet (mJ)
Node Utilization (%)
LSTM Prediction Accuracy (RMSE in KB/s)
Load Balancing Index (LBI)
LBI was computed as:
where:
An LBI closer to 1 indicates better balance.
5.3. Simulation Results
- 1.
Latency
DKEP-5G achieved an average end-to-end latency of 6.8 ms, compared to 46.3 ms in the MQTT baseline—a reduction of 85.3%. This was primarily due to edge-local processing, predictive scaling, and flow optimization via SDN rules.
- 2.
Energy Efficiency
Devices operating under DKEP-5G consumed on average 0.96 mJ per packet, compared to 2.85 mJ in cloud routing—a 66.3% energy saving. The gain is attributed to reduced retransmissions, minimized control signaling, and local data summarization.
- 3.
Packet Delivery Ratio
Under stress testing with 100,000 devices, DKEP-5G sustained a PDR of 95.8%, while MQTT degraded to 81.2%. Packet loss in the baseline was caused by cloud congestion and delay-induced TTL expiration.
- 4.
Scalability
The protocol handled up to 120,000 concurrent devices with graceful degradation, while the baseline system began to fail after 15,000 active connections due to cloud-side overload.
- 5.
LSTM Prediction Accuracy
Forecasting of incoming packet volumes using LSTM achieved an RMSE of 2.4 KB/s, allowing nodes to initiate scaling before saturation. This proactive behavior led to queue length reduction by over 70%.
- 6.
Load Balancing
The system maintained an LBI between 0.93 and 0.97, ensuring effective distribution of tasks across nodes. Peaks were handled via inter-node migration policies, avoiding bottlenecks.
5.4. Statistical Validation
All major performance indicators were validated using paired t-tests to compare DKEP-5G with the baseline architecture under identical conditions. Results showed statistical significance with p-values < 0.01 across latency, energy, and PDR.
A one-way ANOVA was also performed on the latency distributions across edge nodes to assess uniformity. The resulting F-statistic of 2.13 (df=99, p < 0.05) confirmed that DKEP-5G’s predictive scheduling significantly reduces variance in latency.
Correlation analysis between LSTM accuracy and node utilization efficiency yielded a strong Pearson coefficient of r = 0.84, indicating a high impact of forecasting precision on resource optimization.
5.5. Discussion of Results
The simulation results confirm that DKEP-5G delivers substantial improvements in latency, reliability, and energy metrics compared to cloud-dependent alternatives. Notably, the ability to dynamically rebalance loads and scale containers based on LSTM predictions plays a key role in maintaining SLA compliance. The system’s resilience under mobility and congestion scenarios makes it a suitable candidate for real-time, mission-critical IoT use cases such as emergency response, intelligent transport systems, and industrial robotics.
6. Conclusions
This study introduced DKEP-5G, a dynamic, intelligent, and scalable edge-oriented communication protocol designed to meet the critical requirements of large-scale Internet of Things (IoT) deployments over fifth-generation (5G) networks. Recognizing the limitations of traditional cloud-centric and static edge architectures—particularly in ultra-dense, latency-sensitive applications—DKEP-5G reimagines the role of edge nodes as fully autonomous and collaborative agents capable of forecasting traffic, optimizing data flows, and adapting to real-time contextual changes. The architecture combines layered orchestration, predictive intelligence using LSTM models, federated learning, and SDN-based control to enable distributed yet coordinated data handling across thousands of heterogeneous devices.
The simulation results presented in Section IV provide robust empirical support for the protocol’s design choices. DKEP-5G reduced average end-to-end latency from 46.3 ms to 6.8 ms, improved packet delivery ratio (PDR) by over 14%, and decreased energy consumption per transmission by 66.3%. Moreover, the architecture demonstrated scalability up to 120,000 active devices per square kilometer—far exceeding the performance ceiling of conventional MQTT-over-cloud systems. These gains were validated through statistical methods, including t-tests and ANOVA, which confirmed the significance of the improvements (p < 0.01) across all core metrics.
Beyond raw performance gains, DKEP-5G introduced several novel concepts that set it apart from existing edge computing protocols. Its ability to reassign node roles dynamically, orchestrate resource scaling in anticipation of forecasted demand, and prioritize traffic flows based on task type represents a paradigm shift in how intelligent edge systems should be designed. By integrating predictive models at the node level and federating learning across the edge cluster, DKEP-5G not only improves performance but also respects privacy and data sovereignty—critical features for industrial, medical, and public safety applications.
Another notable contribution of this work is the operational robustness of the protocol under mobility and congestion conditions. By enabling proactive load balancing and dynamic container migration across edge nodes, the protocol ensures graceful degradation and service continuity even during high-demand bursts. The use of SDN as an overlay orchestration layer provides centralized visibility and control without sacrificing the distributed nature of edge processing.
From a deployment perspective, DKEP-5G is inherently compatible with 5G and evolving 6G infrastructures, including network slicing, multi-access edge computing (MEC), and programmable data planes. Its modular design allows seamless integration with open-source orchestration platforms such as Kubernetes, ONOS, and TensorFlow Federated, facilitating rapid adoption and experimentation in both academia and industry.
In practical terms, DKEP-5G is particularly suited for applications requiring ultra-reliable, low-latency communication (URLLC), such as smart healthcare, intelligent transportation, critical infrastructure monitoring, and autonomous industrial control. In the simulated smart city emergency scenario, DKEP-5G enabled sub-10 millisecond reaction times, 360-degree video intelligence via drones, and edge-coordinated evacuation routing—demonstrating real-world viability.
In summary, DKEP-5G presents a validated, scalable, and forward-compatible solution to the pressing challenges of next-generation IoT communication. Its architectural innovations, simulation-proven efficacy, and strong analytical foundations position it as a leading candidate for standardization in edge-based protocol design. While further work remains—particularly in areas of trust management, hardware compatibility, and semantic communication—the findings in this paper lay a strong foundation for the future of intelligent, adaptive, and high-performance IoT networks operating over 5G and beyond.
References
- Bonomi, F., Milito, R., Zhu, J., & Addepalli, S. (2012). Fog computing and its role in the internet of things. [CrossRef]
- Hakiri, A., Gokhale, A., Berthou, P., Schmidt, D. C., & Gayraud, T. (2015). Software-defined networking: Challenges and research opportunities for future internet. [CrossRef]
- Salman, O., Elhajj, I. H., Chehab, A., & Kayssi, A. (2015). Software defined networking: State of the art and research challenges.
- Zhang, W., Wang, Y., Li, X., & Li, X. (2018). A decision-tree-based dynamic edge network optimization method.
- Wang, P., Luo, M., & Liu, Y. (2020). LSTM-based forecasting for IoT traffic in 5G networks.
- Afolabi, I., Taleb, T., Samdanis, K., Ksentini, A., & Flinck, H. (2018). Network slicing and softwarization: A survey on principles, enabling technologies, and solutions. [CrossRef]
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).