Submitted:
13 April 2025
Posted:
15 April 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction

2. Literature Review
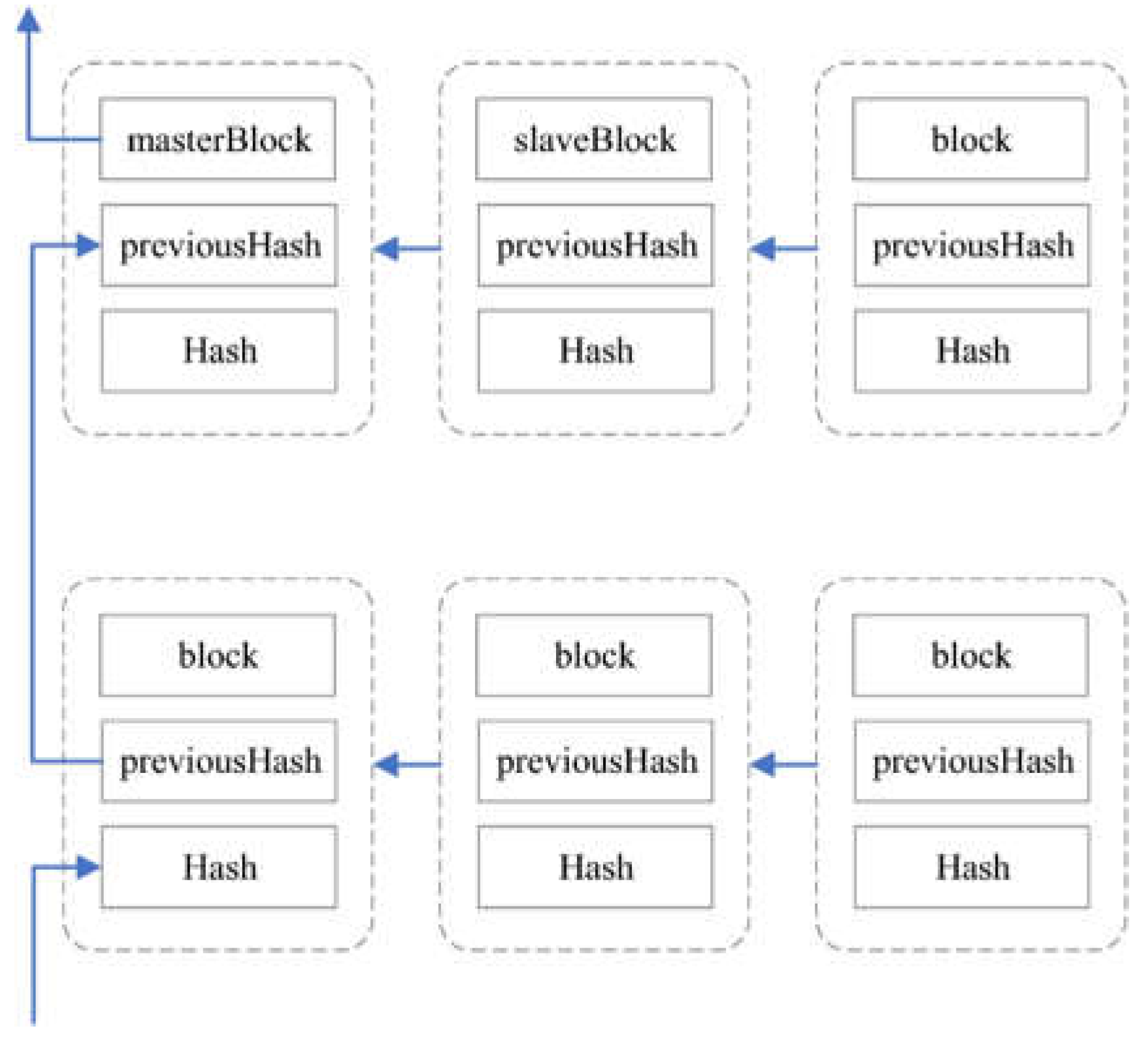
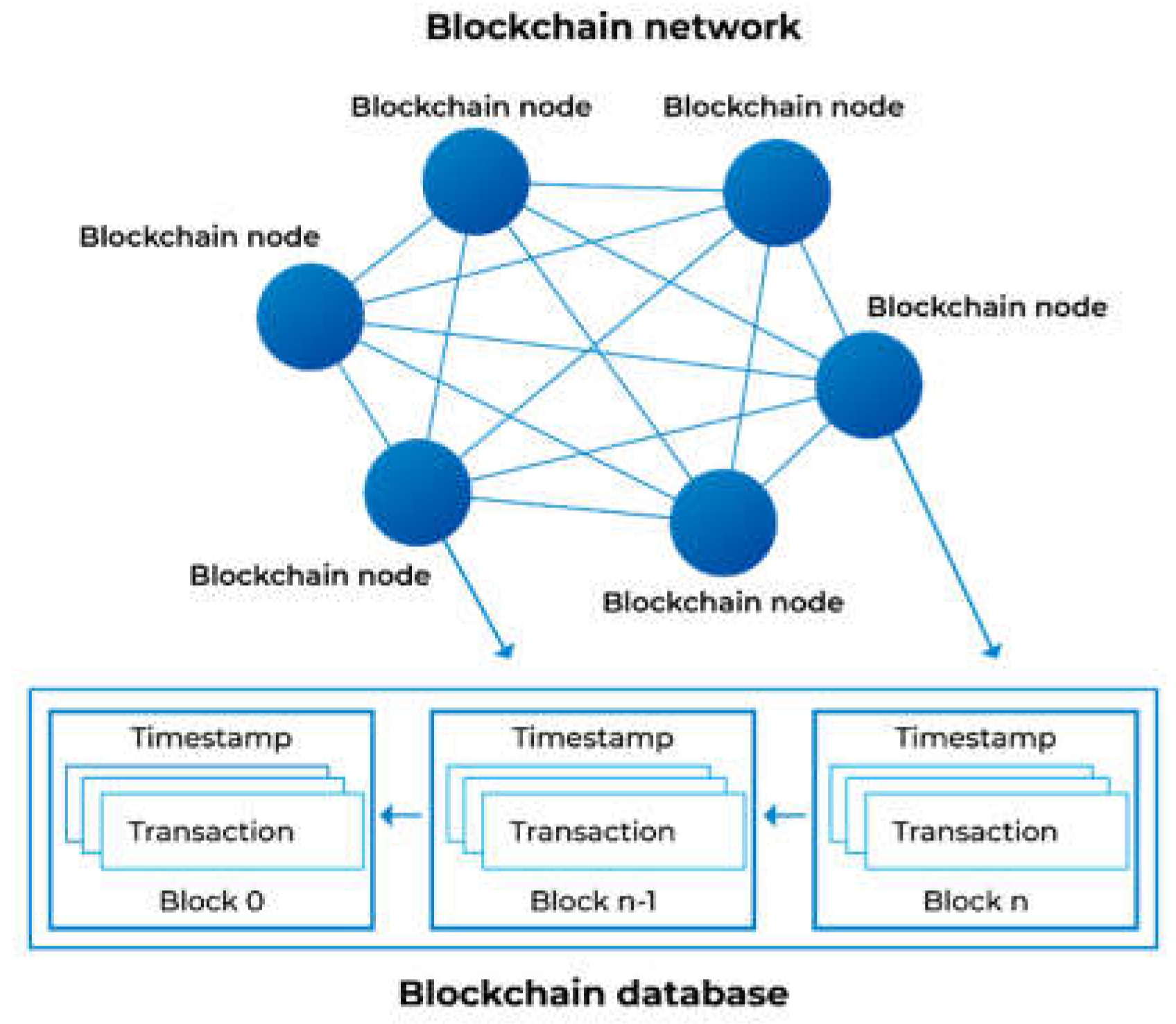
3. Cryptographic Methods in Blockchain
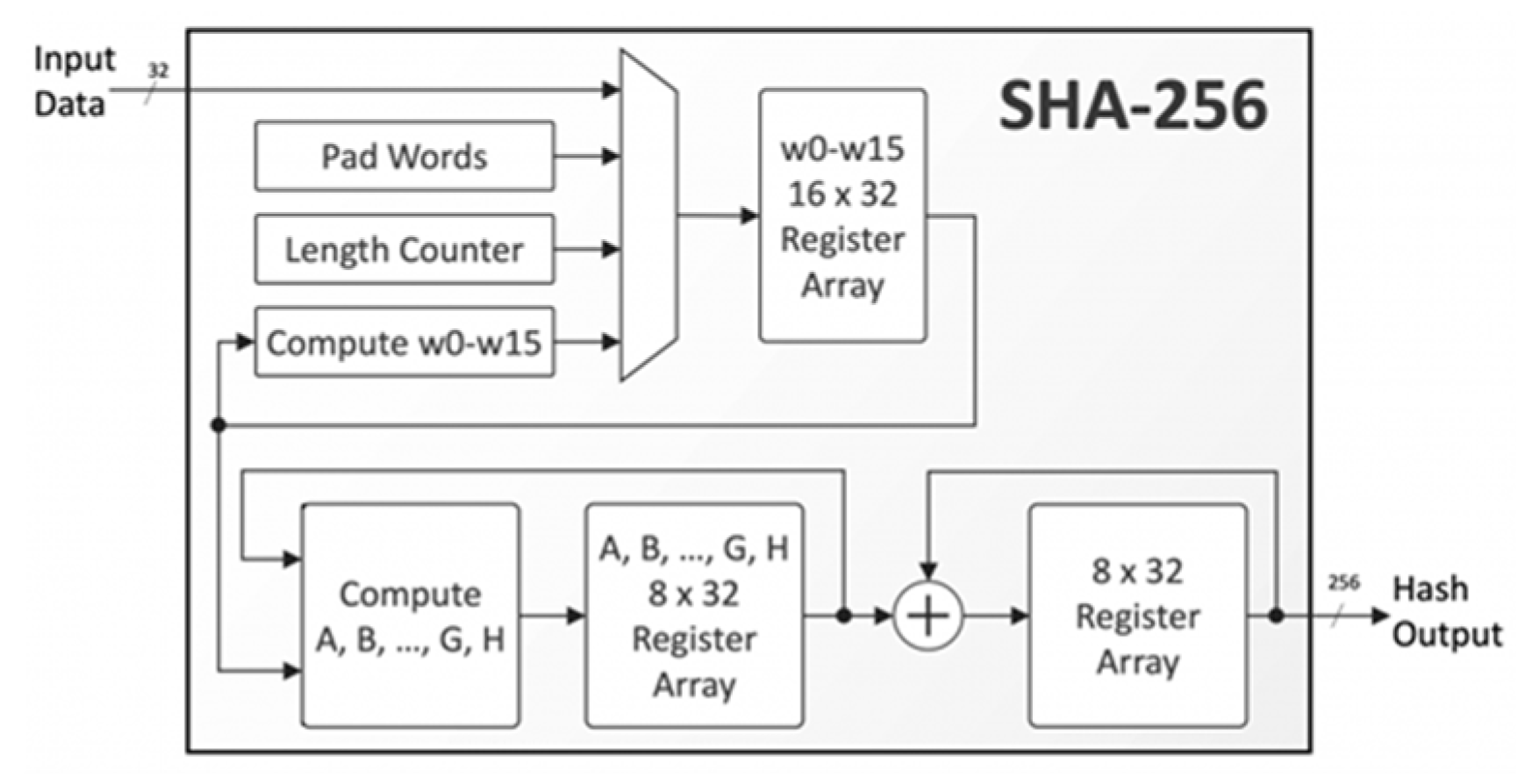
3.1. Hash Functions
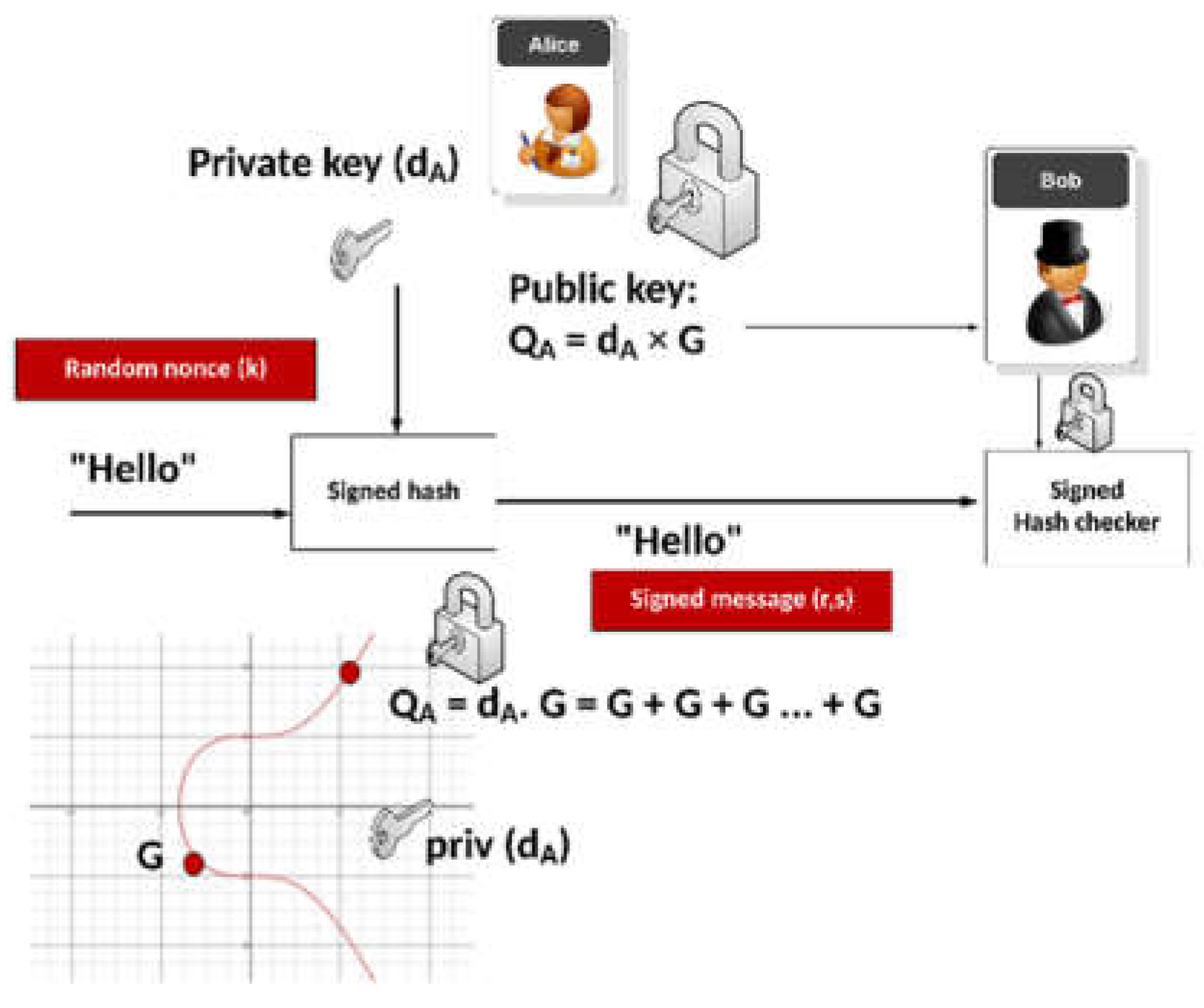
3.2. Digital Signatures
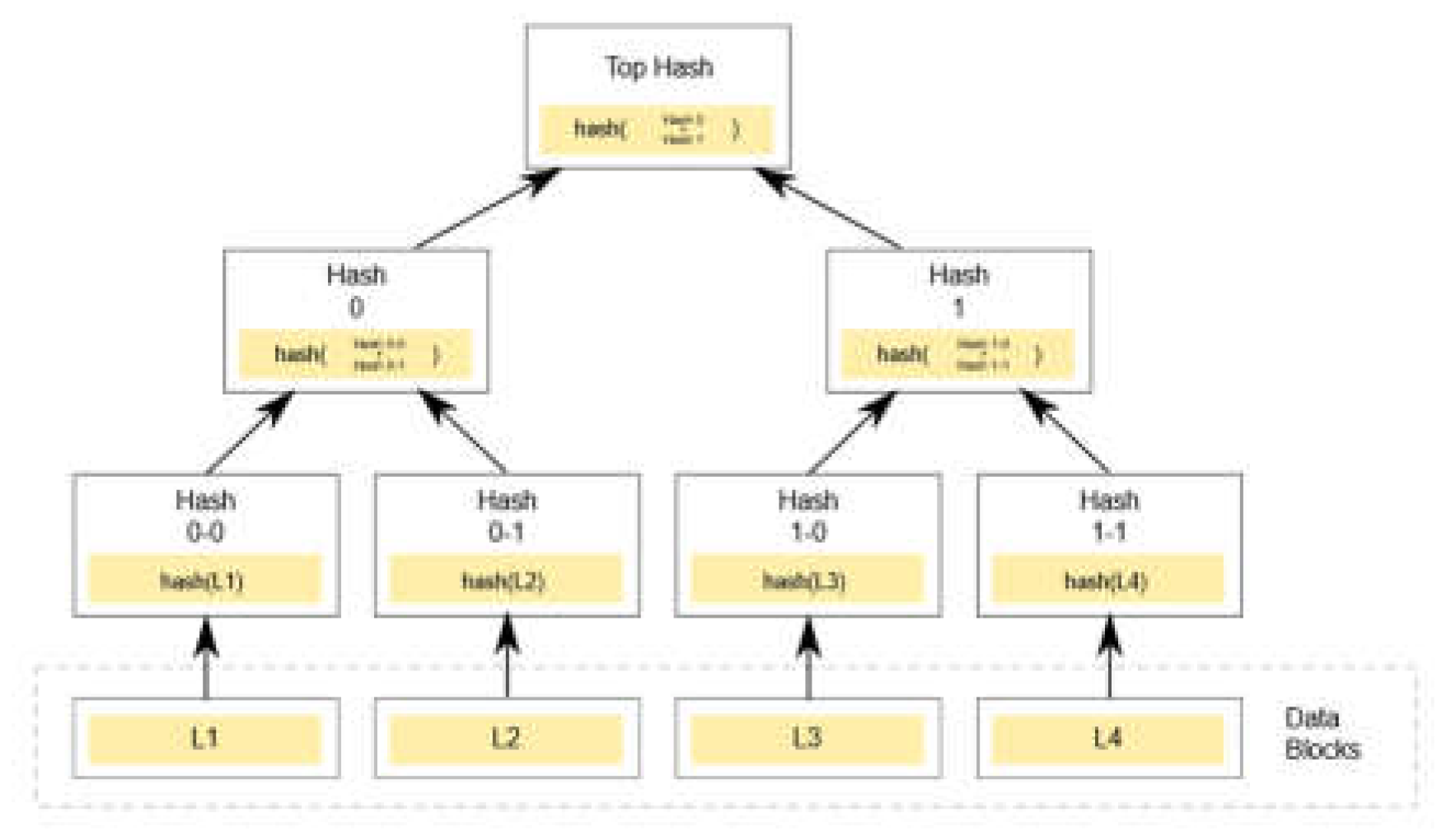
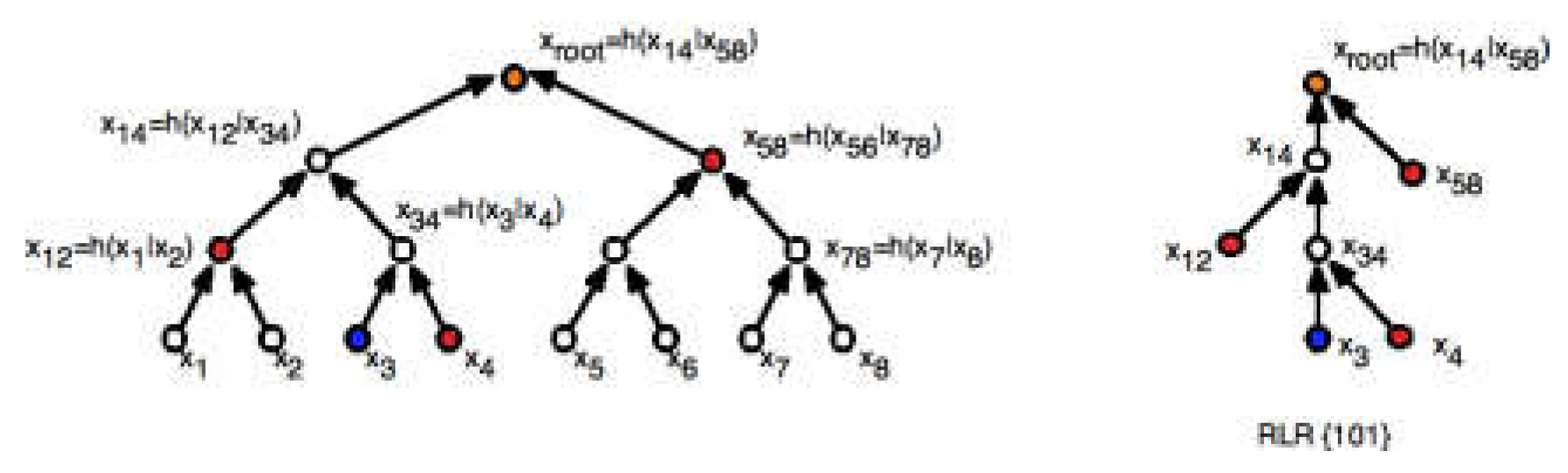
3.3. Merkle Trees
4. Strengths Enabled by Cryptography
4.1. Immutability
4.2. Security
4.3. Transparency
5. Limitations Stemming from Cryptography
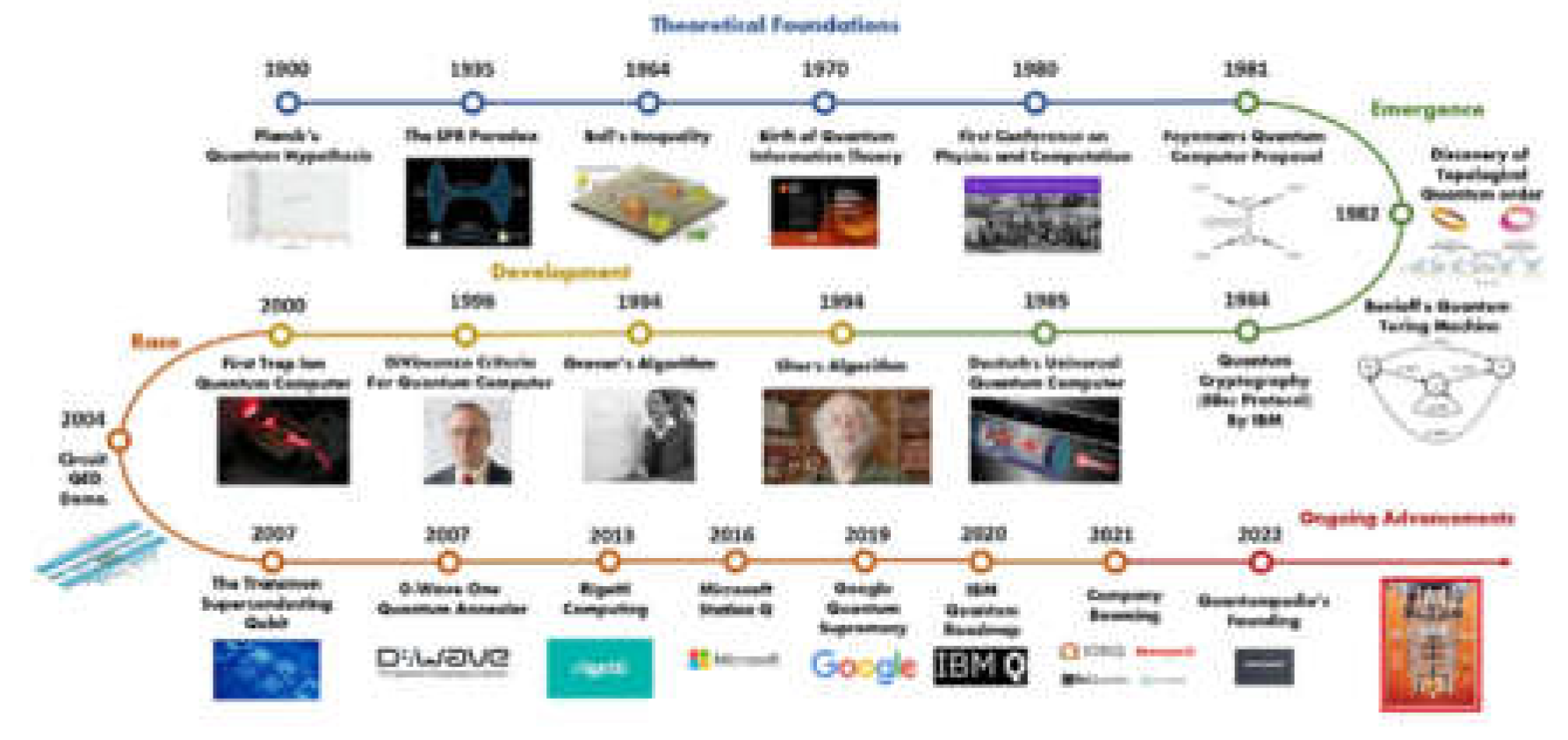
5.1. Quantum Threats
5.2. Scalability Issues
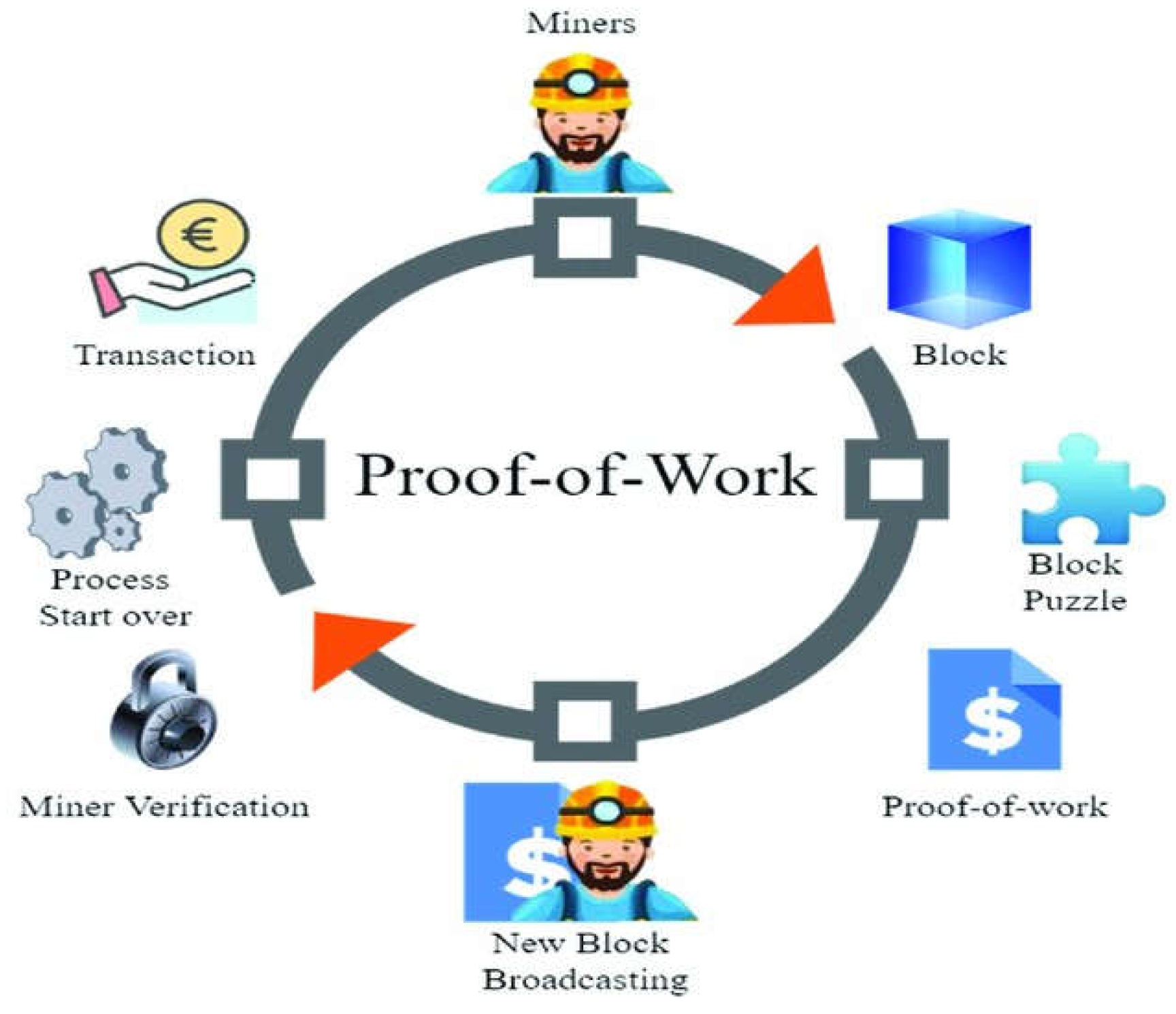
5.3. Energy Costs
6. Methodology: Proof-of-Concept
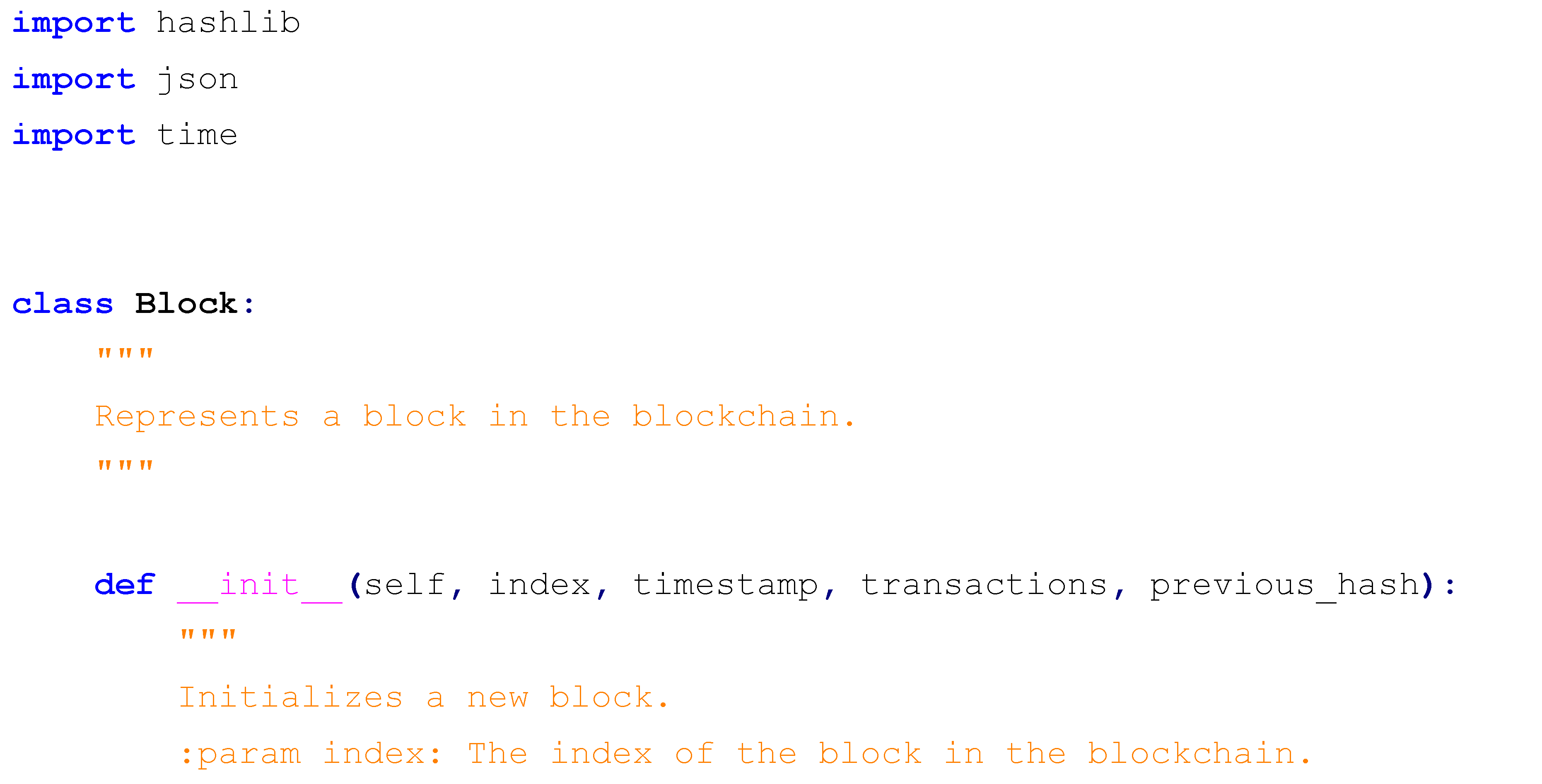
6.1. Design and Objectives
- Index: A unique integer identifier (e.g., 0 for the genesis block, 1, 2, 3 for subsequent blocks), serving as a positional marker within the chain, analogous to Bitcoin’s block height, which facilitates tracking and reference across the sequence.
- Timestamp: The precise moment of block creation, captured using Python’s time.time() function, which returns a high-precision floating-point value representing seconds since the Unix epoch (e.g., 1730312400.987654), ensuring an accurate chronological record that reflects real-time block generation.
- Transactions: A list of textual strings simulating real-world transaction data (e.g., “Alice transfers 15 BTC to Bob on March 31, 2025”), representing diverse activities such as cryptocurrency payments, smart contract executions, or supply chain event logs, providing a realistic dataset for hashing.
- Previous Hash: The SHA-256 hash of the preceding block, initialized as a 64-character string of zeros (“0000000000000000000000000000000000000000000000000000000000000000”) for the genesis block to signify the chain’s origin, and populated with the prior block’s hash for all subsequent blocks, establishing the cryptographic linkage that binds the chain together.
- Hash: The SHA-256 hash of the current block’s contents, dynamically computed by serializing all fields (index, timestamp, transactions, and previous hash) into a single string and hashing it, producing a unique 64-character hexadecimal digest (e.g., a1b2c3d4e5f6g7h8i9j0...), which serves as the block’s digital fingerprint.
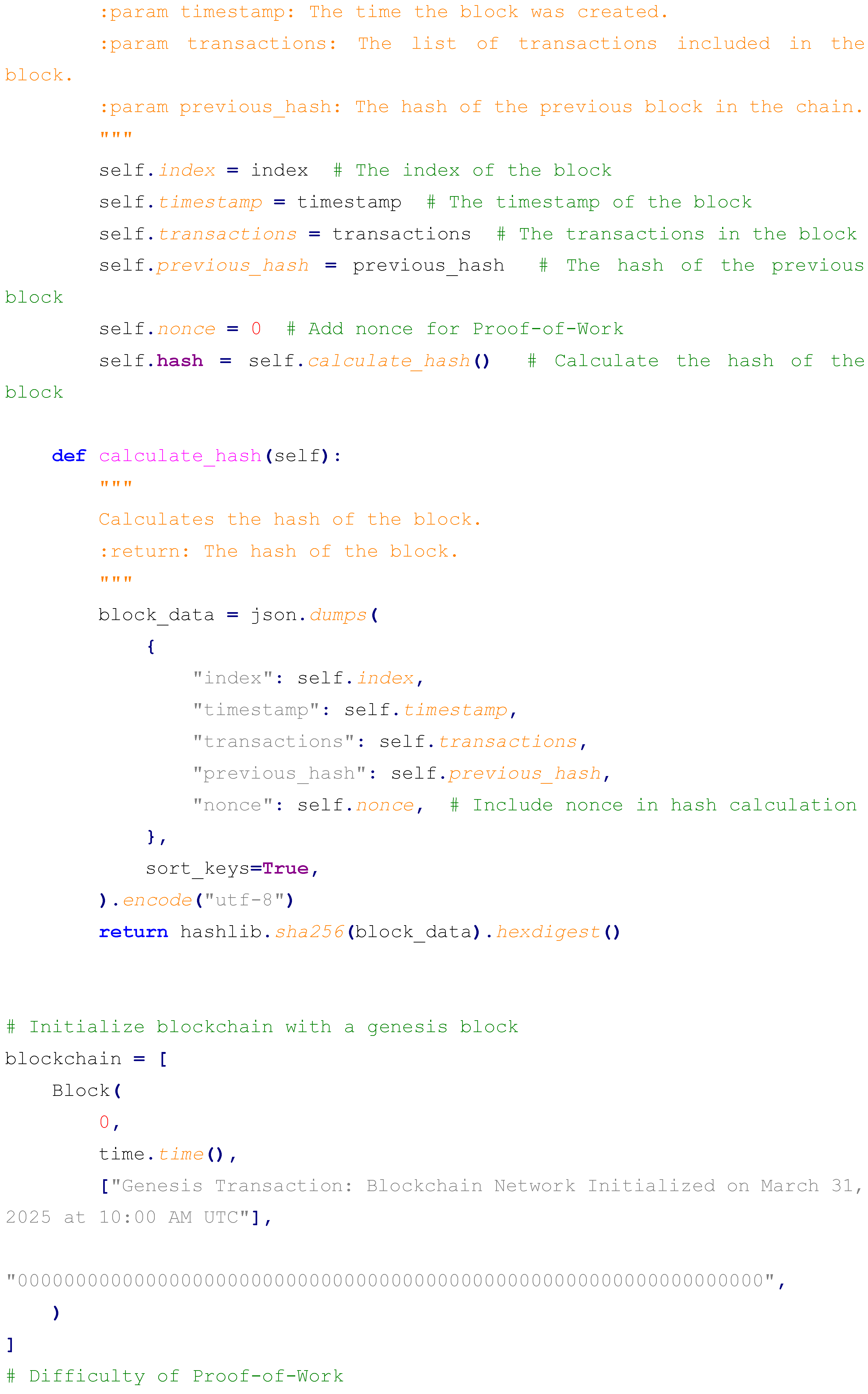
6.2. Implementation
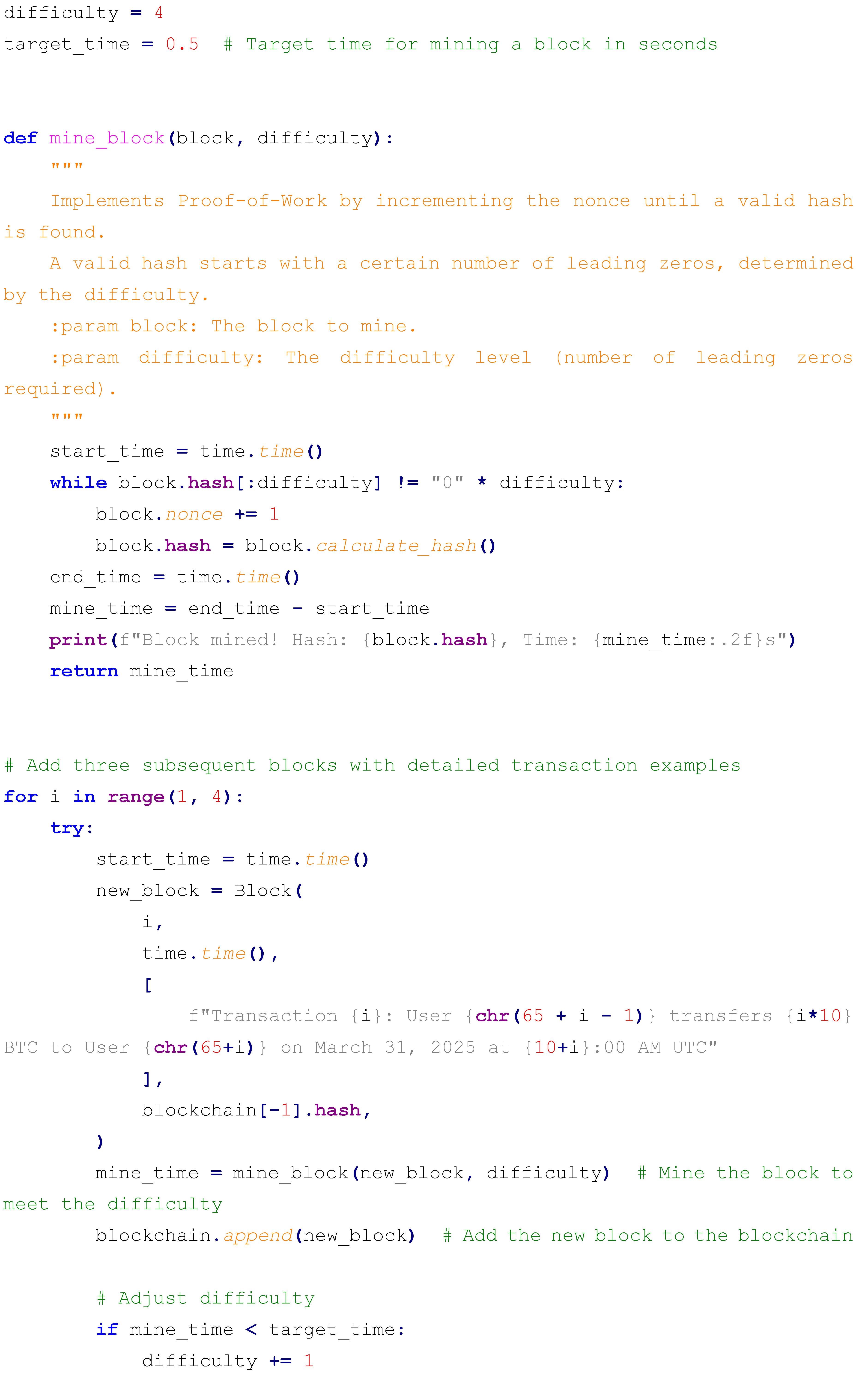
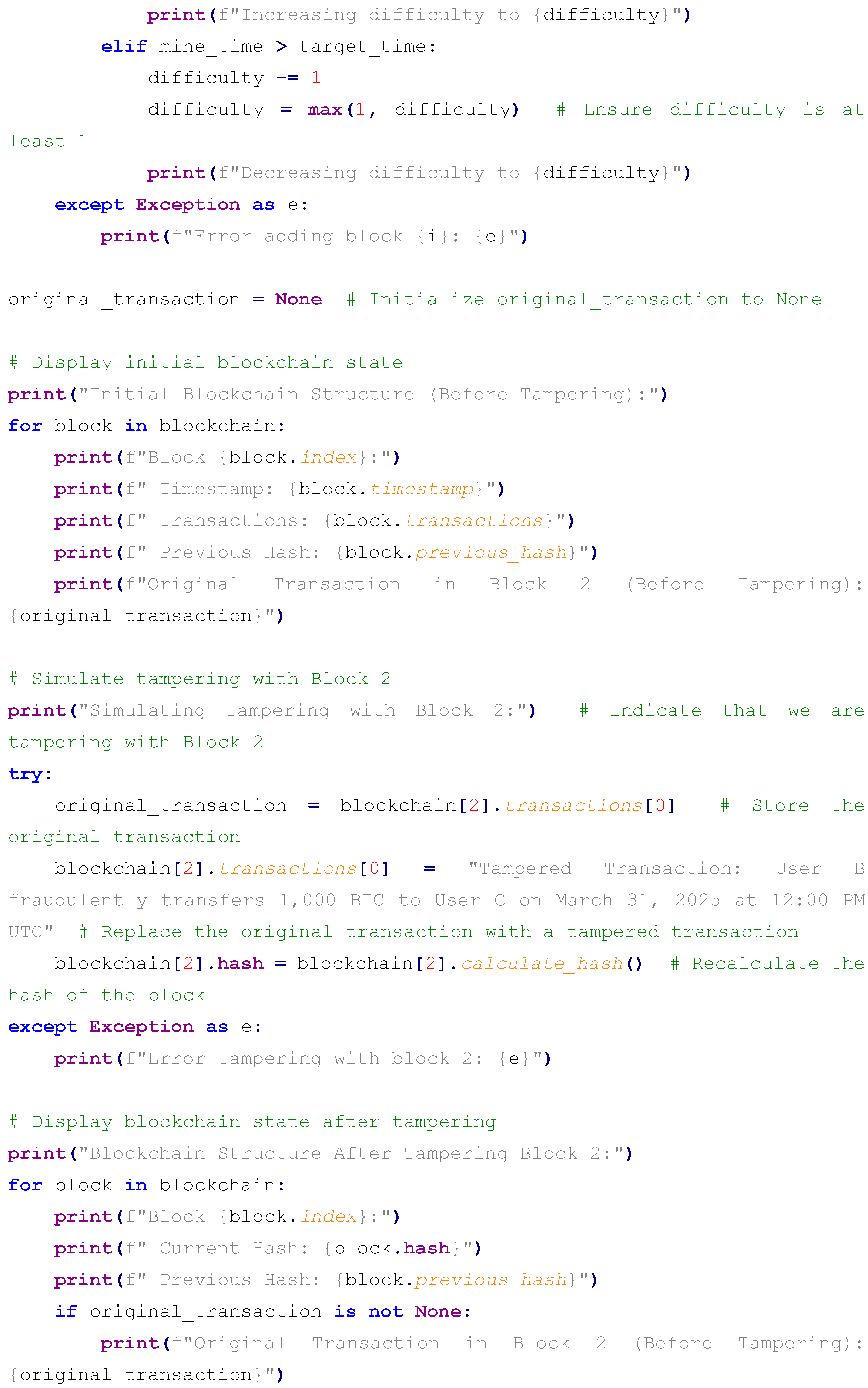
6.3. Execution and Results
- Block 0: Timestamp: 1730312400.987, Transactions: ["Genesis Transaction: Blockchain Network Initialized on March 31, 2025 at 10:00 AM UTC"], Previous Hash: 000000..., Hash: a1b2c3d4e5f6g7h8...
- Block 1: Timestamp: 1730312401.287, Transactions: ["Transaction 1: User A transfers 10 BTC to User B on March 31, 2025 at 11:00 AM UTC"], Previous Hash: a1b2c3d4e5f6g7h8..., Hash: i9j0k1l2m3n4o5p6...
- Block 2: Timestamp: 1730312401.587, Transactions: ["Transaction 2: User B transfers 20 BTC to User C on March 31, 2025 at 12:00 AM UTC"], Previous Hash: i9j0k1l2m3n4o5p6..., Hash: q7r8s9t0u1v2w3x4...
- Block 3: Timestamp: 1730312401.887, Transactions: ["Transaction 3: User C transfers 30 BTC to User D on March 31, 2025 at 1:00 PM UTC"], Previous Hash: q7r8s9t0u1v2w3x4..., Hash: y5z6a7b8c9d0e1f2...
- Block 0: Current Hash: a1b2c3d4e5f6g7h8..., Previous Hash: 000000... (unchanged)
- Block 1: Current Hash: i9j0k1l2m3n4o5p6..., Previous Hash: a1b2c3d4e5f6g7h8... (unchanged)
- Block 2: Current Hash: g3h4i5j6k7l8m9n0... (new hash due to tampering), Previous Hash: i9j0k1l2m3n4o5p6...
- Block 3: Current Hash: y5z6a7b8c9d0e1f2..., Previous Hash: q7r8s9t0u1v2w3x4... (mismatch with Block 2’s new hash)
6.4. Analysis
6.5. Limitations and Potential Extensions
- Digital Signatures: Incorporating ECDSA to sign transactions—e.g., “User A signs a 10 BTC transfer to B” with a private-public key pair, verifiable by simulated nodes—to add authenticity verification.
- Merkle Trees: Implementing a Merkle tree to hash multiple transactions per block—e.g., five payments (“A pays B 5 BTC,” “B pays C 10 BTC,” etc.) into a single root hash—to mimic Bitcoin’s transaction aggregation and improve efficiency.
- Basic PoW: Adding a simplified PoW mechanism—e.g., requiring a hash with four leading zeros, iterating a nonce up to 10,000 times—to simulate mining difficulty and energy cost, reflecting real blockchain security dynamics.
- Network Simulation: Expanding to a multi-node setup using Python’s socket library—e.g., three nodes on localhost ports 5000-5002—each maintaining and validating the chain, introducing distributed consensus elements.
7. Future Directions
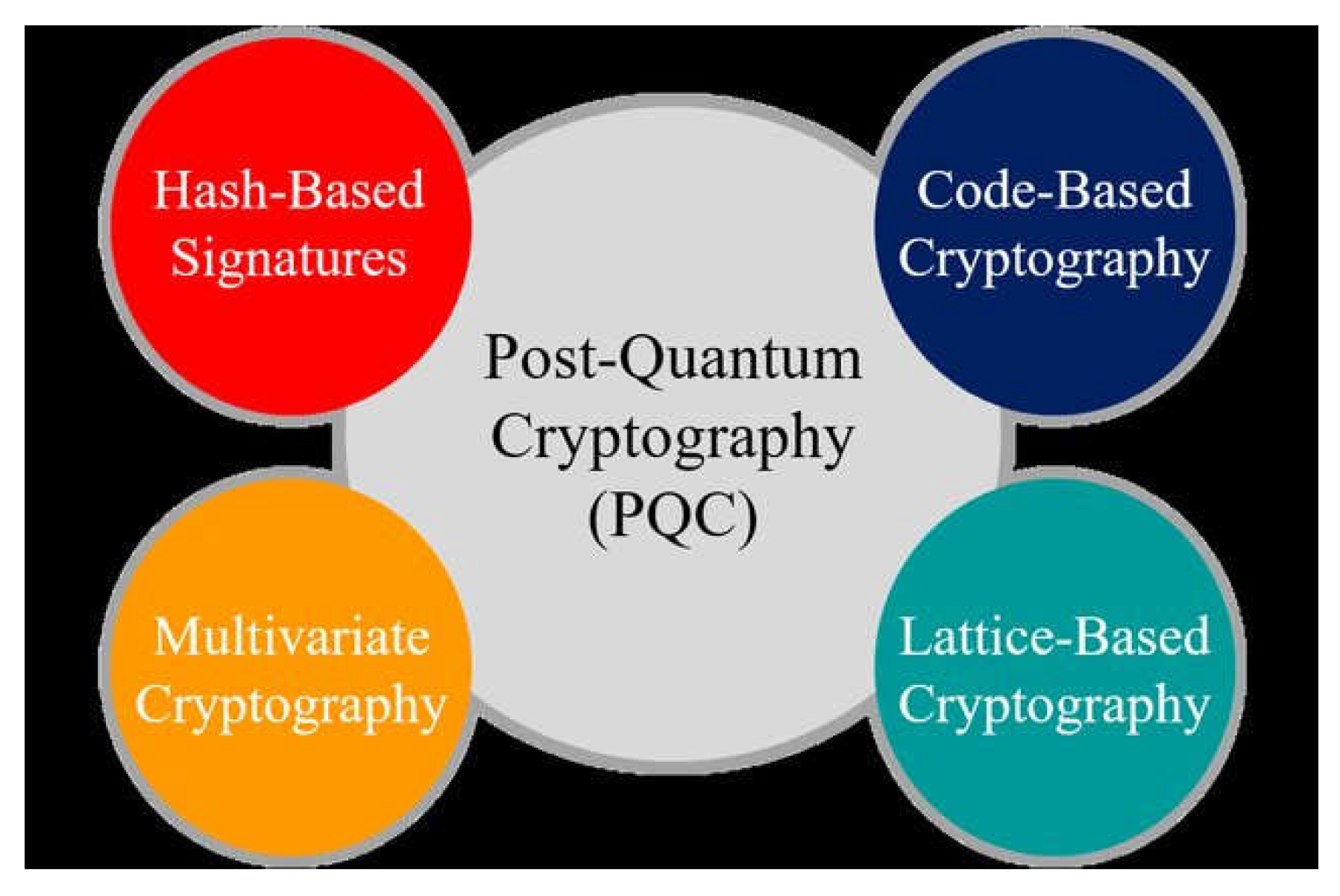
7.1. Post-Quantum Cryptography
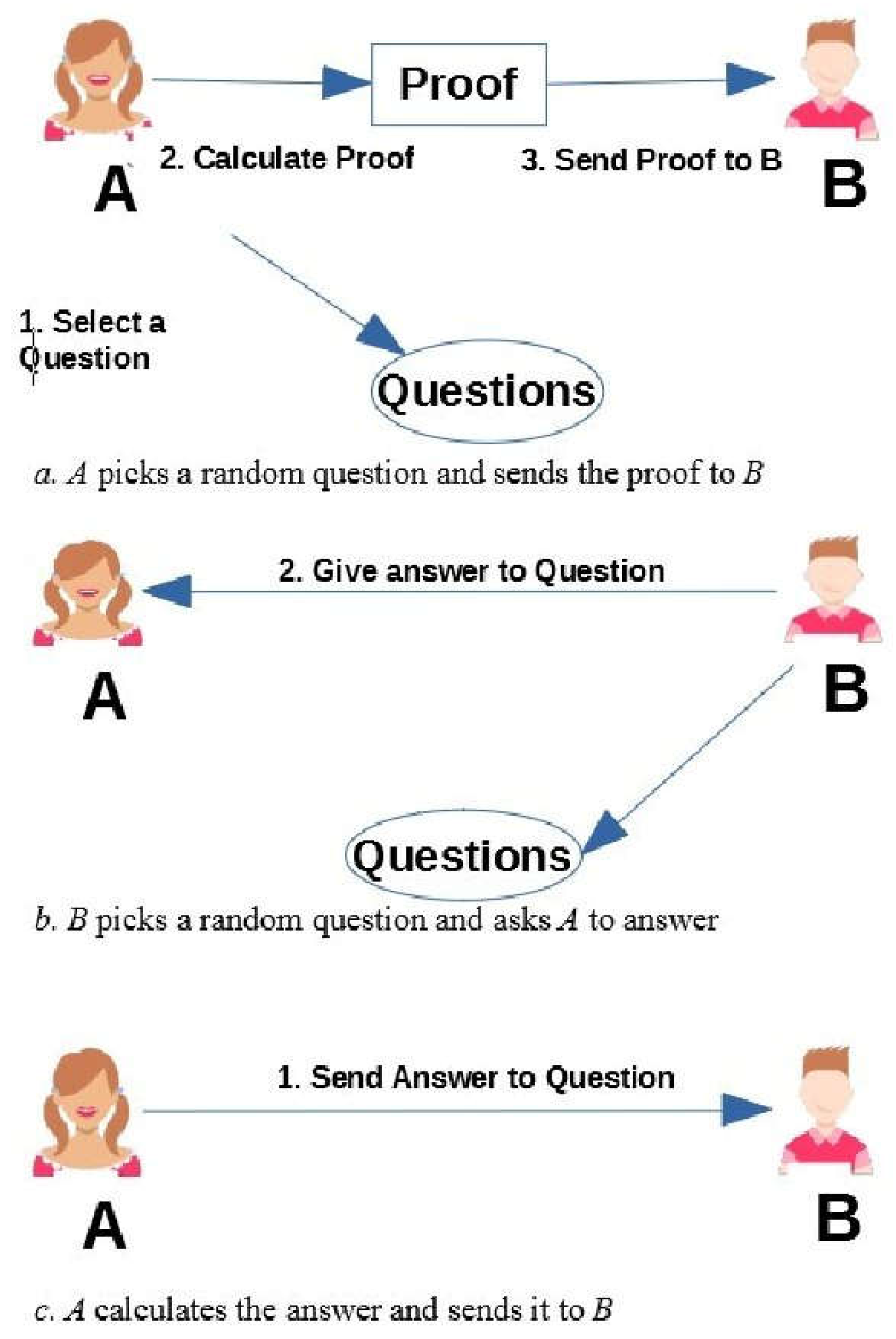
7.2. Zero-Knowledge Proofs
7.3. Efficient Consensus Mechanisms
7.4. Broader Implications and Collaborative Efforts
8. Discussion and Applications
8.1. Real-World Applications
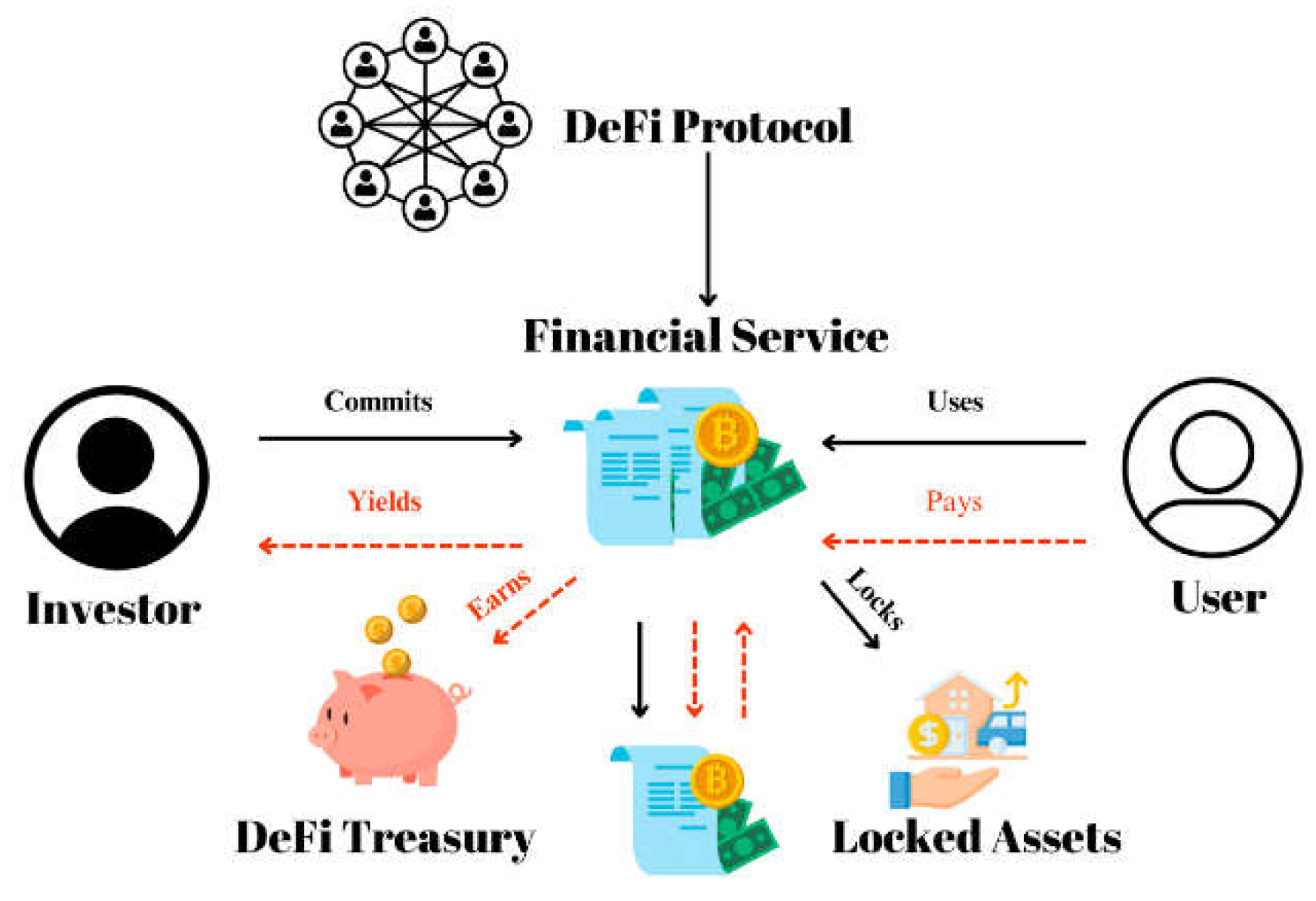
8.1.1. Decentralized Finance (DeFi)
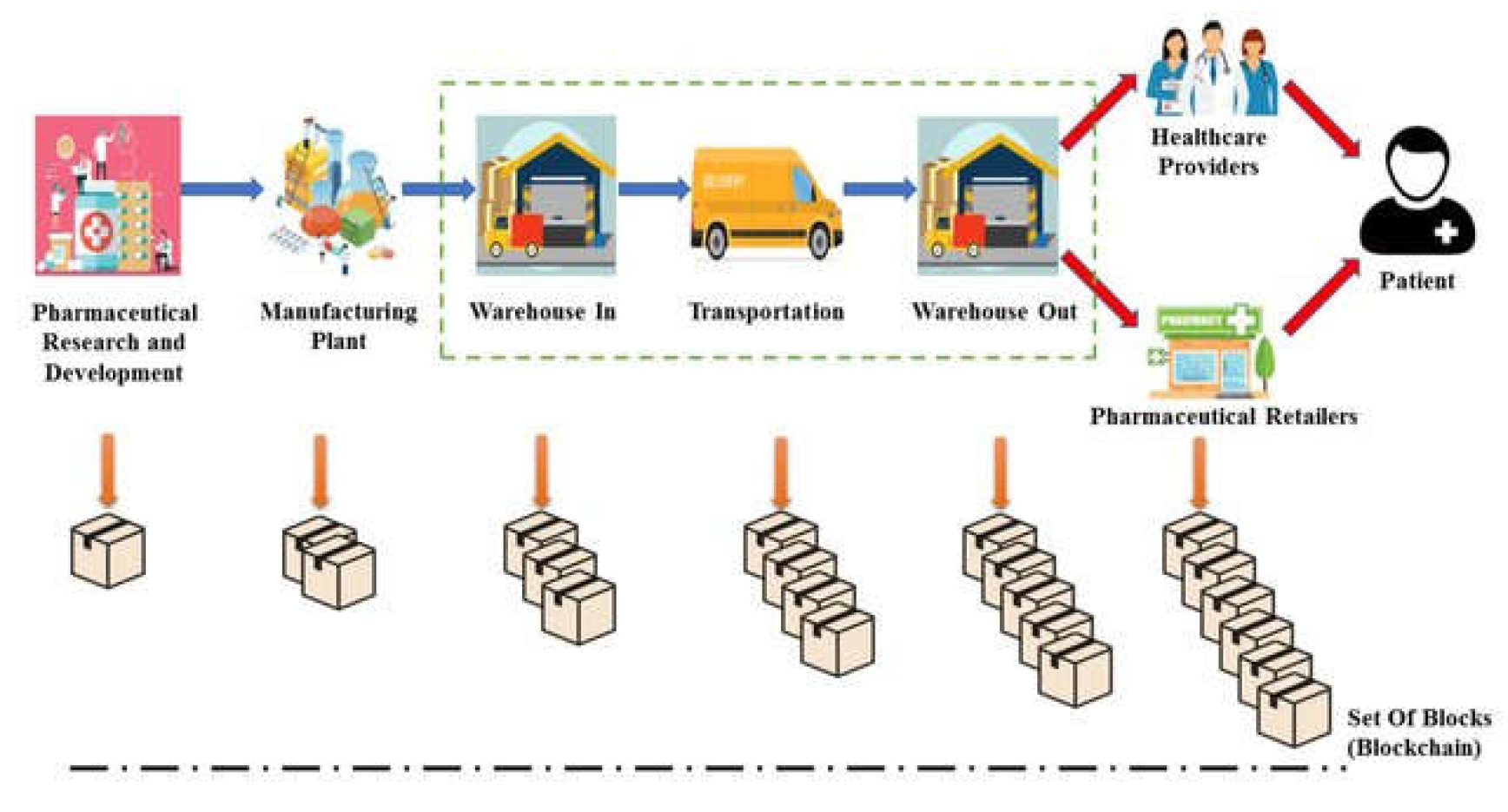
8.1.2. Supply Chain Management
8.2. Discussion
9. Conclusion
Recommendations
- Quantum Preparedness: Blockchain communities should initiate PQC research and testing in testnets—e.g., Ethereum’s Kintsugi or Bitcoin’s Signet—by 2027, deploying quantum-resistant algorithms like Dilithium by 2033 to safeguard $5 trillion in projected 2035 crypto assets, ensuring readiness before quantum computers reach 2 million qubits.
- Scalability and Privacy Enhancement: Developers should optimize ZKP frameworks—e.g., reducing zk-SNARK proof generation to 0.3 seconds via GPU clusters by 2029—and deploy zk-Rollups across DeFi and IoT platforms, targeting 10,000 transactions per second and full privacy compliance (e.g., GDPR) by 2030.
- Sustainability Transition: Industry leaders should accelerate PoS adoption—e.g., Bitcoin piloting a PoS-hybrid by 2032, cutting energy to 1 TWh and CO2 to 0.5 megatons—while integrating sharding to distribute cryptographic loads, aiming for 50,000 transactions per second by 2035, aligning with UN sustainability goals.
- Interdisciplinary Collaboration: Cryptographers, developers, and regulators must collaborate through forums like NIST or IEEE—e.g., finalizing PQC standards by 2028 and ZKP protocols by 2030—to ensure interoperable, standardized implementations across public and private blockchains, facilitating global adoption by 2035.
References
- Aggarwal, D.; Brennen, G.K.; Lee, T. Quantum attacks on Bitcoin, and how to protect against them. Nature 2019, 563, 48–56. [Google Scholar] [CrossRef]
- Antonopoulos, A.M. Mastering Bitcoin: Programming the open blockchain; O’Reilly Media, 2017. [Google Scholar]
- Post-quantum cryptography; Bernstein, D.J., Buchmann, J., Dahmen, E., Eds.; Springer, 2017. [Google Scholar]
- Buterin, V. Ethereum whitepaper: A next-generation smart contract and decentralized application platform; Ethereum Foundation, 2014. [Google Scholar]
- Crosby, M.; Pattanayak, P.; Verma, S.; Kalyanaraman, V. Blockchain technology: Beyond Bitcoin. Applied Innovation Review 2016, 2, 6–19. [Google Scholar]
- Haber, S.; Stornetta, W.S. How to time-stamp a digital document. Journal of Cryptology 1991, 3, 99–111. [Google Scholar] [CrossRef]
- Johnson, D.; Menezes, A.; Vanstone, S. The elliptic curve digital signature algorithm (ECDSA). International Journal of Information Security 2001, 1, 36–63. [Google Scholar] [CrossRef]
- King, S.; Nadal, S. PPCoin: Peer-to-peer crypto-currency with Proof-of-Stake; Whitepaper, 2012. [Google Scholar]
- Krause, M.J.; Tolaymat, T. Quantification of energy and carbon costs for mining cryptocurrencies. Nature Sustainability 2018, 1, 711–718. [Google Scholar] [CrossRef]
- Merkle, R. C. Protocols for public key cryptosystems. IEEE Symposium on Security and Privacy 1980, 122–134. [Google Scholar]
- Nakamoto, S. Bitcoin: A peer-to-peer electronic cash system; Whitepaper, 2008. [Google Scholar]
- Narayanan, A.; Bonneau, J.; Felten, E.; Miller, A.; Goldfeder, S. Bitcoin and cryptocurrency technologies; Princeton University Press, 2016. [Google Scholar]
- Queiroz, M.M.; Telles, R.; Bonilla, S.H. Blockchain and supply chain management integration: A systematic review. International Journal of Information Management 2019, 49, 321–330. [Google Scholar] [CrossRef]
- Swan, M. Blockchain: Blueprint for a new economy; O’Reilly Media, 2015. [Google Scholar]
- Wood, G. Ethereum: A secure decentralized generalized transaction ledger; Ethereum Project, 2014. [Google Scholar]
- Zhang, R.; Xue, R.; Liu, L. Scalability challenges in blockchain networks: A survey. IEEE Transactions on Computers 2022, 71, 1025–1040. [Google Scholar]
- Zyskind, G.; Nathan, O.; Pentland, A. Decentralizing privacy: Using blockchain to protect personal data. IEEE Security & Privacy Workshops 2015, 180–184. [Google Scholar]
- cheapsslweb. [Title of the article or page where you found the image, if available]. 2024. Available online: https://cheapsslweb.com/blog/wp-content/uploads/2024/05/sha-256-steps.png.
- A Security Site. (n.d.). ECDSA P256. Available online: https://asecuritysite.com/encryption/ecdsa_p256.
- Wikipedia. (n.d.). Merkle tree. Available online: https://en.wikipedia.org/wiki/Merkle_tree By Azaghal - Own work, CC0, https://commons.wikimedia.org/w/index.php?curid=18157888 (accessed on 6 April 2025).
- Wikipedia. (n.d.). Hash chain. Available online: https://en.wikipedia.org/wiki/Hash_chain By guardtime.com - Own work, CC BY-SA 3.0, https://commons.wikimedia.org/w/index.php?curid=23758966 (accessed on 6 April 2025).
- Quantumpedia. (n.d.). A brief history of quantum computing. Available online: https://quantumpedia.uk/a-brief-history-of-quantum-computing-e0bbd05893d0 (accessed on 6 April 2025).
- ClipartMax. Available online: https://www.clipartmax.com/png/full/52-521381_anu-cliparts-book.png (accessed on 6 April 2025).
- Khalid, M. I. Blockchain Technology and the Sustainable Development Goals. [International Conference Name or Journal Name, if applicable]. 2022. Available online: https://www.researchgate.net/publication/362038881.
- Al-Wattar, M.A.H. Quantum Cryptography and Post-Quantum Cryptography: A Survey. 2021 17th International Conference on Electrical Engineering/Electronics, Computer, Telecommunications and Information Technologies(ECTI-CON). 2021. Available online: https://www.researchgate.net/publication/349071555.
- Tyagi, S. Blockchain Technology and Security: Challenges and Future Research Directions. 2022 2nd International Conference on Advance Computing and Innovative Technologies in Engineering (ICACITE). 2022. Available online: https://www.researchgate.net/publication/362705957.
- Batubara, F. R. Blockchain Technology in Supply Chain Management: Literature Review. Proceedings of the 3rd International Conference on Informatics, Technology and Engineering (InCITE 2023). 2023. Available online: https://www.researchgate.net/publication/366997910.
- Pourmirza, Z.S.M.; Rafsanjani, M.K.; Dehkordi, P.F.; Hakimi, A.A. A Comprehensive Survey on Decentralized Finance (DeFi): Framework, Applications, Challenges, and Future Directions. Future Internet 2024, 16, 76. Available online: https://www.mdpi.com/futureinternet/futureinternet-16-00076.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



