Submitted:
14 March 2025
Posted:
17 March 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
II. Literature Review
III. Methodology
IV. The Role of Cyber Insurance
- Market Analysis from 2015-2017 shows [10]
- *
- Total participants increased from 453 to 615 mainly in packaged coverage
- *
- Cyber insurance necessity increases substantially reaching .034% of P&C industry premiums by 2017
- *
- Premium volume grew 31% in 2016 and 55% in 2017
- *
- Market shifted from standalone to packaged coverage dominance by 2017
- *
- Professional surplus insurers write 20% of coverage, but firms with surplus affiliations write 60%
- A.
- Insurance Type
| Region | USA | Europe |
|---|---|---|
| First Party Coverage | ||
| 1. Loss or Damage of digital Assets | It covers the cost of repair or restore of lost data and software cyber insurance company mostly covers this portion of loss approximately 70% | Strong coverage by Household Insurance and Cyber Insurance covers 39% of it |
| 2. Business Interruption | Covers lost income and cost due to network failure this rate depends on the organizational structure and types of industry mostly it goes around 4% | If it comes to the Account blockage, then cyber Insurance provide a handsome amount otherwise business interruption does not include in policy category with high importance |
| 3. Cyber Extortion | Forensics investigation and ransom payments this segment covers the highest section around 59% (Wells-Dietel & Erkan-Barlow, 2023)#break##break#of the payment covers this section. | Cyber Extortion also includes a higher rate from the cyber insurance policy almost 68% payment are covered through this. |
| 4. Forensics investigation and Restoration costs | Software restoration along with the system restoration covers in this section. | Data recovery cost covered Household Insurance 54.90%, and 39.22% by Standalone insurance whereas Liability and Legal Protection provide a very short amount of coverage for forensic investigation. |
| Third Party Coverage | ||
| 1. Coverage types | Outlines third-party coverage areas including Credit Monitoring/Cell Center, Multimedia Liability, and Public Relations. | Encompass broad categories of third- party protection including Malware Transmission, Copyright Violations and Cyberbullying compensation. GDPR provides specific coverage percentage or particular scenario |
| 2. Granularity | The coverage study emphasizes a qualitative methodology, provides broad explanations of insurance types and their uses for personal and organizational aspect instead of in-depth statistical analyses in category wise | GDPR provides detailed quantitative breakdowns of coverage proportions for various scenarios, specifically focusing on Data Protection Violations and Antivirus Software implementations. Different insurance types specialize in specific coverage areas, with SAI (Security Assurance Insurance) primarily covering Malware Transmission cases, while LYI (Liability Yield Insurance) focuses on Damage Claims Protection. |
| 3. Use Cases and Context | California Act focuses on purpose and scope of coverage types with practical examples of each. | The analysis provides valuable insights into insurance coverage comparisons, where they followed GDPR framework to design insurance policies and finding out most comprehensive support for specific third-party liabilities and allowing for effective evaluation of coverage options across predefined categories. |
| 4. Applications | Insurance comparison based on coverage proportions. | GDPR framework is particularly valuable for insurance policy selection, allowing individuals to compare coverage proportions across different policy types (SAI, LYI, LPI, HOI) and identify potential coverage gaps in critical areas like IT assistance and cyberbullying protection. |
- B.
- Insurability Criteria
- C.
- Compare different Cyber security and Management Act according to geographical area:
| USA | Europe | Australia | |
| Scope | California Consumer Privacy Act [14] focuses on the consumers’ collection of data where only residents were the initial service receiver of this act. | This comprehensive regulation focuses on the data and information systems infrastructure, where data protection, Network Security Directive, and cybersecurity strategies are some main content. GDPR highlights global impact, EU’s harmonization effort and strategies to take actions against cyber threats. | Australia follows their Privacy Act 1988 [13], Privacy Amendment Act and Consumer Data Right and they targets data protection and cyber resilience across various sectors liner banking energy and telecommunication |
| Principle | CCPA - spotlights transparency and control allowing consumers to request their data access, data monetization and protects consumers from discrimination upon their privacy choices | Golden Rule of Information Security Policy harbored in privacy by design, explicit consent, and data minimization. Initiate strict data sharing rule, breach notification severe penalties for noncompliance. | Emphasis on mandatory breach notification also prioritizes consumer protection over fundamental rights, focusing on practical measures like credit reporting, secure data sharing, and incident reporting. |
| Data Breach notification Requirements | CCPA encourages businesses to notify users however there is not a certain timeline. | GDPR [15] follows the 72 hours timeframe for notify data protection authority and individuals must also notify if the breach constitutes a significant threat to their rights. | Following GDPR Australian Framework follows informing Australian Information Commissioner and affected individuals within 72 hours if any breach cases serious harm [16] |
| Enforcement and Penalties | CCPA Attorney General fines up to $7500 per intentional violation and $2500 per unintentional violation | National Data protection authorities impose up to €20M or 4% of the global revenue for serious violations while affected individuals can ask for compensation. | The Office Australian Information Commissioner Office administers these penalties amounting up to $2.1 M AUD for serious or repeated breaches. |
| Features | Focuses on clients restricting Data Monetization and protecting consumers rights. | Establishes two fundamental rights: data portability (moving personal data between services) and the right to erasure (having personal data deleted upon request). Sets regulations for international data transfers and mandates that large organizations employ Data Protection Officers to supervise data handling practices. | Australian Framework enforces banking standards governing data security and financial privacy. Requires security incident reporting and national frameworks. |
| Conclusion | Focuses on individual consumers rights | They set a global standard of privacy, emphasizing fundamental rights, strict compliance, and risk management. | Australian Framework protects industry specific regulations and practical implementation strategies. |
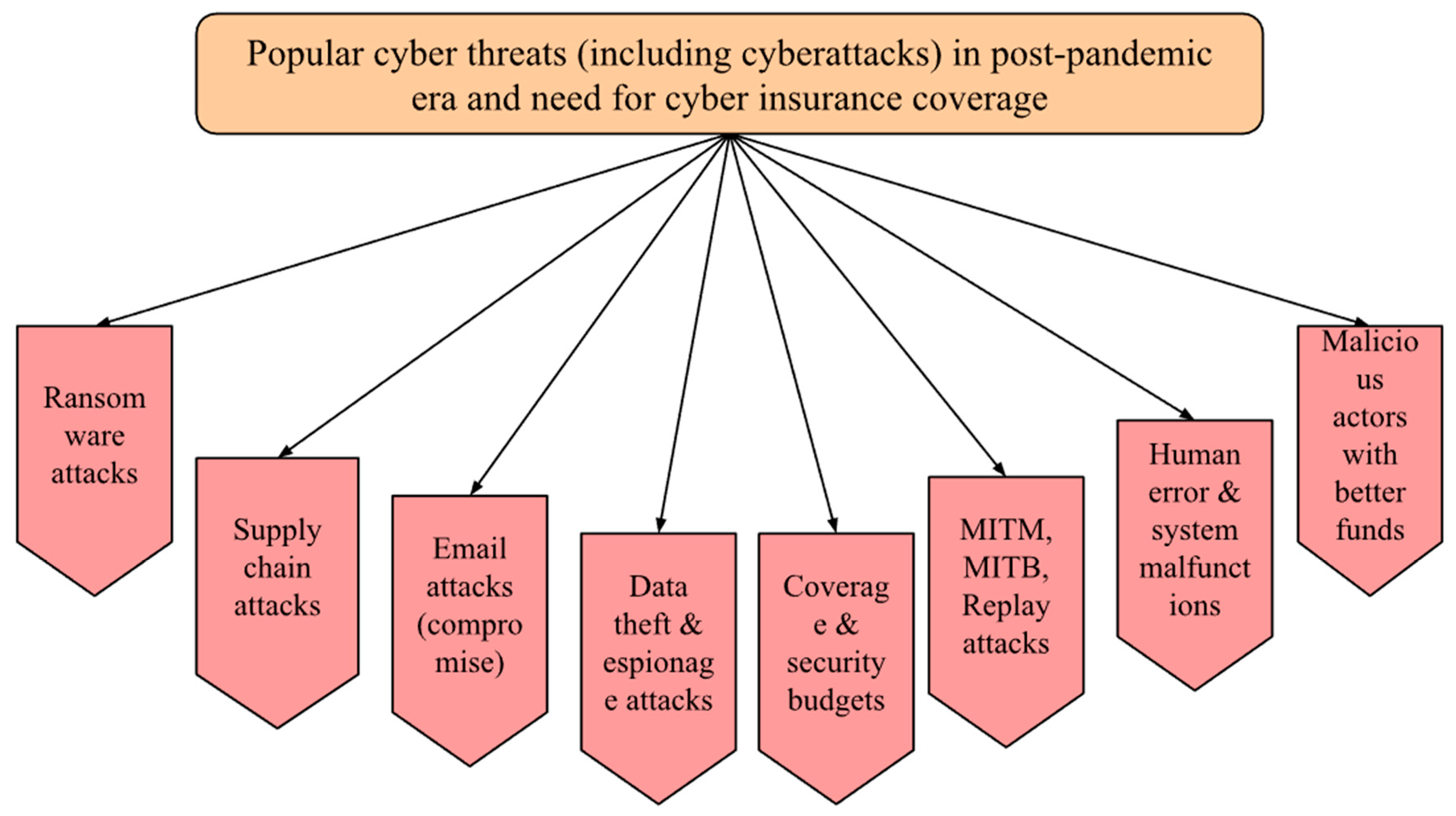
V. Case Studies
- A.
- Case Study I - Sinclair Broadcast Group, Inc. Ransomware Attack 2021
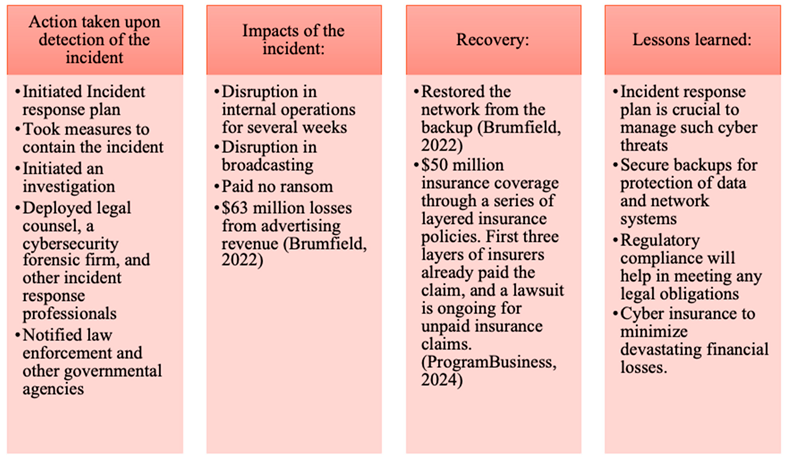 |
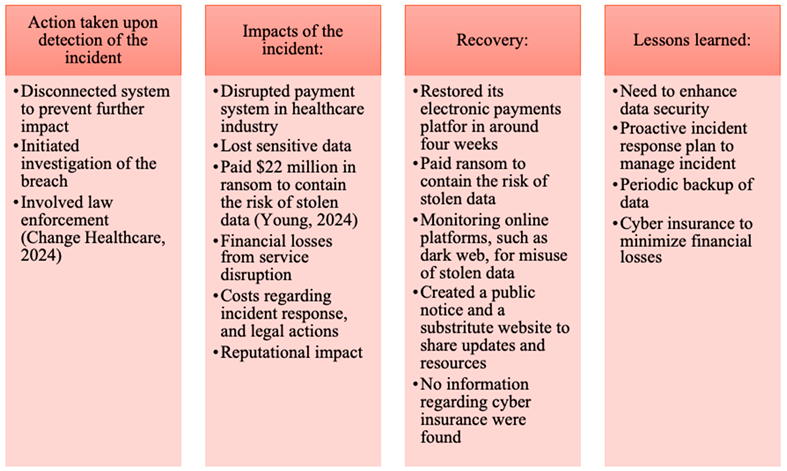
- B.
- Case Study II - Change Healthcare Security Incident 2024
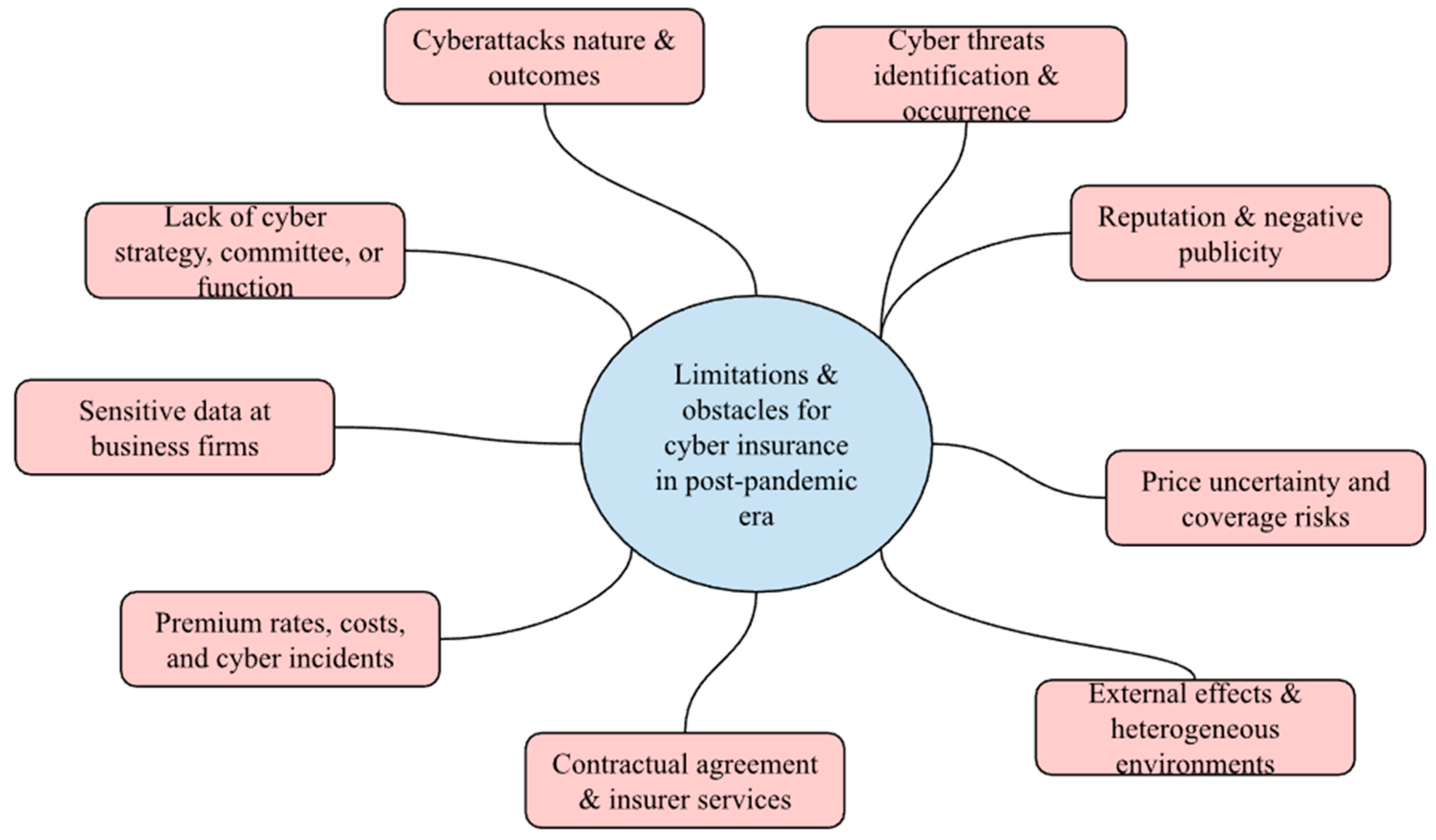
VI. Discussion and Limitation
VII. Conclusion and Future Scope
References
- Zakharevych, M., & Hryhorenko, V. (2024). Digital Competence and Digital Literacy of Higher Education Acquires. Collection of Scientific Papers of Uman State Pedagogical University, 1, 119–129. [CrossRef]
- Panda, S. et al. (2021) ‘Cyber-Insurance: Past, present and future’, Encyclopedia of Cryptography, Security and Privacy, pp. 1–4. [Sec1-Ref2]. [CrossRef]
- Granato, A. and Polacek, A. (2019) The growth and challenges of Cyber Insurance, Federal Reserve Bank of Chicago. Available at: https://www.chicagofed.org/publications/chicago-fed-letter/2019/426 (Accessed: 18 February 2025).
- Jawhar, S., Kimble, C. E., Miller, J. R., & Bitar, Z. (2024, January). Enhancing Cyber Resilience with AI-Powered Cyber Insurance Risk Assessment. In 2024 IEEE 14th Annual Computing and Communication Workshop and Conference (CCWC) (pp. 0435-0438). IEEE.
- Tsohou, A., Diamantopoulou, V., Gritzalis, S., & Lambrinoudakis, C. (2023). Cyber insurance: state of the art, trends, and future directions. International Journal of Information Security, 22(3), 737-748. [CrossRef]
- Aziz, B. (2020, October). A systematic literature review of cyber insurance challenges. In 2020 International Conference on Information Technology Systems and Innovation (ICITSI) (pp. 357-363). Houston, USA. IEEE.
- Bajracharya, A., Harvey, B., & Rawat, D. B. (2023, March). Recent advances in cybersecurity and fraud detection in financial services: a survey. In 2023 IEEE 13th Annual Computing and Communication Workshop and Conference (CCWC) (pp. 0368-0374). IEEE.
- Choudhary, A., Choudhary, G., Pareek, K., Kunndra, C., Luthra, J., & Dragoni, N. (2022). Emerging cyber security challenges after COVID pandemic: a survey. Journal of Internet Services and Information Security, 12(2), 21-50.
- Schütz, F., Rampold, F., Kalisch, A., & Masuch, K. (2023). Consumer Cyber Insurance as Risk Transfer: A Coverage Analysis. Procedia Computer Science, 219, 521–528. ScienceDirect. [CrossRef]
- Xie, X., Lee, C., & Eling, M. (2020). Cyber insurance offering and performance: an analysis of the U.S. cyber insurance market. The Geneva Papers on Risk and Insurance - Issues and Practice, 45, 690–736. [CrossRef]
- Pfeffer, I., Mehr, R. I., & Cammack, E. (1973). Principles of Insurance. The Journal of Risk and Insurance, 40(2), 274. [CrossRef]
- Berliner, B. (1985). Large Risks and Limits of Insurability. The Geneva Papers on Risk and Insurance, 10(37), 313–329. http://www.jstor.org/stable/41950168.
- OAIC. (2024). The Privacy Act. OAIC; Australian Government. https://www.oaic.gov.au/privacy/privacy-legislation/the-privacy-act.
- State of California Department of Justice. (2024, March 13). California Consumer Privacy Act (CCPA). State of California - Department of Justice - Office of the Attorney General. https://oag.ca.gov/privacy/ccpa.
- GDPR. (2018). General Data Protection Regulation (GDPR). General Data Protection Regulation (GDPR). https://gdpr-info.eu/.
- Thilla Rajaretnam. (2020). A Review of Data Governance Regulation, Practices and Cyber Security Strategies for Businesses: An Australian Perspective. International Journal of Technology Management and Information System, 2(1), 1–17. https://myjms.mohe.gov.my/index.php/ijtmis/article/view/8359.
- Sinclair Press Releases (2021) Sinclair Broadcast Group provides information on Cybersecurity incident, Sinclair, Inc. Available at: https://sbgi.net/sinclair-broadcast-group-provides-information-on-cybersecurity-incident/ (Accessed: 13 January 2025).
- Brumfield, C. (2022) SEC filings show hidden ransomware costs and losses, CSO Online. Available at: https://www.csoonline.com/article/572321/sec-filings-show-hidden-ransomware-costs-and-losses.html (Accessed: 13 January 2025).
- ProgramBusiness, P. (2024) Sinclair files lawsuit against Cyber Insurers - programbusiness: Where insurance industry clicks, ProgramBusiness. Available at: https://programbusiness.com/news/sinclair-files-lawsuit-against-cyber-insurers-over-unpaid-ransomware-claims/ (Accessed: 13 January 2025).
- Change Healthcare (2024) DATA BREACH NOTICE (June 20, 2024; updated July 31, 2024, and August 8, 2024), Change Healthcare. Available at: https://www.changehealthcare.com/hipaa-substitute-notice-spanish.html (Accessed: 13 January 2025).
- Young, K. (2024) Cyber case study: Change healthcare cyberattack, CoverLink Insurance - Ohio Insurance Agency. Available at: https://coverlink.com/cyber-liability-insurance/cyber-case-study-change-healthcare-cyberattack/ (Accessed: 14 January 2025).
- Pavlík, L., Ficek, M., & Rak, J. (2022). Dynamic assessment of cyber threats in the field of insurance. Risks, 10(12), 222.
- Kshetri, N. (2019). The economics of cyber-insurance. IT Professional, 20(6), 9-14.
- Gatzert, N., & Schubert, M. (2022). Cyber risk management in the US banking and insurance industry: A textual and empirical analysis of determinants and value. Journal of Risk and Insurance, 89(3), 725-763.
- Hutson, J., Coble, K., Kshetri, N., & Smith, A. (2023). Exploring the intersection of digital marketing and retail: Challenges and opportunities in AI, privacy, and customer experience. Confronting Security and Privacy Challenges in Digital Marketing, 50-72. [CrossRef]
- Osama, O. F., Kshetri, N., Rahman, M. M., & Pokharel, B. P. (2025). healthMLsec: Machine Learning based Vulnerability Assessment in Health Systems: A Framework for Enhancing Cybersecurity and Patient Data. https://www.preprints.org/manuscript/202502.2165/v1.
- Kshetri, N., Rahman, M. M., Sayeed, S. A., & Sultana, I. (2024, May). cryptoRAN: A review on cryptojacking and ransomware attacks wrt banking industry-threats, challenges, & problems. In 2024 2nd International Conference on Advancement in Computation & Computer Technologies (InCACCT) (pp. 523-528). IEEE. [CrossRef]
- Cremer, F. (2024) ‘On the efficacy of modern cyber (re)insurance: an analysis of policy coverage, capacity constraints, cyber warfare, and data availability’, available. [CrossRef]
- Wang, S.S (2019), ‘Integrated framework for information security investment and cyber insurance’, Pacific-Basin Finance Journal, Volume 57, 101173, ISSN 0927-538X. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).