Submitted:
04 March 2025
Posted:
04 March 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Ensemble-Based Anomaly Detection: The proposed model integrates LSTM, GRU, and stacked autoencoders to detect malicious web requests. This ensemble structure enables the model to effectively learn normal request patterns while enhancing its robustness against unknown attack strategies.
- Zero-Day Attack Detection Without Labeled Anomalous Data: Unlike conventional detection methods that require labeled datasets containing both normal and malicious samples, the proposed model is trained exclusively on normal web requests. This approach enables it to detect both known and zero-day attacks by identifying deviations from learned normal behaviors.
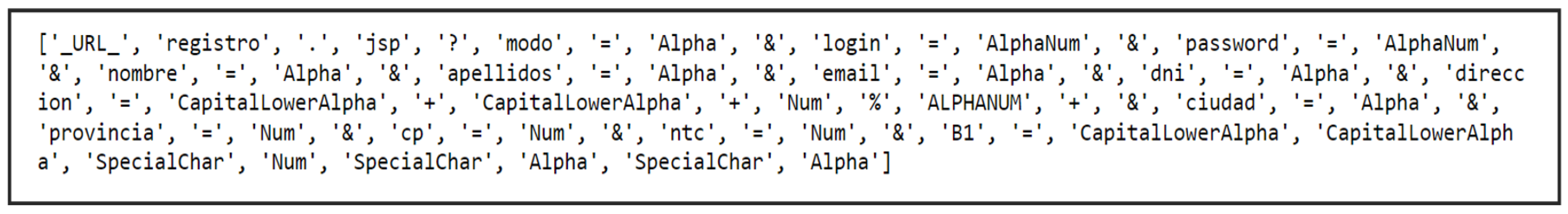
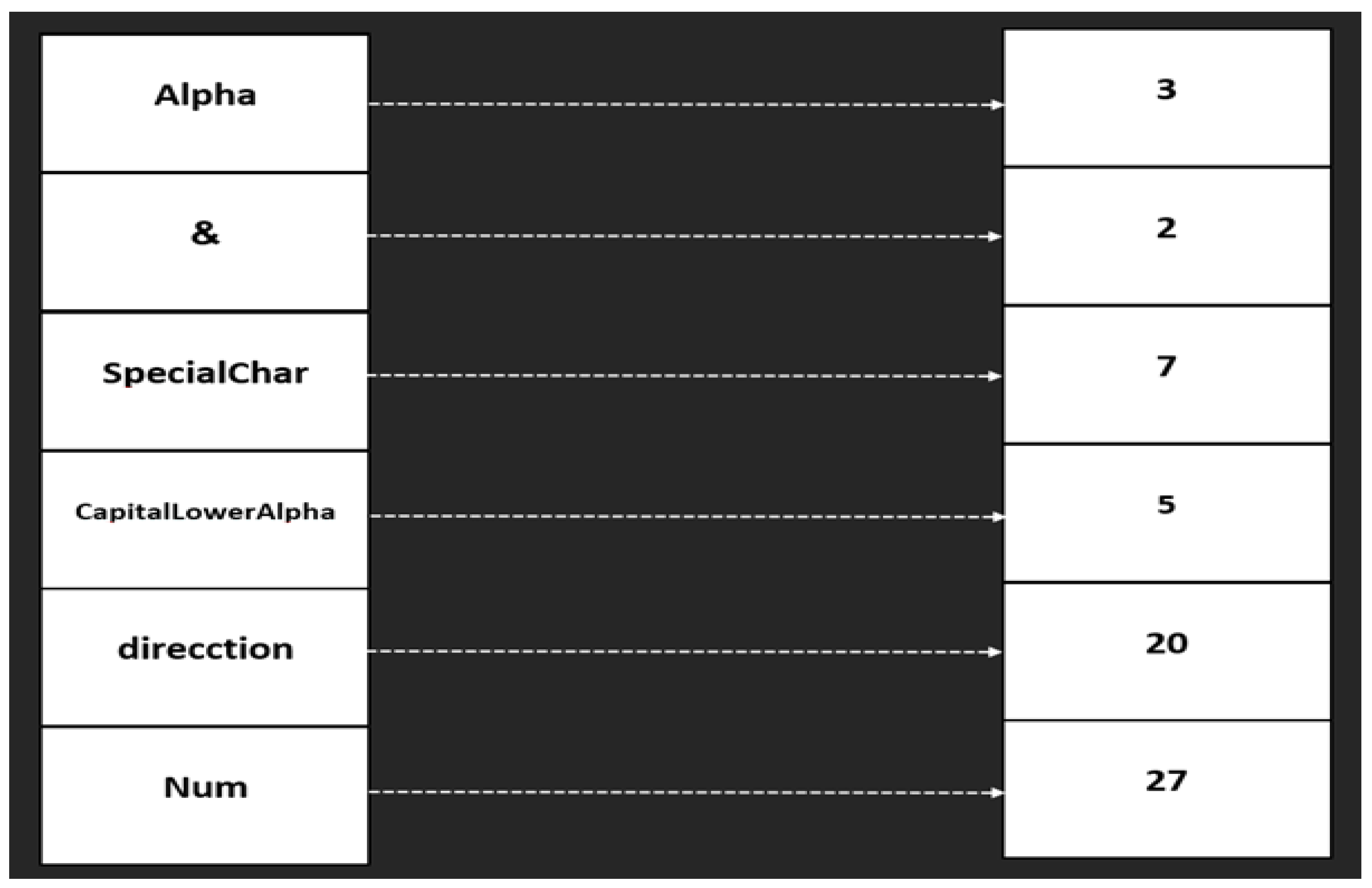
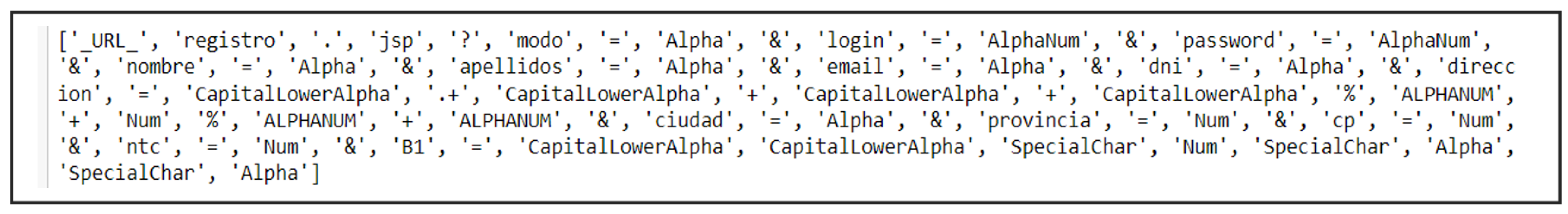
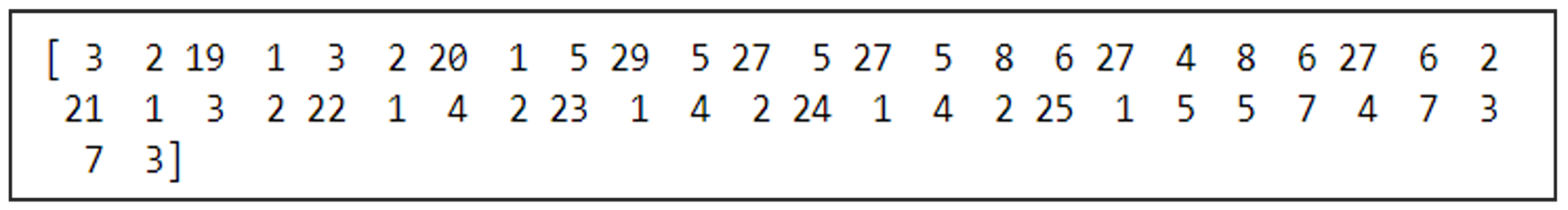
- Advanced Tokenization and Feature Mapping: A novel tokenization strategy is introduced, classifying tokens based on character composition (e.g., numeric, lowercase, uppercase, special characters). This method reduces input dimensionality, enhances pattern consistency, and improves the model’s ability to distinguish between benign and malicious activities.
- Comprehensive Performance Evaluation: The effectiveness of the proposed model is assessed using multiple performance metrics, including accuracy, precision, recall, specificity, F1 score, false positive rate and also consumed time for training and testing phases. The results demonstrate that the ensemble model consistently outperforms individual sub-models and previous approaches, achieving a higher detection rate with a significantly lower false positive rate.
2. Background
3. Related Work
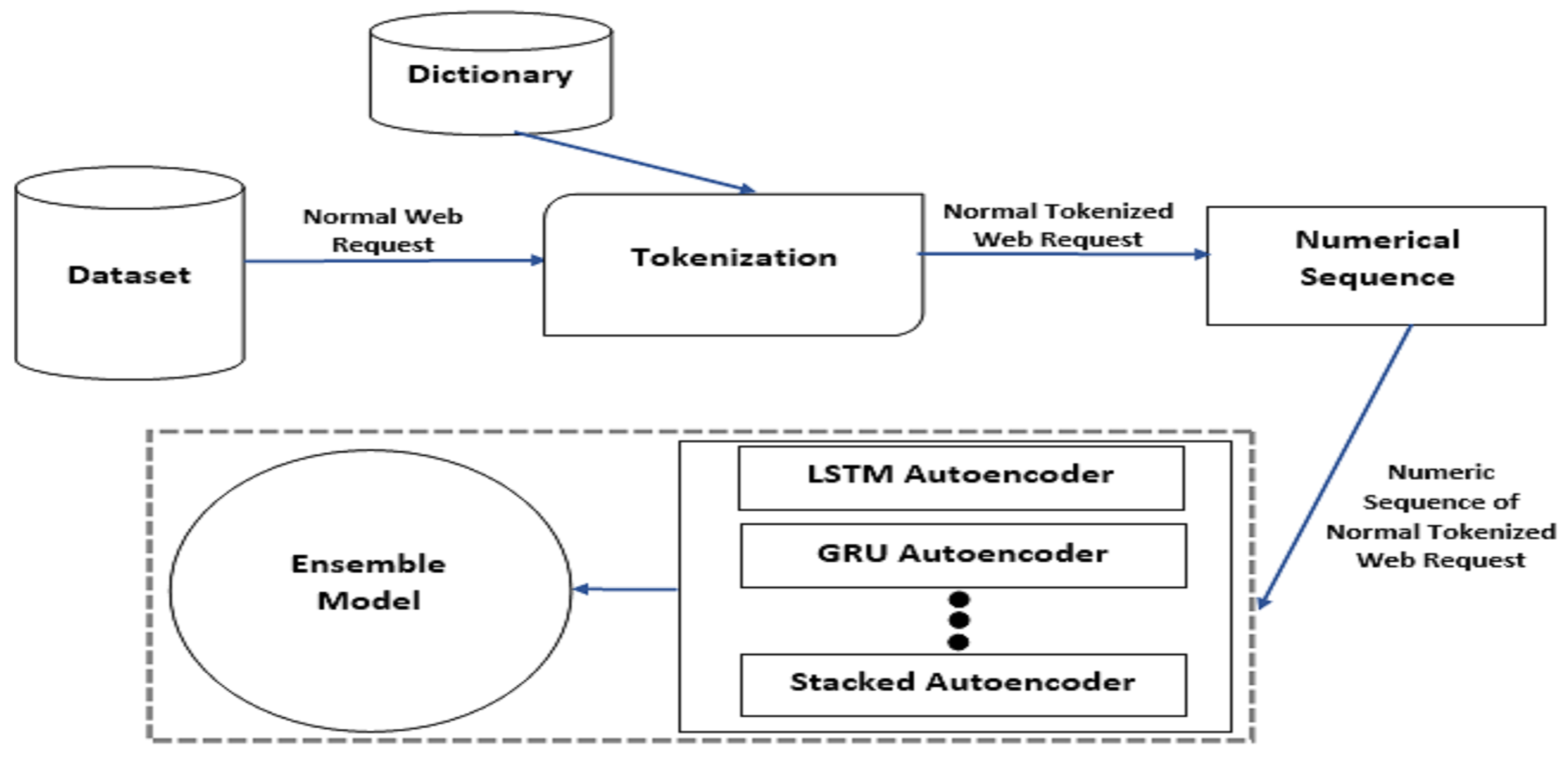
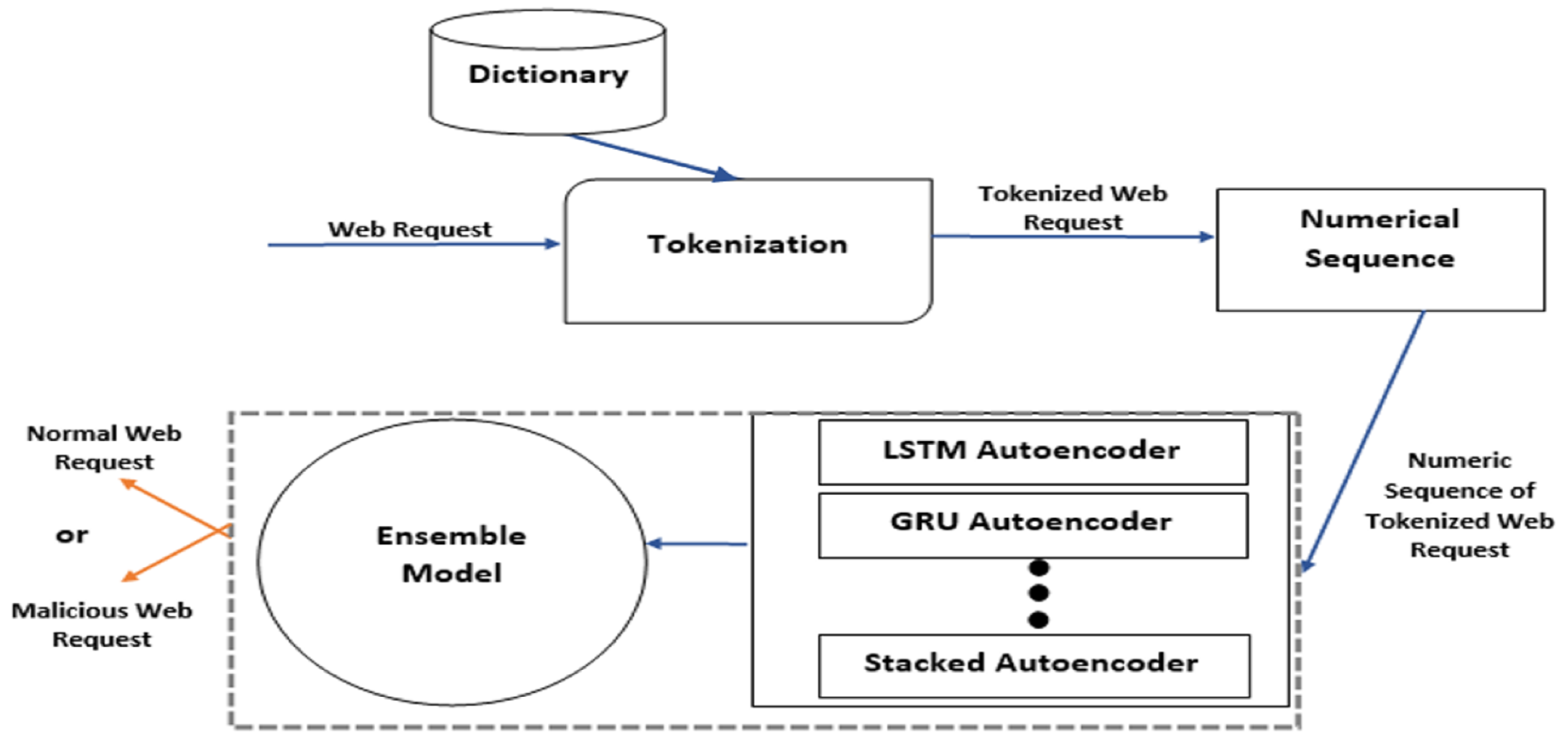
4. Proposed Model
4.1. Architecture
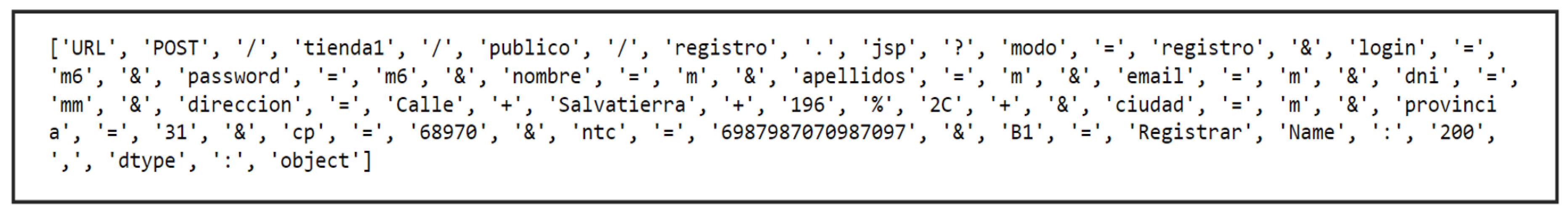
4.1.1. Tokenization
4.1.2. Dictionary
- Data volume reduction: The tokenization process optimizes data representation, reducing the complexity and size of input data, thereby improving computational efficiency.
- Pattern identification for anomaly detection: By establishing a structured pattern for normal web requests, the tokenization method enhances the model’s ability to differentiate between legitimate and anomalous activities, ensuring higher accuracy in detecting malicious web requests.
4.1.3. Numerical Sequence
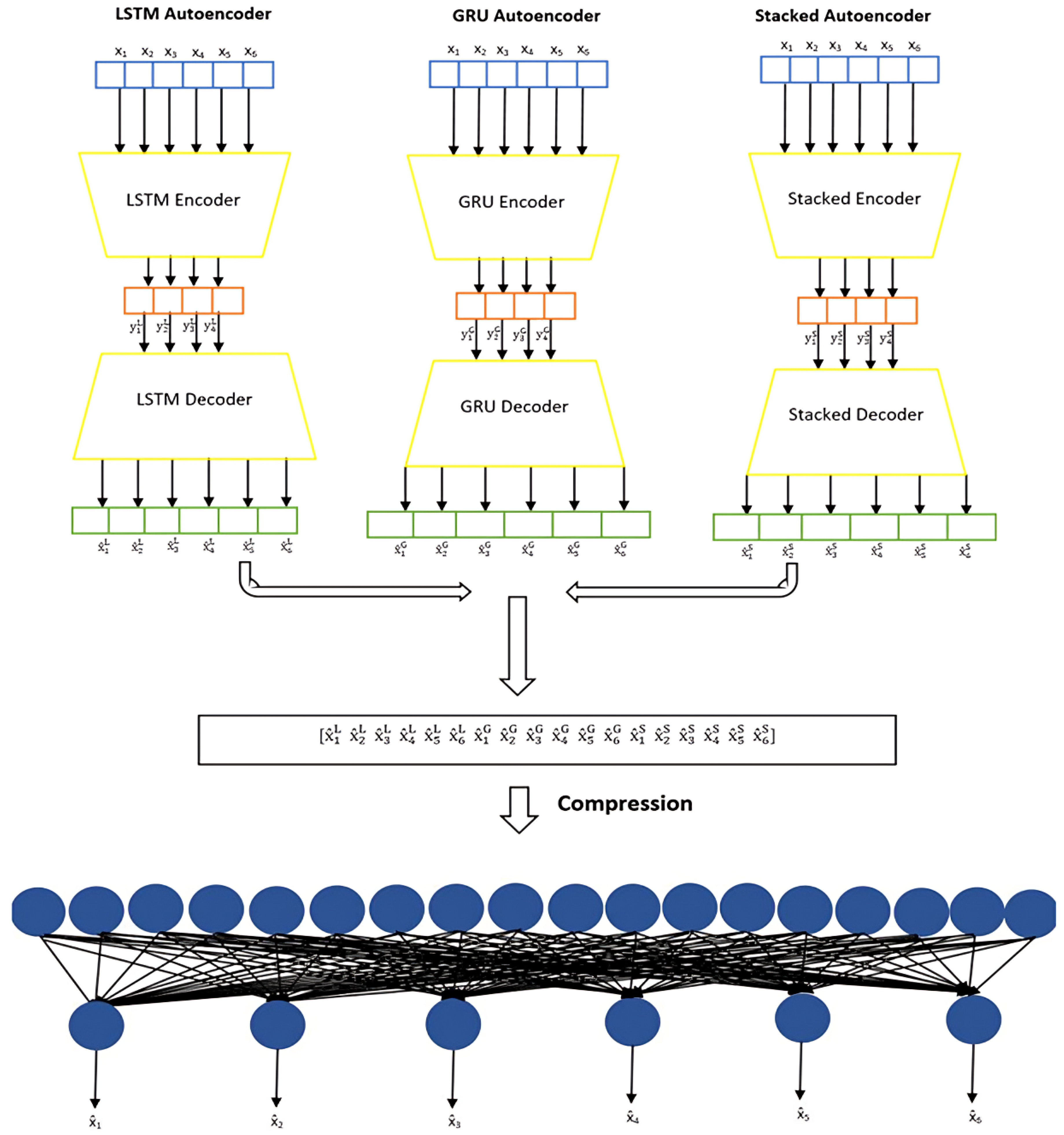
4.1.4. Ensemble Model
5. Evaluation and Results
5.1. Data Collection
- It encompasses a diverse range of malicious requests, including SQL Injection (SQLi), Cross-Site Scripting (XSS), and Buffer Overflow attacks.
- It contains normal (benign) web requests, ensuring a balanced distribution of data for effective training and evaluation.
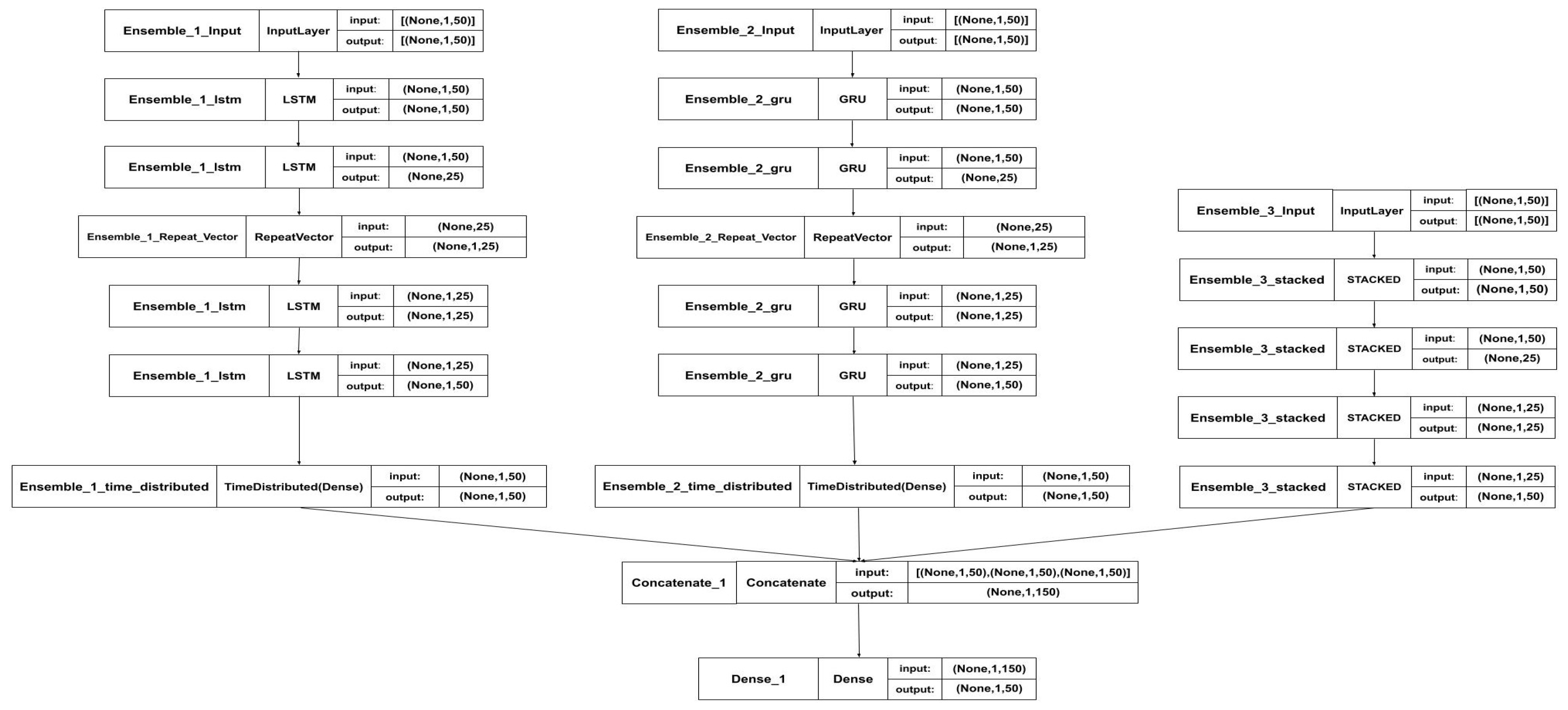
5.2. The Ensemble Model Structure
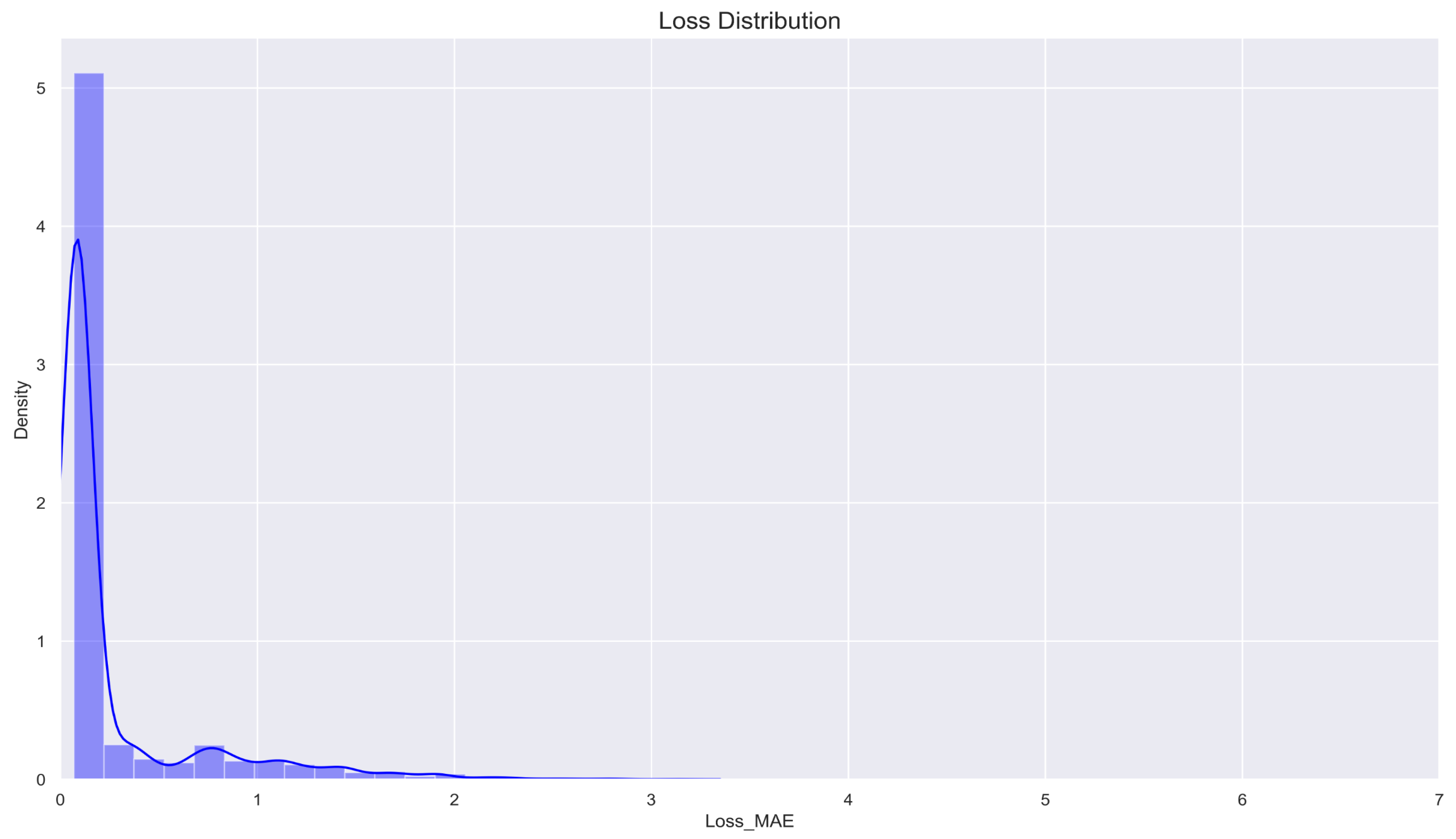
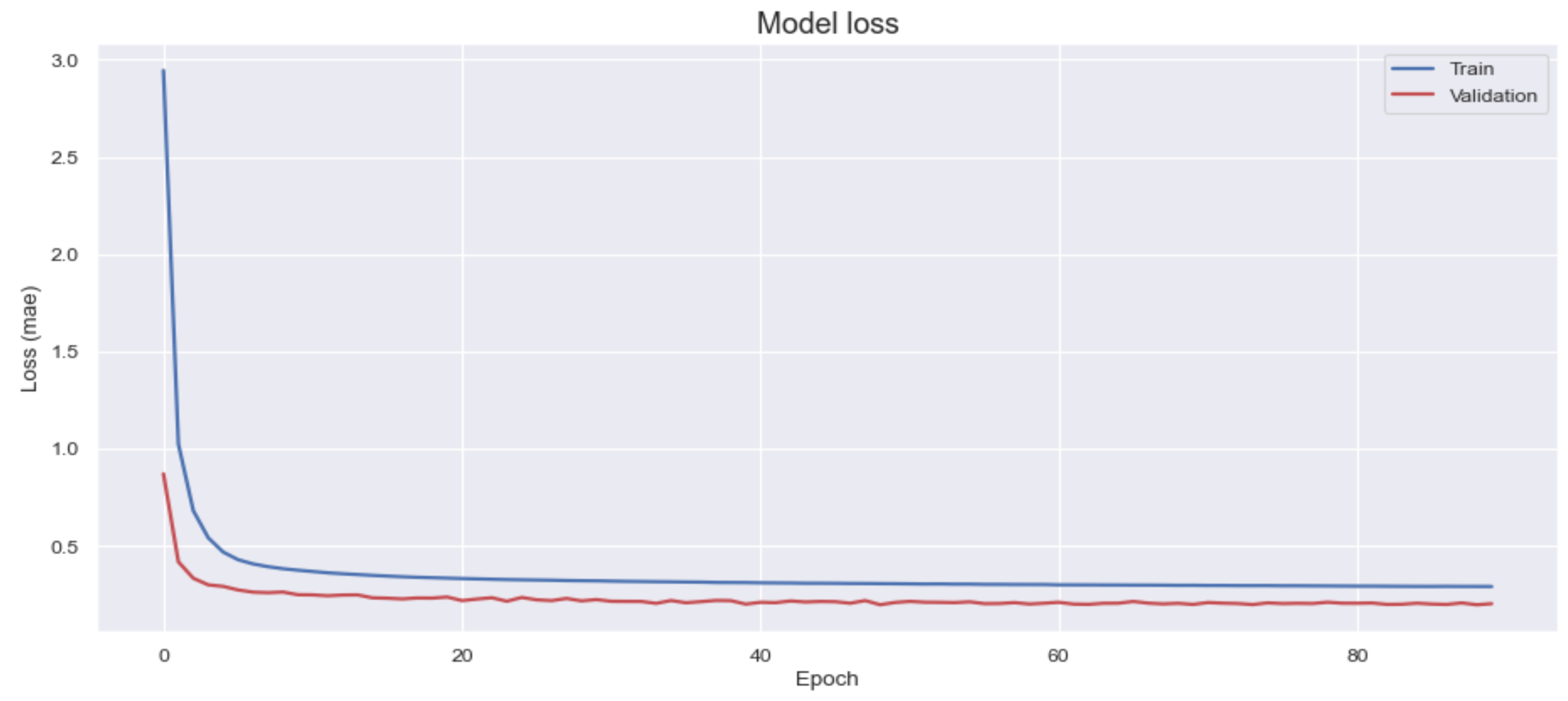
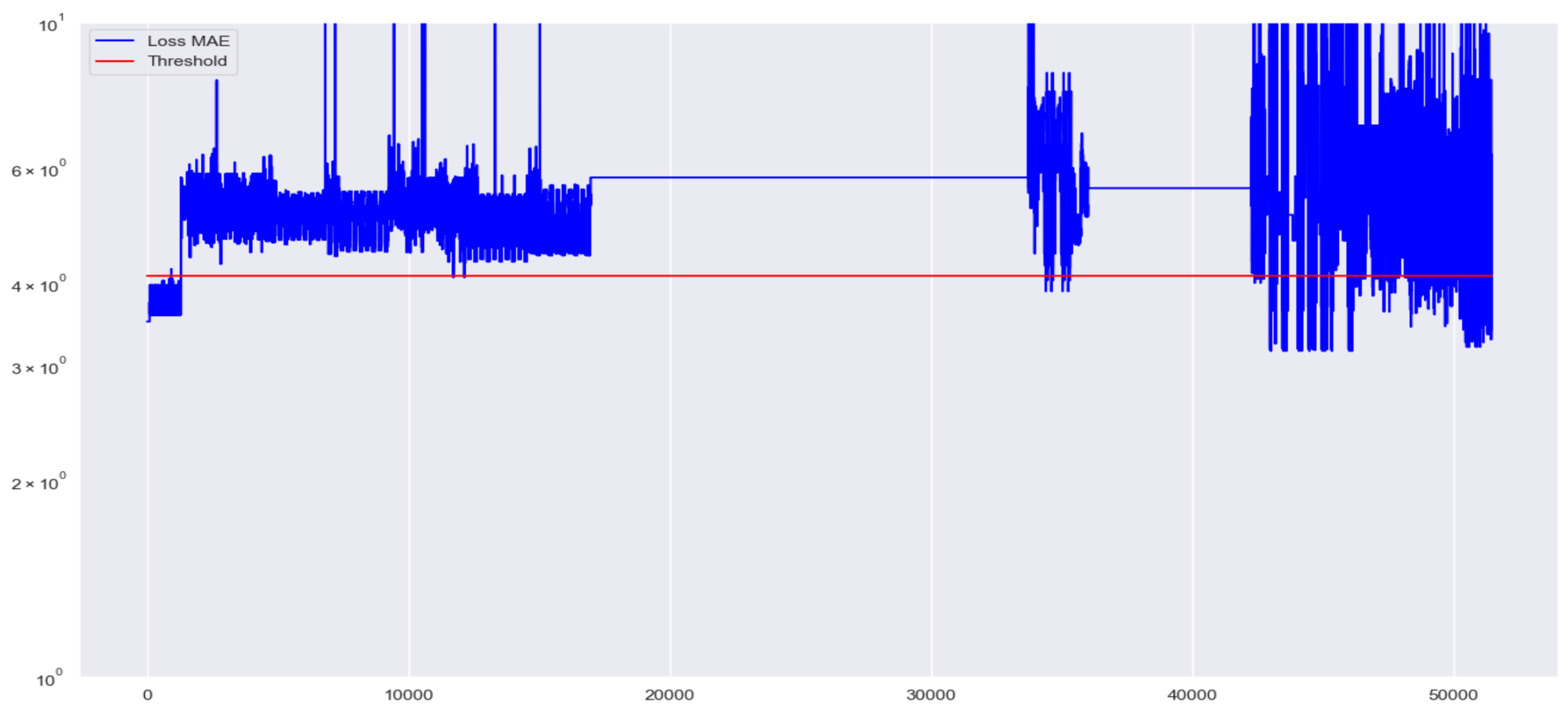
5.3. Results
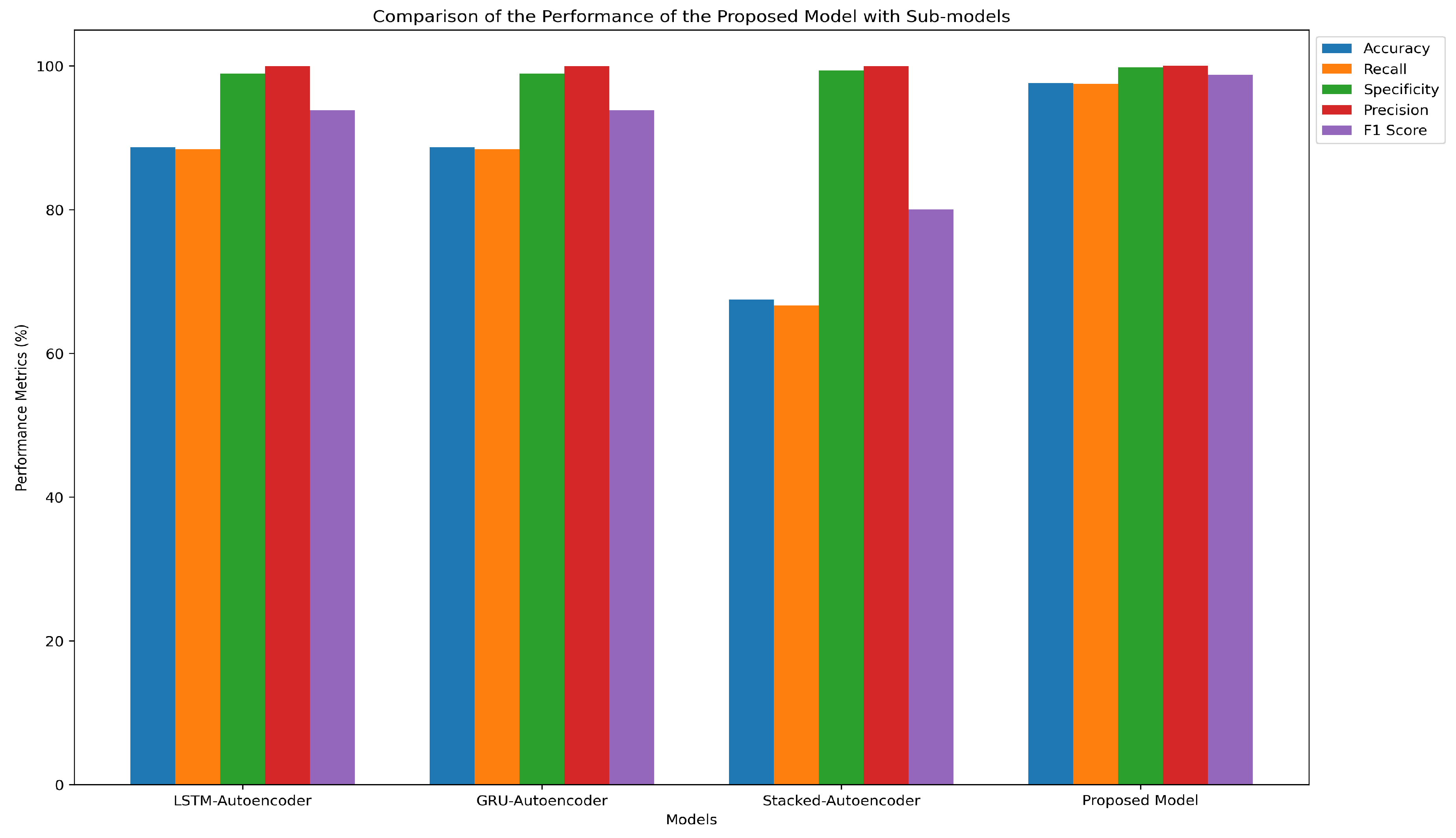
| Models | Accuracy | Recall | Specificity | Precision | False Positive Rate | F1 Score |
|---|---|---|---|---|---|---|
| LSTM-Autoencoder | 88.68% | 88.41% | 98.92% | 99.96% | 1% | 93.83% |
| GRU-Autoencoder | 88.69% | 88.42% | 98.92% | 99.96% | 1% | 93.83% |
| Stacked-Autoencoder | 67.48% | 66.65% | 99.38% | 99.97% | 0.6% | 79.98% |
| Proposed Model | 97.58% | 97.52% | 99.76% | 99.99% | 0.2% | 98.74% |
6. Discussion
6.1. Effectiveness of the Ensemble Model
- LSTM Autoencoder: Captures long-term dependencies in web request sequences, enhancing the ability to recognize complex request structures.
- GRU Autoencoder: Provides computational efficiency while preserving strong sequential pattern recognition capabilities.
- Stacked Autoencoder: Focuses on dimensionality reduction and latent feature extraction, improving anomaly detection in subtle attack patterns.
6.2. Practical Considerations and Limitations
7. Conclusions
8. Future Work
References
- Ahmad, R.; Alsmadi, I.; Alhamdani, W.; Tawalbeh, L. Zero-day attack detection: a systematic literature review. Artificial Intelligence Review 2023, 56, 10733–10811.
- Dawadi, B.R.; Adhikari, B.; Srivastava, D.K. Deep learning technique-enabled web application firewall for the detection of web attacks. Sensors 2023, 23, 2073. [CrossRef]
- Yang, J.; Chen, Y.L.; Por, L.Y.; Ku, C.S. A systematic literature review of information security in chatbots. Applied Sciences 2023, 13, 6355.
- Calzavara, S.; Conti, M.; Focardi, R.; Rabitti, A.; Tolomei, G. Machine learning for web vulnerability detection: the case of cross-site request forgery. IEEE Security & Privacy 2020, 18, 8–16.
- Ahmed, M.; Mahmood, A.N.; Hu, J. A survey of network anomaly detection techniques. Journal of Network and Computer Applications 2016, 60, 19–31.
- Pu, G.; Wang, L.; Shen, J.; Dong, F. A hybrid unsupervised clustering-based anomaly detection method. Tsinghua Science and Technology 2020, 26, 146–153.
- Long, H.V.; Tuan, T.A.; Taniar, D.; Can, N.V.; Hue, H.M.; Son, N.T.K. An efficient algorithm and tool for detecting dangerous website vulnerabilities. International Journal of Web and Grid Services 2020, 16, 81–104.
- Ingham, K.L.; Somayaji, A.; Burge, J.; Forrest, S. Learning DFA representations of HTTP for protecting web applications. Computer Networks 2007, 51, 1239–1255.
- Sivri, T.T.; Akman, N.P.; Berkol, A.; Peker, C. Web intrusion detection using character level machine learning approaches with upsampled data. Annals of Computer Science and Information Systems 2022, 32.
- Jung, I.; Lim, J.; Kim, H.K. PF-TL: Payload feature-based transfer learning for dealing with the lack of training data. Electronics 2021, 10, 1148. [CrossRef]
- Vartouni, A.M.; Kashi, S.S.; Teshnehlab, M. An anomaly detection method to detect web attacks using stacked auto-encoder. In Proceedings of the 2018 6th Iranian Joint Congress on Fuzzy and Intelligent Systems (CFIS). IEEE, 2018, pp. 131–134.
- Ariu, D.; Tronci, R.; Giacinto, G. HMMPayl: An intrusion detection system based on Hidden Markov Models. computers & security 2011, 30, 221–241.
- Liang, J.; Zhao, W.; Ye, W. Anomaly-based web attack detection: a deep learning approach. In Proceedings of the Proceedings of the 2017 VI International Conference on Network, Communication and Computing, 2017, pp. 80–85.
- Kuang, X.; Zhang, M.; Li, H.; Zhao, G.; Cao, H.; Wu, Z.; Wang, X. DeepWAF: detecting web attacks based on CNN and LSTM models. In Proceedings of the Cyberspace Safety and Security: 11th International Symposium, CSS 2019, Guangzhou, China, December 1–3, 2019, Proceedings, Part II 11. Springer, 2019, pp. 121–136.
- Tang, R.; Yang, Z.; Li, Z.; Meng, W.; Wang, H.; Li, Q.; Sun, Y.; Pei, D.; Wei, T.; Xu, Y.; et al. Zerowall: Detecting zero-day web attacks through encoder-decoder recurrent neural networks. In Proceedings of the IEEE INFOCOM 2020-IEEE Conference on Computer Communications. IEEE, 2020, pp. 2479–2488.
- Indrasiri, P.L.; Halgamuge, M.N.; Mohammad, A. Robust ensemble machine learning model for filtering phishing URLs: Expandable random gradient stacked voting classifier (ERG-SVC). Ieee Access 2021, 9, 150142–150161.
- Gong, X.; Lu, J.; Zhou, Y.; Qiu, H.; He, R. Model uncertainty based annotation error fixing for web attack detection. Journal of Signal Processing Systems 2021, 93, 187–199. [CrossRef]
- Tekerek, A. A novel architecture for web-based attack detection using convolutional neural network. Computers & Security 2021, 100, 102096.
- Jemal, I.; Haddar, M.A.; Cheikhrouhou, O.; Mahfoudhi, A. SWAF: a smart web application firewall based on convolutional neural network. In Proceedings of the 2022 15th International Conference on Security of Information and Networks (SIN). IEEE, 2022, pp. 01–06.
- Alaoui, R.L.; et al. Web attacks detection using stacked generalization ensemble for LSTMs and word embedding. Procedia Computer Science 2022, 215, 687–696.
- Mohamed, S.M.; Rohaim, M.A. Multi-Class Intrusion Detection System using Deep Learning. Journal of Al-Azhar University Engineering Sector 2023, 18, 869–883.
- Shahid, W.B.; Aslam, B.; Abbas, H.; Khalid, S.B.; Afzal, H. An enhanced deep learning based framework for web attacks detection, mitigation and attacker profiling. Journal of Network and Computer Applications 2022, 198, 103270.
- Moarref, N.; Sandıkkaya, M.T. MC-MLDCNN: Multichannel Multilayer Dilated Convolutional Neural Networks for Web Attack Detection. Security and Communication Networks 2023, 2023, 2415288.
- Thomas, S.; Koleini, F.; Tabrizi, N. Dynamic defenses and the transferability of adversarial examples. In Proceedings of the 2022 IEEE 4th International Conference on Trust, Privacy and Security in Intelligent Systems, and Applications (TPS-ISA). IEEE, 2022, pp. 276–284.
- Khalid, M.N.; Farooq, H.; Iqbal, M.; Alam, M.T.; Rasheed, K. Predicting web vulnerabilities in web applications based on machine learning. In Proceedings of the Intelligent Technologies and Applications: First International Conference, INTAP 2018, Bahawalpur, Pakistan, October 23-25, 2018, Revised Selected Papers 1. Springer, 2019, pp. 473–484.
- Levene, M.; Poulovassilis, A.; Davison, B.D. Learning web request patterns. Web Dynamics: Adapting to Change in Content, Size, Topology and Use 2004, pp. 435–459.
- Vijayarani, S.; Janani, R.; et al. Text mining: open source tokenization tools-an analysis. Advanced Computational Intelligence: An International Journal (ACII) 2016, 3, 37–47.
- Rashvand, N.; Hosseini, S.S.; Azarbayjani, M.; Tabkhi, H. Real-Time Bus Arrival Prediction: A Deep Learning Approach for Enhanced Urban Mobility. arXiv preprint arXiv:2303.15495 2023.
- Vaswani, A. Attention is all you need. Advances in Neural Information Processing Systems 2017.
- Rashvand, N.; Witham, K.; Maldonado, G.; Katariya, V.; Marer Prabhu, N.; Schirner, G.; Tabkhi, H. Enhancing automatic modulation recognition for iot applications using transformers. IoT 2024, 5, 212–226. [CrossRef]
- Shaheed, A.; Kurdy, M.B. Web application firewall using machine learning and features engineering. Security and Communication Networks 2022, 2022, 5280158.
- DuckDuckBug. CNN Web Application Firewall. https://github.com/DuckDuckBug/cnn_waf, 2023. Accessed: January 29, 2025.
- Jagat, R.R.; Sisodia, D.S.; Singh, P. Detecting web attacks from HTTP weblogs using variational LSTM autoencoder deviation network. IEEE Transactions on Services Computing 2024. [CrossRef]
- Abshari, D.; Fu, C.; Sridhar, M. LLM-assisted Physical Invariant Extraction for Cyber-Physical Systems Anomaly Detection. arXiv preprint arXiv:2411.10918 2024.
- Zibaeirad, A.; Koleini, F.; Bi, S.; Hou, T.; Wang, T. A comprehensive survey on the security of smart grid: Challenges, mitigations, and future research opportunities. arXiv preprint arXiv:2407.07966 2024.
- Abshari, D.; Sridhar, M. A Survey of Anomaly Detection in Cyber-Physical Systems. arXiv preprint arXiv:2502.13256 2025.
- Babaey, V.; Ravindran, A. GenSQLi: A Generative Artificial Intelligence Framework for Automatically Securing Web Application Firewalls Against Structured Query Language Injection Attacks. Future Internet 2025, 17, 8. [CrossRef]
- White, J.; Fu, Q.; Hays, S.; Sandborn, M.; Olea, C.; Gilbert, H.; Elnashar, A.; Spencer-Smith, J.; Schmidt, D.C. A prompt pattern catalog to enhance prompt engineering with chatgpt. arXiv preprint arXiv:2302.11382 2023.
- Graves, A.; Jaitly, N.; Mohamed, A.r. Hybrid speech recognition with deep bidirectional LSTM. In Proceedings of the 2013 IEEE workshop on automatic speech recognition and understanding. IEEE, 2013, pp. 273–278.
| System | Details |
|---|---|
| Neural Networks | LSTM, GRU, and Stacked Autoencoder |
| Operating System | Windows 11 |
| Programming Language | Python v3.12 |
| Python Library | Scikit-learn v1.6.0 |
| Natural Language Toolkit (NLTK) Library | WordPunctTokenizer |
| Feature Extraction and Tokenization Tool | Tokenizer class in python |
| Evaluation Metric for measuring prediction accuracy | Mean Absolute Error (MAE) |
| Metric | Definition/Calculation |
|---|---|
| Total (T) | Total number of requests = 51473 |
| Correct Predictions (CP) | Number of correctly predicted requests = 50230 |
| Negatives | Normal requests = 1299 |
| Positives | Malicious requests = 50174 |
| True Negatives (TN) | Normal requests correctly predicted as normal = 1296 |
| False Positives (FP) | Normal requests incorrectly predicted as malicious = 3 |
| False Negatives (FN) | Malicious requests incorrectly predicted as normal = 1240 |
| True Positives (TP) | Malicious requests correctly predicted as malicious = 48934 |
| Accuracy | |
| Recall (Sensitivity) | |
| Specificity | |
| Precision | |
| False Positive Rate | |
| F1 Score |
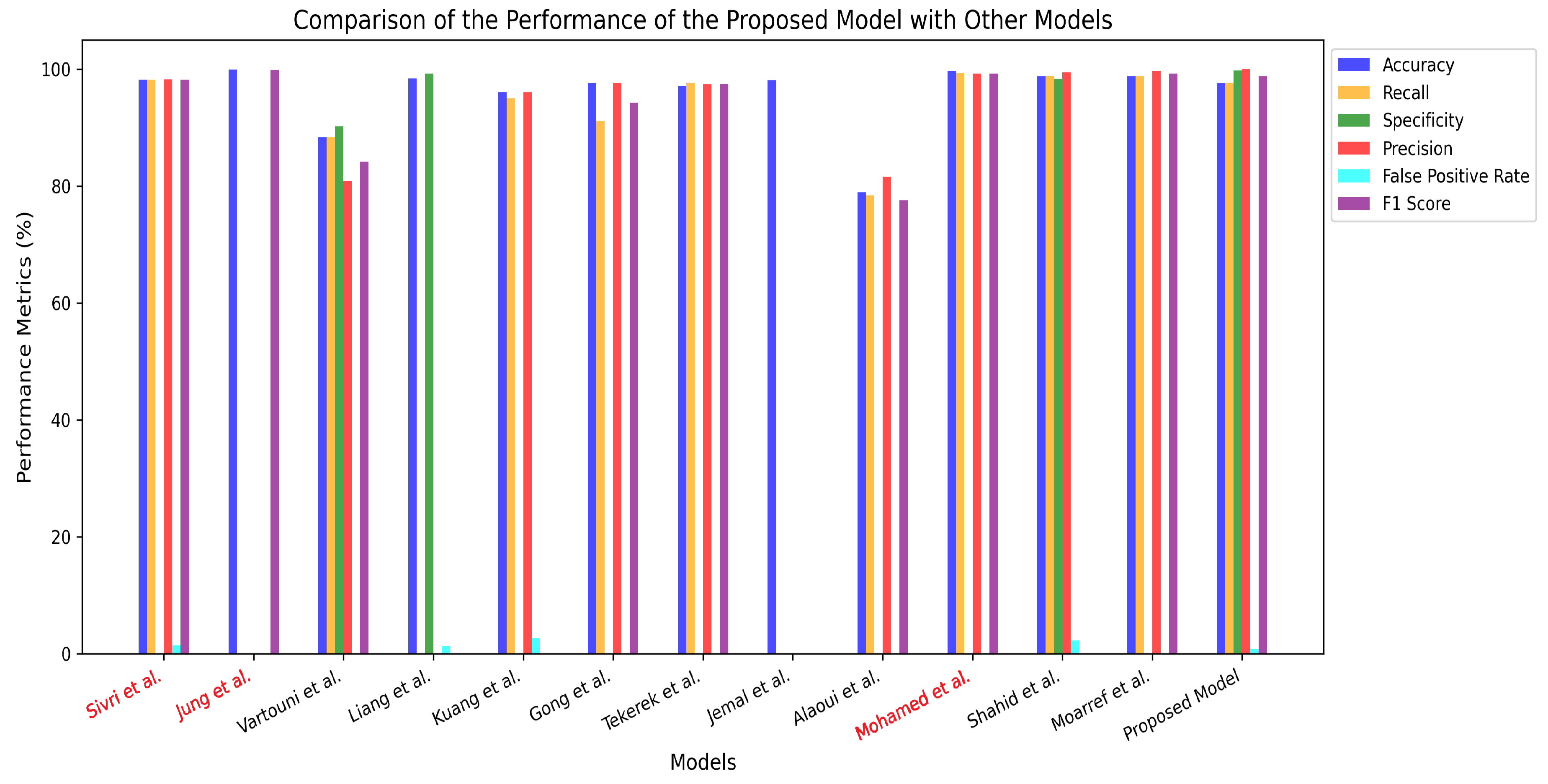
| Models | Accuracy | Recall | Specificity | Precision | False Positive Rate | F1 Score |
|---|---|---|---|---|---|---|
| Sivri, T.T. et al. [9] | 98.15% | 98.15% | - | 98.20% | 0.8% | 98.16% |
| Jung et al. [10] | 99.88% | - | - | - | - | 99.80% |
| Vartouni et al. [11] | 88.32% | 88.34% | 90.20% | 80.79% | - | 84.12% |
| Liang et al. [13] | 98.42% | - | 99.21% | - | 0.7% | - |
| Kuang et al. [14] | 96% | 95% | - | 96% | 2% | - |
| Gong et al. [17] | 97.64% | 91.11% | - | 97.62% | - | 94.25% |
| Tekerek et al. [18] | 97.07% | 97.59% | - | 97.43% | - | 97.51% |
| Jemal, Ines, et al. [19] | 98.1% | - | - | - | - | - |
| Alaoui, Rokia Lamrani [20] | 78.95% | 78.41% | - | 81.54% | - | 77.57% |
| Mohamed, S.M. & Rohaim, M.A. [21] | 99.66% | 99.28% | - | 99.18% | - | 99.22% |
| Shahid, Waleed Bin, et al. [22] | 98.73% | 98.87% | 98.33% | 99.41% | 1.67% | 99.13% |
| Moarref, N., & Sandikkaya, M. T. [23] | 99.36% | 98.80% | - | 99.65% | - | 99.22% |
| Proposed Model | 97.58% | 97.52% | 99.76% | 99.99% | 0.2% | 98.74% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




