Submitted:
02 March 2025
Posted:
03 March 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Literature Review
3. Proposed Methodology
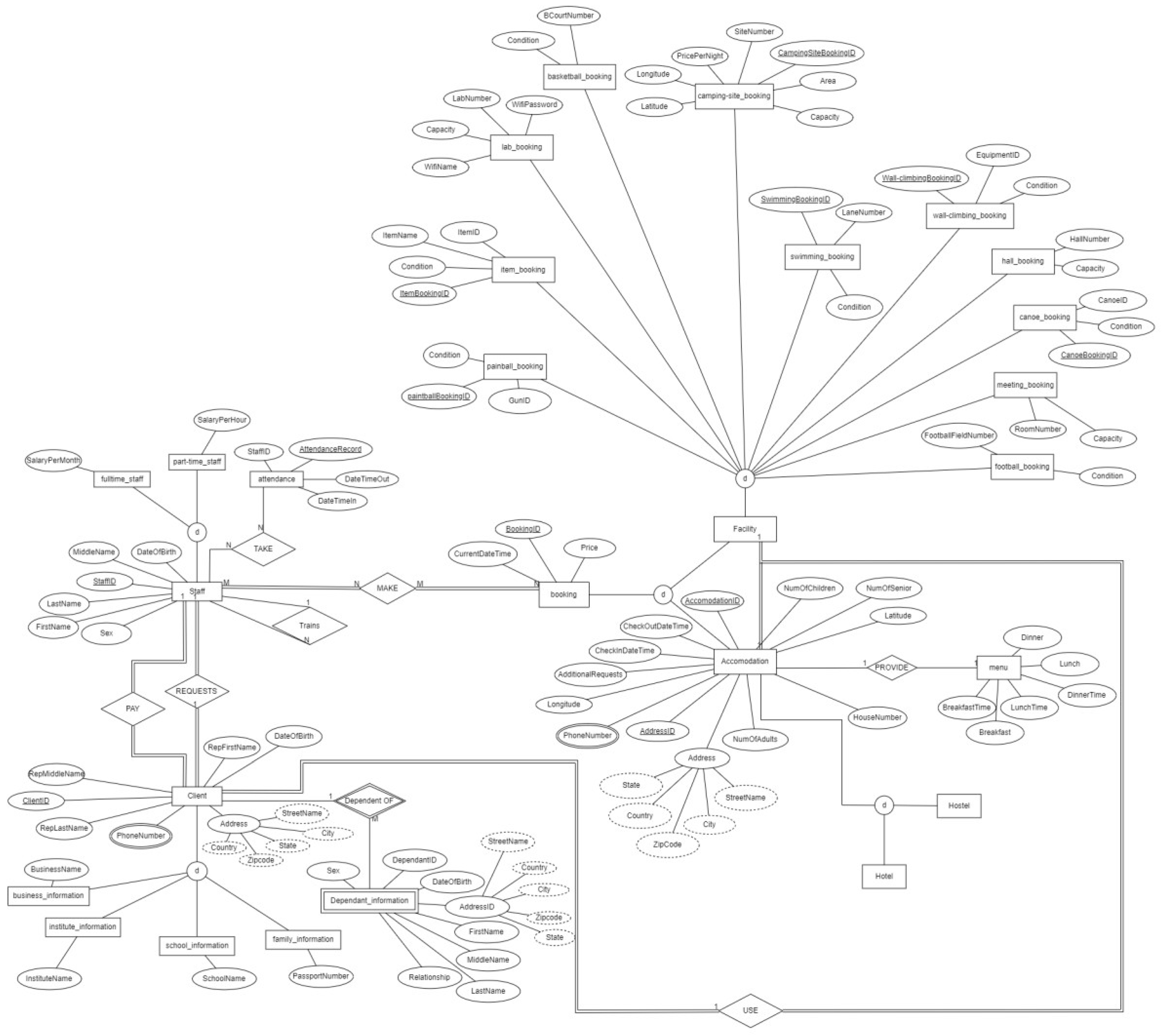
4. Entity-Relationship Diagram (ERD)
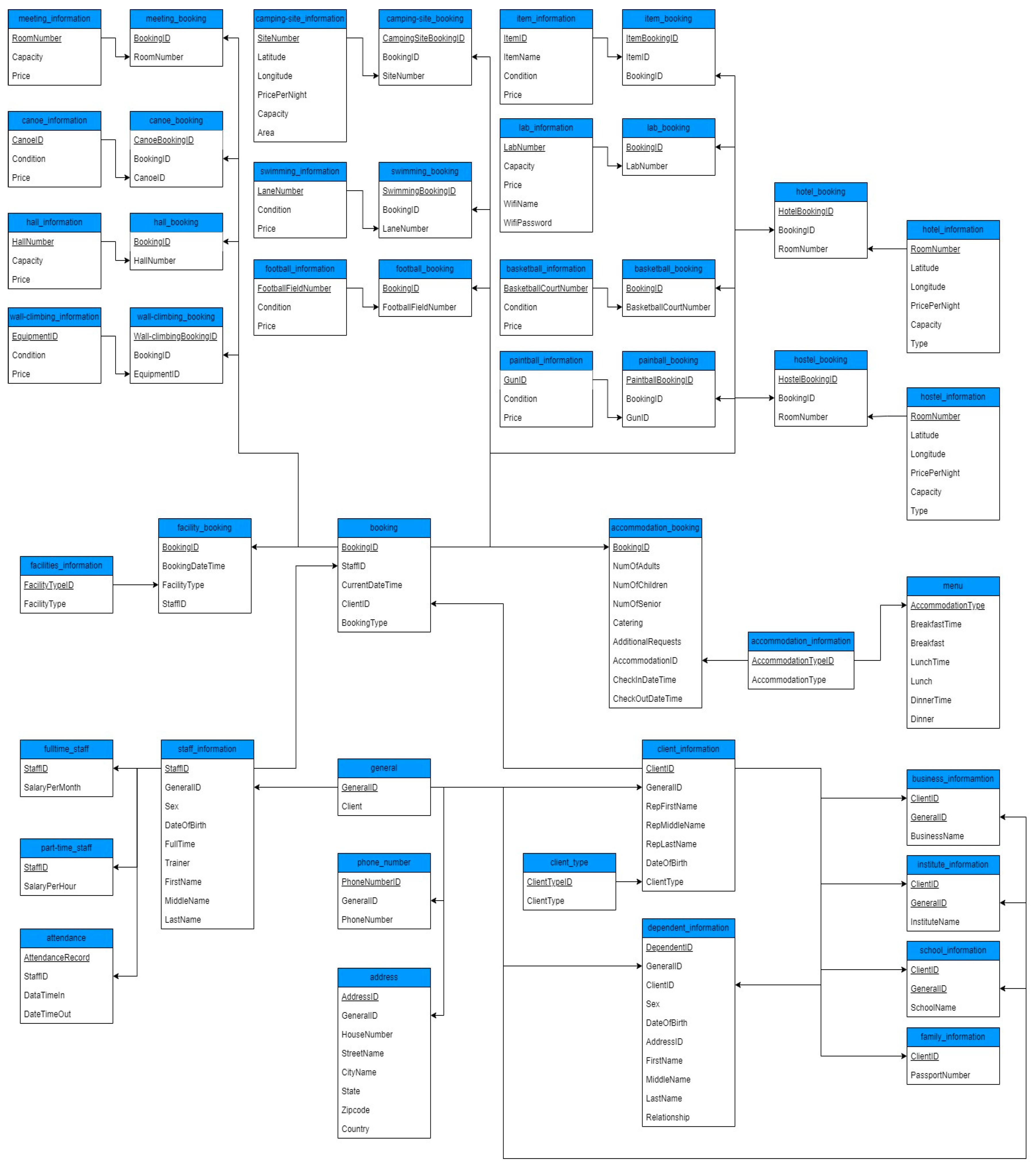
4.1. Physical Model
4.2. Results and Discussion
4.2.1. Data Integrity and Consistency
4.2.2. Scalability and Adaptability of the System
4.2.3. Analytical Insights and Business Intelligence
4.2.4. Challenges and Limitations
5. Unforeseen Challenges
6. Conclusions
References
- Lee, J. M., Jung, I. H., & Hwang, K. (2022). Design and Implementation of Database for Shared Facility Reservation System in School. Journal of Positive School Psychology, 6(8), 7033-7041.
- Williams, K., & Micheal, A. (2018). Design and Implementation of Reservation Management System Case Study: Grand Ville Hotels. Journal of Information Technology & Software Engineering, 8(04), 1-10.
- Chogo, O. J., & Musinga, J. (2012). Design and implementation of an interactive secure patient appointment booking information system: a case study Kibuli Muslim Hospital (Doctoral dissertation, Kampala International University, School of Computing and Information Technology (SCIT)).
- Amin, N. U., Alsukhailah, A. A., Ghaleb, A. A. F., Mobarak, M. A. A., Algaafari, H. A., Algaafari, H. W., & Zaman, S. (2025). Design and Implementation of a Database System for Event Management Customizer (EMC): A Case-Based Approach.
- Kamil, J., & Amer, M. (2023). An Integrated Room Booking and Access Control System for Public Spaces.
- Saeed, S., & Abdullah, A. (2021). Combination of brain cancer with hybrid K-NN algorithm using statistical analysis of cerebrospinal fluid (CSF) surgery. International Journal of Computer Science and Network Security, 21(2), 120-130.
- Saeed, S., & Abdullah, A. (2019). Analysis of lung cancer patients for data mining tool. International Journal of Computer Science and Network Security, 19(7), 90-105.
- Saeed, S., Abdullah, A., Jhanjhi, N. Z., Naqvi, M., & Nayyar, A. (2022). New techniques for efficiently k-NN algorithm for brain tumor detection. Multimedia Tools and Applications, 81(13), 18595-18616. [CrossRef]
- Saeed, S. (2021). Optimized hybrid prediction method for lung metastases. Artificial Intelligence in Medicine.
- Saeed, S., Abdullah, A., & Naqvi, M. (2019). Implementation of Fourier transformation with brain cancer and CSF images. Indian Journal of Science & Technology, 12(37), 1-16. [CrossRef]
- Ronald, W. E., & Fredrick, J. (2009). Design and implementation of an online airline booking system using PHP, MYSQL, JAVA script and cascading style sheets (Doctoral dissertation, Kampala International University, School of Computing and Information Technology).
- Magnifique, U. M. U. R. E. R. W. A. (2024). ONLINE BOOKING WEDDING VENUE MANAGEMENT SYSTEM Case study: AmaliTech (Doctoral dissertation, ULK).
- Maulana, R. A., Fatih, M. A., Suto, L. A., & Darwis, M. (2024). Development of Paramadina Roomhub Application As Room Booking System Using Waterfall Method. JISA (Jurnal Informatika dan Sains), 7(2), 176-185.
- Kumar, M. S., Vimal, S., Jhanjhi, N. Z., Dhanabalan, S. S., & Alhumyani, H. A. (2021). Blockchain-based peer-to-peer communication in autonomous drone operation. Energy Reports, 7, 7925-7939. [CrossRef]
- Jhanjhi, N. Z., Humayun, M., & Almuayqil, S. N. (2021). Cybersecurity and privacy issues in industrial Internet of Things. Computer Systems Science & Engineering, 37(3). [CrossRef]
- Lee, S., Abdullah, A., & Jhanjhi, N. Z. (2020). A review on honeypot-based botnet detection models for smart factory. International Journal of Advanced Computer Science and Applications, 11(6). [CrossRef]
- Khan, N. A., Jhanjhi, N. Z., Brohi, S. N., Almazroi, A. A., & Almazroi, A. A. (2022). A secure communication protocol for unmanned aerial vehicles. CMC-Computers, Materials & Continua, 70(1), 601-618. [CrossRef]
- Brohi, S. N., Jhanjhi, N. Z., Brohi, N. N., & Brohi, M. N. (2023). Key applications of state-of-the-art technologies to mitigate and eliminate COVID-19. Authorea Preprints.
- Gill, S. H., Razzaq, M. A., Ahmad, M., Almansour, F. M., Haq, I. U., Jhanjhi, N. Z., ... & Masud, M. (2022). Security and privacy aspects of cloud computing: a smart campus case study. Intelligent Automation & Soft Computing, 31(1), 117-128. [CrossRef]
- Muzafar, S., & Jhanjhi, N. Z. (2020). Success stories of ICT implementation in Saudi Arabia. In Employing Recent Technologies for Improved Digital Governance (pp. 151-163). IGI Global.
- Shah, I. A., Jhanjhi, N. Z., & Laraib, A. (2023). Cybersecurity and blockchain usage in contemporary business. In Handbook of Research on Cybersecurity Issues and Challenges for Business and FinTech Applications (pp. 49-64). IGI Global.
- Aldughayfiq, B., Ashfaq, F., Jhanjhi, N. Z., & Humayun, M. (2023). Explainable AI for retinoblastoma diagnosis: interpreting deep learning models with LIME and SHAP. Diagnostics, 13(11), 1932. [CrossRef]
- Aherwadi, N., Mittal, U., Singla, J., Jhanjhi, N. Z., Yassine, A., & Hossain, M. S. (2022). Prediction of fruit maturity, quality, and its life using deep learning algorithms. Electronics, 11(24), 4100.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



