Submitted:
27 January 2025
Posted:
28 January 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Related Work
3. Preliminaries
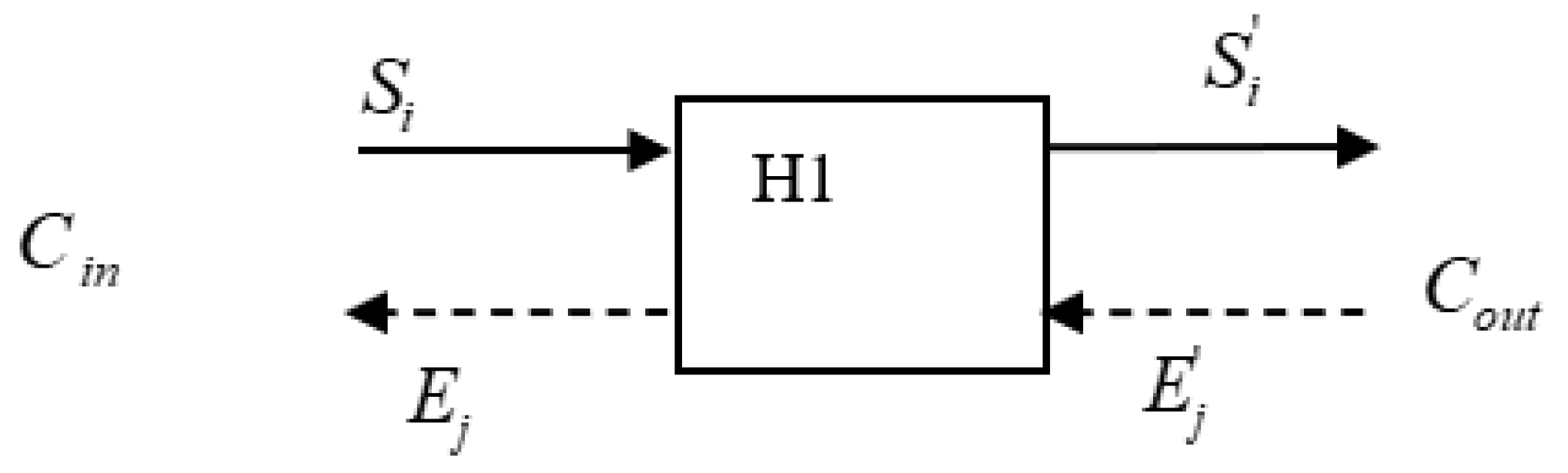
3.1. A Matched Pair of a Send Packet and its Corresponding Echo
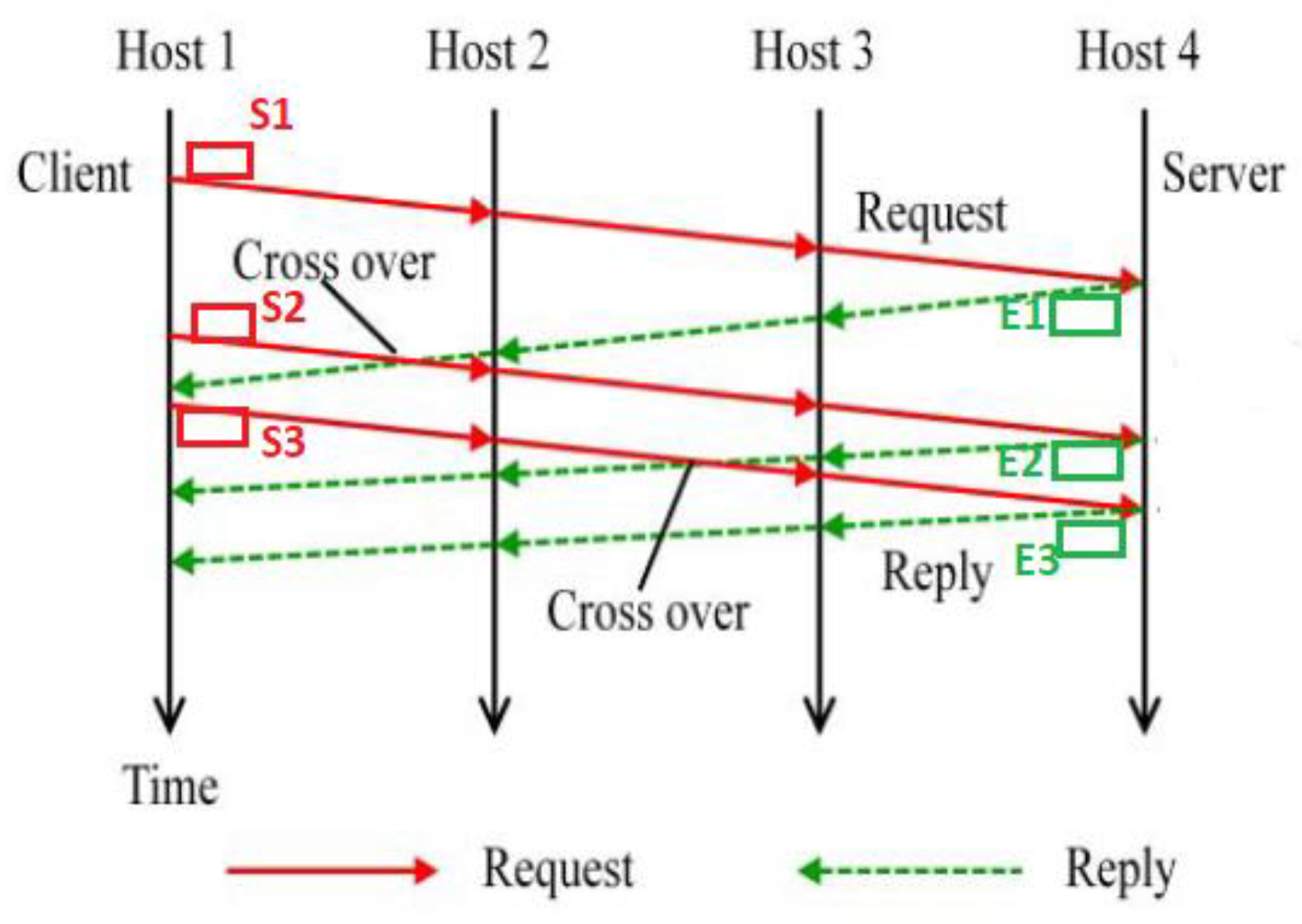
3.2. Crossover of Packets
4. Matching Packets Using Packet Crossover for Network Traffic with Chaff
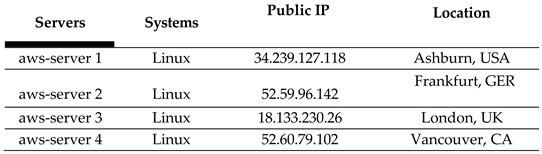
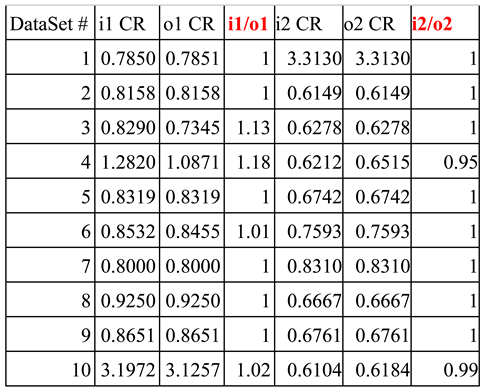
5. Network Experimental Results and Analysis
6. Conclusion and Future Work
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- S. Staniford-Chen, and L. T. Heberlein, “Holding Intruders Accountable on the Internet,” Proc. IEEE Symposium on Security and Privacy, Oakland, CA, 39-49, 1995. [CrossRef]
- Y. Zhang, and V. Paxson, “Detecting Stepping-Stones,” Proc. of the 9th USENIX Security Symposium, Denver, CO, 67-81, August 2000.
- D. Donoho, A. Flesia, U. Shankar, V. Paxson, J. Coit, and S. Staniford, “Multiscale stepping-stone detection: Detecting pairs of jittered interactive streams by exploiting maximum tolerable delay,” in 5th International Symposium on Recent Advances in Intrusion Detection, Lecture Notes in Computer Science, 2516, 2002. [CrossRef]
- T. He and L. Tong, “Detecting Stepping-stone Traffic in Chaff: Fundamental Limits and Robust Algorithms,” the 9th International Symposium on Recent Advances in Intrusion Detection (RAID 2006), April 2006.
- T. He, L. Tong, “Detecting encrypted stepping-stone connections,” In: Proceedings of IEEE Transaction on signal processing, 55(5), 1612-1623, 2007. [CrossRef]
- A. Blum, D. Song, And S. Venkataraman, “Detection of Interactive Stepping-Stones: Algorithms and Confidence Bounds”, Proceedings of International Symposium on Recent Advance in Intrusion Detection (RAID), Sophia Antipolis, France, 20-35, September 2004. [CrossRef]
- S. S.-H Huang, H. Zhang, and M. Phay, “Detecting Stepping-stone intruders by identifying crossover packets in SSH connections”, the Proceedings of 30th IEEE International Conference on Advanced Information Networking and Applications, Fukuoka, Japan, 1043-1050, March 2016. [CrossRef]
- Yoda, K.; Etoh, H. Finding Connection Chain for Tracing Intruders. In Proceedings of the 6th European Symposium on Research in Computer Security, Toulouse, France, 4–6 October 2000; Volume 1985, pp. 31–42.
- L. Wang, J. Yang, and A. Lee, “An Effective Approach for Stepping-Stone Intrusion Detection Using Packet Crossover,” the 377 23rd World Conference on Information Security Applications (WISA), August 24-26, 2022. [CrossRef]
- L. Wang, J. Yang, A. Lee, and P.-J. Wan: Matching TCP Packets to Detect Stepping-Stone Intrusion using Packet Crossover, Advances in Science, Technology and Engineering Systems Journal, Vol. 7, No. 6 (Nov. 2022).
- L. Wang, J. Yang, J. Kim, and P.-J. Wan: An Effective Approach for Stepping-stone Intrusion Detection Resistant to Intruders’ Chaff-Perturbation via Packet Crossover, MDPI Electronics, Vol. 12, No. 3855 (Sept. 2023).

 |
 |
 |
 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




