Submitted:
12 January 2025
Posted:
13 January 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Related Works
3. Materials and Methods
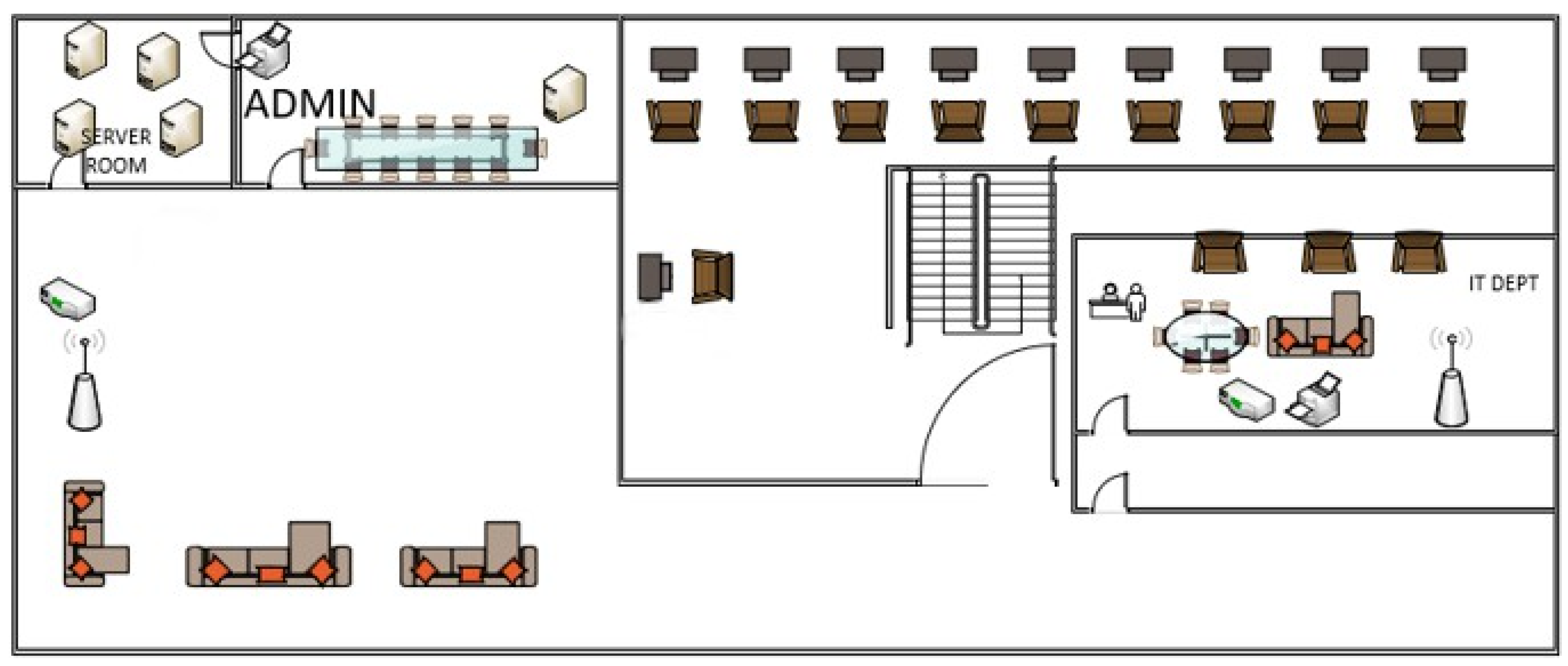
- Server Room: Incorporates four servers: Server 1, Server 2, Server 3, and another unnamed server and is the central component of the organization’s IT structure.
- Admin Room: Ideal for administrative work and small conferences and for this it requires one server, one printer and a conference table.
- Staff Room: Equipped with 10 chairs and table for workers and it can employ a sizable number of employees within the firm.
- IT Department: It has a collection of furniture such as three chairs, a 3-seater sofa, a six-seater round table, a wireless connector as well as a printer which makes Information Technology collaborative work possible.
- Reception: Has direct communication with the first line of clientele and customers
- Client Waiting Area: With furniture like 3 sofas, wireless connector and wireless access point to make clients comfortable while waiting.
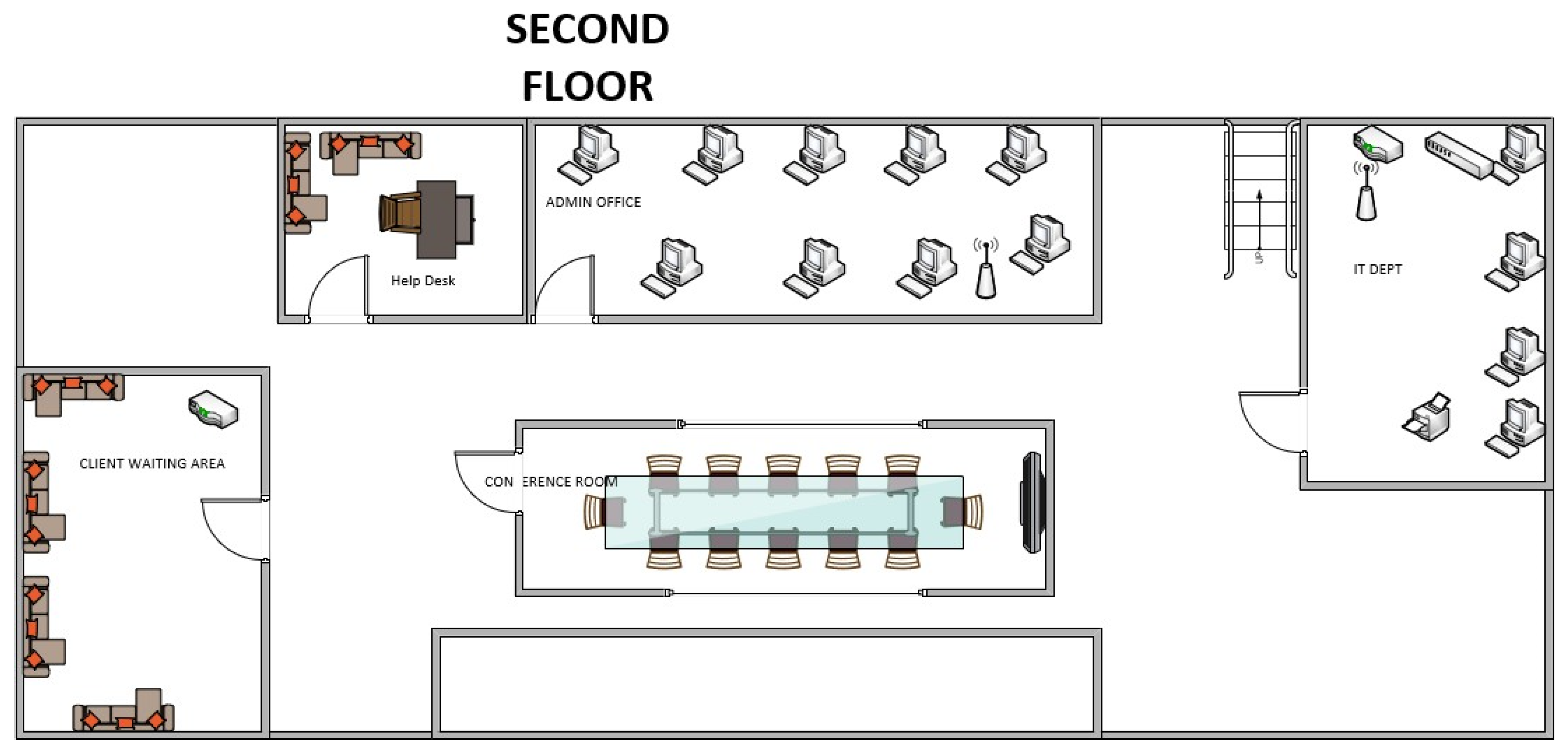
- Help Desk Room: Has 1 table with 1 chair and 2 sofas probably for interactions that may be IT support related.
- Admin Office: Located operating rooms, houses 9 computers and a wireless access point for the administrative workers.
- IT Department Room: Furnishes 4 computers, 1 printer, 1 WAP, and 1 WPC that in turn enhances IT firepower.
- Conference Room: Has a very large table for a conference also has LCD for the meetings and the presentations.
- Client Waiting Area: Has 4 sofas for 3 people each and a wireless connector for the convenience of the clients and integration purposes.
- Escalator: It helps people to move across the floors of the building or from one floor to the next.
- a)
- Internet Connectivity:
- b)
- Core Network:
- c)
- Firewall:
- d)
- Switching Infrastructure:
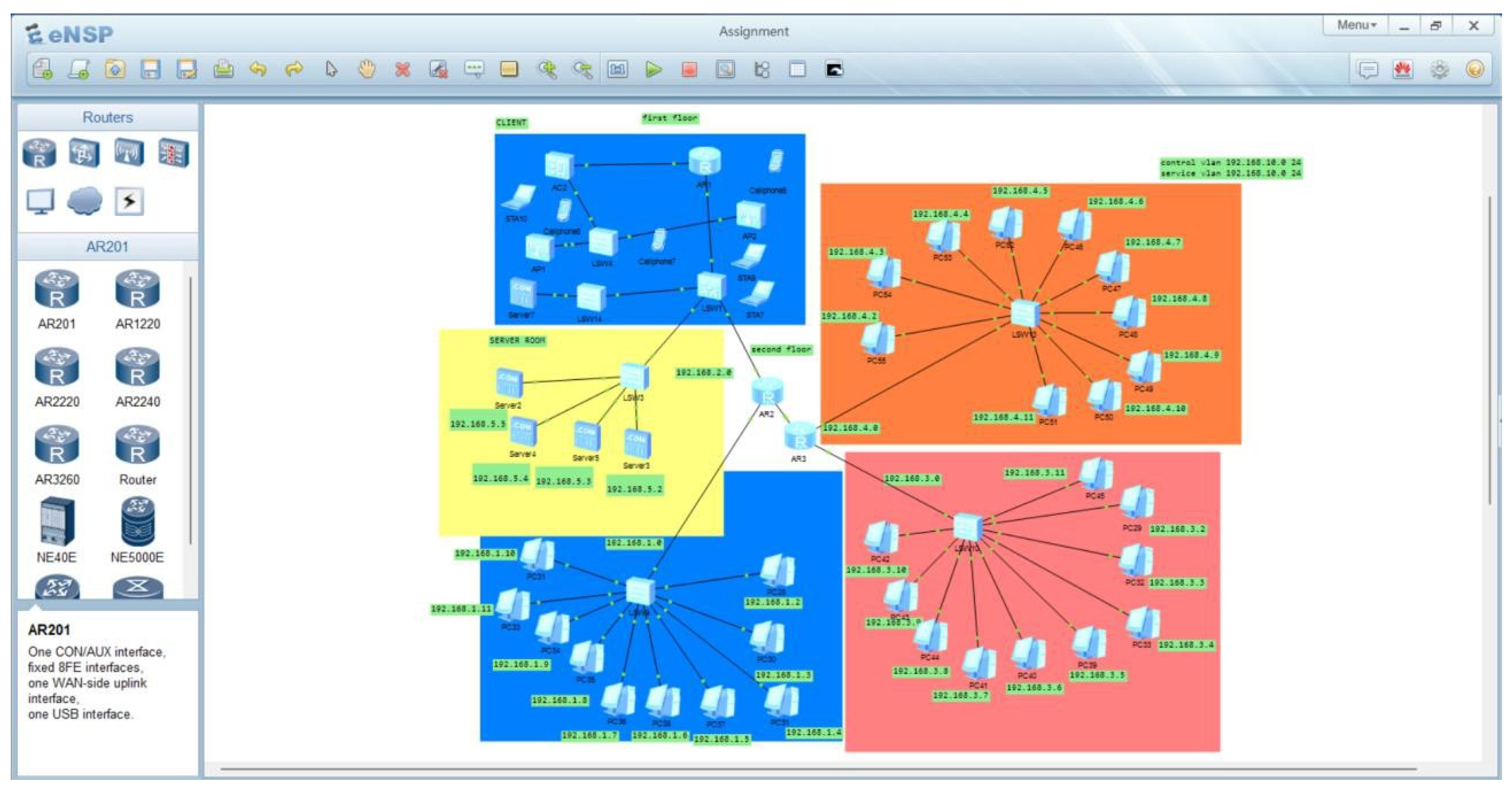
- LSW1: Primary switch for the first floor
- LSW4: Possibly a secondary switch for the first floor or a specific department
- LSW5: Connects to the server room devices
- LSW9: Primary switch for the second floor
- LSW10 and LSW11: Additional switches for the second floor, possibly for different departments
- e)
- Wireless Infrastructure:
- AP1: Located on the first floor, offering both 2.4GHz (600Mbps) and 5GHz (1300Mbps) connections
- Additional access points are presumed on the second floor, though not explicitly shown in the diagram
- f)
- Server Infrastructure:
- Server1 (192.168.40.1): Likely a primary application or file server
- Server2 and Server3: Additional servers for various services or redundancy
- An unnamed server, possibly for backup or specific applications
- g)
- VLAN Configuration:
- Control VLAN: 192.168.10.0/24
- Service VLAN: 192.168.10.0/24 (Note: This appears to be a typo in the diagram and should likely be a different subnet)
- h)
- IP Addressing Scheme:
- 192.168.1.0/24: Network department first floor
- 192.168.2.0/24: Second floor general network
- 192.168.3.0/24: Core router network
- 192.168.40.0/24: Admin and server network
- 192.168.42.0/24: Additional subnet, possibly for specific departments or services
- 1.
- First Floor Configuration:
- Admin area: PC1 (192. 168. 40. 2) and PC2 are connected, most probably for the administrative employees of the given company.
- Server room: Connected via LSW5, which hosts the main servers for the base of operations.
- Staff area: Another wired connectivity for the employees is appended as Multiple PCs such as PC7, PC9 and so on connect.
- Wireless: AP1 offers a 2. 4 GHZ band and the 5. 0 GHZ band to ensure that the devices in the residence are all covered.
- 2.
- Second Floor Configuration:
- Admin office: LAN connected Pcs (PC28, pc 29, PC30, PC31 etc.) for office related works.
- IT Department: PC and printers linked for employees especially the IT team.
- Wireless: Though not illustrated, it is understood that access point offers wireless coverage.
- 3.
- Inter-floor Connectivity:
- 4.
- Wireless Coverage:
- Smoking is prohibited in any area of the hospital, and there is no smoking areas located within any parts of AP1 on the first floor. The length of the stay is between 2. 4 distributed in a range of 4GHz and 5GHz bands that cater for all devices’ requirements.
- As it is, extra access points placed on the second floor are not illustrated, yet they would guarantee coverage.
- The dual-band provision boosts speeds which on 5GHz can go up to 1300Mbps for compatible devices while supporting older 2. 4GHz devices
- 5.
- Employee Connectivity:
- Wired: A local area network connection of Ethernet type is provided at each workstation and in the shared spaces.
- Wireless: There is dual band coverage Wi-Fi to guarantee multiple device connection for the employees in the firm without the usual wired connection.
- 6.
- Client Areas:
- 7.
- Scalability:
- 8.
-
Security Considerations:
- VLAN segmentation came into the limelight as organization started adopting networking to powerfully segment separated portions of an organization so as to bring about security.
- The art imagined to be situated at the network periphery shields against external threats
- Organization of subnets that provide exclusive areas for certain departments (for example, admin, staff, IT) makes the process more detailed concerning access to certain channels.
- 9.
-
Performance:
- Gigabit switches (inferred from the network design) guarantee a network bandwidth of gigabit to wired devices.
- The feature of the dual-band wireless setup is also usable for attaining the high- speed wireless connection which is vital in the business of the current world.
- 10.
- Redundancy:
4. Star Topology Overview:
- 1.
- Centralized Management:
- 2.
- Scalability:
- 3.
- Performance Optimization:
- 4.
- Fault Isolation:
- 5.
- Ease of Troubleshooting:
- Recommendations:
Conclusion
References
- Forouzan, B. A. (2012). Data Communications and Networking. McGraw-Hill Education.
- Jordão, R. V. D., & Novas, J. C. (2024). Information and knowledge management, intellectual capital, and sustainable growth in networked small and medium enterprises. Journal of the Knowledge Economy, 15(1), 563-595. [CrossRef]
- Valeri, M., & Baggio, R. (2021). Italian tourism intermediaries: A social network analysis exploration. Current Issues in Tourism, 24(9), 1270-1283. [CrossRef]
- Moisio, T. (2022). Capacity planning in network architecture: Strategies for sustainable growth. Network Design Journal.
- HP Networking. (2022). Unified network solutions for mobility and BYOD policies. HP Networking White Paper.
- ComScore. (2022). Modern IT infrastructure for mid-sized businesses: Building scalable solutions. ComScore Insights.
- AIMMS. (2022). Case studies in strategic network planning for supply chain optimization. AIMMS White Paper.
- Meter.com. (2022). Custom network design for corporate and retail environments. Meter Blog.
- Opex Analytics. (2022). Network design in mergers and acquisitions: Ensuring seamless integration. Opex Analytics Reports.
- Lex Technology. (2024). Network design basics for small and medium-sized businesses. Lex Technology White Paper.
- Jejeniwa, T.O., Mhlongo, N.Z., & Jejeniwa, T.O. (2024). A comprehensive review of the impact of artificial intelligence on modern accounting practices and financial reporting. Computer Science & IT Research Journal, 5(4), 1031-1047. [CrossRef]
- Roux, M., Chowdhury, S., Kumar Dey, P., Vann Yaroson, E., Pereira, V., & Abadie, A. (2023). Small and medium-sized enterprises as technology innovation intermediaries in sustainable business ecosystem: interplay between AI adoption, low carbon management and resilience. Annals of Operations Research, 1-50.
- Ediae, A.A., Chikwe, C.F., & Kuteesa, K.N. (2024). Empowering youth through sexuality and leadership education: Approaches and outcomes. World Journal of Advanced Research and Reviews, 22(1), 1250-1265.
- Adenekan, O.A., Ezeigweneme, C., & Chukwurah, E.G. (2024). Driving innovation in energy and telecommunications: next-generation energy storage and 5G technology for enhanced connectivity and energy solutions. International Journal of Management & Entrepreneurship Research, 6(5), 1581-1597. [CrossRef]
- Joel O. T., & Oguanobi V. U. (2024). Data-driven strategies for business expansion: Utilizing predictive analytics for enhanced profitability and opportunity identification. International Journal of Frontiers inEngineering and Technology Research, 2024, 06(02), 071–081. [CrossRef]
- Kaushik, P., Rao, A.M., Singh, D.P., Vashisht, S., & Gupta, S. (2021, November). Cloud computing and comparison based on service and performance between Amazon AWS, Microsoft Azure, and Google Cloud. In 2021 International Conference on Technological Advancements and Innovations (ICTAI) (pp. 268-273). IEEE.
- Shoetan, P.O., Oyewole, A.T., Okoye, C.C., Ofodile, O.C. (2024). Reviewing the role of big data analytics in financial fraud detection. Finance & Accounting Research Journal, 6(3), 384-394. [CrossRef]
- Nihar, A., Ciardi, T.G., Chawla, R., Akanbi, O., Chaudhary, V., Wu, Y., & French, R.H. (2023, December). Accelerating time to science using CRADLE: a framework for materials data science. In 2023 IEEE 30th International Conference on High Performance Computing, Data, and Analytics (HiPC) (pp. 234-245). IEEE.
- Gopi, R., Sathiyamoorthi, V., Selvakumar, S., Manikandan, R., Chatterjee, P., Jhanjhi, N. Z., & Luhach, A. K. (2022). Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things. Multimedia Tools and Applications, 1-19.
- Dogra, V., Singh, A., Verma, S., Kavita, Jhanjhi, N.Z., Talib, M.N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In: Peng, SL., Hsieh, SY., Gopalakrishnan, S., Duraisamy, B. (eds) Intelligent Computing and Innovation on Data Science. Lecture Notes in Networks and Systems, vol 248. Springer, Singapore. [CrossRef]
- Alex, S. A., Jhanjhi, N. Z., Humayun, M., Ibrahim, A. O., & Abulfaraj, A. W. (2022). Deep LSTM model for diabetes prediction with class balancing by SMOTE. Electronics, 11(17), 2737. [CrossRef]
- Chesti, I. A., Humayun, M., Sama, N. U., & Jhanjhi, N. Z. (2020, October). Evolution, mitigation, and prevention of ransomware. In 2020 2nd International Conference on Computer and Information Sciences (ICCIS) (pp. 1-6). IEEE.
- Alkinani, M. H., Almazroi, A. A., Jhanjhi, N. Z., & Khan, N. A. (2021). 5G and IoT based reporting and accident detection (RAD) system to deliver first aid box using unmanned aerial vehicle. Sensors, 21(20), 6905. [CrossRef]
- Alferidah, D. K., & Jhanjhi, N. Z. (2020, October). Cybersecurity impact over bigdata and iot growth. In 2020 International Conference on Computational Intelligence (ICCI) (pp. 103-108). IEEE.
- Humayun, M., Jhanjhi, N. Z., Hamid, B., & Ahmed, G. (2020). Emerging smart logistics and transportation using IoT and blockchain. IEEE Internet of Things Magazine, 3(2), 58-62. [CrossRef]
- Srinivasan, K., Garg, L., Chen, B. Y., Alaboudi, A. A., Jhanjhi, N. Z., Chang, C. T., ... & Deepa, N. (2021). Expert System for Stable Power Generation Prediction in Microbial Fuel Cell. Intelligent Automation & Soft Computing, 30(1).
- Humayun, M., Niazi, M., Jhanjhi, N. Z., Mahmood, S., & Alshayeb, M. (2023). Toward a readiness model for secure software coding. Software: Practice and Experience, 53(4), 1013-1035. [CrossRef]
- Mughal, M. A., Ullah, A., Cheema, M. A. Z., Yu, X., & Jhanjhi, N. Z. (2024). An intelligent channel assignment algorithm for cognitive radio networks using a tree-centric approach in IoT. Alexandria Engineering Journal, 91, 152-160. [CrossRef]
- Konatham, B., Simra, T., Amsaad, F., Ibrahem, M. I., & Jhanjhi, N. Z. (2024). A Secure Hybrid Deep Learning Technique for Anomaly Detection in IIoT Edge Computing. Authorea Preprints.
| Device name | Ip address | Subnet mask | gateway |
|---|---|---|---|
| STA 10 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| Cell phone 7 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| Cell phone 6 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| Device name | Ip address | Subnet mask | gateway |
|---|---|---|---|
| STA 7 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| STA 9 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| Cell phone 5 | PROVIDED by AC2 | 255.255.255.0 | 192.168.10.0 |
| Device name | Ip address | Subnet mask | gateway |
|---|---|---|---|
| Pc29 | 192.168.3.2 | 255.255.255.0 | 192.168.3.0 |
| Pc 32 | 192.168.3.3 | 255.255.255.0 | 192.168.3.0 |
| Pc 33 | 192.168.3.4 | 255.255.255.0 | 192.168.3.0 |
| Pc 39 | 192.168.3.5 | 255.255.255.0 | 192.168.3.0 |
| Pc 40 | 192.168.3.6 | 255.255.255.0 | 192.168.3.0 |
| Pc 41 | 192.168.3.7 | 255.255.255.0 | 192.168.3.0 |
| Pc 42 | 192.168.3.8 | 255.255.255.0 | 192.168.3.0 |
| Pc 43 | 192.168.3.9 | 255.255.255.0 | 192.168.3.0 |
| Pc 44 | 192.168.3.10 | 255.255.255.0 | 192.168.3.0 |
| Pc 45 | 192.168.3.11 | 255.255.255.0 | 192.168.3.0 |
| Device name | Ip address | Subnet mask | gateway |
|---|---|---|---|
| Pc28 | 192.168.1.2 | 255.255.255.0 | 192.168.1.0 |
| Pc 30 | 192.168.1.3 | 255.255.255.0 | 192.168.1.0 |
| Pc 31 | 192.168.1.4 | 255.255.255.0 | 192.168.1.0 |
| Pc 37 | 192.168.1.5 | 255.255.255.0 | 192.168.1.0 |
| Pc 38 | 192.168.1.6 | 255.255.255.0 | 192.168.1.0 |
| Pc 36 | 192.168.1.7 | 255.255.255.0 | 192.168.1.0 |
| Pc 35 | 192.168.1.8 | 255.255.255.0 | 192.168.1.0 |
| Pc 34 | 192.168.1.9 | 255.255.255.0 | 192.168.1.0 |
| Pc 32 | 192.168.1.10 | 255.255.255.0 | 192.168.1.0 |
| Pc 31 | 192.168.1.11 | 255.255.255.0 | 192.168.1.0 |
| Device name | Ip address | Subnet mask | gateway |
|---|---|---|---|
| Pc55 | 192.168.4.2 | 255.255.255.0 | 192.168.4.0 |
| Pc 54 | 192.168.4.3 | 255.255.255.0 | 192.168.4.0 |
| Pc 53 | 192.168.4.4 | 255.255.255.0 | 192.168.4.0 |
| Pc 52 | 192.168.4.5 | 255.255.255.0 | 192.168.4.0 |
| Pc 46 | 192.168.4.6 | 255.255.255.0 | 192.168.4.0 |
| Pc 47 | 192.168.4.7 | 255.255.255.0 | 192.168.4.0 |
| Pc 48 | 192.168.4.8 | 255.255.255.0 | 192.168.4.0 |
| Pc 49 | 192.168.4.9 | 255.255.255.0 | 192.168.4.0 |
| Pc 50 | 192.168.4.10 | 255.255.255.0 | 192.168.4.0 |
| Pc 51 | 192.168.4.11 | 255.255.255.0 | 192.168.4.0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




