Submitted:
04 January 2025
Posted:
06 January 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
Modeling Consensus
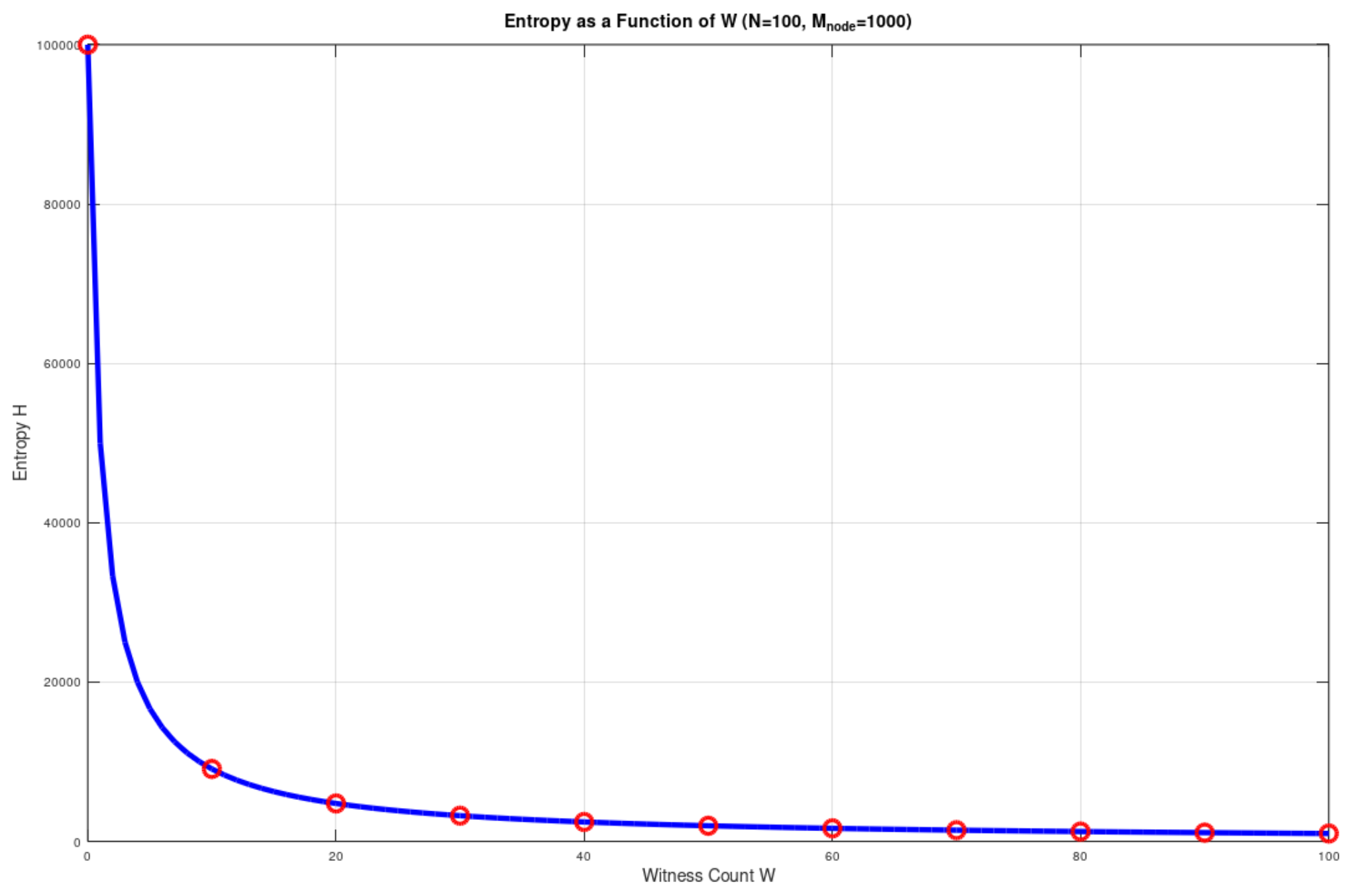
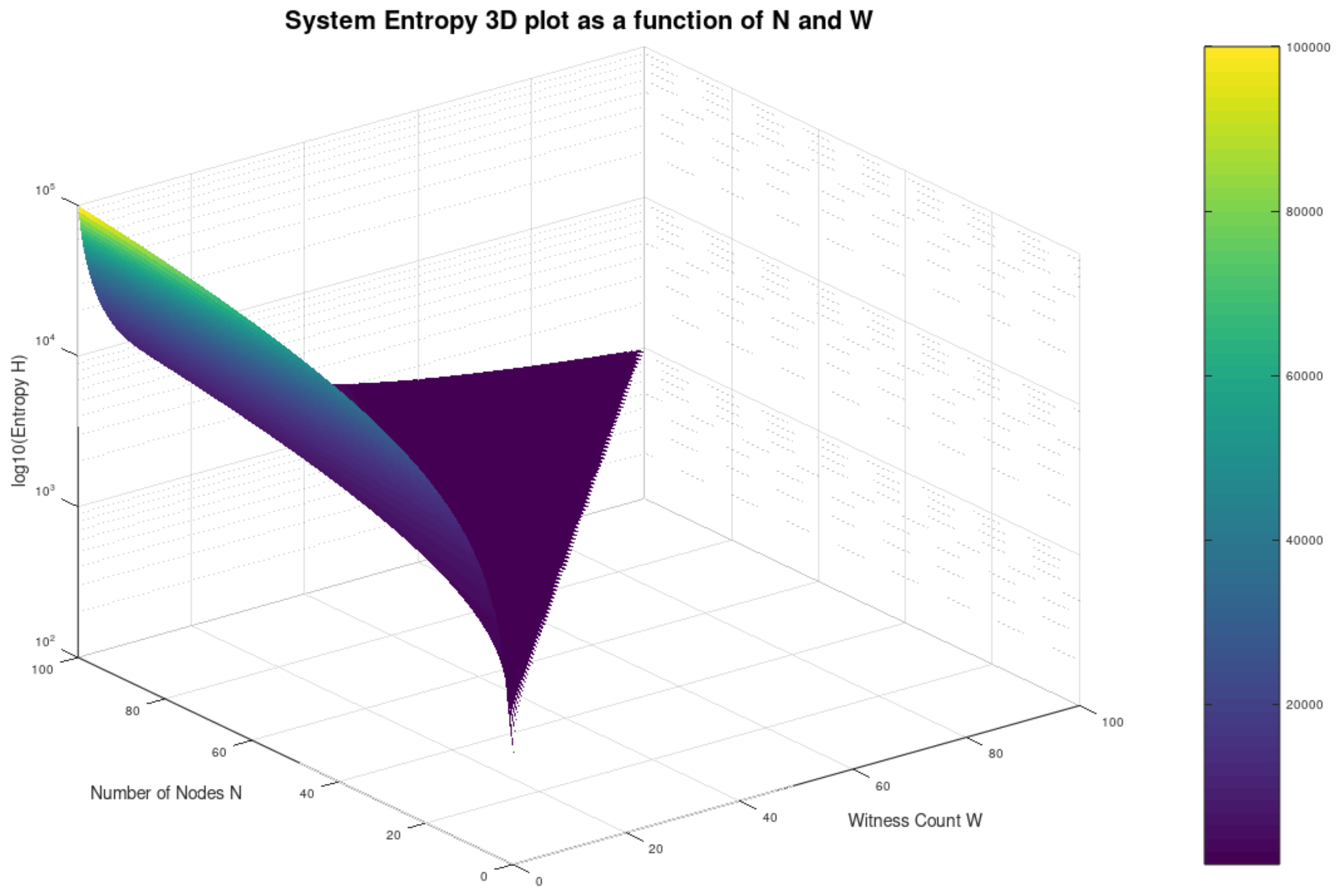
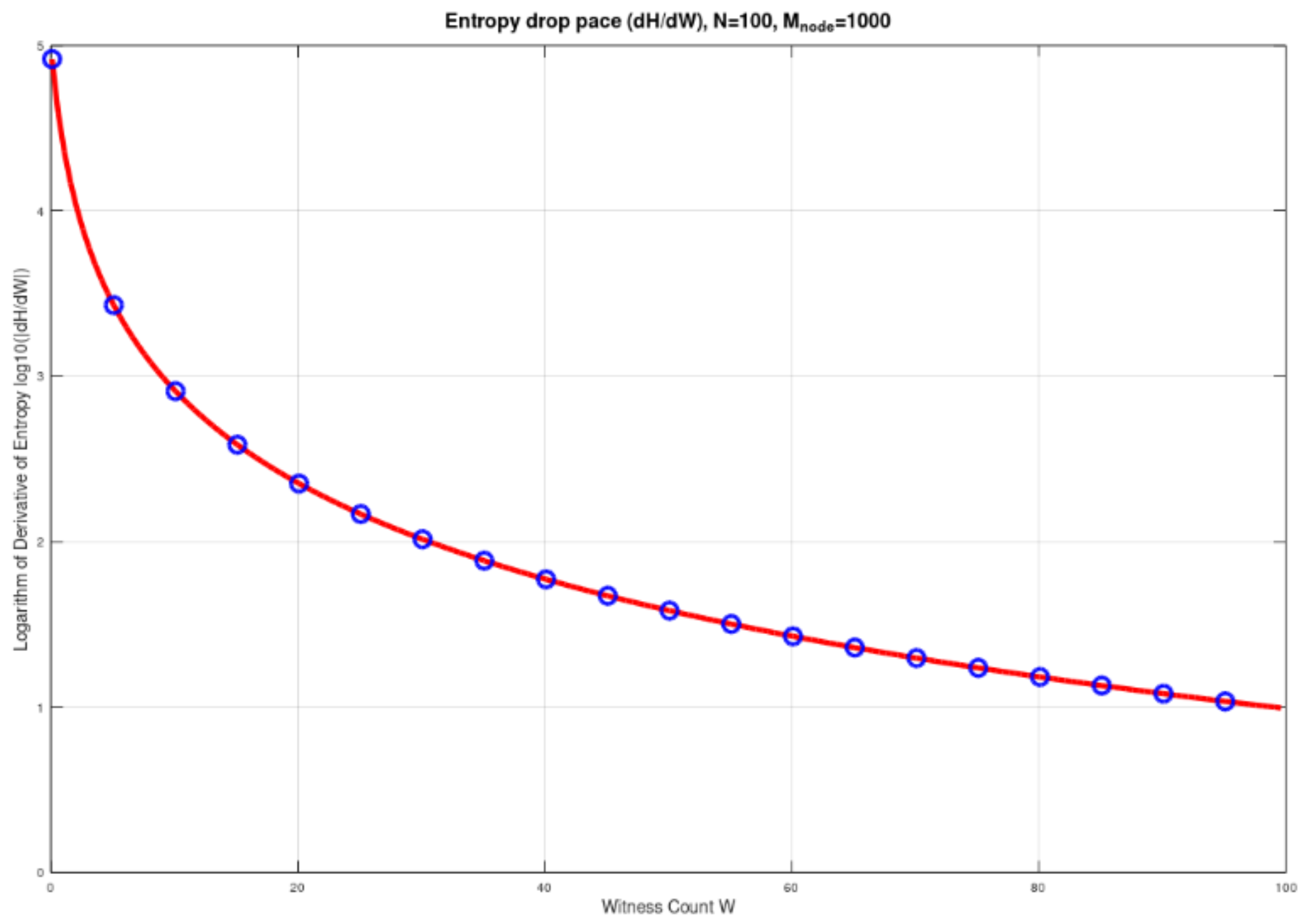
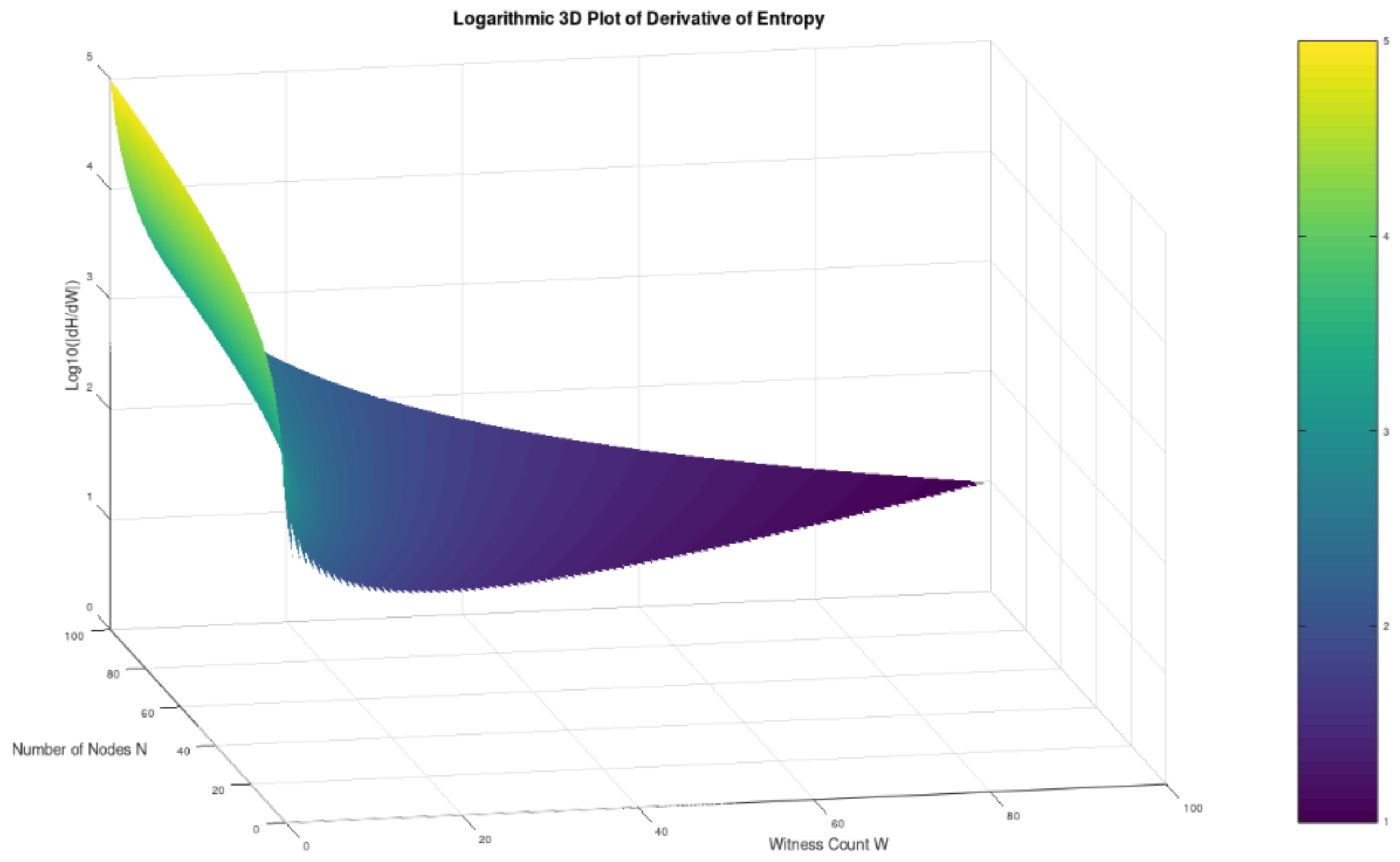
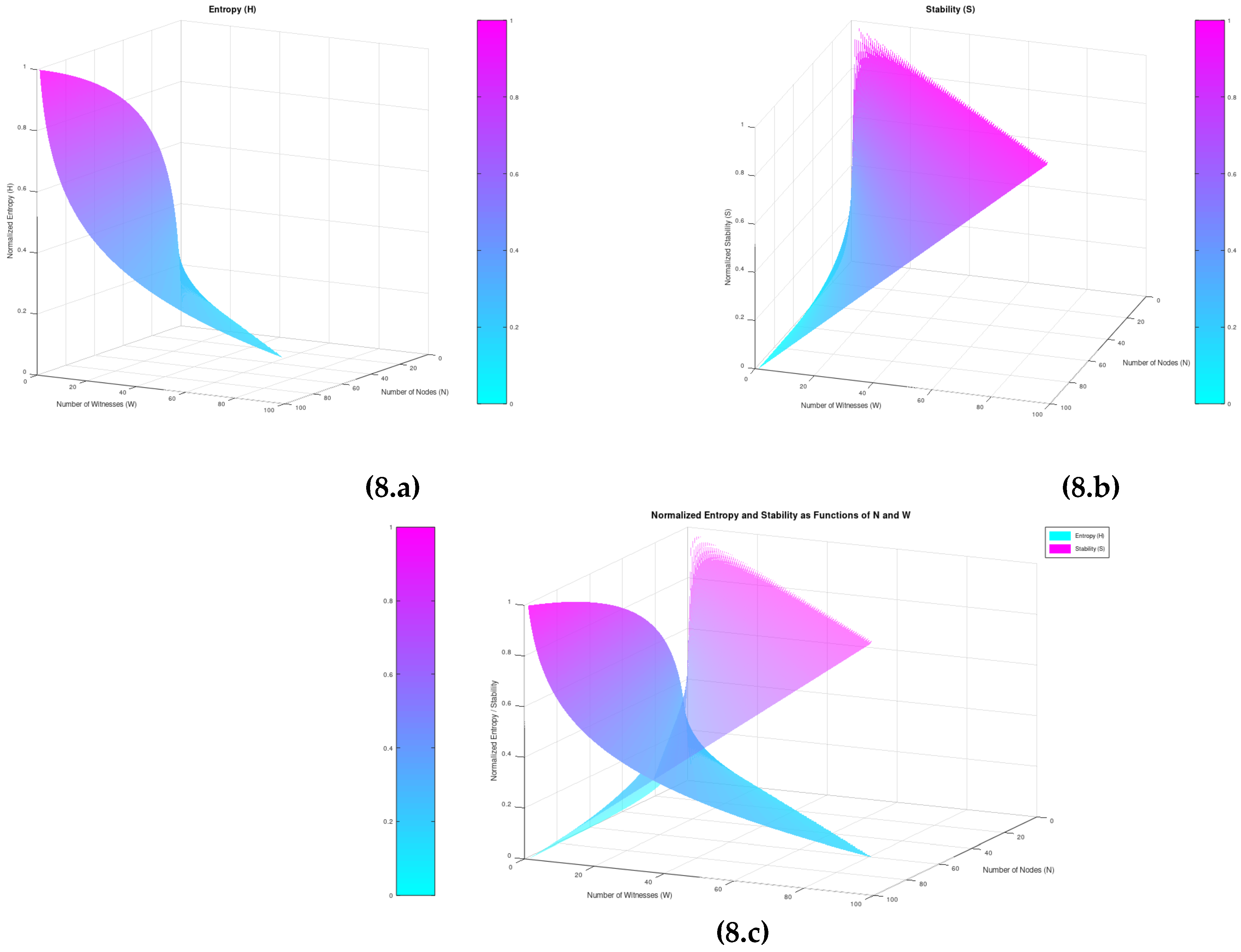
- The adoption of the Boltzmann-Shannon equation on information entropy as the basic tool for our analysis
- The modeling of consensus as a function of the number of nodes-witnesses consenting over an event (W)
- The acknowledgement of the disagreement in a system as a discrete Lyapunov stability function with respect to the number of the event-witnesses in a system
2. Materials and Methods
Consensus and Stability
- at the equilibrium point x* (the desired degree of consensus reached, typically taken as the origin x=0, for simplicity).
- for all , meaning is positive definite around the equilibrium point.
- , meaning decreases or stays constant over time, ensuring that the system does not gain energy or move away from the equilibrium.
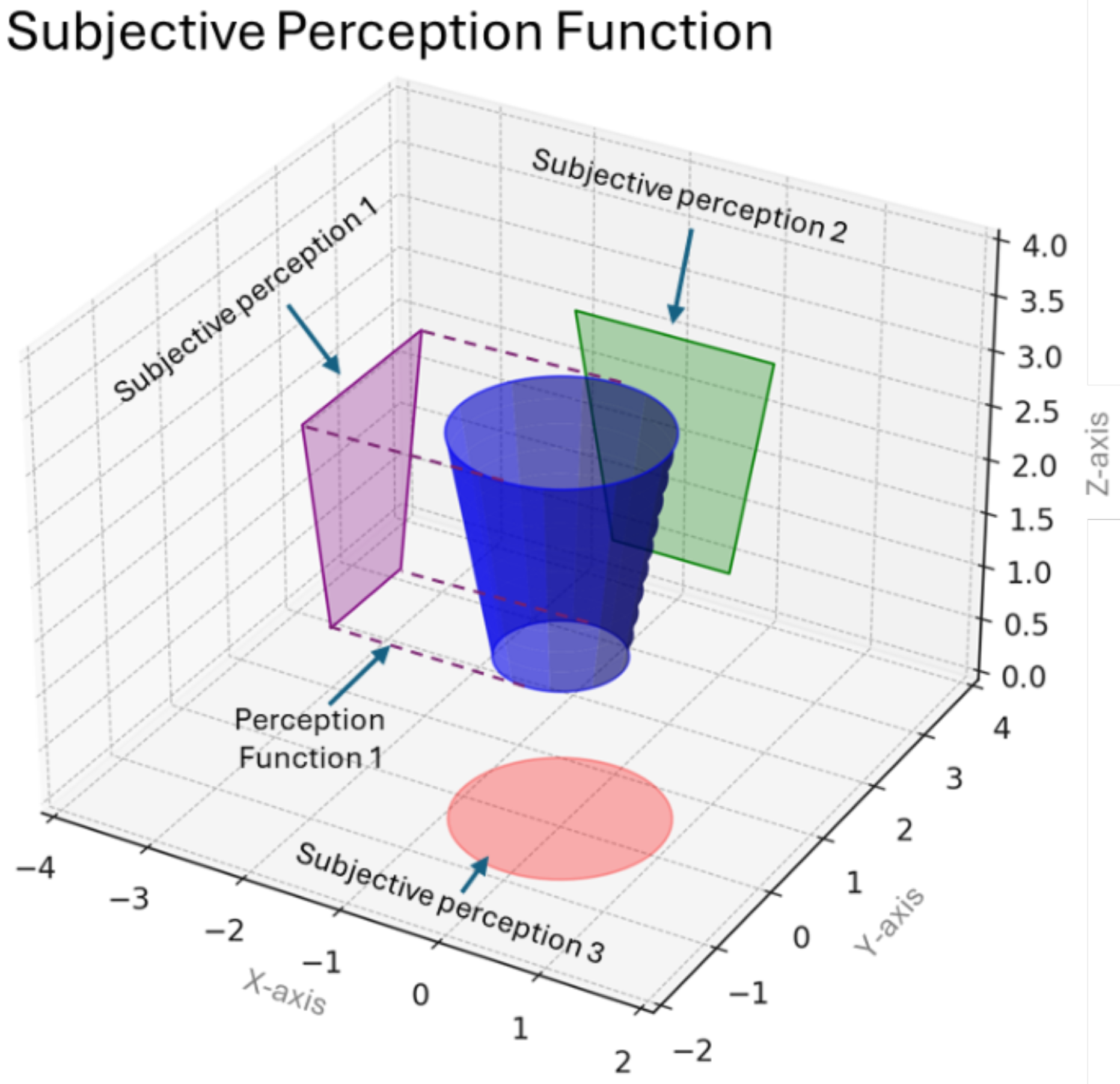
Perception and Consensus
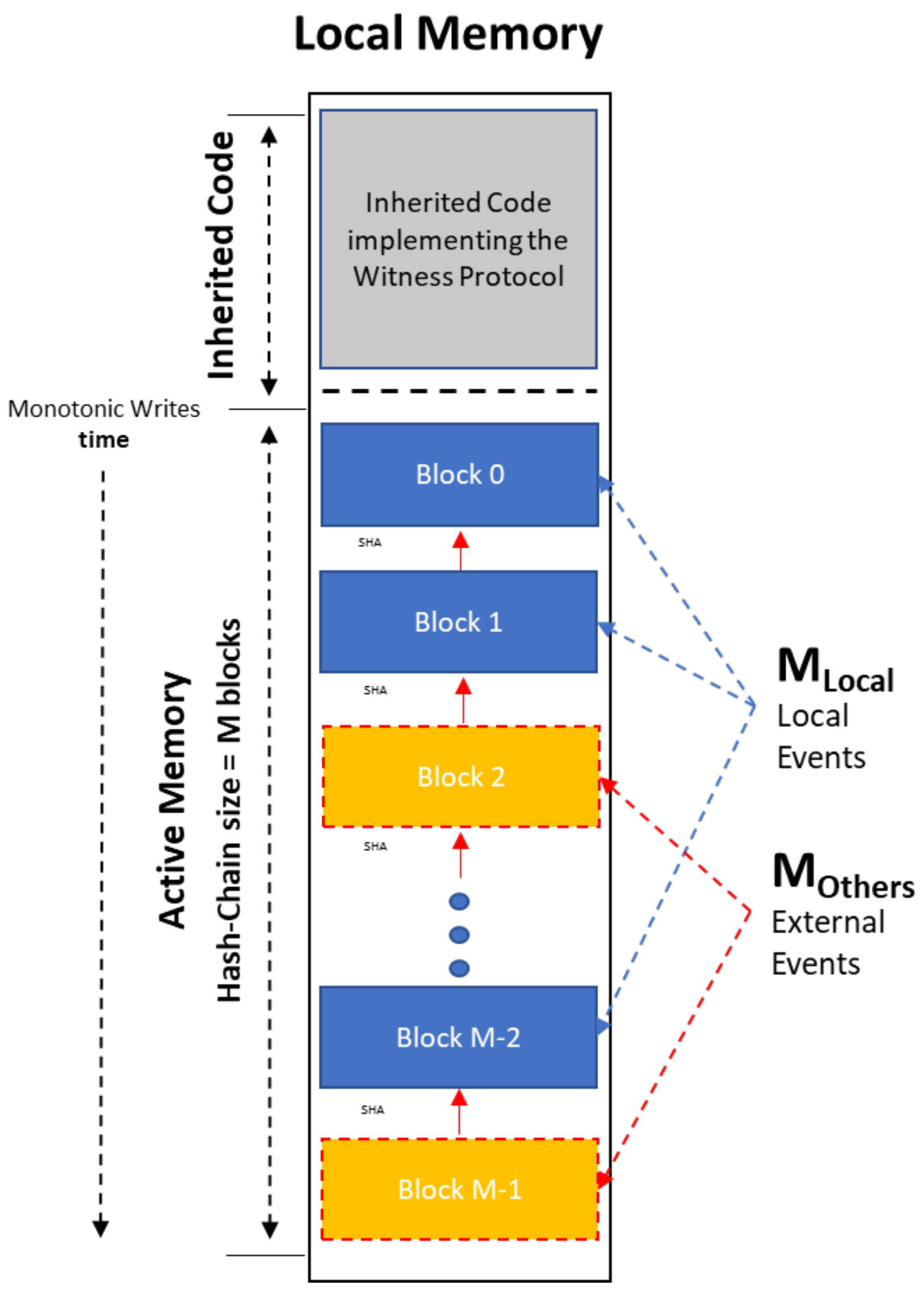
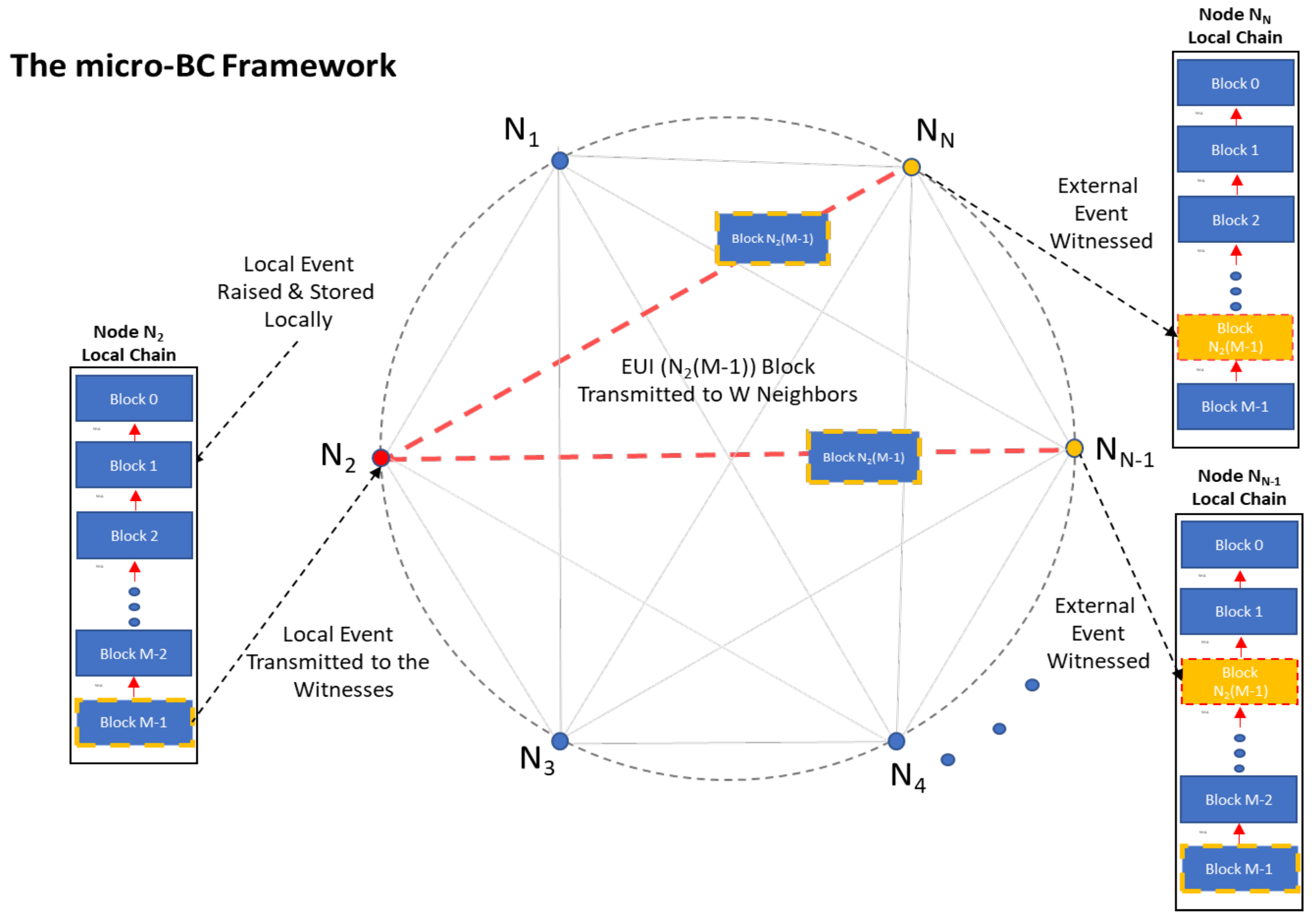
The IoT Micro-Blockchain Framework
3. Analysis and Results
4. Discussion
- The robustness of the system may take various forms, often exceeding the pure BFT consensus consideration (e.g. tolerance to physical disasters), imposing high values of W as a primeval functional mandate.
- Such functionality-redundancy mechanisms, while seen under the prism of the second law of thermodynamics are significantly energy-consuming, and thus are expected to move the overall efficiency away from optimum.
5. Conclusions
Author Contributions
Conflicts of Interest
References
- Shannon, C.E. A Mathematical Theory of Communication. Bell System Technical Journal 1948, 27, 379–423, 623–656. [CrossRef]
- Lyapunov, A.M. The General Problem of the Stability of Motion; Taylor & Francis: London, UK, 1992.
- Rivest, R.L. Cryptography and Machine Learning. In: Imai, H.; Rivest, R.L.; Matsumoto, T. (eds) Advances in Cryptology — ASIACRYPT '91. Lecture Notes in Computer Science, Vol. 739. Springer: Berlin, Heidelberg, 1993. [CrossRef]
- Laskari, E.C.; Meletiou, G.C.; Stamatiou, Y.C.; Vrahatis, M.N. Cryptography and Cryptanalysis Through Computational Intelligence. Studies in Computational Intelligence 2007, 57, 1–49. Springer-Verlag Berlin Heidelberg.
- Blum, A.; Furst, M.; Kearns, M.; Lipton, R.J. Cryptographic Primitives Based on Hard Learning Problems. In: Advances in Cryptology - CRYPT0 ’93. LNCS 773, Springer: Berlin Heidelberg, 1994; pp. 278–291.
- Laskari, E.C.; Meletiou, G.C.; Tasoulis, D.K.; Vrahatis, M.N. Studying the Performance of Artificial Neural Networks on Problems Related to Cryptography. Elsevier Nonlinear Analysis: Real World Applications 2005. [CrossRef]
- Goncharov, S.V. Using Fuzzy Bits and Neural Networks to Partially Invert Few Rounds of Some Cryptographic Hash Functions. arXiv preprint 2019. Available online: https://arxiv.org/pdf/1901.02438.pdf (accessed on March 2024).
- Anagnostakis, A.G.; Naxakis, C.; Giannakeas, N.; Tsipouras, M.G.; Tzallas, A.T.; Glavas, E. Scalable Consensus over Finite Capacities in Multiagent IoT Ecosystems. IEEE Internet of Things Journal 2022. [CrossRef]
- Anagnostakis, A.G.; Giannakeas, N.; Tsipouras, M.G.; Glavas, E.; Tzallas, A.T. IoT Micro-Blockchain Fundamentals. Sensors 2021, 21, 2784. [CrossRef]
- Graziano, M. Consciousness and the Social Brain. Oxford University Press: New York, NY, USA, 2013; ISBN: 978-0199928644.
- Aristoteles (284~322 B.C.) “Hθικά Νικομάχεια” Book 1, pp VII available online at: https://www.greek-language.gr/digitalResources/ancient_greek/library/ browse.html?text_id=78&page=8 Last Accessed May 2022.
- Heekeren, H., Marrett, S. & Ungerleider, L. The neural systems that mediate human perceptual decision making. Nat Rev Neurosci 9, 467–479 (2008). [CrossRef]
- Luu L, Stocker A. Post-decision biases reveal a self-consistency principle in perceptual inference. eLife. May 22 2018, . [CrossRef]
- Kreder, K.; Shastry, S. POEM: Proof of Entropy Minima. arXiv preprint arXiv:2303.04305, 2023. Available online: https://arxiv.org/abs/2303.04305 (accessed on June 2024).
- Lamport, L.; Shostak, R.; Pease, M. The Byzantine Generals Problem. ACM Trans. Program. Lang. Syst. 1982, 4, 382–401.
- Clausius, R. The Mechanical Theory of Heat – With Its Applications to the Steam Engine and to Physical Properties of Bodies; John van Voorst: London, UK, 1867.
- Dwork, C.; Lynch, N.; Stockmeyer, L. Consensus in the Presence of Partial Synchrony. J. ACM 1988, 35, 288–323.
- Vukolic, M. The Quest for Scalable Blockchain Fabric: Proof-of-Work vs. BFT Replication. Open Problems in Network Security 2016, 9591, 112–125. [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. Bitcoin.org, 2008. Available online: https://bitcoin.org/bitcoin.pdf (accessed on May 2024).
- Friston, K. The Free-Energy Principle: A Unified Brain Theory? Nat. Rev. Neurosci. 2010, 11, 127–138. [CrossRef]
- Andrews, M. The Free-Energy Principle: An Accessible Introduction to Its Derivations, Applications, and Implications. ResearchGate 2009, Available online: https://www.researchgate.net/publication/324246948 (accessed on December 2021).
- Schrödinger, E. What is Life? The Physical Aspect of the Living Cell; Cambridge University Press: Cambridge, UK, 1944; ISBN 978-1107604667.
- Beretta GP. The fourth law of thermodynamics: steepest entropy ascent. Phil. Trans. R. Soc. A 378: 20190168, 2020 Available online at: Accessed on Apr. 2022. [CrossRef]
- Chen, J., et al. Resilient Consensus Sustained Collaboratively. arXiv preprint arXiv:2302.02325, 2023. Available online: https://arxiv.org/abs/2302.02325 (accessed on Dec 2024).
- Vogels, W. Eventually Consistent. Commun. ACM 2009, 52, 40–44. [CrossRef]
- Szabo, N. Smart Contracts: Building Blocks for Digital Markets. University of Amsterdam, 1994. Available online: https://szabo.best.vwh.net/smart.contracts.html (accessed on March 2021).
- Buterin, V. Ethereum Whitepaper. Ethereum Foundation, 2015. Available online: https://ethereum.org/en/whitepaper/ (accessed on September 2024).
- Merkle, R.C. A Digital Signature Based on a Conventional Encryption Function. Advances in Cryptology 1987, 293, 369–378.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



