Submitted:
23 December 2024
Posted:
24 December 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Website Blocking in the Southeast Asian Context
1.2. The Broader Role of Website Blocking in Cybersecurity
1.3. Research Significance and Objectives
- How do legal frameworks and practical implementations of website blocking measures influence their effectiveness in reducing online copyright infringement?
- To what extent are website blocking measures effective, and what factors contribute to their success or limitations?
2. Materials and Methods
2.1. Study Design
- Comparative Analysis: Evaluates differences in piracy levels, implementation efficiency, and legal frameworks across the four target jurisdictions
2.2. Grouping and Selection of Jurisdictions
- Characterized by administrative approaches to website blocking.
- Implementations occur rapidly, often within 24 hours (Indonesia) or a few days (Vietnam).
- Judicial oversight is minimal or absent, allowing for streamlined decision-making.
Group 2: Malaysia and Singapore
- Defined by formal legal procedures, emphasizing judicial or quasi-judicial reviews.
- Implementation timelines are longer, ranging from 48 hours (Malaysia) to several months (Singapore).
- Blocking orders require extensive documentation and legal scrutiny.
Control Territories
2.3. Data Collection
- Website Traffic Data: Collected from Alexa Top Sites, which aggregates information on the 10,000 most visited websites in each country. Metrics such as "Reach Per Million" (RPM) provide insights into website popularity and user engagement
- Site Categorization Data: Obtained from Zvelo, a commercial URL categorization service. Zvelo’s algorithms classify websites based on content type, enabling the identification of piracy-related domains
- Blocking Records: Provided by the Coalition Against Piracy (CAP), detailing the number of sites blocked, implementation timelines, and enforcement procedures for each jurisdiction
2.4. Sampling Method
2.5. Classification of Websites
2.6. Metrics for Effectiveness
2.7. Statistical Analysis
2.8. Comparative Analysis
2.9. Contextual Considerations
2.10. Displacement Effects and Adaptive Tactics
3. Results
3.1. The Impact of Legal Frameworks and Implementation Approaches
3.1.1. Indonesia (Administrative Model – High Effectiveness)
3.1.2. Vietnam (Administrative Model – Moderate Effectiveness)
3.1.3. Malaysia (Judicial-Administrative Model – Mixed Results)
3.1.4. Singapore (Judicial Model – Low Effectiveness)
3.2. Overall Effectiveness of Website Blocking Measures
3.2.1. Traffic Reduction to Blocked Sites
3.2.2. Overall Reduction in Piracy Levels
3.2.3. Sustained Impact Over Time
- Dynamic Monitoring: Regular surveillance to identify and block new infringing sites.
- Rapid Response Mechanisms: Minimizing delays between identifying infringing content and executing blocks.
- Comprehensive Ecosystem Targeting: Addressing not only websites but also supporting infrastructure, such as hosting services and payment gateways
3.2.4. Displacement Effects and Adaptive User Behavior
3.2.5. Legal Content Consumption as a Secondary Outcome
3.2.6. Lessons for Cybersecurity Integration
3.3. Regression Modeling
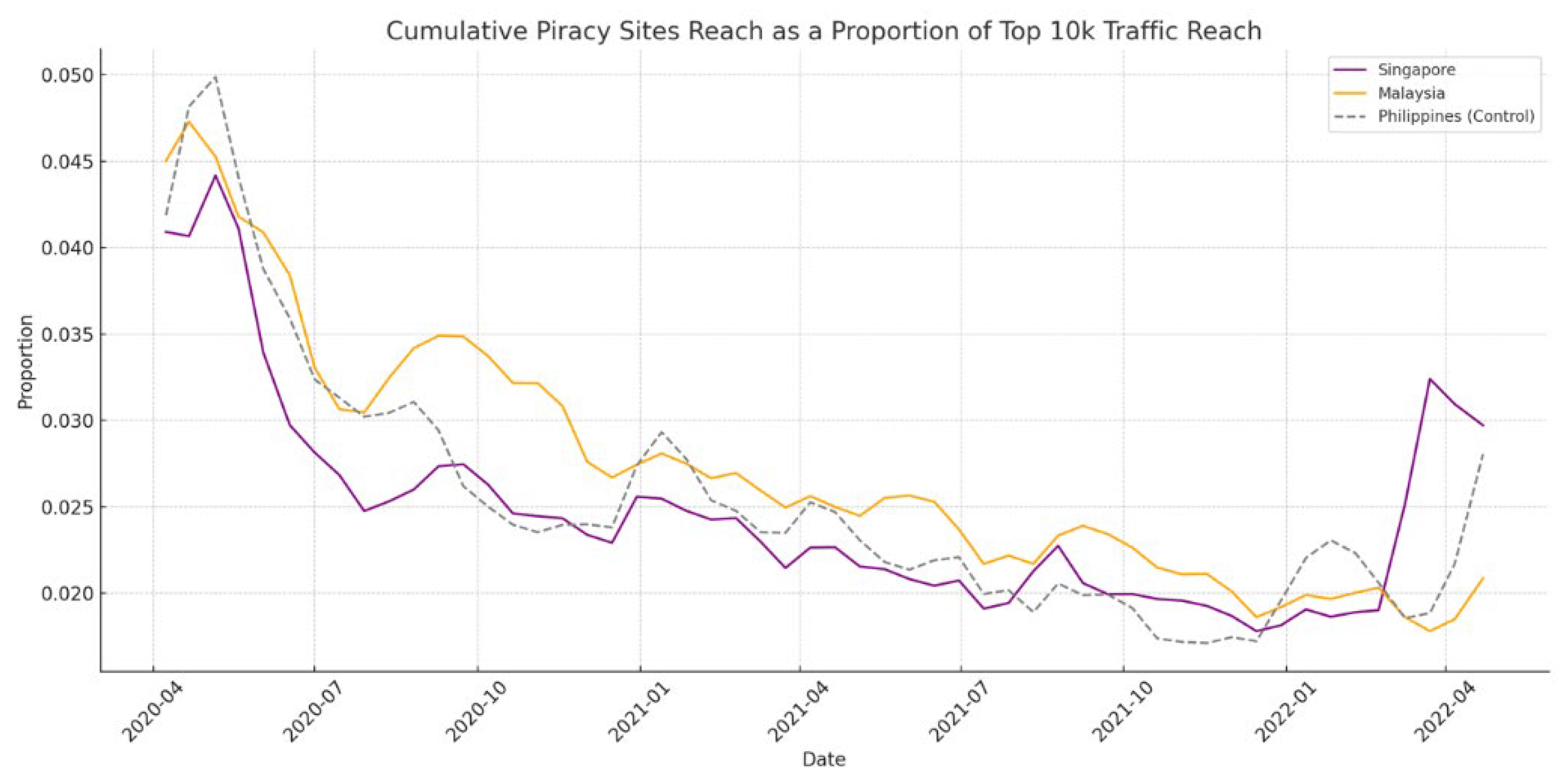
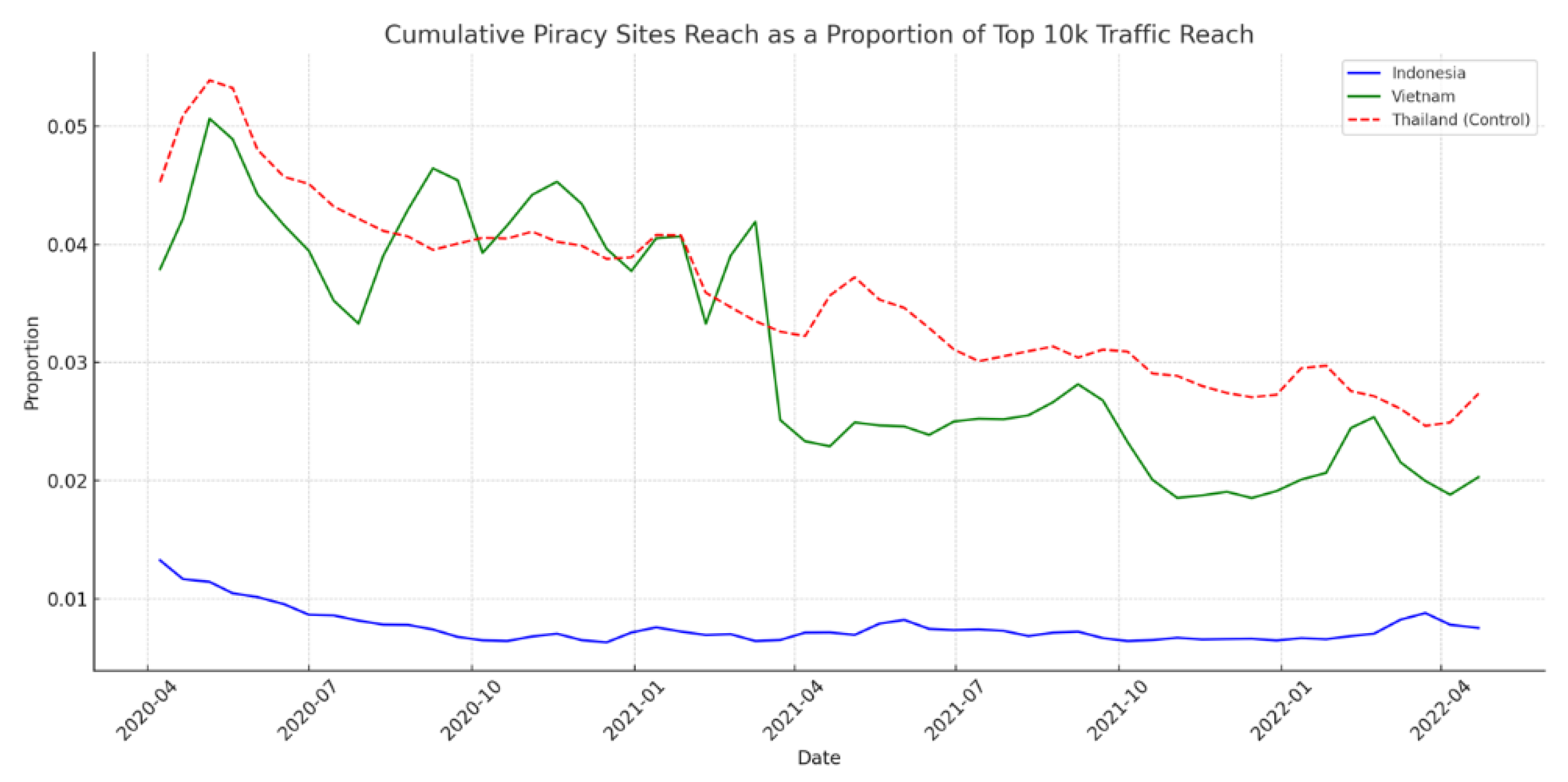
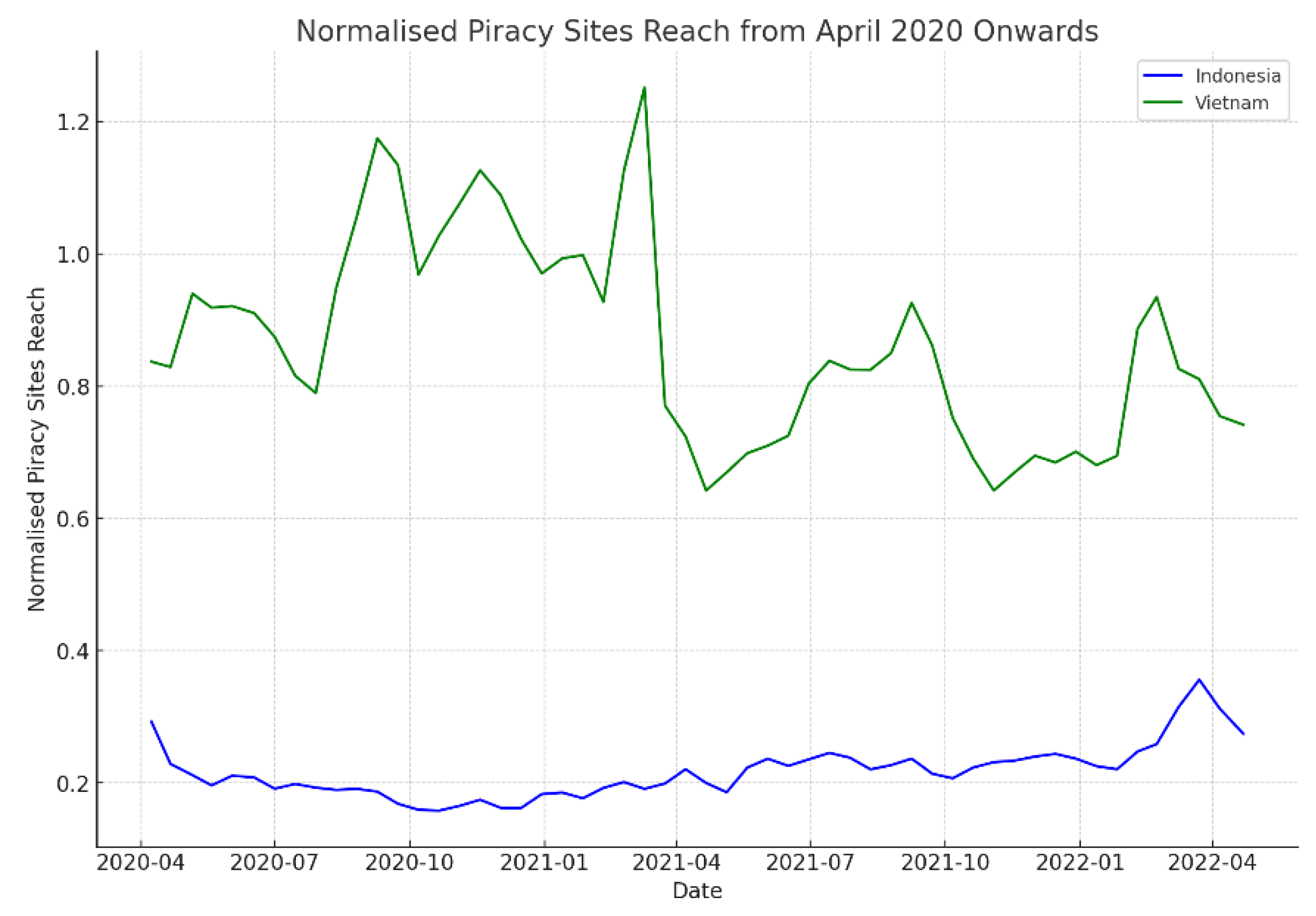
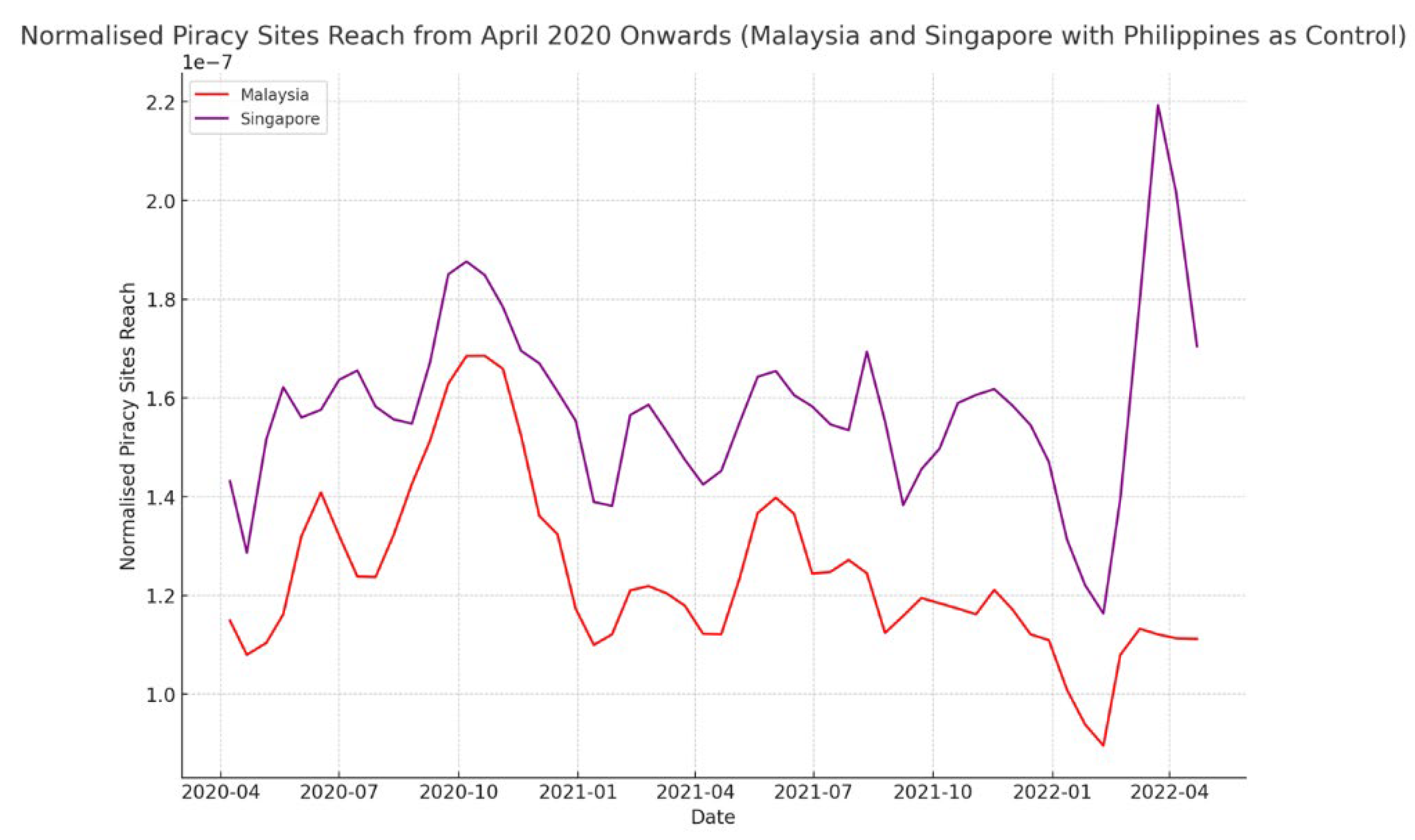
- Cumulative Piracy Sites Reach: The total reach of all identified piracy websites.
- Cumulative Legal Reach: The total reach of identified legitimate content websites.
- Top 10k Cumulative Reach: The total reach of the top 10,000 websites in each country.
- Adjusted Piracy Reach = Cumulative Piracy Sites Reach / Top 10k Cumulative Reach
- Adjusted Legal Reach = Cumulative Legal Reach / Top 10k Cumulative Reach
- β₀ represents the intercept, indicating the expected value of the cumulative legal reach when the cumulative piracy sites reach is zero
- β₁ denotes the coefficient that quantifies the change in the cumulative legal reach associated with a one-unit change in the cumulative piracy sites reach
- ϵ is the error term, accounting for the variation in the cumulative legal reach that is not explained by the cumulative piracy sites reach
4. Discussion
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Danaher, B.; Sivan, L.; Smith, M.D.; Telang, R. (2024). The Impact of Online Piracy Website Blocking on Legal Media Consumption. Available at SSRN.
- Watters, P. (2023). Consumer risks from piracy sites in the Philippines. Available at SSRN 4536945.
- Danaher, B.; Smith, M.D.; Telang, R. (2016). Website Blocking Revisited: The Effect of the UK November 2014 Blocks on Consumer Behavior. ERN: Regulation (IO) (Topic).
- Ververis, V.; Lasota, L.; Ermakova, T.; Fabian, B. Website blocking in the European Union: Network interference from the perspective of Open Internet. Policy & Internet 2024, 16, 121–148. [Google Scholar]
- Snyder, P.; Vastel, A.; Livshits, B. Who filters the filters: Understanding the growth, usefulness and efficiency of crowdsourced ad blocking. Proceedings of the ACM on Measurement and Analysis of Computing Systems 2020, 4, 1–24. [Google Scholar] [CrossRef]
- Carstairs, P. The inevitable actors: An analysis of Australia’s recent anti-piracy website blocking laws, their balancing of rights and overall effectiveness. AUSTL. INTELL. PROP. J. 2021, 31, 1. [Google Scholar]
- Han, J.L.X. Effective Anti-Piracy in Vietnam: A Journey through Site Blocking. Int'l JL Ethics Tech. 2022; 50. [Google Scholar]
- Blakeney, M. (2023). Enforcement of IPRs in ASEAN. In Intellectual Property Law in South East Asia (pp. 358–377). Edward Elgar Publishing.
- Sinpeng, A. Digital media, political authoritarianism, and Internet controls in Southeast Asia. Media, Culture & Society 2020, 42, 25–39. [Google Scholar]
- Ong, E. Online repression and self-censorship: evidence from Southeast Asia. Government and Opposition 2021, 56, 141–162. [Google Scholar] [CrossRef]
- Chang, K.C.; Hobbs, W.R.; Roberts, M.E.; Steinert-Threlkeld, Z.C. COVID-19 increased censorship circumvention and access to sensitive topics in China. Proceedings of the National Academy of Sciences 2022, 119, e2102818119. [Google Scholar] [CrossRef]
- Watters, P. (2021). Consumer Risk and Digital Piracy–Where Does Malware Come From? . Available at SSRN 453 6938.
- Okumuş, M.S. The effects of Covid-19 pandemic on audience practices in cinema, television, and OTT platforms. İstanbul Ticaret Üniversitesi Sosyal Bilimler Dergisi 2022, 21, 133–147. [Google Scholar] [CrossRef]
- Watters, P.; Boslaugh, S. (2008). Statistics in a nutshell. O'Reilly Media, Incorporated.
- Špaček, S.; Laštovička, M.; Horák, M.; Plesník, T. (2019, April). Current issues of malicious domains blocking. In 2019 IFIP/IEEE Symposium on Integrated Network and Service Management (IM) (pp. 551–556). IEEE.
- Bakioǧlu, B.S. The gray zone: Networks of piracy, control, and resistance. The Information Society 2016, 32, 40–50. [Google Scholar] [CrossRef]
- Sarker, I.H.; Janicke, H.; Mohammad, N.; Watters, P.; Nepal, S. (2023). AI potentiality and awareness: a position paper from the perspective of human-AI teaming in cybersecurity. arXiv preprint arXiv:2310.12162, arXiv:2310.12162.
- Amjad, A.H.; Shafiq, Z.; Gulzar, M.A. (2023). Blocking javascript without breaking the web: An empirical investigation. arXiv preprint arXiv:2302.01182, arXiv:2302.01182.
- McIntosh, T.R.; Susnjak, T.; Liu, T.; Watters, P.; Halgamuge, M.N. (2023). From google gemini to openai q*(q-star): A survey of reshaping the generative artificial intelligence (ai) research landscape. arXiv preprint arXiv:2312.10868, arXiv:2312.10868.
- Cory, N. (2020). How Voluntary Agreements Among Key Stakeholders Help Combat Digital Piracy. Information Technology and Innovation Foundation.
| 1 | For further details regarding quasi-experimental designs, see a review in [14]. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



