Submitted:
07 December 2024
Posted:
17 December 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
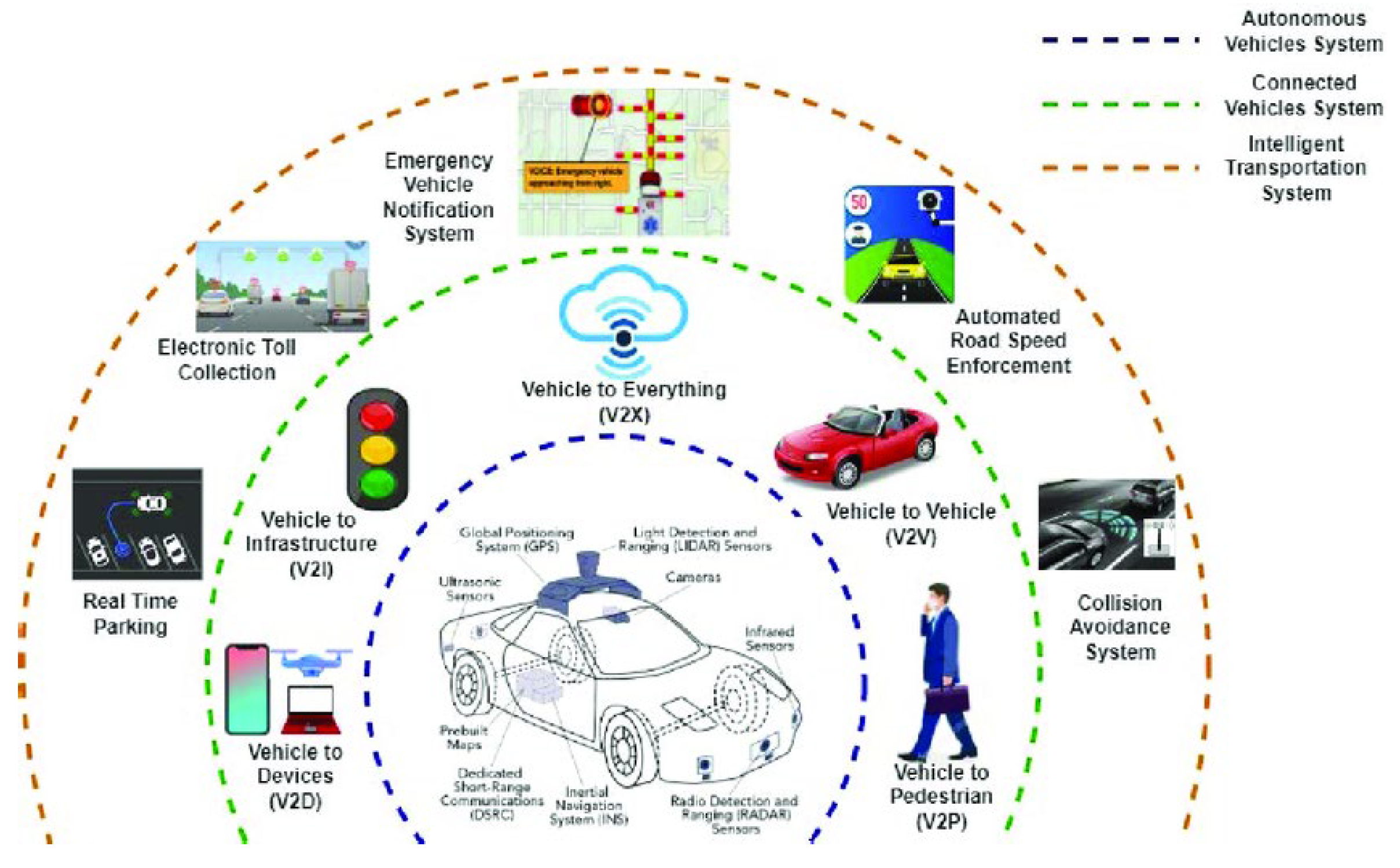
2. Understanding Cybersecurity Challenges in Autonomous Vehicles
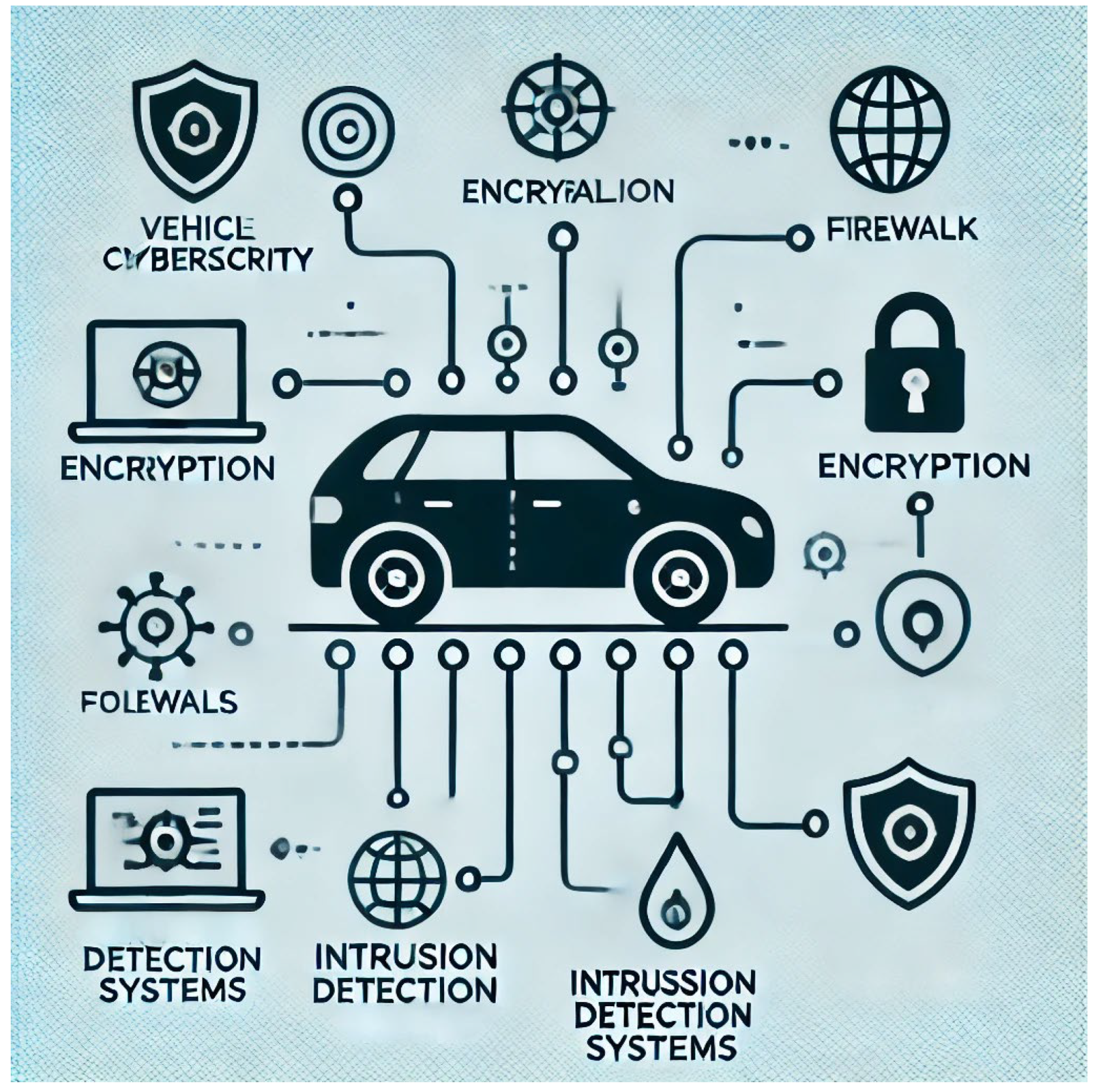
A. Key Vulnerabilities in AV Systems
1. Communication Protocols
2. Software Bugs
3. Sensor Spoofing
4. Insecure Updates
B. Types of Cyber Threats
1. Data Breaches
2. Ransomware Attacks
3. Denial-of-Service (DoS) Attacks
4. Malware and Trojans
C. Potential Impacts of Cyberattacks on AV Safety and User Trust
Safety Risks
Erosion of User Trust
Economic and Reputational Damage
3. Overview of Big Data Analytics

A. Definition and Significance of BDA
- ➢
- Process high-velocity data: AVs generate data at unprecedented speeds, necessitating tools that can handle real-time analytics.
- ➢
- Improve decision-making: By extracting actionable insights, BDA enhances the vehicle's ability to make accurate and timely decisions.
- ➢
- Predict and prevent issues: Proactive threat detection and system maintenance rely on BDA's predictive capabilities.
B. Role of Data Collection, Storage, and Processing in AV Systems
1. Data Collection
2. Data Storage
3. Data Processing
C. How BDA Enables Real-Time and Predictive Insights
1. Real-Time Analytics
2. Predictive Insights
- ❖
- Predictive Maintenance: By analyzing patterns in sensor data, BDA can forecast component failures and schedule maintenance proactively, minimizing downtime.
- ❖
- Threat Detection: Predictive models identify potential cybersecurity threats based on historical attack patterns and behavioral anomalies.
4. Application of Big Data Analytics in Cyber Defense for AVs
A. Threat Detection and Prevention
1. Real-Time Monitoring of AV Systems for Anomalies
2. Use of Machine Learning to Predict and Mitigate Threats
B. Incident Response and Recovery
1. Data-Driven Approaches to Identify Attack Patterns
2. Faster Recovery Through Automated Diagnostics and Updates
C. Enhancing System Resilience
5. Case Studies and Examples
A. Examples of BDA-Powered Cyber Defense Implementations in AVs
1. Tesla’s Data-Driven Threat Monitoring System
2. Waymo’s Predictive Cybersecurity Framework
3. Volvo’s Cybersecurity Platform with BDA Integration
B. Success Stories and Lessons Learned
1. Incident Recovery and Lessons from the Jeep Cherokee Hack
2. BMW’s Enhanced System Resilience
3. Collaboration Between Automakers and Cybersecurity Firms
C. Key Takeaways
- ♦
- Proactive Monitoring is Essential: Real-time analytics can detect anomalies before they escalate, preventing potential breaches and minimizing risk.
- ♦
- Predictive Models Drive Preemptive Actions: By leveraging historical data, BDA enables organizations to identify vulnerabilities and mitigate threats proactively.
- ♦
- Collaboration Enhances Outcomes: Partnerships between automakers, technology providers, and cybersecurity firms accelerate the development and deployment of effective defense mechanisms.
- ♦
- Continuous Learning and Adaptation: BDA allows systems to evolve in response to new threats, ensuring long-term resilience.
6. Challenges in Implementing Big Data Analytics for Cyber Defense
A. Data Privacy and Ethical Concerns
1. Collection and Use of Personal Data
2. Anonymization and Security of Data
3. User Consent and Transparency
B. Scalability and Infrastructure Limitations
1. Data Volume and Velocity
2. High Computational Costs
3. Cloud Dependency and Latency
C. Integration with Existing AV Technologies
1. Compatibility Issues
2. Real-Time Data Processing Constraints
3. Evolving Threat Landscape
7. Future Directions
A. Advances in Artificial Intelligence and Machine Learning for Better Cybersecurity
1. Enhanced Threat Detection with AI
- ✧
- Detect anomalies with greater accuracy by analyzing complex patterns in data.
- ✧
- Adapt to new attack vectors through continuous learning models.
- ✧
- Automate decision-making processes for real-time threat neutralization.
2. Behavioral Analysis for Proactive Defense
B. Collaboration Between Manufacturers, Cybersecurity Firms, and Policymakers
1. Standardization of Cybersecurity Protocols
2. Public-Private Partnerships for Threat Intelligence Sharing
3. Policy and Regulation Support
- ❖
- Mandating regular cybersecurity audits for AV systems.
- ❖
- Incentivizing investment in advanced security technologies.
- ❖
- Promoting transparency in data handling and privacy practices.
C. Potential of Quantum Computing in Future AV Cybersecurity
1. Quantum-Resistant Cryptography
2. Accelerated Threat Analysis
8. Conclusions
References
- Noman, Inshad Rahman, et al. "Data-driven security: Improving autonomous systems through data analytics and cybersecurity." Journal of Computer Science and Technology Studies 4.2 (2022): 182-190.
- Noman, I. R. , Bortty, J. C., Bishnu, K. K., Aziz, M. M., & Islam, M. R. (2022). Data-driven security: Improving autonomous systems through data analytics and cybersecurity. Journal of Computer Science and Technology Studies, 4(2), 182-190.
- Noman, Inshad Rahman, Joy Chakra Bortty, Kanchon Kumar Bishnu, Md Munna Aziz, and Md Rashedul Islam. "Data-driven security: Improving autonomous systems through data analytics and cybersecurity." Journal of Computer Science and Technology Studies 4, no. 2 (2022): 182-190.
- Noman, I.R. , Bortty, J.C., Bishnu, K.K., Aziz, M.M. and Islam, M.R., 2022. Data-driven security: Improving autonomous systems through data analytics and cybersecurity. Journal of Computer Science and Technology Studies, 4(2), pp.182-190.
- Noman IR, Bortty JC, Bishnu KK, Aziz MM, Islam MR. Data-driven security: Improving autonomous systems through data analytics and cybersecurity. Journal of Computer Science and Technology Studies. 2022;4(2):182-90.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



