2.1. Dynamic BeamSNARKS Generation Optimization Mechanism
Ethereum’s Beam Sync upgrade marks a pivotal advancement in blockchain synchronization, introducing efficient on-demand state retrieval and enabling real-time validator functionality. Building upon these foundational enhancements, we strategically developed a Dynamic BeamSNARKS generation mechanism to align with and complement Ethereum’s architectural evolution. This mechanism integrates on-demand state retrieval and incremental proof construction, optimizing resource utilization while maintaining high validation accuracy and synchronization fidelity. This innovation positions BeamSNARKS as a forward-compatible solution that synergizes with Ethereum’s vision of scalable and efficient decentralized networks by addressing the demands of low-latency, high-throughput transaction processing.
To understand Beam Sync, it’s essential to know two synchronization methods: Full Sync and Fast Sync [
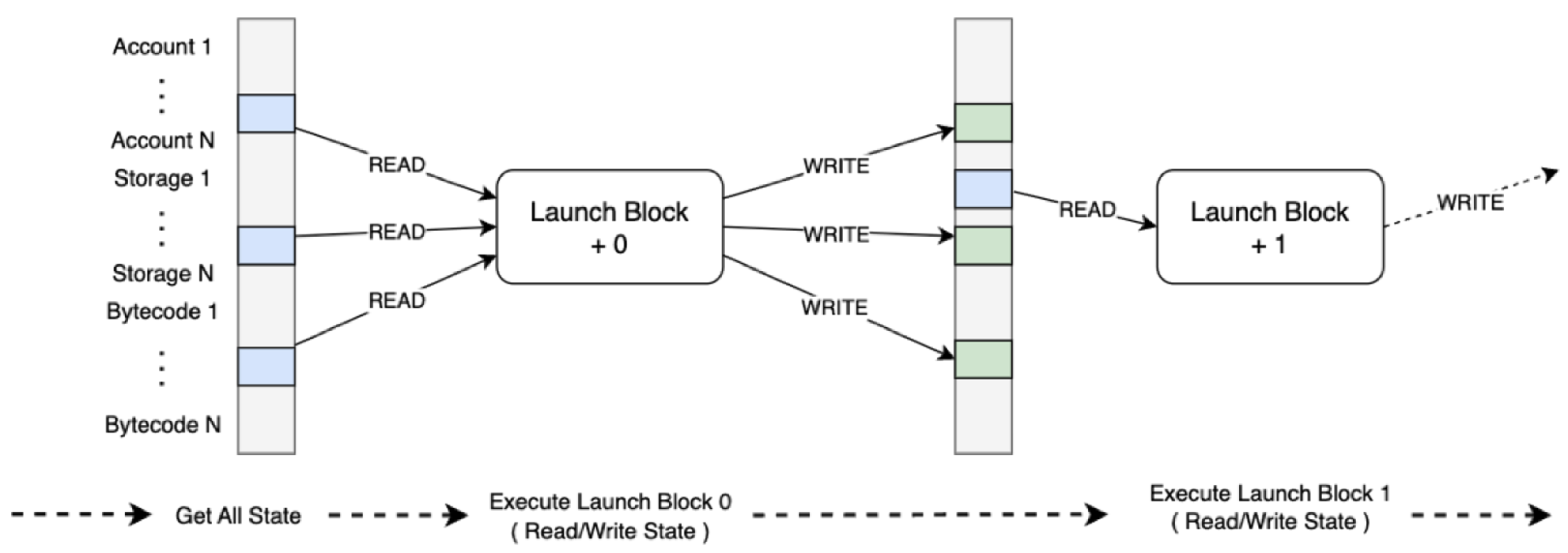
3], each with distinct advantages . The entire Sync processes every block from the genesis block, establishing an initial state of account balances and contract data. However, it’s slow, especially on the mainnet, and the time required increases as the network grows. As illustrated in
Figure 1, Fast Sync speeds up the process by downloading historical blocks and headers and selecting a recent block as the "launch block." It assumes miners follow valid EVM rules, allowing it to skip executing all previous blocks. Before executing the launch block, Fast Sync obtains the current state, including bytecodes and account information, by requesting a state snapshot from peers. After securing this information, it executes valid transactions and transitions into Full Sync to process all subsequent blocks.
Beam Sync is a direct evolution of the Fast Sync process, introducing a critical distinction to enhance synchronization efficiency. Unlike traditional methods, where validators must download and maintain the entire blockchain state, Beam Sync enables validators to execute the launch block immediately while requesting only the state data missing from the local database. This incremental synchronization process ensures that validators can start contributing to the network without waiting to download the complete state.
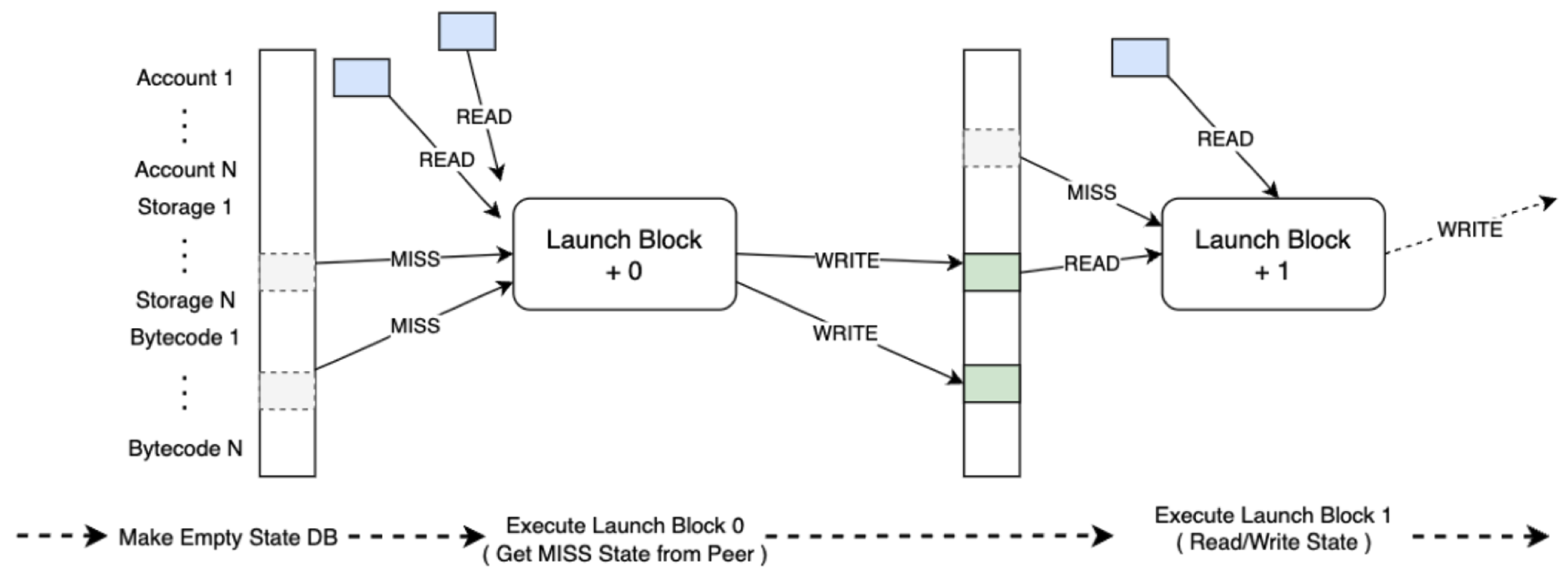
As shown in
Figure 2, Beam Sync retrieves missing state elements on demand during block execution. Validators save the input and output states locally and proceed to the next block, repeating the process while requesting any additional missing data. Over time, more state data becomes available locally as more blocks are processed. Beam Sync also runs a background process to backfill states not accessed during block processing, ensuring that the database eventually contains all necessary state information. This approach minimizes bandwidth and storage demands, making participation feasible even for validators with limited hardware resources or connectivity.
Building upon the technical innovations introduced by Ethereum’s Beam Sync, we proposed a targeted optimization framework: Dynamic zkSNARKS Generation Optimization. This framework addresses the computational and synchronization challenges inherent in zk-Rollup systems, ensuring seamless compatibility with Ethereum’s evolving architecture. Leveraging the on-demand data retrieval mechanism of Beam Sync, this optimization dynamically constructs zkSNARKS proof inputs by synchronizing only the state data directly relevant to the verification process, thus eliminating the need to preload the entire Layer 2 (L2) state. This targeted approach minimizes bandwidth usage and significantly reduces storage requirements, making zk-Rollup systems more accessible to a wider range of participants. Additionally, the proof generation process is incrementally partitioned to improve computational efficiency. Transaction streams are divided into smaller, logically grouped subsets, each independently generating sub-proofs. These sub-proofs are later aggregated into a final BeamSNARK, preserving succinctness while distributing the computational workload across multiple cycles. This incremental architecture reduces peak processing demands and aligns seamlessly with the real-time synchronization capabilities enabled by Beam Sync.
2.1.1. On-Demand State Synchronization
Traditional zk-Rollup systems preload the entire Layer 2 (L2) state
S , incurring high storage and bandwidth costs. BeamSNARK eliminates this inefficiency by dynamically retrieving only the relevant subset
. The cost of state retrieval is modeled as Equation (
1). By dynamically requesting state elements during proof generation, the mechanism significantly reduces
, making the system more efficient. Validators only retrieve data relevant to the transactions being processed, minimizing bandwidth usage and enabling broader participation with limited resources.
where
represents the bandwidth cost of retrieving
at time
, and
k denotes the total number of retrieval steps.
2.1.2. Incremental Proof Generation
Instead of processing an entire batch of transactions
at once, BeamSNARKS partitions
into subsets
, generating proofs incrementally. The total computational cost for a batch
with
n transactions is:
where
is the fixed setup cost,
is the per-step computation cost, and
is the computational depth of transaction
T.
As expressed in Equation (
2), incremental proof generation distributes computational workloads across multiple cycles, significantly reducing peak processing demands. This approach aligns seamlessly with Beam Sync’s real-time block processing, ensuring low latency and scalability.
Following the definition of the cost of state retrieval and computational cost, the total zkSNARKS generation cost integrates the retrieval, computation, and proof finalization phases can be modeled as follow:
where
accounts for overheads such as proof aggregation and Layer 1 submission.
Equation (
3) demonstrates how BeamSNARKS reduces the overall zkSNARKS generation cost. By dynamically synchronizing state retrieval and incrementally constructing proofs, the mechanism lowers computational and bandwidth requirements, enabling validators with standard hardware to participate effectively. By coupling dynamic state synchronization with incremental proof generation, this approach achieves a high degree of resource efficiency while maintaining the cryptographic integrity and performance standards expected in zk-Rollup systems. The proposed optimization significantly lowers the hardware and bandwidth barriers for zk-Rollup nodes, making it feasible for a broader range of participants, including those with limited computational resources, to engage in the network actively. This enhancement boosts scalability and democratizes participation, fostering a more decentralized ecosystem.
2.2. Dynamic SNARKification
SNARKification represents a pivotal innovation in zero-knowledge proof systems, addressing scalability and throughput challenges in Layer 2 rollup mechanisms [
4]. By compressing transaction batches into a single succinct proof, this technology significantly reduces the computational and storage overhead required for Layer 1 submission [
5]. Unlike traditional rollup designs, which often rely on fixed circuits, SNARKification employs adaptive circuit generation and recursive proof aggregation, enabling efficient validation of transactions with varying complexity. These advancements lower gas costs and ensure compatibility with Ethereum’s consensus mechanism, making high-throughput decentralized applications more feasible. As a cornerstone of BeamSNARKS, this technique exemplifies the potential of zero-knowledge technologies to reshape the efficiency and accessibility of blockchain systems.
Central to BeamSNARKS’s innovations is its dynamic SNARKification technology, which breaks away from traditional fixed-circuit designs by introducing adaptive circuit generation and hierarchical proof optimization. This advancement allows blockchains to tailor its zero-knowledge proof schemes to accommodate varying transaction complexities efficiently. Dynamic SNARKification avoids over-design by tailoring circuits to the complexity of transactions. For a batch
partitioned into
m clusters
, the circuit complexity is given by:
where
represents the number of transactions in cluster
, and
is the circuit complexity of
.
Additionally, to minimize Layer 1 submission costs, we aggregates individual proofs
into a single succinct proof
:
where
is the recursive aggregation function. The computational cost of aggregation scales logarithmically with the batch size
n :
with
as the aggregation coefficient. As shown in Equations (
5) and (
6), recursive aggregation drastically reduces the size of proofs submitted to Ethereum’s Layer 1. This efficiency lowers gas costs and ensures scalability for high-throughput rollup systems.
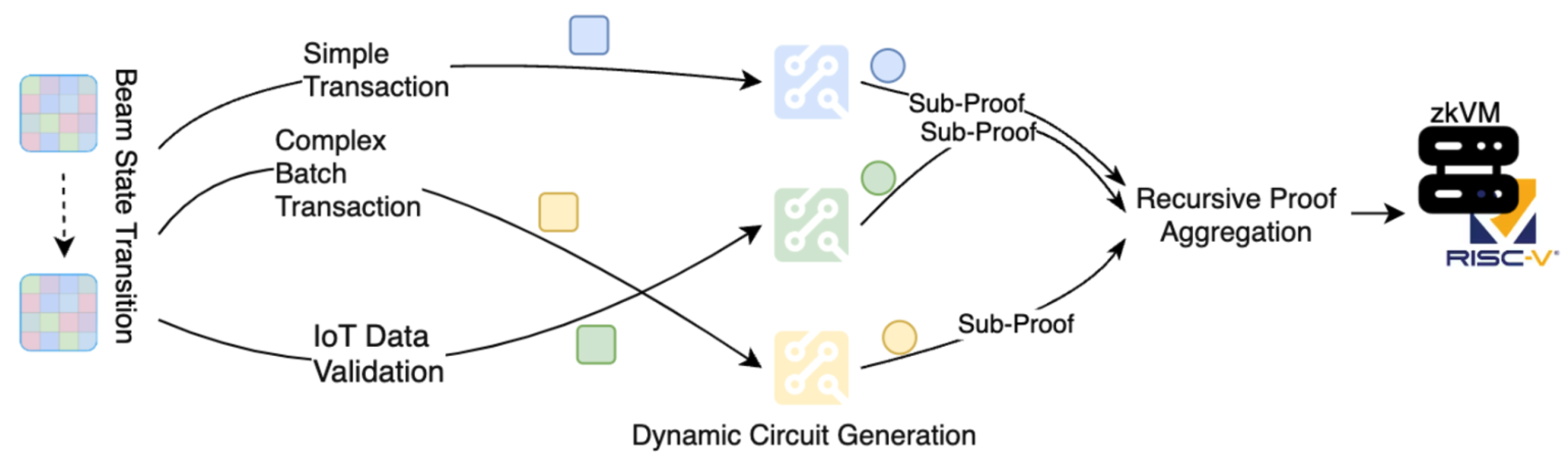
By clustering transactions with similar computational characteristics, BeamSNARKS reduces unused resources and optimizes circuit utilization. As shown in
Figure 3, during the circuit construction phase, the system dynamically adjusts circuit pathways based on transaction types and batch sizes. For simple transactions, such as single payments or IoT device data validations, lightweight circuits minimize proof generation time and memory usage. Conversely, for complex batch transactions, recursive proof aggregation consolidates multiple sub-proofs into a single BeamSNARK, drastically reducing the data volume submitted to Layer 1 and lowering verification costs. This dynamic mechanism avoids over-design in proof generation, improving circuit utilization, reducing gas consumption, and optimizing overall Layer 2 performance.
At the hardware level, our implementation of RISC-V-based zkVMs further enhances the efficiency of dynamic SNARKification. Leveraging the modularity of the RISC-V architecture, these zkVMs are optimized explicitly for cryptographic operations such as elliptic curve multiplications and Merkle tree updates [
6]. This results in a 30%-50% improvement in proof generation throughput on standard hardware configurations. Edge nodes equipped with lightweight zkVMs execute simple zero-knowledge validations, while core nodes, utilizing high-performance zkVMs, perform recursive aggregation to generate compressed proofs for Layer 1 submission. This hierarchical validation architecture reduces the hardware requirements for validator participation and ensures low latency and high throughput across the network.
By seamlessly integrating dynamic SNARKification with zkEVM capabilities, this framework delivers a scalable and efficient solution tailored to the specific demands of decentralized physical infrastructure networks (Depin). The technology excels in processing high-frequency microtransactions, securely validating IoT device data, and enabling efficient resource allocation. Compared to traditional zk-Rollup solutions, this approach significantly lowers resource consumption, accelerates proof generation and verification, and demonstrates superior gas efficiency and scalability. These innovations provide robust foundational support for Depin applications, aligning with Ethereum’s vision for a high-performance blockchain ecosystem.