Submitted:
17 September 2024
Posted:
18 September 2024
You are already at the latest version
Abstract
Crypto-ransomware has emerged as one of the most significant cybersecurity threats in recent years. Ransomware attacks, particularly those involving the encryption of data and demanding payment in cryptocurrency, have caused severe disruptions across various critical industries, including healthcare, energy, and finance. The proliferation of these attacks is largely attributed to the anonymity provided by cryptocurrency transactions and the increasing sophistication of cybercriminal tactics. The impact of ransomware extends beyond immediate financial losses, often leading to prolonged operational downtime, reputational damage, and even risks to public safety. In this research paper, we explore the growing threat of crypto-ransomware by examining real-life case studies in key industries, analyzing the countermeasures taken, and proposing additional solutions to mitigate the risk. The goal is to raise awareness and provide actionable insights for organizations to better protect themselves against this pervasive threat.
Keywords:
1.0. Background
1.1. Purpose
1.3. Architecture Used
1.4. Technology Used
1.4.1. Infection Methods
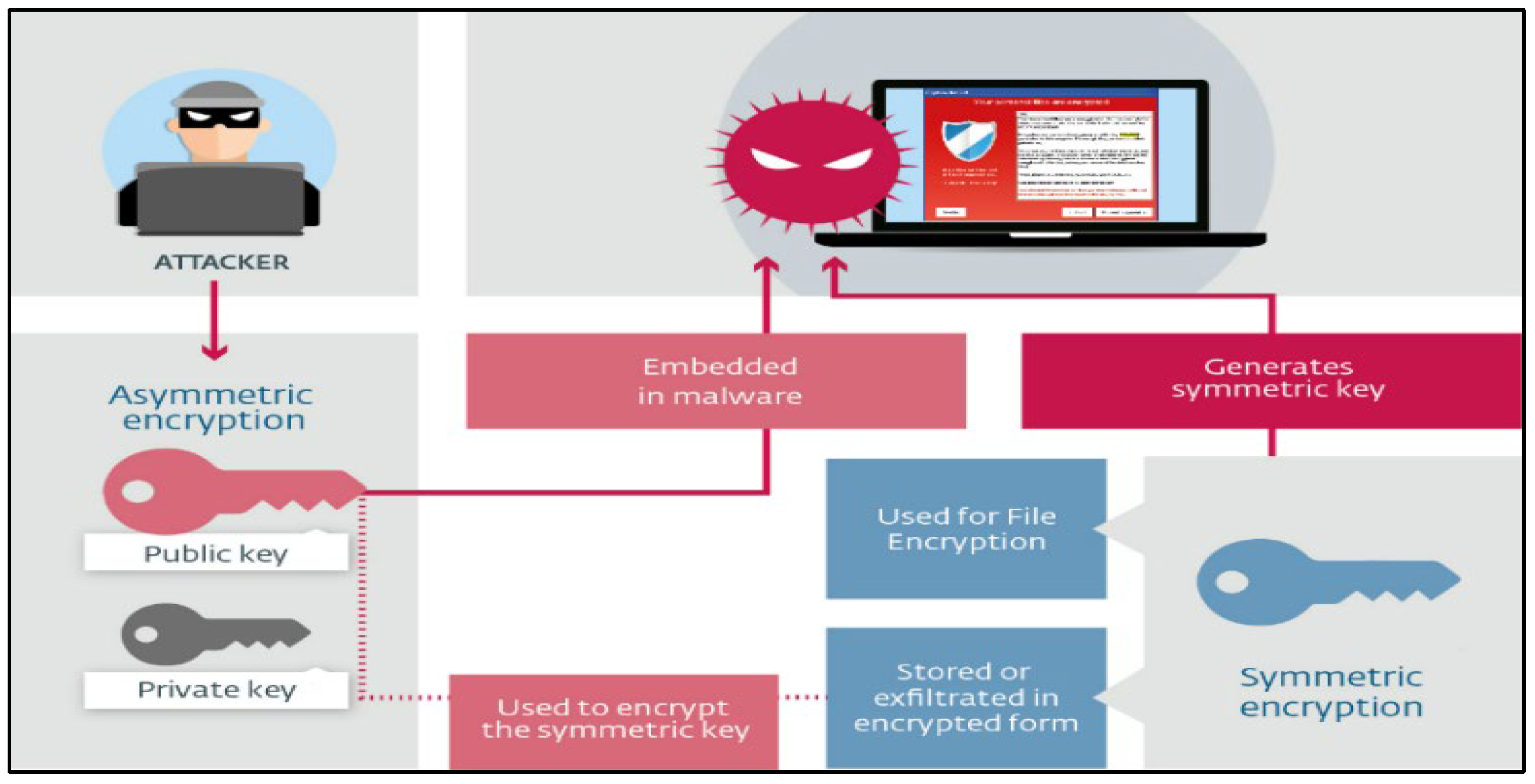
1.4.2. Encryption Methods
2.0. Crypto Ransomware Case Scenario
2.1. Kaseya Case Scenario
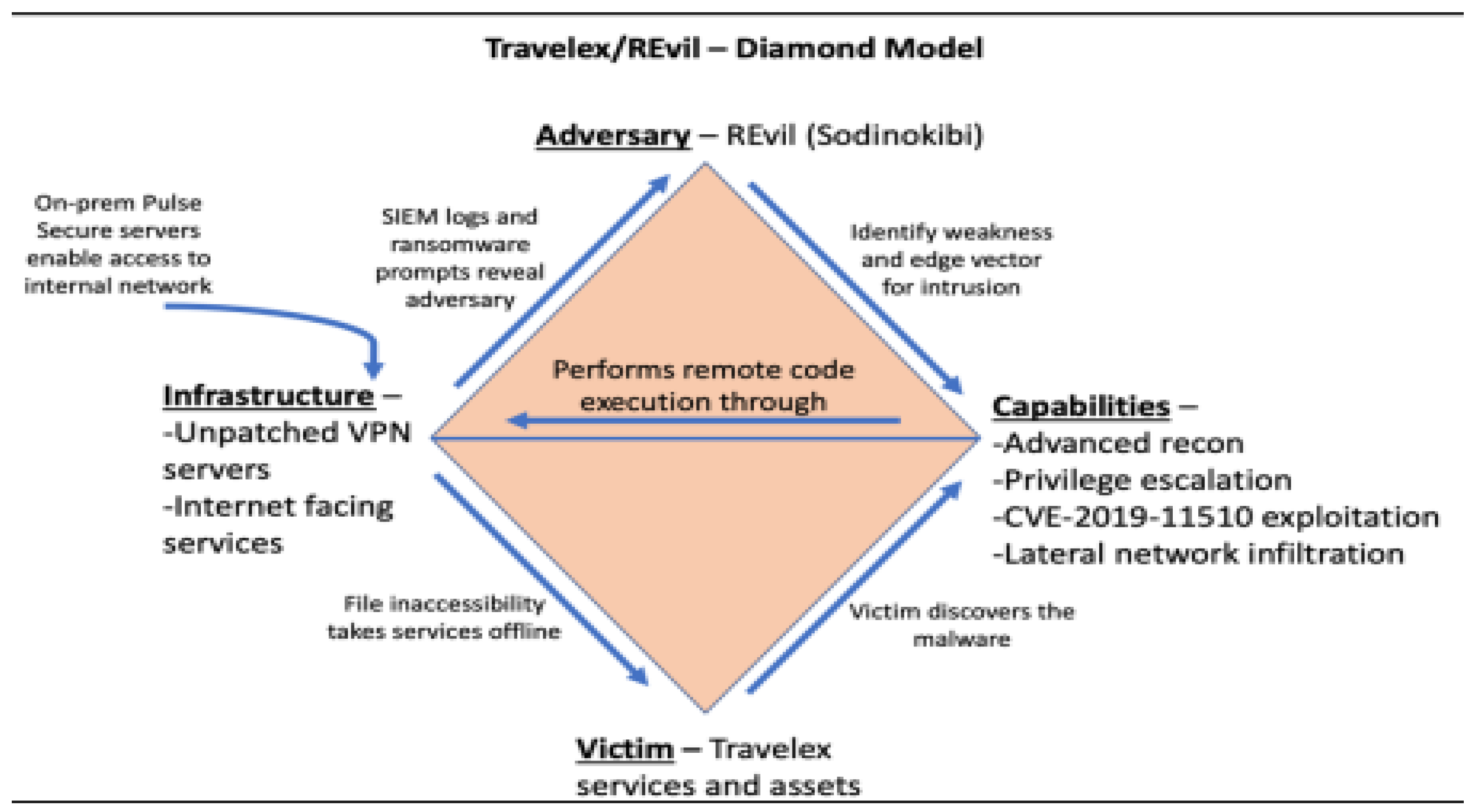
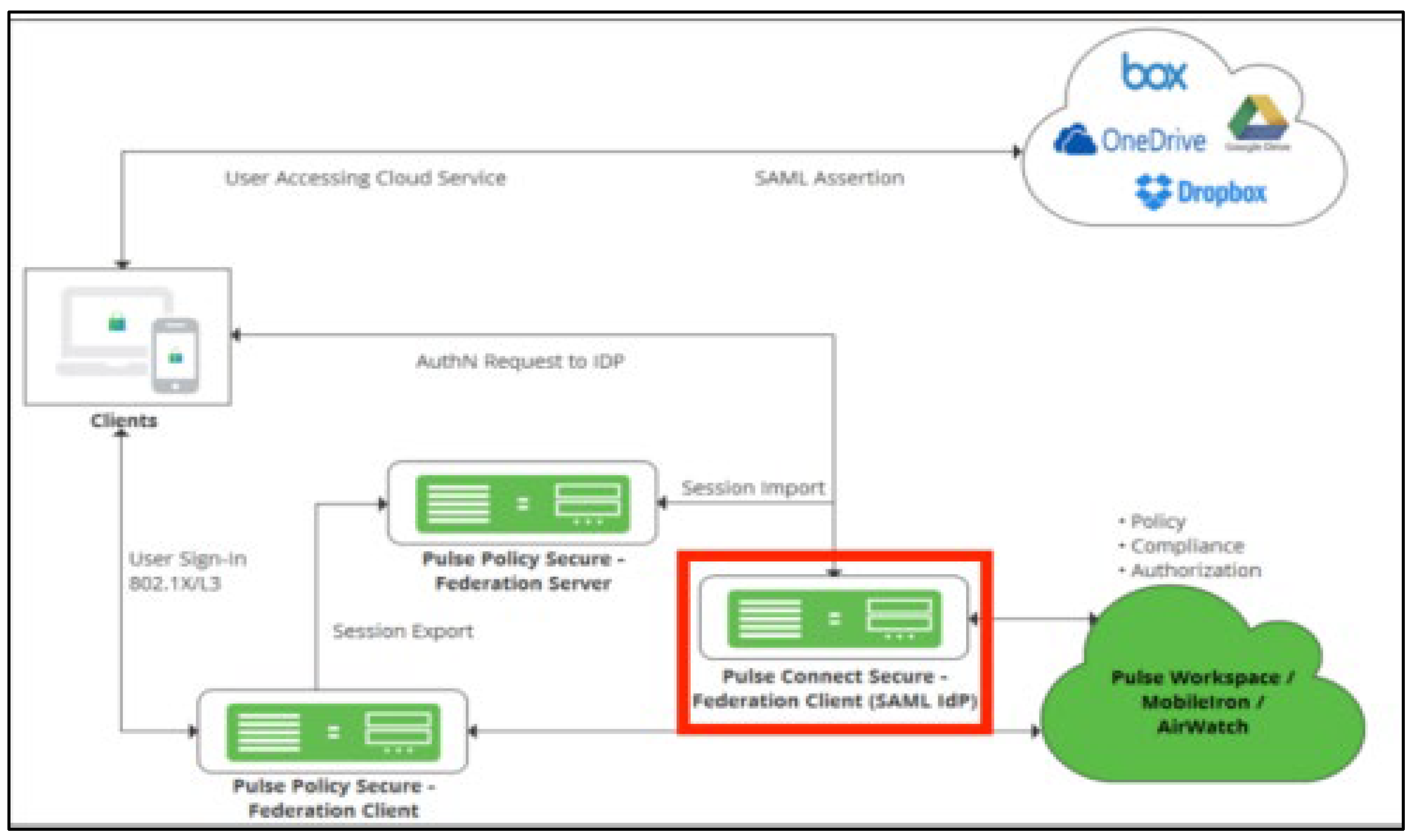
2.2. Travelex Case Scenario
2.3. Colonial Pipeline Case Scenario
3.0. Crypto Ransomware Security Issues
3.1. Kaseya Case Security Issue
3.2. Travelex Case Security Issue
3.3. Colonial Pipeline Ransomware Attack Security Issue
4.0. Crypto Ransomware Potential Threats
4.1. Kaseya
4.2. Travelex
4.3. Colonial Pipeline
5.0. Crypto Ransomware Countermeasures
5.1. Kaseya
5.1.1. Kaseya Countermeasure
5.1.2. Proposed Countermeasure for Kaseya
5.2. Travelex
5.2.1. Travelex Countermeasure
5.2.2. Proposed Countermeasure for Travelex
5.3. Colonial Pipeline
5.3.1. Colonial Pipeline Countermeasure
5.3.2. Proposed Countermeasure for Colonial Pipeline
6.0. Conclusion
References
- BleepingComputer. (n.d.). Travelex Reportedly Paid $2.3 Million Ransom to Restore Operations. [online] Available at: https://www.bleepingcomputer.com/news/security/travelex-reportedly-paid-23-million-ransom-to-restore-operations/.
- blog.avast.com. (n.d.). Avast releases a free decryption tool for EncrypTile ransomware. [online] Available at: https://blog.avast.com/avast-releases-free-decryption-tool-for-encryptile-ransomware [Accessed 6 Jun. 2024].
- Alauthman, M. et al. (2024) ‘Malware Threats Targeting Cryptocurrency: A Comparative Study,’ 2024 2nd International Conference on Cyber Resilience (ICCR) [Preprint]. [CrossRef]
- Alferidah, D.K. and Jhanjhi, N. (2020) ‘Cybersecurity Impact over Bigdata and IoT Growth,’ 2020 International Conference on Computational Intelligence (ICCI) [Preprint]. [CrossRef]
- Alkinani, M.H. et al. (2021) ‘5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle,’ Sensors, 21(20), p. 6905. [CrossRef]
- Allen, J. (2022, June 15). Kaseya Ransomware Attack Explained By Experts. PurpleSec. Retrieved November 15, 2022, from https://purplesec.us/kaseya-ransomware-attackexplained/#Responde.
- Almoysheer, Najd, Mamoona Humayun, and N. Z. Jhanjhi. “Enhancing Cloud Data Security using Multilevel Encryption Techniques.” Turkish Online Journal of Qualitative Inquiry 12, no. 3 (2021).
- Alsharif, Mohammed H., Abu Jahid, Anabi Hilary Kelechi, and Raju Kannadasan. “Green IoT: A review and future research directions.” Symmetry 15, no. 3 (2023): 757. [CrossRef]
- Brohi, S.N. et al. (2020) ‘Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf,’ Techrxiv [Preprint]. [CrossRef]
- Caras, C. (n.d.). Diamond Model of Intrusion Analysis -Travelex Ransomware Attack. [online] Available at: https://repository.gatech.edu/server/api/core/bitstreams/c57ffb71-bcb0-42da-bc85-977db9858952/content [Accessed 5 Jun. 2024].
- Chesti, I.A. et al. (2020) ‘Evolution, Mitigation, and Prevention of Ransomware,’ 2020 2nd International Conference on Computer and Information Sciences (ICCIS) [Preprint]. [CrossRef]
- Chimmanee, K. and Jantavongso, S. (2024) ‘Digital forensic of Maze ransomware: A case of electricity distributor enterprise in ASEAN,’ Expert Systems With Applications, p. 123652. [CrossRef]
- ComputerWeekly.com. (n.d.). Suspected ransomware attack causes worldwide disruption for Travelex. [online] Available at: https://www.computerweekly.com/news/252476220/Suspected-ransomware-attack-causes-worldwide-disruption-for-Travelex.
- CrowdStrike (2021). A Brief History of Ransomware | CrowdStrike. [online] crowdstrike.com. Available at: https://www.crowdstrike.com/cybersecurity-101/ransomware/history-of-ransomware/.
- Datta, P.M. and Acton, T. (2022) ‘From disruption to ransomware: Lessons From hackers,’ Journal of Information Technology Teaching Cases, 13(2), pp. 182–192. [CrossRef]
- Deochakke, A. and Tyagi, A.K. (2022) ‘Analysis of ransomware security on cloud storage systems,’ in Communications in computer and information science, pp. 47–59. [CrossRef]
- Dogra, V. et al. (2021) ‘Analyzing DistilBERT for Sentiment Classification of Banking Financial News,’ in Lecture notes in networks and systems, pp. 501–510. [CrossRef]
- Fatima-Tuz-Zahra, N. et al. (2020) ‘Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning,’ 2020 2nd International Conference on Computer and Information Sciences (ICCIS) [Preprint]. [CrossRef]
- Filiz, B. et al. (2021) ‘On the Effectiveness of Ransomware Decryption Tools,’ Computers & Security, 111, p. 102469. [CrossRef]
- Ford, E. W. (2021). Cyber ransom in the information age: A call to arms against the hackers. Journal of Healthcare Management, 66(4), 243–245. [CrossRef]
- Goenka, R., Chawla, M. and Tiwari, N. (2023) ‘A comprehensive survey of phishing: mediums, intended targets, attack and defence techniques and a novel taxonomy,’ International Journal of Information Security [Preprint]. [CrossRef]
- Gopi, R. et al. (2021) ‘Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things,’ Multimedia Tools and Applications, 81(19), pp. 26739–26757. [CrossRef]
- Gouda, W. et al. (2022) ‘Detection of COVID-19 based on chest x-rays using deep learning,’ Healthcare, 10(2), p. 343. [CrossRef]
- Gaur, L. & Jhanjhi, N. Z. (Eds.). (2023). Digital Twins and Healthcare: Trends, Techniques, and Challenges. IGI Global. [CrossRef]
- Ghani, Norjihan Binti Abdul, Suraya Hamid, Muneer Ahmad, Younes Saadi, N. Z. Jhanjhi, Mohammed A. Alzain, and Mehedi Masud. “Tracking Dengue on Twitter Using Hybrid Filtration-Polarity and Apache Flume.” Comput. Syst. Sci. Eng. 40, no. 3 (2022): 913-926. [CrossRef]
- H. Ashraf, F. Khan, U. Ihsan, F. Al-Quayed, N. Z. Jhanjhi and M. Humayun, “MABPD: Mobile Agent-Based Prevention and Black Hole Attack Detection in Wireless Sensor Networks,” 2023 International Conference on Business Analytics for Technology and Security (ICBATS), Dubai, United Arab Emirates, 2023, pp. 1-11. [CrossRef]
- H. Ashraf, M. Hanif, U. Ihsan, F. Al-Quayed, M. Humayun and N. Jhanjhi, “A Secure and Reliable Supply chain management approach integrated with IoT and Blockchain,” 2023 International Conference on Business Analytics for Technology and Security (ICBATS), Dubai, United Arab Emirates, 2023, pp. 1-9. [CrossRef]
- Hon, K.W. (2024) ‘Security risks and concepts,’ in Edward Elgar Publishing eBooks, pp. 141–157. [CrossRef]
- Humayun, M. et al. (2022) ‘A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma,’ Healthcare, 10(6), p. 1058. [CrossRef]
- Humayun, M., N. Z. Jhanjhi, B. Hamid, and G. Ahmed. “Emerging smart logistics and transportation using IoT and blockchain. IEEE Internet of Things Magazine, 3 (2), 58-62.” (2020). [CrossRef]
- Humayun, M., Khalil, M. I., Alwakid, G., & Jhanjhi, N. Z. (2022). Superlative feature selection based image classification using deep learning in medical imaging. Journal of Healthcare Engineering, 2022(1), 7028717. [CrossRef]
- Ispahany, J. et al. (2024) ‘Ransomware detection using machine learning: A review, research limitations and future directions,’ IEEE Access, 12, pp. 68785–68813. [CrossRef]
- Jacob, S. (no date) The Rapid Increase of Ransomware Attacks Over the 21st Century and Mitigation Strategies to Prevent Them from Arising. https://digitalcommons.liberty.edu/honors/1326/.
- Javaid, Mohd, Abid Haleem, Ravi Pratap Singh, Shahbaz Khan, and Rajiv Suman. “An extensive study on Internet of Behavior (IoB) enabled Healthcare-Systems: Features, facilitators, and challenges.” BenchCouncil Transactions on Benchmarks, Standards and Evaluations 2, no. 4 (2022): 100085. [CrossRef]
- Jhanjhi, N., Humayun, M. and Almuayqil, S.N. (2021) ‘Cyber security and privacy issues in industrial internet of things,’ Computer Systems Science and Engineering, 37(3), pp. 361–380. [CrossRef]
- Jhanjhi, N. Z., Sahil Verma, M. N. Talib, and Gagandeep Kaur. “A canvass of 5G network slicing: Architecture and security concern.” In IOP Conference Series: Materials Science and Engineering, vol. 993, no. 1, p. 012060. IOP Publishing, 2020. [CrossRef]
- King, T. (2023). The 28 Best Database Management Systems & Software for 2024. [online] Best Data Management Software, Vendors and Data Science Platforms. Available at: https://solutionsreview.com/data-management/the-best-database-management-systems-and-software-tools/ [Accessed 8 Jun. 2024].
- KU News, Jon Niccum. (2021). Cyberattack on Colonial Pipeline affected gas prices far less than initially reported, study finds. Retrieved from https://news.ku.edu/news/article/2021/12/16/cyberattack-colonial-pipeline-affected-gas-prices-far-less-initially-reported-study-finds#:~:text=While%20in%20May%2C%20fuel%20prices,largest%20for%20refined%20oil%20products.
- Kumari, A. and Sharma, I. (2024) ‘Mitigating Malvertising Threats: An Exploration of Machine Learning Classification Algorithms for Effective Detection,’ 2024 International Conference on Advancements in Smart, Secure and Intelligent Computing (ASSIC) [Preprint]. [CrossRef]
- Kok, S. H., Abdullah, A., Jhanjhi, N. Z., & Supramaniam, M. (2019). A review of intrusion detection system using machine learning approach. International Journal of Engineering Research and Technology, 12(1), 8-15.
- Lim, Marcus, Azween Abdullah, N. Z. Jhanjhi, Muhammad Khurram Khan, and Mahadevan Supramaniam. “Link prediction in time-evolving criminal network with deep reinforcement learning technique.” IEEE Access 7 (2019): 184797-184807. [CrossRef]
- Lazarovitz, L. (2021). Deconstructing the solarwinds breach. Computer Fraud & Security, 2021(6), 17–19. [CrossRef]
- Lim, K., Park, J. and Kim, D. (2024) ‘Phishing Vs. Legit: Comparative Analysis of Client-Side Resources of Phishing and Target Brand Websites,’ ACM [Preprint]. [CrossRef]
- Longtchi, T.T. et al. (2024) ‘Internet-Based Social Engineering Psychology, Attacks, and Defenses: A survey,’ Proceedings of the IEEE, pp. 1–37. [CrossRef]
- Murphy, G.J. (2024) ‘Conclusion: accessible moments and darkness on the edge of town,’ in Palgrave science fiction and fantasy, pp. 93–112. [CrossRef]
- Muslim, A.K., Dzulkifli, D.Z.M., Nadhim, M.H. and Abdellah, R.H. (2019). A Study of Ransomware Attacks: Evolution and Prevention. Journal of Social Transformation and Regional Development, [online] 1(1), pp.18–25. Available at: https://publisher.uthm.edu.my/ojs/index.php/jstard/article/view/5503/3327.
- Muzafar, S. and Jhanjhi, N.Z. (2020) ‘Success stories of ICT implementation in Saudi Arabia,’ in Advances in electronic government, digital divide, and regional development book series, pp. 151–163. [CrossRef]
- Nagar, G. (2024) ‘The Evolution of Ransomware: Tactics, techniques, and mitigation strategies,’ International Journal of Scientific Research and Management (IJSRM), 12(06), pp. 1282–1298. [CrossRef]
- Nish, A., Naumann, S. and Muir, J., 2022. Enduring cyber threats and emerging challenges to the financial sector. Carnegie Endowment for International Peace.
- Niveditha, V.S., Kunwar, R.S. and Kumar, K. (2024) ‘Ransomware attacks on IoT devices,’ in Chapman and Hall/CRC eBooks, pp. 124–147. [CrossRef]
- Ologunde, E. (2024) ‘Ransomware,’ SSRN Electronic Journal [Preprint]. [CrossRef]
- Osborne, C. (2021). Updated Kaseya ransomware attack FAQ: What we know now. [online] ZDNet. Available at: https://www.zdnet.com/article/updated-kaseya-ransomware-attack-faq-what-we-know-now/.
- Parekh, A. et al. (2023) ‘Multilayer symmetric and asymmetric technique for audiovisual cryptography,’ Multimedia Tools and Applications, 83(11), pp. 31465–31503. [CrossRef]
- Pelliccione, A. (2021, July 5). The ransomware threat rises to the next level: the Kaseya case, how it happened and how to defend yourself. Agenda Digitale. Retrieved 2022, from https://www.agendadigitale.eu/sicurezza/la-minaccia-ransomware-sale-di-livello-il-casokaseya-come-successo-e-come-difendersi.
- Robinson, P. (2023). What is REvil/Sodinokibi Ransomware. [online] Lepide Blog: A Guide to IT Security, Compliance and IT Operations. Available at: https://www.lepide.com/blog/what-is-revil-sodinokibi-ransomware/.
- S, A.C. and Shanker, R. (2023) ‘Zero Trust Resilience Strategy for Linux Crypto Ransomware Obviation and Recuperation,’ 2023 3rd International Conference on Intelligent Technologies (CONIT) [Preprint]. [CrossRef]
- S, K.P.D. and R, P.K.H. (2024) ‘A Systematic Study on Ransomware Attack: Types, Phases and Recent Variants,’ 2024 5th International Conference on Intelligent Communication Technologies and Virtual Mobile Networks (ICICV) [Preprint]. [CrossRef]
- SaberiKamarposhti, M., Ghorbani, A. and Yadollahi, M. (2024) ‘A comprehensive survey on image encryption: Taxonomy, challenges, and future directions,’ Chaos Solitons & Fractals, 178, p. 114361. [CrossRef]
- Saeed, Soobia, Afnizanfaizal Abdullah, N. Z. Jhanjhi, Mehmood Naqvi, Mehedi Masud, and Mohammed A. AlZain. “Hybrid GrabCut Hidden Markov Model for Segmentation.” Computers, Materials & Continua 72, no. 1 (2022). [CrossRef]
- Sangkaran, Theyvaa, Azween Abdullah, and N. Z. Jhanjhi. “Criminal community detection based on isomorphic subgraph analytics.” Open Computer Science 10, no. 1 (2020): 164-174. [CrossRef]
- Sangkaran, Theyvaa, Azween Abdullah, N. Z. JhanJhi, and Mahadevan Supramaniam. “Survey on isomorphic graph algorithms for graph analytics.” International Journal of Computer Science and Network Security 19, no. 1 (2019): 85-92.
- Shah, I. A., Jhanjhi, N. Z., & Ujjan, R. M. (2024). Drone Technology in the Context of the Internet of Things. In I. Shah & N. Jhanjhi (Eds.), Cybersecurity Issues and Challenges in the Drone Industry (pp. 88-107). IGI Global. [CrossRef]
- Shah, I. A., Jhanjhi, N. Z., & Ray, S. K. (2024). Artificial Intelligence Applications in the Context of the Security Framework for the Logistics Industry. In M. Ghonge, N. Pradeep, N. Jhanjhi, & P. Kulkarni (Eds.), Advances in Explainable AI Applications for Smart Cities (pp. 297-316). IGI Global. [CrossRef]
- Sharma, S. et al. (2024) ‘Implementation Analysis of Ransomware and Unmanned Aerial Vehicle Attacks,’ Wiley, pp. 165–211. [CrossRef]
- Sindiramutty, S.R. (2024) ‘Autonomous Threat Hunting: a future paradigm for AI-Driven Threat intelligence,’ arXiv (Cornell University) [Preprint]. [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Gharib, A. H., & Yun, K. J. (2024). Applications of Blockchain Technology in Supply Chain Management. In N. Jhanjhi & I. Shah (Eds.), Cybersecurity Measures for Logistics Industry Framework (pp. 248-304). IGI Global. [CrossRef]
- Sindiramutty, S.R., Tan, C.E., Lau, S.P., et al. (2024) ‘Explainable AI for cybersecurity,’ in Advances in computational intelligence and robotics book series, pp. 31–97. [CrossRef]
- Sindiramutty, S.R., Tan, C.E., Tee, W.J., et al. (2024) ‘Modern smart cities and open research challenges and issues of explainable artificial intelligence,’ in Advances in computational intelligence and robotics book series, pp. 389–424. [CrossRef]
- Sindiramutty, S.R., Tee, W.J., et al. (2024) ‘Explainable AI in healthcare application,’ in Advances in computational intelligence and robotics book series, pp. 123–176. [CrossRef]
- Stephens, T. G. (2021). Lessons learned: The colonial pipeline ransomware attack. California C.P.A.
- Usman, T.M. et al. (2023) ‘Diabetic retinopathy detection using principal component analysis multi-label feature extraction and classification,’ International Journal of Cognitive Computing in Engineering, 4, pp. 78–88. [CrossRef]
- Vijayalakshmi, B., Ramar, K., Jhanjhi, N. Z., Verma, S., Kaliappan, M., & Vijayalakshmi, K. & Ghosh, U.(2021). An attention-based deep learning model for traffic flow prediction using spatiotemporal features towards sustainable smart city. International Journal of Communication Systems, 34(3), e4609. [CrossRef]
- Wen, B.O.T. et al. (2023) ‘Detecting cyber threats with a Graph-Based NIDPS,’ in Advances in logistics, operations, and management science book series, pp. 36–74. [CrossRef]
- Zaman, Noor, and Azween B. Abdullah. “Position responsive routing protocol (prrp).” In 13th International Conference on Advanced Communication Technology (ICACT2011), pp. 644-648. IEEE, 2011.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).



