Submitted:
14 September 2024
Posted:
18 September 2024
You are already at the latest version
Abstract
Keywords:
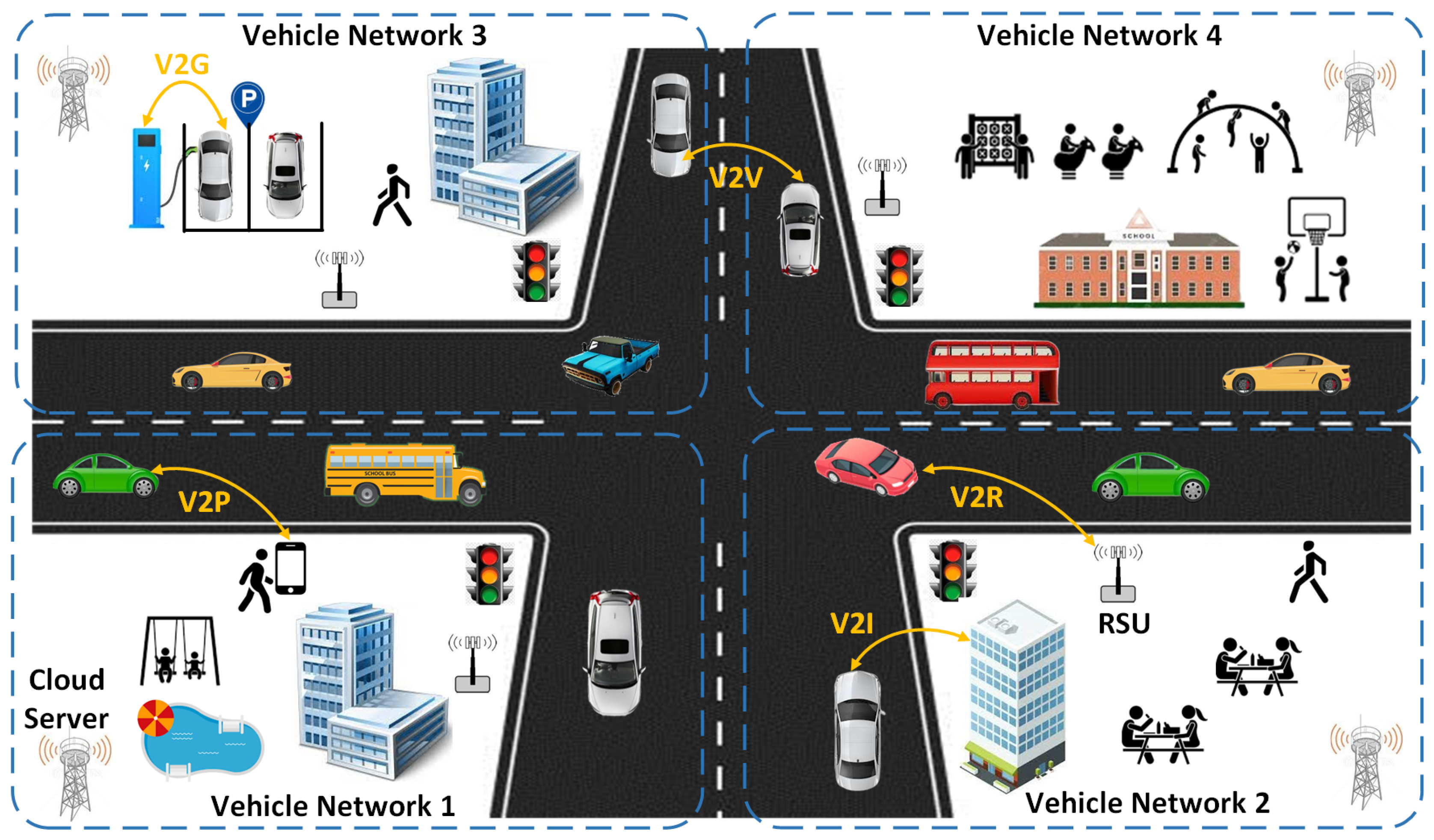
1. Introduction
1.1. Addressing Challenges of Data Source Authenticity
1.2. Addressing The Issue of Data Storing and Sharing Security
1.3. Main Contributions
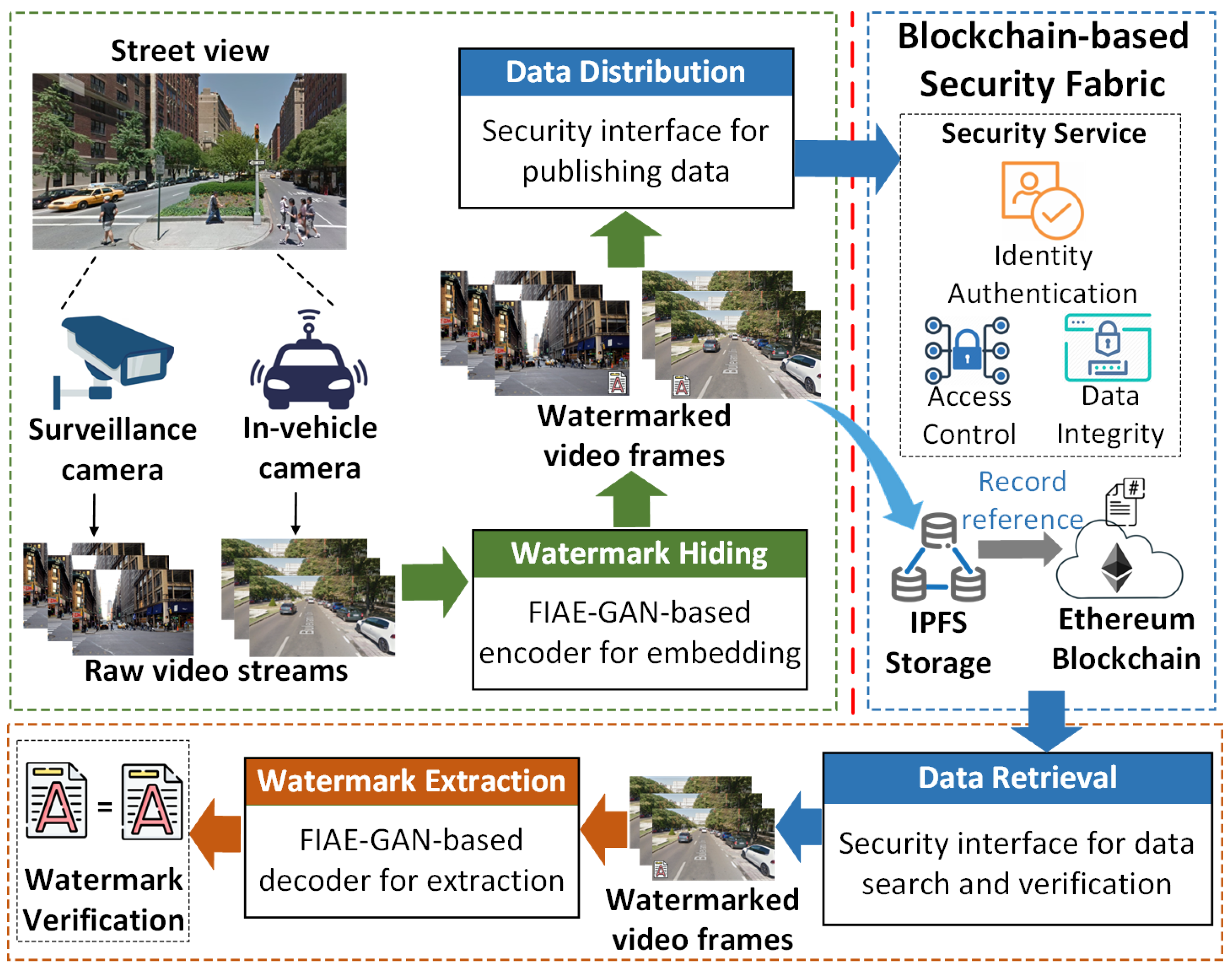
- We propose the system architecture of D2WaVe, a decentralized digital watermarking framework consisting of i) a novel FIAE-GAN model for watermark embedding and extraction and ii) BloVA, a Blockchain-based authentication scheme to support secure video data storage and sharing.
- We introduce a novel FIAE-GAN-based digital watermarking model and provide details on the encoder, decoder, and discriminator.
- We evaluate the performance of the watermarking model and overheads incurred by the video authentication framework. Experimental results demonstrate that both the AEM and FIM are crucial for the watermarking model’s performance, surpassing existing models in watermarked image quality and resilience against diverse attacks.
2. Background and Related Work
2.1. Digital Image Watermarking for Data Authentication
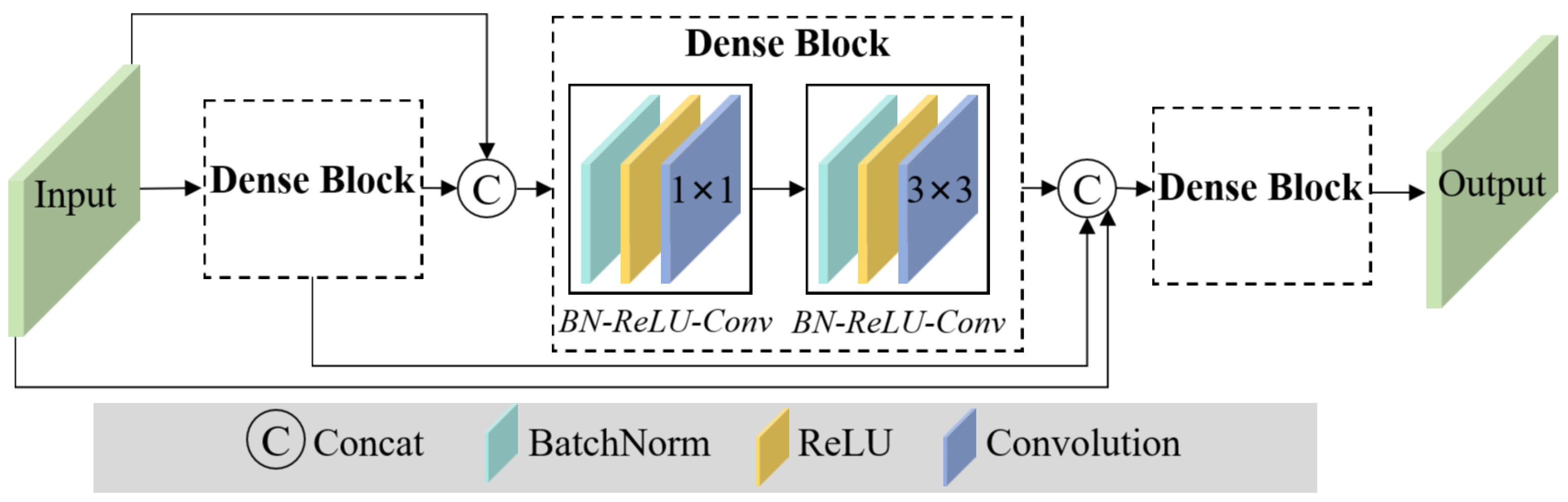
2.2. Feature Integration Module Using DenseNet
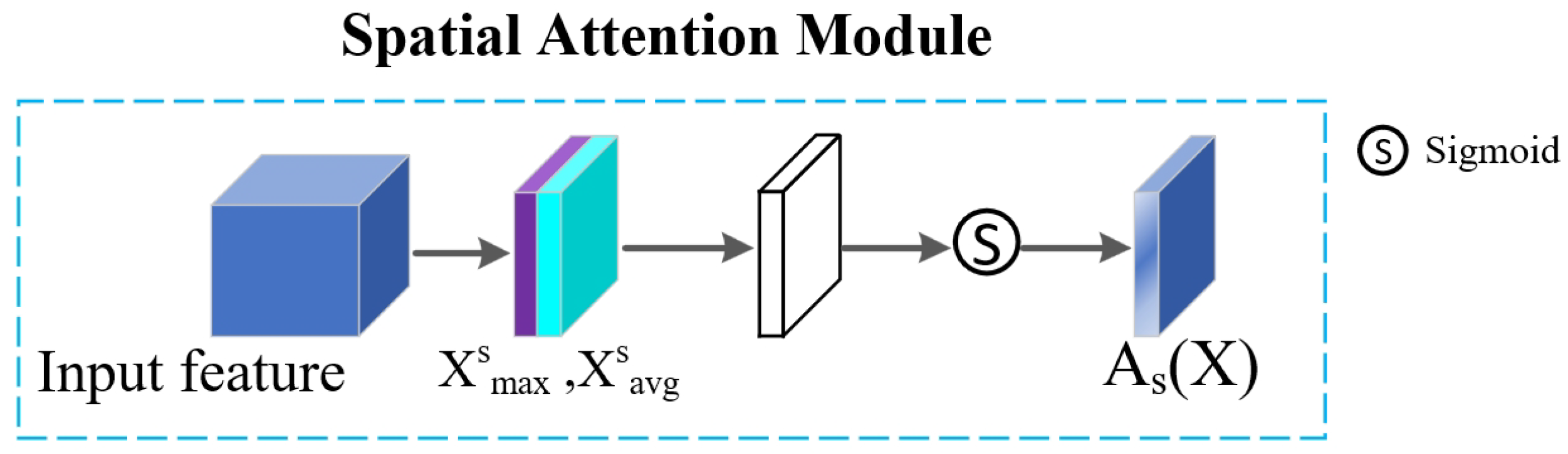
2.3. Attention-Enhanced Module
2.4. Blockchain for IoV Networks
3. D2WaVe: Design Rationale and System Architecture
3.1. System Settings and Adversary Model
3.2. System Overview
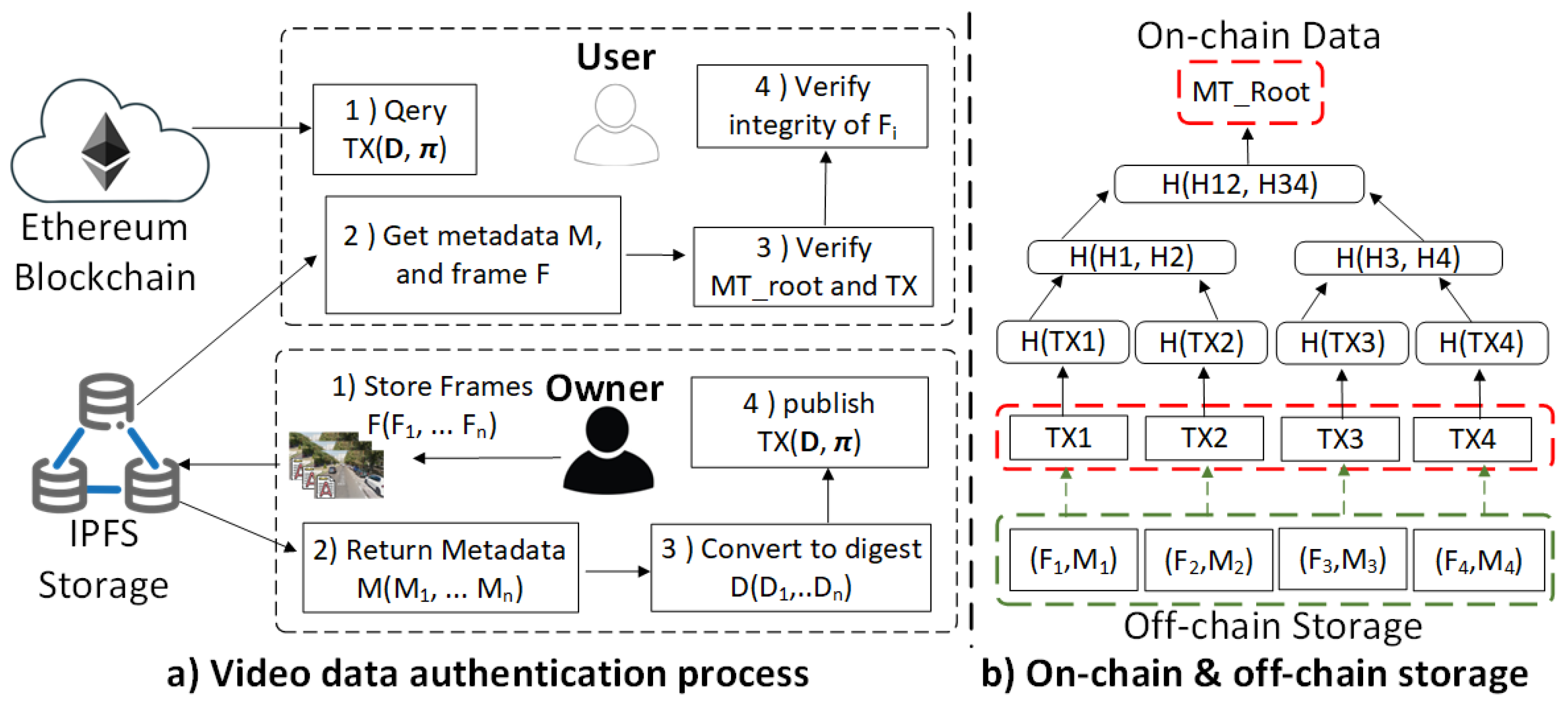
3.3. Video Frames Authentication Scheme
3.3.1. Watermark Generation
3.3.2. Data Publish
3.3.3. Data Retrieval
3.3.4. Watermark Verification
4. FIAE-GAN based Digital Watermarking Model
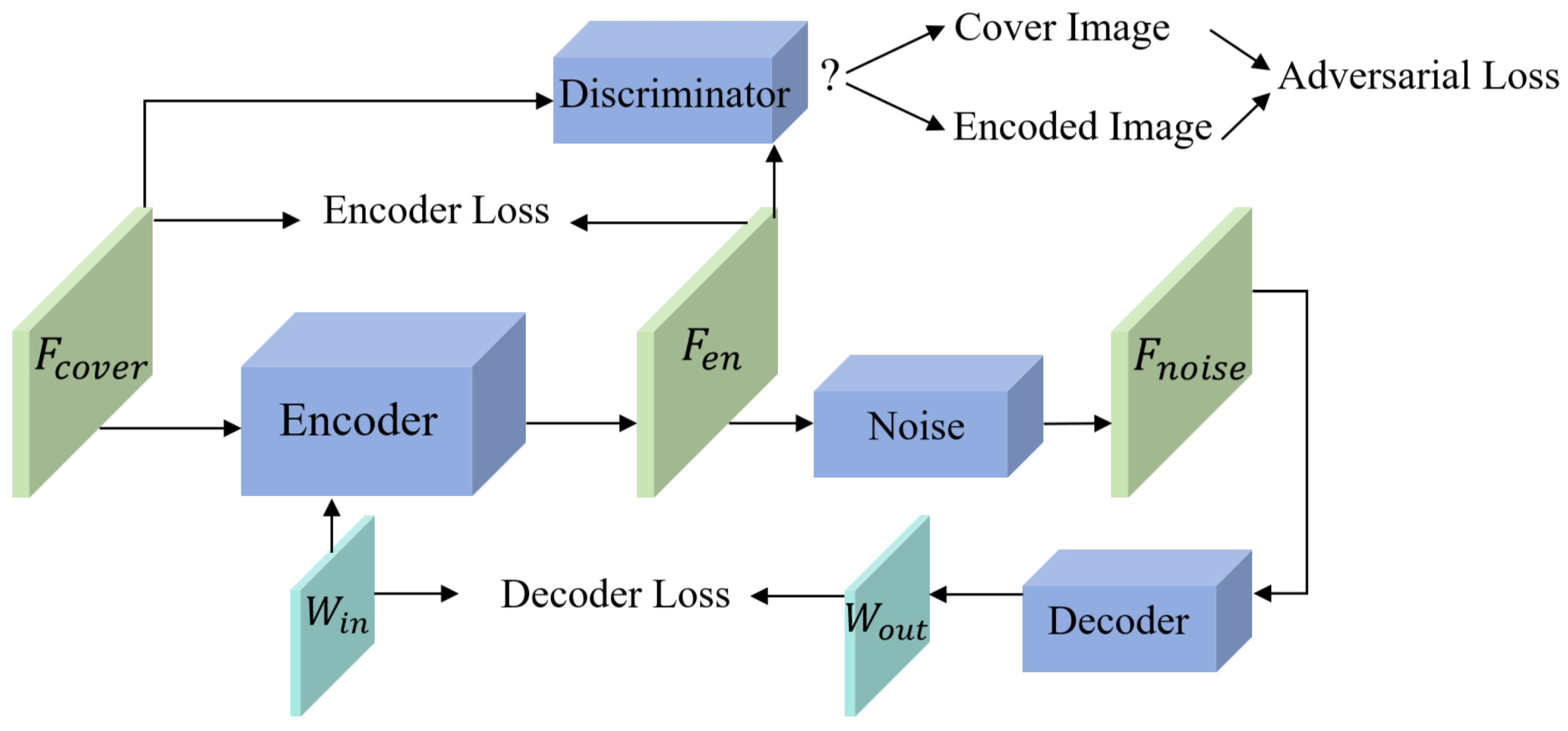
4.1. FIAE-GAN Watermarking Network Model
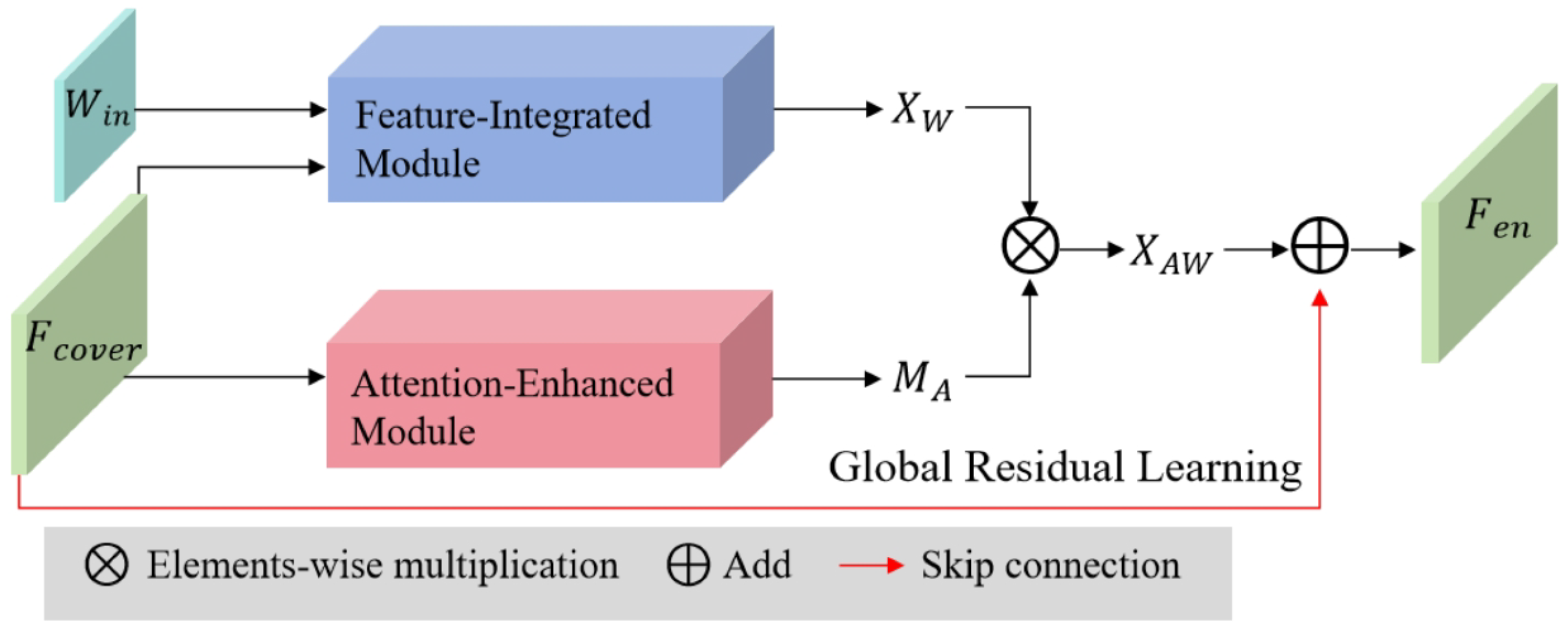
4.2. The structure of encoder
4.3. Watermark Extraction Decoder
4.4. Discriminator
5. Experimental Results and Discussions
5.1. Prototype Implementation and Experiment Configuration
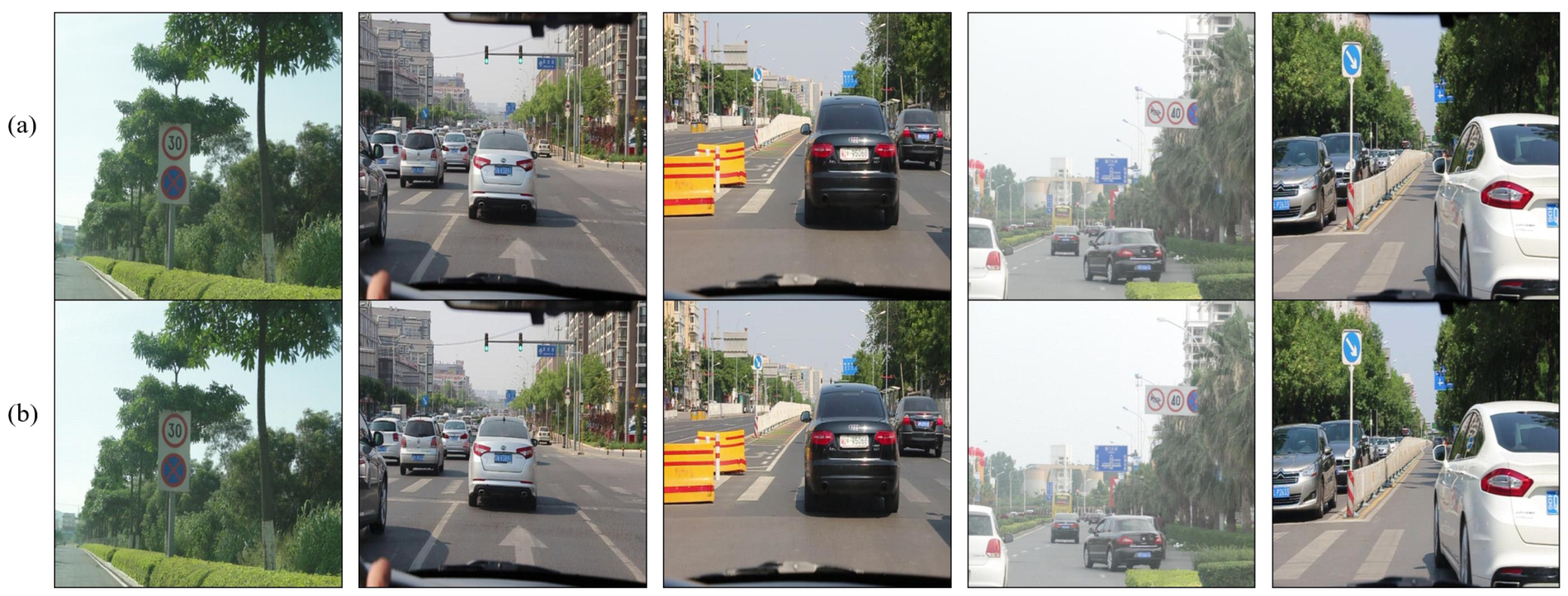
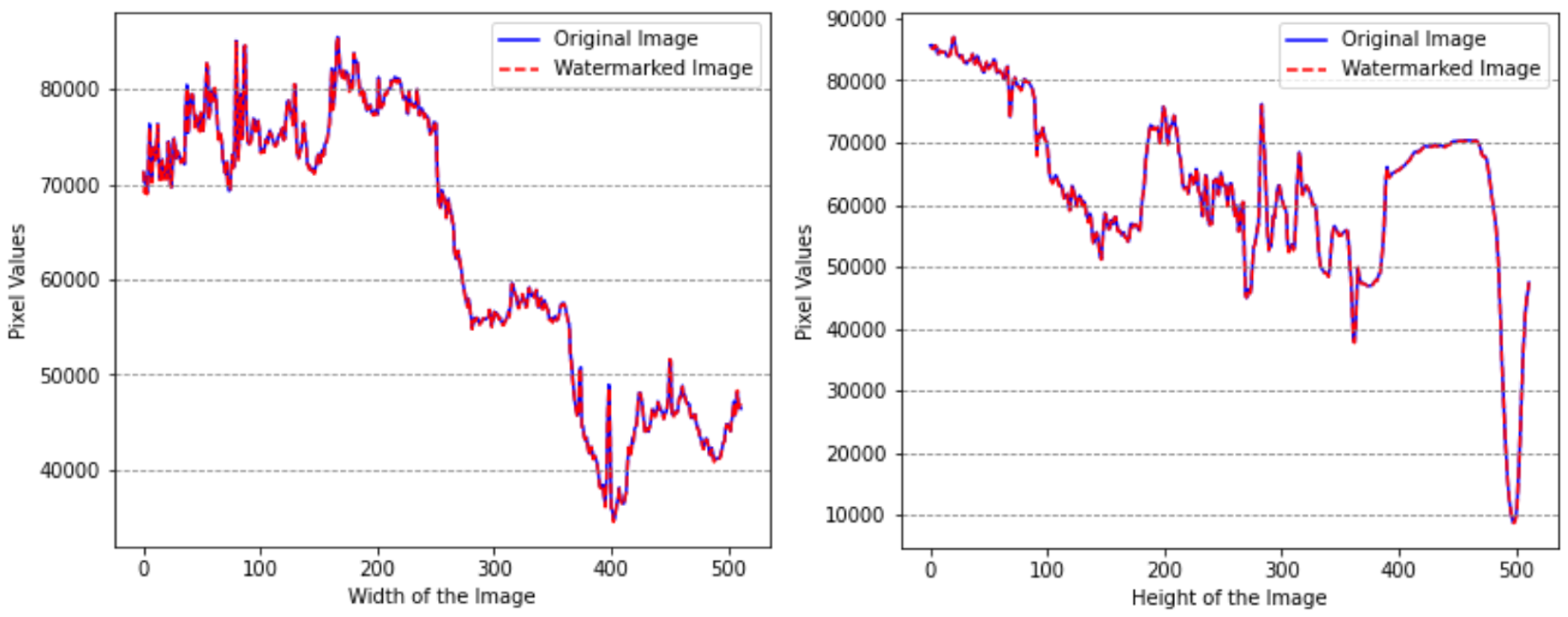
5.2. Subjective Evaluation of the proposed Watermarking Model
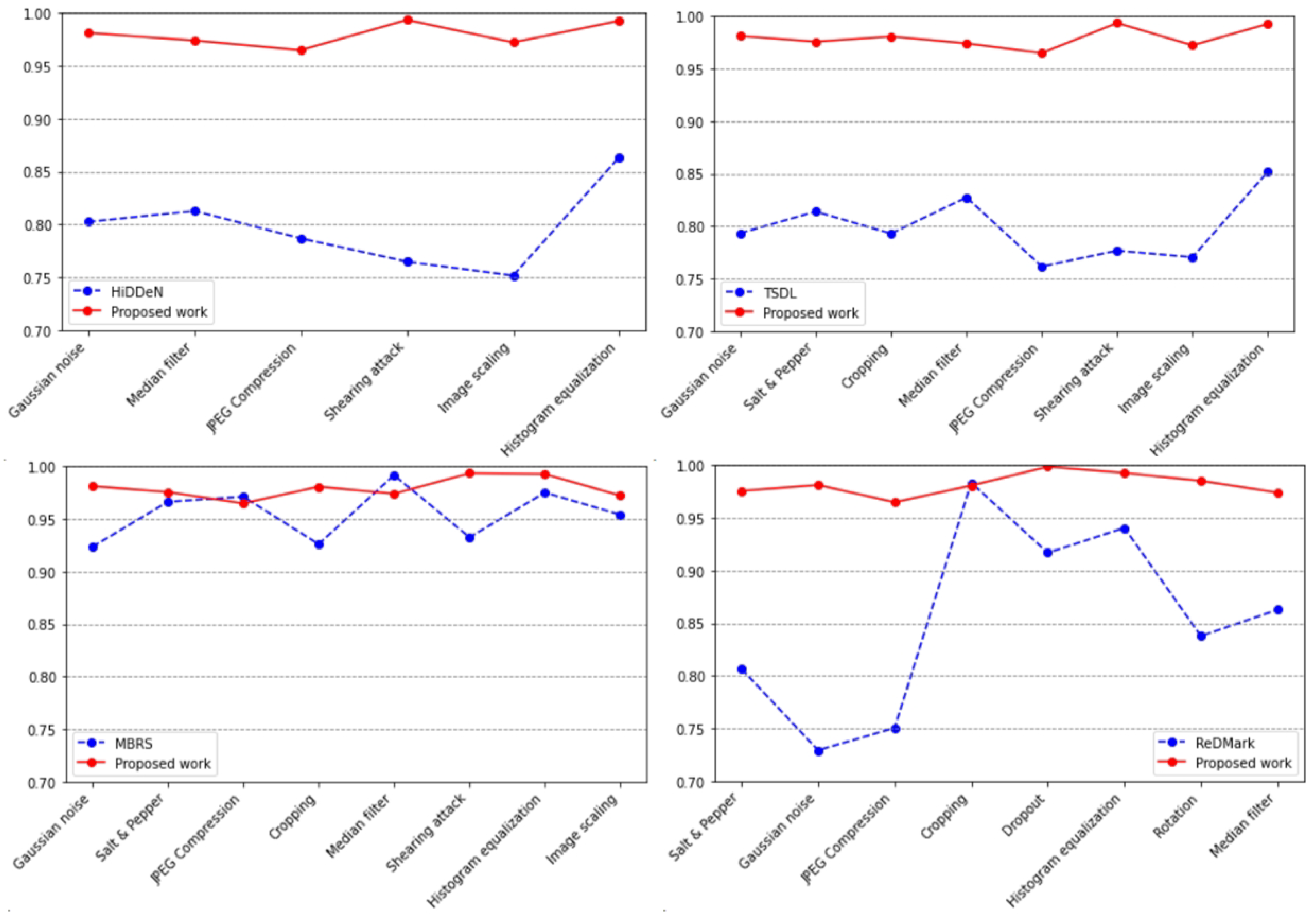
5.3. Objective Evaluation of the proposed Watermarking Model
5.4. Performance and Cost of Video Data Authentication
5.5. Security Analysis
6. Conclusions and Future Work
Author Contributions
Funding
Abbreviations
| AI | Artificial Intelligence |
| AEM | Attention-Enhanced Module |
| BN | Batch Normalization |
| CAV | Connected Automated Vehicles |
| CCTSDB | Chinese Traffic Sign Detection Benchmark |
| DIW | Digital Image Watermarking |
| DLT | Distributed Ledger Technology |
| DFT | Discrete Fourier Transform |
| DCT | Discrete Cosine Transform |
| DWT | Discrete Wavelet Transform |
| ECU | Electronic Control Units |
| FIAE-GAN | Feature-Integrated and Attention-Enhanced Model Based on GAN |
| FIM | Feature-Integrated Module |
| GAN | Generative Adversarial Network |
| GANs | Generative Adversarial Networks |
| IoV | Internet of Vehicles |
| ITS | Intelligent Transportation System |
| MOA | Microservices-Oriented Architecture |
| P2P | Peer-to-Peer |
| PSNR | Peak Signal-to-Noise Ratio |
| PUF | Physically Unclonable Function |
| ReLU | Rectified Linear Unit |
| SIFT | Scale-Invariant Feature Transform |
| SC | Smart Contract |
| SOA | Service-Oriented Architecture |
| SSIM | Structural Similarity Index Metric |
| V2G | Vehicle-to-grid |
| V2I | Vehicle-to-Infrastructure |
| V2R | Vehicle-to-Roadside Unit |
| V2V | Vehicle-to-Vehicle |
| V2X | Vehicle-to-Everything |
References
- Ji, B.; Zhang, X.; Mumtaz, S.; Han, C.; Li, C.; Wen, H.; Wang, D. Survey on the internet of vehicles: Network architectures and applications. IEEE Communications Standards Magazine 2020, 4, 34–41. [Google Scholar] [CrossRef]
- Xu, R.; Nikouei, S.Y.; Nagothu, D.; Fitwi, A.; Chen, Y. Blendsps: A blockchain-enabled decentralized smart public safety system. Smart Cities 2020, 3, 928–951. [Google Scholar] [CrossRef]
- Xu, R.; Nagothu, D.; Chen, Y. AR-Edge: Autonomous and Resilient Edge Computing Architecture for Smart Cities; 2024; pp. 1–21. [Google Scholar]
- Mollah, M.B.; Zhao, J.; Niyato, D.; Guan, Y.L.; Yuen, C.; Sun, S.; Lam, K.Y.; Koh, L.H. Blockchain for the internet of vehicles towards intelligent transportation systems: A survey. IEEE Internet of Things Journal 2020, 8, 4157–4185. [Google Scholar] [CrossRef]
- Nin, J.; Ricciardi, S. Digital watermarking techniques and security issues in the information and communication society. In Proceedings of the 2013 27th International Conference on Advanced Information Networking and Applications Workshops. IEEE; 2013; pp. 1553–1558. [Google Scholar]
- Li, J.; Song, Z.; Zhang, Z.; Li, Y.; Cao, C. In-Vehicle Digital Forensics for Connected and Automated Vehicles With Public Auditing. IEEE Internet of Things Journal 2023. [Google Scholar] [CrossRef]
- Xu, R.; Nagothu, D.; Chen, Y.; Aved, A.; Ardiles-Cruz, E.; Blasch, E. A Secure Interconnected Autonomous System Architecture for Multi-Domain IoT Ecosystems. IEEE Communications Magazine 2024, 62, 52–57. [Google Scholar] [CrossRef]
- Nagothu, D.; Xu, R.; Nikouei, S.Y.; Chen, Y. A microservice-enabled architecture for smart surveillance using blockchain technology. In Proceedings of the 2018 IEEE international smart cities conference (ISC2). IEEE; 2018; pp. 1–4. [Google Scholar]
- Xu, R.; Chen, Y. μDFL: A secure microchained decentralized federated learning fabric atop IoT networks. IEEE Transactions on Network and Service Management 2022, 19, 2677–2688. [Google Scholar] [CrossRef]
- Benet, J. Ipfs-content addressed, versioned, p2p file system. arXiv preprint arXiv:1407.3561 2014. [Google Scholar]
- Wu, W.; Dai, J.; Huang, H.; Zhao, Q.; Zeng, G.; Li, R. A digital watermark method for in-vehicle network security enhancement. IEEE Transactions on Vehicular Technology 2023, 72, 8398–8408. [Google Scholar] [CrossRef]
- Changalvala, R.; Malik, H. LiDAR data integrity verification for autonomous vehicle. IEEE Access 2019, 7, 138018–138031. [Google Scholar] [CrossRef]
- Wang, C.; Cheng, X.; Li, J.; He, Y.; Xiao, K. A survey: Applications of blockchain in the internet of vehicles. EURASIP Journal on wireless communications and networking 2021, 2021, 1–16. [Google Scholar] [CrossRef]
- Ko, H.J.; Huang, C.T.; Horng, G.; Shiuh-Jeng, W. Robust and blind image watermarking in DCT domain using inter-block coefficient correlation. Information Sciences 2020, 517, 128–147. [Google Scholar] [CrossRef]
- Liu, J.; Huang, J.; Luo, Y.; Cao, L.; Yang, S.; Wei, D.; Zhou, R. An optimized image watermarking method based on HD and SVD in DWT domain. IEEE Access 2019, 7, 80849–80860. [Google Scholar] [CrossRef]
- Jin, T.; Zhang, W. A novel interpolated DFT synchrophasor estimation algorithm with an optimized combined cosine self-convolution window. IEEE Transactions on Instrumentation and Measurement 2020, 70, 1–10. [Google Scholar] [CrossRef]
- Ding, S.; Zhang, L.; Pan, M.; Yuan, X. PATROL: Privacy-Oriented Pruning for Collaborative Inference Against Model Inversion Attacks. In Proceedings of the Proceedings of the IEEE/CVF Winter Conference on Applications of Computer Vision, 2024; pp. 4716–4725.
- Zhou, X.; Lei, X.; Yang, C.; Shi, Y.; Zhang, X.; Shi, J. Handling Data Heterogeneity for IoT Devices in Federated Learning: A Knowledge Fusion Approach. IEEE Internet of Things Journal 2023. [Google Scholar] [CrossRef]
- Liu, X.; Liu, Z.; Chatterjee, S.; Portfleet, M.; Sun, Y. Understanding human behaviors and injury factors in underground mines using data analytics. In Proceedings of the 2021 43rd Annual International Conference of the IEEE Engineering in Medicine & Biology Society (EMBC); IEEE, 2021; pp. 2459–2462. [Google Scholar]
- Chen, B.; Zhang, Z.; Li, Y.; Lu, G.; Zhang, D. Multi-label chest X-ray image classification via semantic similarity graph embedding. IEEE Transactions on Circuits and Systems for Video Technology 2021, 32, 2455–2468. [Google Scholar] [CrossRef]
- Mun, S.M.; Nam, S.H.; Jang, H.U.; Kim, D.; Lee, H.K. A robust blind watermarking using convolutional neural network. arXiv preprint arXiv:1704.03248 2017. [Google Scholar]
- Ahmadi, M.; Norouzi, A.; Karimi, N.; Samavi, S.; Emami, A. ReDMark: Framework for residual diffusion watermarking based on deep networks. Expert Systems with Applications 2020, 146, 113157. [Google Scholar] [CrossRef]
- Huang, Z.; Zhang, J.; Zhang, Y.; Shan, H. DU-GAN: Generative adversarial networks with dual-domain U-Net-based discriminators for low-dose CT denoising. IEEE Transactions on Instrumentation and Measurement 2021, 71, 1–12. [Google Scholar] [CrossRef]
- Zhu, J.; Kaplan, R.; Johnson, J.; Fei-Fei, L. Hidden: Hiding data with deep networks. In Proceedings of the Proceedings of the European conference on computer vision (ECCV), 2018; pp. 657–672.
- Huang, G.; Liu, Z.; Van Der Maaten, L.; Weinberger, K.Q. Densely connected convolutional networks. In Proceedings of the Proceedings of the IEEE conference on computer vision and pattern recognition, 2017, pp.; pp. 4700–4708.
- Zhang, K.; Guo, Y.; Wang, X.; Yuan, J.; Ding, Q. Multiple feature reweight densenet for image classification. IEEE access 2019, 7, 9872–9880. [Google Scholar] [CrossRef]
- Adegun, A.A.; Viriri, S. FCN-based DenseNet framework for automated detection and classification of skin lesions in dermoscopy images. IEEE Access 2020, 8, 150377–150396. [Google Scholar] [CrossRef]
- Liu, X.; Zhao, C. AGFA-Net: Attention-Guided and Feature-Aggregated Network for Coronary Artery Segmentation using Computed Tomography Angiography. arXiv preprint arXiv:2406.08724 2024. [Google Scholar]
- Hu, J.; Shen, L.; Sun, G. Squeeze-and-excitation networks. In Proceedings of the Proceedings of the IEEE conference on computer vision and pattern recognition, 2018; pp. 7132–7141.
- Yu, C. Attention based data hiding with generative adversarial networks. In Proceedings of the Proceedings of the AAAI conference on artificial intelligence, 2020; Volume 34, pp. 1120–1128.
- Nakamoto, S. Bitcoin: A peer-to-peer electronic cash system. Technical report, Manubot 2019. [Google Scholar]
- Kang, J.; Yu, R.; Huang, X.; Wu, M.; Maharjan, S.; Xie, S.; Zhang, Y. Blockchain for secure and efficient data sharing in vehicular edge computing and networks. IEEE internet of things journal 2018, 6, 4660–4670. [Google Scholar] [CrossRef]
- Javaid, U.; Aman, M.N.; Sikdar, B. DrivMan: Driving trust management and data sharing in VANETS with blockchain and smart contracts. In Proceedings of the 2019 IEEE 89th Vehicular Technology Conference (VTC2019-Spring). IEEE; 2019; pp. 1–5. [Google Scholar]
- Shi, K.; Zhu, L.; Zhang, C.; Xu, L.; Gao, F. Blockchain-based multimedia sharing in vehicular social networks with privacy protection. Multimedia Tools and Applications 2020, 79, 8085–8105. [Google Scholar] [CrossRef]
- Nagothu, D.; Xu, R.; Chen, Y.; Blasch, E.; Aved, A. Defakepro: Decentralized deepfake attacks detection using enf authentication. IT Professional 2022, 24, 46–52. [Google Scholar] [CrossRef]
- Xu, R.; Chen, Y.; Chen, G.; Blasch, E. SAUSA: Securing Access, Usage, and Storage of 3D Point CloudData by a Blockchain-Based Authentication Network. Future Internet 2022, 14, 354. [Google Scholar] [CrossRef]
- Trautwein, D.; Raman, A.; Tyson, G.; Castro, I.; Scott, W.; Schubotz, M.; Gipp, B.; Psaras, Y. Design and evaluation of IPFS: A storage layer for the decentralized web. In Proceedings of the Proceedings of the ACM SIGCOMM 2022 Conference, 2022; pp. 739–752.
- Icezero00. CCTSDB-YOLO, 2022.
- Flask: A Pyhon Microframework. [Online]. Available online: https://flask.palletsprojects.com/Accessed on September 2022.
- pyca/cryptography documentation. [Online]. Available online: https://cryptography.io/Accessed on September 2022.
- Solidity. https://docs.soliditylang.org/en/v0.8.13/Accessed on September 2022.
- Go-ethereum. https://ethereum.github.io/go-ethereum/Accessed on September 2022.
- Bellavia, F.; Colombo, C. Is there anything new to say about SIFT matching? International journal of computer vision 2020, 128, 1847–1866. [Google Scholar] [CrossRef]
- Pele, O.; Werman, M. A linear time histogram metric for improved sift matching. In Proceedings of the Computer Vision–ECCV 2008: 10th European Conference on Computer Vision, Marseille, France, 12–18 October 2008; Proceedings, Part III 10. Springer, 2008; pp. 495–508. [Google Scholar]
- Luo, X.; Zhan, R.; Chang, H.; Yang, F.; Milanfar, P. Distortion agnostic deep watermarking. In Proceedings of the Proceedings of the IEEE/CVF conference on computer vision and pattern recognition, 2020; pp. 13548–13557.
- Liu, Y.; Guo, M.; Zhang, J.; Zhu, Y.; Xie, X. A novel two-stage separable deep learning framework for practical blind watermarking. In Proceedings of the Proceedings of the 27th ACM International conference on multimedia, 2019; pp. 1509–1517.
- Jia, Z.; Fang, H.; Zhang, W. Mbrs: Enhancing robustness of dnn-based watermarking by mini-batch of real and simulated jpeg compression. In Proceedings of the Proceedings of the 29th ACM international conference on multimedia, 2021; pp. 41–49.

| Model | PSNR | SSIM |
|---|---|---|
| HiDDeN [24] | 32.14 | 0.9315 |
| TSDL [46] | 33.50 | - |
| DA [45] | 33.70 | - |
| MBRS [47] | 35.08 | 0.8914 |
| ReDMark [22] | 35.93 | 0.9660 |
| FIAE-GAN | 35.89 | 0.9679 |
| Attack | Noise density | HiDDeN [.%] | FIAE-GAN [.%] |
|---|---|---|---|
| Gaussian noise | 0.001 | 85.57 | 100.00 |
| 0.05 | 80.23 | 98.13 | |
| 0.10 | 76.81 | 96.85 | |
| JPEG Compression | QF=10 | 73.39 | 94.12 |
| QF=50 | 78.67 | 96.49 | |
| QF=90 | 95.51 | 99.21 | |
| Cropping | [20, 20, 420, 420] | 78.82 | 98.08 |
| Dropout | 0.3 | 87.91 | 99.87 |
| Salt & Pepper | 0.001 | 91.34 | 99.84 |
| 0.05 | 82.73 | 99.31 | |
| 0.1 | 77.56 | 97.57 | |
| Rotation | 45° | 78.81 | 98.53 |
| 90° | 72.94 | 98.12 | |
| Median filter | [2, 2] | 88.39 | 99.64 |
| [3,3] | 81.27 | 97.41 | |
| Adjust Brightness | 1.1 | 92.61 | 98.94 |
| 1.3 | 86.38 | 97.37 | |
| Adjust Contrast | 1.0 | 82.92 | 97.52 |
| 2.0 | 72.45 | 96.87 | |
| Image scaling | 0.5 | 75.14 | 97.23 |
| 2 | 78.45 | 96.61 | |
| Shearing attack | [0.4, 0.4] | 76.47 | 99.36 |
| Histogram equalization | 1.0 | 86.37 | 99.28 |
| Stage | 1 | 2 | 3 | 4 | 5 | 6 |
|---|---|---|---|---|---|---|
| Latency | 1.09 | 0.43 | 5.17 | 0.04 | 0.02 | 0.62 |
| Gas Used | Cost (Ether) | Cost ($) | |
|---|---|---|---|
| Deploy Smart Contract | 190,573 | 0.000191 | 0.45 |
| Update Smart Contract | 875,974 | 0.000876 | 2.07 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




