Submitted:
08 September 2024
Posted:
09 September 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background
2.1. Software Defined Networking (SDN)
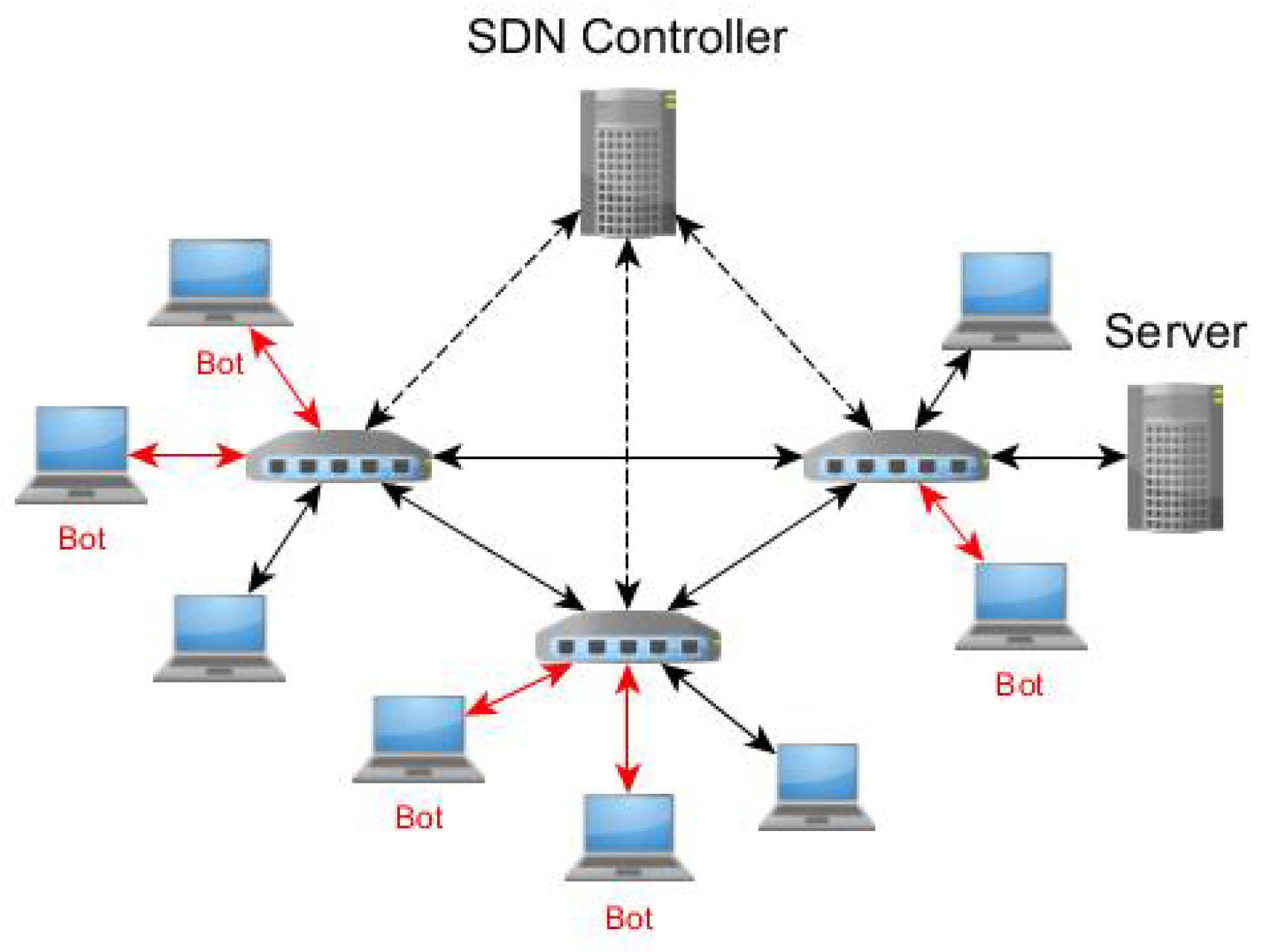
2.2. Distributed Denial of Service (DDoS) Attack
2.2.1. Definition
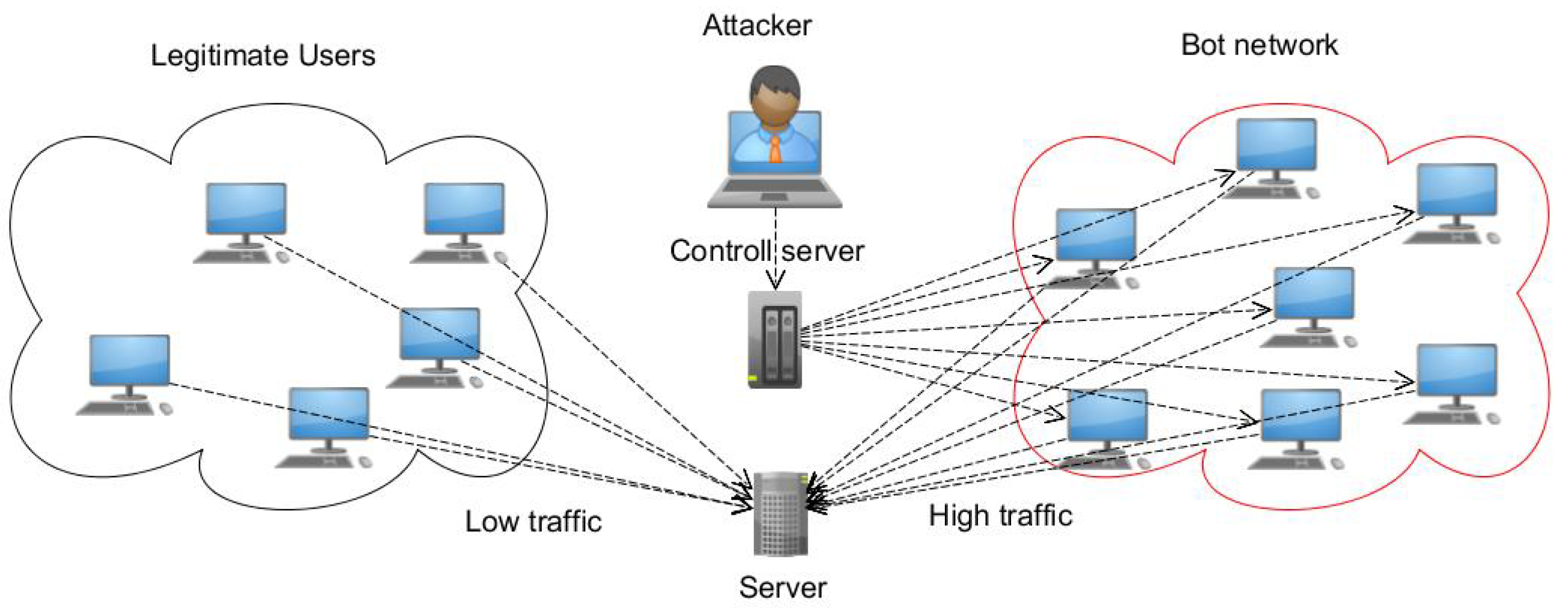
2.2.2. How DDoS Attacks Are Performed
2.2.3. Target of DDoS Attack
2.2.4. DDoS Attack Types
2.2.5. Challenges of DDoS Mitigation
2.2.6. Defense Approaches
3. Problem Modeling Modeling and Statement
4. The Proposed Method Proposed
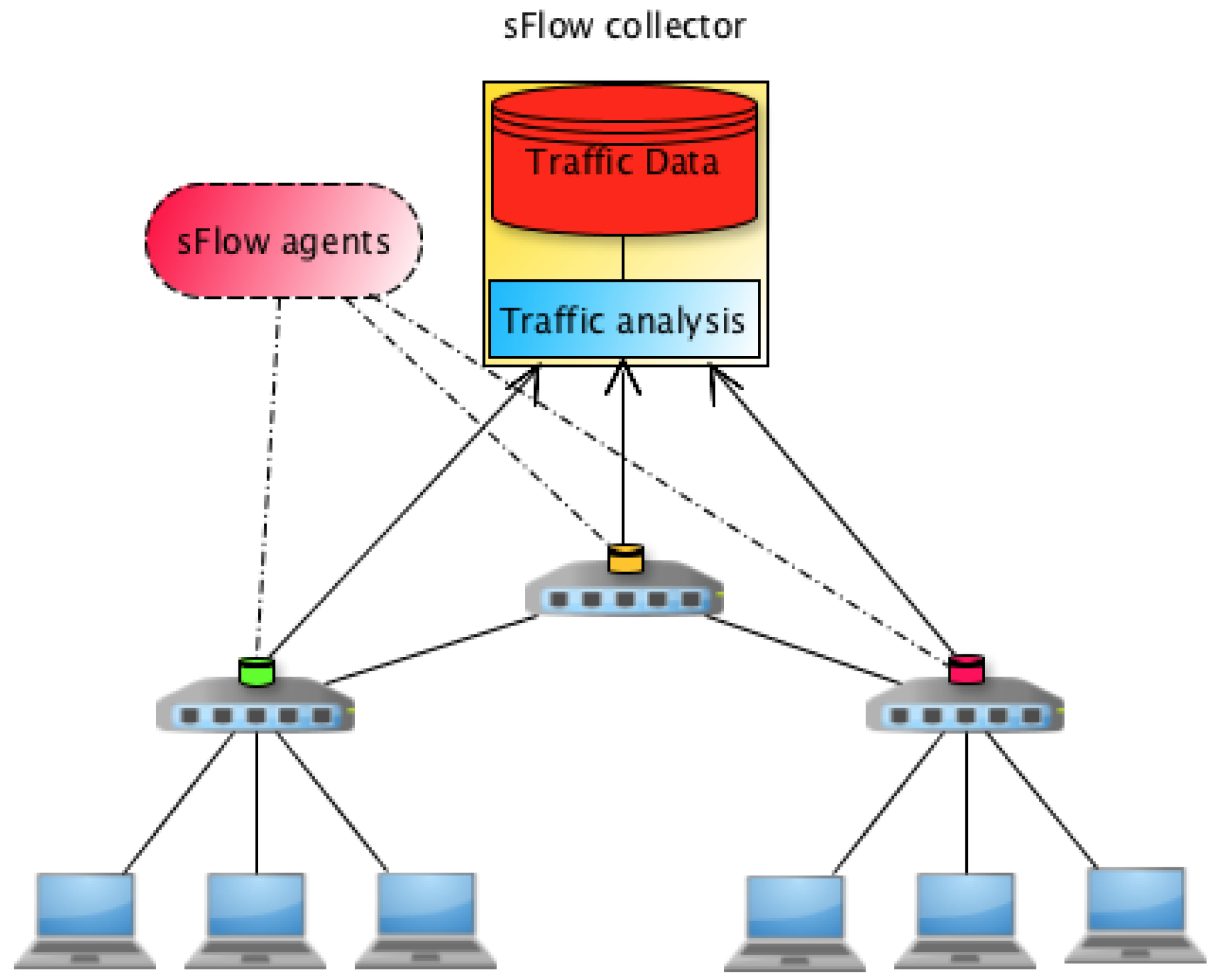
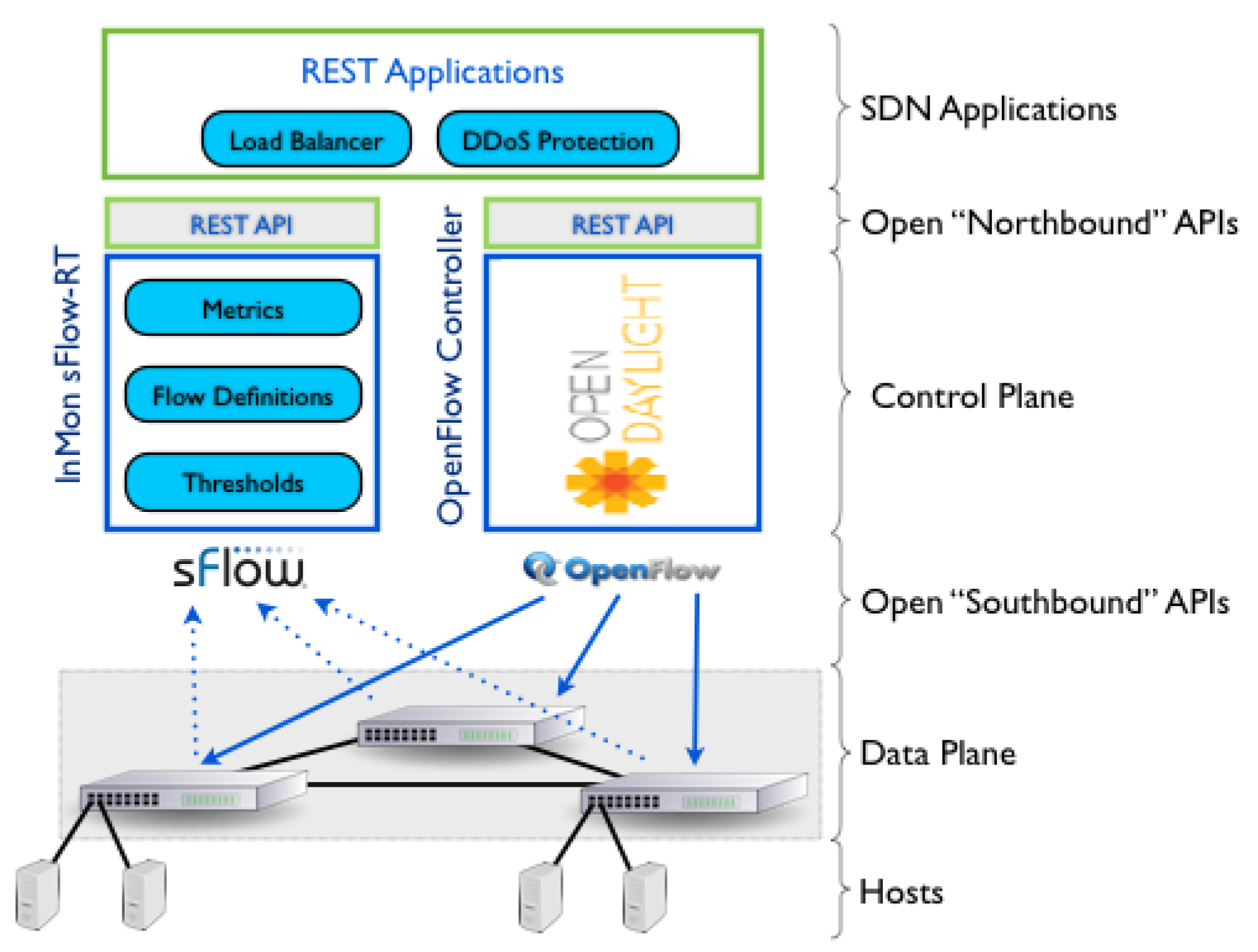
4.1. DDoS Detection and Mitigation System Using sFlow
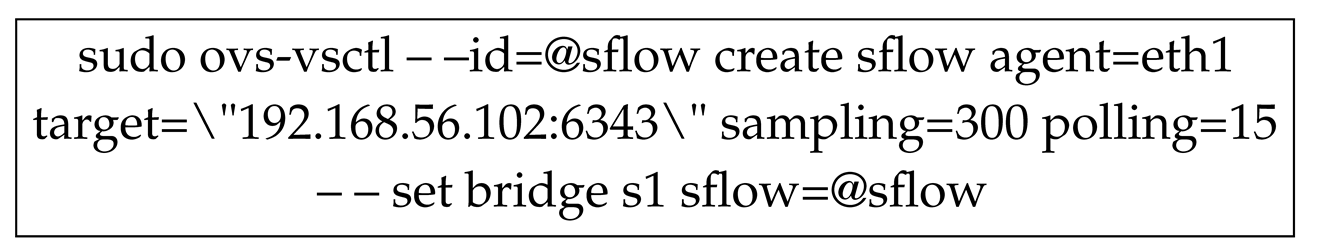
| Algorithm 1 Flow Monitoring and DDoS Attack Detection |
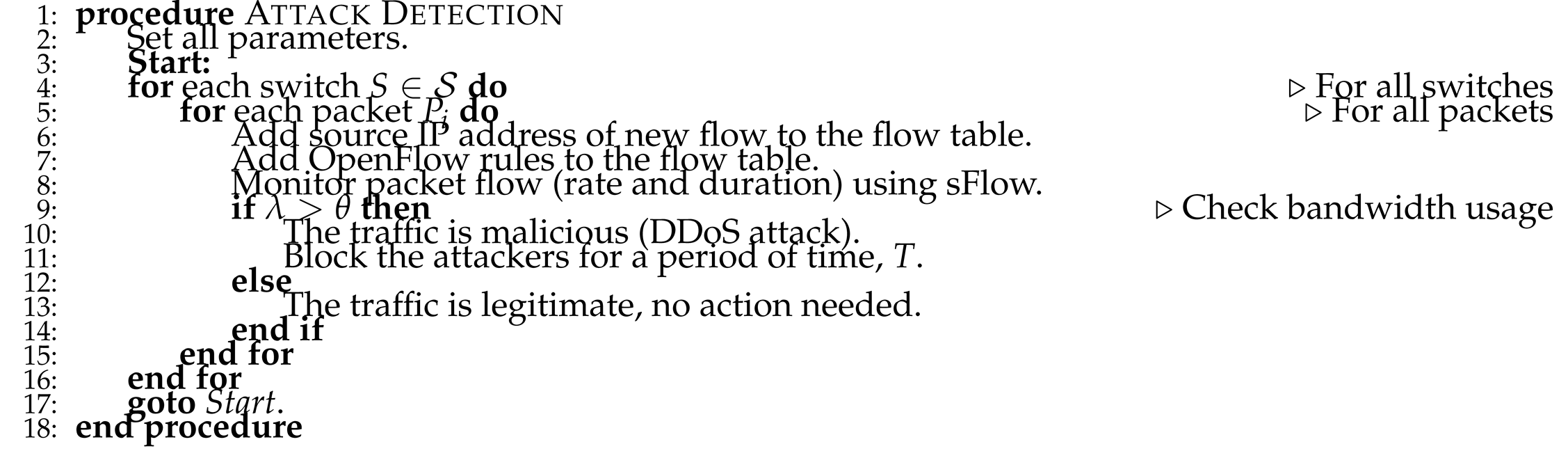 |
5. Testbed and Evaluation
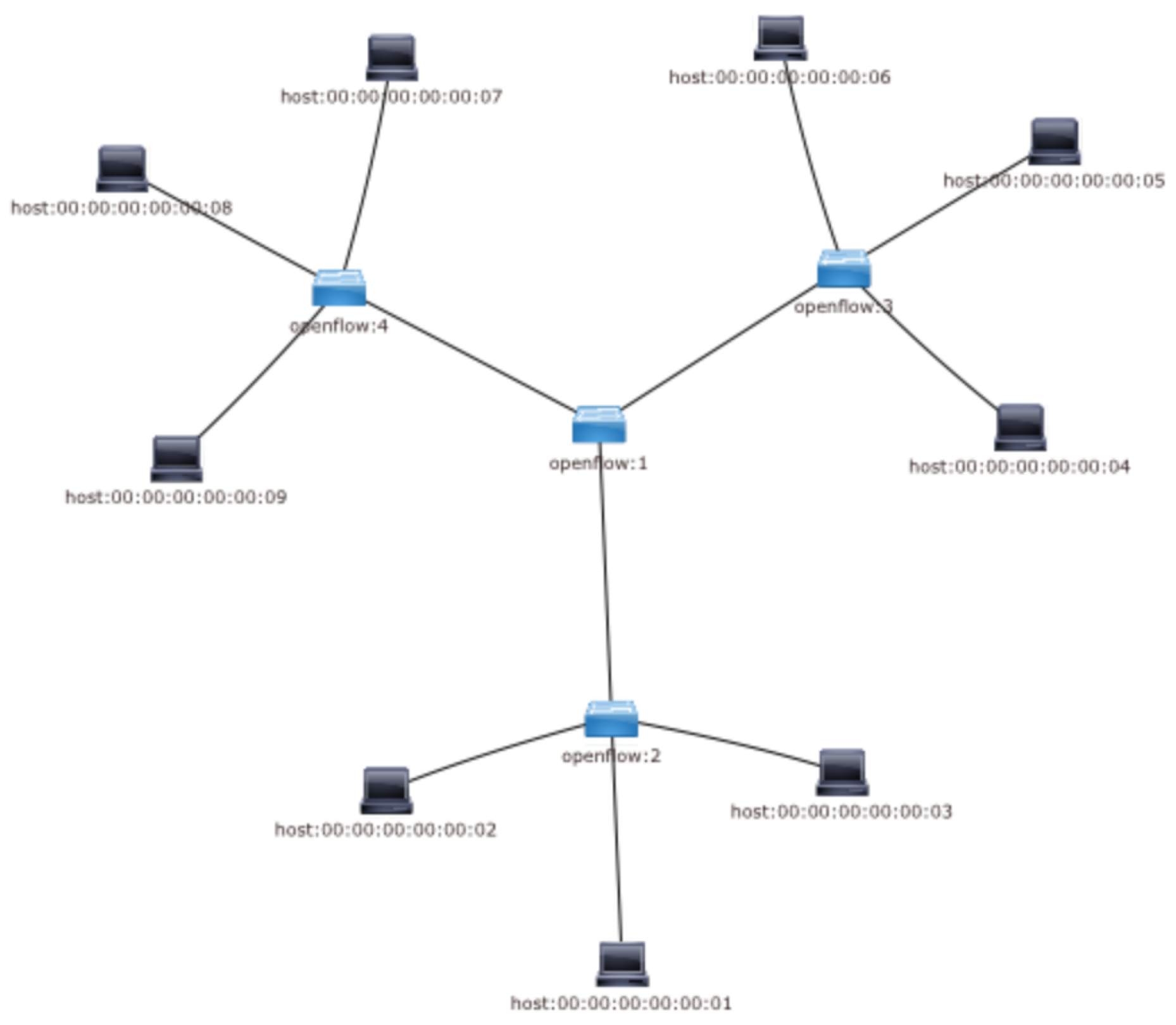
5.1. Network Emulator
5.2. SDN Controller
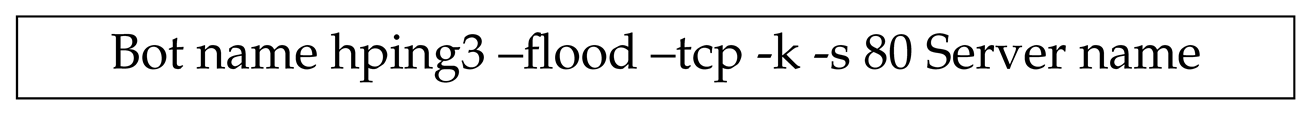
5.3. Network Traffic Generator
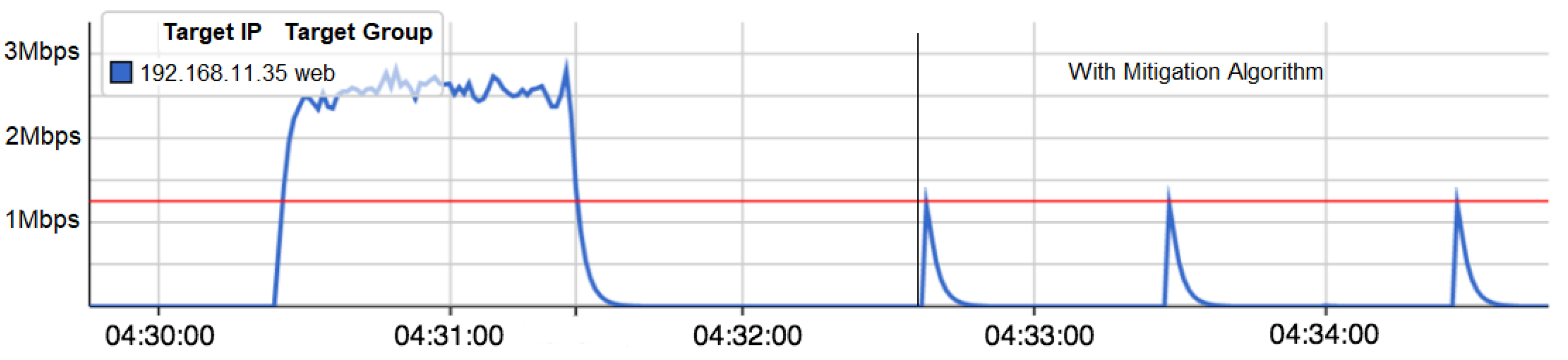
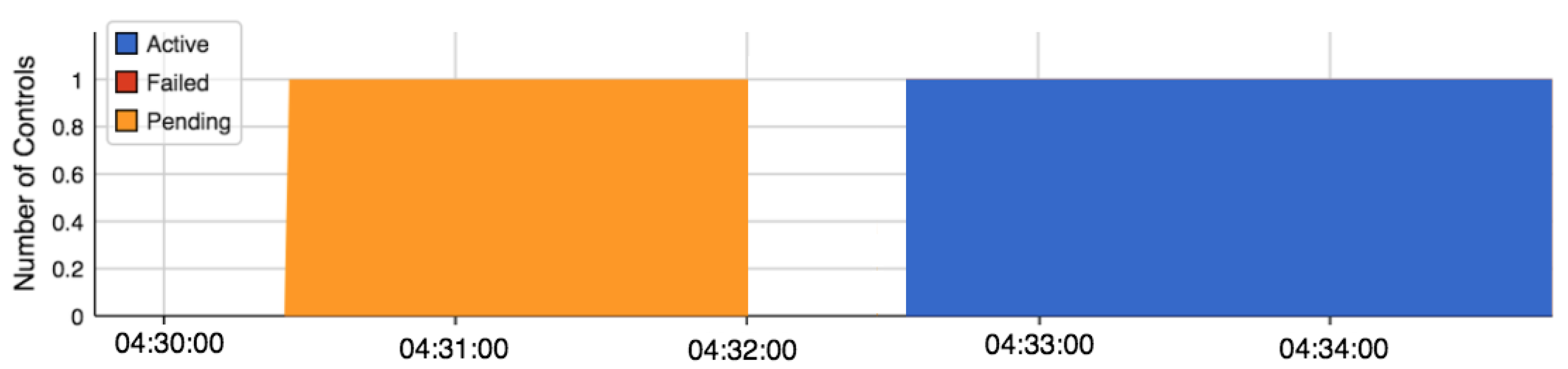
5.4. Case Study
6. Related Work
7. Conclusion
8. Future Work
Author Contributions
Funding
Informed Consent Statement
Acknowledgments
References
- Khan, Latif U. , Zhu Han, Walid Saad, Ekram Hossain, Mohsen Guizani, and Choong Seon Hong. "Digital twin of wireless systems: Overview, taxonomy, challenges, and opportunities.". IEEE Commun. Surv. Tutor. 2022, 24, 2230–2254. [CrossRef]
- Goransson, Paul, Chuck Black, and Timothy Culver. Software defined networks: a comprehensive approach. Morgan Kaufmann, 2016.
- Sarwar, Asima, Abdullah M. Alnajim, Safdar Nawaz Khan Marwat, Salman Ahmed, Saleh Alyahya, and Waseem Ullah Khan. "Enhanced anomaly detection system for iot based on improved dynamic SBPSO.". Sensors 2022, 22, 4926.
- Dhruba Kumar Bhattacharyya and Jugal Kumar Kalita. 2016. DDoS Attacks: Evolution, Detection, Prevention, Reaction, and Tolerance. CRC Press.
- Harish Barapatre, Jai Deshmukh, Vikrant Kapse, and Pritam Patil. DDoS Spyware for Cloud Computing Environment.
- Wang, An, Wentao Chang, Songqing Chen, and Aziz Mohaisen. "Delving into internet DDoS attacks by botnets: characterization and analysis.". IEEE/Acm Trans. Netw. 2018, 26, 2843–2855. [CrossRef]
- Hussain, Mudassar, Nadir Shah, Rashid Amin, Sultan S. Alshamrani, Aziz Alotaibi, and Syed Mohsan Raza. "Software-defined networking: Categories, analysis, and future directions.". Sensors 2022, 22, 5551.
- Neelam Dayal and Shashank Srivastava. 2017. Analyzing Behavior of DDoS Attacks to Identify DDoS Detection Features in SDN. In 2017 9th International Conference on Communication Systems and Networks (COMSNETS), pp. 274-281. IEEE. [CrossRef]
- Aladaileh, Mohammad A. , Mohammed Anbar, Iznan H. Hasbullah, Yung-Wey Chong, and Yousef K. Sanjalawe. "Detection techniques of distributed denial of service attacks on software-defined networking controller–a review.". IEEE Access 2020, 8, 143985–143995. [CrossRef]
- Rawat, Danda B. , and Swetha R. Reddy. "Software defined networking architecture, security and energy efficiency: A survey.". IEEE Communications Surveys and Tutorials 2016, 19, 325–346.
- Open Network Foundation. (2015, May). OpenFlow Switch Specification (Version 1.5.1). [Online]. Available: https://www.opennetworking.org/wp-content/uploads/2014/10/openflow-switch-v1.5.1.pdf.
- Tr, O. (2015). Principles and Practices for Securing Software-Defined Networks. Open Networking Foundation. Palo Alto CA, USA.
- Bhattacharyya, D. K. , and Kalita, J. K. (2016). DDoS Attacks: Evolution, Detection, Prevention, Reaction, and Tolerance. CRC Press.
- Douligeris, C. , and Mitrokotsa, A. DDoS attacks and defense mechanisms: classification and state-of-the-art. Computer Networks 2004, 44, 643–666. [Google Scholar] [CrossRef]
- Holl, P. (2015). Exploring DDoS Defense Mechanisms. Network, 25.
- Mousavi, S. M. , and St-Hilaire, M. (2015). Early detection of DDoS attacks against SDN controllers. In 2015 International Conference on Computing, Networking and Communications, ICNC 2015 (pp. 77-81). IEEE. [CrossRef]
- Keromytis, A. D. Misra, V., and Rubenstein, D. (2002). Using overlays to improve network security. In Proceedings of SPIE ITCom Conference on Scalability and Traffic Control in IP Networks II (Vol. 2002).
- Wang, H. , Zhang, D., and Shin, K. G. Detecting SYN flooding attacks. In INFOCOM 2002. Twenty-First Annual Joint Conference of the IEEE Computer and Communications Societies. Proceedings. IEEE 2002, 3, 1530–1539. [Google Scholar]
- Lersak Limwiwatkul and Arnon Rungsawang, "Distributed denial of service detection using TCP/IP header and traffic measurement analysis," in Communications and Information Technology, 2004. ISCIT 2004. IEEE International Symposium on 2004, 1, 605–610. [CrossRef]
- Rodrigues, Bruno, Eder Scheid, Christian Killer, Muriel Franco, and Burkhard Stiller. "Blockchain signaling system (BloSS): cooperative signaling of distributed denial-of-service attacks.". Journal of Network and Systems Management 2020, 28, 953–989. [CrossRef]
- Haider, Shahzeb, Adnan Akhunzada, Iqra Mustafa, Tanil Bharat Patel, Amanda Fernandez, Kim-Kwang Raymond Choo, and Javed Iqbal. "A deep CNN ensemble framework for efficient DDoS attack detection in software defined networks.". Ieee Access 2020, 8, 53972–53983. [CrossRef]
- Doshi, Keval, Yasin Yilmaz, and Suleyman Uludag. "Timely detection and mitigation of stealthy DDoS attacks via IoT networks.". IEEE Transactions on Dependable and Secure Computing 2021, 18, 2164–2176.
- Aslam, Muhammad, Dengpan Ye, Aqil Tariq, Muhammad Asad, Muhammad Hanif, David Ndzi, Samia Allaoua Chelloug, Mohamed Abd Elaziz, Mohammed AA Al-Qaness, and Syeda Fizzah Jilani. Adaptive machine learning based distributed denial-of-services attacks detection and mitigation system for SDN-enabled IoT.". Sensors 2022, 22, 2697.
- Alsaeedi, Mohammed, Mohd Murtadha Mohamad, and Anas A. Al-Roubaiey. "Toward adaptive and scalable OpenFlow-SDN flow control: A survey.". IEEE Access 2019, 7, 107346–107379. [CrossRef]
- Gupta, Neelam, Mashael S. Maashi, Sarvesh Tanwar, Sumit Badotra, Mohammed Aljebreen, and Salil Bharany. "A comparative study of software defined networking controllers using mininet.". Electronics 2022, 11, 2715. [CrossRef]
- Nugraha, M. , Paramita, I., Musa, A., Choi, D., and Cho, B. Utilizing OpenFlow and sFlow to Detect and Mitigate SYN Flooding Attack. Journal of Korea Multimedia Society 2014, 17, 988–994. [Google Scholar] [CrossRef]
- Lin, H. , and Ping Wang. "Implementation of an SDN-based security defense mechanism against DDoS attacks." In Proceedings of the 2016 Joint International Conference on Economics and Management Engineering (ICEME 2016) and International Conference on Economics and Business Management (EBM 2016). 2016.
- Wang, Yang, Tao Hu, Guangming Tang, Jichao Xie, and Jie Lu. "SGS: Safe-guard scheme for protecting control plane against DDoS attacks in software-defined networking.". IEEE Access 2019, 7, 34699–34710. [CrossRef]
- Wani, Azka, and Rubeena Khaliq. "SDN-based intrusion detection system for IoT using deep learning classifier (IDSIoT-SDL).". CAAI Transactions on Intelligence Technology 2021, 6, 281–290. [CrossRef]
- Varghese, Josy Elsa, and Balachandra Muniyal. "An Efficient IDS framework for DDoS attacks in SDN environment.". IEEE Access 2021, 9, 69680–69699. [CrossRef]
- Mousavi, Seyed Mohammad, and Marc St-Hilaire. "Early detection of DDoS attacks against SDN controllers." In 2015 international conference on computing, networking and communications (ICNC), pp. 77-81. IEEE, 2015.
- Mousavi, Seyed Mohammad, and Marc St-Hilaire. "Early detection of DDoS attacks against SDN controllers." In 2015 international conference on computing, networking and communications (ICNC), pp. 77-81. IEEE, 2015.
- Lim, Sharon, J. Ha, H. Kim, Y. Kim, and S. Yang. "A SDN-oriented DDoS blocking scheme for botnet-based attacks." In 2014 Sixth International Conference on Ubiquitous and Future Networks (ICUFN), pp. 63-68. IEEE, 2014.
- Phan, Trung V., Nguyen Khac Bao, and Minho Park. "A novel hybrid flow-based handler with DDoS attacks in software-defined networking." In 2016 Intl IEEE Conferences on Ubiquitous Intelligence and Computing, Advanced and Trusted Computing, Scalable Computing and Communications, Cloud and Big Data Computing, Internet of People, and Smart World Congress (UIC/ATC/ScalCom/CBDCom/IoP/SmartWorld), pp. 350-357. IEEE, 2016.
- Eliyan, Lubna Fayez, and Roberto Di Pietro. "DoS and DDoS attacks in Software Defined Networks: A survey of existing solutions and research challenges.". Future Generation Computer Systems 2021, 122, 149–171. [CrossRef]
- Macedo, R. , de Castro, R., Santos, A., Ghamri-Doudane, Y., and Nogueira, M. (2016). Self-organized SDN controller cluster conformations against DDoS attacks effects. In 2016 IEEE Global Communications Conference, GLOBECOM 2016 - Proceedings (pp. 1-6). IEEE. [CrossRef]
- Yan, Q. Gong, and F. Richard Yu. "Effective software-defined networking controller scheduling method to mitigate DDoS attacks.". Electronics Letters 2017, 53, 469–471. [Google Scholar] [CrossRef]
- Zhang, P. , Wang, H., Hu, C., and Lin, C. On Denial of Service Attacks in Software Defined Networks. IEEE Network 2016, 28–33. [Google Scholar] [CrossRef]
- Xu, Yang, and Yong Liu. "DDoS attack detection under SDN context." In IEEE INFOCOM 2016-the 35th annual IEEE international conference on computer communications, pp. 1-9. IEEE, 2016.
- Aladaileh, Mohammad A. , Mohammed Anbar, Iznan H. Hasbullah, Yung-Wey Chong, and Yousef K. Sanjalawe. "Detection techniques of distributed denial of service attacks on software-defined networking controller–a review.". IEEE Access 2020, 8, 143985–143995. [CrossRef]
- Hussain, M. , Shah, N., Amin, R., Alshamrani, S.S., Alotaibi, A. and Raza, S.M. Software-defined networking: Categories, analysis, and future directions. Sensors 2022, 22, 5551. [Google Scholar] [CrossRef]
- (2018, March). [Online]. Available: https://sflow-rt.com (Accessed: Mar. 2018).
- Controlling Large Flows with OpenrFlow. [Online]. Available: https://blog.sflow.com/2013/05/controlling-large-flows-with-openflow.html: https://blog.sflow.com/2013/05/controlling-large-flows-with-openflow.html (Accessed: May. 2018).
| 1 | Flow can be defined as a set of consecutive packets that have equivalent properties traveling in the same network. |

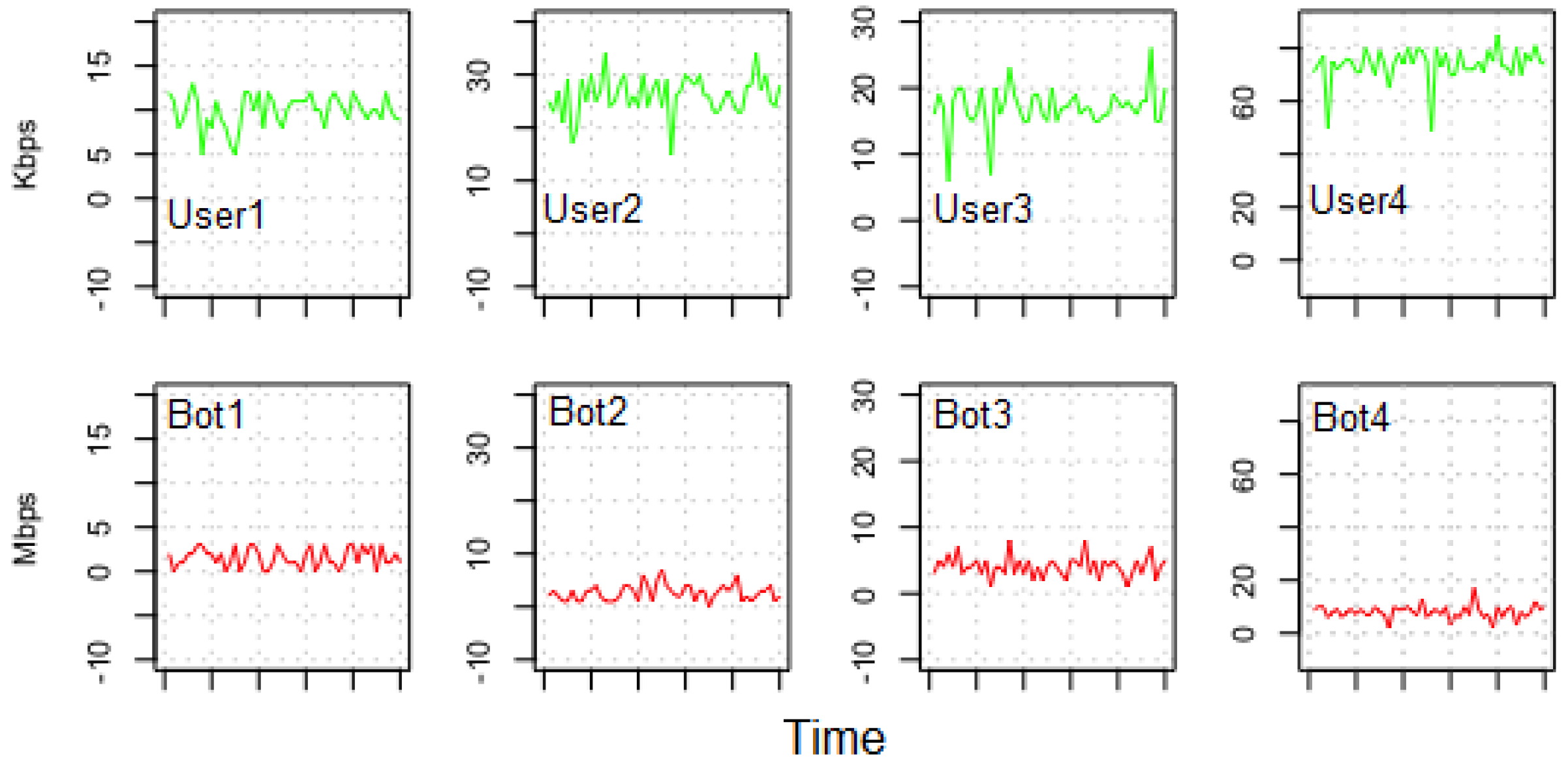
| Host number | Host type | Traffic rate |
|---|---|---|
| 1 | legitimate user | 10Kbps |
| 2 | legitimate user | 30Kbps |
| 3 | legitimate user | 20Kbps |
| 4 | legitimate user | 80Kbps |
| 5 | bot | 3Mbps |
| 6 | bot | 4Mbps |
| 7 | bot | 5Mbps |
| 8 | bot | 10Mbps |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




