Submitted:
22 August 2024
Posted:
23 August 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Problem Statement
2.1. Problem Introduction
2.2. Research Questions
- RQ1: How are SMEs susceptible to common cybersecurity threats such as malware, web-based attacks, and phishing?
- RQ2: How do existing cybersecurity frameworks such as NIST CSF, and ISO 27001/2 address the specific challenges and limitations encountered by SMES?
- RQ3: What techniques or approaches can be implemented to tailor cybersecurity risk assessment methodologies, specifically for SMEs, considering their resource constraints and unique operating environments?
- RQ4: How can the effectiveness of the developed framework and tool be evaluated and validated in real-world SME environments?
3. Background
3.1. Common Threats and Vulnerabilities Faced by SMEs
3.1.1. Employee Attitudes
| Attack | Common Types | SME Vulnerabilities |
|---|---|---|
| Malware | Ransomware. Adware.Spyware. | Lack of awareness.Lack of security professionals [7]. Cyberslacking [15]. |
| Phishing | Deceptive Phishing [16]. Malware-based Phishing [16]. | Lack of training. No warning systems for flagging [14]. No reporting mechanism or verification. |
| Web-based | Cross-site scripting (XSS). SQL Injection. Distributed Denial of Service (DDoS). | No input sanitization. Lack of firewalls. Poor coding practices. |
3.2. Review of Popular Frameworks
3.3. Key Findings
4. Related Work
4.1. Promising Solutions for SMEs
4.2. Techniques for the Framework
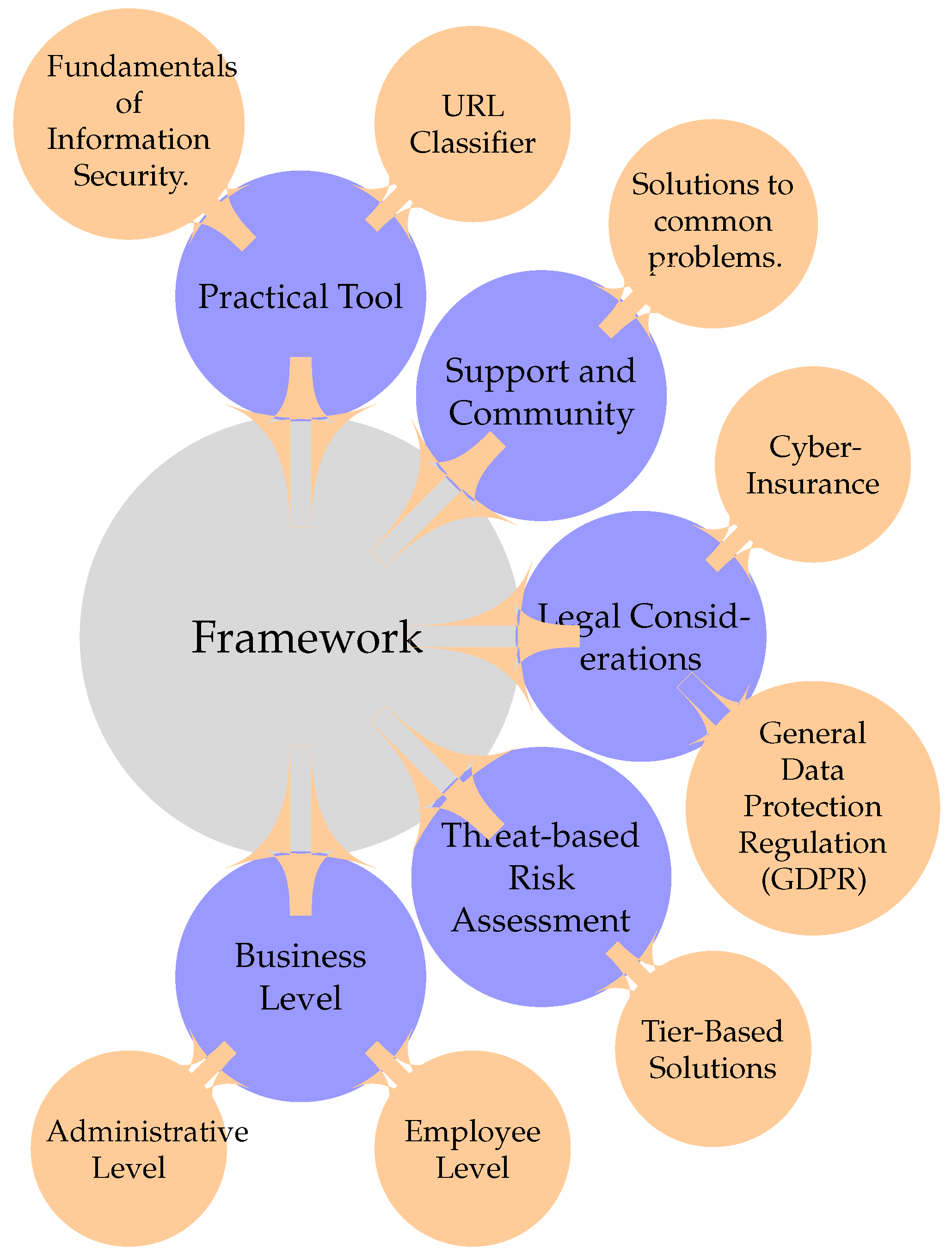
5. Framework
5.1. Overview
5.2. Fundamentals of Information Security
5.3. Cybersecurity Levels
5.3.1. Business Level
5.3.2. Administrative Level
5.3.3. Employee Level
5.4. Threat Classification
6. Tool
6.1. Overview
6.2. Methodology to Develop Model
6.2.1. Identifying the Goal:
6.2.2. Choosing a Model:
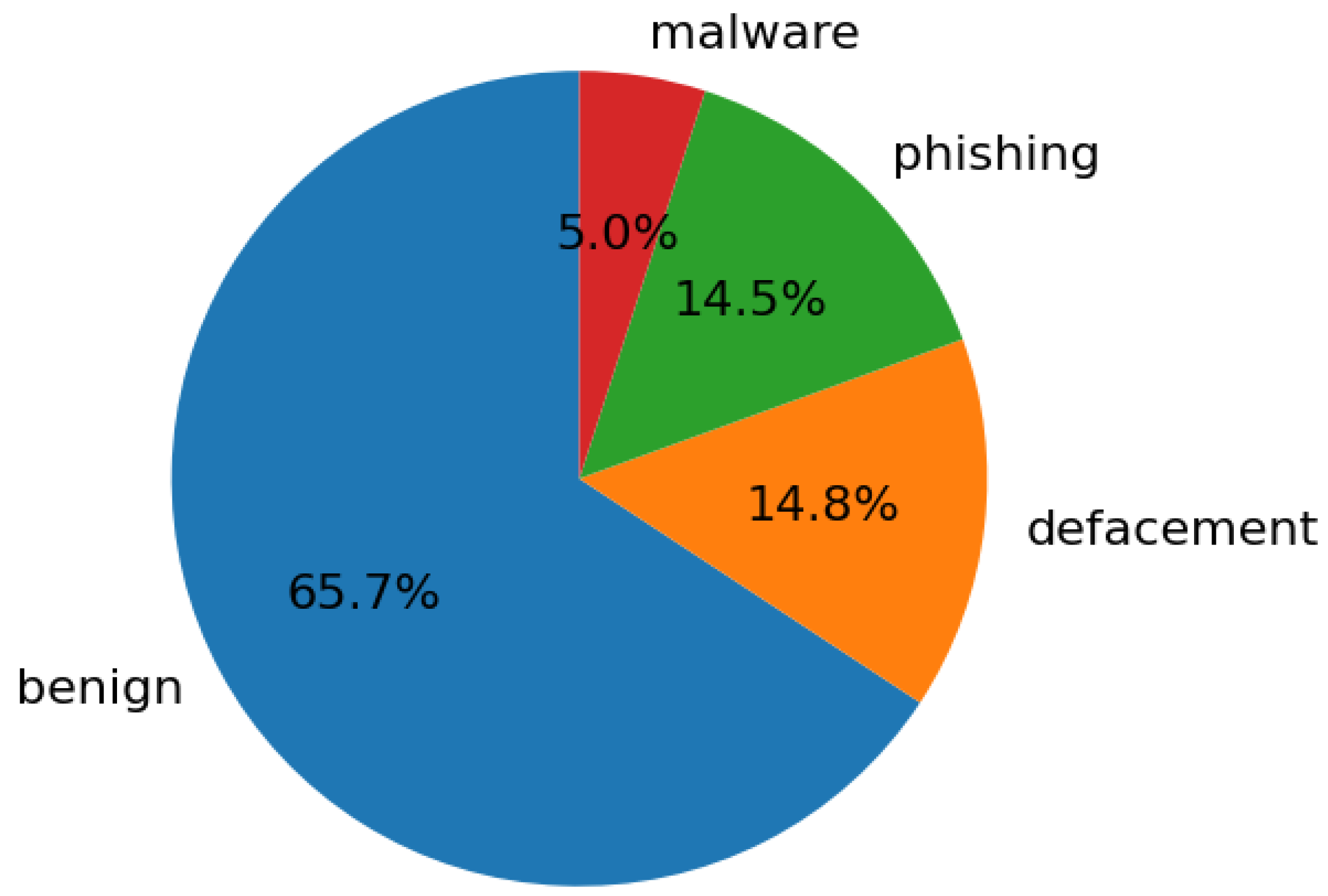
6.3. Data Selection, Sampling, and Distribution
6.4. Extracted Features
- URL Length: Extremely long and short URLs can be a sign of phishing or concealing information.
- Number of digits: A URL with a large number of digits can be a sign of redirection or malicious intent.
- Number of special characters: A large number of special characters can be an indication of malicious intent.
- Has IP address: The presence of an IP address usually means redirection to an unsecured location.
- Has HTTPS: If a website contains HTTP, it has a secure and encrypted connection.
- Number of periods: URLs with many dots mean there are multiple subdomains, a common trick to look legitimate.
- Domain Length: Very long or short domain lengths can potentially be an indicator of a malicious website.
- Port Number: It is unusual for a URL to contain a port number.
- Number of Subdomains: A large number of subdomains can be an indicator of a malicious website.
- Has Redirection: Redirection to another website can be an attempt to conceal malicious intent.
- Path Length: Varying path lengths can be an indicator of phishing or malware.
6.5. Limitations with Dataset
7. Results
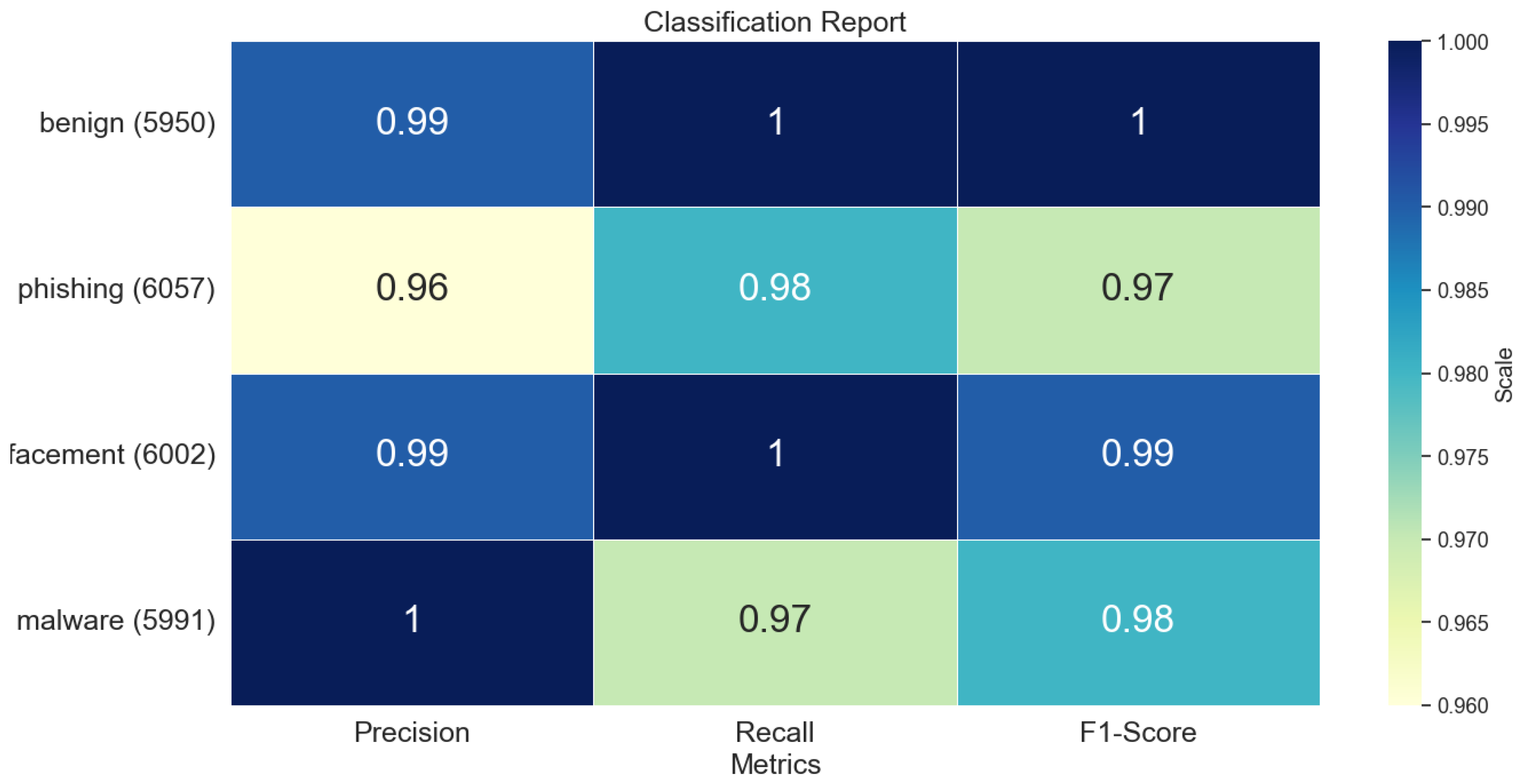
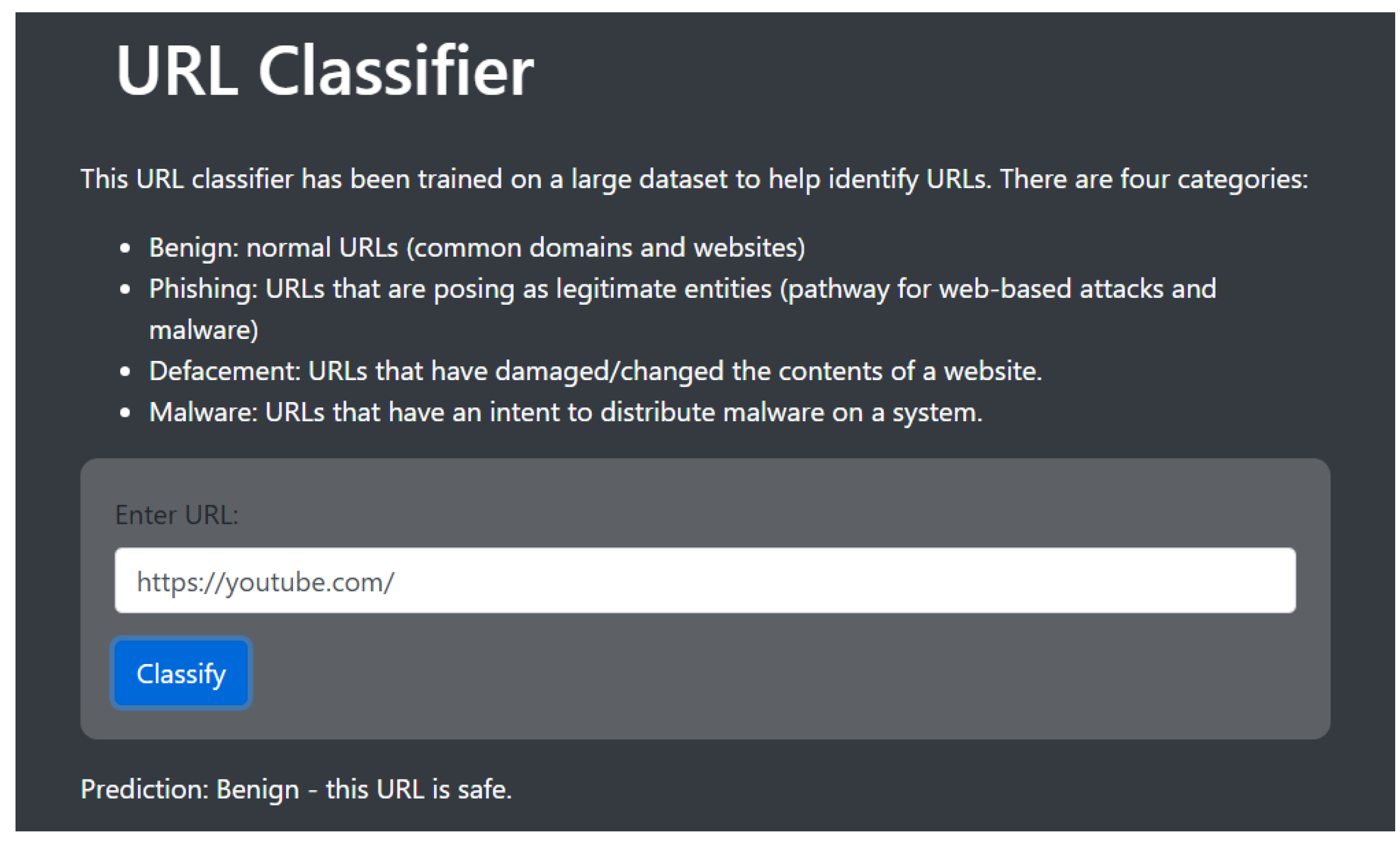
7.1. URL Classifier
7.2. SWOT Analysis
7.3. Expert Feedback
7.3.1. Advantages
7.3.2. Disadvantages
7.3.3. Recommendations
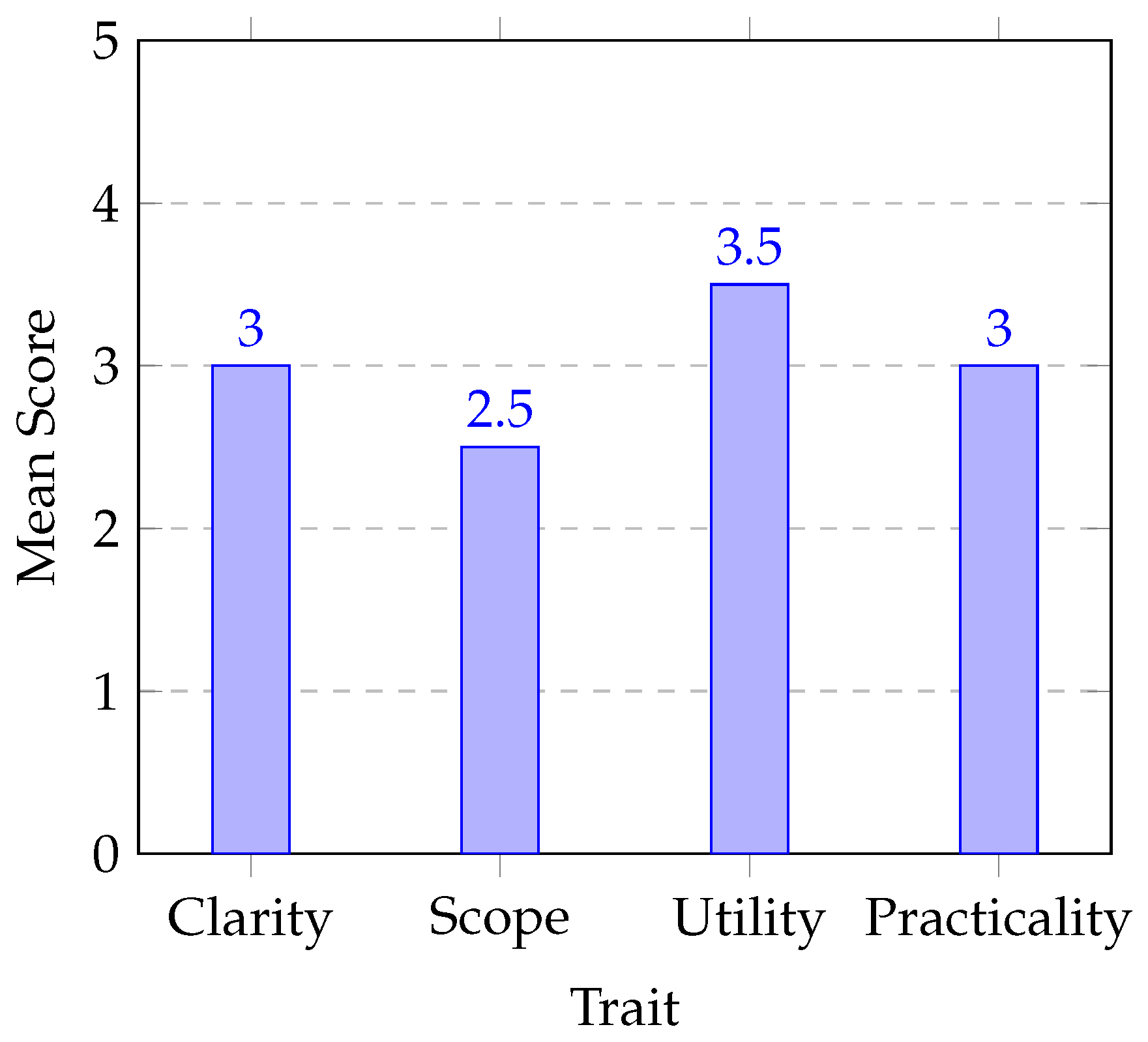
7.4. Usability Testing
7.5. Proposed Pilot Assessment
7.5.1. Setup:
7.5.2. Implementation and Monitoring:
7.5.3. Evaluation:
8. Discussion
8.1. Framework
8.2. Tool
9. Limitations and Future Work
9.1. Limitations
9.2. Future Work
10. Conclusion
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| SMEs | Small and Medium Enterprises |
| NIST | National Institute of Science and Technology |
| ISO | International Organization for Standardization |
| ENISA | European Union Agency for Cybersecurity |
| ISMS | Information Security Management System |
| CET | Cybersecurity Evaluation Tool |
| SDT | Self-Determination Theory |
| LCCI | Least Cybersecurity Controls Implementation |
| CIA | Confidentiality, Authentication, and Integrity |
| MCAs | Mission Critical Assets |
| GDPR | General Data Protection Regulation |
| VPN | Virtual Private Networks |
| MFA | Multi-Factor Authentication |
| ML | Machine Learning |
References
- Chidukwani, A.; Zander, S.; Koutsakis, P. A Survey on the Cyber Security of Small-to-Medium Businesses: Challenges, Research Focus and Recommendations. IEEE Access 2022, 10, 85701–85719. [Google Scholar] [CrossRef]
- Jahankhani, H.; Meda, L.N.K.; Samadi, M. Cybersecurity Challenges in Small and Medium Enterprise (SMEs). In Blockchain and Other Emerging Technologies for Digital Business Strategies; Jahankhani, H., V. Kilpin, D., Kendzierskyj, S., Eds.; Springer International Publishing: Cham, 2022; pp. 1–19. [Google Scholar] [CrossRef]
- AL-Dosari, K.; Fetais, N. Risk-Management Framework and Information-Security Systems for Small and Medium Enterprises (SMEs): A Meta-Analysis Approach. Electronics 2023, 12. [Google Scholar] [CrossRef]
- Carías, J.F.; Borges, M.R.S.; Labaka, L.; Arrizabalaga, S.; Hernantes, J. Systematic Approach to Cyber Resilience Operationalization in SMEs. IEEE Access 2020, 8, 174200–174221. [Google Scholar] [CrossRef]
- Saha, B.; Anwar, Z. A Review of Cybersecurity Challenges in Small Business: The Imperative for a Future Governance Framework. Journal of Information Security 2024, 15, 24–39. [Google Scholar] [CrossRef]
- Islam, M.A.; Khan, M.A.; Obaidullah, A.Z.M.; Alam, M. Effect of Entrepreneur and Firm Characteristics on the Business Success of Small and Medium Enterprises (SMEs) in Bangladesh. International Journal of Business and Management 2011, 6, 289–299. [Google Scholar] [CrossRef]
- Heikkilä, M.; Rättyä, A.; Pieskä, S.; Jämsä, J. Security challenges in small- and medium-sized manufacturing enterprises. 2016 International Symposium on Small-scale Intelligent Manufacturing Systems (SIMS), 2016, pp. 25–30. [CrossRef]
- van Haastrecht, M.; Sarhan, I.; Shojaifar, A.; Baumgartner, L.; Mallouli, W.; Spruit, M. A Threat-Based Cybersecurity Risk Assessment Approach Addressing SME Needs. Proceedings of the 16th International Conference on Availability, Reliability and Security; Association for Computing Machinery: New York, NY, USA, 2021. [Google Scholar] [CrossRef]
- Chindipha, S.; Irwin, B. Evaluation of the Effectiveness of Small Aperture Network Telescopes as IBR Data Sources. PhD thesis, 2023. [CrossRef]
- Lourenco, M.; Marinos, L. ENISA Threat Landscape 2019/2020 - The year in review 2020. pp. 1–20. [CrossRef]
- on National Security, C. Committee on National Security Systems (CNSS) Glossary, 2022.
- Singh, A.; Sharma, A.; Sharma, N.; Kaushik, I.; Bhushan, B. Taxonomy of Attacks on Web Based Applications. 2019 2nd International Conference on Intelligent Computing, Instrumentation and Control Technologies (ICICICT), 2019, Vol. 1, pp. 1231–1235. [CrossRef]
- Nieles, M.; Dempsey, K.; Yan Pillitteri, V. An Introduction to Information Security, 2017. [CrossRef]
- Pugnetti, C.; Casián, C. Cyber risks and Swiss SMEs: an investigation of employee attitudes and behavioral vulnerabilities. ZHAW Digital Collection 2021. [Google Scholar]
- Luna, A.; Levy, Y.; Simco, G.; Li, W. Proposed Empirical Assessment of Remote Workers’ Cyberslacking and Computer Security Posture to Assess Organizational Cybersecurity Risks. 2022 IEEE High Performance Extreme Computing Conference (HPEC), 2022, pp. 1–2. [CrossRef]
- Chawla, M.; Chouhan, S.S. A survey of phishing attack techniques. International Journal of Computer Applications 2014, 93. [Google Scholar] [CrossRef]
- Marican, M.N.Y.; Razak, S.A.; Selamat, A.; Othman, S.H. Cyber Security Maturity Assessment Framework for Technology Startups: A Systematic Literature Review. IEEE Access 2023, 11, 5442–5452. [Google Scholar] [CrossRef]
- Barrett, M. Framework for Improving Critical Infrastructure Cybersecurity Version 1.1, 2018. [CrossRef]
- ISO. ISO/IEC 27001:2022, 2022.
- Benz, M.; Chatterjee, D. Calculated risk? A cybersecurity evaluation tool for SMEs. Business Horizons 2020, 63, 531–540. [Google Scholar] [CrossRef]
- Ganji, D.; Kalloniatis, C.; Mouratidis, H.; Gheytassi, S.M. Approaches to Develop and Implement ISO/IEC 27001 Standard - Information Security Management Systems: A Systematic Literature Review. International Journal on Advances in Software 2019, 12, 228–238. [Google Scholar]
- Pawar, S.; Palivela, D.H. LCCI: A framework for least cybersecurity controls to be implemented for small and medium enterprises (SMEs). International Journal of Information Management Data Insights 2022, 2, 100080. [Google Scholar] [CrossRef]
- Tsokkis, P.; Stavrou, E. A password generator tool to increase users’ awareness on bad password construction strategies. 2018 International Symposium on Networks, Computers and Communications (ISNCC), 2018, pp. 1–5. [CrossRef]
- Kubariev, O.; Piatykop, O.; Pronina, O.; Levytska, T. The Research on Methods for Generating Random Passwords. 2023 IEEE International Conference on Information and Telecommunication Technologies and Radio Electronics (UkrMiCo), 2023, pp. 63–66. [CrossRef]
- Team, E. Why Are Strong Passwords Still Crucial Even with MFA Enabled? - Enpass — enpass.io. Available online: https://www.enpass.io/blog/security/strong-passwords-still-crucial-with-mfa-enabled/.
- Möller, D.P.F.; Vakilzadian, H. Cybersecurity Awareness Training: A Use Case Model. 2023 IEEE International Conference on Electro Information Technology (eIT), 2023, pp. 242–247. [CrossRef]
- Sandhu, R.S. Role-based Access Control11Portions of this chapter have been published earlier in Sandhu et al. (1996), Sandhu (1996), Sandhu and Bhamidipati (1997), Sandhu et al. (1997) and Sandhu and Feinstein (1994).; Elsevier, 1998; Vol. 46, Advances in Computers, pp. 237–286. [CrossRef]
- Moses, S.; Rowe, D. Physical Security and Cybersecurity: Reducing Risk by Enhancing Physical Security Posture through Multi-Factor Authentication and other Techniques. International Journal for Information Security Research 2016, 6, 667–676. [Google Scholar] [CrossRef]
- Donges, N. Random Forest: A Complete Guide for Machine Learning. 2024. Available online: https://builtin.com/data-science/random-forest-algorithm.
- Siddhartha, M. Malicious URLs dataset — kaggle.com. 2021. Available online: https://www.kaggle.com/datasets/sid321axn/malicious-urls-dataset.
- Kanstrén, T. A Look at Precision, Recall, and F1-Score — towardsdatascience.com. 2020. Available online: https://towardsdatascience.com/a-look-at-precision-recall-and-f1-score-36b5fd0dd3ec.
- Kenton, W. How To Perform a SWOT Analysis — investopedia.com. 2024. Available online: https://www.investopedia.com/terms/s/swot.asp.
| Framework | Advantages | Disadvantages |
|---|---|---|
| NIST CSF | Flexible. Common terminology.Reduces confusion [1]. | 55 page manual.Relatively new terminology for SMEs. Forces businesses to rate themselves (no clear standards) [20]. |
| ISO 27001/2 | Robust. Creation of an ISMS. Effective security measures for structure [1]. | Extremely technical. Large knowledge gap between technicality and implementation. Complicated process for adoption [21]. |
| Strengths | Weaknesses |
|---|---|
|
|
| Opportunities | Threats |
|
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




