Submitted:
20 August 2024
Posted:
21 August 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Increased cost: there is a marked increase in cost and overheads with each new addition of hardware and its associated software from development to maintenance [7].
- Increased complexity: the complexity of the modern automotive E/E architecture has arisen from the ever-increasing interactions between various components parts. The introduction of multiple in-vehicle networking solutions such as CANBus, LIN, Flexray has aided in overall system complexity. As more automotive functions require data across multiple automotive domains of responsibility [2,7].
- Reduced scalability: embedded systems are not inherently scalable by design. They are bespoke pieces of hardware which have been highly optimized on an architectural level to ensure that only the necessary components are included [16]
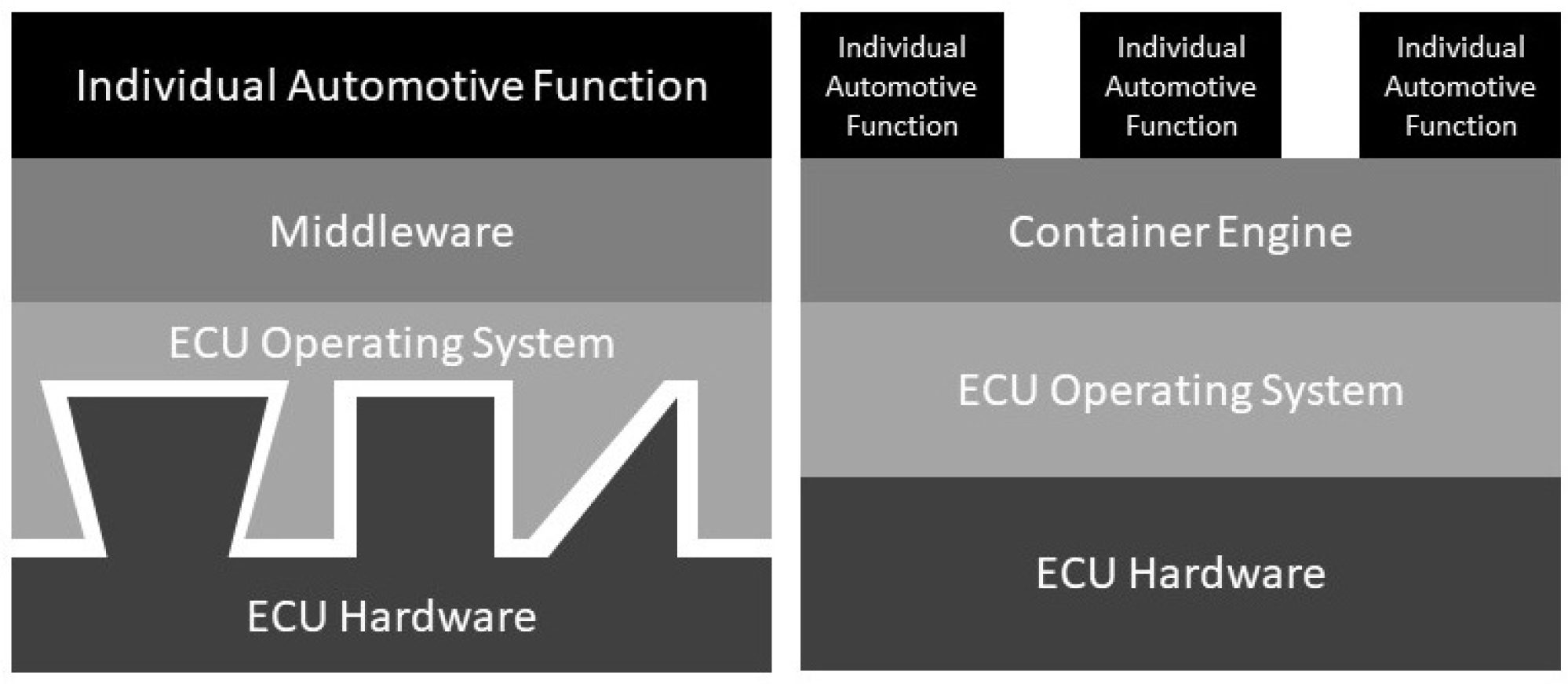
2. Virtualisation in the Automotive Domain
3. Related Work
4. Design of a Container Based ECU
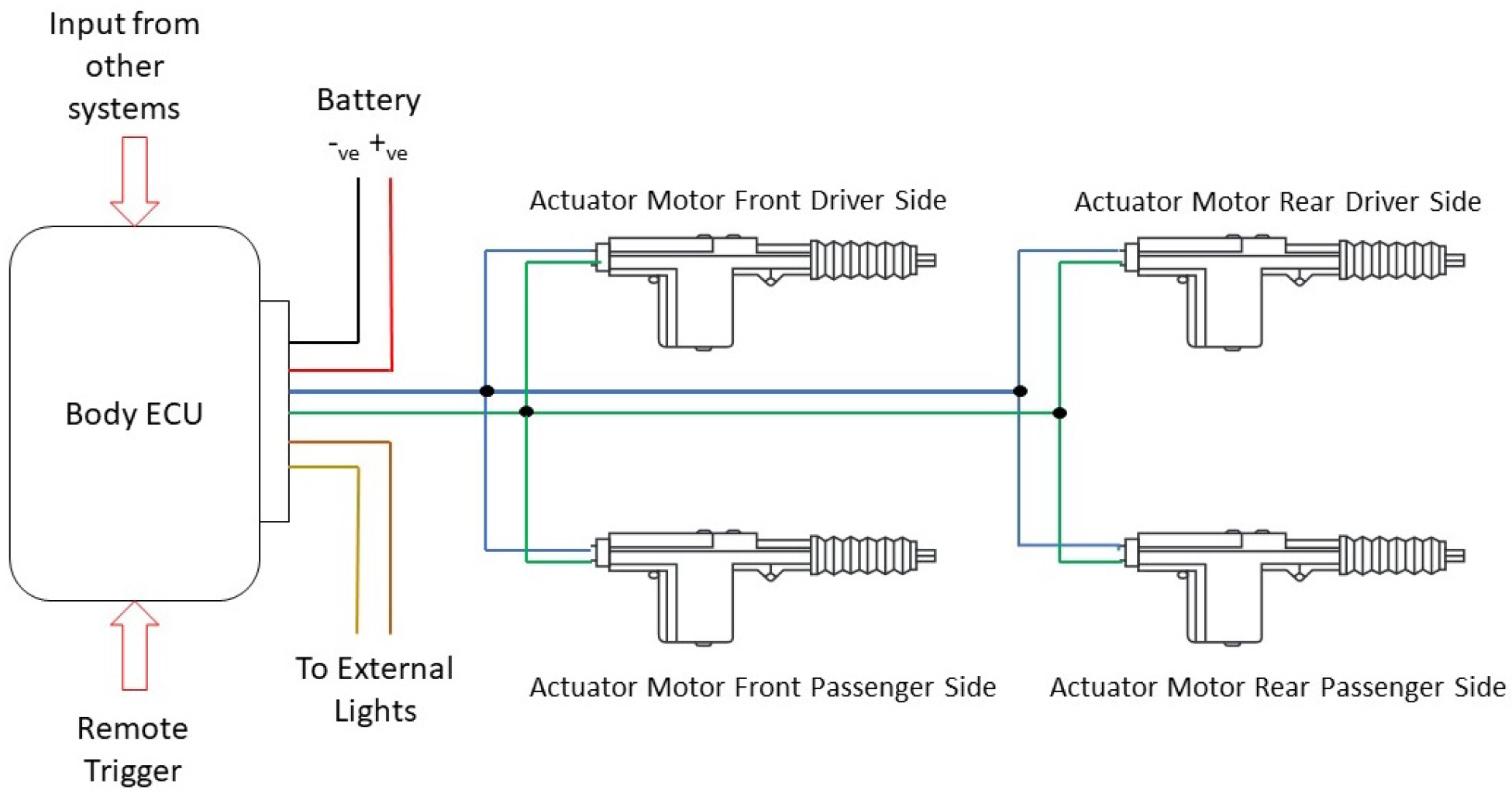
4.1. Automotive Central Locking Function
- Infrared Remote (Simulated remote key fob)
- Transmission - Selection of a specific gear
- Vehicle Speed - When vehicle achieves a specific speed
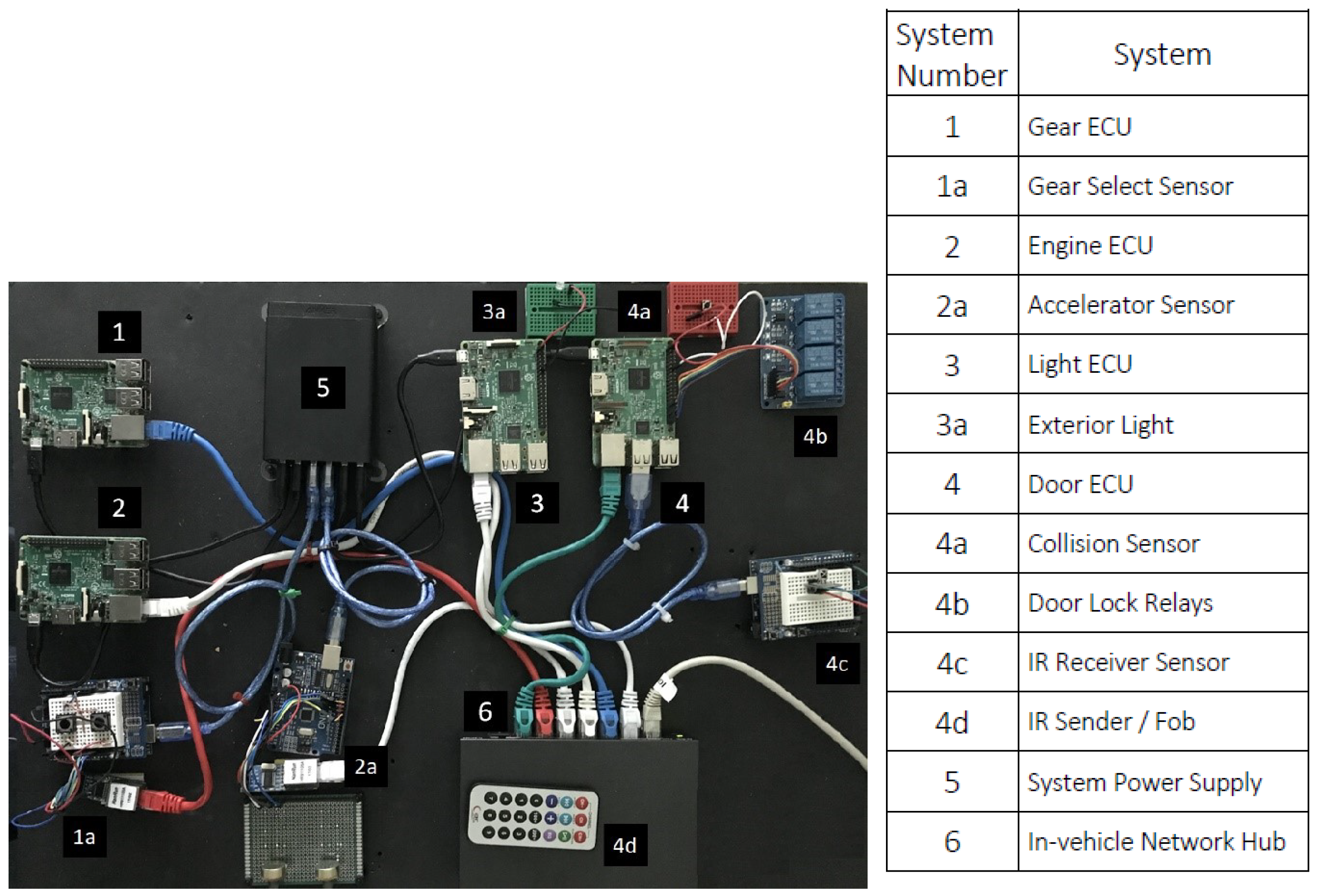
4.2. Test Bed- ECU and Sensor Hardware
- Central door locking mechanism - provided by a four-channel relay module. Each relay represents a particular vehicle door. The vehicle doors are locked when the relay corresponding to it is in the closed position.
- Remote door lock trigger - manual door states are affected via a remote IR transmitter device. The IR transmitter sends one of three selectable door commands to an IR receiver. This particular functionality is suspended if the current transmission state is in any gear other than neutral.
- External lighting - an LED simulates the vehicle headlights, which illuminates according to the received door state.
- Gear position – the current selected gear is represented by a series of depressions on one of two push-button sensors that either increase or decrease the gear.
- Vehicle acceleration – the simulated engine r/min is selected by a potentiometer position setting with a data range of 0–1024.
- The collision sensor – a push-button sensor simulates the deployment of an airbag or activation of a collision sensor and when pressed, activates the overriding safety mechanism.
5. Implementation
- Transmission ECU - part of the transmission domain
- Acceleration ECU - part of the engine domain
- Door Control ECU - part of the body domain
- Light Control ECU - part of the body domain
6. Evaluation
6.1. System Performance Metrics
- Utilisation – the percentage of time a resource is busy compared to when that resource is available over a given time interval.
- Saturation – the amount of work that is queued or waiting for an available resource, often expressed as a queue length.
- Duration – the amount of time spent serving a request.
6.2. ECU Test Mode of Operation
- Base system test mode - This initial test mode establishes a baseline benchmark of the system resources used when the modelled ECU is in an idle state. Any system overhead introduced by the ECU software across subsequent test modes can be compared to this baseline set of results to determine the overheads when the ECU functional software is executed natively and within a container.
- Native system test mode - This test mode generally mirrors current automotive E/E architectures and ECU function operations. During this test mode, the results will show specific increases in system resource use when each ECU functional software is in execution compared with the base system test.
- Container system test mode - This test mode measures any other system resources or resource overhead required to run the ECU software within a container when compared with native operation.
- time_60 = 60-second sample run - some tests investigate specific resource use required during ECU software initialisation. Thus, only the first few initial seconds were required for analysis. A 60-second test run was a sufficient time to allow for an initial warm-up period before script execution.
- time_600 = 600-second sample run – these tests investigated the functional software’s entire life cycle from initialisation to termination. These time frame tests included a system idle warm-up period of 30 seconds, which eliminated spikes in specific resources associated with the initial stages of software execution. Script execution time for these timed tests was 500 seconds, at which point the script terminated, with the final 30 seconds of the test being the cool-down period. CPU and memory resource levels after script execution were a crucial area of investigation. They revealed whether the system returned to a similar state before the script was executed. It was important to understand the level of resources which were not released back to the system after execution, particularly ECU systems that only activate periodically to accomplish a specific task or function.
- time_1200 = 1200-second sample run – this test period investigated resource use trends over an extended time to understand if there were specific increases during long execution cycles. However, to display this information, the published results must be a cross-section of the entire 1200-second test, especially where test results showed little to no observable activity.
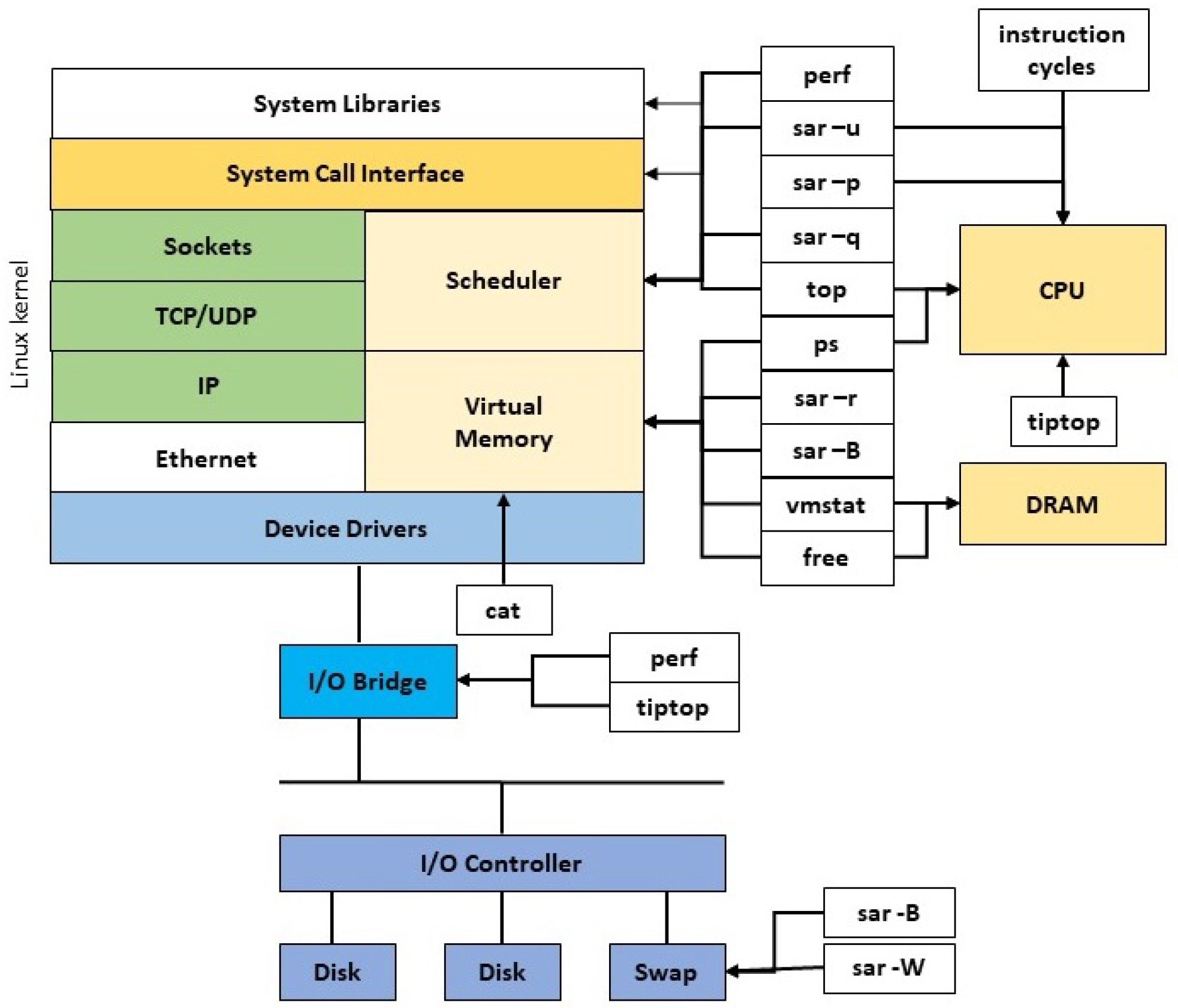
7. Software Tools
7.1. Vmstat
- The number of processes/tasks waiting runtime (R state)
- The number of processes/tasks waiting in an uninterruptible sleep (D state)
- The amount of free or idle system memory
- Memory swap information
- CPU statistics including %us, %sy and %id.
7.2. Free (Free and Used Memory)
7.3. Schedstat (Scheduler Statistics)
- The sum of time spent running processes in the processor.
- The sum of time spent waiting to run a task (often measured in jiffies).
- The number of time slices or voluntary and involuntary switches running on the CPU.
7.4. Sar (System Activity Reporter)
- sar -B - reported system paging statistics.
- sar -q – monitors CPU load, run queue and process list lengths.
- sar -R - monitors general memory statistics.
- sar -r - reports on the percentage of system memory used.
- sar -W - monitors swap in and swap out rates.
7.5. Perf (Performance Analysis)
7.6. Pidstat (Process Statistics)
7.7. Top / htop / nmon
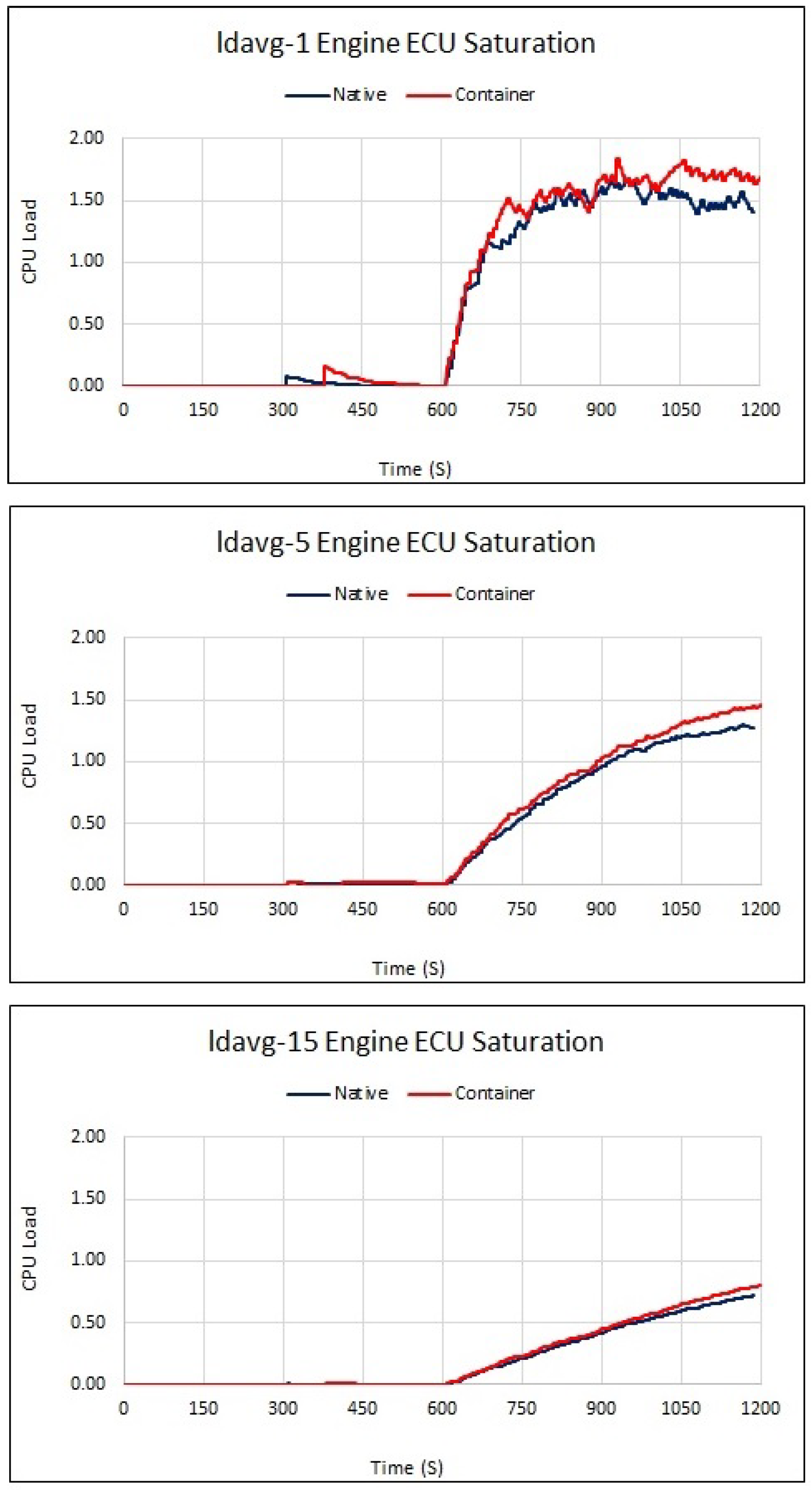
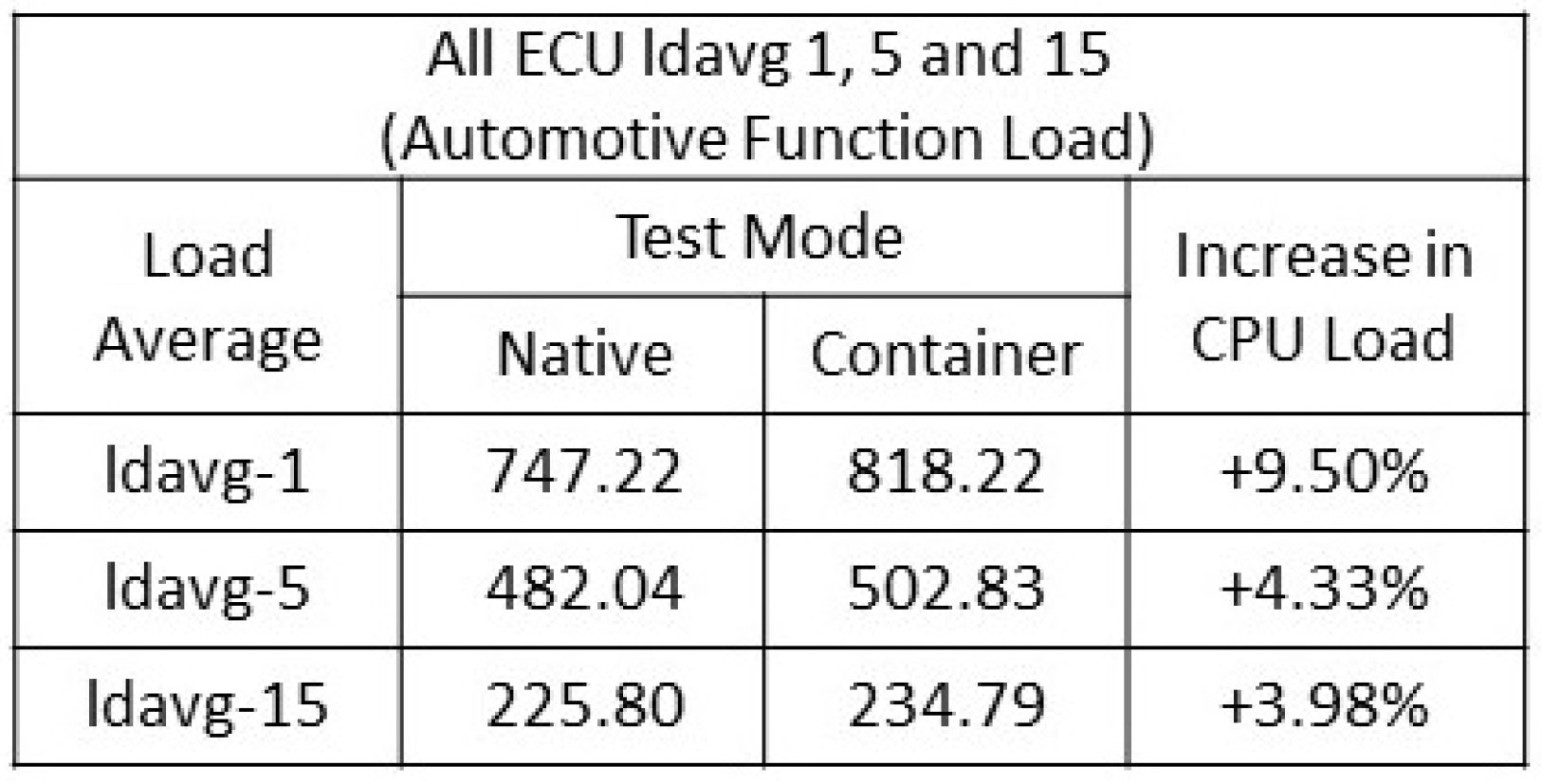
8. System Saturation
- A longer wait for a process in an idle or wait state.
- An increase in overall request-response times.
- A subsequent increase in CPU utilisation.
8.1. System Load
- If the average is 0.00, the system is regarded as being in an idling state
- If the 5 or 15-minute average is higher than the 1-minute average, overall system load is increasing
- If the 5 or 15-minute average is lower than the 1-minute average, overall system load is decreasing
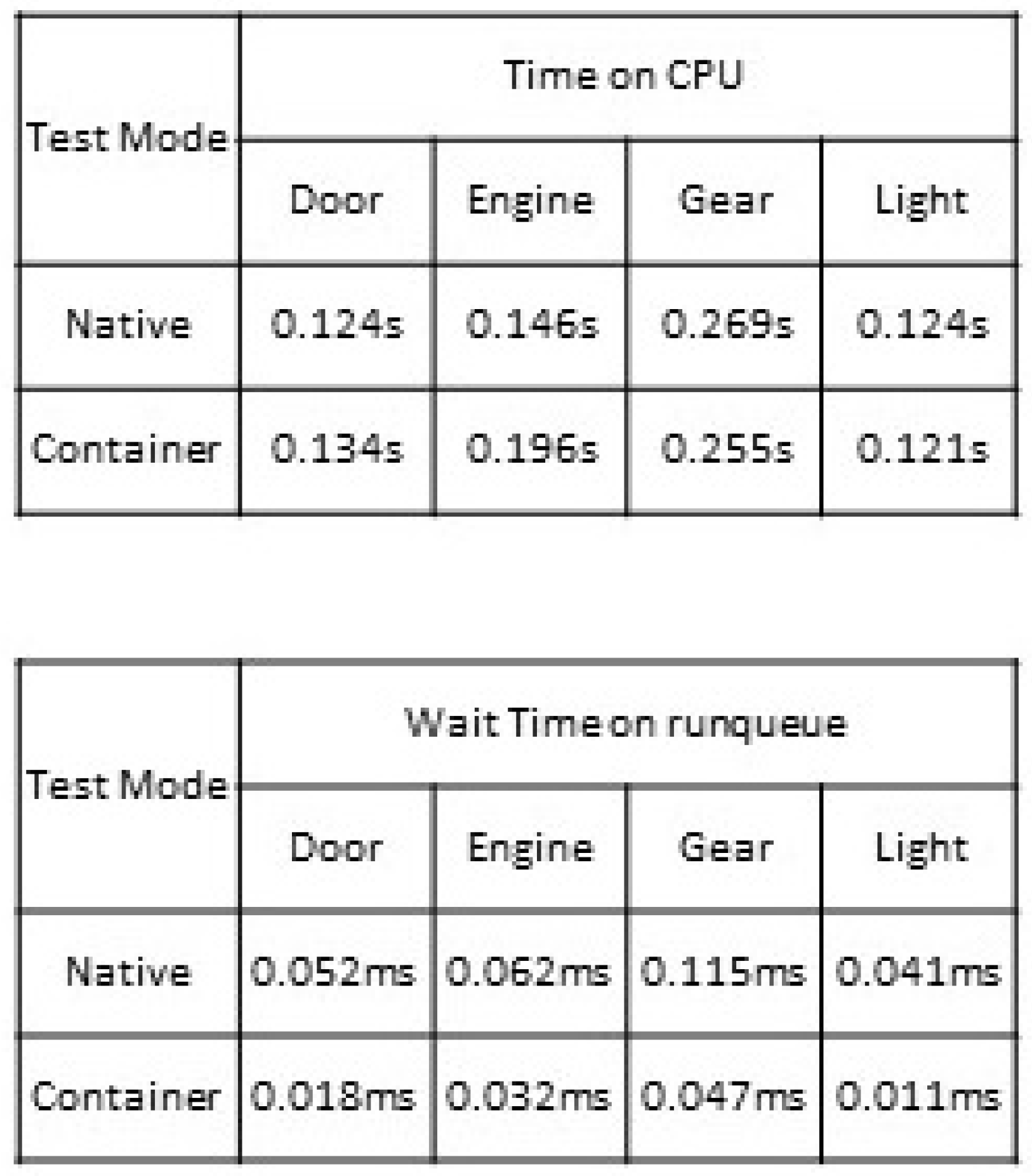
8.2. Scheduler Statistics
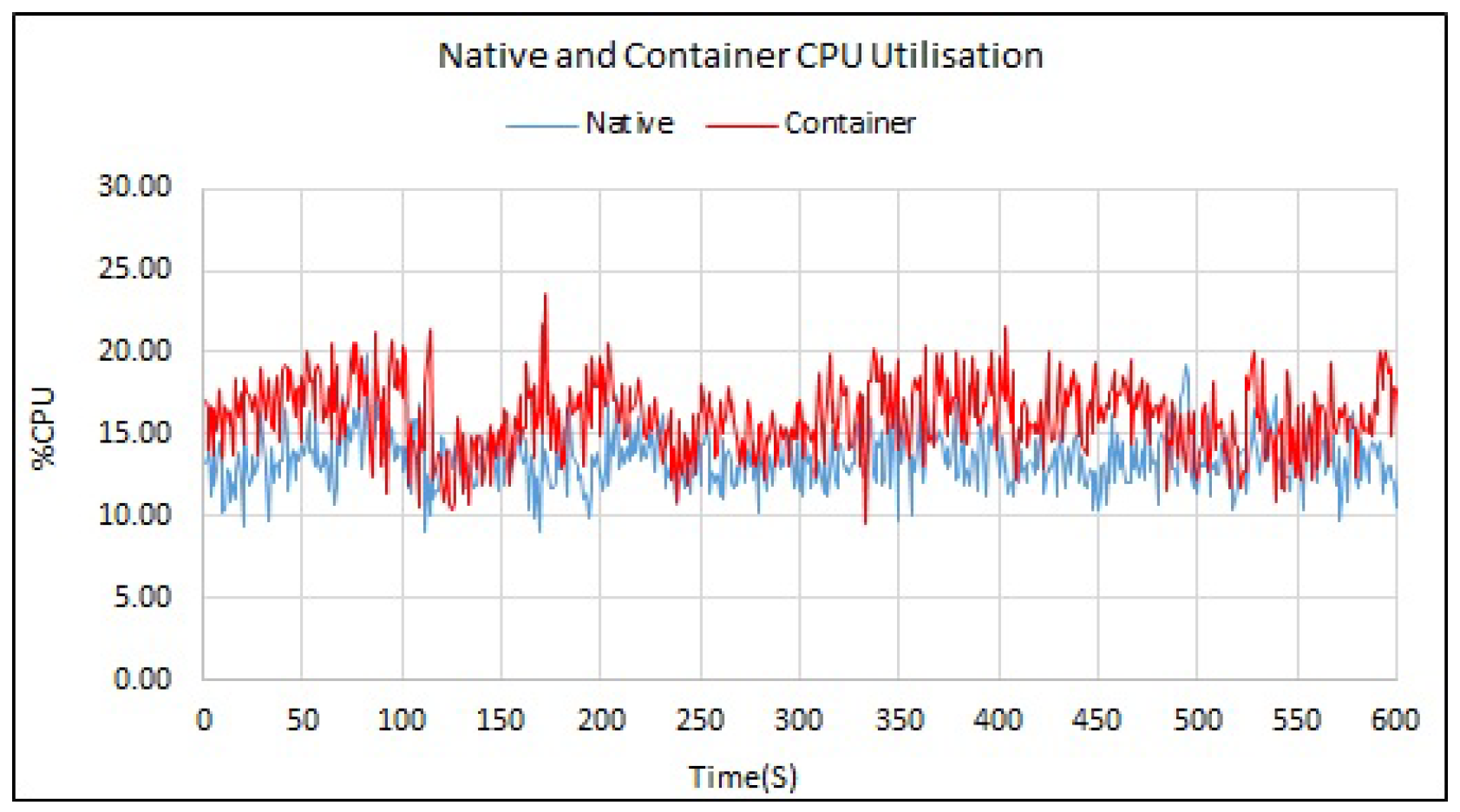
9. System Resource Utilisation
- %user - percentage of CPU utilisation while executing processes at the application (user) level and pertains to kernel activities such as servicing interrupts and resource management.
- %system - percentage of CPU utilisation while running processes at the system (kernel) level.
- %idle - percentage of time the CPU was inactive with no outstanding disk I/O requests.
- %nice - percentage of CPU utilisation executing higher-level processes at the user level. It must also be considered when examining overall CPU utilisation - a positive value indicates higher priority user-level processes which can affect overall CPU utilisation.
- %iowait - percentage of time the CPU was idle with outstanding disk I/O requests.
- High temperatures can reduce the CPU’s operational lifetime or can cause premature failure.
- An increase in overall power consumption (an essential factor in automotive systems).
- A subsequent increase in CPU utilisation.
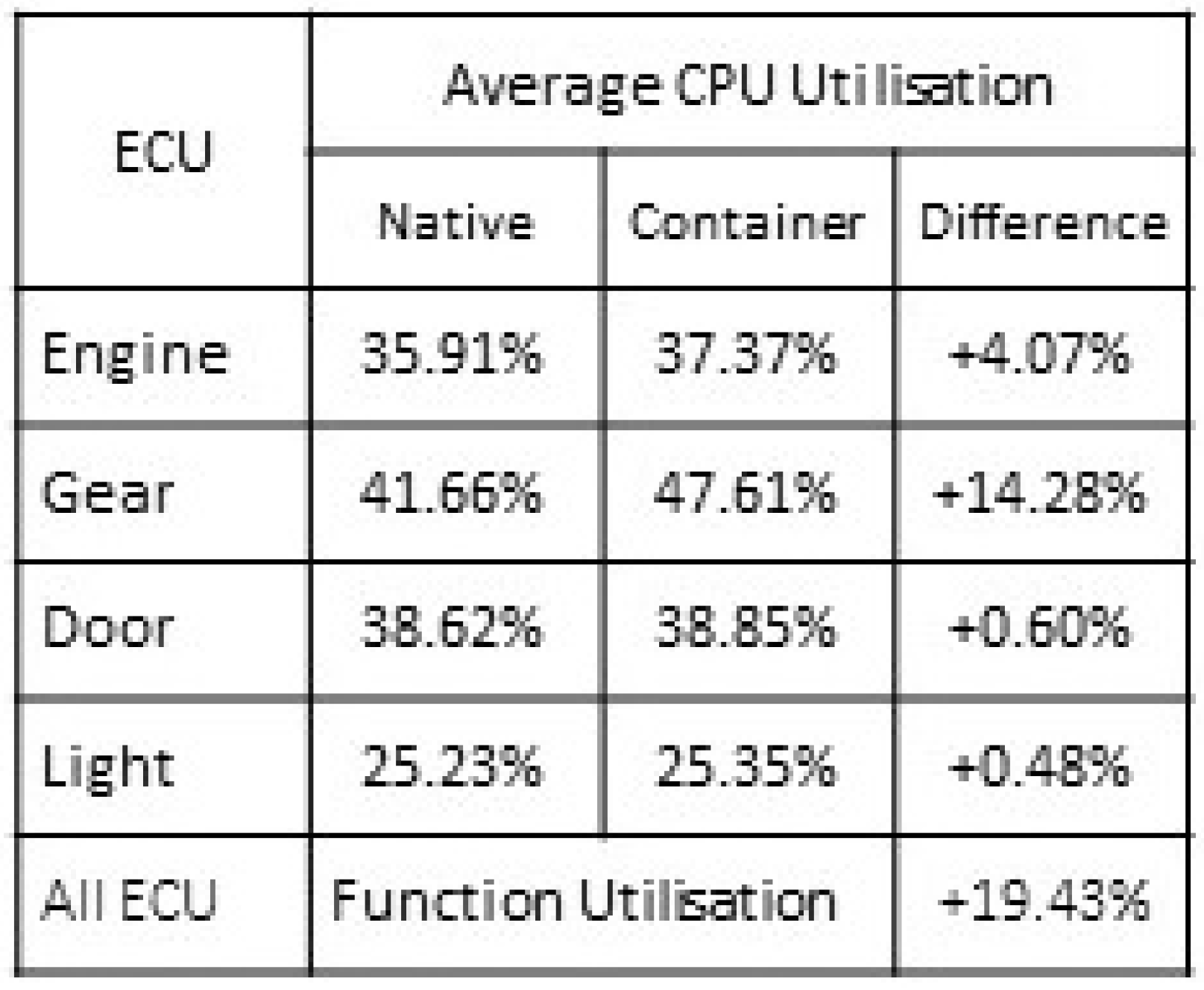
9.1. Overall CPU Utilisation
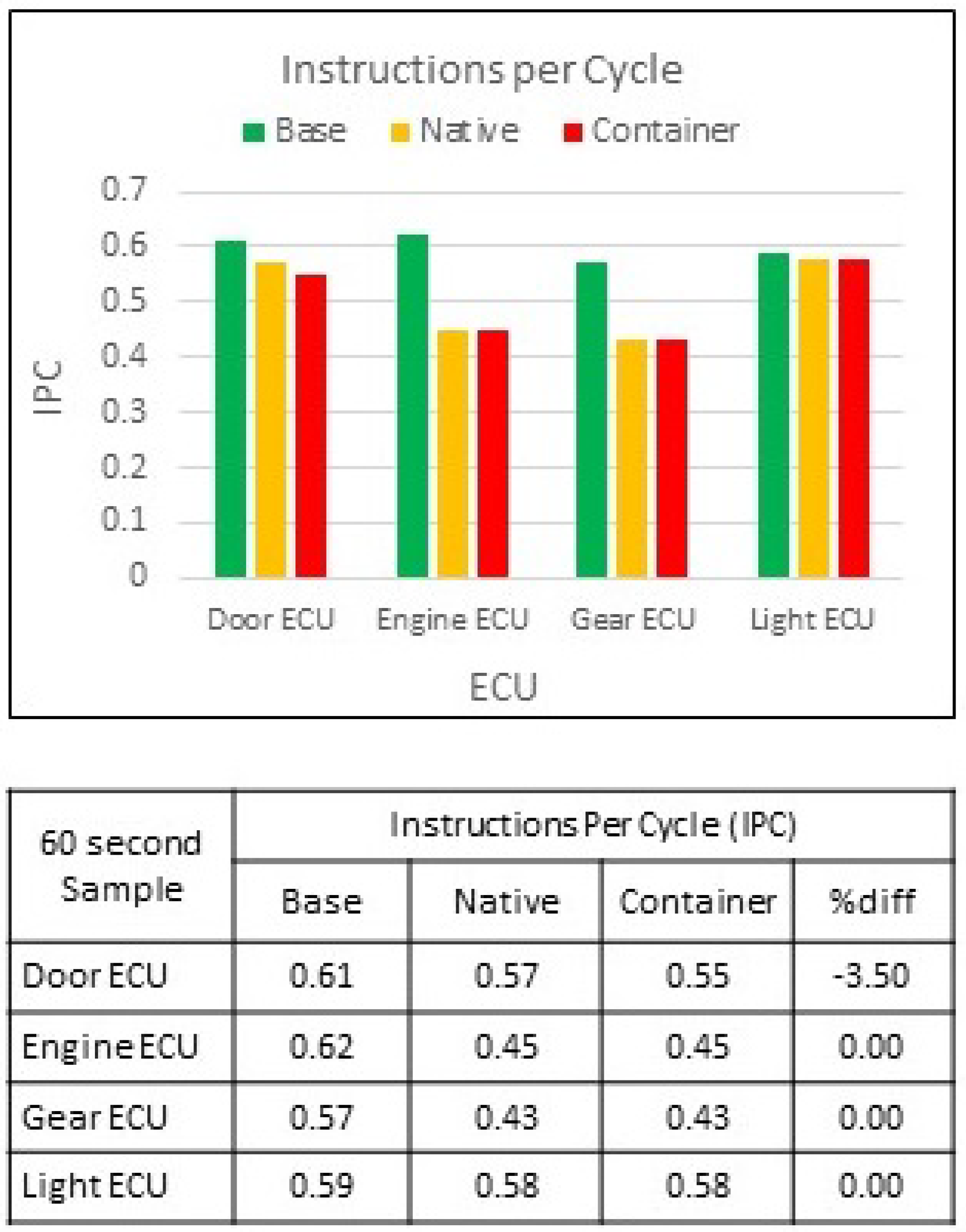
9.2. Instructions per Cycle
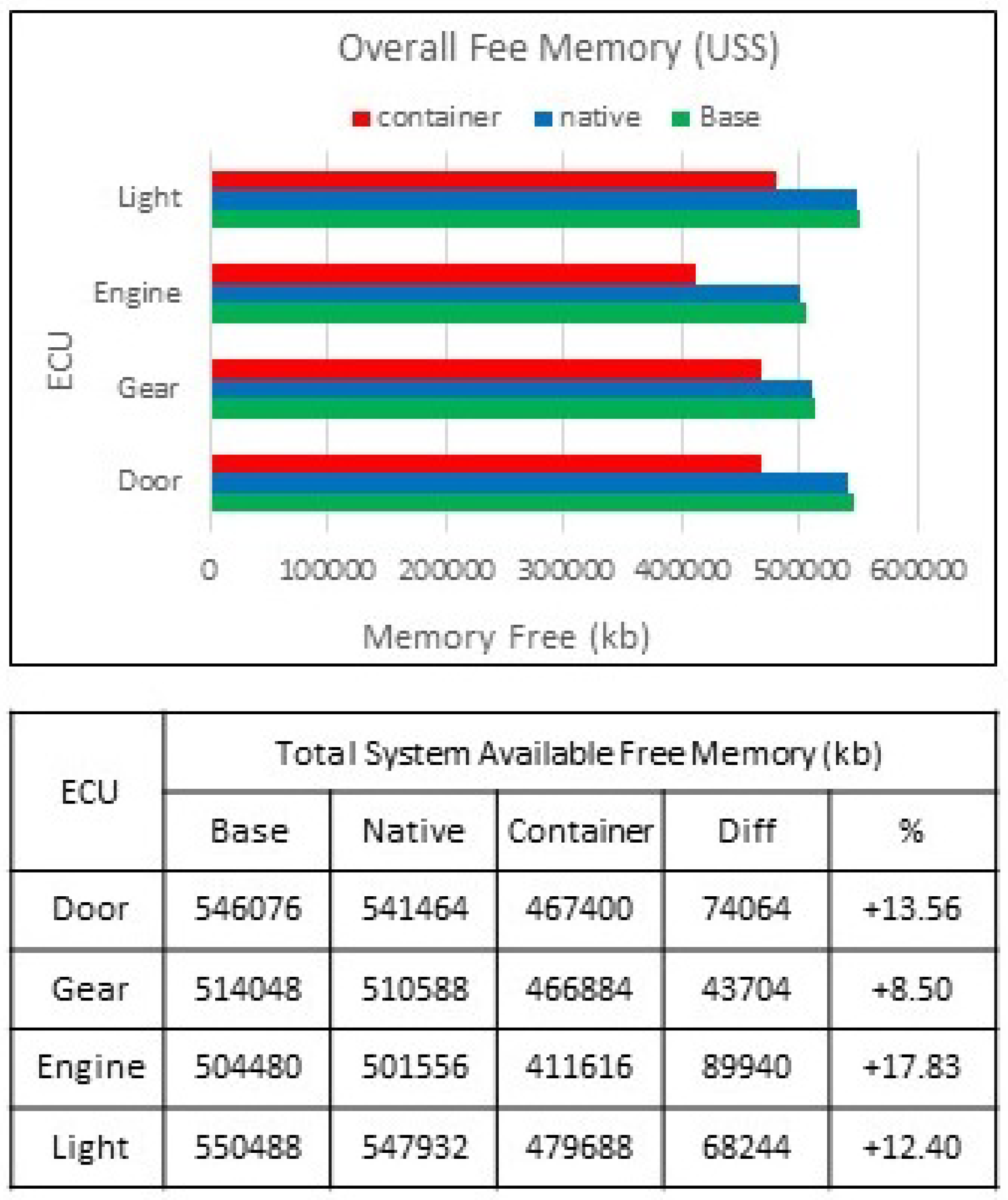
9.3. Memory Unique Set Size
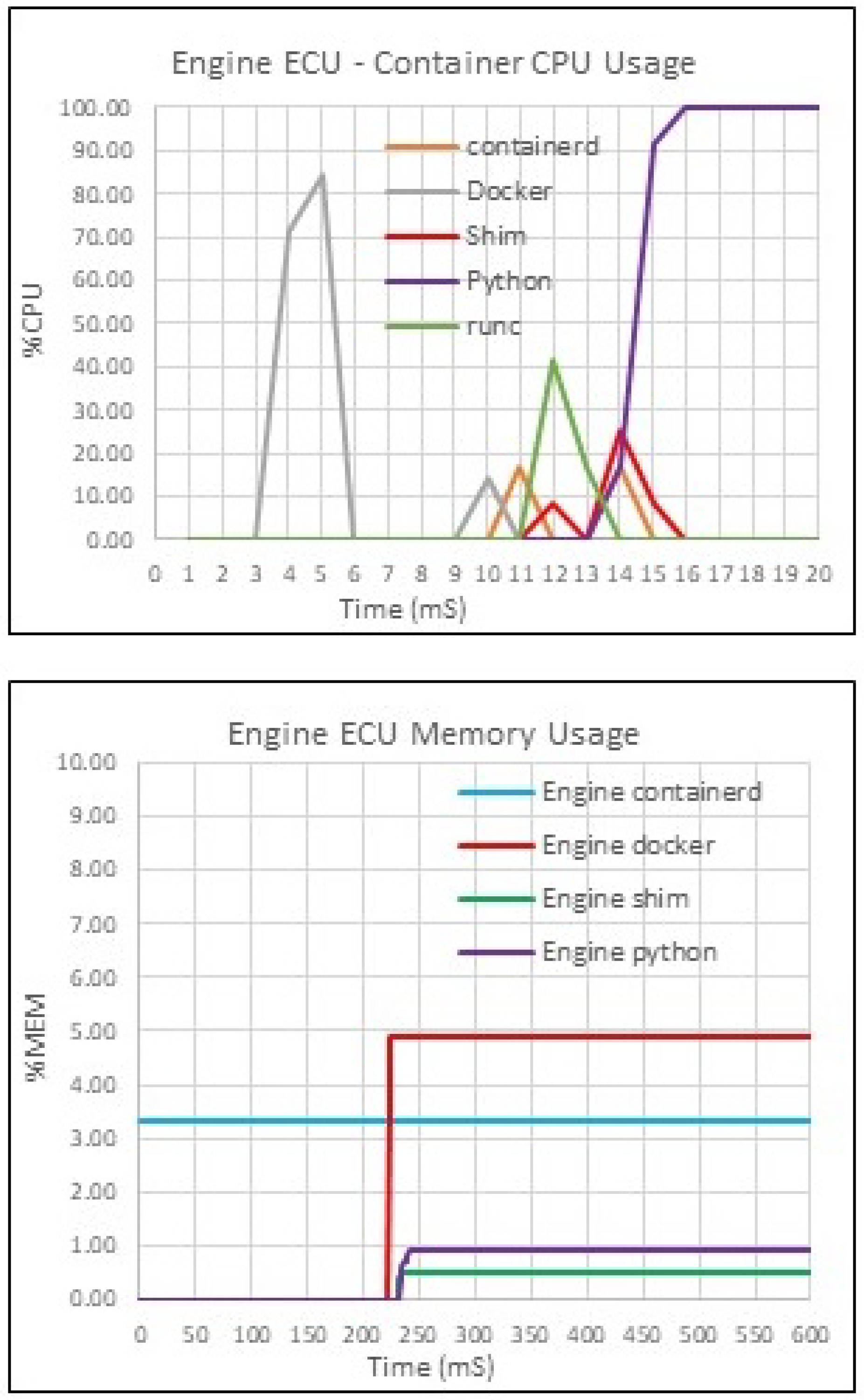
10. Evaluation of Container Specific Resource Consumption
11. Conclusion and Future Work
11.1. Key Findings
11.2. In Summary
11.3. Going Forward
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| MDPI | Multidisciplinary Digital Publishing Institute |
| ND | Nicholas Ayres |
| LD | Lipika Deka |
| DP | Daniel Paluszczyszyn |
References
- H. Takada, "Introduction to Automotive Embedded Systems, Nagoya: Nagoya University" [Online] Available at: https://cse.buffalo.edu/~bina/cse321/fall2015/Automotive-embedded-systems.pdf [Accessed 16 August 2024].
- T. Nolte, H. Hansson, and L. L. Bello, "Automotive communications-past, current and future", in IEEE Conference on Emerging Technologies and Factory Automation, 2005, pp. 8. [CrossRef]
- H. Hartmann, System Monitoring with the USE Dashboard. 2017. [Online] Available at: https://www.circonus.com/2017/08/system-monitoring-with-the-use-dashboard/ [Accessed 16 August 2024].
- J. Jackson, The RED Method: A New Approach to Monitoring Microservices. 2018 [Online] Available at: https://thenewstack.io/monitoring-microservices-red-method/ [Accessed 16 August 2024].
- T. Wilke, The RED Method: Key metrics for microservices architecture. 2017 [Online] Available at: https://www.weave.works/blog/the-red-method-key-metrics-for-microservices-architecture/ [Accessed 16 August 2024].
- J. Bereisa, "Applications of microcomputers in automotive electronics," IEEE Transactions on Industrial Electronics, vol. 2, pp. 87-96. [CrossRef]
- C. P. Quigley, R. McMurran, R. P. Jones, and P. T. Faithfull, " An Investigation into Cost Modelling for Design of Distributed Automotive Electrical Architectures", in 3rd Institution of Engineering and Technology Conference on Automotive Electronics, 2007, pp. 1-9.
- B. Bermejo, and C. Juiz, "Virtual machine consolidation: A systematic review of its overhead influencing factors" The Journal of Supercomputing, 2020, vol 76, issue 1, pp. 324-361. [CrossRef]
- S. Halder, A. Ghosal, and M. Conti, "Secure over-the-air software updates in connected vehicles: A survey", Computer Networks, 2020, vol. 178, Issue C. [CrossRef]
- J. Pelzl, M. Wolf, and T. Wollinger, "Virtualization Technologies for Cars: Solutions to increase safety and security of vehicular ECUs", Proceedings of embedded world conference. Nuremberg, Germany, 2008, [Online].Available: http://www.escrypt.com.
- H. Dakroub, A. Shaout, and A. Awajan, "Connected Car Architecture and Virtualization", SAE International Journal of Passenger Cars - Electronic and Electrical Systems, 2016, vol. 9, pp. 153-159. [CrossRef]
- S. Soltesz, P. Herbert, M. E. Fiuczynski, A. Bavier and L. Peterson, "Container-based operating system virtualization: A scalable, high-performance alternative to hypervisors", in Proceedings of the 2nd ACM SIGOPS/EuroSys European conference on computer systems, 2007, pp. 275-287. [CrossRef]
- J. Walter, M. Fakih, and K. Grüttner, "Hardware-based real-time simulation on the Raspberry pi", in 2nd. Workshop on High performance and Real-time Embedded Systems, 2014.
- B. Gregg, "Thinking methodically about performance", Communications of the ACM, 2013, vol. 56, pp. 45-51. [CrossRef]
- N. Ayres, L. Deka, and D. Paluszczyszyn, "Continuous Automotive Software Updates through Container Image Layers", Electronics, 2021, vol. 10, pp. 739. . [CrossRef]
- M. Broy, "Challenges in automotive software engineering", in Proceedings of the 28th International Conference on Software Engineering, 2006, pp 33-42. [CrossRef]
- D. Reinhardt, and M. Kucera, "Domain controlled architecture", in Proceedings 3rd International Conference on Pervasive and Embedded Computing and Communication Systems (PECCS 2013), Barcelona.
- G. Heiser, "Hypervisors for consumer electronics", in 6th IEEE Consumer Communications and Networking Conference, 2009, pp. 1-5. [CrossRef]
- D. Reinhardt, and G. Morgan, "An embedded hypervisor for safety-relevant automotive E/E-systems", in Proceedings of the 9th IEEE International Symposium on Industrial Embedded Systems (SIES 2014), 2014, pp. 189-198. [CrossRef]
- Felter, W., Ferreira, A., Rajamony, R. and Rubio, J., 2015, March. An updated performance comparison of virtual machines and linux containers. In 2015 IEEE international symposium on performance analysis of systems and software (ISPASS) (pp. 171-172). IEEE. [CrossRef]
- S. Kugele, D. Hettler, and J. Peter, "Data-Centric Communication and Containerization for Future Automotive Software Architectures", in IEEE International Conference on Software Architecture (ICSA), Seattle, WA, 2018, pp. 65-69. [CrossRef]
- N. Ayres, L. Deka, and B. Passow, "Virtualisation as a Means for Dynamic Software Update within the Automotive E/E Architecture", in 2019 IEEE SmartWorld, Ubiquitous Intelligence and Computing, Advanced and Trusted Computing, Scalable Computing and Communications, Cloud and Big Data Computing, Internet of People and Smart City Innovation, Leicester, United Kingdom, 2019, pp. 154-157. [CrossRef]
- M. G. Xavier, M. V. Neves, F. D. Rossi, T. C. Ferreto, and C. A. F. De Rose, "Performance Evaluation of Container-Based Virtualization for High Performance Computing Environments", in 21st Euromicro International Conference on Parallel, Distributed, and Network-Based Processing, 2013, pp. 233-240. [CrossRef]
- R. Morabito, "A performance evaluation of container technologies on Internet of Things devices", in IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), 2016, pp. 999-1000. [CrossRef]
- V. Noronha, E. Lang, M. Riegel, and T. Bauschert, "Performance Evaluation of Container Based Virtualization on Embedded Microprocessors", in 30th International Teletraffic Congress (ITC 30), 2018, pp. 79-84. [CrossRef]
- S. Saidi, S. Steinhorst, A. Hamann, D. Ziegenbein, and M. Wolf, "Future automotive systems design: Research challenges and opportunities", in Proceedings of the International Conference on Hardware/Software Codesign and System Synthesis, 2018. [CrossRef]
- M. Chebiyyam, R. Malviya, S. K. Bose, and S. Sundarrajan, "Server consolidation: Leveraging the benefits of virtualization". Infosys Research, SETLabs Briefings, vol. 7, pp. 65-75.
- L. Malhotra, D. Agarwal, and A. Jaiswal, "Virtualization in cloud computing". Journal of Information Technology and Software Engineering, 2014, Vol. 4, pp. 1-3. [CrossRef]
- F. Lombardi, and R. Di Pietro, "Secure virtualization for cloud computing", Journal of Network and Computer Applications, vol. 34, pp. 1113-1122. [CrossRef]
- D. Breitschwerdt, A. Cornet, S. Kempf, L. Michor, and M. Schmidt, "The changing aftermarket game and how automotive suppliers can benefit from arising opportunities". McKinsey.
- R. Morabito, "Virtualization on Internet of Things Edge Devices With Container Technologies: A Performance Evaluation", in IEEE Access, 2017, vol. 5, pp. 8835-8850. [CrossRef]
- M. J. Scheepers, "Virtualization and containerisation of application infrastructure: A comparison", in 21st Twente Student Conference on IT, 2014, Enschede, The Netherlands. Vol. 21.
- O. Rolik, E. Zharikov, S. Telenyk, V. Samotyy, "Dynamic virtual machine allocation based on adaptive genetic algorithm", in Proceedings of the Eighth International Conference on Cloud Computing, GRIDs, and Virtualization, Athens, Greece, 2017, pp. 108–114.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



