1. Introduction
The notion of unconditional secrecy was introduced by Claude Shannon in [
1], to describe an encryption system resistant to any passive attack on messages based on ciphertext. However, he showed in the same paper that the necessary condition for unconditional secrecy is that the secret key length must be at least as long as the message, which is impractical for most applications. To address this, various approaches have been developed to create secure ciphers with shorter keys. Shannon himself suggested so-called ideal and strongly ideal cipher systems, where an adversary is left with many equally probable decryption options, rather than a unique solution.
In this paper, we address two main questions:
Is it possible to develop a general concept for constructing ideal cipher systems with a predetermined minimum value of key equivocation, independent of the telecommunication environment, the probabilistic structure of the message, and without additional infrastructure for generating and distributing secret keys?
Is it possible to apply this solution to any existing symmetric stream ciphering system without modifying it or knowing the encryption key generation algorithm, except for the length of the applied secret key?
If feasible, such a system would possess the following properties:
Ideal secrecy - Guaranteed minimum value of key equivocation, regardless of the length of the ciphertext used by the adversary.
Autonomy - The autonomous ability to maintain a given minimum value of key equivocation by continuously refreshing keys without additional infrastructure for key generation and distribution.
Robustness - Retains guaranteed properties regardless of the probabilistic structure of the messages.
We refer to this system as the ISAR (Ideally Secure Autonomous Robust) ciphering system. This paper presents a class of ISAR systems based on wiretap polar codes.
1.1. Related Works
Since key equivocation directly depends on the entropy of messages, the first group of works on ideal ciphering systems focuses on preprocessing messages before encryption, to reduce redundancies (or equivalently to increase entropy). In this way, the minimum key equivocation available to a system attacker could be controlled. Compression and randomization techniques are standard for this approach and have a long tradition in cryptography, [
1,
2,
3,
4,
5]. The homophonic coding technique, which transforms a sequence of message symbols into a uniquely decodable sequence where all symbols have the same frequency, also belongs to this approach, [
2,
6,
7,
8]. The effectiveness of this approach depends on knowledge of the probabilistic properties of messages and reliable estimates of the statistical properties of the message source being encrypted.
Another approach, not much different from the first, is entropic security, [
4,
9,
10,
11]. The main difference lies in the security metrics used as a criterion. The goal of this metric is that any function of the original message is unattainable to passive adversaries. In the limiting case, when the so-called leakage parameter is equal to zero, this criterion aligns with Shannon's definition of a perfect ciphering system. However, then all the obtained results for the length of the secret key become practically unusable or give lengths equal to the length of the messages, reducing these procedures to the Vernam cipher.
The honey cipher, introduced in [
12], is similar to the concept of ideal cipher. The main goal of this approach is that an adversary is left with many highly probable hypotheses about secret keys or messages. In [
13] authors combine the ideas of honey ciphers and entropic security to create, practically implementable short-key ciphering system. The dependence of the efficiency of these systems on the knowledge of the probabilistic properties of the source being encrypted is even more critical than previous approaches. This is a consequence of the very idea of the system that, in the process of brute force attacks, hypothesis messages are generated that are difficult to distinguish from the true ones. However, the future development of these systems will likely enhance understanding of the relationship between the probabilistic properties of the source and the minimum length of secret keys sufficient to prevent brute force attacks by an unbounded adversary, which brings us back to Shannon's original ideas about the meaning of non-zero equivocation values of secret keys.
The final group of methods, relevant for the construction of ideally secret systems, comes from the broad research domain of combining the methods of error correcting codes, especially wiretap codes and cryptography, [
6,
14,
15,
16,
17,
18,
19]. In [
6], a system based on wiretap codes was proposed, which proved to improve the performance of an arbitrary stream cyphering system in the regime of short messages, but whose key equivocation drops to zero for sufficiently long messages. In the paper [
20], the authors integrated wiretap polar coding in encryption schemes based on learning with errors problem and showed that with appropriate refresh of secret key procedures, they achieve non-zero equivocation of keys. In paper [
21], the connection between ideal secrecy and wiretap coding approach is clarified. The same authors in [
22] proposed an encryption system over the MIMO wiretap channel, which for infinite lattice input alphabet guarantees perfect security, while for finite constellations guarantees ideal secrecy with high probability. In [
23] authors proposed a polar coding scheme which achieves maximal secrecy capacity for a secret key of arbitrary non-zero rate, shared between transmitter and legitimate receiver. In [
24] an encrypted secure polar coding scheme for general two-way wiretap channel is presented. To achieve strong security and reliability criteria, without any key pre-sharing, it is necessary to apply a complex cooperative jumming strategy.
Based on the presented analysis of the relevant published results, we can conclude the following:
Based on this analysis that includes all four approaches, we conclude that there is no example of an ISAR system in the available literature.
1.2. Paper Organization
Section 2 provides a basic conceptual and theoretical basis for understanding ISAR systems, particularly from the domain of wiretap channels, polar coding, privacy amplification techniques and Shannon’s notion of ideal and strongly ideal systems.
Section 3 describes the system architecture and security properties of the ISAR ciphering system. First, it is shown that the system is equivalent to a wiretap model, whose main channel is error-free, while the wiretap channel is equivalent to an embedded symmetric stream cyphering system. In Theorem 2, it is proved how wiretap coding should be constructed in order to achieve strong secrecy and reliability. Theorem 4 gives the capacity of the wiretap channel, which turns out to decrease linearly with the length of the secret key. Theorem 5 gives equivocation of secret key, while Theorem 6 gives secrecy capacity of proposed ISAR as a function of polar code length and security margins for equivocation and privacy amplification. Then it was shown that for an arbitrary cipher system to be ideal with the same lower bound of key equivocation as the ISAR system, its secret key must be
-times greater than that of ISAR, where
is proportional to message length. Thus, the superiority of the ISAR system increases with the length of the messages. The chapter concludes with a demonstration of how any symmetric stream ciphering system can be transformed into ISAR.
Section 4 provides security analysis of ISAR ciphering system, including its resistance to passive attacks both on secret keys and messages.
Section 5 summarizes the practical aspects of the implementation and application of the ISAR system in contemporary information and communication infrastructure. It is shown that the complexity of the system is
, where n is the length of the polar code. For point-to-point protection, the initial exchange of the secret key and the hash function seed is performed only once, regardless of the number of sessions or communication disruptions.
Section 6 concludes the paper with a summary of findings and suggestions for future research directions.
1.3. Notations
We define integer interval as the integer set between and . We denote random variables taking values in alphabets , and their realization is denoted by respectively. Also, we denote a size vector and denote . Further, for any index set , we define denotes entropy and denotes mutual information.
2. Preliminaries
In order to make it easier to understand the operation of the proposed system, in this section we will present basic concepts from the domain of wiretap channel model, polar coding and privacy amplification, since these three elements are its basic building blocks. In the final part of the chapter, the definition of an ideal autonomous ciphering system is given, as a kind of generalization of Shannon’s notions of ideal and strongly ideal ciphering systems, [
25].
2.1. Wiretap Channel Model
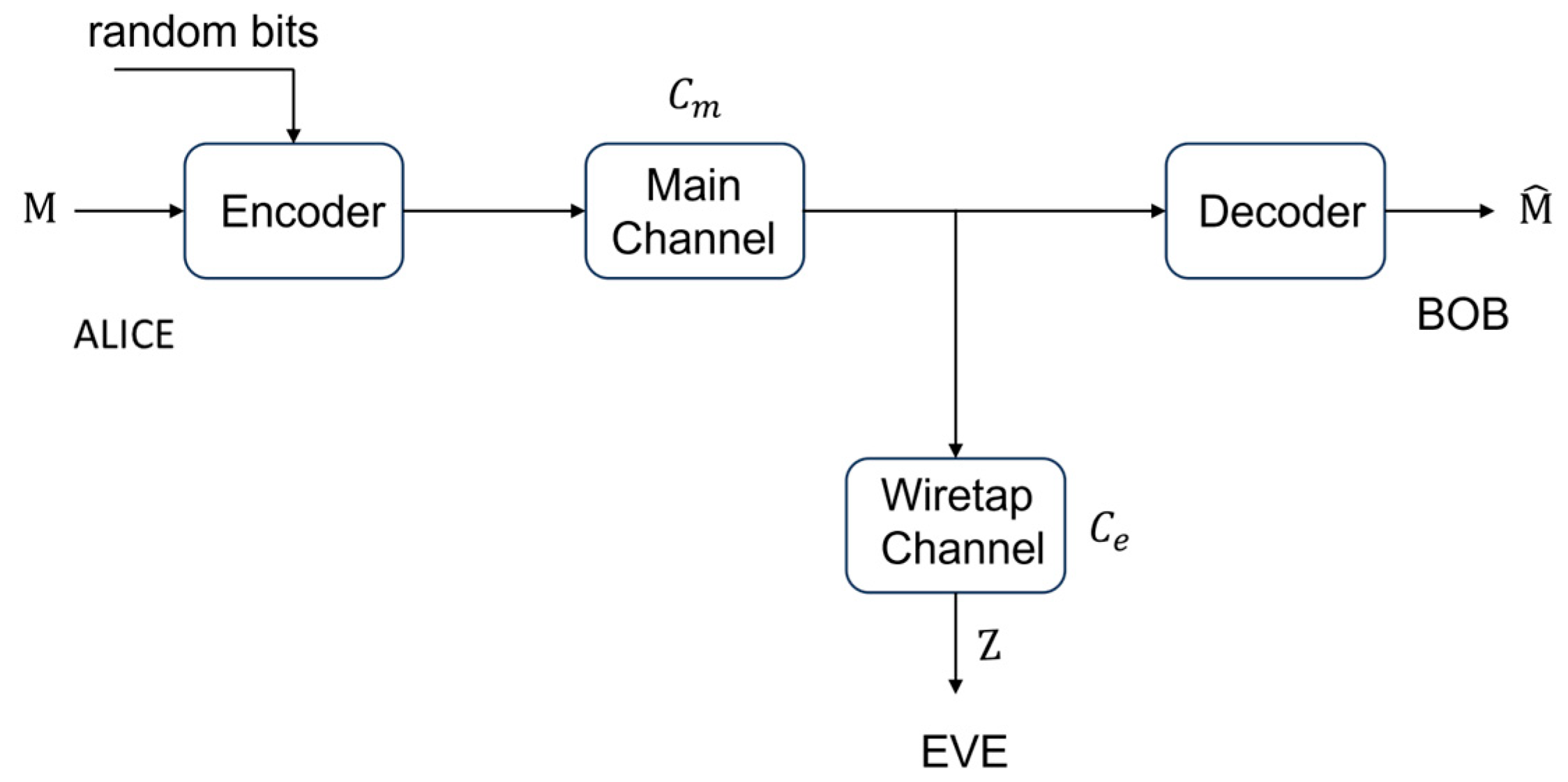
The wiretap model consists of two channels
and
, the main and wiretap channels, respectively, first time introduced by Wyner [
14], see
Figure 1.
denotes the
-bit message that Alice wants to send to Bob. With the help of random bits, the encoder maps
into sequence
of
-bit channel symbols. This sequence is sent on the main and wiretap channels, giving the corresponding channel outputs
and
. On Bob's side, the decoder maps
into estimate
of the original message.
If the main channel is superior to the wiretap channel, we say that the wiretap channel is degraded relative to the main channel. Formally, for each wiretap channel degraded with respect to the main channel can be find a third channel , such that can be represented as a cascade of channels and . In other words, the degraded channel always has a lower capacity compared to the main channel.
The basic purpose of wiretap coding is the design of encoders and decoders that provide for legitimate users (Alice, Bob) at the same time reliability and security when the message length
tends to infinity. Reliability is usually measured in terms of the probability of error in recovering the message sent by Alice at Bob's side
As a rule, security is measured in terms of mutual information between the message M and Eve's observation Z, giving the two most frequently analyzed criteria, so called week security criterion
and strong security criterion
As Maurer first pointed out [
26,
27], Eve can disclose
message bits, while (2) is still true, which is obviously unacceptable. Therefore, satisfying the strong security criterion (3) is the generally accepted gold standard of the cryptographic community. Note that there are other secrecy measures, such as advantage and semantic security, which are shown to be equivalent to the strong security criterion [
15].
The largest transmission rate at which both reliability and secrecy conditions are simultaneously satisfied is commonly referred to as the secrecy capacity
. In case the main and wiretap channels are binary symmetric channels (BSC) and the wiretap channel is degraded with respect to the main channel,
was given by [
28]
where the random variable at the input to the channel is uniform over , while ( denotes the capacities of the main and wiretap channels.
2.2. Wiretap Polar Coding
Polar codes, introduced by Erdal Arikan [
29,
30], are a class of error-correcting codes that achieve the capacity of binary-input symmetric memoryless (BSM) discrete channels. The key idea behind polar coding is to transform a set of
communication channels into a set of polarized channels, where a subset of channels become nearly perfect (noiseless) and the others become completely noisy. If with
we denote BSM channel
, the Bhattacharyya parameter of
is
Value (5) is equal to the upper bound probability of error Maximum Likelihood (ML) decoding on a single use of the channel. It is shown that
takes values from the interval [0,1]. Channels with small
values are almost noiseless, while channels with
values close to 1 are almost pure-noise channels [
30]. The essence of wiretap polar coding is the transformation of n instances of
and
into n-input channels
and
, which are polarized either as good or bad channels depending on their Bhattacharyya parameters
and
and/or symmetric capacity
. In order to achieve strong secrecy [
17,
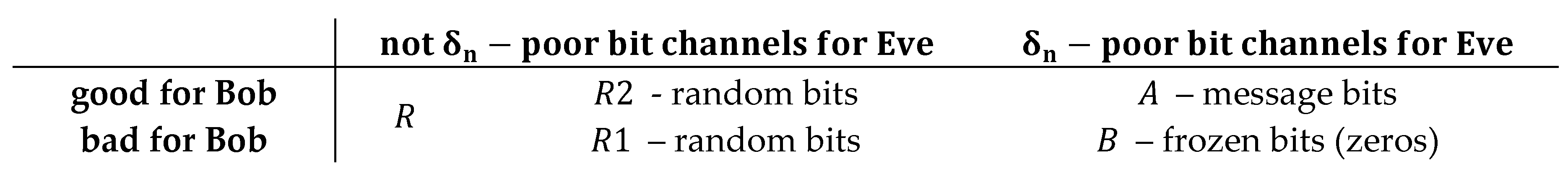
18] proposed the following definition of good and bad polarized channels
using security function
and a parameter
. For fixed
, we can define next partition of
Next, let's partition the set R into two subsets R1 and R2 (R= R1 ⋃ R2)
This obtained subsets of polarized channels, and their meaning in terms of transmission quality in the main and wiretap channels, are shown in
Table 1.
A polar wiretap encoder performs a 1-1 transformation of the original input vector
into an
-dimensional code vector
,
where
is Arikan’s generator matrix, given by
is the
bit-reversal permutation matrix defined in [
30], while
is the b-fold tensor product of
with itself. The input vector
has the following structure
The corresponding components of the input vector
, are set to the following values
where
is random vector, selected by Alice uniformly at random from {0, 1}. Vector of frozen bits
is set to 0 vector of dimension
, where
is the complement of
in
. As it was mentioned in [
30], in the case of symmetric channels, any choice of frozen values is as good as other. From now on, we will assume that it is
For the described coding scheme, in [
17], see Proposition 16., is proven to hold
From here follows the conclusion that by choosing the security function
, we can bound mutual information leaked to Eve, for any message distribution. Specifically, according to [
17], see Theorem 17., for any security function such that
described wiretap coding scheme guarantees strong security.
As for achieving reliability conditions, since it is in the general case
it is necessary to apply involving chaining construction [
18] over multiple blocks to ensure reliability. Namely, since non frozen channels in strong security coding scheme are given by
it is necessary to ensure reliable transmission in the channels indexed in the index set
. This is exactly what chaining construction achieves by taking a subset of indices from set
, i.e.,
such that
. Random bits that are placed in
in the
-th block are used in
in the
-th block for
…. In the first block, random bits are used that were distributed to Alice and Bob before starting communication. In this way, the SC decoder on Bob's side in each block can successfully decode the contents in the channels with indices from (22), and therefore
Regarding the obtained secrecy capacity, the answer is provided by Theorem 1, from [
17]:
Theorem 1.
For any security function , and constants that satisfies condition
the rate of the corresponding strong-security coding scheme approaches the secrecy capacity given by (4), namely
2.3. Privacy Amplification (PA)
Privacy amplification is a technique used in cryptography to enhance the security of a shared secret key between two parties. The primary goal is to convert a partially secure or somewhat compromised key into a highly secure key, even in the presence of an eavesdropper who may have some knowledge about the original key [
19,
31]. In terms of practical application, hash functions called universal families have a special role. [
32].
Definition 1.
Family of functions , where and are two final sets, is 2 – universal, or in short – universal, if it holds
where is a random variable that represents a random choice of a afunction uniformly at random in .
An example of a frequently used class of universal hash functions, see for example [
33,
34,
35], is given by
In applications, a random choice of a hash function from a given set is implemented using a seeded pseudorandom generator. To emphasize this fact, we explicitly introduce seed notation. Therefore, a hash function from the class
, is denoted as
where denotes seed of adequate length. If is available only to legitimate users, the hash functions are typically known as cryptographic hash functions.
Definition 2.
The difference between the dimensions of the domain and codomain of a given class of hash functions will be referred to as its compression rate .
Compression rate of class , defined in (26) is
2.4. Ideal and Ideal Autonomous Cipher System
Consider a general symmetric cipher system , where is the input plaintext, is the ciphertext, and is the secret key.
According to Shannon, an ideal ciphering system is one in which the key equivocation, i.e.,
remains non-zero even as the number of ciphertext symbols
approaches infinity, [
25]. This means that the uncertainty about the key does not reduce to zero, regardless of how much ciphertext is available to an attacker. Important properties of ideal encryption systems are:
Non-zero Key Equivocation: The key remains partially unknown, no matter the length of the intercepted ciphertext.
Security over Time: The security of the system does not degrade with the amount of data encrypted and transmitted.
Practical Key Length: The key length can be shorter than the message length, unlike a one-time pad, but must be sufficient to maintain key equivocation.
A strongly ideal system has key equivocation constant at entropy of secret key, i.e This implies an even higher level of security, ensuring that the key's uncertainty remains unchanged from its apriory value, regardless of the volume of ciphertext available. Key Characteristics:
Constant Key Equivocation: The amount of information about the key that remains unknown does not diminish with increasing ciphertext.
Enhanced Security: Offers superior protection against extensive ciphertext analysis, maintaining key secrecy over an indefinite amount of encrypted data.
Robust Design: Typically requires more sophisticated cryptographic techniques to ensure that key equivocation remains constant.
By distinguishing between these two concepts, Shannon's theories provide a framework for evaluating and designing cryptographic systems based on the desired level of security and practical constraints.
Starting from these founding Shannon definitions, we will define a new term - ideal autonomous ciphering system.
Definition 3.
An ideally secret autonomous robust (ISAR) ciphering system is one which can maintain minimal key equivocation at predefined value , i.e.
If several different secret keys are used during operation of one cipher system, which correspond to ciphertexts we say that the system is ideal and autonomous if it is able to maintain a predetermined minimum value of equivocation for each of the applied keys, i.e.
Remark 1.
In Shannon's definition of an ideal system, it is important that the key equivocation is not reduced to zero with an unlimited increase of the available ciphertext. On the other hand, a strongly ideal cipher system requires constant maintenance of key equivocation at the entropy level of the secret key. An ideal autonomous cipher system is in a certain sense between these two extremes. It maintains the minimum value of key equivocation at a predetermined value, which in general belongs to the open interval .
Remark 2. Since is a non-increasing function of the number of observed ciphertext symbols n, the minimum in (27) is always reached at the maximum available n.
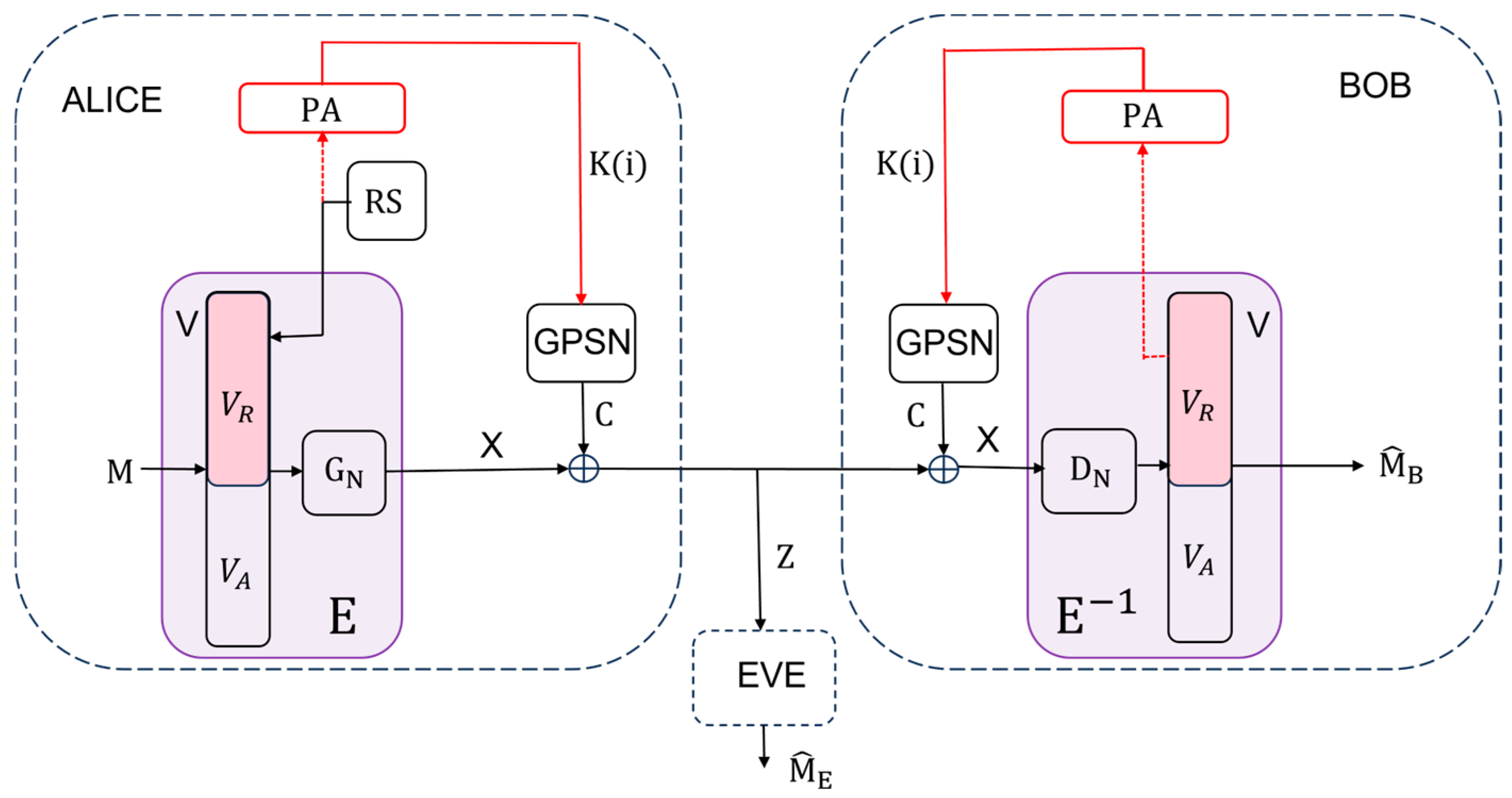
3. System Architecture and Security Properties of ISAR Cyphering System
Let the protected communication between the legitimate parties Alice and Bob take place in the successive exchange of messages
, which were previously divided into a series of blocks of length
. At their disposal is a symmetric stream cyphering system (GPSN,
) with short secret key
. As is known [
1], such systems cannot provide strong security, and practical secrecy is measured by the amount of spent computer resources of the adversary (Eve) in arriving either to the message (partial system cracking) or to the secret key (total system cracking). Block
denotes a polar coder, which performs a 1-1 transformation of messages
into an
-dimensional codeword vector
, while block
performs an inverse transformation of vector
into message
. Alice and Bob have local sources of randomness (denoted by RS on Alice's side), as well as Privacy Amplification (PA) blocks, which, based on the input random string obtained in block
, generate a shorter random string that serves as a new secret key
for encrypting the vector
in block
. We will assume that the system uses a cryptographic hash function
from the class of universal hash functions (25), as well as that the seed
was previously exchanged between Alice and Bob. In the initial block,
, i.e., the initial secret key of the given stream cipher system (GPSN,
).
Remark 3.
Additionally, we will assume that the cipher system (GPSN, ) is semi-injective with respect to , i.e., that the knowledge of ciphers and messages uniquely determines , i.e., holds .
A system conceived in this way can also be viewed as a kind of wiretap model. Legitimate users Alice and Bob are communicating over an equivalent noiseless main channel
, where
is identity matrix, see
Figure 2. An eavesdropper Eve is wiretapping over an equivalent wiretap channel
, where
is an
matrix
being the probability of receiving
given that
was sent, see
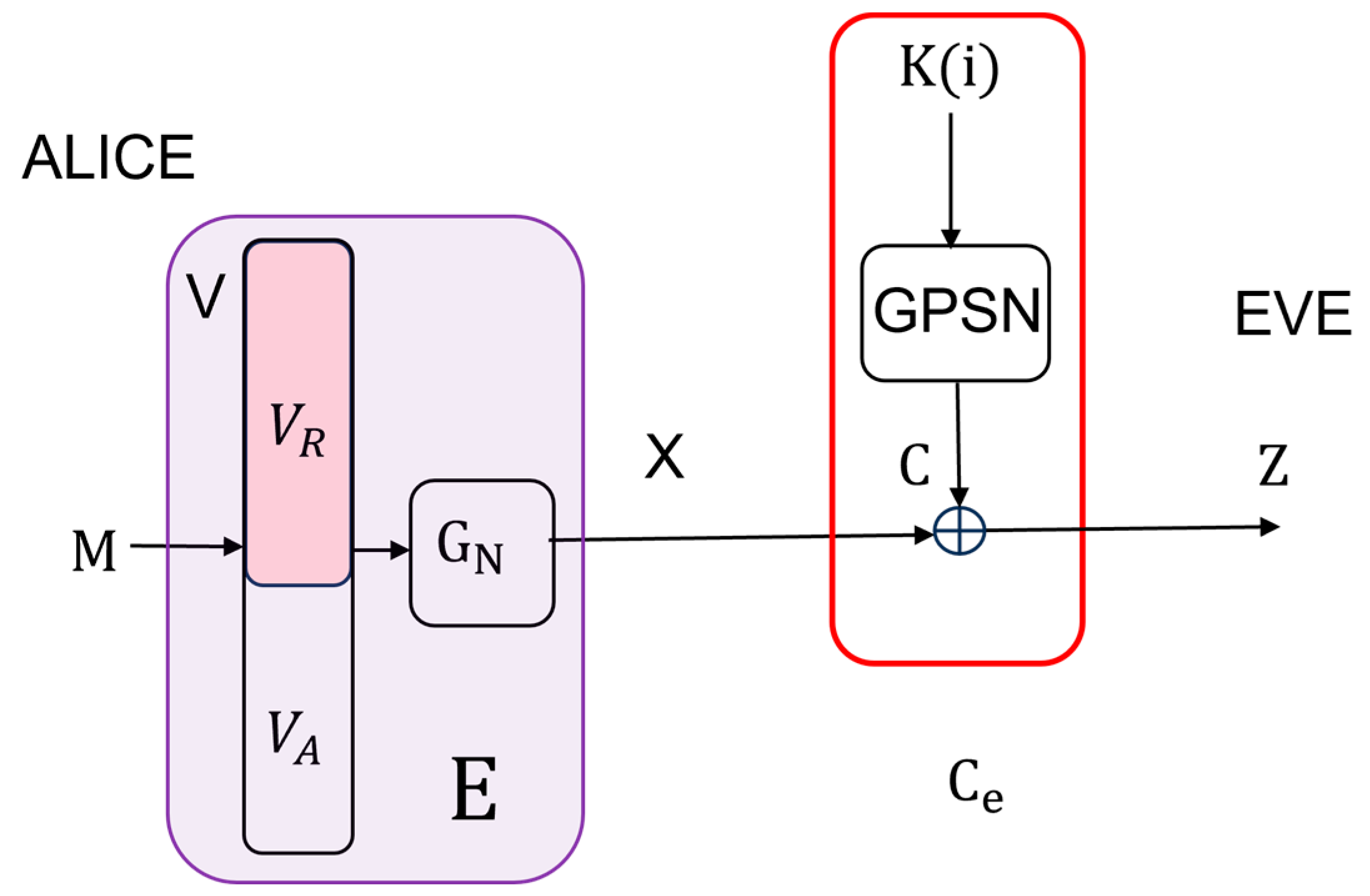
Figure 4. In order to be able to apply the results presented in chapter 2, we have to prove that the equivalent wiretap channel is BSC.
Lemma 1. Equivalent wiretap channel is a BSC.
Proof. Equivalent wiretap channel is a BSC.
According to the proposed scheme
, see
Figure 4,
Since is independent of , (3.1) je equivalent to BSC ( where crossover probability data is . □
We can now formulate the main result of this part of the work.
Theorem 2.
Let , be an arbitrary security function that satisfies condition (1). Let the index sets and be given by , , while is random vector, selected by Alice uniformly at random from {0, 1}. If in the ISAR system, the input vector is structured as follows
then it satisfies both reliability and strong security criteria, precisely
Proof. Bearing in mind that the equivalent main channel for ISAR system is noiseless, the wiretap coding scheme for strong secrecy is determined by the sets of polarized channels indices (6) – (13), which now have the following values
According to (39) the problematic set of indices
is an empty set, therefore it is not necessary to apply the chaining scheme. By structuring the input vector
according to (30), where the sets of indices
and
are given by (36) and (37) respectively, we conclude that the proposed polar coding scheme is merely an instantiation of the general polar wiretap coding scheme from section 2.2, which, under the assumptions of Theorem 2, ensures both reliability and strong secrecy. Since the main channel is noiseless, decoding on Bob's side is not performed using the SC decoder, but rather by a simple inverse operation with respect to the encoding, that is
given that the Arikan transform matrix
is its own inverse over Galois field
. Therefore, the reliability condition expressed by (31), is actually deterministically satisfied. This completes the proof.
□
Theorem 3.
For any security function , and constants that satisfies condition (22) the rate of the coding scheme of proposed system from Figure 2 , approaches the secrecy capacity, namely
Proof. The proof follows directly from Theorem 1 [
17], and the fact that the capacity of main channel is
. □
Remark 4.
Eve's optimal strategy is to attempt to decode the wiretapped , using the Successive Cancellation (SC) decoder, after receiving it [30]. The average block error probability at Eve’s side can be lower bounded, applying Lemma 2.9 of [36] by Korada
where is information set. Considering that Eve does not know frozen bits on her side, the information set includes all indices, i.e., and the polar code applied is of rate 1, see the similar argumentation in [37]. The maximum value of is very close to 1, having in mind that includes bad channels as well. Therefore, according to (43) it follows
where is small. From this, we conclude that Eve's optimal decoding strategy of using the SC decoder results in the maximum decoding error, preventing her from obtaining both the message and the purely random sequence .
It is evident that the key properties of the proposed system depend on the capacity of the wiretap channel . The following theorem determines the value of this quantity, depending on the length of the polar code and the length of the secret key .
Theorem 4.
The capacity of Eve’s channel in the proposed system from Figure 2 is given by
where is the length of the secret key of the given symmetric stream cyphering system (GPSN, ), while is the length of the polar code.
Proof. For a discrete memoryless symmetric channel
with input
and output
, channel capacity is defined as
where the maximum is taken over all possible input distributions
, [
38]. Further, we have
The input to the wiretap channel
is simultaneously the input (message) to the symmetric stream ciphering system (GPSN,
). Message equivocation is equal to key equivocation
for every semi-injective symmetric ciphering system, see Theorem 2, [
39]. On the other hand, it well known that (see for example [
25])
which, by substituting into (48), and then into (47) gives
One of the primary goals in the designing any cipher system is for ciphertext to appear to be totally random for as long as possible, i.e., that
this holds for larger values of
. The assumption (51) is referred to by Massey in [
40] as “total randomness” assumption, and it is shown to be valid as long as
where
is the unicity distance of given cipher system, [
1]. Considering (51), and the fact that
since secret keys are chosen as purely random sequences, from (50) we obtain
, or normalized per bit
which had to be proven. □
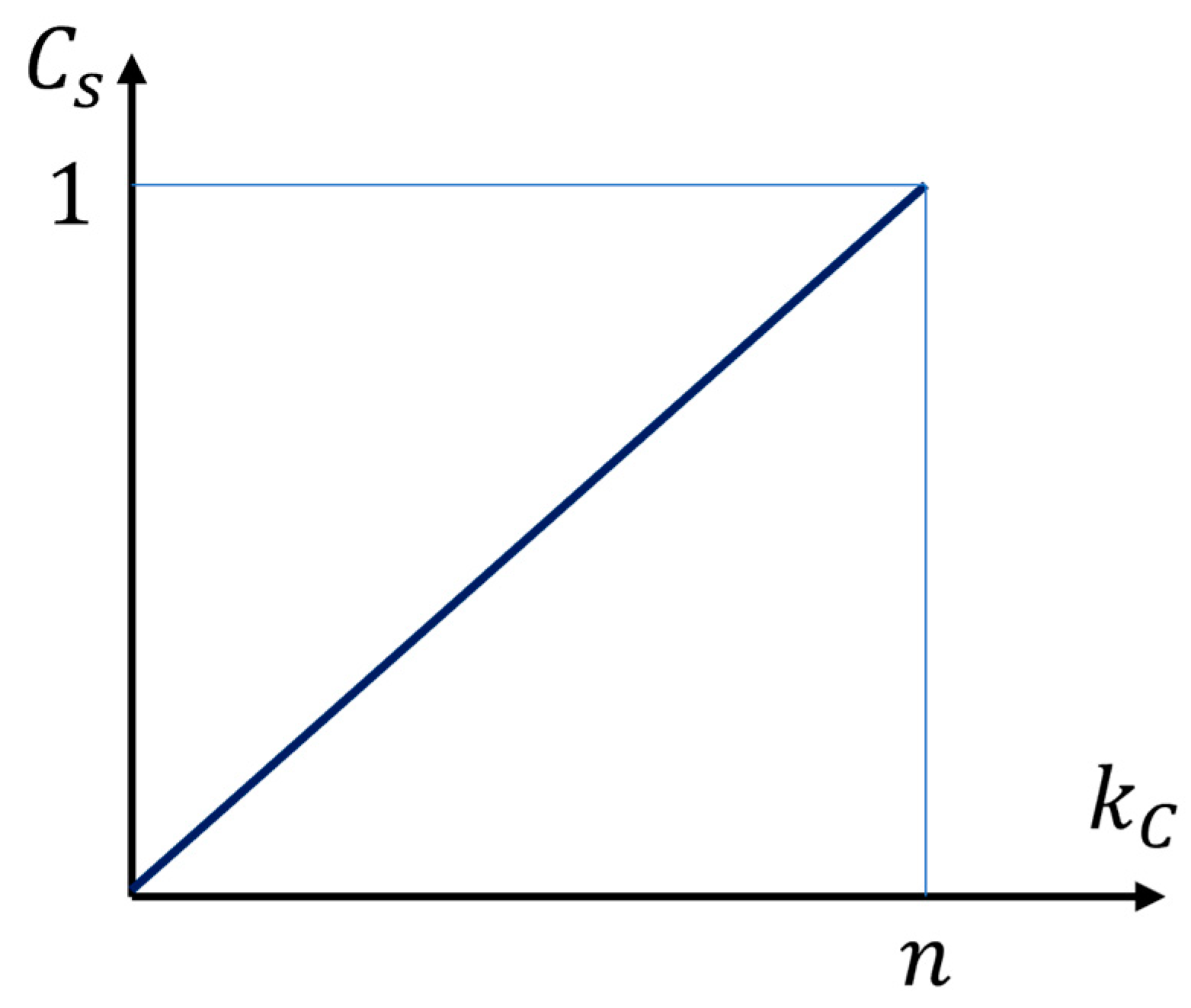
Remark 5.
Given Theorems 3 and 4, the secrecy capacity of the proposed system is
from this, the fundamental impact of the secret key length is clearly evident, see
Figure 5. For , system does not provide any security, while for , . It means that in latter case we can choose all n bits of polar code for secure transmitting of n message bits.
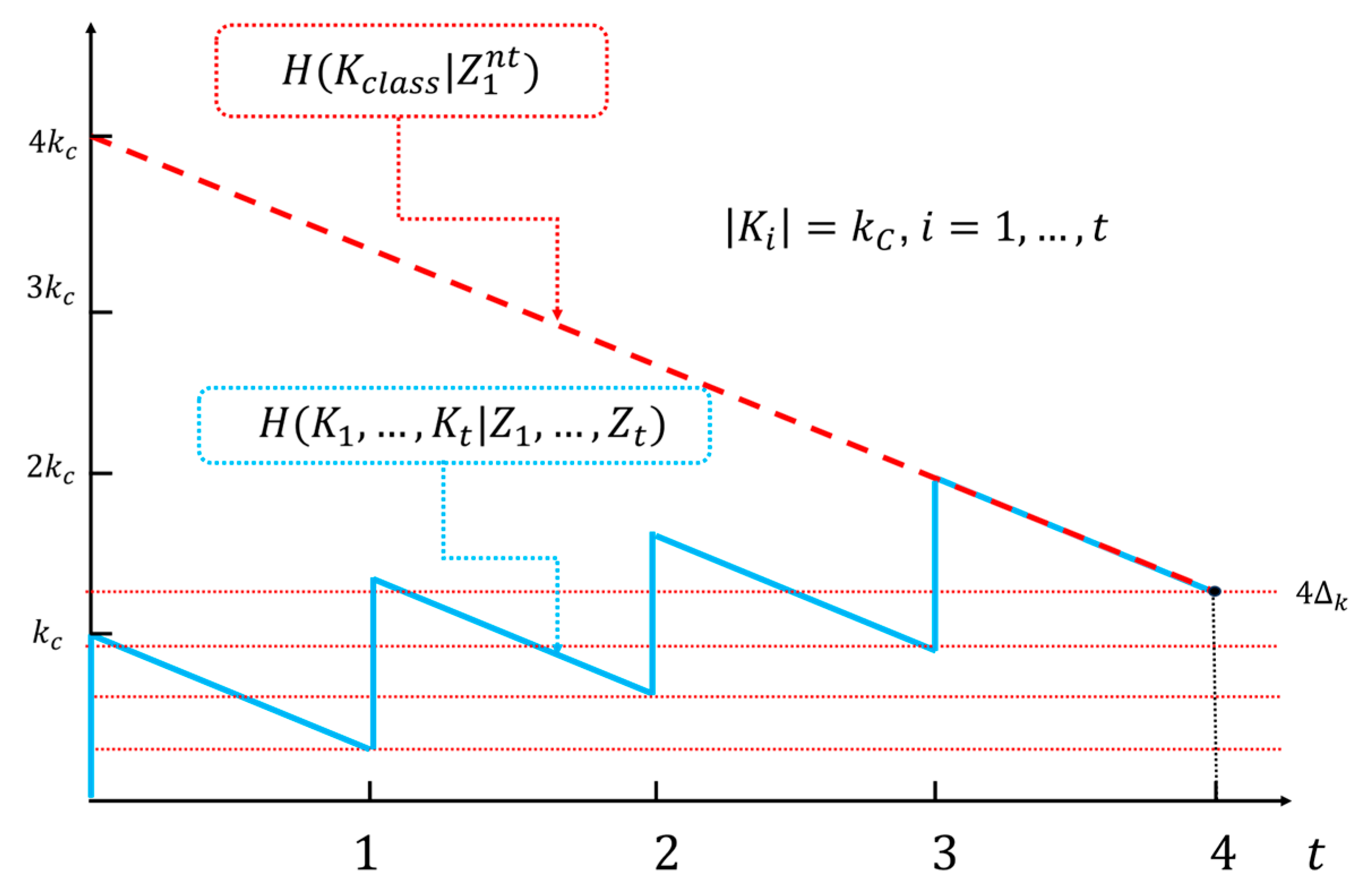
In order to examine the properties of ideally secret autonomous cipher systems, we need the following theorem which provides a lower bound on the equivocation of the system’s secret keys.
Theorem 5.
The equivocation of the secret keys , GPSN(), when the ciphertext is known, satisfies the inequality
where n is the length of the polar code, is the entropy of the secret key, and is a purely random vector of dimension
.
Proof. Generally, according to [
25], for any cipher system with a secret key
, input
, and ciphertext(output)
, it holds
. Based on (13), the output vector
can be written in the form
where
and
are submatrices of polar code generation matrix
consisting of corresponding rows in
.
The ranks of the matrices
and
are
and
, respectively, because the generator matrix
has full rank
. Therefore
and
can be uniquely represented by a set of basis vectors of dimensions
and
. These basis vectors are some of the column vectors of the matrices
and
respectively. We will denote these sets of column indices as
and
. Then there exists a one-to-one correspondence between
and
, and between
and
. Hence
Based on the data processing properties of entropy [
38] , we conclude that in the PA procedure there is a limitation,
, from which it follows that the secrecy capacity in the ISAR system must be
Thus, it holds that
given the condition
and the fact that
is purely random vector with maximum entropy equal to
Since it is always true that
we finally get
which had to be proven. □
To ensure the system possesses autonomy in generating secret keys, we must restrict the secrecy capacity, as some of the bits of the polar code need to be used for generating and distributing secret keys. Additionally, for the system to be ideal and autonomous, a further reduction in secrecy capacity is necessary to maintain the desired minimum level of key equivocation. These facts are summarized in Theorem 6 below.
Theorem 6.
The proposed system is ideal and autonomous, with secrecy capacity
where is a given minimum value of key equivocation, and
is the compression rate of the applied class of universal hash functions.
Proof. To prove that the proposed system is ideal, it is necessary to show that
, kada
Since
this is equivalent to the condition
, as
Consider the general case where Alice sends Bob a message
of arbitrary length
. The message
will be divided into blocks of length
The total number of blocks will be
, where
is the length of the polar code, so
The last block, if it is not of length
, can be padded with arbitrary content. According to the proposed coding scheme that provides strong security,
. Based on (41), in addition to the transmitted message
, Bob decodes without error a purely random vector
, of length
, which was written on the indices from the set
given in (36) during the encoding process on Alice's side. Thus, Alice and Bob, after decoding, possess identical random sequences
, in each of the
transmitted blocks of the polar code. Eve's optimal strategy is to decode her received signal at the output of the wiretap channel using the SC decoder. Eve knows the parameters of the applied polar code, such as the length
, and the index sets A and R, but does not know the values of the bits at those positions. This situation is equivalent to the SC decoder operating in the mode of unknown so-called frozen bits. As noted in Remark 4, Eve's error in optimal decoding is close to the maximum, so it can be said that Eve's information about the sequence
is close to zero. By applying PA to the common random sequences
, Alice and Bob can further reduce Eve's residual information about these sequences. In each current block, a secret key of length
is generated for the next block using some chosen PA algorithm
Given that
is the compression rate of the class of universal hash functions applied in the PA process, it follows that
Considering Theorem 2 and (64), and assuming the ergodicity of the local randomness source, i.e.,
,
, it can be obtained from (53)
For the system to be ideal, it is sufficient to ensure that the right-hand side of (61) equals a predetermined minimum value of key equivocation
, in each block, i.e.
that is
By substituting (65) into (67) it is obtained that
which had to be proven. □
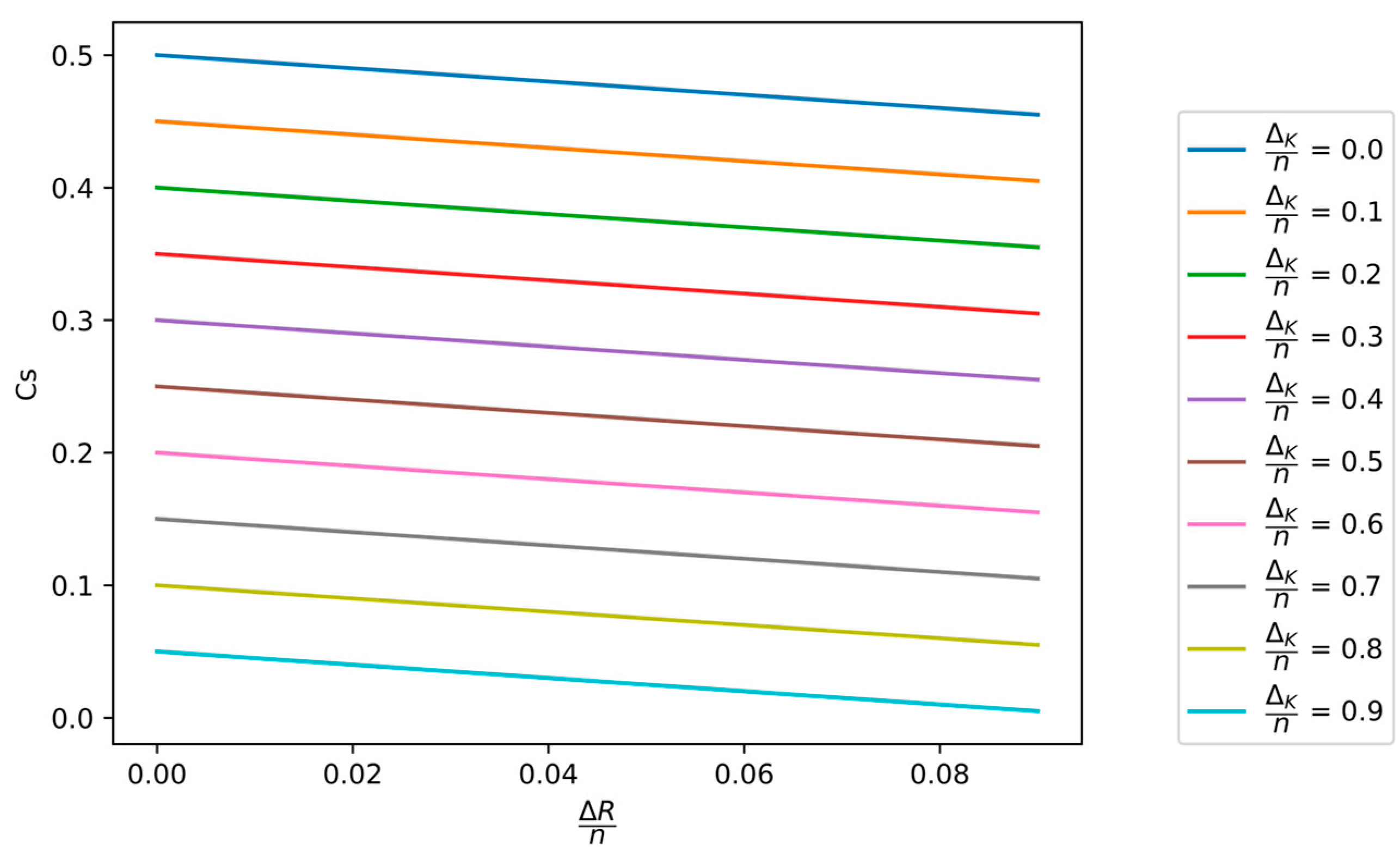
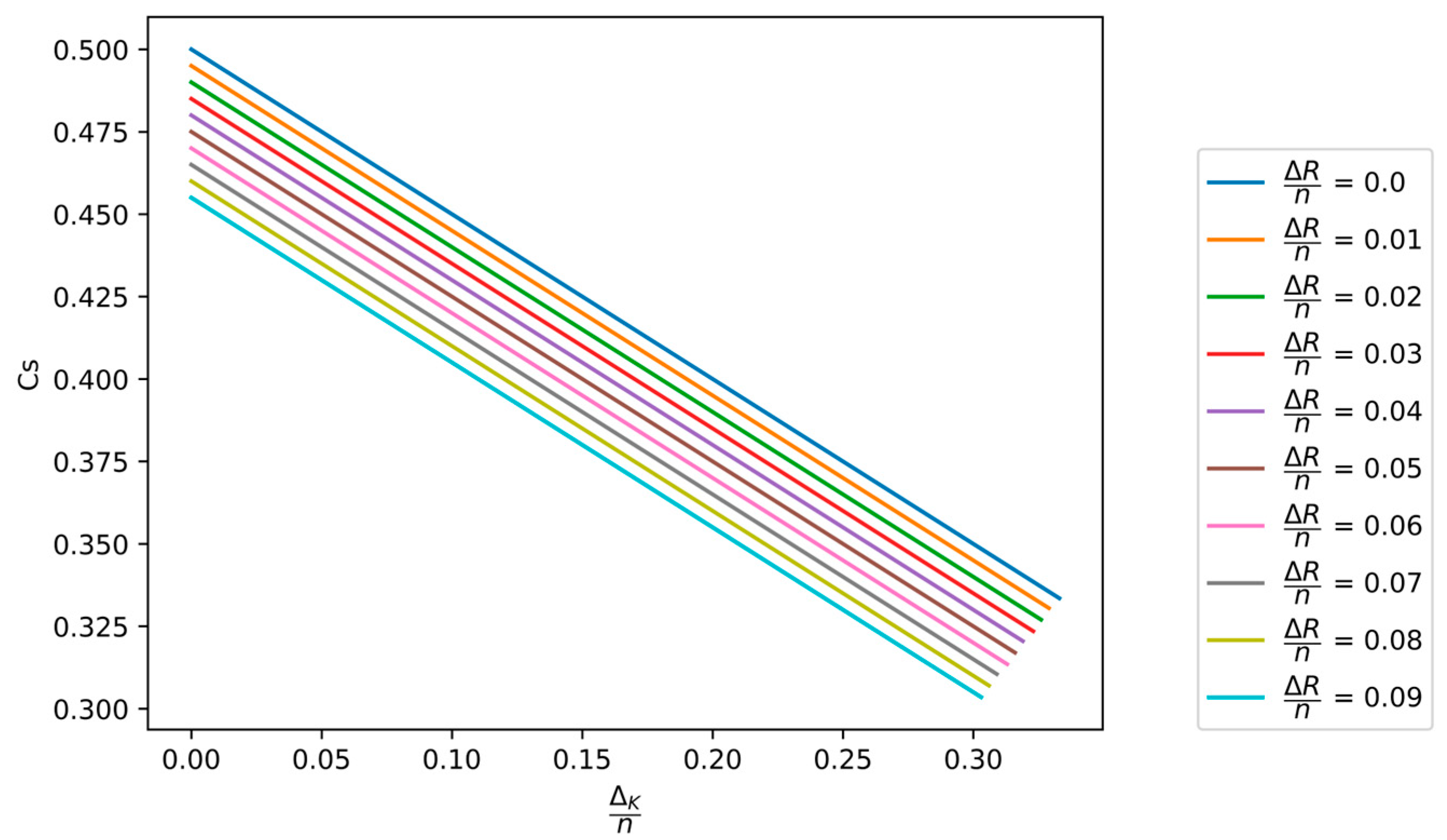
In
Figure 6 and
Figure 7, the dependence of the secrecy capacity
on the normalized minimum value of key equivocation
and the normalized compression rate
of the hash function applied in the PA process is shown.
Note that if the security margins and are fixed constants, then based on Theorem 6, we conclude that holds, which is the maximum possible value of the secret capacity of ISAR system.
The presented theoretical offer an effective methodology for synthesizing this class of systems with predetermined security margins.
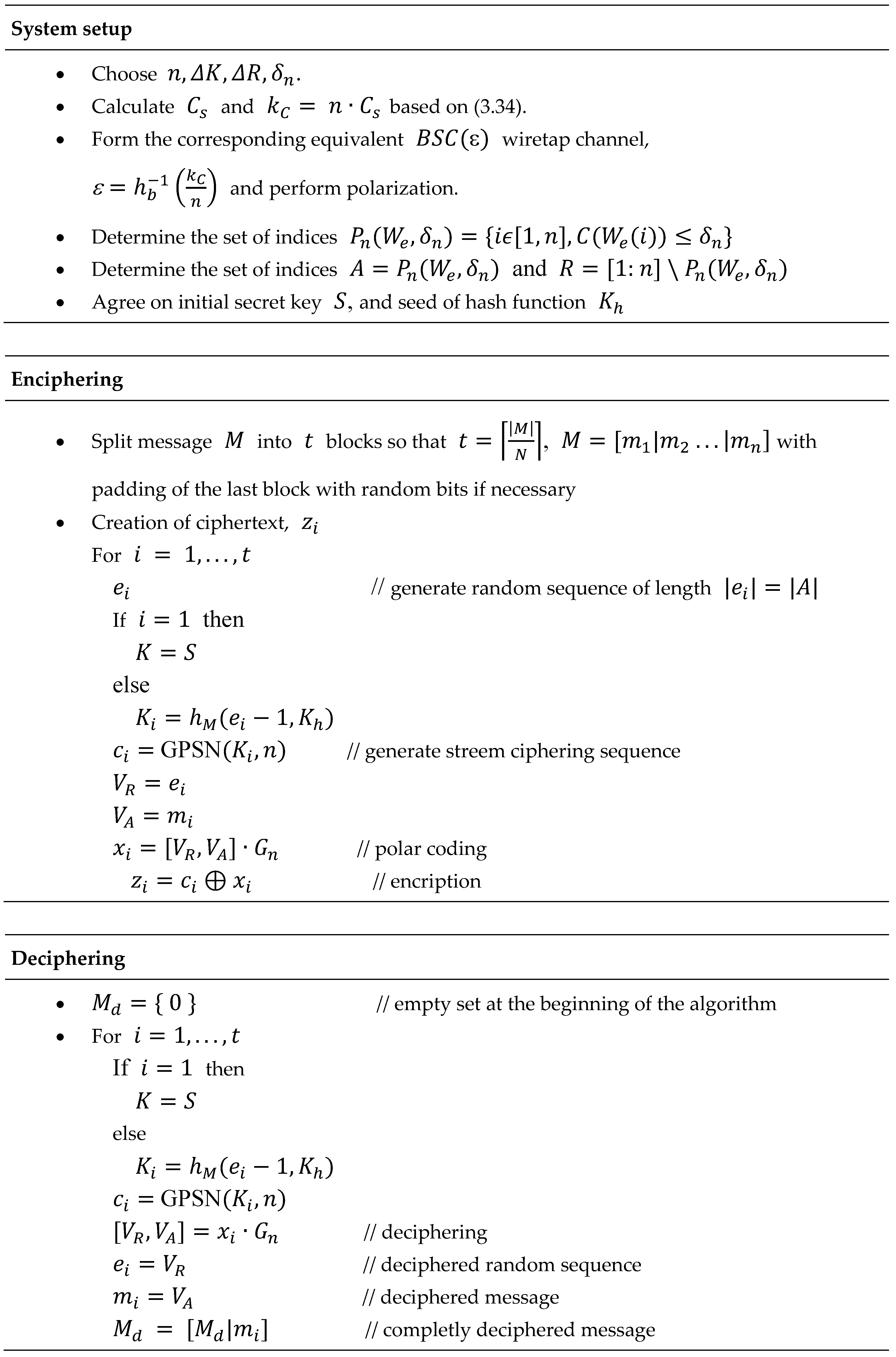
Table 2 outlines the algorithms for configuring the ISAR system and for enciphering/deciphering messages of arbitrary length. Based on the initial values of parameters
and
, the secrecy capacity
and the length of the secret key
are determined. If these parameters are acceptable, the synthesis of the corresponding wiretap polar code proceeds. Identifying the index sets
and
, requires the polarization of the wiretap channel. For practical purposes, it is simpler to replace this channel with an equivalent
channel of the same capacity. Consequently, the crossover probability must satisfy the condition
where
is the binary entropy function, and
is its inversion. The polarization procedure under SC decoding can be performed using various methods, such as Monte-Carlo [
30], Density Evolution (DE) [
41,
42], DE with Gaussian Approximation (GA) [
43], among others. In the ISAR system, where the wiretap channel is designed by the system developer, all essential parameters for the wiretap channel are much more accessible and accurately estimated compared to a scenarios involving real wiretap channels. For instance, when determining the Bhattacharyya parameters
using the Monte-Carlo method for polarization, generating an ensemble of wiretap channel output samples is manageable. This process is facilitated by the precise knowledge of the crossover probability (69), allowing for accurate assessment of the results.
Remark 6.
Let's compare the proposed ISAR system with a classic ideal cipher system that has the same minimal key equivocation value for the same length of observed ciphertext. To ensure a fair comparison, we will assume that the entropy of the input messages is identical in both systems. After encrypting blocks of messages, and assuming the blocks are independent, the ISAR system has a total equivocation of all applied keys equal to
since the formation of each block in the polar code is independent of the previously formed blocks, a classic ideal cipher system with secret key
under the same conditions and for the same length of ciphertext, has an equivocation given by
Equating (71) and (72) yields the condition that
that is,
assumed that all secret keys in both systems have maximum entropy.
To ensure that a classic encryption system achieves the same lower bound on key equivocation as the ISAR system for a given ciphertext length, it would need a secret key t-times longer than the key length of the GPSN(
), see
Figure 8. Additionally,
must be pre-distributed to legitimate parties. The length of this key scales linearly with the message length
, specifically with
. In contrast, the proposed ideal autonomous system requires only a fixed-length secret key K, independent of the message length, and necessitates only an initial exchange of the key values
. Therefore, the benefits of the ISAR system become more significant as the length of the messages increases.
Remark 7. The ISAR system can be obtained by a suitable transformation of any given stream ciphering system GPSN() with a known secret key length . The procedure includes the following steps:
-
Based on the expression (62) for the given value of the length of the secret key , we can directly obtain the required length of the polar code, i.e.,
Since the length of the polar code must be a power of 2, it is necessary to correct (75) to the value
The corrected value of the length of the polar code block (76) allows the eventual correction of the total security margin to the new value
bearing in mind the limitation
Since all elements for ISAR system setup are available in this step, i.e., , further operation of the system takes place according to the algorithm from Table 2.
4. Security Analysis of ISAR Ciphering System
In the following analysis, we will focus on the examination of passive attacks on the system. This implies that the attacker has access to the output of the wiretap channel and all information related to the architecture and operation of the system, except for the initial value and the seed of the chosen hash function Based on the primary objective of the attack, we can distinguish three types: message attacks, attacks on locally generated random sequences, and attacks on the secret key.
4.1. Message Attacks
In this type of attack, Eve attempts to obtain the message in each block based on the observation of the wiretap channel output .
According to Theorem 2, the proposed system satisfies the strong security criterion (32), which means that asymptotically, with an increase in the codeword length , Eve can only acquire a negligible amount of information about the messages .
4.2. Attacks on Locally Generated Random Sequences
In this type of attack, Eve first tries to obtain one of the random sequences locally generated by Alice based on the observation of the wiretap channel outputs . In the second step, using some obtained value , Alice could potentially generate the correct secret key for the next block . Knowing the secret key for block , Eve could successfully decode all subsequent blocks, thereby obtaining all messages in the sequence . However, this scenario is not feasible. The first step cannot be realized since, according to Remark 3.2, the average block error probability on Eve's side is close to maximal (see (44)). The second step is not possible without knowing the seed of the chosen hash function As the success of this attack depends on the success of both steps, this type of attack is practically unfeasible because the overall difficulty of the attack is equal to the product of the difficulties of both steps.
4.3. Attacks on the Secret Key GPSN()
A far more powerful cryptanalytic attack than an attack on individual messages is an attack on the secret key of the GPSN. If Eve were to obtain the secret key
in block
where
, she would be able to access message
, the random sequence
, and consequently the secret key
for the next block. This would allow her to repeat the same process for each subsequent block, thereby gaining access to all subsequent transmitted messages
, random sequenced
and generated secret keys
From the system designer's perspective, it is crucial to prevent this scenario. The information-theoretic quantity that quantifies the likelihood of such an attack is the equivocation of the secret keys for a given wiretap channel output. As the ISAR system is ideally secure, its secret key equivocation, according to (66), never falls below the value
, which is the security parameter in the synthesis process of ISAR. Therefore, the system designer can render this attack unsuccessful with any chosen margin of security. It is important to note that increasing the margin of security leads to a reduction in the secrecy capacity of ISAR (see Theorem 6 and
Figure 7).
Example To understand the order of magnitude of the difficulty of executing this attack, let us consider a typical example of ISAR with parameters (expressed in bits) . According to (62), , and the key length is bits. Let’s assume that Eve’s optimal strategy for each block of the polar wiretap code reaches the lower bound of equivocation of 100 bits of the key. This means that Eve cannot resolve this uncertainty in any way. Recall that in a brute force attack examining all possible keys, all decrypted messages would be equally likely and valid as potential final solutions.
The above example shows that for the polar code length n of order
, the key length of GPSN(
) is of order
. These lengths are not common for commercial stream ciphering systems. However, this does not mean that such systems cannot be relatively easily upgraded to the required key lengths. As an example, we cite a generic model of a pseudo-random generator described in [
44]. If the address and selection sequences are chosen so that they are the outputs of two multiple linear shift registers, then the lengths of the equivalent secret key of this pseudo-random generator can easily be set in ranges of order
.
6. Conclusions
In this paper, we introduced a class of symmetric ciphering systems termed ISAR (Ideally Secret Autonomous Robust) systems. These systems are designed to provide ideal secrecy, autonomy in key generation and distribution, and robustness to the probabilistic structure of messages. These systems address the longstanding challenge in cryptography of balancing security with practicality, particularly by eliminating the need for lengthy secret keys and additional key distribution infrastructure. By ensuring a predetermined minimum value of key equivocation and continuous key refreshing, ISAR systems provide robust security against passive attacks on both keys and messages.
Our work demonstrates that ISAR systems can be applied to any existing symmetric stream ciphering system without requiring changes to the original encryption algorithm, thus offering a versatile and efficient solution for enhancing the security of current cryptographic practices. This transformation greatly supports privacy, a critical requirement for modern security systems.
Overall, the ISAR system represents an advancement in cryptographic security, offering an efficient methodology for creating ciphering systems with predetermined security margins. Future research directions include exploring further optimizations in the ISAR architecture, extending its applicability to a broader range of cryptographic scenarios, and investigating additional techniques for enhancing its resistance to more sophisticated attack vectors. The continued development of ISAR systems holds the promise of ensuring stronger privacy and security measures in an increasingly digital world.
Author Contributions
Conceptualization, M.M.; methodology, M.M., T.U., J.R.; software, J.R.; validation, M.M., J.R., B.B.; formal analysis, M.M., J.R., T.U.; investigation, M.M., J.R.; resources, B.B.; data curation, J.R., B.B.; writing—original draft preparation, M.M., J.R.; writing—review and editing, M.M., J.R.; visualization, M.M., J.R.; supervision, M.M., B.B.; project administration, J.R.; funding acquisition, B.B. All authors have read and agreed to the published version of the manuscript.