Submitted:
16 July 2024
Posted:
17 July 2024
You are already at the latest version
Abstract
Keywords:
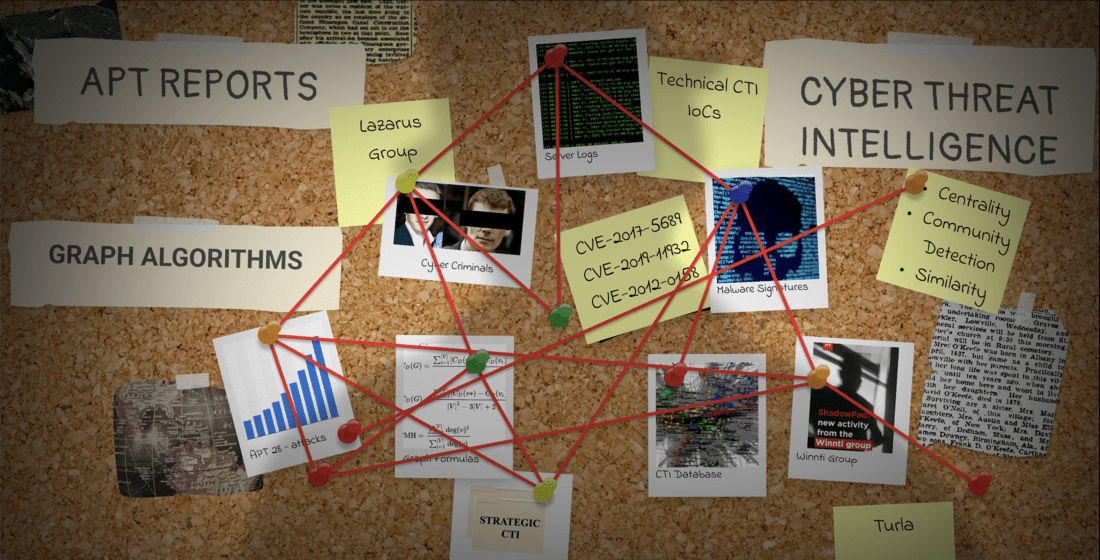
1. Introduction
- We proposed a system architecture to collect APT-related analysis reports from open-source intelligence (OSINT) sources. Synthetic datasets are not used.
- We produced a weighted graph to strengthen the impact of the most encountered data. This helped us to produce strategic CTI.
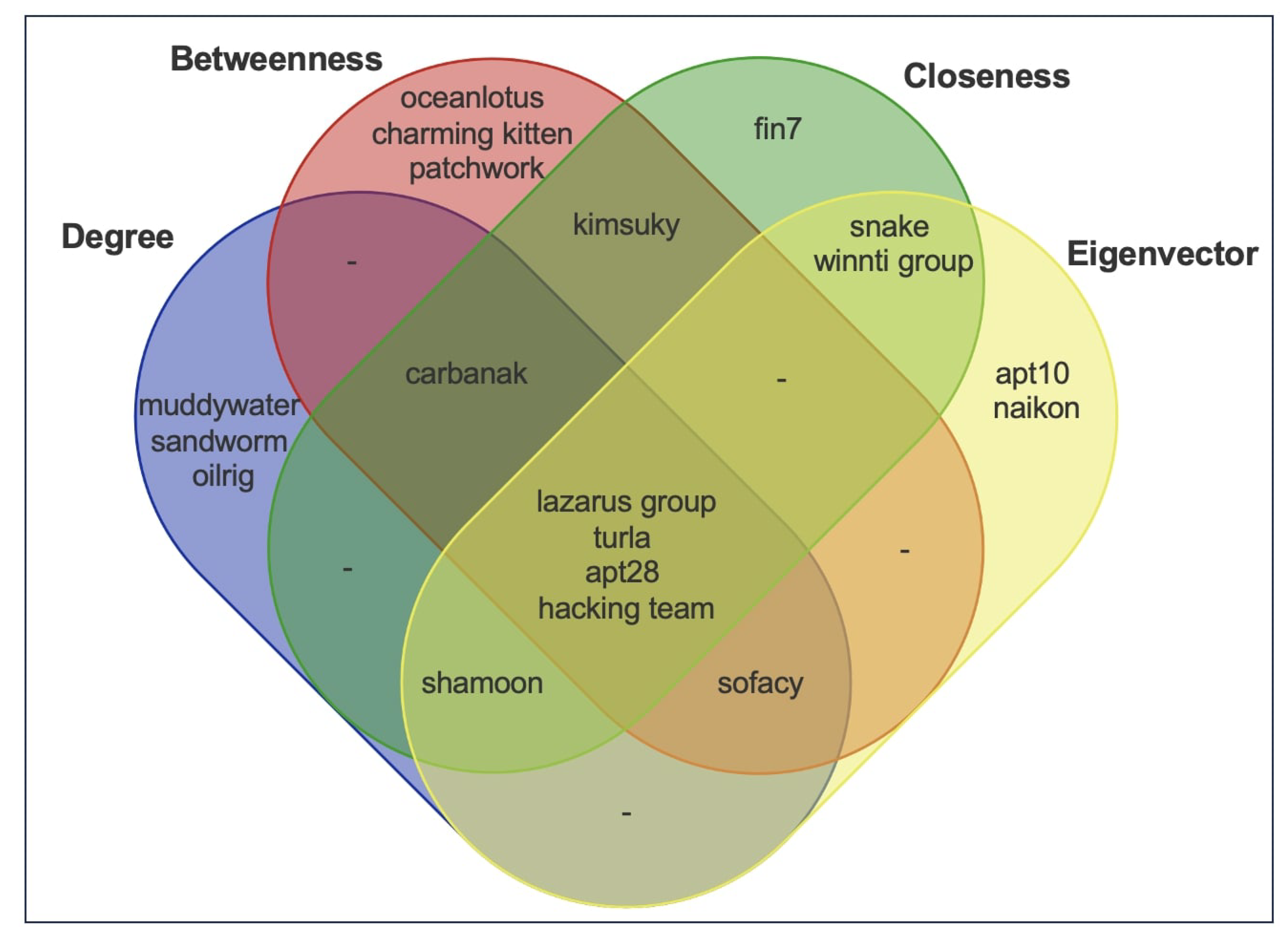
- We discovered the most influential IoCs and APT groups on the graph of CTI using centrality analysis. These nodes were also the most bridging nodes playing central roles in different attacks.
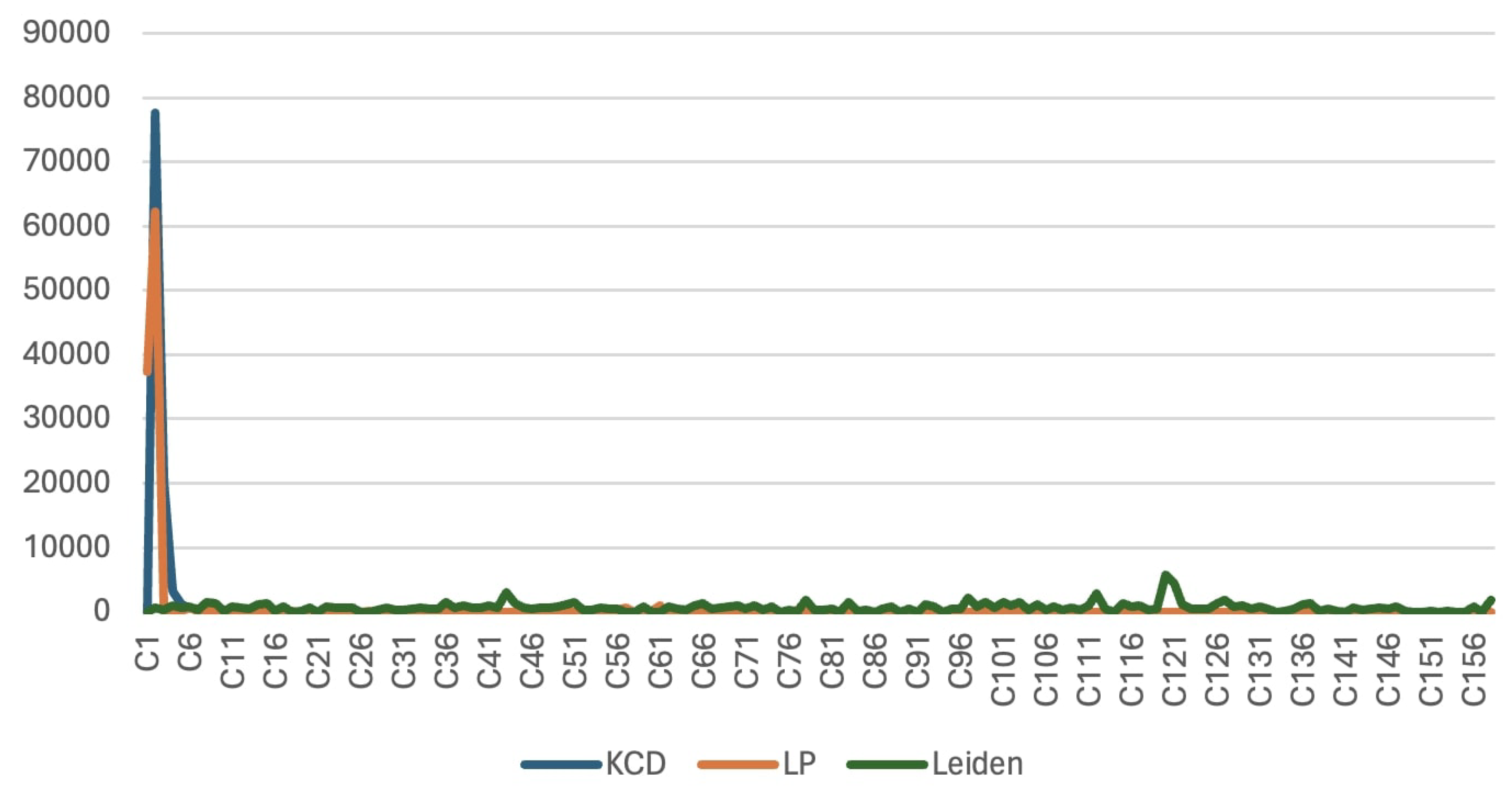
- We detected communities of APT actors who seem to be acting together and have similar malicious activities using community detection techniques.
- We exposed similar APT attacks with too much common technical and tactical CTI knowledge using graph-based similarity analysis techniques.
- We created a systematic and empirical methodology to produce strategic CTI from technical and tactical CTI by processing APT analysis reports.
2. Background and Related Works
2.1. Centrality Analysis
2.2. Community Detection Analysis
2.3. Similarity Analysis
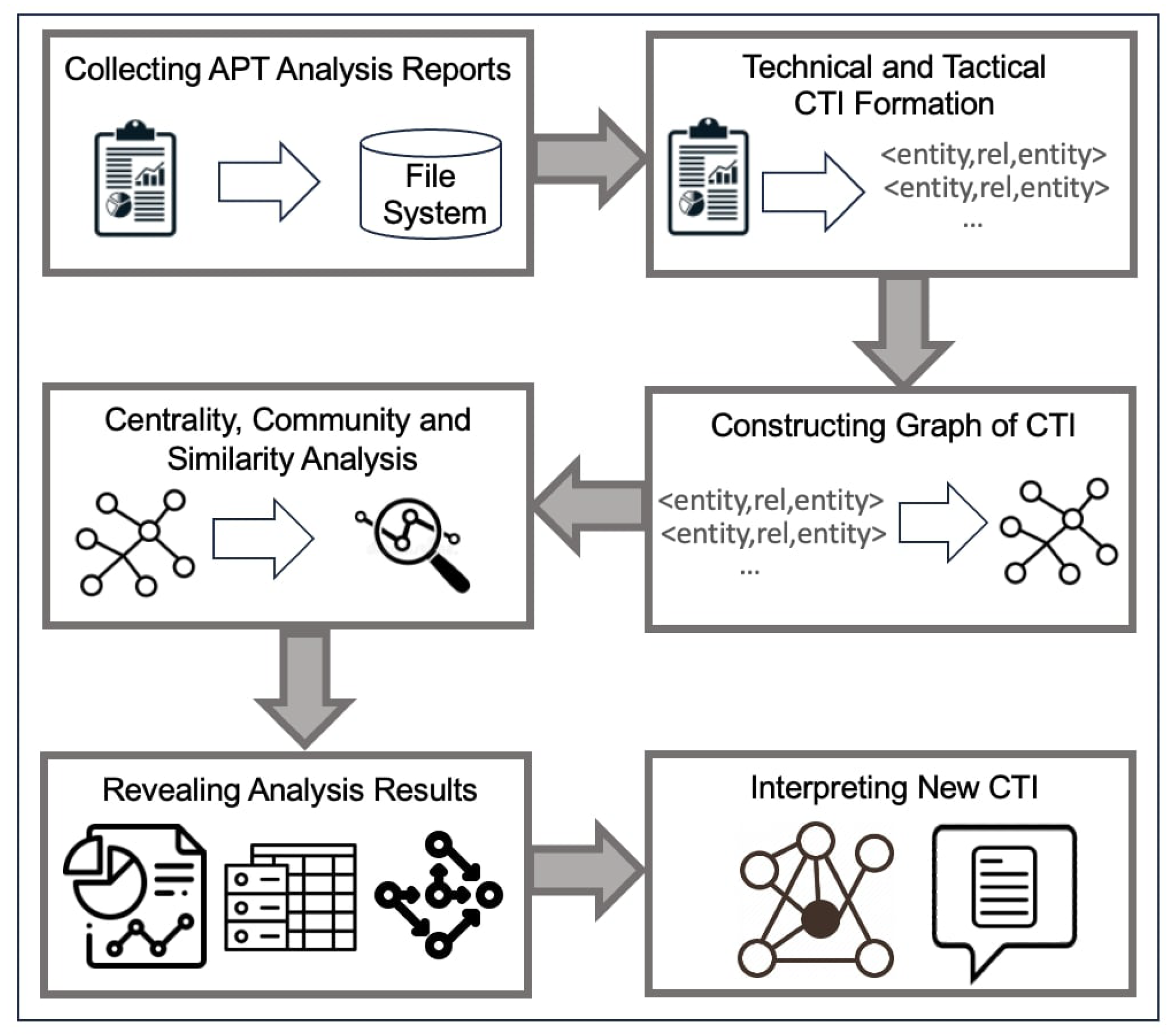
3. Proposed Methodology
- Data Collection Stage: A widely inclusive APT report corpus is built using open-source repositories.
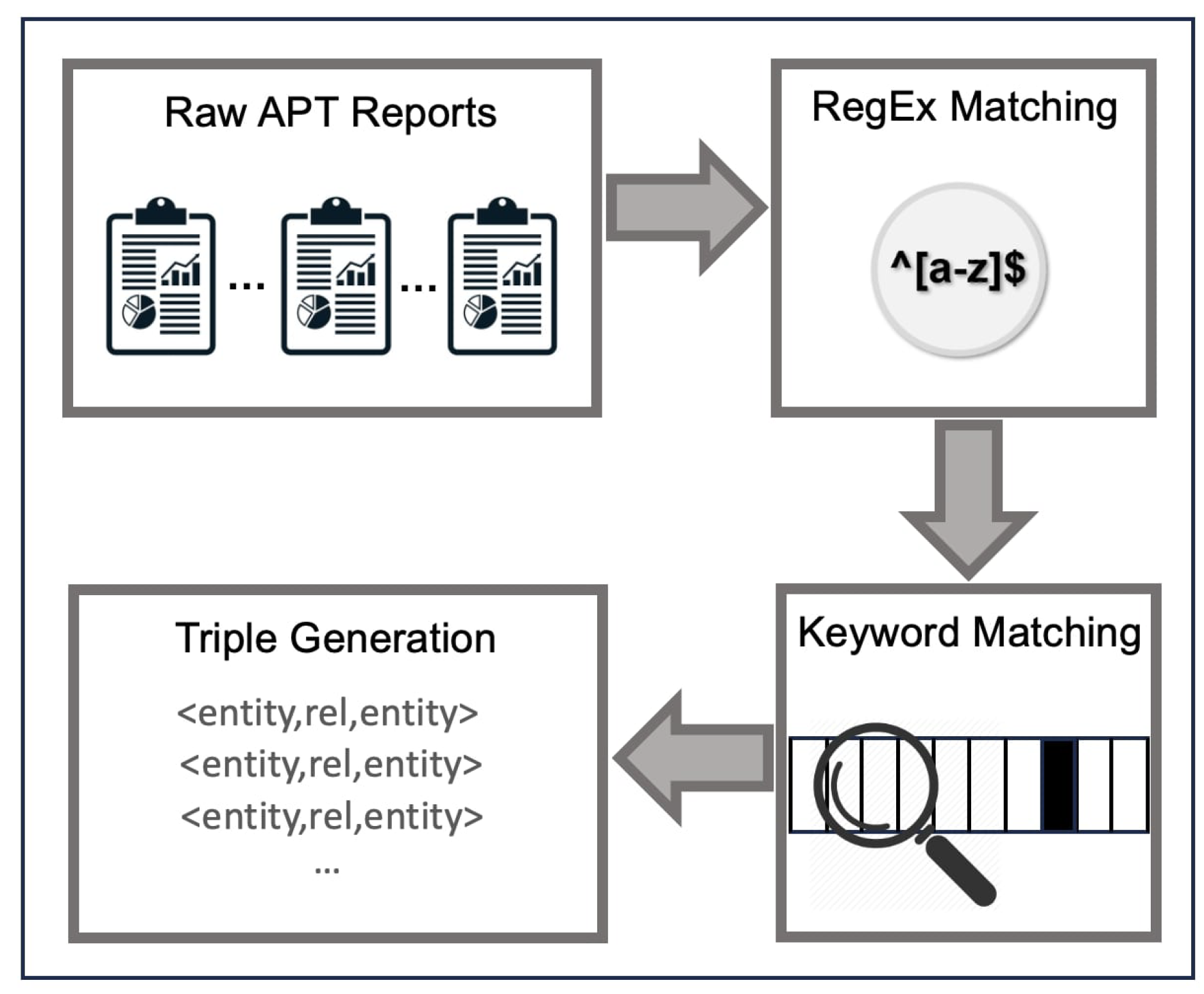
- Knowledge Extraction Stage: APT analysis reports are scanned to recognize IoCs and other contextual entities like malwares, APT groups, and countries.
- Graph Generation Stage: Using previously extracted CTI knowledge, a graph of nodes and edges is formed.
- Graph Analysis Stage: The most influential APT groups and IoCs are detected. Results are interpreted in the context of APT attacks.
- Gathering Analysis Results: Numerical analysis results are captured in this stage. Outputs of applied algorithms needed to be interpreted.
- Interpreting Analysis Results: Outputs of applied algorithms were interpreted in this stage. Generated scores at the previous stage needed more contextual explanation. The most remarkable output of the stage was strategic CTI generated for long-term usage.
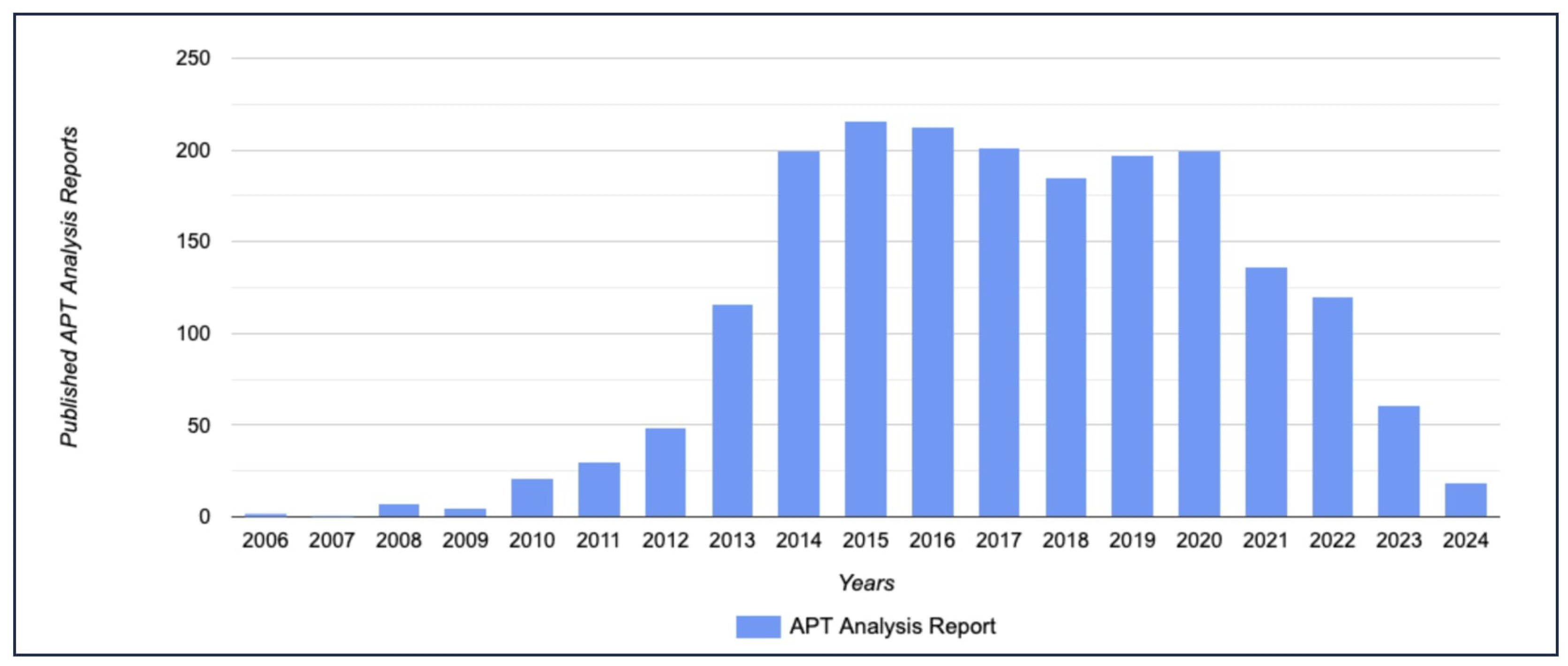
3.1. Collecting APT Analysis Reports
3.2. Technical and Tactical CTI Formation
3.3. Constructing Graph of CTI
3.4. Centrality, Community and Similarity Analysis on Graph of CTI
3.4.1. Centrality Analysis of APT Group and IoC Nodes
- s stands for source vertex, t stands for target vertex and for each pairs , compute the shortest paths between s and t.
- For each pairs, calculate the fraction of shortest paths that pass through the current vertex v.
- Sum the calculated fraction for all pairs.
3.4.2. Community Detection on Graph of CTI
| Algorithm 1 Pseudo-code implementation of k-core decomposition. The input to the algorithm is a graph G consisting of a set of nodes V and a set of edges E. The output of the algorithm is core number for each node in V. |
|
| Algorithm 2 Pseudo-code implementation of Label Propagation algorithm. The input to the algorithm is a graph G consisting of a set of nodes V and a set of edges E. The output of the algorithm is final community labels for each node in V. |
|
| Algorithm 3 Pseudo-code implementation of the Leiden algorithm. The input to the algorithm is a graph G consisting of a set of nodes V and a set of edges E. The output of the algorithm is the final community labels for each node in V. |
|
3.4.3. Similarity Analysis of APT Attacks
4. Evaluation of Proposed Framework and Experiments
4.1. Examining Analyses Results in the CTI Context
- gold lowell, topgear
- unc2643, iamtheking
- hurricane panda, playful dragon, nightshade panda, anchor panda, tg-6952
- shell crew, brownfox, group 35, group 13, potassium, pinkpanther, shanghai group, kungfu kittens
- menupass team, cvnx, red apollo
4.2. Formation and Interpretation of the Strategic CTI
- By considering Table 1, threat hunting is critical since dwell time can be dramatically decreased with internal detection efforts. Even though external CTI feeds are effective in gaining confidence about cyber attacks, organizations must accept that external notifications are not enough to evade targeted APT attacks. Organizations had better invest in intrusion detection systems (IDS), endpoint detection and response (EDR) solutions, and threat hunting activities rather than relying solely on external CTI feeds.
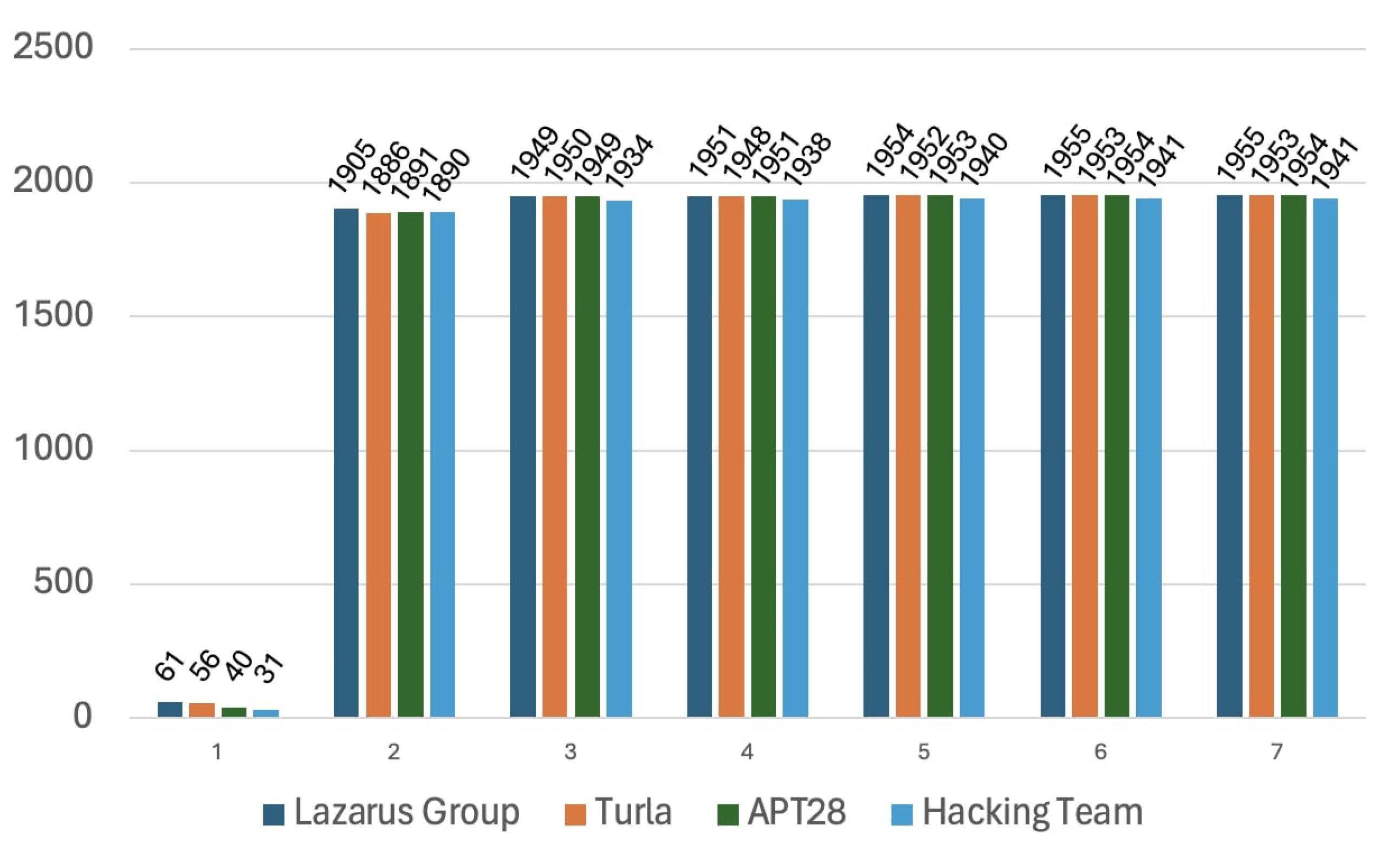
- Lazarus Group, Turla, APT 28, and Hacking Team APT groups have the highest centrality measurements. It has been believed that the Lazarus Group originates from North Korea, Turla and APT 28 from Russia, and the Hacking Team from Italy [85]. The most active APT groups are not attributed to a single country. We believe that international developments and political tensions targeting these countries may trigger corresponding threat actors. The existence of an APT group also causes the formation of an opposing force.
- According to Table 15, Trojans and RATs were the top encountered malware types. This indicates that file-borne attack vectors are the most practical and impactful. Organizations must utilize proxy servers to pass client requests and responses through the Internet content adaptation protocol (ICAP) servers. By using an ICAP server, virus scanning on files in front lines provides proactive protection. Defending the systems against email attachments and file-based contents is a strategic decision to prevent further attacks.
- The most influential malware families were Mimikatz, PlugX, Mimic, and Rogue. Mimikatz is an open-source credential dumping program to obtain account login and password information. PlugX is a remote administration tool (RAT). Mimic is ransomware-type malware. Rogue is a fake malware removal tool. All of the said malwares reached its goals by deceiving end users. We want to emphasize the importance of cybersecurity awareness training. Investing in human capital is significantly more cost-effective than covering the damage caused by APT attacks.
- According to Table 16, Iran plays a key role in APT landscape as a country. This situation might be due to Iran being the attacked country, the starting point of the attacks, or a transit point for the attacks. Organizations might pay attention for incoming and outgoing network traffic related to IP blocks of Iran.
5. Conclusions and Future Research
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| APT | Advanced Persistent Threat |
| TTP | Tactics, Techniques, Procedures |
| CTI | Cyber Threat Intelligence |
| IoC | Indicators of Compromise |
| IP | Internet Protocol |
| URL | Uniform Resource Locator |
| SOC | Security Operations Center |
| OSINT | Open Source Intelligence |
| CPS | Cyber-Physical Systems |
| IoC | Internet of Things |
| BiLSTM | Bidirectional Long Short-Term Memory |
| GCN | Graph Convolutional Networks |
| DC | Degree Centrality |
| BC | Betweenness Centrality |
| CC | Closeness Centrality |
| EC | Eigenvector Centrality |
| KCD | K-Core Decomposition |
| LP | Label Propagation |
| ATT&CK | Adversarial Tactics, Techniques, and Common Knowledge |
| MD5 | Message Digest Method 5 |
| SHA-1 | Secure Hash Algorithm 1 |
| SHA-256 | Secure Hash Algorithm 256-bit |
| C2 | Command and Control |
| RegEx | Regular Expression |
| CVE | Common Vulnerabilities and Exposures |
| IDS | Intrusion Detection System |
| EDR | Endpoint Detection and Response |
| RAT | Remote Administration Tool |
| ICAP | Internet Content Adaptation Protocol |
References
- Alshamrani, A.; Myneni, S.; Chowdhary, A; Huang, D. A Survey on Advanced Persistent Threats: Techniques, Solutions, Challenges, and Research Opportunities. IEEE Communications Surveys & Tutorials 2019, 21, pp–1851. [Google Scholar] [CrossRef]
- Yan, D.; Liu, F.; Jia, K. Modeling an Information-Based Advanced Persistent Threat Attack on the Internal Network. IEEE International Conference on Communications (ICC) 2019, 1–7. [Google Scholar] [CrossRef]
- Ruohonen, S.; Kirichenko, A.; Komashinskiy, D.; Pogosova, M. Instrumenting OpenCTI with a Capability for Attack Attribution Support. Forensic Sciences. 2024, 4, pp–12. [Google Scholar] [CrossRef]
- Alzahrani, I.Y.; Lee, S.; Kim, K. Enhancing Cyber-Threat Intelligence in the Arab World: Leveraging IoC and MISP Integration. Electronics. 2024, 13, 2526. [Google Scholar] [CrossRef]
- Cho, J.; Gong, S. Dynamic Data Abstraction-Based Anomaly Detection for Industrial Control Systems. Electronics. 2024, 13, 158. [Google Scholar] [CrossRef]
- Duary, S.; Choudhury, P.; Mishra, S.; Sharma, V.; Rao, D. D.; Adedapo P., A. Cybersecurity Threats Detection in Intelligent Networks using Predictive Analytics Approaches. International Conference on Innovative Practices in Technology and Management (ICIPTM). 2024, 4, pp–1. [Google Scholar] [CrossRef]
- Hasan, K.; Shetty, S.; Islam, T.; Ahmed, I. Predictive Cyber Defense Remediation against Advanced Persistent Threat in Cyber-Physical Systems. International Conference on Computer Communications and Networks (ICCCN) 2022, 1–10. [Google Scholar] [CrossRef]
- Kao, D.-Y. Performing an APT Investigation: Using People-Process-Technology-Strategy Model in Digital Triage Forensics. IEEE 39th Annual Computer Software and Applications Conference. 2015, 3, pp–47. [Google Scholar] [CrossRef]
- Bhardwaj, A.; Kaushik, K.; Alomari, A.; Alsirhani, A.; Alshahrani, M.M.; Bharany, S. BTH: Behavior-Based Structured Threat Hunting Framework to Analyze and Detect Advanced Adversaries. Electronics, 2022, 11, 2992. [Google Scholar] [CrossRef]
- Gan, C.; Lin, J.; Huang, D.-W.; Zhu, Q.; Tian, L. Advanced Persistent Threats and Their Defense Methods in Industrial Internet of Things: A Survey. Mathematics, 2023, 11, 3115. [Google Scholar] [CrossRef]
- Hughes, C.; Robinson, N. Vulnerability Threat Intelligence. In Effective Vulnerability Management: Managing Risk in the Vulnerable Digital Ecosystem; 1st edn.; John Wiley & Sons: Hoboken, NJ, USA, 2024; pp. 145–154. [Google Scholar]
- Fischer, D.; Sauerwein, C.; Werchan, M.; Stelzer, D. An Exploratory Study on the Use of Threat Intelligence Sharing Platforms in Germany, Austria and Switzerland. International Conference on Availability, Reliability and Security, 2023, 8, pp–1. [Google Scholar] [CrossRef]
- Kim, B.; Kim, N.; Lee, S.; Cho, H.; Park, J. A Study on a Cyber Threat Intelligence Analysis (CTI) Platform for the Proactive Detection of Cyber Attacks Based on Automated Analysis. International Conference on Platform Technology and Service (PlatCon) 2018, 1–6. [Google Scholar] [CrossRef]
- Leong, Y. The Implementation of Strategic Threat Intelligence for Business Organization. Journal of IT in Asia, 2021, 9, pp–41. [Google Scholar] [CrossRef]
- Liu, J.; Zhan, J. Constructing Knowledge Graph from Cyber Threat Intelligence Using Large Language Model. IEEE International Conference on Big Data (BigData), 2023; 516–521. [Google Scholar] [CrossRef]
- Gao, Y.; Li, X.; Peng, H.; Fang, B.; Yu, P. S. HinCTI: A Cyber Threat Intelligence Modeling and Identification System Based on Heterogeneous Information Network. IEEE Transactions on Knowledge and Data Engineering, 2022, 34, pp–708. [Google Scholar] [CrossRef]
- Nazari, H.; Yazdinejad, A.; Dehghantanha, A.; Zarrinkalam, F.; Srivastava, F. arXiv—P3GNN: A Privacy-Preserving Provenance Graph-Based Model for APT Detection in Software Defined Networking. 17 Jun 2024. Available online: https://arxiv.org/abs/2406.12003 (accessed on 30 Jun 2024).
- Zhou,F.; Chang,B.; Wen, Y.; Meng, D. ProDE: Interpretable APT Detection Method Based on Encoder-decoder Architecture. IEEE 29th International Conference on Parallel and Distributed Systems (ICPADS) 2023, 340–347. [CrossRef]
- Ren, Y.; Xiao, Y.; Zhou, Y.; Zhang, Z.; Tian, Z. CSKG4APT: A Cybersecurity Knowledge Graph for Advanced Persistent Threat Organization Attribution. IEEE Transactions on Knowledge & Data Engineering 2023, 35, pp–5695. [Google Scholar] [CrossRef]
- Jung, J.W.; Lee, S.W. Security Requirement Recommendation Method Using Case-Based Reasoning to Prevent Advanced Persistent Threats. Applied Sciences 2023, 13, 1505. [Google Scholar] [CrossRef]
- Li, L.; Chen, W. ConGraph: Advanced Persistent Threat Detection Method Based on Provenance Graph Combined with Process Context in Cyber-Physical System Environment. Electronics 2024, 13. [Google Scholar] [CrossRef]
- Wang, N.; Wen, X.; Zhang, D.; Zhao, X. arXiv—TBDetector:Transformer-Based Detector for Advanced Persistent Threats with Provenance Graph. 6 Apr 2023. Available online: https://arxiv.org/pdf/2304.02838 (accessed on 30 Jun 2024).
- Hangsheng, Z.; Haitao, L.; Jie, L.; Ting, L.; Liru, G.; Yinlong, L.; Shujuan, C. Defense Against Advanced Persistent Threats: Optimal Network Security Hardening Using Multi-stage Maze Network Game. EEE Symposium on Computers and Communications (ISCC). [CrossRef]
- Cho, D.; Nguyen, H.D.; Dao, M.H. APT Attack Detection Based on Flow Network Analysis Techniques Using Deep Learning. Journal of Intelligent and Fuzzy Systems. [CrossRef]
- Lutu, N.; Patricia, E. Using Twitter Mentions and a Graph Database to Analyse Social Network Centrality. 6th International Conference on Soft Computing and Machine Intelligence (ISCMI) 2019, pp. 155–159. [CrossRef]
- RafieeFard, J.; Teimourpour, B. OCRR, A Fast Algorithm for Centrality-Based Graph Reduction in Social Networks. 20th CSI International Symposium on Artificial Intelligence and Signal Processing (AISP) 2024, pp. 1–5. [CrossRef]
- Munir, S.; Malick, R.A.S.; Ferretti, S. A Network Analysis-Driven Framework for Factual Explainability of Knowledge Graphs. IEEE Access 2024,, 11, pp. 28071–28082. , pp. 28071–28082. [CrossRef]
- Bendahman, N.; Lotfi, D. Unveiling Influence in Networks: A Novel Centrality Metric and Comparative Analysis through Graph-Based Models. Entropy 2024, 26, 486. [Google Scholar] [CrossRef]
- Verma, A.K.; Saxena, R.; Jadeja, M.; Bhateja, V.; Lin, J.C.W. Bet-GAT: An Efficient Centrality-Based Graph Attention Model for Semi-Supervised Node Classification. Applied Sciences 2023, 13, 847. [Google Scholar] [CrossRef]
- Ai, J.; Su, Z.; Wang, K.; Wu, C.; Peng, D. Decentralized Collaborative Filtering Algorithms Based on Complex Network Modeling and Degree Centrality. IEEE Access 2020, 8, pp. 151242–151249. [CrossRef]
- Krnc, M.; Škrekovski, R. Group Degree Centrality and Centralization in Networks. Mathematics 2020, 8, 1810. [Google Scholar] [CrossRef]
- Cai, B.; Zeng, L.; Wang, Y.; Li, H.; Hu, Y. Community Detection Method Based on Node Density, Degree Centrality, and K-Means Clustering in Complex Network. Entropy 2019, 21, 1145. [Google Scholar] [CrossRef]
- Powell, J.; Hopkins, M. Graph analytics techniques. In A Librarian’s Guide to Graphs, Data and the Semantic Web; 1st edn.; Chandos Publishing: Hull, East Yorkshire, England, 2015; pp. 167–174. [Google Scholar]
- Umunnakwe, A.; Sahu, A.; Davis, K. Multi-Component Risk Assessment Using Cyber-Physical Betweenness Centrality. IEEE Madrid PowerTech 2021, pp. 1–6. https://10.1109/PowerTech46648.2021. 9494. [Google Scholar]
- Perez, C; Germon, R. Graph Creation and Analysis for Linking Actors: Application to Social Data. In Automating Open Source Intelligence; Layton, R., Watters, P. A. 1st edn.; Syngress: Boston, MA, USA, 2016; pp. 103–129. [Google Scholar]
- Nandini, Y.V.; Lakshmi, T.J.; Enduri, M.K.; Sharma, H. Link Prediction in Complex Networks Using Average Centrality-Based Similarity Score. Entropy, 2024, 26, 433. [Google Scholar] [CrossRef] [PubMed]
- Wu, W.; Wang, S.; Liu, B. Software Fault Localization Based on Weighted Association Rule Mining and Complex Networks. Mathematics, 2113; 12. [Google Scholar] [CrossRef]
- Segarra, S.; Ribeiro, A. Stability and Continuity of Centrality Measures in Weighted Graphs. IEEE Transactions on Signal Processing, 2016, 64, pp–543. [Google Scholar] [CrossRef]
- Zhang, Z.; Wang, J.; Xu, Y. Research on node influence in complex network based on multi-scale centrality algorithm. Procedia Computer Science, 2023, 228, pp–1128. [Google Scholar] [CrossRef]
- Srichandra, I. V.; Bhadra, P. Community Detection Using Graph Attention Networks Clustering Algorithm. IEEE International Conference for Convergence in Technology (I2CT) 2024, 1–6. [Google Scholar] [CrossRef]
- Rajita, B.S.A.S.; Panda, S. Community Detection Techniques for Evolving Social Networks. International Conference on Cloud Computing, Data Science & Engineering 2019, 681–686. [Google Scholar] [CrossRef]
- Gao, S.; Xu, J.; Li, X.; Fu, F.; Zhang, W.; Ouyang, W.; Tao, Y. ; Cui. B. K-Core Decomposition on Super Large Graphs with Limited Resources. arXiv 2021. [Google Scholar] [CrossRef]
- Laishram, R.; Soundarajan, S. On Finding and Analyzing the Backbone of the k-Core Structure of a Graph. IEEE International Conference on Data Mining (ICDM) 2022, 1017–1022. [Google Scholar] [CrossRef]
- Bhatia, V.; Rani, R. An efficient influence based label propagation algorithm for clustering large graphs. International Conference on Infocom Technologies and Unmanned Systems (ICTUS) 2017, 1–7. [Google Scholar] [CrossRef]
- Xie, T.; Wang, B.; Kuo, C.-C. J. GraphHop: An Enhanced Label Propagation Method for Node Classification. IEEE Transactions on Neural Networks and Learning Systems, 2023, 34, pp–9287. [Google Scholar] [CrossRef]
- Blekanov, I.; Bodrunova, S.S.; Akhmetov, A. Detection of Hidden Communities in Twitter Discussions of Varying Volumes. Future Internet, 2021, 13, 295. [Google Scholar] [CrossRef]
- Kadem, B. A.; Al-sultany, G. Enhancing Community Detection Using Maximal and Maximum Cliques into Hierarchical Algorithms. IEEE International Conference on Artificial Intelligence and Mechatronics Systems (AIMS) 2024, 1–6. [Google Scholar] [CrossRef]
- Gupta, S. K.; Singh, D. P. CBLA: A Clique Based Louvain Algorithm for Detecting Overlapping Community. International Conference on Machine Learning and Data Engineering, 2023, 218, pp–2201. [Google Scholar] [CrossRef]
- Dermawan, F.; Kwang, C. H.; Adijanto, M. D.; Rakhmawati, N. A.; Basara, N. R. Product Recommendations through Neo4j by Analyzing Patterns in Customer Purchases. International Conference in Emerging Technologies for Sustainability and Intelligent Systems, 2024; 1–4. [Google Scholar] [CrossRef]
- Edie, K.; Mckee, C.; Duby, A. Extending Threat Playbooks for Cyber Threat Intelligence: A Novel Approach for APT Attribution. 11th International Symposium on Digital Forensics and Security, 2023; 1–6. [Google Scholar] [CrossRef]
- Chachoo, M. A. Social Network Analysis Based Criminal Community Identification Model with Community Structures and Node Attributes. 4th International Conference on Smart Systems and Inventive Technology, 2022; 334–339. [Google Scholar] [CrossRef]
- Kim, H. M.; Song, H. M.; Seo, J. W.; Kim, H. K. Andro-Simnet: Android Malware Family Classification using Social Network Analysis. 16th Annual Conference on Privacy, Security and Trust, 2018; 1–8. [Google Scholar] [CrossRef]
- Shoeibi, N.; Shoeibi, N.; Chamoso, P.; Alizadehsani, Z.; Corchado, J.M. A Hybrid Model for the Measurement of the Similarity between Twitter Profiles. Sustainability, 2022, 14, 4909. [Google Scholar] [CrossRef]
- Haque, M. A.; Shetty, S.; Kamhoua, C. A.; Gold, K. Adversarial Technique Validation & Defense Selection Using Attack Graph & ATT&CK Matrix. International Conference on Computing, Networking and Communications, 2023; 181–187. [Google Scholar] [CrossRef]
- Desku, A.; Raufi, B.; Luma, A.; Selimi, B. Cosine Similarity through Control Flow Graphs For Secure Software Engineering. International Conference on Engineering and Emerging Technologies, 2021; 1–4. [Google Scholar] [CrossRef]
- Adamic, L.A.; Adar, E. Friends and neighbors on the web. Social Networks. 2003, 25, pp–211. [Google Scholar] [CrossRef]
- Nandini, Y.V.; Lakshmi, T.J.; Enduri, M.K.; Sharma, H. Link Prediction in Complex Networks Using Average Centrality-Based Similarity Score. Entropy 2024, 26, 433. [Google Scholar] [CrossRef] [PubMed]
- Chalkiadakis, G.; Ziogas, I.; Koutsmanis, M.; Streviniotis, E.; Panagiotakis, C.; Papadakis, H. A Novel Hybrid Recommender System for the Tourism Domain. Algorithms, 2023, 16, 215. [Google Scholar] [CrossRef]
- Azevedo, R.; Medeiros, I.; Bessani, A. PURE: Generating Quality Threat Intelligence by Clustering and Correlating OSINT. 18th IEEE International Conference On Trust, Security And Privacy In Computing And Communications, 2019; 483–490. [Google Scholar] [CrossRef]
- Hofer-Schmitz, K.; Kleb, U.; Stojanović, B. The Influences of Feature Sets on the Detection of Advanced Persistent Threats. Electronics 2021, 10, 704. [Google Scholar] [CrossRef]
- Maglaras, L.; Ferrag, M. A.; Derhab, A.; Mukherjee, M.; Janicke, H.; Rallis, S. Threats, Countermeasures and Attribution of Cyber Attacks on Critical Infrastructures. EAI Endorsed Transactions on Security and Safety 2018, 5. [Google Scholar] [CrossRef]
- Baghirov, E. Techniques of Malware Detection: Research Review. 15th International Conference on Application of Information and Communication Technologies (AICT) 2021. [Google Scholar] [CrossRef]
- Goel, N.; Sethi, N. Cyber Threat Intelligence: a Survey on Progressive Techniques and Challanges. International Conference on Big Data, IoT, Cyber Security and Information Technology, 2022, 13, 65–70. [Google Scholar]
- Tatam, M.; Shanmugam, B.; Azam, S.; Kannoorpatti, K. A review of threat modelling approaches for APT-style attacks. Heliyon, 2021, 7, 1–19. [Google Scholar] [CrossRef] [PubMed]
- MITRE ATT&CK Framework. Available online: https://attack.mitre.org/.
- Caballero, J.; Gomez, G.; Matic, S.; Sánchez, G.; Sebastián, S.; Villacañas, A. The Rise of GoodFATR: A Novel Accuracy Comparison Methodology for Indicator Extraction Tools. Future Generation Computer Systems 2023, 7, pp–74. [Google Scholar] [CrossRef]
- APT Groups and Operations. Available online: https://docs.google.com/spreadsheets/d/1H9_xaxQHpWaa4O_Son4Gx0YOIzlcBWMsdvePFX68EKU/edit?gid=1864660085#gid=1864660085 (accessed on 1 July 2024).
- Malpedia Malware Families. Available online: https://malpedia.caad.fkie.fraunhofer.de/families (accessed on 1 July 2024).
- MITRE Att&ck Enterprise, Mobile and ICS Techniques. Available online: https://attack.mitre.org/techniques/enterprise (accessed on 1 July 2024).
- Yan, D.; Wu, T.; Liu, Y.; Gao, Y. An efficient sparse-dense matrix multiplication on a multicore system. 17th International Conference on Communication Technology, 2017; 1880–1883. [Google Scholar] [CrossRef]
- Borgatti, S.; Everett, M. A Graph-Theoretic Perspective on Centrality. Social Networks , 2006, 28, 466–484. [Google Scholar] [CrossRef]
- Freeman, L. A Set of Measures of Centrality Based on Betweenness. Sociometry, 1977, 40, 35–41. [Google Scholar] [CrossRef]
- Brandes, U. A faster algorithm for betweenness centrality. Journal of Mathematical Sociology, 2004, 25, 163–177. [Google Scholar] [CrossRef]
- Bavelas, A. Communication patterns in task-oriented groups. The Journal of the Acoustical Society of America, 1950, 22, 725–730. [Google Scholar] [CrossRef]
- Negre, C.F.A.; Morzan, U.N.; Hendrickson, H.P.; Pal, R.; Lisi, G.P.; Loria, J.P.; Rivalta, I.; Ho, J.; Batista, V.S. Eigenvector Centrality for Characterization of Protein Allosteric Pathways. The Proceedings of the National Academy of Sciences (PNAS), 2018, 115, pp–12201. [Google Scholar] [CrossRef]
- Newman, M.E.J. The mathematics of networks. The New Palgrave Encyclopedia of Economics, 2008, 2, 1–12. [Google Scholar] [CrossRef]
- Kabir, H.; Madduri, K. Parallel k-Core Decomposition on Multicore Platforms. IEEE International Parallel and Distributed Processing Symposium Workshops, 2017; 1482–1491. [Google Scholar] [CrossRef]
- Dasari, N. S.; Desh, R.; Zubair, M. ParK: An efficient algorithm for k-core decomposition on multicore processors. IEEE International Conference on Big Data, 2014; 9–16. [Google Scholar] [CrossRef]
- Raghavan, N.; Albert, R.; Kumara, S. Near Linear Time Algorithm to Detect Community Structures in Large-Scale Networks. Physical Review E, 2007, 76, 2375–2387. [Google Scholar] [CrossRef] [PubMed]
- Traag, V.; Waltman, L.; and van Eck, N. J. From Louvain to Leiden: Guaranteeing Well-Connected Communities. Scientific Reports, 2019, 9, 5233–5258. [Google Scholar] [CrossRef] [PubMed]
- Li, X.; Li, P. Rejection Sampling for Weighted Jaccard Similarity Revisited. Proceedings of the AAAI Conference on Artificial Intelligence, 2021, 35, 4197–4205. [Google Scholar] [CrossRef]
- Frigo, M.; Cruciani, E.; Coudert, D.; Deriche, R.; Natale, E.; Deslauriers-Gauthier, S. Network alignment and similarity reveal atlas-based topological differences in structural connectomes. Network Neuroscience, 2021, 5, 711–733. [Google Scholar] [CrossRef] [PubMed]
- CVE-2017-5689 Vulnerability Details. Available online: https://www.cvedetails.com/cve/CVE-2017-5689/ (accessed on 11 July 2024).
- CVE-2019-11932 Vulnerability Details. Available online: https://www.cvedetails.com/cve/CVE-2019-11932/ (accessed on 11 July 2024).
- MITRE APT Groups. Available online: https://attack.mitre.org/groups/ (accessed on 11 July 2024).
- Gulbay, B. Dataset and Source Code for the Paper: A Framework for Developing Strategic Cyber Threat Intelligence from Advanced Persistent Threat Analysis Reports Using Graph-Based Algorithms. Zenodo, 2024. [CrossRef]
Short Biography of Authors
 |
Burak Gulbay Received the BS degree in Computer Engineering from Atılım University in 2013 and also completed his minor in Software Engineering. He received MSc degree in Computer Engineering from Gazi University in 2013. He has been studying Information Security Engineering as PhD candidate at Gazi University. He is currently working as Next Generation Technologies Lead in defence industry. He participated in various software development projects as a software engineer, team manager, project manager, and consultant in both the public and private sectors. His research interests include Cyber Threat Intelligence, Graph Theory, Data Intensive Cloud Native Systems, and Digital Transformation |
 |
Mehmet Demirci Mehmet Demirci received his B.S. degree in computer science and mathematics (double major) from Purdue University in 2006, and his M.Sc. and Ph.D. degrees in computer science from Georgia Institute of Technology in 2009 and 2013, respectively. He is currently an assistant professor with the Department of Computer Engineering, Faculty of Engineering, Gazi University. His current research interests are SDN, NFV, network security, network architecture & future Internet. |
| Detection Source | 2011 | 2012 | 2013 | 2014 | 2015 | 2016 | 2017 | 2018 | 2019 | 2020 | 2021 | 2022 | 2023 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| External Notification | - | - | - | - | 320 | 107 | 186 | 184 | 141 | 73 | 28 | 19 | 13 |
| Internal Detection | - | - | - | - | 56 | 80 | 57.5 | 50.5 | 30 | 12 | 18 | 13 | 9 |
| All | 416 | 243 | 229 | 205 | 146 | 99 | 101 | 78 | 56 | 24 | 21 | 16 | 10 |
| Node Label | Count |
|---|---|
| apt_group | 785 |
| apt_report | 1980 |
| bitcoin | 5 |
| bitcoincash | 1 |
| copyright | 384 |
| country | 133 |
| cve | 573 |
| dashcoin | 1 |
| domain | 15901 |
| 1480 | |
| ethereum | 7 |
| facebook_handle | 61 |
| github_handle | 246 |
| ip | 9985 |
| ip4net | 365 |
| linkedin_handle | 19 |
| litecoin | 1 |
| malware | 882 |
| md5 | 17893 |
| mitre_technique | 181 |
| monero | 1 |
| onion_address | 14 |
| package_name | 3 |
| phone | 197 |
| pinterest_handle | 1 |
| ripple | 1 |
| sha1 | 7582 |
| sha256 | 12755 |
| subdomain | 13190 |
| telegram_handle | 2 |
| trademark | 211 |
| twitter_handle | 138 |
| url | 19762 |
| uuid | 482 |
| youtube_channel | 3 |
| youtube_handle | 8 |
| zcash | 1 |
| Minimum Score | Maximum Score | Mean Score |
|---|---|---|
| 0.0000 | 1865.0078 | 2.9822 |
| APT Group | Degree Centrality |
|---|---|
| lazarus group | 61 |
| turla | 56 |
| sofacy | 45 |
| apt28 | 40 |
| shamoon | 38 |
| carbanak | 34 |
| muddywater | 33 |
| hacking team | 31 |
| oilrig | 31 |
| sandworm | 27 |
| APT Group | Betweenness Centrality |
|---|---|
| lazarus group | 17064084.27 |
| apt28 | 6594142.41 |
| turla | 6393610.82 |
| hacking team | 5876781.64 |
| sofacy | 5218912.24 |
| patchwork | 5018645.94 |
| oceanlotus | 3999530.36 |
| kimsuky | 3945141.78 |
| charming kitten | 3878083.47 |
| carbanak | 3174435.89 |
| Minimum Score | Maximum Score | Mean Score |
|---|---|---|
| 0.00 | 1186373632.00 | 202920.06 |
| Minimum Score | Maximum Score | Mean Score |
|---|---|---|
| 0.0000 | 1.0000 | 0.2080 |
| APT Group | Closeness Centrality |
|---|---|
| lazarus group | 0.2564 |
| apt28 | 0.2542 |
| winnti group | 0.2542 |
| snake | 0.2538 |
| kimsuky | 0.2536 |
| hacking team | 0.2532 |
| turla | 0.2529 |
| carbanak | 0.2528 |
| fin7 | 0.2527 |
| shamoon | 0.2525 |
| APT Group | Eigenvector Centrality |
|---|---|
| lazarus group | 0.0189 |
| turla | 0.0178 |
| apt28 | 0.0177 |
| sofacy | 0.0172 |
| shamoon | 0.0171 |
| snake | 0.0166 |
| apt10 | 0.0165 |
| hacking team | 0.0160 |
| winnti group | 0.0160 |
| naikon | 0.0158 |
| Minimum Score | Maximum Scorre | Mean Score |
|---|---|---|
| 1.521e-12 | 0.3422 | 0.0005 |
| Community | APT Group Count |
|---|---|
| C1 | 195 |
| C2 | 166 |
| C3 | 106 |
| C4 | 82 |
| C5 | 71 |
| Community | APT Group Count |
|---|---|
| C1 | 732 |
| C2 | 52 |
| C3 | 1 |
| Community | APT Group Count |
|---|---|
| C1 | 226 |
| C2 | 83 |
| C3 | 50 |
| C4 | 49 |
| C5 | 44 |
| APT Report | APT Report | Similarity |
|---|---|---|
| ThaiCERT-A_Threat_Actor_Encyclopedia(06-19-2019).pdf | Threat Group Cards.pdf | 0.9958 |
| BlackEnergy2_Plugins_Router.pdf | be2-custom-plugins-router-abuse-and-target-profiles.pdf | 0.9804 |
| iranian-threat-group-updates-ttps-in-spear-phishing-campaign.pdf | MuddyWaters Recent Activity.pdf | 0.9215 |
| CERTFR-2019-CTI-005.pdf | cta-2019-0206.pdf | 0.4516 |
| Donot Team in South Asia.pdf | Musical Chairs Playing Tetris.pdf | 0.3649 |
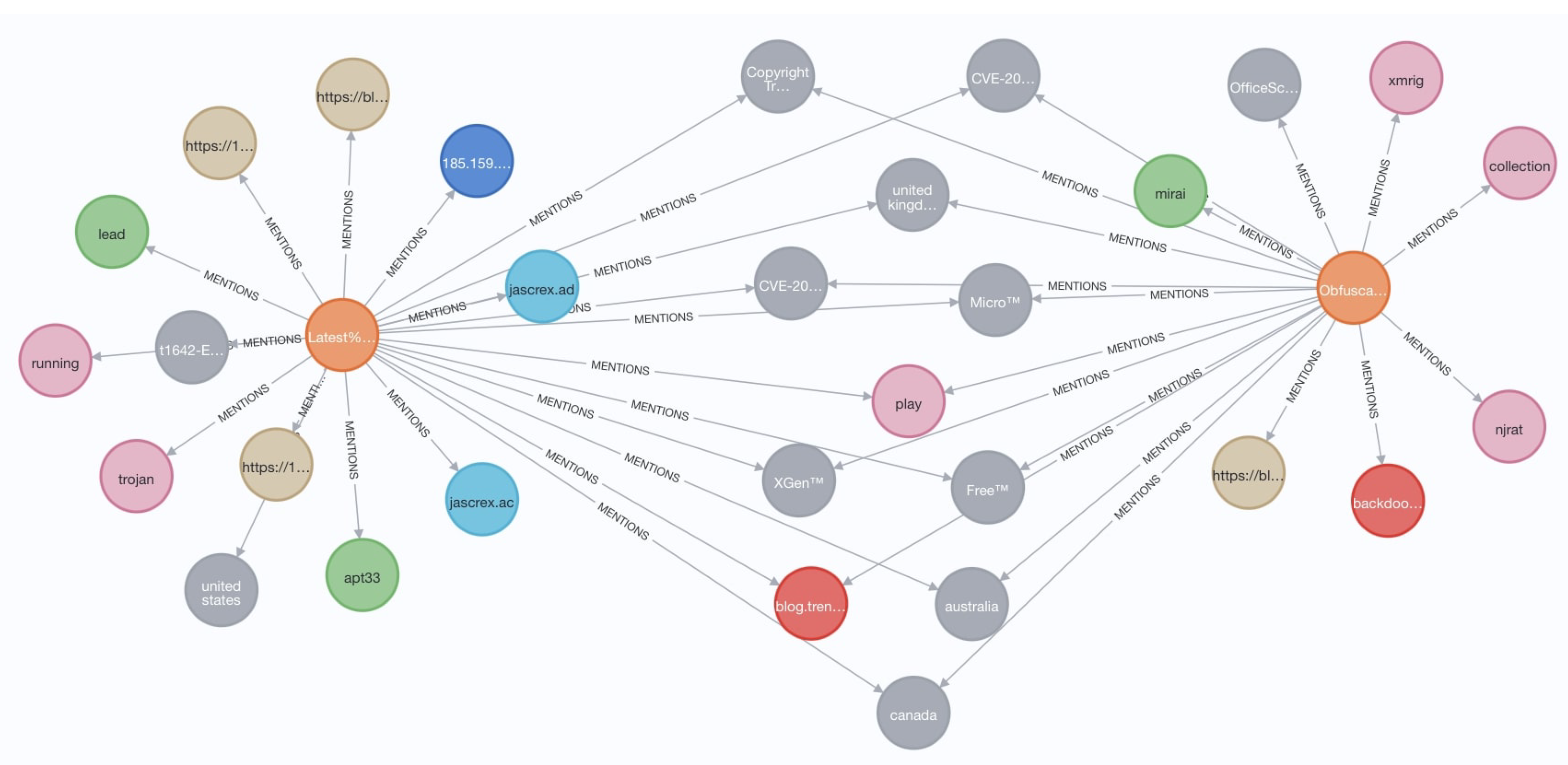
| Latest Trickbot Campaign Delivered via Highly Obfuscated-JS File.pdf | Obfuscation Tools Found in the Capesand Exploit Kit Possibly Used in KurdishCoder Campaign.pdf | 0.3548 |
| More than a Dozen Obfuscated APT33 Botnets Used for Extreme Narrow Targeting.pdf | wp-drilling-deep-a-look-at-cyberattacks-on-the-oil-and-gas-industry.pdf | 0.3441 |
| Elfin Relentless Espionage Group Targets Multiple Organizations in Saudi Arabia and US.pdf | cta-2019-0626.pdf | 0.3355 |
| Deep in Thought_ Chinese Targeting of National Security Think Tanks.pdf | Mo Shells Mo Problems - Web Server Log Analysis.pdf | 0.3333 |
| Latest Trickbot Campaign Delivered via Highly Obfuscated JS File .pdf | URSNIF EMOTET DRIDEX and BitPaymer Gangs Linked by a Similar Loader.pdf | 0.3333 |
| Node Label | Node Name | Weight |
|---|---|---|
| malware | trojan | 414 |
| malware | rat | 324 |
| domain | github.com | 233 |
| country | united states | 183 |
| domain | gmail.com | 150 |
| country | ukraine | 135 |
| apt_group | turla | 112 |
| cve | CVE-2012-0158 | 106 |
| malware | mimikatz | 106 |
| mitre_technique | t1059-Command and Scripting Interpreter | 90 |
| Centrality | Node Label | IoC | Measurement |
|---|---|---|---|
| Degree Centrality | malware | mimikatz | 106.00 |
| cve | CVE-2012-0158 | 106.00 | |
| country | iran | 101.00 | |
| malware | plugx | 95.00 | |
| malware | mimic | 85.00 | |
| Betweenness Centrality | cve | CVE-2012-0158 | 56628354.08 |
| malware | Mimic Ransomware | 31474216.60 | |
| cve | CVE-2017-11882 | 29433514.48 | |
| malware | mimikatz | 29010596.68 | |
| malware | plugx | 26132601.01 | |
| Closeness Centrality | sha256 | 92d057720eab41e9c6bb684e834da632ff3d79 b1d42e0 27e761d21967291ca50 |
0.66 |
| sha256 | d48bcca19522af9e11d5ce8890fe0b8daa01f93 c95e6a 338528892e152a4f63c |
0.66 | |
| uuid | BDE316E7-2665-4511-A4C4-8D4D0B7A9EAC | 0.66 | |
| domain | tawaranmurah.com | 0.52 | |
| ip | 81.4.100.197 | 0.52 | |
| Eigenvector Centrality | counrty | iran | 0.0316 |
| country | japan | 0.0307 | |
| cve | CVE-2012-0158 | 0.0265 | |
| malware | mimikatz | 0.0264 | |
| malware | rogue | 0.0252 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




