Submitted:
13 July 2024
Posted:
15 July 2024
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
- Introduction of IOTA 2.0 Smart Contracts for SDN Security: We leverage the IOTA Tangle’s unique directed acyclic graph (DAG) structure to implement scalable, efficient, and feeless smart contracts specifically designed to address the security challenges of SDN environments.
- Development of a Comprehensive Security Framework: We propose and implement three distinct smart contracts—Authority, Access Control, and DoS Detector—that work in unison to provide robust security mechanisms, ensuring secure network operations, preventing unauthorized access, and mitigating denial-of-service attacks.
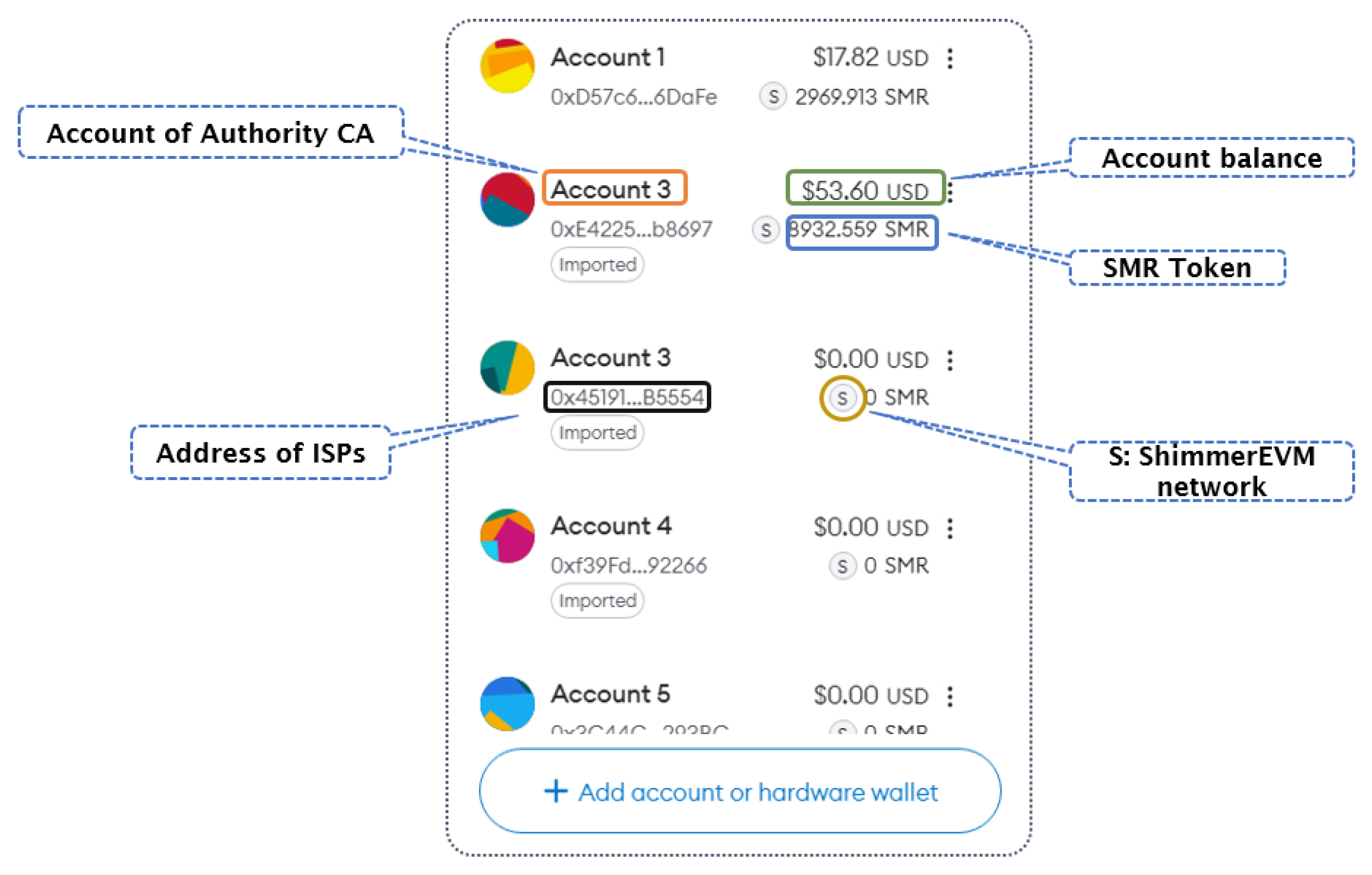
- Integration and Simulation in Realistic Environments: Through extensive simulations using Mininet and the ShimmerEVM IOTA Test Network, we validate the efficacy of our approach in real-world scenarios, demonstrating significant improvements in SDN security and resilience.
- Evaluation and Comparison with Existing Solutions: We conduct a thorough comparative analysis of our proposed system against existing blockchain-based security solutions for SDN, highlighting the advantages of IOTA 2.0 in terms of scalability, energy efficiency, and transaction costs.
2. Related Work
3. Background
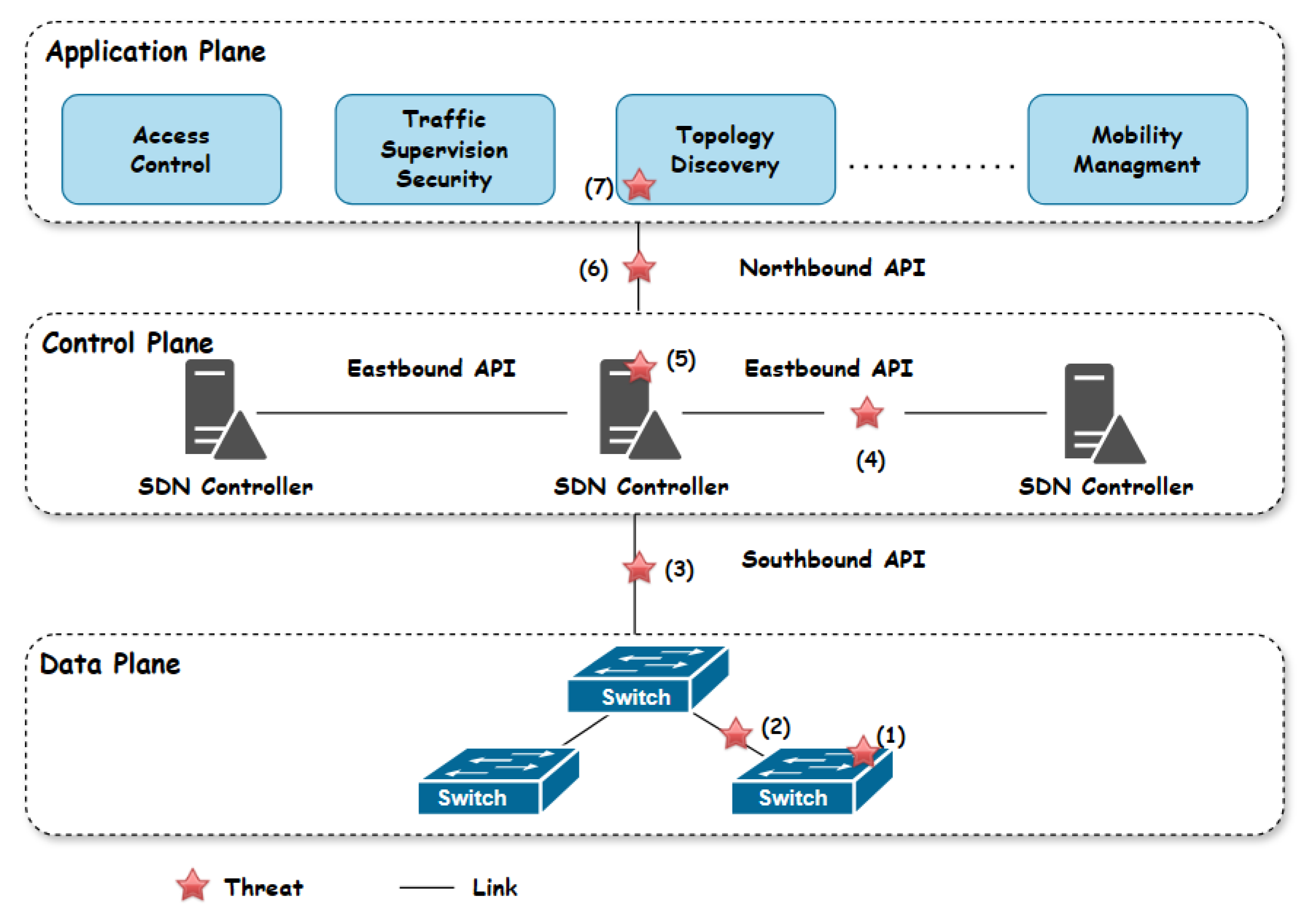
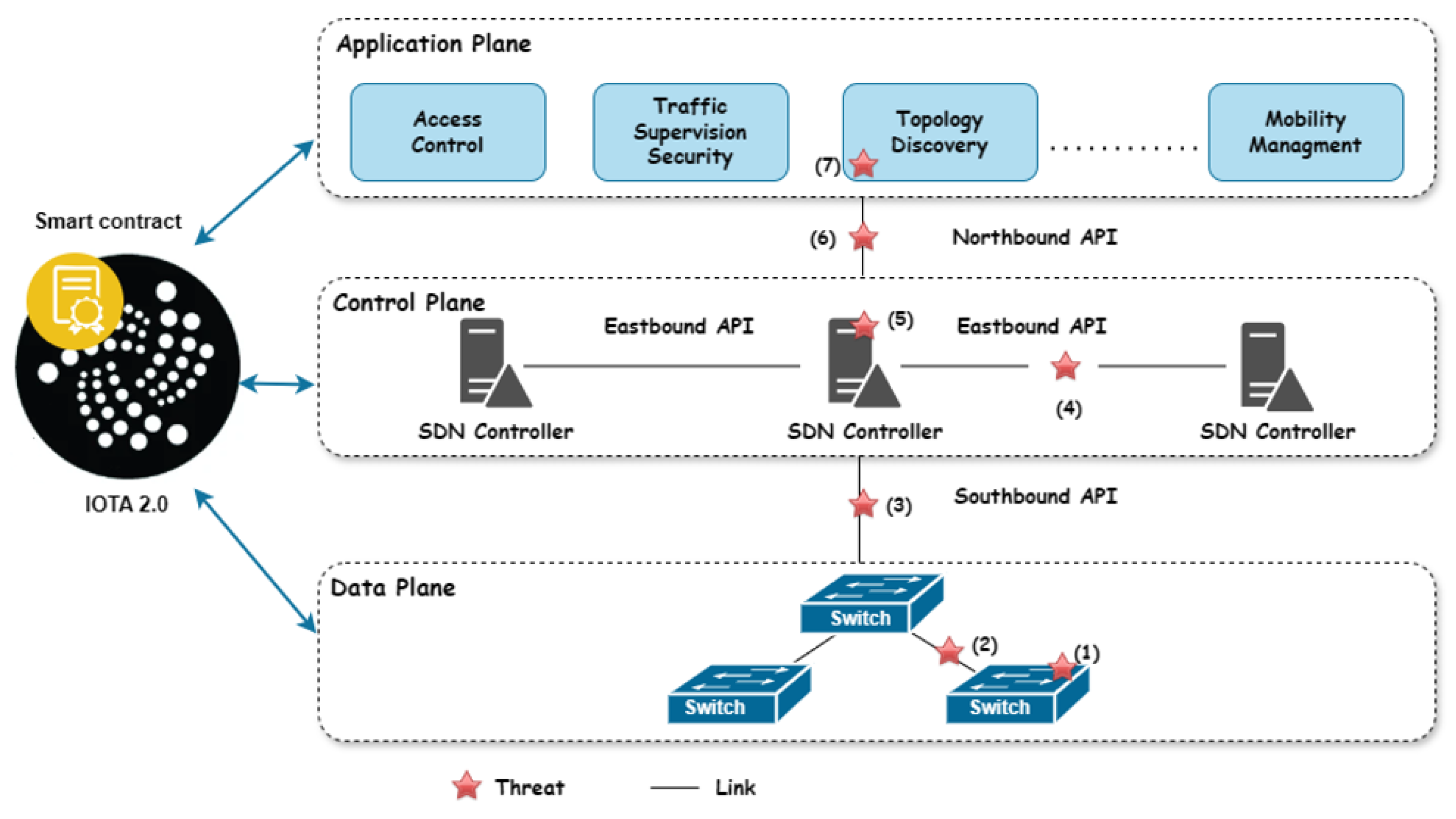
3.1. Comprehensive Analysis of SDN Security Challenges
- (1)
- The SDN switch is typically a distinct device comprising both hardware and software components, vulnerable to threats like flow table modification, topology spoofing, and DDoS attacks. Attackers can insert malicious nodes or modify flow rules, disrupting network integrity.
- (2)
- The link between switches: The SDN architecture’s lack of encryption on links between SDN switches allows hackers to intercept information, thereby compromising network security.
- (3)
- The eastbound interfaces are vulnerable to security threats due to the lack of encryption on the links connecting controllers. This vulnerability compromises the integrity of inter-controller communications, allowing hackers to manipulate network behavior and share false information.
- (4)
- SDN controllers, due to their centralized architecture, confront significant security challenges. They are particularly vulnerable to DDoS attacks, unauthorized access stemming from inadequate access control mechanisms, and interception risks, all of which compromise network scalability and availability. The lack of standardized security protocols further exacerbates these vulnerabilities, rendering SDN controllers susceptible to network disruptions and compromises. Attackers can also use the Link Layer Discovery Protocol to change information about the network’s topology and separate switches that have been hacked. Malformed packets can cause OpenFlow to flood with packets, which wastes resources and makes the network slow.
- (5)
- The northbound interface, a communication interface between applications and controllers, is vulnerable due to weak authentication and inappropriate authorization. This can lead to identity theft attacks and unauthorized access. Hackers can use multiple requests to create flow modifications, bottlenecks, and processor overload, compromising security and reliability between controllers and multiple applications.
- (6)
- The applications plane faces distinct security challenges, primarily due to its integral role in managing network behaviors and policies. This plane, often lacking robust authentication and access control mechanisms, is vulnerable to the introduction of malicious applications, which can lead to policy conflicts, unauthorized access, and resource exhaustion. The plane’s direct interaction with the SDN controller, where compromised applications can alter network configurations or launch attacks like DDoS, exacerbates these vulnerabilities. Furthermore, the absence of standardized security protocols on the application plane heightens the risk of tampering and eavesdropping.
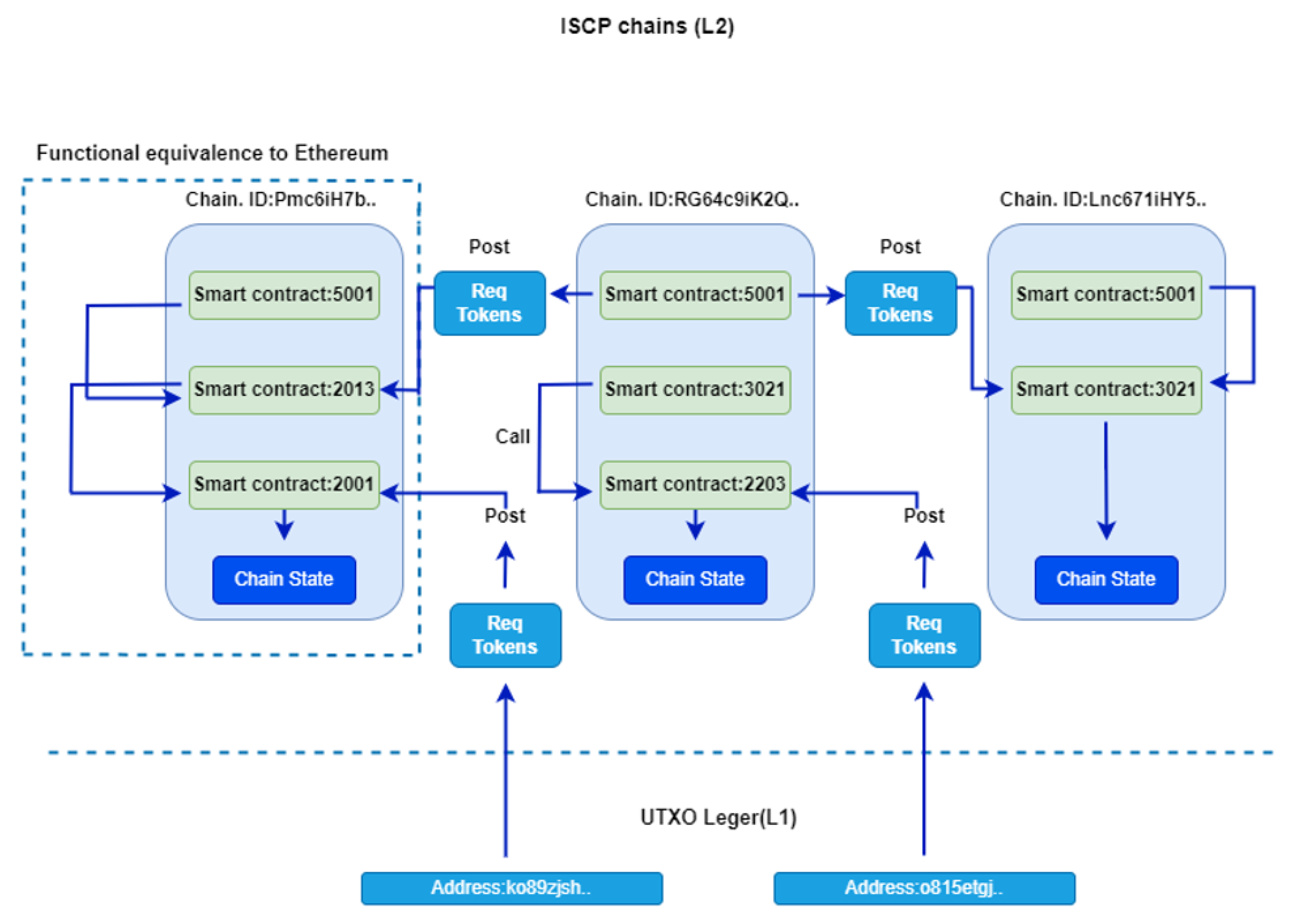
3.2. Overview of IOTA 2.0 Smart Contracts
- Tangle technology: Coordicide uses a directed acyclic graph called the Tangle, unlike traditional blockchains, which use a linear chain of blocks. This structure enables parallel transaction processing, ensuring high scalability and high throughput transaction per second (TPS).
- Decentralization and scalability: IOTA 2.0 eliminates the Coordinator, a special node for transaction validation. Moving towards a fully decentralized system enhances the network’s scalability and security.
- Energy efficiency: The Tangle’s design, which eliminates the need for miners, significantly reduces computational power for transaction validation, simplifying the process and making IOTA more energy-efficient compared to traditional proof-of-work blockchain systems.
- No transaction fees: IOTA 2.0 maintains its no-fee transaction feature. This feature makes microtransactions viable and opens up a range of applications, particularly in the Internet of Things domain.
- Interoperability: IOTA Tangle 2.0 facilitates the transfer of value between different BC networks due to its interoperability with other BC platforms.
- Smart contract capabilities: With IOTA 2.0, the network introduces support for SCs, allowing developers to create more complex decentralized applications. This feature aims to make IOTA a more competitive platform in the broader landscape of distributed ledger technologies.
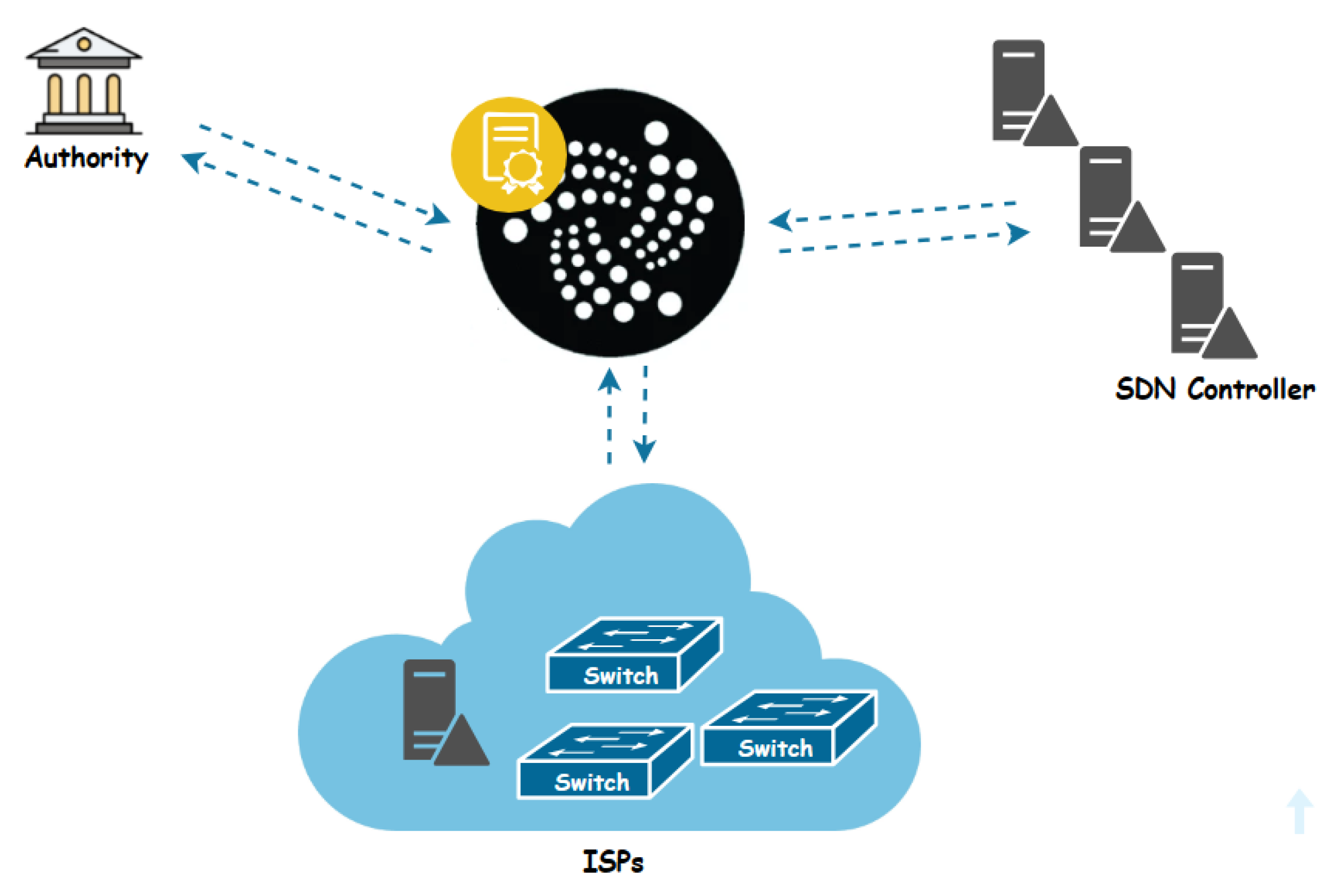
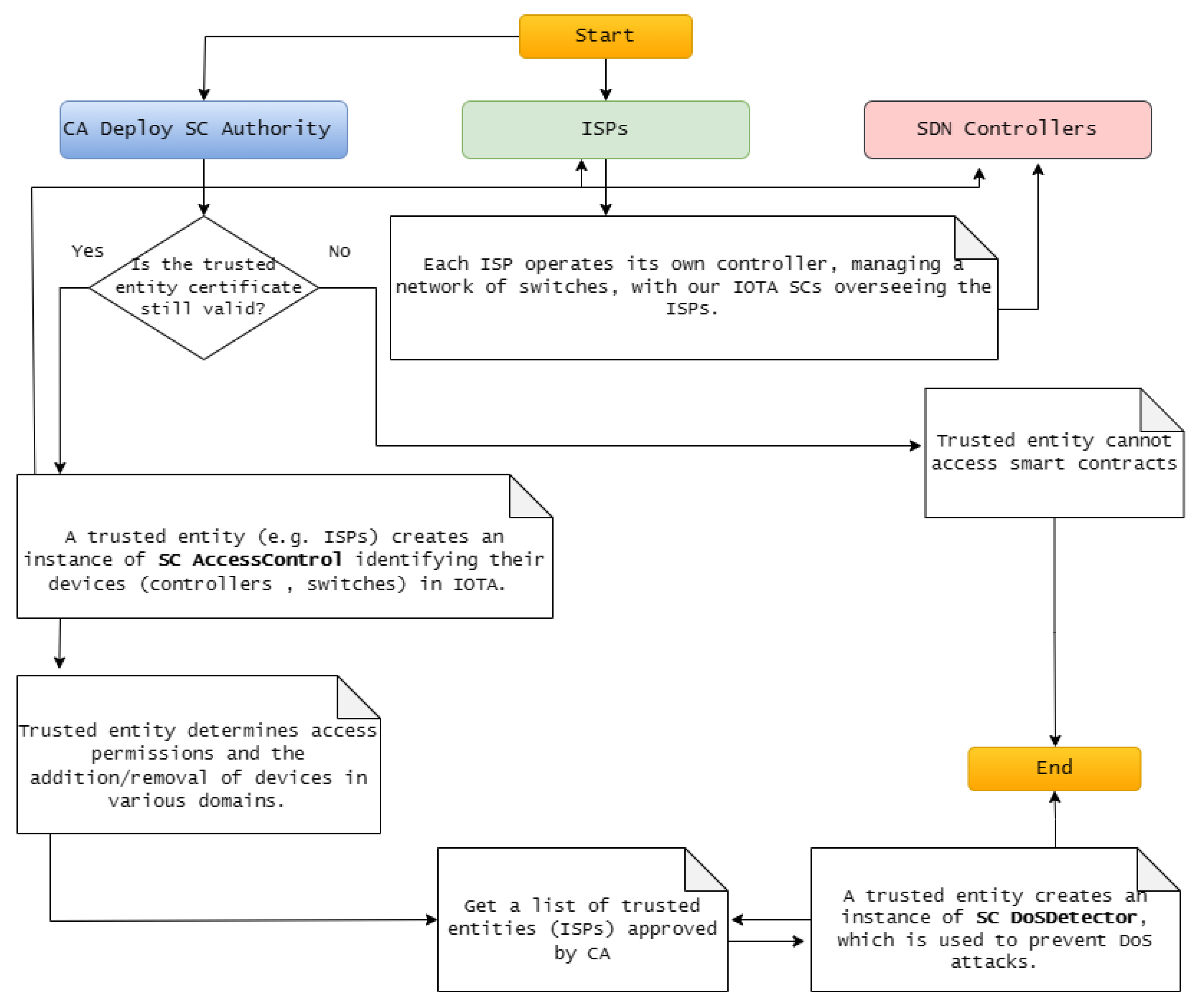
4. Proposed IOTA-SDN System
- The Authority: functioning as a Certificate Authority (CA), holds pivotal responsibility in overseeing the involvement of trusted entities, specifically ISPs, within our proposed system. Its primary role lies in ensuring the exclusive authorization of an ISP to integrate its controller, switches, and standby controller components. Moreover, the CA serves as a cornerstone in upholding the security and integrity of the system by meticulously managing the authorization procedures for these entities. Furthermore, it defines the expiration parameters of digital certificates and offers essential revocation services to invalidate non-expired certificates when necessary.
- ISPs: within our system, only trusted entities (ISPs), approved by the Authority acting as (CA), are granted access. Each ISP assumes a critical role, maintaining its controller and switches. These controllers serve as primary administrators, intricately connected to a network of switches, facilitating efficient data transmission and network management. Notably, ISPs wield the authority to manage access permissions, authorizing or withdrawing access and integrating or excluding backup controllers across different network domains. This architecture ensures both robust network functionality and stringent security standards, empowering ISPs to oversee their network infrastructure effectively.
- The SDN controller: within the system architecture, the controller assumes a dual role of paramount importance. Firstly, it functions as the primary administrator within its designated domain, overseeing and orchestrating network operations, managing data flow, and ensuring the smooth functioning of connected switches. As the primary administrator, the controller holds authoritative control over the domain’s network infrastructure, making critical decisions to optimize performance and maintain security. Additionally, the controller assumes the crucial responsibility of serving as the standby controller for other domains within the system. In this capacity, it stands ready to assume control in the event of a primary controller failure or disruption, ensuring seamless continuity of network operations. This dual functionality not only enhances the efficiency and reliability of network management within individual domains but also contributes to the overall resilience and fault tolerance of the system as a whole.
4.1. Overview of the Architecture and Components of the Proposed System
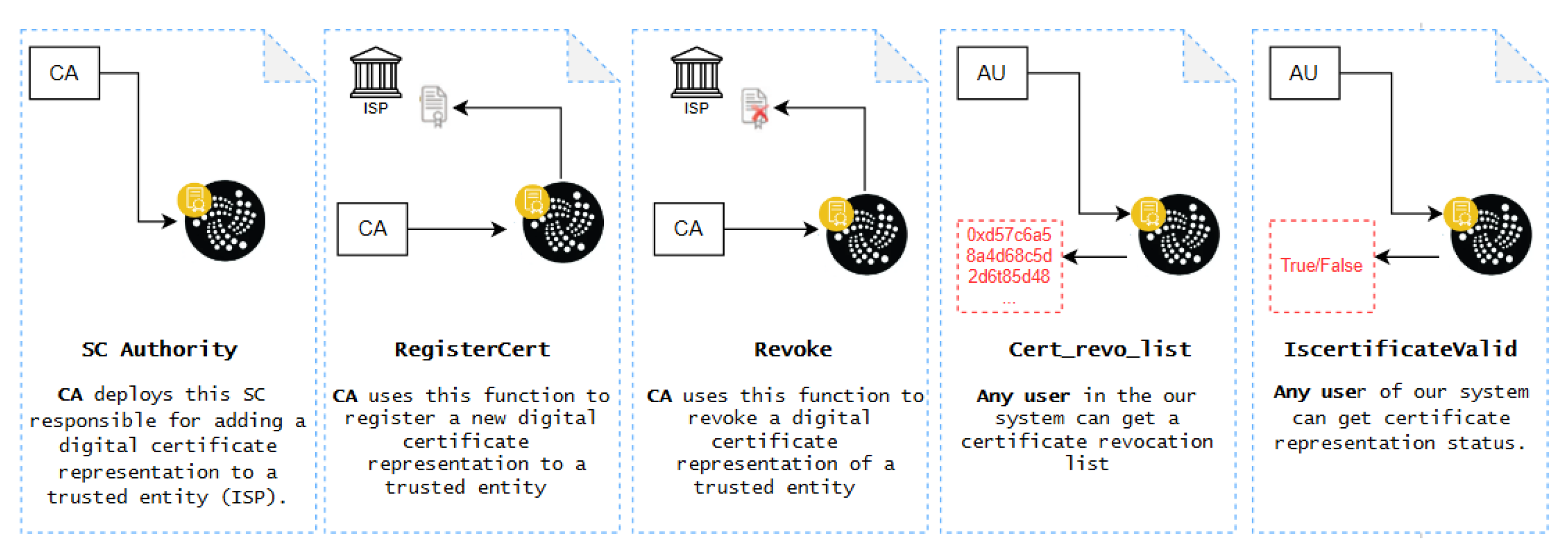
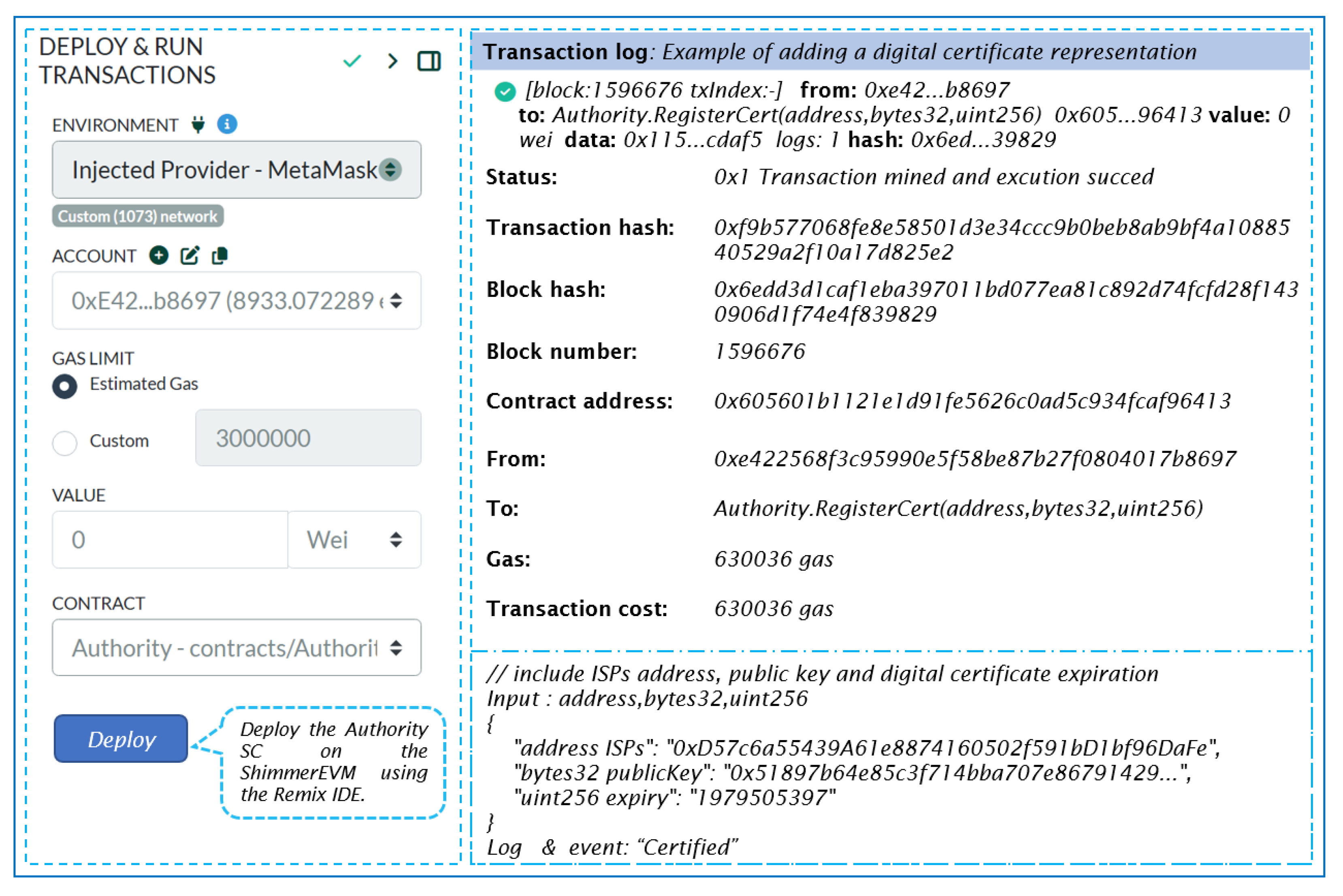
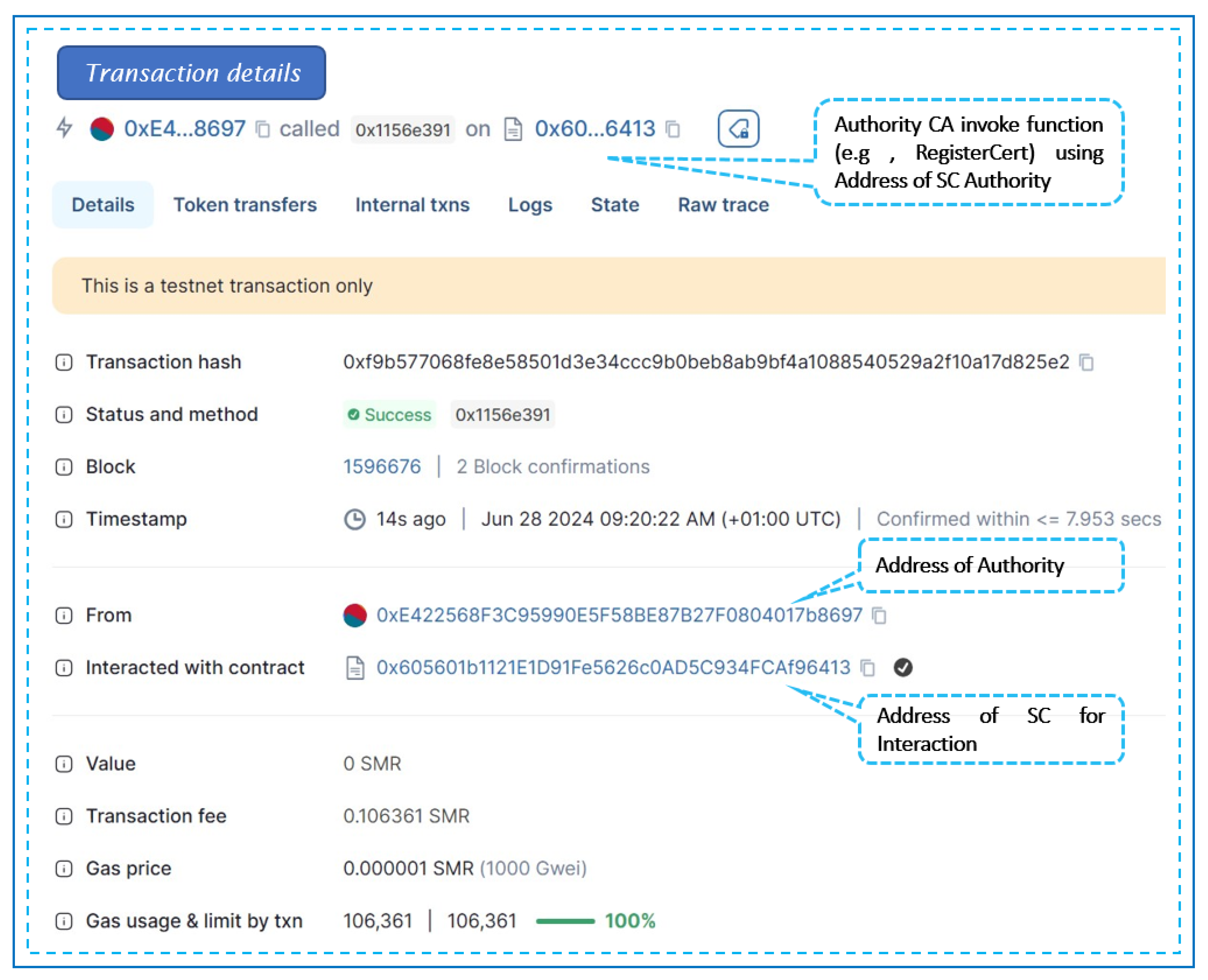
4.2. Smart contract Authority of CA
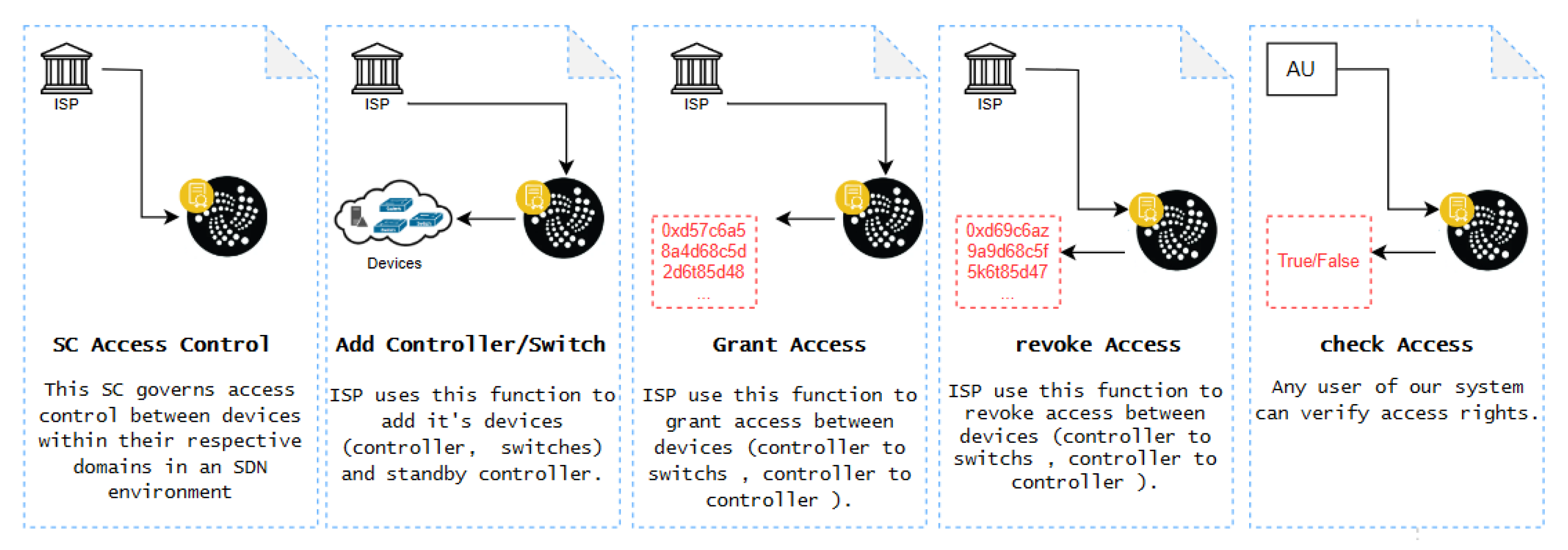
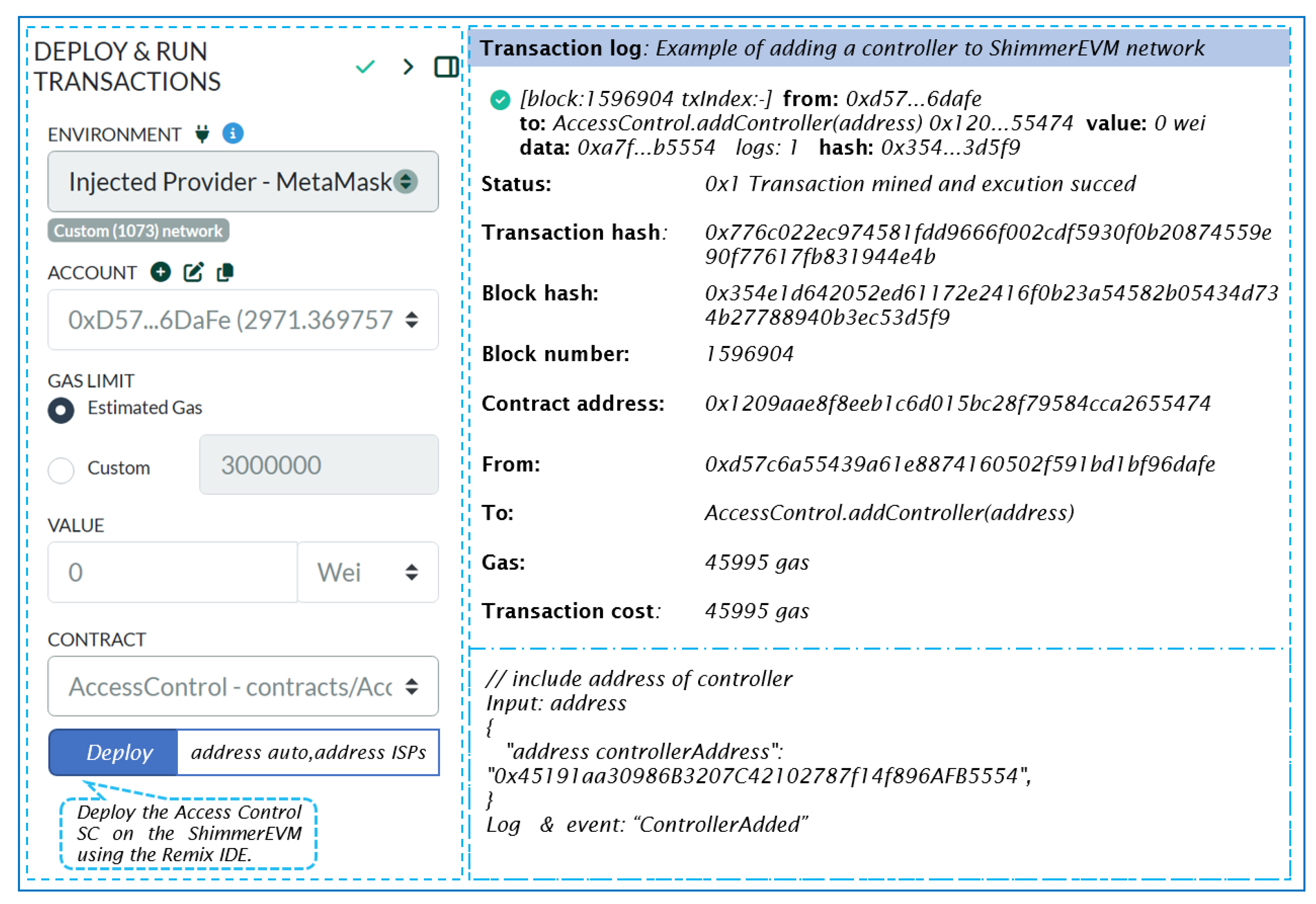
4.3. Smart contract Access Control of CA
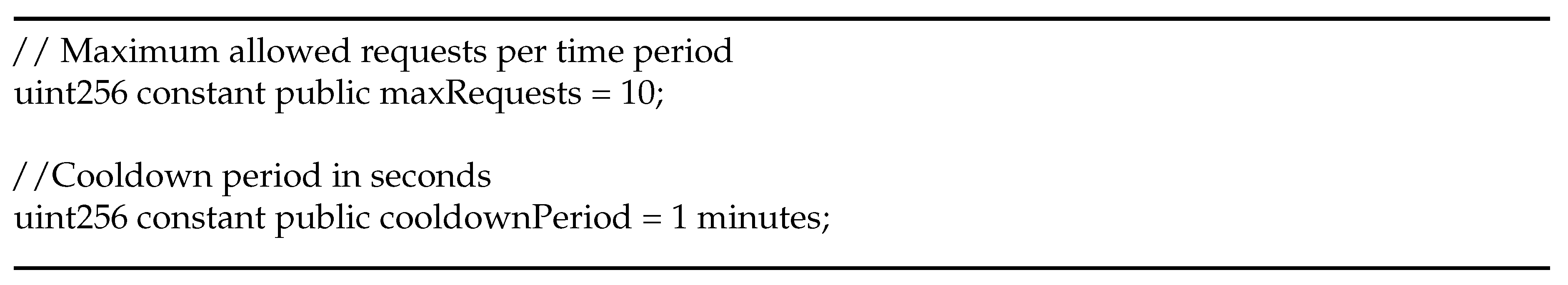
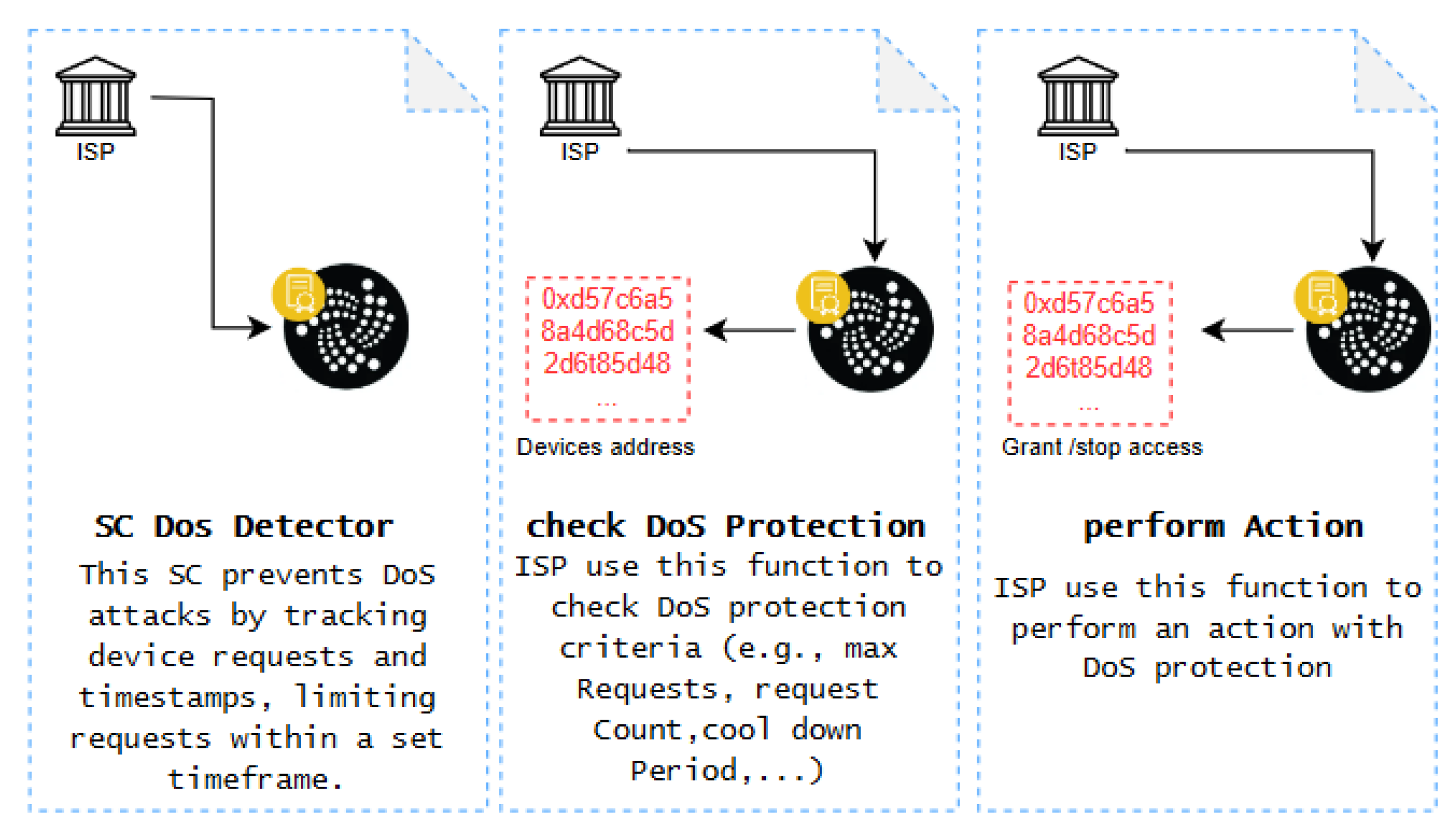
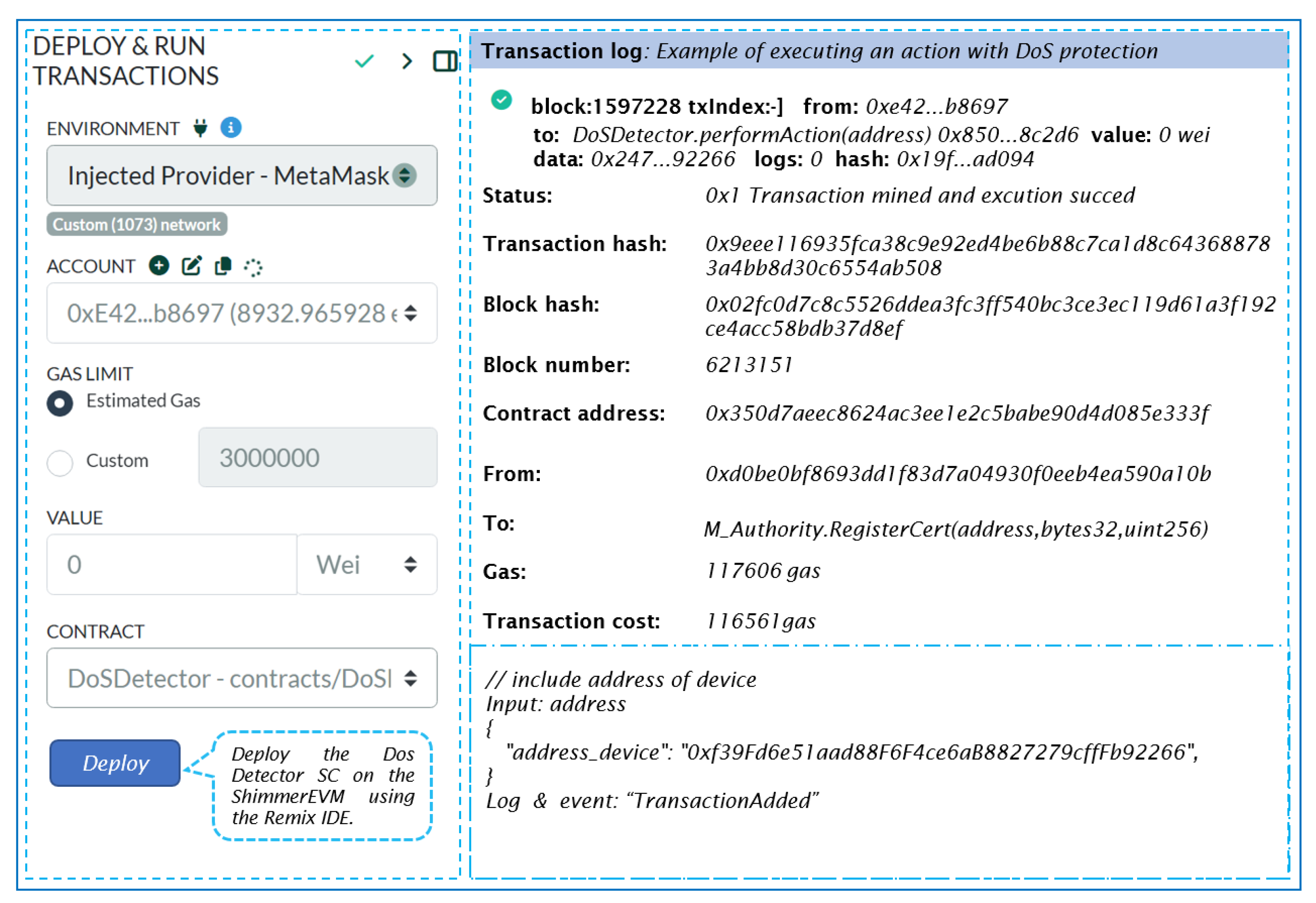
4.3.1. Smart contract DoS Detector of CA
4.4. Key Benefits of the Proposed System
5. Simulation Results and Discussion
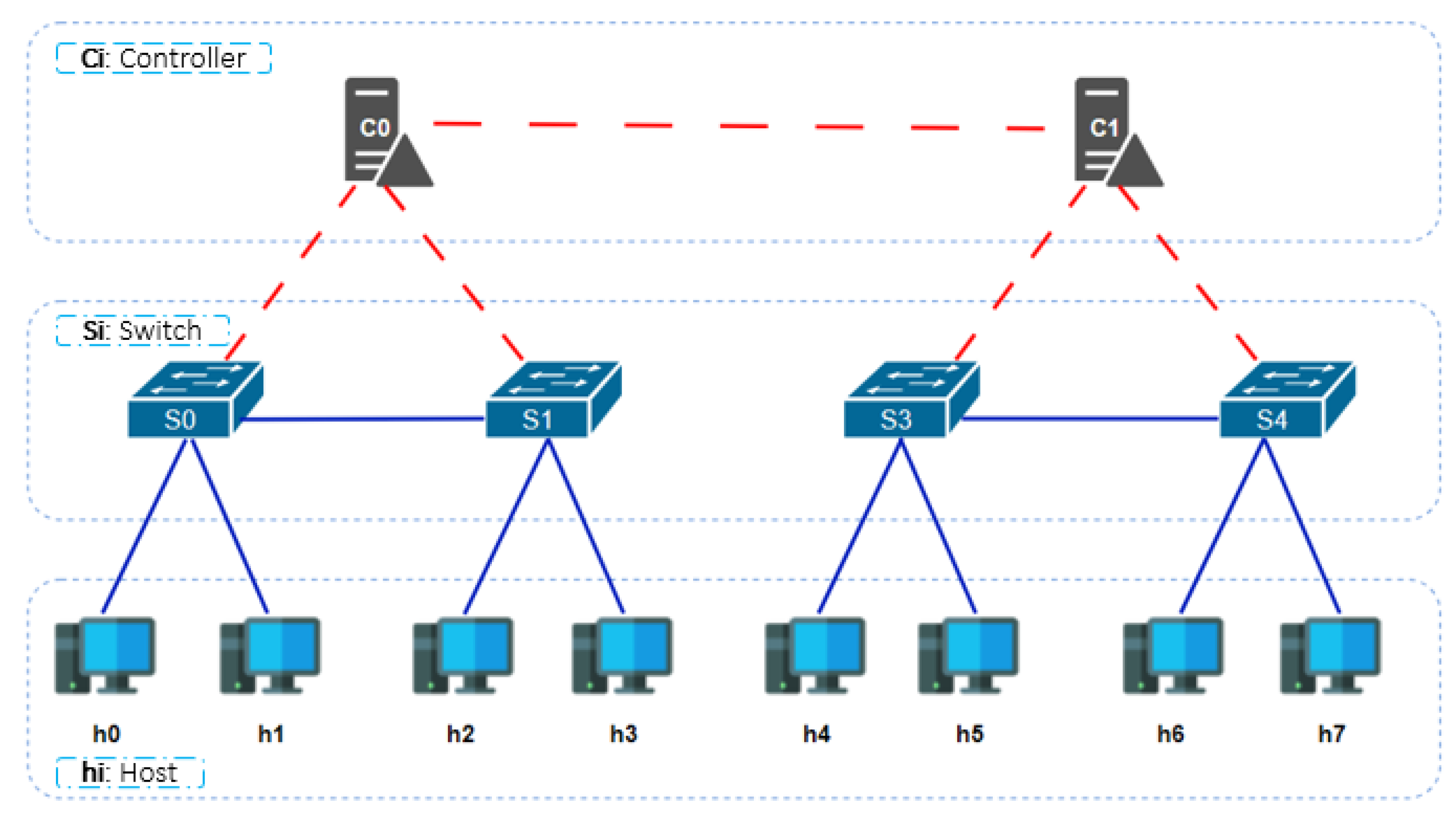
5.1. Emulation SDN using Mininet
5.2. Smart Contract Authority
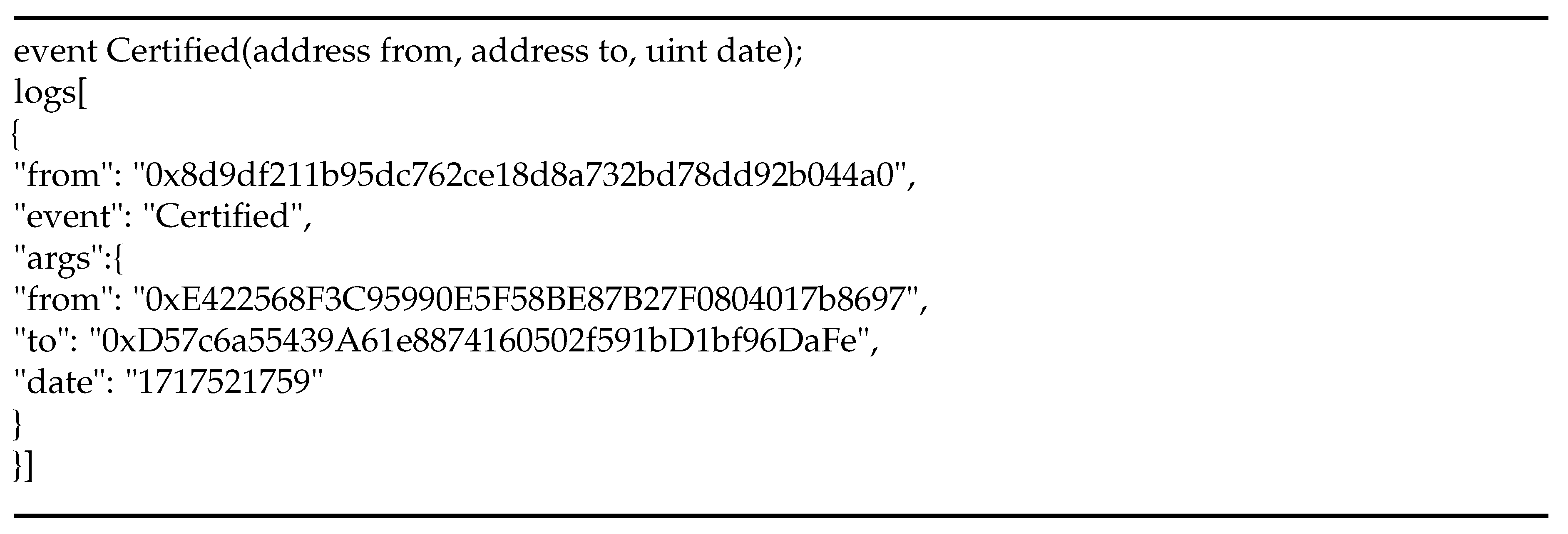
5.3. Smart Contract Access Control
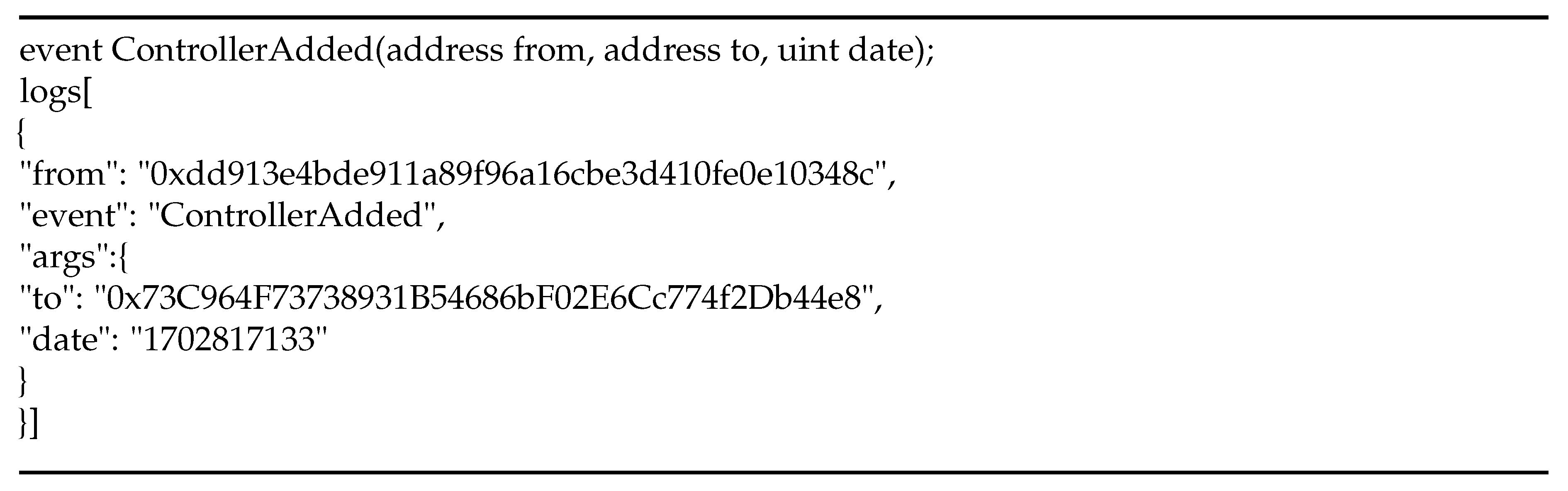
5.4. Smart Contract DoS Detector
5.5. Limitations of the Proposed System
6. Conclusion and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A
References
- Sezer, S.; Scott-Hayward, S.; Chouhan, P.; Fraser, B.; Lake, D.; Finnegan, J.; Viljoen, N.; Miller, M.; Rao, N. Are We Ready for SDN? Implementation Challenges for Software-Defined Networks. IEEE Commun. Mag. 2013, 51, 36–43. [Google Scholar] [CrossRef]
- Hu, F.; Hao, Q.; Bao, K. A Survey on Software-Defined Network and OpenFlow: From Concept to Implementation. IEEE Commun. Surv. Tutorials 2014, 16, 2181–2206. [Google Scholar] [CrossRef]
- Kreutz, D.; Ramos, F.M.V.; Verissimo, P.E.; Rothenberg, C.E.; Azodolmolky, S.; Uhlig, S. Software-Defined Networking: A Comprehensive Survey. Proc. IEEE 2015, 103, 14–76. [Google Scholar] [CrossRef]
- Singh, S.; Jha, R.K. A Survey on Software Defined Networking: Architecture for Next Generation Network. J. Network Syst. Manage. 2016, 25, 321–374. [Google Scholar] [CrossRef]
- Abdulghaffar, A.; Mahmoud, A.; Abu-Amara, M.; Sheltami, T. Modeling and Evaluation of Software Defined Networking Based 5G Core Network Architecture. IEEE Access 2021, 9, 10179–10198. [Google Scholar] [CrossRef]
- Bonanni, M.; Chiti, F.; Fantacci, R.; Pierucci, L. Dynamic Control Architecture Based on Software Defined Networking for the Internet of Things. Future Internet 2021, 13, 113. [Google Scholar] [CrossRef]
- Boukraa, L.; Mahrach, S.; Makkaoui, K.E.; Esbai, R. SDN Southbound Protocols: A Comparative Study. In Lecture notes on data engineering and communications technologies; 2022; pp. 407–418.
- Ahmad, I.; Namal, S.; Ylianttila, M.; Gurtov, A. Security in Software Defined Networks: A Survey. IEEE Commun. Surv. Tutorials 2015, 17, 2317–2346. [Google Scholar] [CrossRef]
- Maleh, Y.; Qasmaoui, Y.; Gholami, K.E.; Sadqi, Y.; Mounir, S. A Comprehensive Survey on SDN Security: Threats, Mitigations, and Future Directions. J. Reliab. Intell. Environ. 2022, 9, 201–239. [Google Scholar] [CrossRef]
- Farooq, M.S.; Riaz, S.; Alvi, A. Security and Privacy Issues in Software-Defined Networking (SDN): A Systematic Literature Review. Electronics 2023, 12, 3077. [Google Scholar] [CrossRef]
- Bhuiyan, Z.A.; Islam, S.; Islam, Md.M.; Ullah, A.B.M.A.; Naz, F.; Rahman, M.S. On the (in)Security of the Control Plane of SDN Architecture: A Survey. IEEE Access 2023, 11, 91550–91582. [Google Scholar] [CrossRef]
- Setitra, M.A.; Fan, M.; Benkhaddra, I.; Bensalem, Z.E.A. DoS/DDoS Attacks in Software Defined Networks: Current Situation, Challenges and Future Directions. Comput. Commun. 2024. [Google Scholar] [CrossRef]
- Polat, H.; Polat, O.; Cetin, A. Detecting DDoS Attacks in Software-Defined Networks Through Feature Selection Methods and Machine Learning Models. Sustainability 2020, 12, 1035. [Google Scholar] [CrossRef]
- Bahashwan, A.A.; Anbar, M.; Manickam, S.; Al-Amiedy, T.A.; Aladaileh, M.A.; Hasbullah, I.H. A Systematic Literature Review on Machine Learning and Deep Learning Approaches for Detecting DDoS Attacks in Software-Defined Networking. Sensors 2023, 23, 4441. [Google Scholar] [CrossRef]
- Liu, Z.; Wang, Y.; Feng, F.; Liu, Y.; Li, Z.; Shan, Y. A DDoS Detection Method Based on Feature Engineering and Machine Learning in Software-Defined Networks. Sensors 2023, 23, 6176. [Google Scholar] [CrossRef]
- Alshahrani, M.M. A Secure and Intelligent Software-Defined Networking Framework for Future Smart Cities to Prevent DDoS Attack. Appl. Sci. 2023, 13, 9822. [Google Scholar] [CrossRef]
- Faezi, S.; Shirmarz, A. A Comprehensive Survey on Machine Learning Using in Software Defined Networks (SDN). Hum.-Centric Intell. Syst. 2023, 3, 312–343. [Google Scholar] [CrossRef]
- Boukraa, L.; Essahraui, S.; Maleh, Y.; El Makkaoui, K.; Ouahbi, I.; Esbai, R. MACHINE LEARNING-BASED INTRUSION DETECTION SYSTEMS FOR SDN: AN EMPIRICAL STUDY USING KNIME. EDPACS 2024, 69, 46–59. [Google Scholar] [CrossRef]
- Alharbi, T. Deployment of Blockchain Technology in Software Defined Networks: A Survey. IEEE Access 2020, 8, 9146–9156. [Google Scholar] [CrossRef]
- Kovacs, R.; Buzura, S.; Iancu, B.; Dadarlat, V.; Peculea, A.; Cebuc, E. Practical Implementation of a Blockchain-Enabled SDN for Large-Scale Infrastructure Networks. Appl. Sci. 2024, 14, 1914. [Google Scholar] [CrossRef]
- Guo, H.; Yu, X. A Survey on Blockchain Technology and Its Security. Blockchain: Res. Appl. 2022, 3, 100067. [Google Scholar] [CrossRef]
- Krichen, M.; Ammi, M.; Mihoub, A.; Almutiq, M. Blockchain for Modern Applications: A Survey. Sensors 2022, 22, 5274. [Google Scholar] [CrossRef] [PubMed]
- Yang, S.; Li, S.; Chen, W.; Zhao, Y. A Redactable Blockchain-Based Data Management Scheme for Agricultural Product Traceability. Sensors 2024, 24, 1667. [Google Scholar] [CrossRef] [PubMed]
- Lee, S.; Kim, Y.; Cho, S. Searchable Blockchain-Based Healthcare Information Exchange System to Enhance Privacy Preserving and Data Usability. Sensors 2024, 24, 1582. [Google Scholar] [CrossRef] [PubMed]
- Kongsen, J.; Chantaradsuwan, D.; Koad, P.; Thu, M.; Jandaeng, C. A Secure Blockchain-Enabled Remote Healthcare Monitoring System for Home Isolation. J. Sens. Actuator Netw. 2024, 13, 13. [Google Scholar] [CrossRef]
- Taherdoost, H. Blockchain Integration and Its Impact on Renewable Energy. Computers 2024, 13, 107. [Google Scholar] [CrossRef]
- Rustemi, A.; Dalipi, F.; Atanasovski, V.; Risteski, A. A Systematic Literature Review on Blockchain-Based Systems for Academic Certificate Verification. IEEE Access 2023, 11, 64679–64696. [Google Scholar] [CrossRef]
- Litoussi, M.; Fartitchou, M.; El Makkaoui, K.; Ezzati, A.; El Allali, Z. Digital Certifications in Moroccan Universities: Concepts, Challenges, and Solutions. Procedia Comput. Sci. 2022, 201, 95–100. [Google Scholar] [CrossRef]
- Biswas, K.; Chowdhury, M.J.M.; Usman, M. Blockchain of Things: Benefits, Challenges and Future Directions. Sensors 2024, 24, 934. [Google Scholar] [CrossRef]
- Ahakonye, L.A.C.; Nwakanma, C.I.; Kim, D.-S. Tides of Blockchain in IoT Cybersecurity. Sensors 2024, 24, 3111. [Google Scholar] [CrossRef]
- Arachchige, K.G.; Branch, P.; But, J. An Analysis of Blockchain-Based IoT Sensor Network Distributed Denial of Service Attacks. Sensors 2024, 24, 3083. [Google Scholar] [CrossRef]
- Lamriji, Y.; Kasri, M.; El Makkaoui, K.; Beni-Hssane, A. A comparative study of consensus algorithms for blockchain. In Proceedings of the 2023 IEEE 3rd International Conference on Innovative Research in Applied Science, Engineering and Technology, Mohammedia, Morocco, 18-19 May 2023; pp. 1–8. [Google Scholar]
- Alghamdi, T.A.; Khalid, R.; Javaid, N. A Survey of Blockchain Based Systems: Scalability Issues and Solutions, Applications and Future Challenges. IEEE Access, 2024.
- Rebello, G.A.F.; Camilo, G.F.; De Souza, L.A.C.; Potop-Butucaru, M.; De Amorim, M.D.; Campista, M.E.M.; Costa, L.H.M.K. A Survey on Blockchain Scalability: From Hardware to Layer-Two Protocols. IEEE Commun. Surv. Tutorials 2024, 1. [Google Scholar] [CrossRef]
- Rao, I.S.; Kiah, M.L.M.; Hameed, M.M.; Memon, Z.A. Scalability of Blockchain: A Comprehensive Review and Future Research Direction. Cluster Comput., 2024.
- Popov, S.; Lu, Q. IOTA: feeless and free. IEEE Blockchain Technical Briefs 2019, 6. [Google Scholar]
- Silvano, W.F.; Marcelino, R. Iota Tangle: A Cryptocurrency to Communicate Internet-of-Things Data. Future Gener. Comput. Syst. 2020, 112, 307–319. [Google Scholar] [CrossRef]
- Fartitchou, M.; Boussouf, J.; El Makkaoui, K.; Maleh, Y.; El Allali, Z. IOTA TANGLE 2.0: AN OVERVIEW. EDPACS 2023, 68, 15–26. [Google Scholar] [CrossRef]
- Gilani, S.M.; Anjum, A.; Khan, A.; Syed, M.H.; Moqurrab, S.A.; Srivastava, G. A Robust Internet of Drones Security Surveillance Communication Network Based on IOTA. Internet of Things 2024, 25, 101066. [Google Scholar] [CrossRef]
- Denis, N.; Chabridon, S.; Laurent, M. Bringing Privacy, Security and Performance to the Internet of Things Using IOTA and Usage Control. Ann. Telecommun. 2024. [Google Scholar] [CrossRef]
- Zhao, L.; Ferraro, P.; Shorten, R. A Smart Mask to Enforce Social Contracts Based on IOTA Tangle. PloS One 2024, 19, e0292850. [Google Scholar] [CrossRef] [PubMed]
- Lin, I.-C.; Tseng, P.-C.; Chen, P.-H.; Chiou, S.-J. Enhancing Data Preservation and Security in Industrial Control Systems through Integrated IOTA Implementation. Processes 2024, 12, 921. [Google Scholar] [CrossRef]
- Gligoric, N.; Escuín, D.; Polo, L.; Amditis, A.; Georgakopoulos, T.; Fraile, A. IOTA-Based Distributed Ledger in the Mining Industry: Efficiency, Sustainability and Transparency. Sensors 2024, 24, 923. [Google Scholar] [CrossRef]
- Mazzocca, C.; Romandini, N.; Montanari, R.; Bellavista, P. Enabling Federated Learning at the Edge through the IOTA Tangle. Future Gener. Comput. Syst. 2024, 152, 17–29. [Google Scholar] [CrossRef]
- Weng, J.-S.; Weng, J.; Liu, J.-N.; Zhang, Y. Secure Software-Defined Networking Based on Blockchain. arXiv (Cornell University) 2019.
- Pourvahab, M.; Ekbatanifard, G. An Efficient Forensics Architecture in Software-Defined Networking-IoT Using Blockchain Technology. IEEE Access 2019, 7, 99573–99588. [Google Scholar] [CrossRef]
- Yazdinejad, A.; Parizi, R.M.; Dehghantanha, A.; Choo, K.-K.R. P4-to-Blockchain: A Secure Blockchain-Enabled Packet Parser for Software Defined Networking. Comput. Secur. 2020, 88, 101629. [Google Scholar] [CrossRef]
- Aujla, G.S.; Singh, M.; Bose, A.; Kumar, N.; Han, G.; Buyya, R. BlockSDN: Blockchain-as-a-Service for Software Defined Networking in Smart City Applications. IEEE Network 2020, 34, 83–91. [Google Scholar] [CrossRef]
- Shashidhara, R.; Ahuja, N.; Lajuvanthi, M.; Akhila, S.; Das, A.K.; Rodrigues, J.J.P.C. SDN-chain: Privacy-preserving Protocol for Software Defined Networks Using Blockchain. Secur. Privacy 2021, 4, e178. [Google Scholar] [CrossRef]
- Algarni, S.; Eassa, F.; Almarhabi, K.; Algarni, A.; Albeshri, A. BCNBI: A Blockchain-Based Security Framework for Northbound Interface in Software-Defined Networking. Electronics 2022, 11, 996. [Google Scholar] [CrossRef]
- Kovacs, R.; Buzura, S.; Iancu, B.; Dadarlat, V.; Peculea, A.; Cebuc, E. Practical Implementation of a Blockchain-Enabled SDN for Large-Scale Infrastructure Networks. Appl. Sci. 2024, 14, 1914. [Google Scholar] [CrossRef]
- Han, T.; Jan, S.R.U.; Tan, Z.; Usman, M.; Jan, M.A.; Khan, R.; Xu, Y. A Comprehensive Survey of Security Threats and Their Mitigation Techniques for Next-generation SDN Controllers. Concurrency Comput. Pract. Exper. 2020, 32, e5300. [Google Scholar] [CrossRef]
- Chica, J.C.C.; Imbachi, J.C.; Vega, J.F.B. Security in SDN: A Comprehensive Survey. J. Network Comput. Appl. 2020, 159, 102595. [Google Scholar] [CrossRef]
- Ahmad, S.; Mir, A.H. Scalability, Consistency, Reliability and Security in SDN Controllers: A Survey of Diverse SDN Controllers. J. Network Syst. Manage. 2021, 29, 1–59. [Google Scholar] [CrossRef]
- Kaur, S.; Kumar, K.; Aggarwal, N.; Singh, G. A Comprehensive Survey of DDoS Defense Solutions in SDN: Taxonomy, Research Challenges, and Future Directions. Comput. Secur. 2021, 110, 102423. [Google Scholar] [CrossRef]
- Deb, R.; Roy, S. A Comprehensive Survey of Vulnerability and Information Security in SDN. Comput. Networks 2022, 206, 108802. [Google Scholar] [CrossRef]
- Alrubei, S.M.; Ball, E.A.; Rigelsford, J.M.; Willis, C.A. Latency and Performance Analyses of Real-World Wireless IoT-Blockchain Application. IEEE Sens. J. 2020, 20, 7372–7383. [Google Scholar] [CrossRef]
- Zafar, S.; Bhatti, K.M.; Shabbir, M.; Hashmat, F.; Akbar, A.H. Integration of Blockchain and Internet of Things: Challenges and Solutions. Ann. Telecommun. 2021, 77, 13–32. [Google Scholar] [CrossRef]
- Abdelmaboud, A.; Ahmed, A.I.A.; Abaker, M.; Eisa, T.A.E.; Albasheer, H.; Ghorashi, S.A.; Karim, F.K. Blockchain for IoT Applications: Taxonomy, Platforms, Recent Advances, Challenges and Future Research Directions. Electronics 2022, 11, 630. [Google Scholar] [CrossRef]
- Adhikari, N.; Ramkumar, M. IoT and Blockchain Integration: Applications, Opportunities, and Challenges. Network 2023, 3, 115–141. [Google Scholar] [CrossRef]
- Helmer, L.; Penzkofer, A. Report on the Energy Consumption of the IOTA 2.0 Prototype Network (GoShimmer 0.8.3) under Different Testing Scenarios. arXiv (Cornell University) 2022.
- Popov, S. IOTA Tangle Whitepaper, 2018. Available online: PDF (accessed on 03 June 2024).
- Drąsutis, E. IOTA smart contracts, 2022. Available online: PDF (accessed on 03 June 2024).
- Müller, S.; Penzkofer, A.; Polyanskii, N.; Theis, J.; Sanders, W.; Moog, H. Tangle 2.0 Leaderless Nakamoto Consensus on the Heaviest DAG. IEEE Access 2022, 10, 105807–105842. [Google Scholar] [CrossRef]
- IOTA Wiki. Available online: Link (accessed on 03 June 2024).
- Conti, M.; Kumar, G.; Nerurkar, P.; Saha, R.; Vigneri, L. A Survey on Security Challenges and Solutions in the IOTA. J. Network Comput. Appl. 2022, 203, 103383. [Google Scholar] [CrossRef]
- Müller, S.; Penzkofer, A.; Polyanskii, N.; Theis, J.; Sanders, W.; Moog, H. Reality-Based UTXO Ledger. Distrib. Ledger Technol.: Res. Pract. 2023, 2, 1–33. [Google Scholar] [CrossRef]
- Popov, S.; et al. The coordicide. 2020, 1–30. Available online: PDF (accessed on 03 June 2024).
- Ferraro, P.; Penzkofer, A.; King, C.; Shorten, R. Feedback Control for Distributed Ledgers: An Attack Mitigation Policy for DAG-Based DLTs. IEEE Trans. Autom. Control 2024, 1–8. [Google Scholar] [CrossRef]
- Minhas, N.N.; Mubeen, M.W.; Khawaja, H. Distributed Ledger Technologies for Electronic Health Care: IOTA-Based Remote Patient Monitoring and Telemedicine System. Computer 2023, 56, 31–39. [Google Scholar] [CrossRef]
- Niebla-Montero, Á.; Froiz-Míguez, I.; Varela-Barbeito, J.; Fraga-Lamas, P.; Fernández-Caramés, T.M. IOTA and Smart Contract Based IoT Oxygen Monitoring System for the Traceability and Audit of Confined Spaces in the Shipbuilding Industry. Eng. Proc. 2023, 58, 120. [Google Scholar] [CrossRef]
- Akhtar, M.M.; Rizvi, D.R.; Ahad, M.A.; Kanhere, S.S.; Amjad, M.; Coviello, G. Efficient Data Communication Using Distributed Ledger Technology and IOTA-Enabled Internet of Things for a Future Machine-to-Machine Economy. Sensors 2021, 21, 4354. [Google Scholar] [CrossRef] [PubMed]
- Sealey, N.; Aijaz, A.; Holden, B. IOTA Tangle 2.0: Toward a Scalable, Decentralized, Smart, and Autonomous IoT Ecosystem. International Conference on Smart Applications, Communications and Networking (SmartNets), Palapye, Botswana, 2022, pp. 1–8.
- Apatu, E.; Goudar, P. Bitcoin Use Cases: A Scoping Review. Challenges 2024, 15, 15. [Google Scholar] [CrossRef]
- Kushwaha, S.S.; Joshi, S.; Singh, D.; Kaur, M.; Lee, H.-N. Ethereum Smart Contract Analysis Tools: A Systematic Review. IEEE Access 2022, 10, 57037–57062. [Google Scholar] [CrossRef]
- Ucbas, Y.; Eleyan, A.; Hammoudeh, M.; Alohaly, M. Performance and Scalability Analysis of Ethereum and Hyperledger Fabric. IEEE Access 2023, 11, 67156–67167. [Google Scholar] [CrossRef]
| Ref. | Focus Area | Key Contributions | DLT | SC | Limitations |
|---|---|---|---|---|---|
| [45] | BC-based monolithic secure mechanism for SDN. | Decentralizing control planes, ensuring authenticity and accountability of application flows, access control mechanisms, and integrating secure protocols with SCs. | BC |  |
Potential scalability challenges, performance overhead, SC complexity, and interoperability issues. The type of SCs used is not specified. |
| [46] | Forensic SDN-IoT architecture with BC. | Enhancing security and efficiency in digital forensics, ensuring data integrity, preventing tampering, and securing the chain of custody for digital evidence. | BC |  |
Potential scalability challenges and overhead of BC integration in large-scale SDN environments. |
| [47] | BC-enabled packet parser architecture. | Enhancing security in SDN through FPGA hardware, efficient attack detection, a low false positive rate, and a high detection rate. | BC |  |
Scalability challenges inherent in BC implementation at the data plane level of SDN networks. |
| [48] | Integration of BC with SDN for smart cities. | Addressing challenges in smart cities, enhancing data transmission efficiency and security, and improving bandwidth capabilities and flexibility. | BC |  |
Complexity and potential overhead introduced by integrating BC technology into SDN infrastructures. |
| [49] | BC-based privacy-preserving protocol for SDN. | Addressing ARP poisoning and DDoS attacks, enhancing network reliability, safety, and decentralization, and reducing delay and bandwidth. | BC |  |
Potential scalability and performance challenges for real-world network operations. |
| [50] | BC-based security framework for Northbound Interface in SDN. | Enhancing security by addressing confidentiality, integrity, and availability, authenticating applications and SDN controllers, and enforcing access control policies. | BC |  |
Potential challenges related to scalability, performance overhead, and the computational resources required for BC operations. |
| [51] | Network optimization and security in BC-enabled SDN and IoT. | Secure storage and access for task scheduling, the development of proof-of-authentication mechanisms, cooperative traffic control, and ML-based action recommenders. | BC |  |
Challenge of scalability and performance issues for large-scale Infrastructure Networks. |
| Our System | IOTA 2.0 SCs for Securing SDN. | Introducing a novel approach to secure SDN environments using IOTA Tangle, leveraging smart contracts for authority, access control, and DoS detection | IOTA Tangle |  |
Potential reduction in quality of service, increased latency, and impact on data traffic due to the integration of the DoS Detector smart contract |
| Feature/ | IOTA 2.0 | Bitcoin | Ethereum | Hyperledger |
|---|---|---|---|---|
| Criteria | ||||
| Transaction | Up to 1,000 TPS | 3-7 TPS | 15-30 TPS | 1,000-10,000 TPS |
| Speed | (varies by implementation) | |||
| Scalability | High | Low | Low | Low |
| Energy | Very low | High | Medium-High | Low to Medium |
| Consumption | ||||
| Consensus | FPC binary voting protocol | PoW | PoW, transitioning to PoS | PBFT variants, Raft, etc. |
| Mechanism | ||||
| Security | EdDSA | ECDSA | ECDSA | ECDSA |
| Protocols | ||||
| Decentralization | Fully decentralized | Fully decentralized | Fully decentralized | Permissioned (Partially decentralized) |
| SC Support |  |
 |
 |
 |
| SC Speed | Fast execution (parallel Transactions) | - | Slower execution | Slower execution |
| Micro-transactions |  |
 |
 |
 |
| Transactions fees | Very low | - | High | High |
| Limitations | Early stage of development | Scalability issues, | Scalability issues, | Limited Decentralization, |
| Limited adoption | high energy consumption | gas fees | complexity | |
| Potential network stability issues |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




