Submitted:
09 July 2024
Posted:
10 July 2024
You are already at the latest version
Abstract
Keywords:
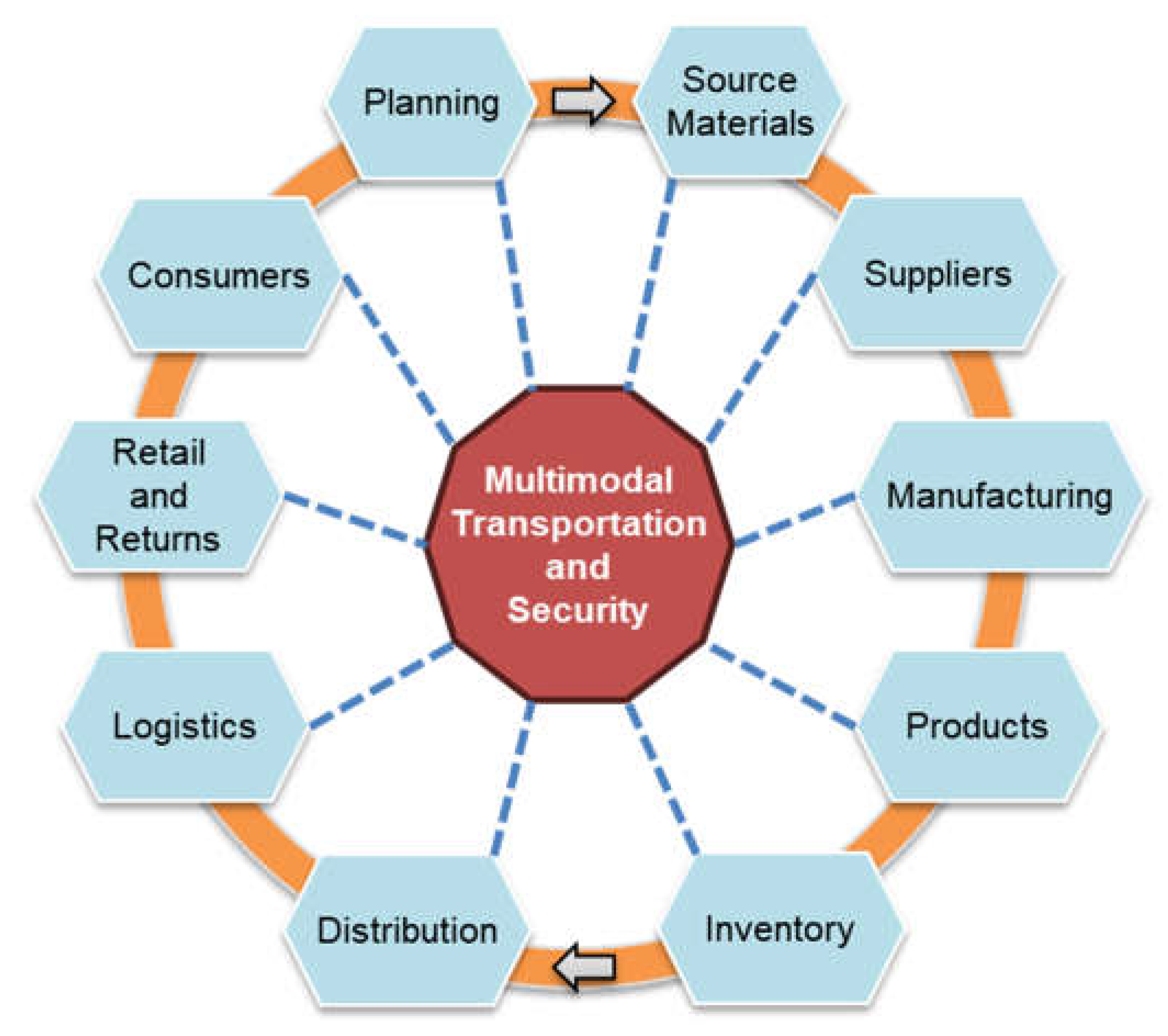
1. Introduction
2. Literature Review
2.1. Themes and Theories
2.2. Historical Perspective
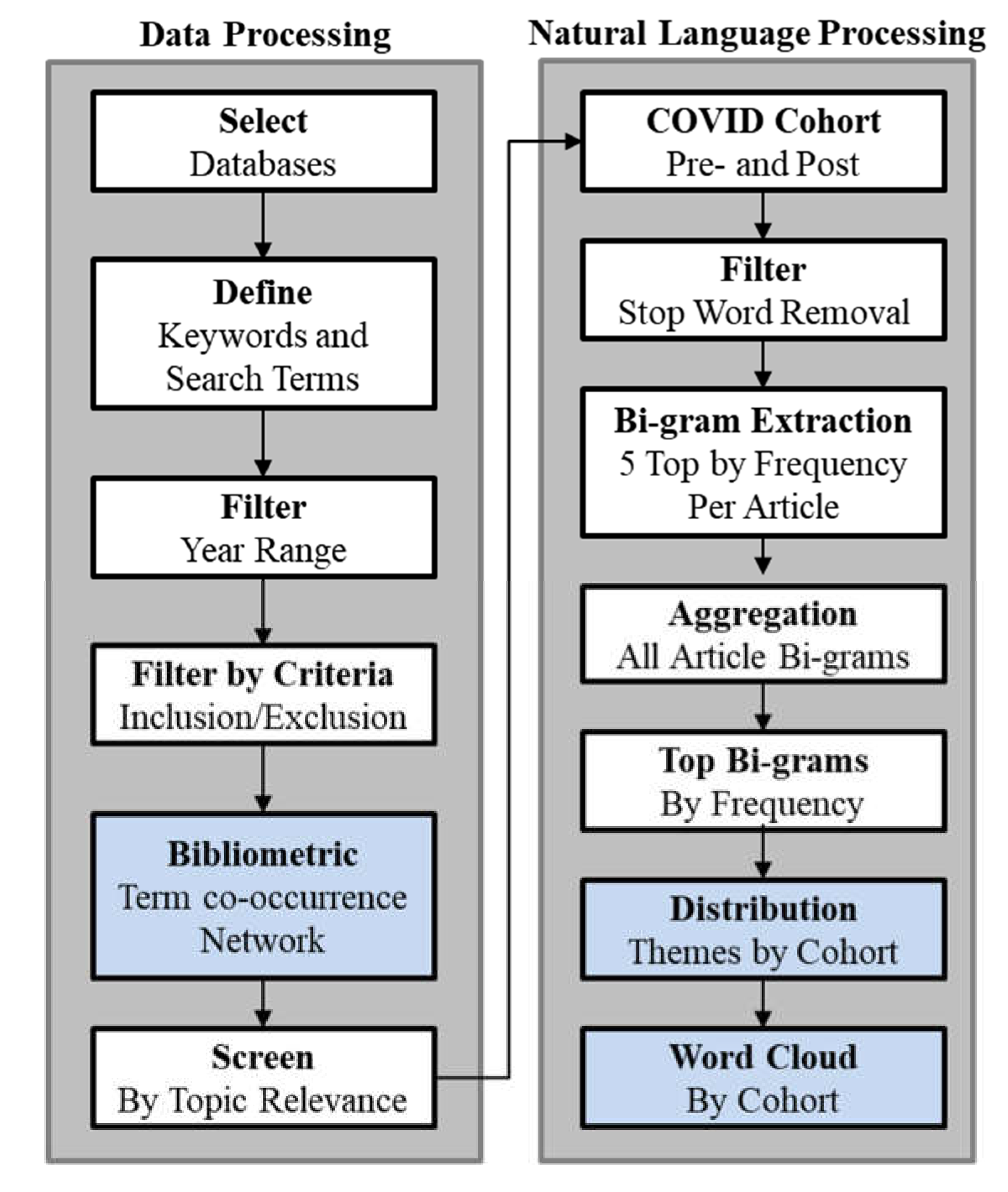
3. Materials and Methods
Database Selection and Search Strategy
Inclusion and Exclusion Criteria
Bibliometric Analysis
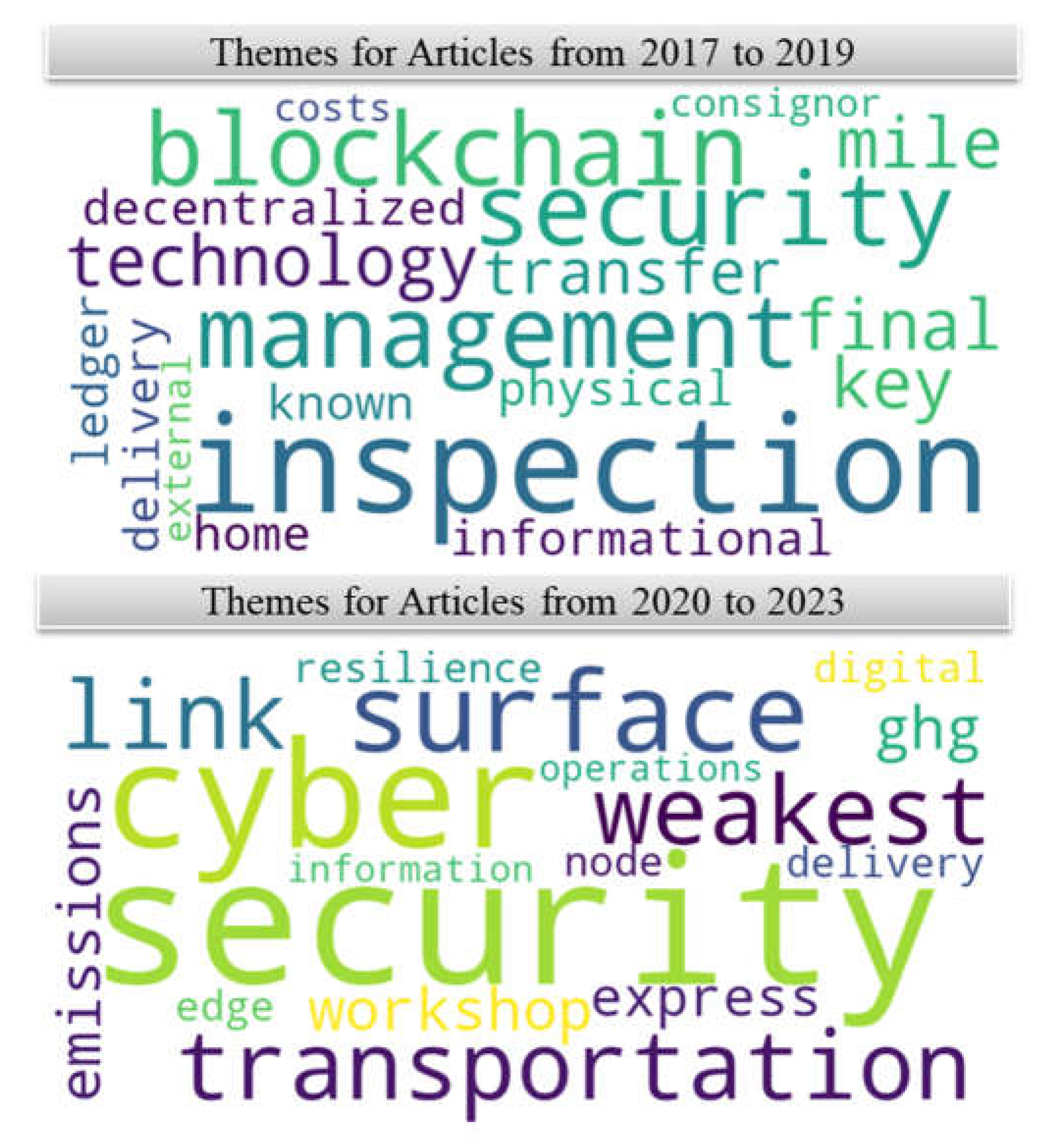
Thematic Categorization
- Stop Word Removal: Filtering out common stop words and irrelevant terms to enhance analytical precision.
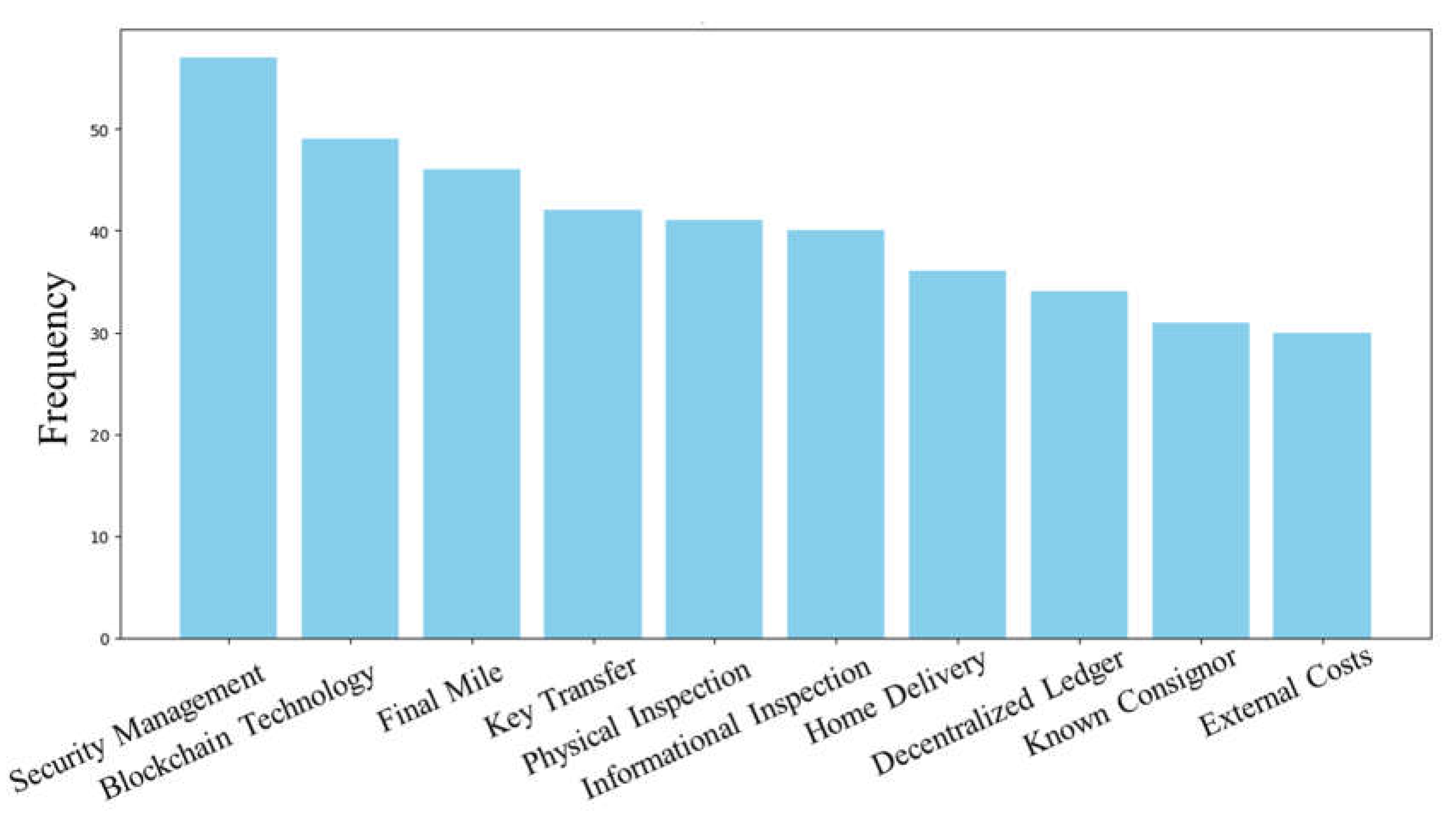
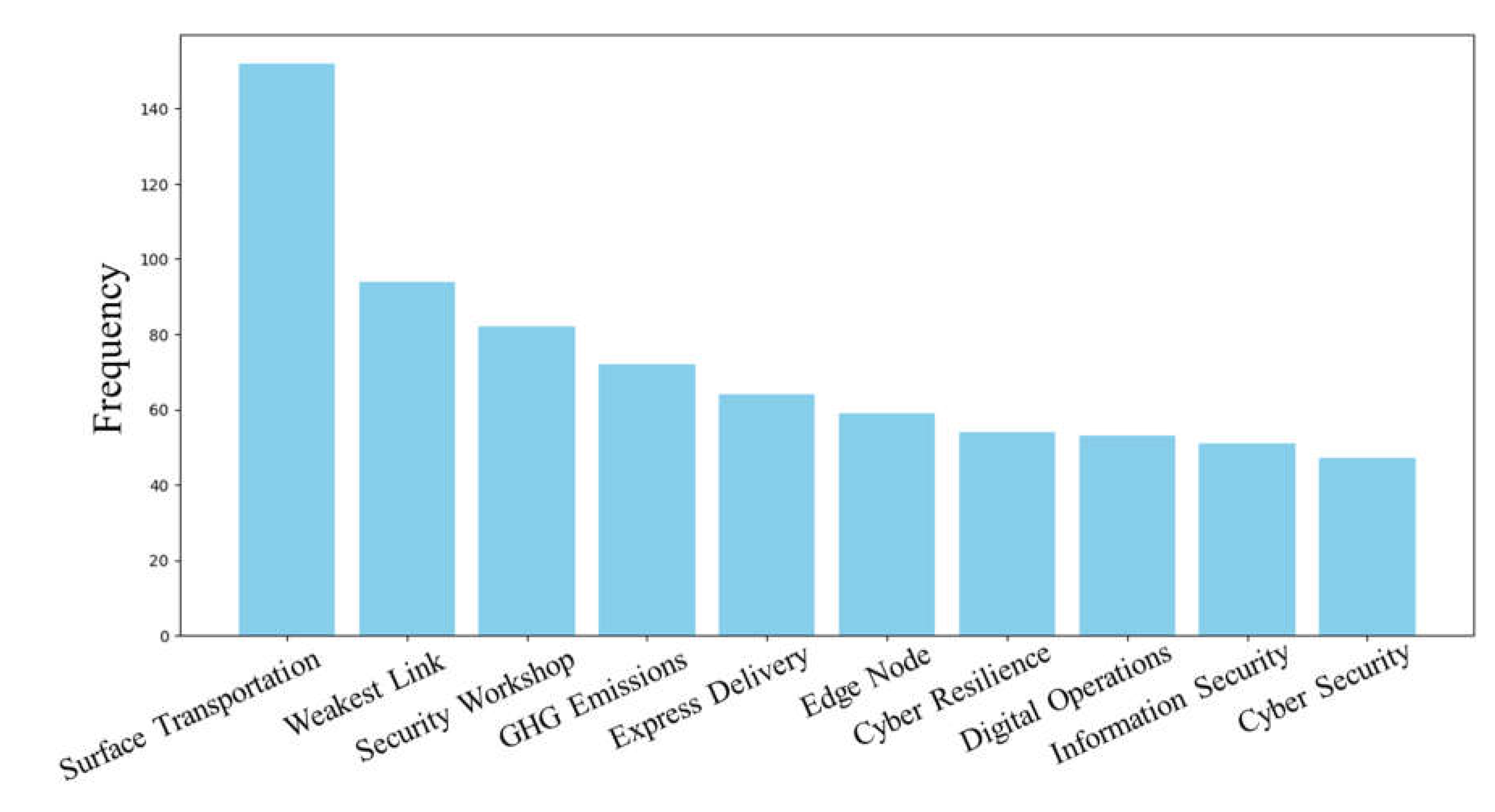
- Bigram Extraction: Identifying the top five bigrams by frequency for each article after applying lemmatization to convert words to their root forms.
- Bigram Aggregation: Pooling extracted bigrams across all articles within each document group and ranking them by frequency.
- Frequency Analysis: Highlighting the most prominent themes and terms within the literature corpus.
- Distribution Analysis: Examining the frequency and context of top bigrams to reveal thematic shifts over time.
- Visualization: Generating word clouds and distribution graphs to visually represent the predominant themes within each temporal cohort.
Algorithmic Workflow
- Step 1: Database Identification—identifying databases rich in relevant research articles.
- Step 2: Keyword Formulation—creating a list of search terms.
- Step 3: Temporal Filter—conducting searches within the specified year range.
- Step 4: Criteria-Based Filtering—screening search results based on inclusion and exclusion criteria.
- Step 5: Bibliometric Analysis—generating term co-occurrence networks.
- Step 6: Topical Relevance Filtering—ensuring selected literature contributes meaningfully to the objectives of the study.
- Step 1: Corpus Bifurcation—segmenting literature into pre- and post-COVID temporal cohorts for trend analysis.
- Step 2: Stop Word Removal—enhancing focus on content-rich words.
- Step 3: Bigram Extraction—identifying significant word pairs.
- Step 4: Bigram Aggregation—aggregating and ranking bigrams by frequency.
- Step 5: Frequency Analysis—highlighting prominent themes.
- Step 6: Distribution Analysis—identifying thematic shifts over time.
- Step 7: Visualization—creating word clous visual representations of thematic data.
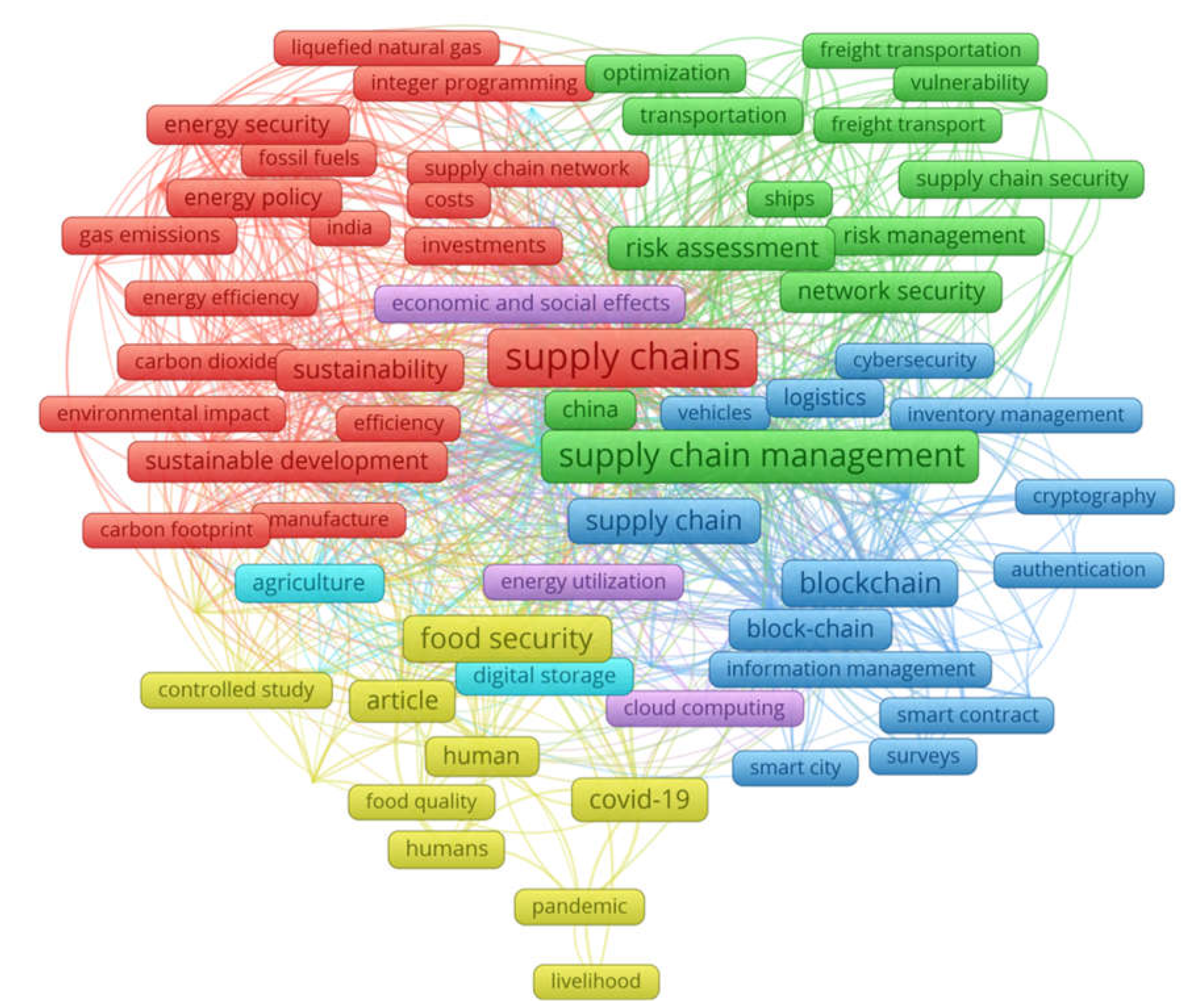
4. Results
- Red Cluster: the main themes are sustainability and energy with key terms including “energy security,” “sustainable development,” “carbon footprint,” and “environmental impact.”
- Green Cluster: the main themes are risk and security within the supply chain with key terms being “supply chain security,” “risk assessment,” “network security,” and “freight transportation.”
- Blue Cluster: the main themes are technology and data management with key terms being “blockchain,” “cybersecurity,” “internet of things,” and “smart contract.”
- Yellow Cluster: the main themes are food security and the impacts of the COVID-19 pandemic with key terms being “food quality,” “pandemic,” and “livelihood.”
- Purple Cluster: the main themes are economic and social effects with key terms being “energy utilization,” and “health care.”
| Category | Theme | Sample Articles |
|---|---|---|
| Emerging Technologies | Blockchain and biometrics are pivotal in enhancing security and transparency in transportation | [1,4,5,26,27,28,29,39,40,41,46,47,48] |
| Environmental Considerations | Integrating environmental sustainability with security in transportation is crucial for resilient supply chains. | [49,50] |
| E-commerce Challenges | The surge in e-commerce demands innovative security strategies for efficient and safe package delivery. | [51,52] |
| Standardization and Regulation Needs | Consistent standards and regulations are vital for ensuring security, especially in international supply chains. | [30,35,36,37,53,54,55] |
| Practical Insights from Real-World Scenarios | Empirical studies offer valuable insights into the practical challenges and potentials of transportation security systems. | [10,31,32,33,34,56,57,58] |
5. Discussion
6. Conclusion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- V. А. Kulik, V. Y. Marchuk, O. M. Harmash, O. V. Karpun and N. M. Perederii, "Security Management of Intermodal Transportation in Conditions of Sustainable Development of Global Supply Chains," Electronic Scientific and Practical Publication in Economic Sciences, pp. 45-56, 2022.
- S. H. Zailani, K. S. Subaramaniam, M. Iranmanesh and M. R. Shaharudin, "The impact of supply chain security practices on security operational performance among logistics service providers in an emerging economy: Security culture as moderator," International Journal of Physical Distribution & Logistics Management, vol. 45, no. 7, pp. 652-673, 2015. [CrossRef]
- U. G. Okafor, M. A. Olalaye, H. C. Asobara and E. F. Umeodinka, "Global impact of COVID-19 pandemic on public health supply chains," in Science-Based Approaches to Respond to COVID and Other Public Health Threats, E. Guerrero, Ed., IntechOpen, 2021, p. 280.
- S. K. Nanda, S. K. Panda and M. Dash, "Medical supply chain integrated with blockchain and IoT to track the logistics of medical products." Multimedia Tools and Applications," vol. 82, p. 32917–32939, 2023.
- I. G. Koliousis, U. Tanveer and S. Ishaq, "A Conceptual Information Sharing Framework to Improve Supply Chain Security Collaboration," International Journal of Value Chain Management, vol. 11, no. 4, pp. 346-365, 2020.
- T. P. Stank and T. J. Goldsby, "A Framework for Transportation Decision Making in an Integrated Supply Chain," Supply Chain Management: An International Journal, vol. 5, no. 2, pp. 71-78, 2000. [CrossRef]
- Y.-C. Yang, "Impact of the container security initiative on Taiwan's shipping industry," Maritime Policy & Management, vol. 37, no. 7, pp. 699-722, 2010.
- J. E. Gould, C. Macharis and H.-D. Haasis, "Emergence of security in supply chain management literature," Journal of Transportation Security, vol. 3, pp. 287-302, 2010.
- S. Chopra and P. Meindl, Supply Chain Management: Strategy, Planning, and Operation, Pearson, 2014, p. 516.
- M. T. Alshurideh, B. A. Kurdi, A. A. Alzoubi and M. Al-Okaily, "The Impact of Transportation Reliability on Supply Chain Efficiency at UAE Maritime Industry," International Journal of Business Analytics and Security, vol. 2, no. 1, pp. 141-154, 2022.
- W. Schivelbusch, The Railway Journey: The Industrialization of Time and Space in the Nineteenth Century, University of California Press, 2014, p. 248.
- A. Casadevall, "Antibody-based vaccine strategies against intracellular pathogens," Current Opinion in Immunology, vol. 53, pp. 74-80, 2018.
- E. Candra, A. Azmi and A. Gunawati, "Position and Protection of Association Rights Security Unit in Human Rights Perspective According to the Basic State Law of the Republic of Indonesia Year 1945," JHR (Jurnal Hukum Replik), vol. 9, no. 2, pp. 157-171, 2021.
- G. Flitton, T. P. Breckon and N. Megherbi, "A 3D extension to cortex like mechanisms for 3D object class recognition," in 2012 IEEE Conference on Computer Vision and Pattern Recognition, Providence, RI, USA, 2012.
- G. Blalock, V. Kadiyali and D. H. Simon, "The impact of post-9/11 airport security measures on the demand for air travel," The Journal of Law and Economics, vol. 50, no. 4, pp. 731-755, 2007.
- P. Seidenstat, "Terrorism, airport security, and the private sector," Review of Policy Research, vol. 21, no. 3, pp. 275-291, 2004.
- E. KARŞIGİL and A. T. E. Ş. Savaş, "Security Control Process Modeling During the Covid-19 Pandemic: Example Of Esenboğa Airport," Akıllı Ulaşım Sistemleri ve Uygulamaları Dergisi, vol. 5, no. 2, pp. 188-199, 2022.
- R. Holz, Y. Sheffer and P. Saint-Andre, "Recommendations for secure use of transport layer security (TLS) and datagram transport layer security (DTLS)," RFC 7525, 2015.
- S. Nižetić, P. Šolić, D. L.-d.-I. Gonzalez-De and L. Patrono, "Internet of Things (IoT): Opportunities, issues and challenges towards a smart and sustainable future," Journal of Cleaner Production, vol. 274, p. 122877, 2020. [CrossRef]
- F. Wang, L. P. Casalino and D. Khullar, "Deep learning in medicine—promise, progress, and challenges," JAMA internal medicine, vol. 179, no. 3, pp. 293-294, 2019.
- C. Morosan, "Theoretical and empirical considerations of guests’ perceptions of biometric systems in hotels: Extending the technology acceptance model," Journal of Hospitality & Tourism Research, vol. 36, no. 1, pp. 52-84, 2012.
- D. Nyale and S. M. Angolo, "A Survey of Artificial Intelligence in Cyber Security," International Journal of Computer Applications Technology and Research, vol. 11, no. 12, pp. 474-477, 2022.
- M. Nikita, L. Kashyap, B. P. Singh and D. Tyagi, "AI Enabled Advance Surveillance System," International Research Journal of Modernization in Engineering Technology and Science, vol. 5, no. 4, 2023.
- Y. Yu and, S. Lee, "Remote driving control with real-time video streaming over wireless networks: Design and evaluation," IEEE Access, vol. 10, pp. 64920-64932, 2022.
- M. Lou, X. Dong, Z. Cao and J. Shen, "SESCF: A Secure and Efficient Supply Chain Framework Via Blockchain-Based Smart Contracts," Security and Communication Networks, pp. 1-18, 2021.
- A. Shahzad, K. Zhang and A. Gherbi, "Intuitive development to examine collaborative IoT supply chain system underlying privacy and security levels and perspective powering through proactive blockchain," Sensors, vol. 20, no. 13, p. 3760, 2020.
- X. Zhang, P. Sun, J. Xu, X. Wang, J. Yu, Z. Zhao and Y. Dong, "Blockchain-based safety management system for the grain supply chain," IEEE Access, vol. 8, pp. 36398-36410, 2020.
- V. V. Nair, "Drones as Futuristic Crime Prevention Strategy: Situational Review During COVID-19 Lockdown," Journal of Social Sciences, vol. 64, no. 1-3, pp. 22-29, 2020.
- M. Kunovjanek and C. Wankmüller, "Containing the COVID-19 pandemic with drones-Feasibility of a drone enabled back-up transport system," Transport Policy, vol. 106, pp. 141-152, 2021.
- D. Asamoah, D. Nuertey, B. Agyei-Owusu and I. N. Acquah, "Antecedents And Outcomes of Supply Chain Security Practices: The Role of Organizational Security Culture and Supply Chain Disruption Occurrence," International Journal of Quality & Reliability Management, vol. 39, no. 4, pp. 1059-1082, 2022.
- F. D. G. Solfa, "Impacts of Cyber Security and Supply Chain Risk on Digital Operations: Evidence from the Pharmaceutical Industry," International Journal of Technology, Innovation and Management, vol. 2, no. 2, 2022.
- M. T. Alshurideh, E. K. Alquqa, H. M. Alzoubi, B. A. Kurdi and S. Hamadneh, "The effect of information security on e-supply chain in the UAE logistics and distribution industry,". Uncertain Supply Chain Management, vol. 11, no. 1, pp. 145-152, 2023.
- P. Kang, G. Song, M. Xu, T. R. Miller, H. Wang, H. Zhang, G. Liu, Y. Zhou, J. Ren, R. Zhong and H. Duan, "Low-carbon pathways for the booming express delivery sector in China," Nature Communications, vol. 12, no. 1, p. 450, 2021.
- J. S. Szyliowicz, "International transportation security," Review of Policy Research, vol. 21, no. 3, pp. 351-368, 2004.
- E. Kusrini and K. Hanim, "Analysis of compliance and supply chain security risks based on ISO 28001 in a logistic service provider in Indonesia," International Journal of Safety and Security Engineering, vol. 11, no. 2, pp. 135-142, 2021.
- M. Jażdżewska-Gutta and P. Borkowski, "As strong as the weakest link. Transport and supply chain security," Transport Reviews, vol. 42, no. 6, pp. 762-783, 2022.
- M. Pourakbar and R. A. Zuidwijk, "The role of customs in securing containerized global supply chains," European Journal of Operational Research, vol. 271, no. 1, pp. 331-340, 2018.
- J. Zhao, X. Liu, Q. Yan, B. Li, M. Shao, H. Peng and L. Sun, "Automatically predicting cyber attack preference with attributed heterogeneous attention networks and transductive learning," Computers & Security, vol. 102, p. 102152, 2021.
- O. Pozniak and, K. Yurchenko, "Formation of the optimal business model of a logistics company," Intellectualization of Logistics and Supply Chain Management, vol. 10, pp. 19-36, 2021.
- N. De Liso and L. Zamparini, "Innovation, transport security and supply chains: a review," Transport Reviews, vol. 42, no. 6, pp. 725-738, 2022.
- L. Zamparini, "A review of models for transport security and of their relevance for supply chains," Transport Reviews, vol. 42, no. 6, pp. 784-800, 2022.
- F. L. Edwards and D. C. Goodrich, Introduction to transportation security., 2nd ed., Boca Raton, Florida: CRC Press, 2024.
- M. J. Page, J. E. McKenzie, P. M. Bossuyt, I. Boutron, T. C. Hoffmann, C. D. Mulrow, L. Shamseer, J. M. Tetzlaff, E. A. Akl, S. E. Brennan, J. G. Roger Chou, J. M. Grimshaw, A. Hróbjartsson, M. M. Lalu, T. Li, E. W. Loder, E. Mayo-Wilson, S. McDonald, L. A. McGuinness, L. A. Stewart, J. Thomas, A. C. Tricco, V. A. Welch, P. Whiting and D. Moher, "The PRISMA 2020 statement: an updated guideline for reporting systematic reviews," Systematic Reviews, vol. 10, no. 89.
- N. J. v. Eck and L. Waltman, "VOSviewer," Leiden University, 1 July 2024. [Online]. Available: vosviewer.com. [Accessed 30 June 2024.
- C. C. Aggarwal, Data Mining, New York, New York: Springer International Publishing, 2015, p. 734.
- A. Lei, H. Cruickshank, Y. Cao, P. Asuquo, C. P. A. Ogah and Z. Sun, "Blockchain-based dynamic key management for heterogeneous intelligent transportation systems," IEEE Internet of Things Journal, vol. 4, no. 6, pp. 1832-1843, 2017.
- L. A. Ajao, J. Agajo, E. A. Adedokun and L. Karngong, "Crypto hash algorithm-based blockchain technology for managing decentralized ledger database in oil and gas industry," J (Multidisciplinary Scientific Journal), vol. 2, no. 3, pp. 300-325, 2019.
- T. Reeb, Ed., Empowering the New Mobility Workforce: Educating, Training, and Inspiring Future Transportation Professionals, Amsterdam, Netherlands: Elsevier, 2019.
- K. Zavitsas, T. Zis and M. G. Bell, "The impact of flexible environmental policy on maritime supply chain resilience," Transport Policy, vol. 72, pp. 116-128, 2018.
- C.-M. Pintea, A. Calinescu, C. P. Sitar and P. C. Pop, ""Towards secure & green two-stage supply chain networks," Logic Journal of the IGPL, vol. 27, no. 2, pp. 137-148, 2019.
- H. E. Seaton, "The new e-commerce/home delivery retail distribution paradigm," Journal of Transportation Management, vol. 29, no. 1, pp. 7-25, 2018.
- F. Arnold, I. Cardenas, K. Sörensen and W. Dewulf, "Simulation of B2C e-commerce distribution in Antwerp using cargo bikes and delivery points," European Transport Research Review, vol. 10, no. 2, pp. 1-13, 2018.
- L. Urciuoli, "The risk of standards proliferation–An analysis of differences between private and public transport standards," Transportation research part A: policy and practice, vol. 116, pp. 591-602, 2018.
- M. Pourakbar and R. A. Zuidwijk, "The role of customs in securing containerized global supply chains," European Journal of Operational Research, vol. 271, no. 1, pp. 331-340, 2018.
- X. Tong, C. K. Lo, K.-h. Lai and T. C. E. Cheng, "Supply chain security management: a citation network analysis," International Journal of Shipping and Transport Logistics, vol. 11, no. 6, pp. 508-532, 2019.
- A. Sidebottom, A. Thornton, L. Tompson, J. Belur, N. Tilley and K. Bowers, "A systematic review of tagging as a method to reduce theft in retail environments," Crime science, vol. 6, no. 7, pp. 1-17, 2017.
- A. Khaslavskaya and, V. Roso, "Outcome-driven supply chain perspective on dry ports," Sustainability, vol. 11, no. 5, p. 1492, 2019.
- D. T. Fokum, V. S. Frost, M. Kuehnhausen, D. DePardo, A. N. Oguna, L. S. Searl, E. Komp, M. Zeets, D. D. Deavours, J. B. Evans and G. J. Minden, "An open-system transportation security sensor network: Field-trial experiences," IEEE transactions on vehicular technology, vol. 59, no. 8, pp. 3942-3955, 2010.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




