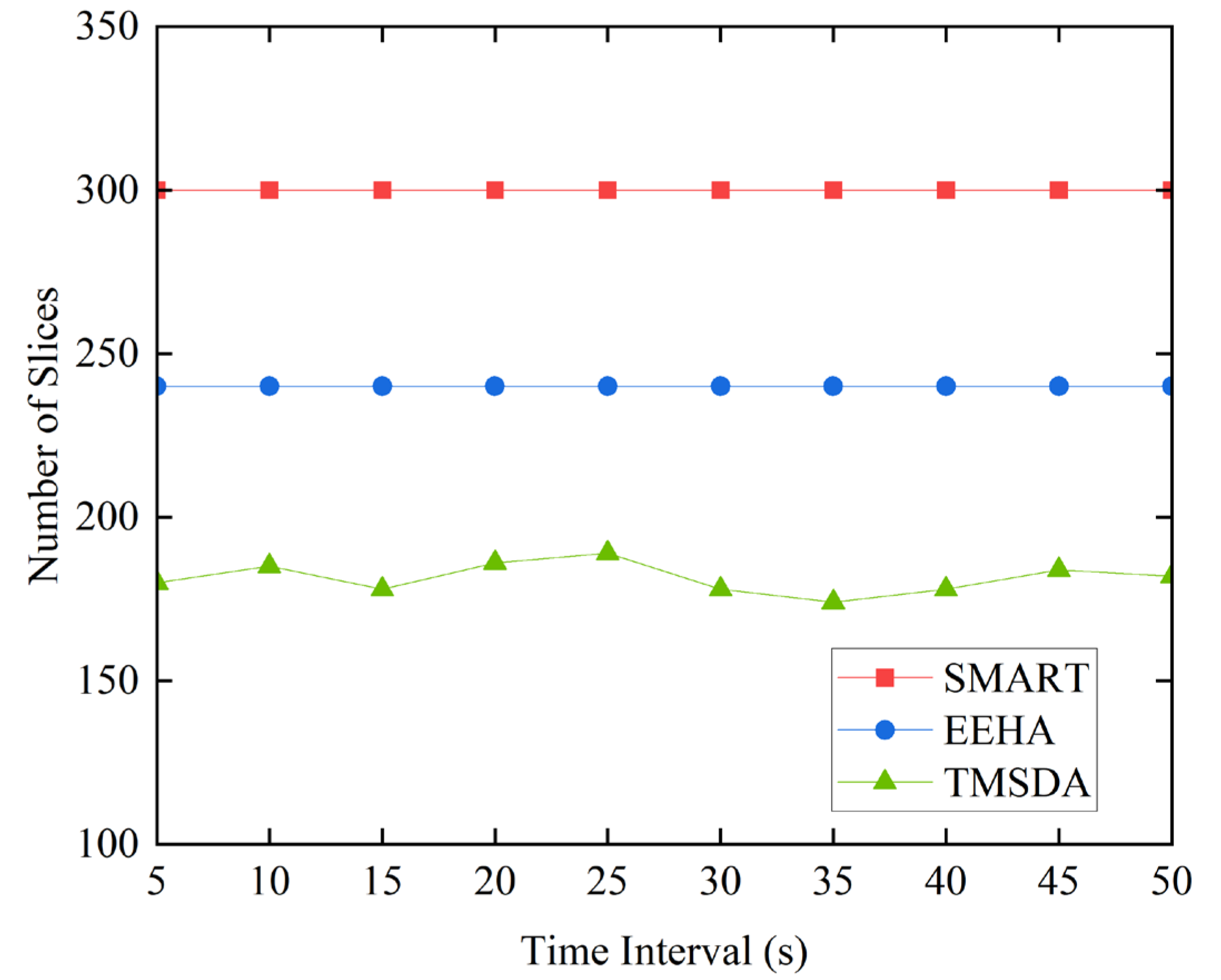
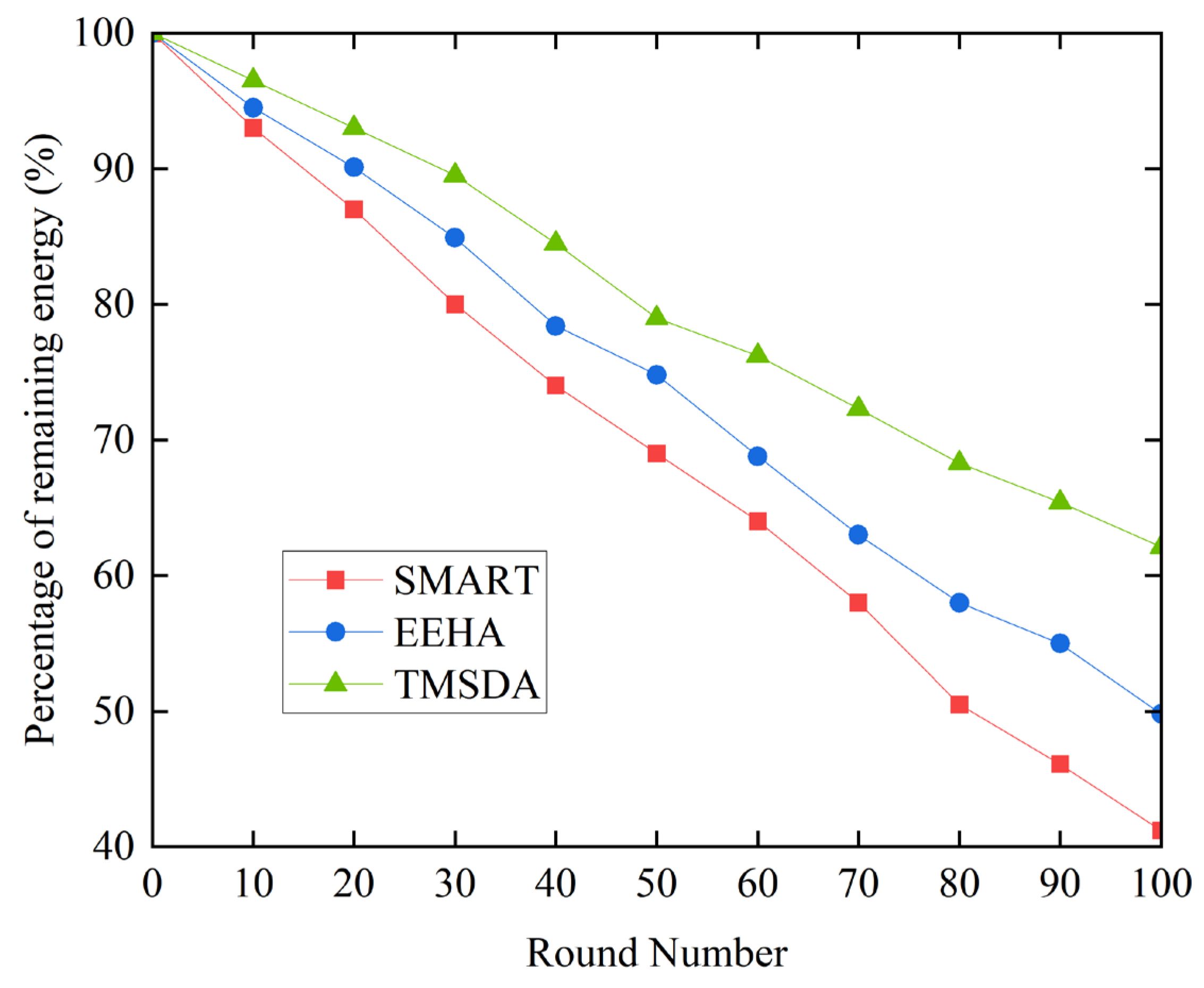
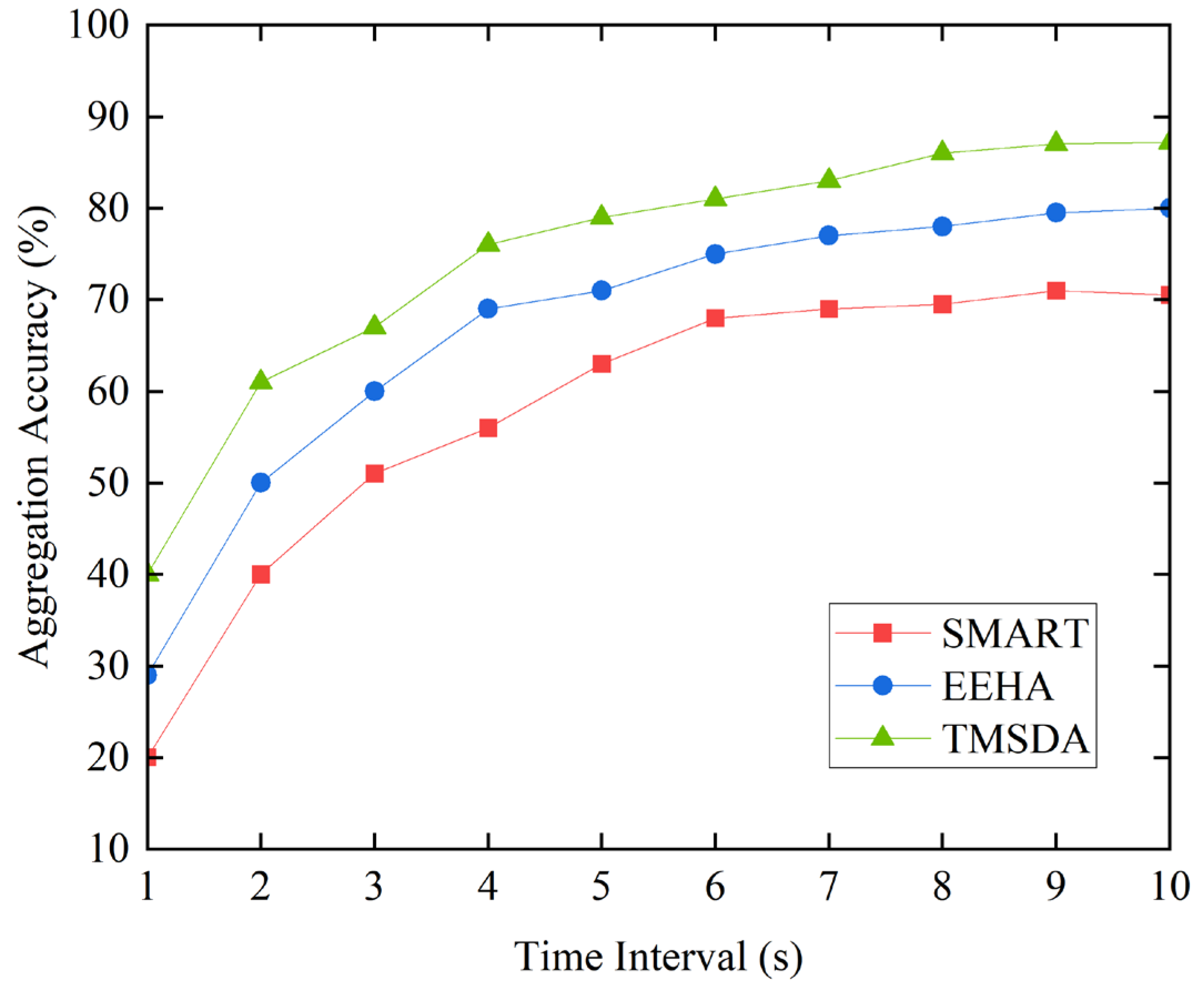
4. TMSDA Algorithm
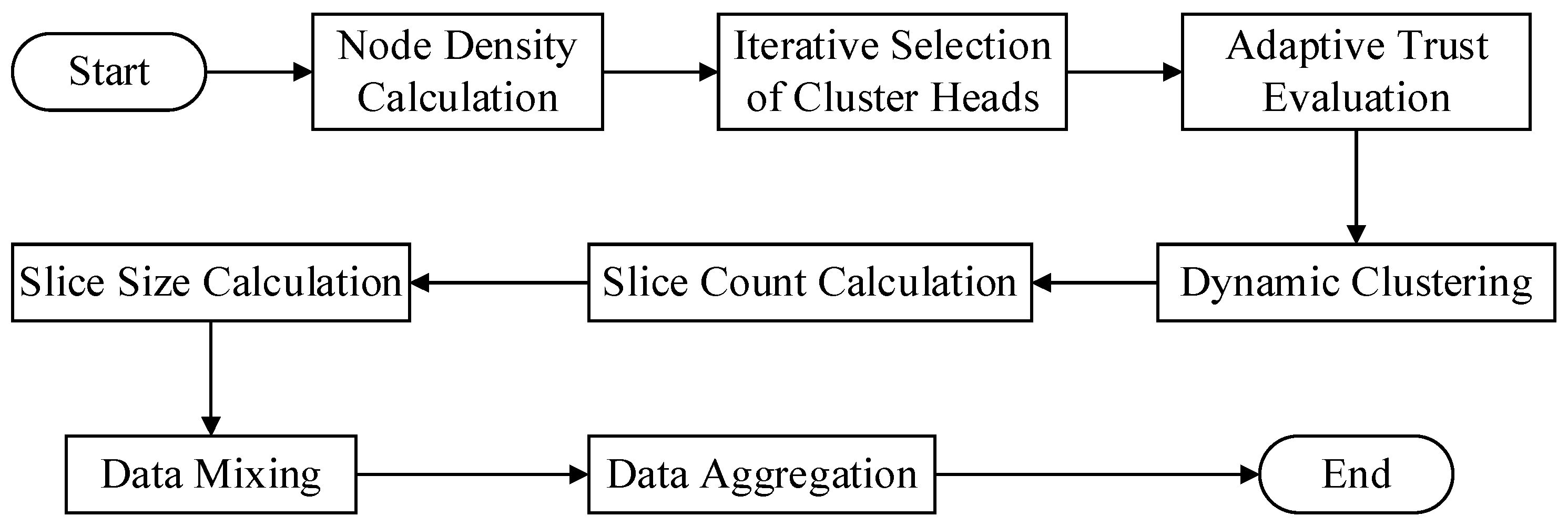
This work proposes a data aggregation algorithm that is based on a trust mechanism. It may be broadly classified into four stages.
Figure 1 shows the specific algorithm flow.
(1) Dynamic clustering stage: At this stage, the algorithm determines each node's local density throughout the network and uses that information to dynamically choose cluster head nodes. Once every cluster head node in the network has been selected, the cluster is formed by each cluster head node selecting cluster member nodes based on their trust value toward neighboring nodes.
(2) Dynamic slicing stage: In this stage, cluster member nodes determine the number of slices based on the trust value assigned by the cluster head node. Nodes with higher trust values receive fewer slices. Simultaneously, the size of the slices is adjusted according to the transmission distance between nodes, with distant nodes receiving smaller slices and closer nodes receiving larger ones. Finally, each cluster member retains one data slice and encrypts the remaining slices before randomly sending them to other neighboring nodes within the cluster.
(3) Data mixing stage: During this stage, A node builds a new mixed data packet by receiving encrypted data slices from other nodes, decrypting them with a shared key, and combining them with its own retained slice.
(4) Data aggregation stage: In this stage, cluster member nodes encrypt mixed data packets with a shared key before sending them to the cluster head node. The cluster head node collects all encrypted data slices from cluster members, performs decryption and aggregation operations to generate the final aggregated output, and then uploads it layer by layer to the base station.
4.1. Dynamic Clustering
In underwater environments, the distribution of sensor nodes often exhibits a random and dynamic nature. These nodes may constantly change their positions due to the influence of water currents, the activities of marine organisms, or interference from other external factors. This dynamic change in position undoubtedly poses numerous challenges to the construction and maintenance of underwater wireless sensor networks. One significant issue is the notable difference in node density across various regions within the network. This uneven node distribution directly affects the efficiency and energy consumption of data transmission. To address this problem, we propose a cluster head selection strategy based on node density. The core idea of this strategy is to optimize the network topology by selecting nodes located in high-density areas as cluster heads, thereby improving data transmission efficiency and reducing energy consumption. Our approach comprehensively considers the local density information of nodes to ensure that the selected cluster heads can effectively shorten the data transmission distance between cluster members.
Prior to putting this technique into practice, we determine each node's node density. The number of nearby nodes that are within a sensor node's communication range is usually used to compute node density, a crucial indicator that assesses the concentration of other nodes around the node. If a node is surrounded by more neighboring nodes, its node density is relatively high. High node density implies closer distances between nodes, which offers significant advantages during data transmission. Shorter distance communication requires less transmission power, effectively reducing energy consumption while enhancing communication reliability.
Our technique first determines the density of each node and then chooses nodes in high-density areas to be the cluster heads. This strategy has several advantages. First off, because data may reach the cluster head and be transmitted to its destination more quickly, it helps minimize the number of hops needed for data transmission. Second, there can be a significant reduction in the energy usage during communication because of the shorter distance between the cluster head and cluster members. Lastly, our approach can also improve the network's overall performance by improving the network architecture, which will make the network more stable and robust.
Once the cluster head is selected, it invites trustworthy nodes to join its cluster based on its trust evaluation of neighboring nodes. This dynamic cluster formation mechanism not only considers the density factor of nodes but also ensures the trustworthiness and security of cluster members. Through this approach, our method can better adapt to various complex situations in underwater environments, guaranteeing the safety and reliability of data transmission.
In summary, our proposed cluster head selection strategy based on node density is an effective solution that addresses the issues of uneven node distribution and high energy consumption during data transmission in underwater environments. The particular procedure is as follows:
(1) Node Density Calculation
The density
of each node
in the network is expressed by finding the number of surrounding nodes
that are within its communication range:
where
is the number of members in node
's set of surrounding nodes.
(2) Cluster Head Selection
Choose the node with the highest density as the initial cluster head, node , based on the density of each node in the network. To prevent the chosen cluster head from having an influence, the density of the other nodes must be updated after the first cluster head, node , is chosen. The purpose of updating is to reduce the density of nodes adjacent to the selected cluster head, thereby reducing their likelihood of becoming the next cluster head and avoiding excessive concentration of selected cluster heads in the network.
(3) Density Update
For each node other than the first cluster head node
, update the density based on its distance from the selected cluster head node
. The updated density
can be expressed as:
Where
is an adjustment parameter used to control the extent of density reduction, and
is a distance-related attenuation function that decreases with increasing distance. In this paper, a step function of the following form is used to represent it:
Where is the communication radius of node . This means that if a node is within the communication range of , its density will decrease by a fixed amount ; otherwise, the density remains unchanged.
(4) Iterative Cluster Head Selection
Reorder the remaining nodes based on the revised densities , then designate the node with the highest density as the subsequent cluster head . Until the required cluster head count is reached or there are no more available eligible nodes, repeat the density update and cluster head selection procedure.
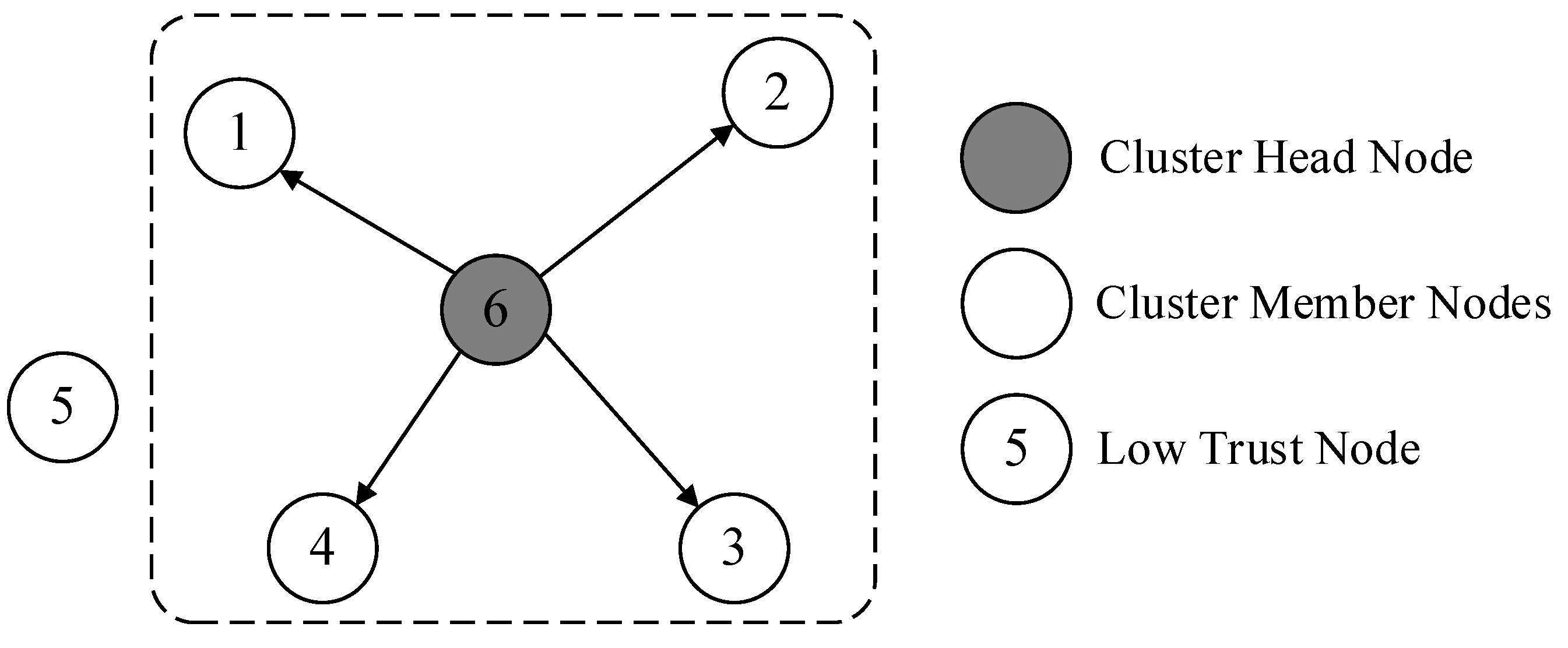
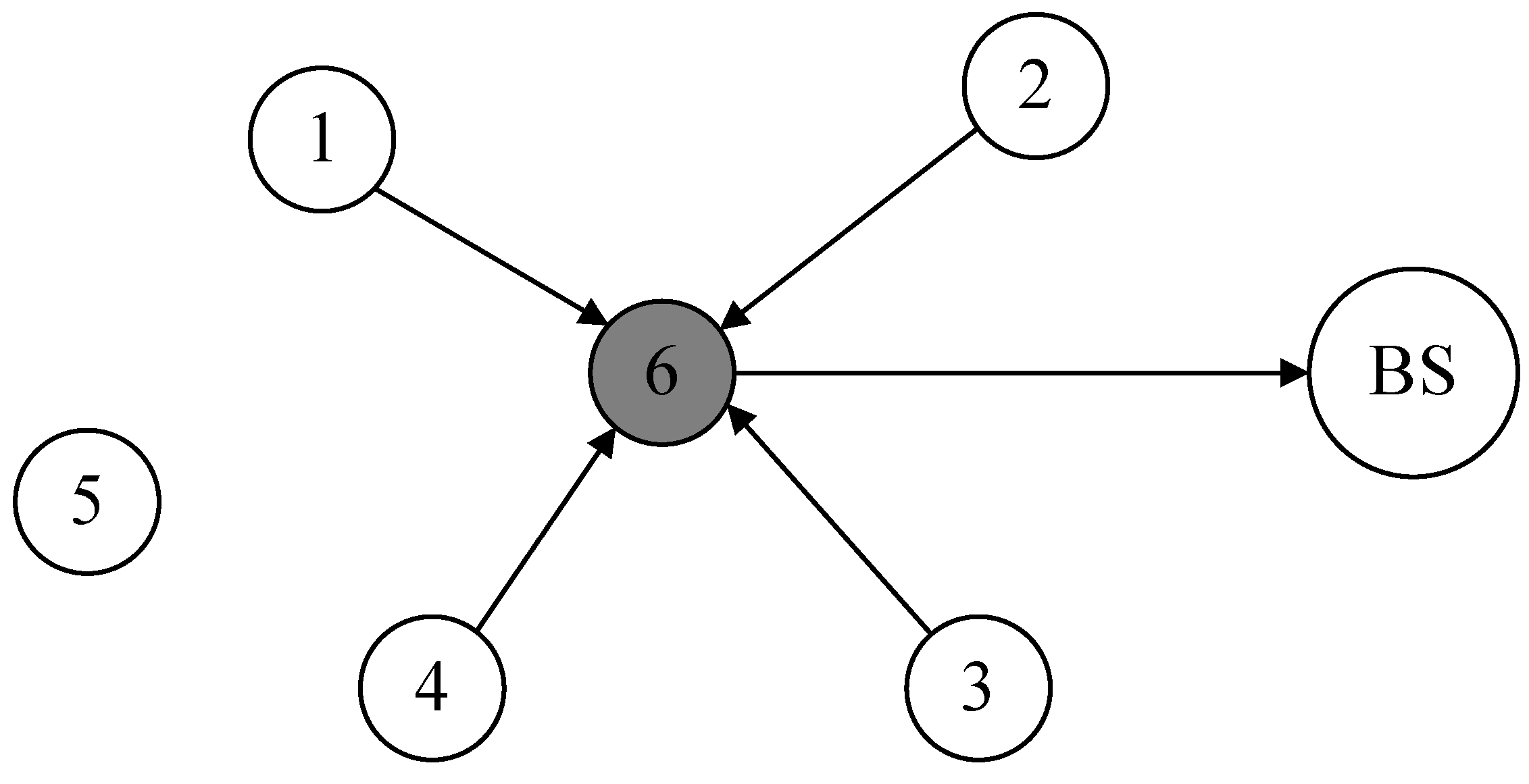
Through the above steps, the selection of all cluster heads in the network is completed. Afterwards, cluster heads recruit neighboring nodes within their communication range to complete the construction of the cluster. When selecting cluster members, cluster heads use the trust evaluation model to calculate the trust values of neighboring nodes. Neighboring nodes with low trust values are not invited to join the cluster, thereby reducing the impact of abnormal nodes on network operation. The cluster building process is shown in
Figure 2.
Furthermore, after a given amount of network operation, it becomes necessary to reselect cluster heads and rebuild clusters using the previously specified procedures due to the constant movement of nodes in the underwater environment, which causes dynamic changes in the network topology.
4.2. Dynamic Slicing
During the dynamic slicing process, cluster head nodes play a crucial role. They perform a variety of functions as the hub of the local network, including as gathering information from cluster member nodes, combining it, and sending the processed data to the base station. In order to maintain efficient information flow, certain cluster head nodes further serve as data relays, transmitting data between cluster heads. These complex operations result in significantly higher energy consumption for cluster head nodes compared to other nodes. As a result, our design specifies that cluster head nodes are simply in charge of data aggregation and do not carry out data slicing tasks.
(1) Determining the Number of Slices
A dynamic slicing technique based on trust values is presented in this study. The core idea of this strategy is to flexibly adjust the number of slices based on trust values, aiming to optimize network performance and data transmission efficiency. Here, the trust value refers specifically to the comprehensive trust assessment made by the cluster head node towards its cluster members. This assessment is multidimensional, considering various critical factors such as link quality, historical behavior of nodes, and their current energy status.
In the dynamic slicing strategy, the level of trust directly determines the number of slices during node data transmission. Specifically, for nodes with higher trust values, we tend to believe that they can complete data transmission tasks more stably and reliably. Therefore, to reduce network complexity and unnecessary overhead, we decrease the number of slices for these nodes. Conversely, for nodes with lower trust values, due to their potential uncertainties and risks, we increase the number of slices to enhance the fault tolerance of data transmission. This way, even if a slice encounters issues during transmission, other slices can still carry partial or complete information to the destination.
Overall, this trust-based dynamic slicing strategy aims to ensure data transmission security, reduce network traffic, and improve overall data transmission efficiency through intelligent adjustment of slices. The specific slicing rules can be represented by the following formula:
where
is the cluster head node's trust value for its cluster member node
,
is the number of slices for node
, and
is the number of node
's adjacent nodes. Different numbers of slices are set for different trust values. Since low-trust nodes are not selected as cluster members during the dynamic clustering phase, the trust values of cluster members are generally within a reasonable range. Furthermore, a node's number of slices cannot be greater than the total number of nodes that surround it. This fine-grained slicing strategy ensures that nodes with different trust values transmit data optimally.
(2) Determining the Size of Slices
In determining the size of data slices, this paper proposes an innovative strategy that bases the slice size on the distance of data transmission. The objective of this approach is to enable cluster members to intelligently divide the data to be sent into slices of varying sizes, depending on the distance to their neighboring nodes. By using this approach, we may improve the efficiency and dependability of data transmission by better accommodating variations in the distance between network nodes.
More specifically, a node determines how far away its neighbors nodes are before deciding to transfer data. For nodes that are farther away, the sending node opts to transmit smaller data slices. The advantage of this is that smaller slices are more likely to maintain data integrity during transmission. Additionally, due to their smaller size, the cost of retransmission is relatively low. Moreover, smaller data slices allow for more efficient utilization of network resources, reducing energy consumption associated with long-distance transmission. Conversely, for nodes that are closer, the sending node chooses to send larger data slices. Because of the proximity, both the reliability and efficiency of transmission are relatively high, enabling larger slices to convey more information more effectively. This strategy not only reduces the number of data packets, lowering the likelihood of network congestion, but also increases overall data throughput. Overall, this strategy of determining slice size based on data transmission distance effectively adapts to neighboring nodes at varying distances, optimizing data transmission within the network.
We define
as the initial data that node
needs to transmit. When node
sends data to node
, the size of the data slice sent is denoted as
. Specifically, when node
retains a data slice for itself, we refer to it as
. Meanwhile, we use
to represent the physical distance between node
and node
. Based on a dynamic slicing strategy that considers trust values, node
will divide its data to be sent into
slices, one of which is
. The size of
will be determined according to the specific strategy.
This represents the separation between node
and node
, which is nearby:
Then, the sizes of the remaining
slices can be represented as:
Where
and the distance between node
and any nearby node
can be expressed as follows if the shortest distance is used as the unit distance:
Then, equation (9) can be transformed into:
Consequently, the network's cluster member nodes can use the following equation to calculate the size of their slice data:
This strategy makes sure that each slice uses the least amount of energy possible when transmitting data by sizing the slices according to the transmission distance. Dynamic slicing technology also enhances network security. Since attackers cannot obtain all information from only a small portion of original data, even if they intercept some data slices, they cannot easily reconstruct the complete original data.
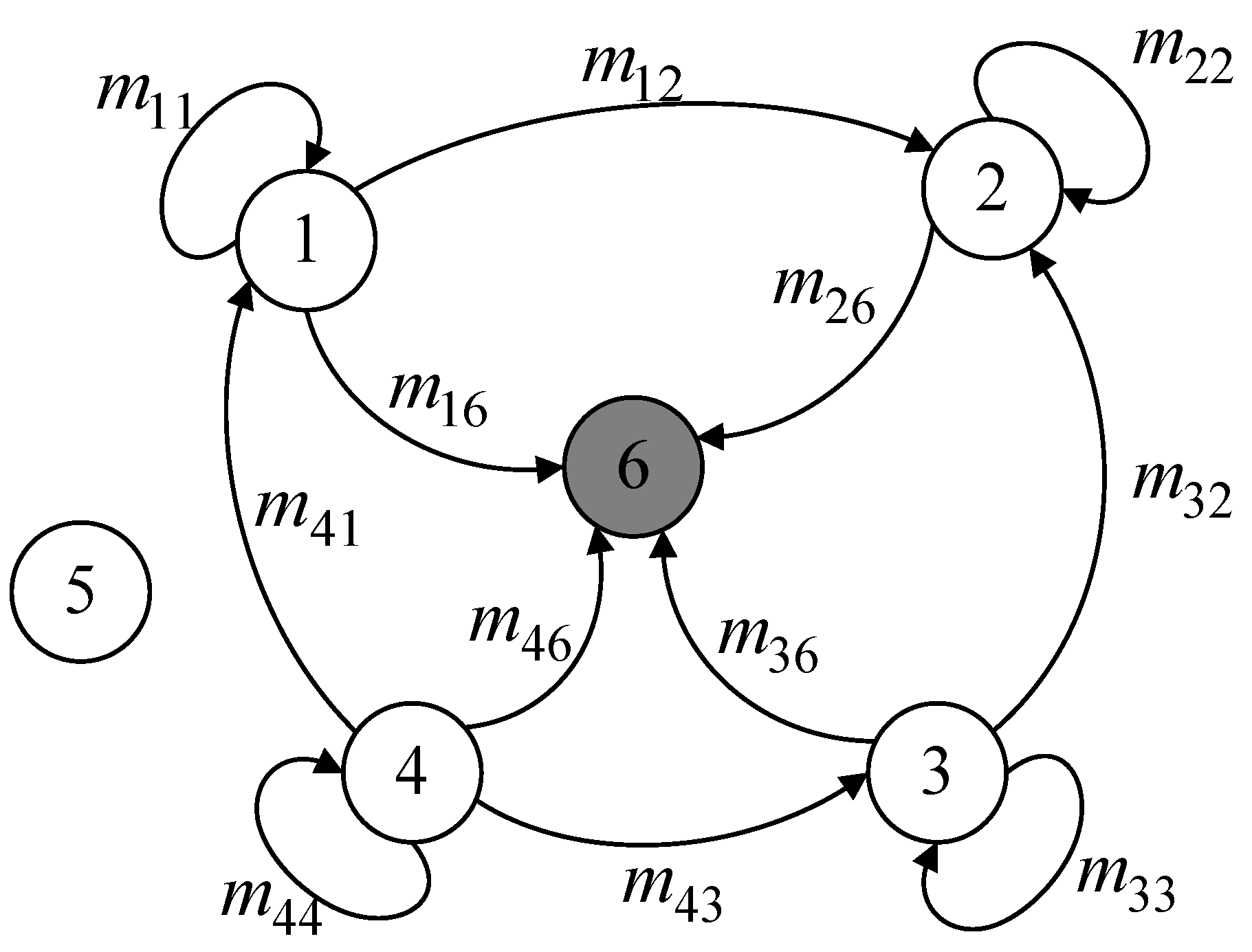
Figure 3.
Dynamic Slicing.
Figure 3.
Dynamic Slicing.
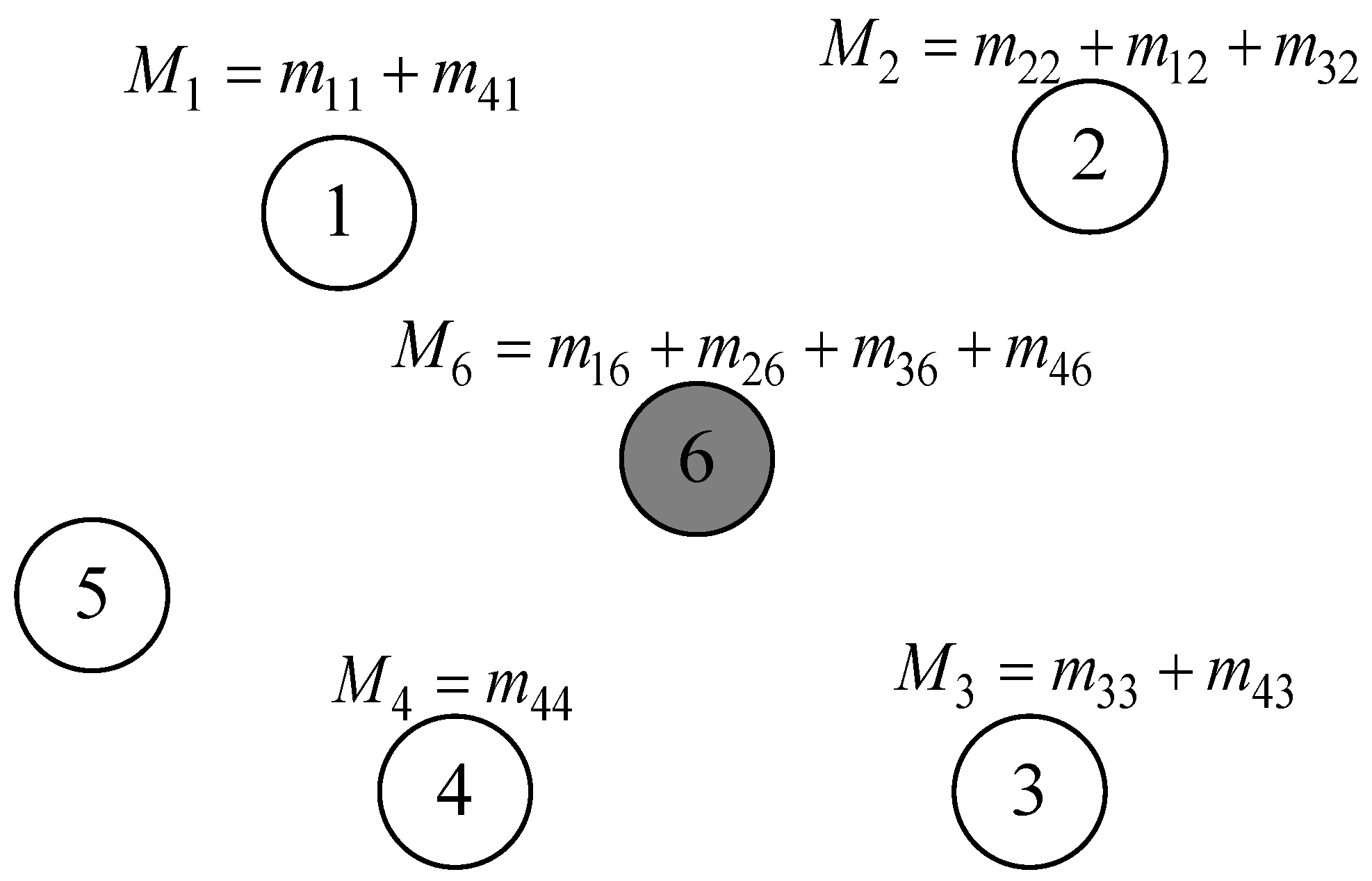
4.3. Data Mixing and Aggregation
During the data mixing phase, cluster member nodes combine the data slices they have retained with the data slices they have received after dividing the data slices according to the dynamic slicing algorithm and sending them. This creates a new mixed data packet. During this process, the exchange of data slices between nodes may cause congestion in communication links, leading to the risk of data collision and information loss. Therefore, it is necessary to formulate a reasonable slicing transmission strategy. In the proposed scheme, except for retaining one data slice themselves, nodes transmit the remaining slices to neighboring nodes based on their trust values, prioritizing high-trust neighboring nodes as recipients to ensure data security. Additionally, for nodes requiring four slices, one slice needs to be sent to the nearest neighboring cluster node. This strategy helps reduce data slice collisions and improves the accuracy of data aggregation. As shown in
Figure 4.
During data aggregation, each cluster member node encrypts mixed data packets using a shared key before transmitting them to the cluster head node. The cluster head node receives the encrypted mixed data packets and decodes them with the shared key. It then constructs the final data packet for the cluster by merging the decrypted data with the data it retains. The final data packet within the cluster is sent to the next cluster head node until it reaches the base station, at which point the cluster head node travels toward the base station.
Figure 5 illustrates a process illustration.