Submitted:
14 April 2024
Posted:
15 April 2024
You are already at the latest version
Abstract
Keywords:
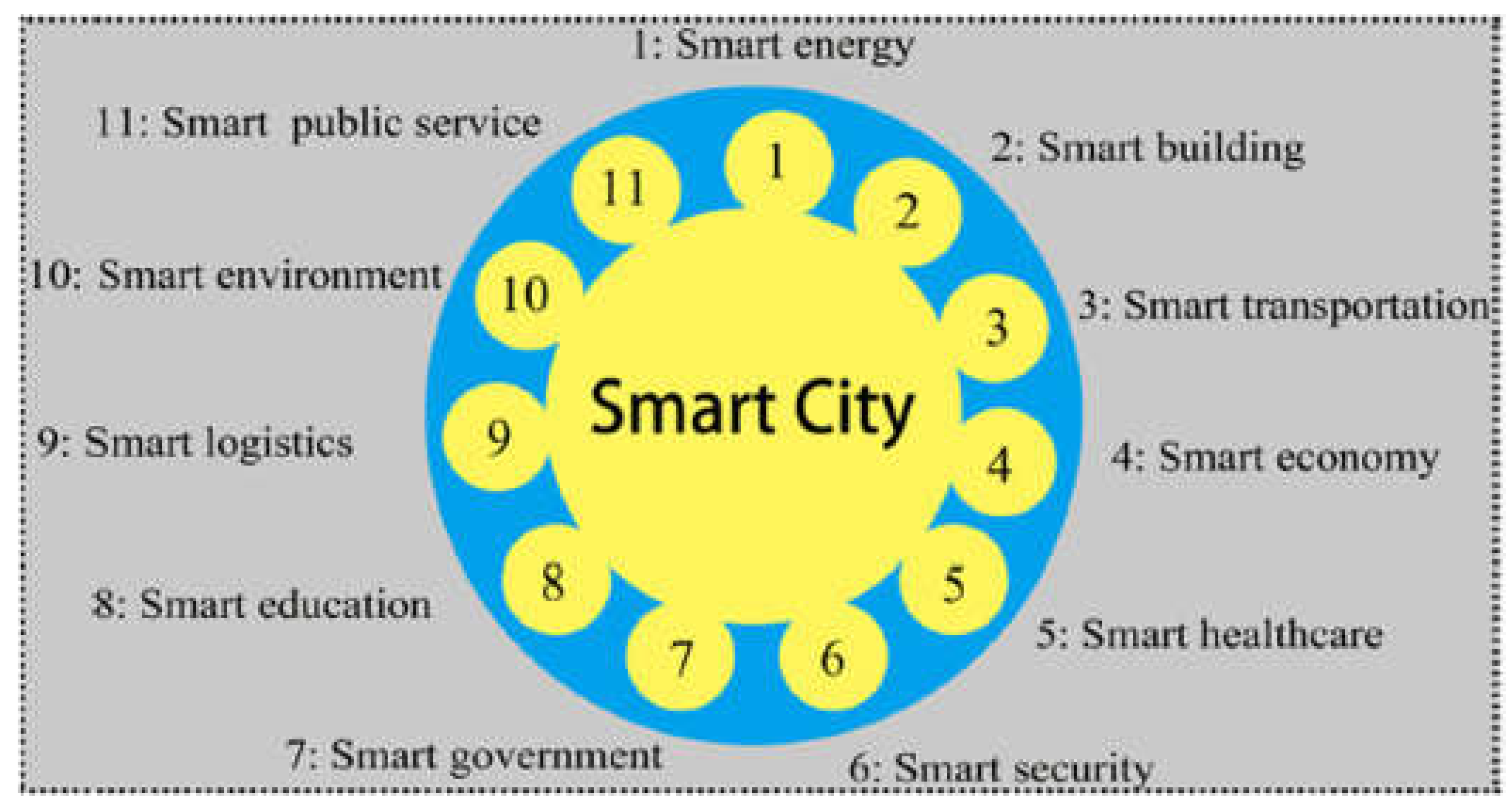
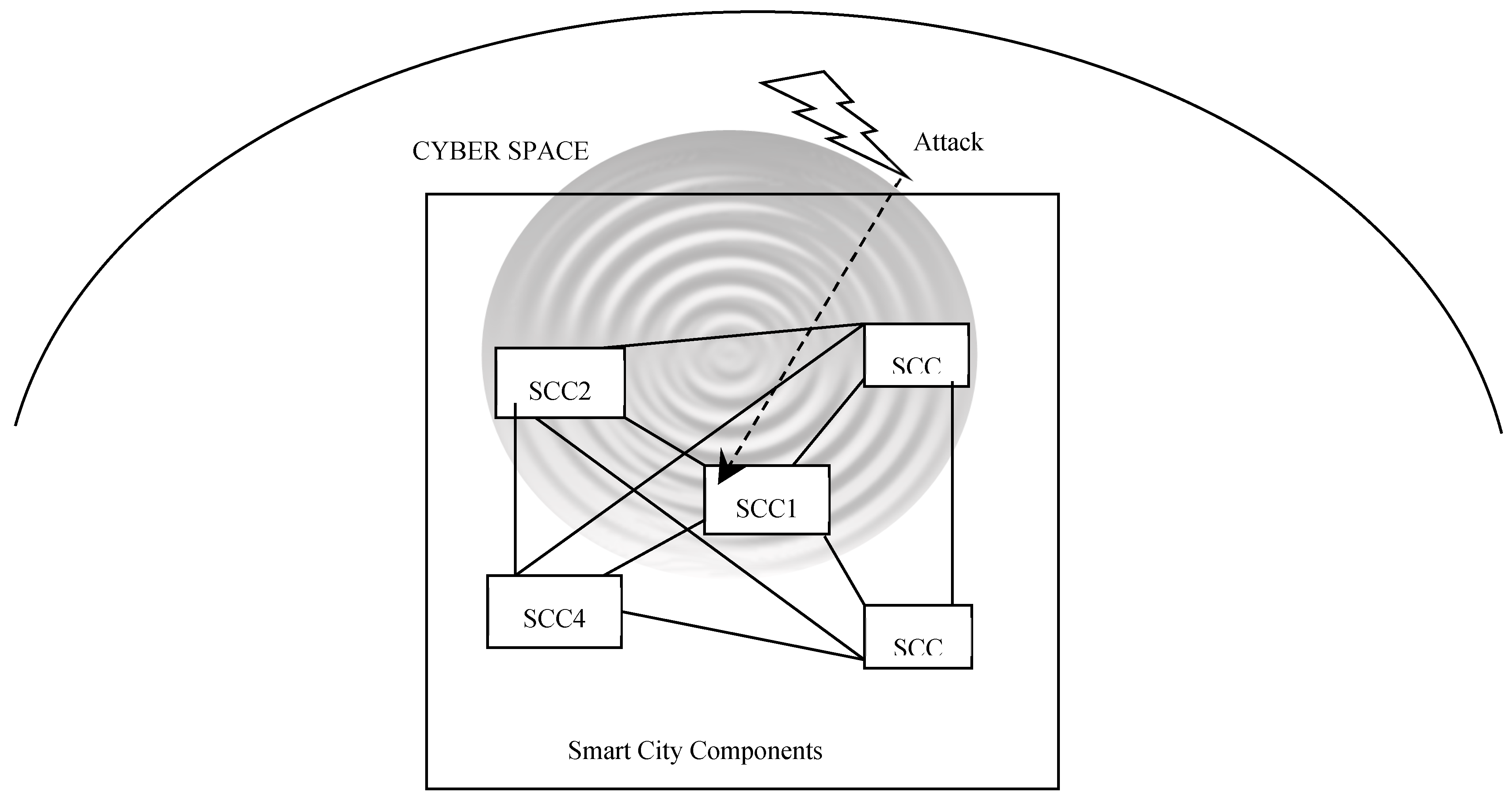
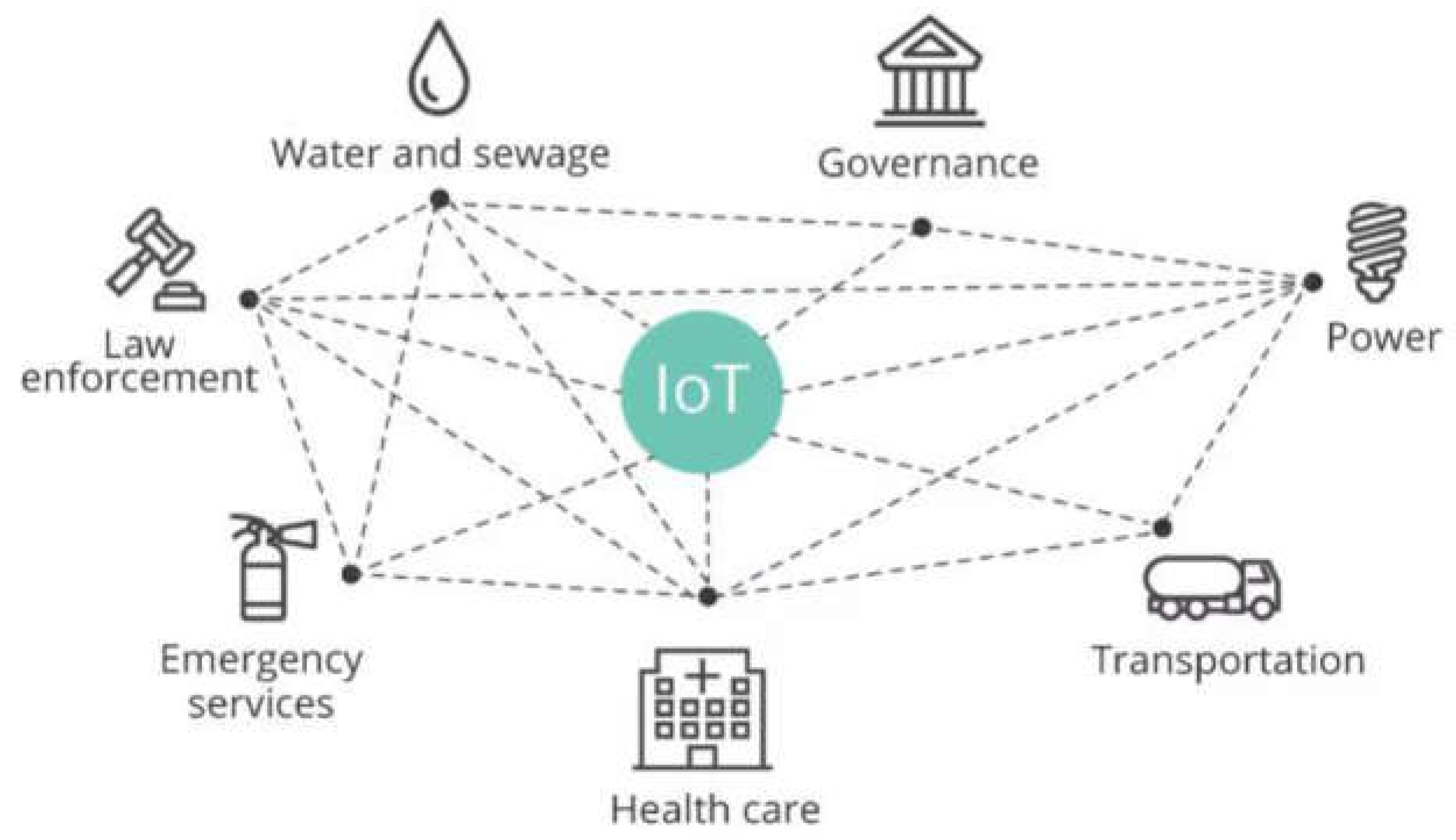
Introduction
Materials and Methods
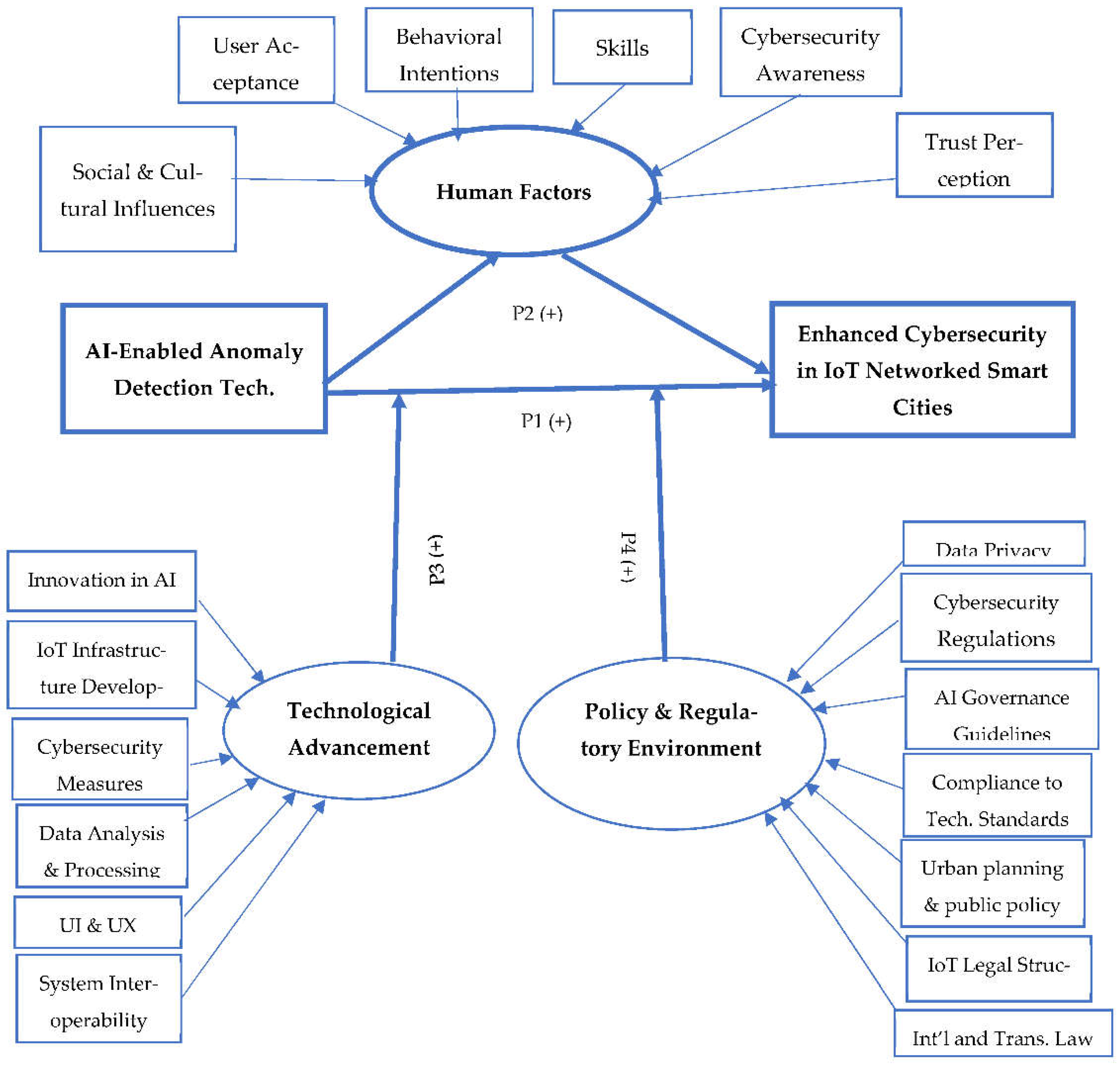
Conceptual Model and Propositions
Theoretical Framework
Study Propositions and Conceptual Model
- A.
- AI-Driven Anomaly Detection Techniques: These are the AI-driven approaches used to recognize and address cybersecurity risks (Hassan et al., 2023) in IoT networks seen in smart cities (Caiazzo et al, 2023). By modeling the actions that are deemed typical within a system and recognizing prospective assaults from behaviors that differ from the established normal behavior pattern, the anomaly-based approach seeks to discover new (unknown) attacks (Panagiotou, 2021).
- B.
- Cybersecurity Enhancement in Smart City IoT Networks: this outcome variable measures how much smart city IoT networks' security and resistance to cyber threats have improved overall (Khatoun and Zeadally, 2017; Rawat and Ghafoor, 2018). The main indicators of enhanced IoT-networked smart city cybersecurity are social welfare, urban mobility solutions, operational resilience, and sustainability of the city. (Alahi et al., 2023). Of course, operational resilience is essential to ensure and maintain continuity in services and high up time (Chakrabarty and Engels, 2020).
- C.
- Human factors, which include user behavior, acceptance, and knowledge of cybersecurity measures driven by AI. The relationship between AI-driven anomaly detection and cybersecurity enhancing effectiveness is mediated by human variables, including: (Chow et al., 2023; Adel, 2023; Ahmad et al., 2022; Cao et al., 2021)
- a.
- Acceptance and Adoption by Users: this dimension deals with how people accept and employ AI technologies, from citizens to municipal officials. It involves views of utility and simplicity of use, perceived performance expectancy, and perceived effort expectancy, which are crucial in determining the desire to interact with and use new technologies.
- b.
- Behavioral Intentions: this dimension examines how users' beliefs, subjective standards, and perceived behavioral control affect their intents and behaviors. It discusses how social forces and perceptions affect how AI technologies are used in smart cities.
- c.
- Training and Development of Skills: the degree of instruction and skill-building that AI system users can access. This aspect is essential for guaranteeing that people possess the skills and knowledge required to communicate with and operate AI-driven cybersecurity solutions.
- d.
- Cybersecurity Awareness: users' overall knowledge and comprehension of cybersecurity issues. This covers being aware of possible dangers, following safe procedures, and how AI can help reduce the risk of cyberattacks.
- e.
- Perception of Trust and Reliability: A key component influencing AI solution acceptability and efficacy is trust. This encompasses users' opinions of these technologies' reliability in identifying and countering cybersecurity risks, as well as their faith in AI systems.
- f.
- Social and Cultural Influences: this dimension acknowledges the substantial influence that social settings and cultural norms can have on attitudes and behaviors regarding technology.
- D.
- Technology Advancement: technological advancements play a crucial role in shaping the efficacy of AI-enabled anomaly detection systems. As technology evolves, these systems become more sophisticated, capable of handling more complex threats and adapting to new cybersecurity challenges. The level of technological maturity can significantly influence how effectively AI tools identify and respond to threats in smart city environments. The concept of technology advancement could encompass: (Son et al., 2023; Alahi et al., 2023; Adel, 2023; Fatima et al., 2020; Shneiderman et al., 2016; Liu et al., 2018):
- a.
- Technological Innovation in AI and Machine Learning: this component deals with the creation and application of novel machine learning and artificial intelligence algorithms. It covers innovations especially suited for cybersecurity applications in fields like deep learning, neural networks, and predictive analytics.
- b.
- IoT Infrastructure Development: the degree of IoT infrastructure integration and sophistication in smart cities. This involves the implementation of sophisticated sensors, network systems, and connected devices that enable large-scale data gathering and exchange.
- c.
- Capabilities for Data Analysis and Processing: the capacity to effectively handle and evaluate massive amounts of data produced by IoT networks in smart cities. This encompasses developments in edge computing, cloud computing, and big data technologies that improve the ability to manage and analyze large, complicated datasets.
- d.
- Cybersecurity Measures: the creation and use of cutting-edge cybersecurity policies and procedures. This dimension includes advancements in intrusion detection systems, network security, encryption, and other security technologies meant to fend off dynamic cyberthreats.
- e.
- System Interoperability & Integration: the degree of integration and coherence among diverse technology systems in smart cities. This dimension is centered on the creation of protocols and standards that provide smooth interoperability between various platforms and technologies.
- f.
- Interface and Experience Design for Users: developments in the creation of user experiences and interfaces that accommodate a variety of user groups. Creating more logical, user-friendly mechanisms that make interacting and interacting with technology easier is part of this.
- E.
- Policies & Regulatory Framework: Policies and regulations governing data privacy, security standards, and the use of AI technology can either enable or restrict the capabilities of AI systems in cybersecurity applications. Effective policy frameworks that support innovation while ensuring security and privacy can enhance the impact of AI-enabled systems on cybersecurity. Conversely, restrictive or outdated policies may hinder their potential. This framework includes (Alahi et al., 2023; Zhou and Kankanhalli, 2021; Chakrabarty and Engels, 2020; Wang et al., 2021; Weber, 2010; Roman et al., 2013)
- a.
- Data Privacy & Protection Law: regulations that control data collection, storage, processing, and sharing are included in this dimension. They have an effect on the development and functionality of AI systems by dictating how private and sensitive data must be treated.
- b.
- Regulations pertaining to cybersecurity: cybersecurity measures are mandated by these particular laws and standards. These include specifications for data encryption, network security, and breach reporting, making sure AI systems in smart cities follow strict security guidelines.
- c.
- AI Governance Guidelines: policies that particularly address the creation and application of AI technologies fall under this category. To guarantee that AI is utilized responsibly and ethically, it comprises accountability measures, requirements for algorithmic transparency, and ethical norms.
- d.
- Compliance to Technology Standards: this dimension includes standards and compliance requirements for quality assurance, interoperability, and technology implementation. By ensuring that AI and IoT technologies adhere to global norms and industry best practices, they promote dependability and compatibility.
- e.
- Urban planning and public policy: policies pertaining to public welfare and urban development that affect how AI and IoT technologies are integrated in smart cities. This includes policies for public participation, resource allocation, and strategic planning that influence how technology is used to meet urban demands.
- f.
- Legal Structure for the Implementation of IoT: laws that particularly control the implementation of IoT, with an emphasis on network security, device security, and ecosystem management. This dimension makes sure that IoT networks and devices run effectively and safely in smart cities.
- g.
- International and Transnational Law: laws and regulations that deal with worldwide collaboration in AI and IoT governance, cross-border cybersecurity risks, and international data sharing. For smart cities to be a part of a global network and communicate with global data and technological standards, this dimension is essential.
Discussion
Conclusion and Future Research Recommendations
Funding
Data Availability Statement
Conflicts of Interest
References
- Abdullahi, M.; Baashar, Y.; Alhussian, H.; Alwadain, A.; Aziz, N.; Capretz, L.F.; Abdulkadir, S.J. Detecting cybersecurity attacks in internet of things using artificial intelligence methods: A systematic literature review. Electronics 2022, 11, 198. [Google Scholar] [CrossRef]
- Adel, A. Unlocking the Future: Fostering Human–Machine Collaboration and Driving Intelligent Automation through Industry 5.0 in Smart Cities. Smart Cities 2023, 6, 2742–2782. [Google Scholar] [CrossRef]
- Ahmad, K.; Maabreh, M.; Ghaly, M.; Khan, K.; Qadir, J.; Al-Fuqaha, A. Developing future human-centered smart cities: Critical analysis of smart city security, Data management, and Ethical challenges. Computer Science Review 2022, 43, 100452. [Google Scholar] [CrossRef]
- Ahmad, K.; Maabreh, M.; Ghaly, M.; Khan, K.; Qadir, J.; Al-Fuqaha, A. Developing future human-centered smart cities: Critical analysis of smart city security, interpretability, and ethical challenges. arXiv arXiv:2012.09110, 2020.
- Ahmed, M.; Mahmood, A.N.; Hu, J. A survey of network anomaly detection techniques. Journal of Network and Computer Applications 2016, 60, 19–31. [Google Scholar] [CrossRef]
- Ajzen, I. The theory of planned behavior. Organizational behavior and human decision processes 1991, 50, 179–211. [Google Scholar] [CrossRef]
- Alaba, F.A.; Othman, M.; Hashem, I.A.T.; Alotaibi, F. Internet of Things security: A survey. Journal of Network and Computer Applications 2017, 88, 10–28. [Google Scholar] [CrossRef]
- Alahi, M.E.E.; Sukkuea, A.; Tina, F.W.; Nag, A.; Kurdthongmee, W.; Suwannarat, K.; Mukhopadhyay, S.C. Integration of IoT-Enabled Technologies and Artificial Intelligence (AI) for Smart City Scenario: Recent Advancements and Future Trends. Sensors 2023, 23, 5206. [Google Scholar] [CrossRef]
- Ali, S.; Rehman, S.U.; Imran, A.; Adeem, G.; Iqbal, Z.; Kim, K.I. Comparative Evaluation of AI-Based Techniques for Zero-Day Attacks Detection. Electronics 2022, 11, 3934. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Zahmatkesh, H.; Shahroze, R. An overview of security and privacy in smart cities' IoT communications. Transactions on Emerging Telecommunications Technologies 2022, 33, e3677. [Google Scholar] [CrossRef]
- Antonakakis, M.; April, T.; Bailey, M.; Bernhard, M.; Bursztein, E.; Cochran, J.; ... & Lever, C. (2017). Understanding the Mirai Botnet. In 26th USENIX Security Symposium (USENIX Security 17) (pp. 1093-1110).
- Ashraf, J.; Keshk, M.; Moustafa, N.; Abdel-Basset, M.; Khurshid, H.; Bakhshi, A.D.; Mostafa, R.R. IoTBoT-IDS: A novel statistical learning-enabled botnet detection framework for protecting networks of smart cities. Sustainable Cities and Society 2021, 72, 103041. [Google Scholar] [CrossRef]
- Badii, C.; Bellini, P.; Difino, A.; Nesi, P. Smart city IoT platform respecting GDPR privacy and security aspects. IEEE Access 2020, 8, 23601–23623. [Google Scholar] [CrossRef]
- Badran, A. Developing smart cities: Regulatory and policy implications for the State of Qatar. International Journal of Public Administration 2023, 46, 519–532. [Google Scholar] [CrossRef]
- Baig, Z.A.; Szewczyk, P.; Valli, C.; Rabadia, P.; Hannay, P.; Chernyshev, M. . & Peacock, M. Future challenges for smart cities: Cyber-security and digital forensics. Digital Investigation 2017, 22, 3–13. [Google Scholar]
- Batty, M.; Axhausen, K.W.; Giannotti, F.; Pozdnoukhov, A.; Bazzani, A.; Wachowicz, M. . & Portugali, Y. Smart cities of the future. European Physical Journal Special Topics 2012, 214, 481–518. [Google Scholar]
- Blake, A. (2018). Malware infection poised to cost $1 million to Allentown (February 21, 2018). Retrieved from: https://www.washingtontimes.com/news/2018/feb/21/malware-infection-posed-cost-1-million-allentown-p/.
- Bokhari, S.A.A.; Myeong, S. The influence of artificial intelligence on e-Governance and cybersecurity in smart cities: A stakeholder’s perspective. IEEE Access 2023. [CrossRef]
- Caiazzo, B.; Murino, T.; Petrillo, A.; Piccirillo, G.; Santini, S. An IoT-based and cloud-assisted AI-driven monitoring platform for smart manufacturing: design architecture and experimental validation. Journal of Manufacturing Technology Management 2023, 34, 507–534. [Google Scholar] [CrossRef]
- Cao, G.; Duan, Y.; Edwards, J.S.; Dwivedi, Y.K. Understanding managers’ attitudes and behavioral intentions towards using artificial intelligence for organizational decision-making. Technovation 2021, 106, 102312. [Google Scholar] [CrossRef]
- Caragliu, A.; Del Bo, C.; Nijkamp, P. Smart cities in Europe. Journal of Urban Technology 2011, 18, 65–82. [Google Scholar] [CrossRef]
- Chakrabarty, S.; Engels, D.W. (2020, December). Secure smart cities framework using IoT and AI. In 2020 IEEE Global Conference on Artificial Intelligence and Internet of Things (GCAIoT) (pp. 1-6). IEEE.
- Chow, C.S.K.; Zhan, G.; Wang, H.; He, M. Artificial Intelligence (Ai) Adoption: An Extended Compensatory Level Of Acceptance. Journal of Electronic Commerce Research 2023, 24, 84–106. [Google Scholar]
- Costa, D.G.; Duran-Faundez, C. Open-source electronics platforms as enabling technologies for smart cities: Recent developments and perspectives. Electronics 2018, 7, 404. [Google Scholar] [CrossRef]
- Davis, F.D. Perceived usefulness, perceived ease of use, and user acceptance of information technology. MIS quarterly 1989, 319–340. [Google Scholar] [CrossRef]
- de Azambuja, A.J.G.; Plesker, C.; Schützer, K.; Anderl, R.; Schleich, B.; Almeida, V.R. Artificial Intelligence-Based Cyber Security in the Context of Industry 4.0—A Survey. Electronics 2023, 12, 1920. [Google Scholar] [CrossRef]
- Demertzi, V.; Demertzis, S.; Demertzis, K. An Overview of Cyber Threats, Attacks and Countermeasures on the Primary Domains of Smart Cities. Applied Sciences 2023, 13, 790. [Google Scholar] [CrossRef]
- Demertzi, V.; Demertzis, S.; Demertzis, K. An Overview of Cyber Threats, Attacks and Countermeasures on the Primary Domains of Smart Cities. Applied Sciences 2023, 13, 790. [Google Scholar] [CrossRef]
- Ejaz, W.; Anpalagan, A.; Ejaz, W.; Anpalagan, A. Internet of things for smart cities: overview and key challenges. Internet of Things for Smart Cities: Technologies, Big Data and Security 2019, 1–15. [Google Scholar]
- Elmaghraby, A.S.; Losavio, M.M. Cyber security challenges in Smart Cities: Safety, security and privacy. Journal of advanced research 2014, 5, 491–497. [Google Scholar] [CrossRef] [PubMed]
- Fatima, S.; Desouza, K.C.; Dawson, G.S. National strategic artificial intelligence plans: A multi-dimensional analysis. Economic Analysis and Policy 2020, 67, 178–194. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Derdour, M.; Mukherjee, M.; Derhab, A.; Maglaras, L.; Janicke, H. . & Raza, I. Blockchain technologies for the Internet of Things: Research issues and challenges. IEEE Internet of Things Journal 2018, 6, 2188–2204. [Google Scholar]
- Granjal, J.; Monteiro, E.; Sa Silva, J. Security for the Internet of Things: A survey of existing protocols and open research issues. IEEE Communications Surveys & Tutorials 2015, 17, 1294–1312. [Google Scholar]
- Guembe, B.; Azeta, A.; Misra, S.; Osamor, V.C.; Fernandez-Sanz, L.; Pospelova, V. The emerging threat of ai-driven cyber attacks: A review. Applied Artificial Intelligence 2022, 36, 2037254. [Google Scholar] [CrossRef]
- Hasan, K.; Shetty, S.; Ullah, S. (2019, December). Artificial intelligence empowered cyber threat detection and protection for power utilities. In 2019 IEEE 5th International Conference on Collaboration and Internet Computing (CIC) (pp. 354-359). IEEE.
- Hashem, I.A.T.; Chang, V.; Anuar, N.B.; Adewole, K.; Yaqoob, I.; Gani, A. . & Chiroma, H. The role of big data in smart city. International Journal of Information Management 2016, 36, 748–758. [Google Scholar]
- Hassan, M.M.; Abrar, M.F.; Hasan, M. (2023). An Explainable AI-Driven Machine Learning Framework for Cybersecurity Anomaly Detection. In Cyber Security and Business Intelligence (pp. 197-219). Routledge.
- Himeur, Y.; Ghanem, K.; Alsalemi, A.; Bensaali, F.; Amira, A. Artificial intelligence based anomaly detection of energy consumption in buildings: A review, current trends and new perspectives. Applied Energy 2021, 287, 116601. [Google Scholar] [CrossRef]
- Hodo, E.; Bellekens, X.; Hamilton, A.; Dubouilh, P.L.; Iorkyase, E.; Tachtatzis, C.; Atkinson, R. (2016, May). Threat analysis of IoT networks using artificial neural network intrusion detection system. In 2016 International Symposium on Networks, Computers and Communications (ISNCC) (pp. 1-6). IEEE.
- Holland, J.H. 'Complex adaptive systems (CAS)', Complexity: A Very Short Introduction, Very Short Introductions (Oxford, 2014; online edn, Oxford Academic, 24 July 2014).
- Huber, B.; Kandah, F.; Skjellum, A. BEAST: Behavior as a Service for Trust management in IoT devices. Future Generation Computer Systems 2023, 144, 165–178. [Google Scholar] [CrossRef]
- Ismail, L.; Buyya, R. Artificial intelligence applications and self-learning 6G networks for smart cities digital ecosystems: Taxonomy, challenges, and future directions. Sensors 2022, 22, 5750. [Google Scholar] [CrossRef] [PubMed]
- Jia, Y.; Gu, Z.; Du, L.; Long, Y.; Wang, Y.; Li, J.; Zhang, Y. Artificial intelligence enabled cyber security defense for smart cities: A novel attack detection framework based on the MDATA model. Knowledge-Based Systems 2023, 276, 110781. [Google Scholar] [CrossRef]
- Jing, Q.; Vasilakos, A.V.; Wan, J.; Lu, J.; Qiu, D. Security of the Internet of Things: perspectives and challenges. Wireless Networks 2014, 20, 2481–2501. [Google Scholar] [CrossRef]
- Kaspersky (2023). Kaspersky unveils an overview of IoT-related threats in 2023(September). Retrieved from: https://www.kaspersky.com/about/press-releases/2023_kaspersky-unveils-an-overview-of-iot-related-threats-in-2023.
- 46. Kaspersky. (2020). IoT report: Year in figures. Kaspersky Lab.
- Khatoun, R.; Zeadally, S. Cybersecurity and privacy solutions in smart cities. IEEE Communications Magazine 2017, 55, 51–59. [Google Scholar] [CrossRef]
- Kitchin, R. The real-time city? Big data and smart urbanism. GeoJournal 2014, 79, 1–14. [Google Scholar] [CrossRef]
- Konstantopoulou, E.; Sklavos, N.; Ognjanovic, I. (2023). Securing Public Safety Mission-Critical 5G Communications of Smart Cities. In Internet of Everything for Smart City and Smart Healthcare Applications (pp. 61-74). Cham: Springer Nature Switzerland.
- Krichen, M.; Lahami, M. Towards a runtime testing framework for dynamically adaptable internet of things networks in smart cities. Smart Infrastructure and Applications: Foundations for Smarter Cities and Societies 2020, 589–607. [Google Scholar]
- Linde, L.; Sjödin, D.; Parida, V.; Wincent, J. Dynamic capabilities for ecosystem orchestration A capability-based framework for smart city innovation initiatives. Technological Forecasting and Social Change 2021, 166, 120614. [Google Scholar] [CrossRef]
- Liu, Y.; Zhang, P.; Zhou, J. Using AI to enhance the security of Internet of Things. Sensors 2018, 18, 403. [Google Scholar]
- Lu, Y.; Xu, L.D.; Xu, J. Internet of Things (IoT) cybersecurity research: A review of current research topics. IEEE Internet of Things Journal 2018, 6, 2103–2115. [Google Scholar] [CrossRef]
- Ma, C. Smart city and cyber-security; technologies used, leading challenges and future recommendations. Energy Reports 2021, 7, 7999–8012. [Google Scholar] [CrossRef]
- Magaia, N.; Fonseca, R.; Muhammad, K.; Segundo, A.H.F.N.; Neto, A.V.L.; de Albuquerque, V.H.C. Industrial internet-of-things security enhanced with deep learning approaches for smart cities. IEEE Internet of Things Journal 2020, 8, 6393–6405. [Google Scholar] [CrossRef]
- Malhotra, C.; Srivastava, A.; Gandotra, V. Cybersecurity and Smart Cities: Establishing the Need for Capacity Building. CYBERNOMICS 2019, 1, 6–15. [Google Scholar]
- Mehta, P.; Pandit, A.K.; Modi, C. Machine learning-based anomaly detection techniques for smart cities: A survey. Information Processing & Management 2020, 57, 102181. [Google Scholar]
- Nautiyal, L.; Malik, P.; Agarwal, A. Cybersecurity system: an essential pillar of smart cities. Smart Cities: Development and Governance Frameworks 2018, 25–50. [Google Scholar]
- Neirotti, P.; De Marco, A.; Cagliano, A.C.; Mangano, G.; Scorrano, F. Current trends in Smart City initiatives: Some stylised facts. Cities 2014, 38, 25–36. [Google Scholar] [CrossRef]
- Panagiotou, P.; Mengidis, N.; Tsikrika, T.; Vrochidis, S.; Kompatsiaris, I. Host-based intrusion detection using signature-based and ai-driven anomaly detection methods. Information & Security 2021, 50, 37–48. [Google Scholar]
- Pandey, P.; Golden, D.; Peasley, S.; and Kelkar, M. (2019). Making smart cities cybersecure. Retrieved from: https://www2.deloitte.com/us/en/insights/focus/smart-city/making-smart-cities-cyber-secure.html.
- Papernot, N.; McDaniel, P.; Wu, X.; Jha, S.; Swami, A. (2016). Distillation as a defense to adversarial perturbations against deep neural networks. In 2016 IEEE Symposium on Security and Privacy (SP) (pp. 582-597).
- Smart cities cybersecurity and privacy; Rawat, D.B., Ghafoor, K.Z., Eds.; Elsevier, 2018. [Google Scholar]
- Rejeb, A.; Rejeb, K.; Simske, S.; Treiblmaier, H.; Zailani, S. The big picture on the internet of things and the smart city: a review of what we know and what we need to know. Internet of Things 2022, 19, 100565. [Google Scholar] [CrossRef]
- Roman, R.; Zhou, J.; Lopez, J. On the features and challenges of security and privacy in distributed internet of things. Computer Networks 2013, 57, 2266–2279. [Google Scholar] [CrossRef]
- Schmitt, M. Securing the Digital World: Protecting smart infrastructures and digital industries with Artificial Intelligence (AI)-enabled malware and intrusion detection. Journal of Industrial Information Integration 2023, 36, 100520. [Google Scholar] [CrossRef]
- Shahidehpour, M.; Li, Z.; Ganji, M. Smart cities for a sustainable urbanization: Illuminating the need for establishing smart urban infrastructures. IEEE Electrification magazine 2018, 6, 16–33. [Google Scholar] [CrossRef]
- Sharma, A.; Jain, P. Adaptability of IoT and Cloud for Enabling the Smart City: Applications and Challenges. Handbook of Research on Network-Enabled IoT Applications for Smart City Services 2023, 54–74. [Google Scholar]
- Sharma, H.; Haque, A.; Blaabjerg, F. Machine learning in wireless sensor networks for smart cities: a survey. Electronics 2021, 10, 1012. [Google Scholar] [CrossRef]
- Sharma, R.; Arya, R. Security threats and measures in the Internet of Things for smart city infrastructure: A state of art. Transactions on Emerging Telecommunications Technologies 2023, 34, e4571. [Google Scholar] [CrossRef]
- Shin, D. The effects of explainability and causability on perception, trust, and acceptance: Implications for explainable AI. International Journal of Human-Computer Studies 2021, 146, 102551. [Google Scholar] [CrossRef]
- Shneiderman, B.; Plaisant, C.; Cohen, M.; Jacobs, S.; Elmqvist, N.; Diakopoulos, N. Designing the user interface: strategies for effective human-computer interaction; Pearson, 2016. [Google Scholar]
- Sicari, S.; Rizzardi, A.; Grieco, L.A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Computer Networks 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Singh, A.P. (2023). AI in Cyber Security: Advantages, Applications and Use Cases. Retrieved from: https://www.analyticsvidhya.com/blog/2023/02/future-of-ai-and-machine-learning-in-cybersecurity/.
- Son, T.H.; Weedon, Z.; Yigitcanlar, T.; Sanchez, T.; Corchado, J.M.; Mehmood, R. Algorithmic urban planning for smart and sustainable development: Systematic review of the literature. Sustainable Cities and Society 2023, 104562. [Google Scholar] [CrossRef]
- 76. Statista. (2020). Number of Internet of Things (IoT) connected devices worldwide in 2019, 2020 and 2025. Statista Research Department.
- Security and Privacy Applications for Smart City Development; Tamane, S.C., Dey, N., Hassanien, A.E., Eds.; Springer, 2021; p. 308. [Google Scholar]
- Trist, E.L. (1981). The evolution of socio-technical systems (Vol. 2). Toronto: Ontario Quality of Working Life Centre.
- Ullah, Z.; Al-Turjman, F.; Mostarda, L.; Gagliardi, R. Applications of artificial intelligence and machine learning in smart cities. Computer Communications 2020, 154, 313–323. [Google Scholar] [CrossRef]
- Umair, M.; Cheema, M.A.; Cheema, O.; Li, H.; Lu, H. Impact of COVID-19 on IoT adoption in healthcare, smart homes, smart buildings, smart cities, transportation and industrial IoT. Sensors 2021, 21, 3838. [Google Scholar] [CrossRef] [PubMed]
- Umpleby, S.A.; Dent, E.B. The origins and purposes of several traditions in systems theory and cybernetics. Cybernetics & Systems 1999, 30, 79–103. [Google Scholar]
- Villegas-Ch, W.; Govea, J.; Jaramillo-Alcazar, A. IoT Anomaly Detection to Strengthen Cybersecurity in the Critical Infrastructure of Smart Cities. Applied Sciences 2023, 13, 10977. [Google Scholar] [CrossRef]
- Wang, K.; Zhao, Y.; Gangadhari, R.K.; Li, Z. Analyzing the adoption challenges of the Internet of things (Iot) and artificial intelligence (ai) for smart cities in china. Sustainability 2021, 13, 10983. [Google Scholar] [CrossRef]
- Weber, R.H. Internet of Things – New security and privacy challenges. Computer Law & Security Review 2010, 26, 23–30. [Google Scholar]
- Wu, H.; Han, H.; Wang, X.; Sun, S. Research on artificial intelligence enhancing internet of things security: A survey. IEEE Access 2020, 8, 153826–153848. [Google Scholar] [CrossRef]
- Xu, L.D.; He, W.; Li, S. Internet of Things in industries: A survey. IEEE Transactions on Industrial Informatics 2014, 10, 2233–2243. [Google Scholar] [CrossRef]
- Yampolskiy, R.V. AI-complete, AI-hard, or AI-easy? Classification of problems in AI. arXiv arXiv:1308.1458, 2013.
- Yigitcanlar, T.; Desouza, K.C.; Butler, L.; Roozkhosh, F. Contributions and risks of artificial intelligence (AI) in building smarter cities: Insights from a systematic review of the literature. Energies 2020, 13, 1473. [Google Scholar] [CrossRef]
- Zhang, Y.; Deng, R.H.; Liu, X.; Zheng, D.; Mahmood, A. Analysis and outlook: From network security to cybersecurity. Journal of Computer Research and Development 2019, 56, 1–21. [Google Scholar]
- Zhou, Y.; Kankanhalli, A. AI regulation for smart cities: Challenges and principles. Smart Cities and Smart Governance: Towards the 22nd Century Sustainable City 2021, 101–118. [Google Scholar]
- Ziegeldorf, J.H.; Morchon, O.G.; Wehrle, K. Privacy in the Internet of Things: Threats and challenges. Security and Communication Networks 2014, 7, 2728–2742. [Google Scholar] [CrossRef]
| Proactive Detection | Unlike conventional rule-based systems, AI uses machine learning to identify unexpected dangers. |
| Adaptive Learning | AI upgrades its knowledge of assault patterns on a regular basis. |
| Analysis of Behavior | AI recognizes anomalies in behavior and distinguishes departures from the norm. |
| Identification of Patterns | Even under disguise, AI is able to identify intricate assault patterns. |
| Reduced False Positives | Decreased False Positives: AI improves threat identification, reducing the number of false alarms. |
| Dynamic Response | AI makes quick decisions in response to threats. |
| Threat Hunting | AI actively looks for undiscovered dangers. |
| Forecasting and Avoidance | AI anticipates dangers so that preventative measures can be taken. |
| Scalability | AI analyzes massive amounts of data effectively. |
| Acquiring Knowledge from Experience | AI gets better with time as a result of previous events. |
| Handling Complexity | AI handles complexity by coordinating several attack tactics. |
| Reduced Human Biasedness | Reduced Human Bias: AI offers unbiased danger evaluations. |
| CAS Feature | Relevance to Study |
|---|---|
| CAS Structure Using Adaptive Agents | Adaptive agents, or AI models and algorithms, make up CAS. These agents interact with the system and data to learn and adapt. Agents in anomaly detection adapt to novel threats and patterns. |
| CAS Lever Points | Modest CAS adjustments can have a big effect. Small changes to algorithms can significantly enhance anomaly detection in AI. AI models can be improved to identify cyber threats more accurately. |
| Three CAS Agent Activity Levels | Performance: AI systems' in-the-moment activities, such as network data analysis. Credit assignment: Assessing AI models' efficacy in threat identification. Rule-Discovery: creating fresh techniques to improve anomaly detection. |
| Hierarchical Structure and Adaptive Interactions | The adaptive interactions among AI models determine the behavior of the system. Several models operating at different levels in a multi-layered AI method. AI structure that is hierarchical and has layers for analysis, prediction, and data processing |
| Theory | Relationship | Relevance & Justification |
|---|---|---|
| Complex Adaptive Systems (CAS) (Holland, 1995) | AI-enabled Anomaly Detection → Enhanced Cybersecurity in Smart City IoT Networks | Smart city AI-powered anomaly detection systems can be thought of as adaptable agents inside these intricate networks. They constantly engage with and absorb large volumes of data, adapting to novel threat trends and risks. Understanding how AI technologies dynamically enhance the security and resilience of smart cities requires this viewpoint. |
| Technology Acceptance Model (TAM) (Davis, 1989) Theory of Planned Behavior (Ajzen, 1991) |
AI-enabled Anomaly Detection → Human Factor → Enhanced Cybersecurity in Smart City IoT Networks | The usefulness and usability of AI-driven anomaly detection are seen differently by different stakeholders in smart cities, and this perception affects their acceptance and support for such technologies. TAM can be used to examine this perception. By examining how people's attitudes, social norms, and control perceptions affect how AI is implemented and used in cybersecurity, this theory can assist in better understanding the human factor in the framework. |
| Theory of Socio-Technical Systems | AI-enabled Anomaly Detection * [Technological, Policy, and Environmental Factors] → Enhanced Cybersecurity in Smart City IoT Networks | Blending social and technical factors is especially relevant to comprehend how AI-driven anomaly detection is integrated into smart cities, striking a balance between technological efficiency and social considerations like user trust and legal compliance. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




