Submitted:
19 March 2024
Posted:
19 March 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. A One Time Pad with True Randomness
-
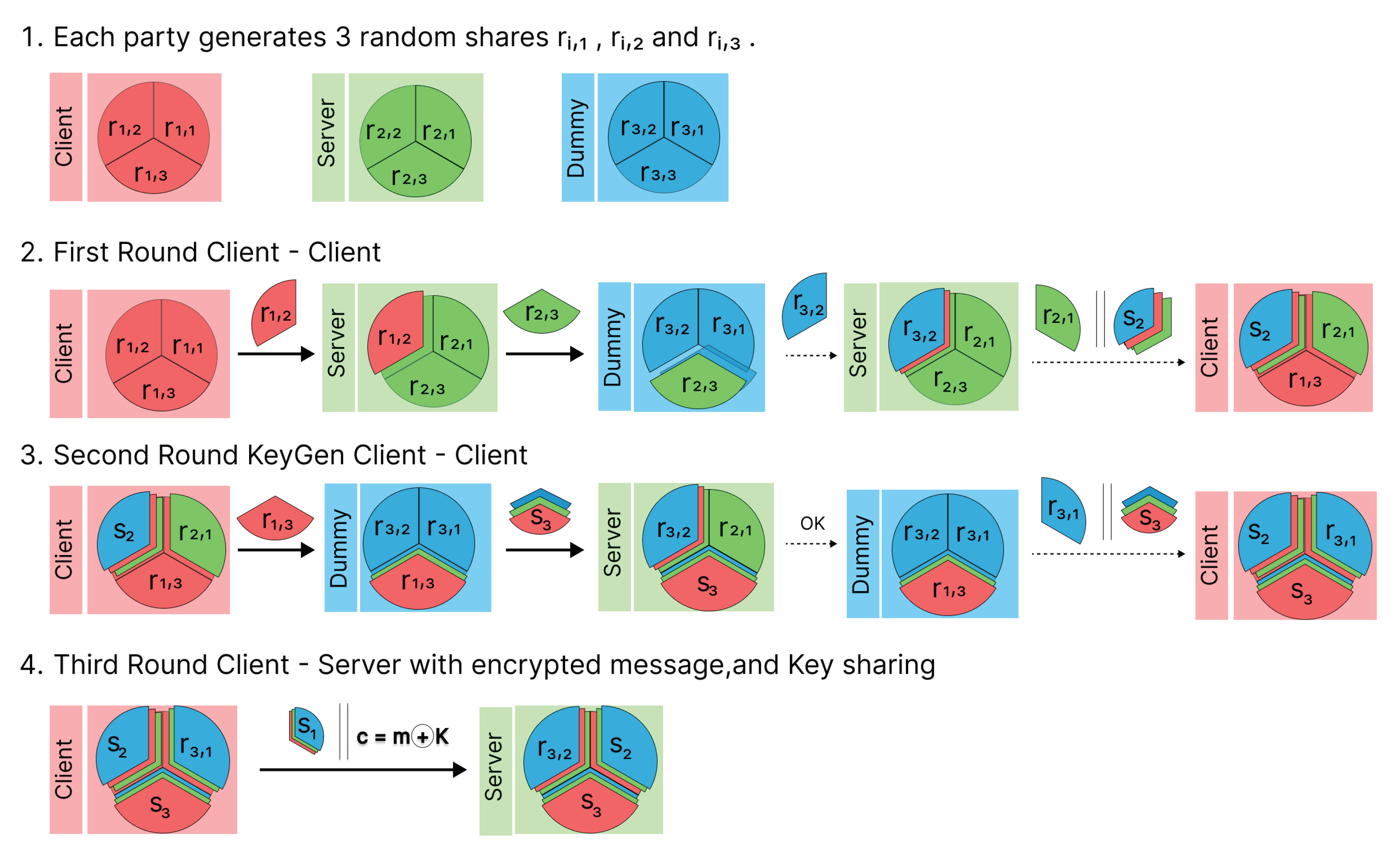
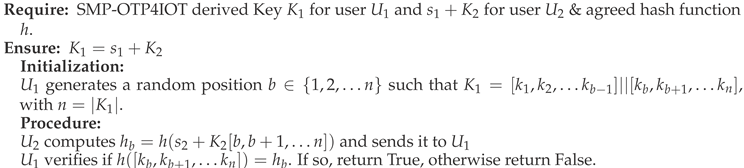
Share generation: Each party , generates two random shares and in , and computes a third share as the difference between their private input and the sum of the two random shares, modulo p. This is described by the equations:The party generates three random numbers , .
- Standard share distribution (as in [9]): Each party sends two of its three shares to the other parties according to a specific rule to ensure that no one party receives all shares from another party. Quote: Each sends privately , to , , to , and , to . Hence, the distribution pattern is:
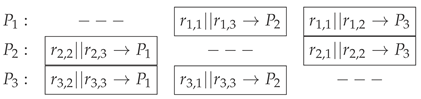
- Modified share distribution: Each sends privately , to , , . Hence, the distribution pattern is as follows:
-
Partial Sum Determination: In the standard procedure, each party adds the corresponding shares as: , , . In the modified share distribution, each party computes the (single) sum of the shares received according to:For instance, is aware of his own generated shares, , , and . Additionally, he has obtained from and from . Therefore, can calculate which is expressed as: .
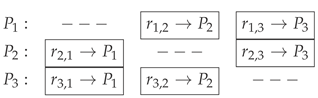
- Partial sum distribution: In the standard procedure, each party computes and announces (broadcasts) two values. In our proposed modification, sends to , sends to and broadcast to and :
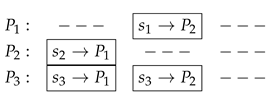
- Final sum calculation: In the standard procedure, all parties compute the result . In our modified procedure, and calculate both the sum , while learns nothing. Therefore, K will be known only for and , while all private inputs remain private and cannot be deduced from the outputs.
3. On the Fly KeyGen and Encryption
| ProtocolSMP-OTF4IOT: On the Fly KeyGen and Encryption |
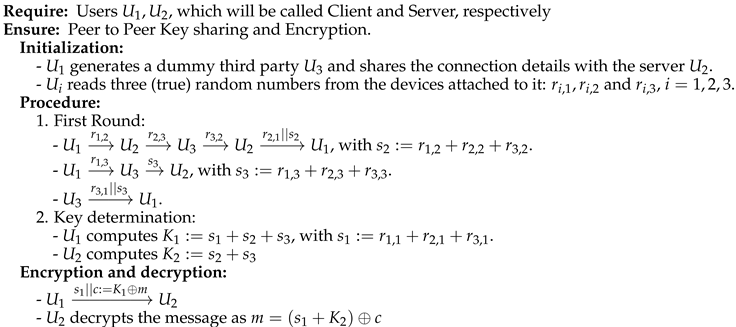 |
4. Methodology and Implementation
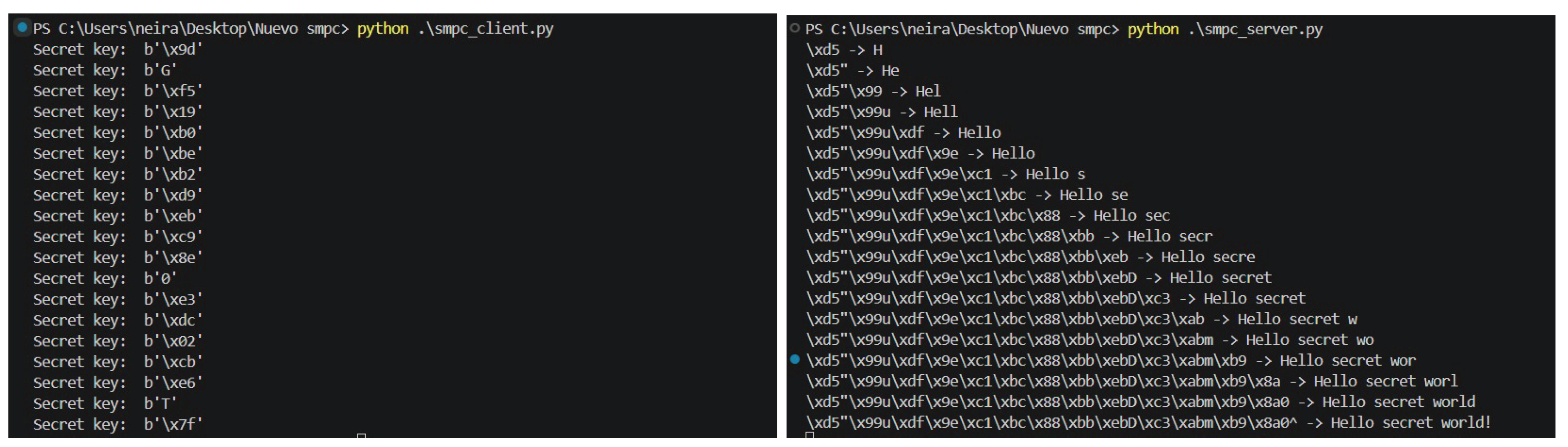
4.1. ZeroC-Ice Implementation on SMP-OTF4IOT
| Listing 1: ZeroC-Ice SMPC Implementation. |
| module SMPC{ interface Server { void deliverFromClient(int share, out int shareServer, out int sumServer ); void deliverFromDummy(int sum); void terminate(int sum, byte payload); } interface Dummy { void deliverFromClient(int share, out int shareDummy, out int sumDummy ); void deliverFromServer(int share, out int shareDummy ); } } |
5. Security Analysis
5.1. Privacy, Computation and Communication Costs
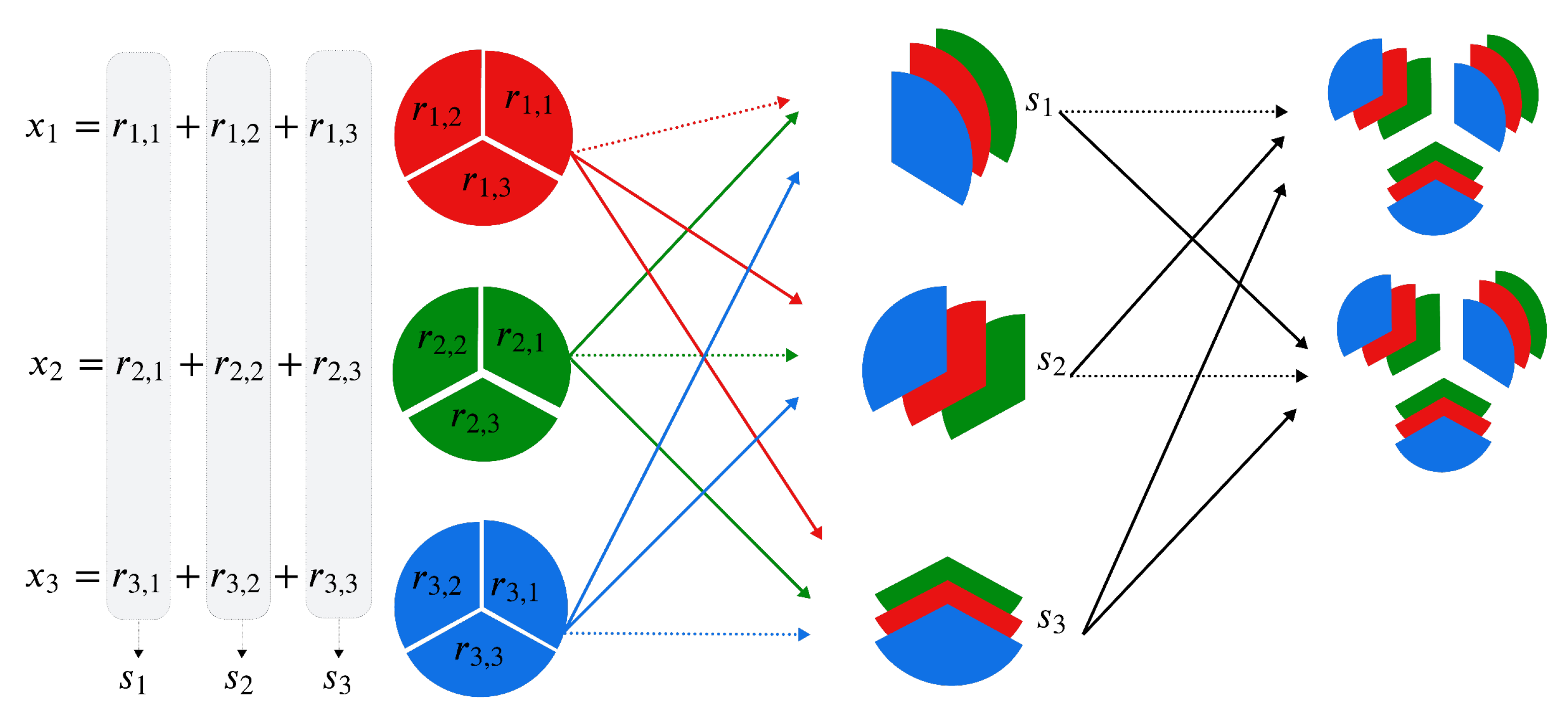
5.2. Error Correction and Privacy Amplification
| Protocol KeyGen-security check: Error correction and privacy amplification |
 |
5.3. Abstract Requirements for SMPC
6. Discussion
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| OTP | One Time Pad |
| SMP-OTP4IO | Secure multiparty One-time pad protocol for IoT |
| XOR | Exclusive OR |
References
- Vorakulpipat, C.; Rattanalerdnusorn, E.; Thaenkaew, P.; Hai, H.D. Recent challenges, trends, and concerns related to IoT security: An evolutionary study. In Proceedings of the 2018 20th International Conference on Advanced Communication Technology (ICACT). IEEE, 2018, pp. 405–410.
- Cravero, A.; Bustamante, A.; Negrier, M.; Galeas, P. Agricultural Big Data Architectures in the Context of Climate Change: A Systematic Literature Review. Sustentability 2022, 22, 7855. [CrossRef]
- Mohammadi, M.; Al-Fuqaha, A.; Sorour, S.; Guizani, M. Deep learning for IoT big data and streaming analytics: A survey. IEEE Communications Surveys & Tutorials 2018, 20, 2923–2960. [CrossRef]
- Lopez-Fenner, J.; Sepulveda, S.; Bittencourt, L.F.; Costa, F.M.; Georgantas, N. Privacy Preserving Multi Party Computation for Data-Analytics in the IoT-Fog-Cloud Ecosystem. In Proceedings of the CICCSI 2020 : IV International Congress of Computer Sciences and Information Systems, Mendoza / Virtual, Argentina, 2020; CICCSI 2020 Proceedings.
- Hossain, E.; Khan, I.; Un-Noor, F.; Sikander, S.S.; Sunny, M.S.H. Application of big data and machine learning in smart grid, and associated security concerns: A review. Ieee Access 2019, 7, 13960–13988. [CrossRef]
- Diffie, W.; Hellman, M. New directions in cryptography. IEEE Transactions on Information Theory 1976, 22, 644–654. [CrossRef]
- Patel, K. Secure multiparty computation using secret sharing. In Proceedings of the 2016 International Conference on Signal Processing, Communication, Power and Embedded System (SCOPES). IEEE, 2016, pp. 863–866. [CrossRef]
- Niu, Z.; Wang, H.; Li, Z.; Song, X. Privacy-preserving statistical computing protocols for private set intersection. International Journal of Intelligent Systems 2022, 37, 10118–10139. [CrossRef]
- Cramer, R.; Damgård, I.B.; et al. Secure multiparty computation; Cambridge University Press, 2015.
- ZeroC. Ice - The Internet Communications Engine. https://doc.zeroc.com/ice/3.6/introduction, 2022. [Accessed 22 Jan. 2024].
- Van Rossum, G.; Drake Jr, F.L. Python tutorial; Centrum voor Wiskunde en Informatica Amsterdam, The Netherlands, 1995.
- Cremers, C. Symbolic security analysis using the tamarin prover. In Proceedings of the 2017 Formal Methods in Computer Aided Design (FMCAD). IEEE, 2017, pp. 5–5.
- Blanchet, B.; et al. Modeling and verifying security protocols with the applied pi calculus and ProVerif. Foundations and Trends® in Privacy and Security 2016, 1, 1–135.
- Modesti, P.; Garcia, R. Formal Modeling and Security Analysis of Security Protocols. In Handbook of Formal Analysis and Verification in Cryptography; CRC Press, 2023; pp. 213–274.
- Yao, A.C. Protocols for secure computations. In Proceedings of the 23rd annual symposium on foundations of computer science (sfcs 1982). IEEE, 1982, pp. 160–164.
- Yao, A.C.C. How to generate and exchange secrets. In Proceedings of the 27th annual symposium on foundations of computer science (Sfcs 1986). IEEE, 1986, pp. 162–167.
- Dolev, D.; Yao, A. On the security of public key protocols. IEEE Transactions on information theory 1983, 29, 198–208. [CrossRef]
- Fort, M.; Freiling, F.; Penso, L.D.; Benenson, Z.; Kesdogan, D. TrustedPals: Secure multiparty computation implemented with smart cards. In Proceedings of the Computer Security–ESORICS 2006: 11th European Symposium on Research in Computer Security, Hamburg, Germany, September 18-20, 2006. Proceedings 11. Springer, 2006, pp. 34–48.
- Ambrose, J.A.; Ragel, R.G.; Parameswaran, S. RIJID: Random code injection to mask power analysis based side channel attacks. In Proceedings of the Proceedings of the 44th annual Design Automation Conference, 2007, pp. 489–492.
- Aumasson, J.P.; Meier, W.; Phan, R.C.W.; Henzen, L.; Aumasson, J.P.; Meier, W.; Phan, R.C.W.; Henzen, L. Blake2. The Hash Function BLAKE 2014, pp. 165–183.
- Shamshad, S.; Riaz, F.; Riaz, R.; Rizvi, S.S.; Abdulla, S. An enhanced architecture to resolve public-key cryptographic issues in the internet of things (IoT), Employing quantum computing supremacy. Sensors 2022, 22, 8151.
- McCann, D.; Eder, K.; Oswald, E. Characterising and comparing the energy consumption of side channel attack countermeasures and lightweight cryptography on embedded devices. In Proceedings of the 2015 International Workshop on Secure Internet of Things (SIoT). IEEE, 2015, pp. 65–71.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



