Submitted:
02 January 2024
Posted:
03 January 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
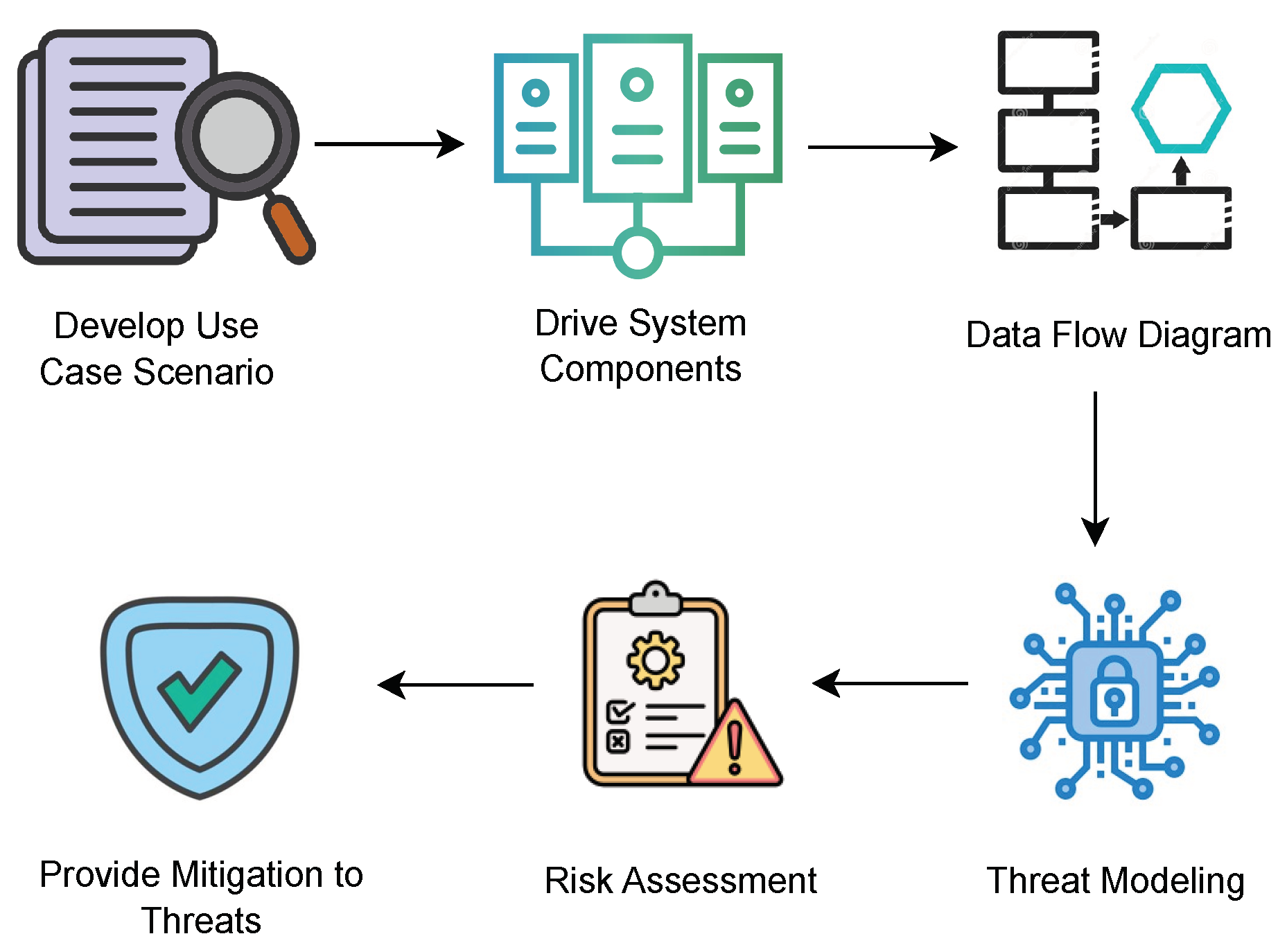
2. Methodology
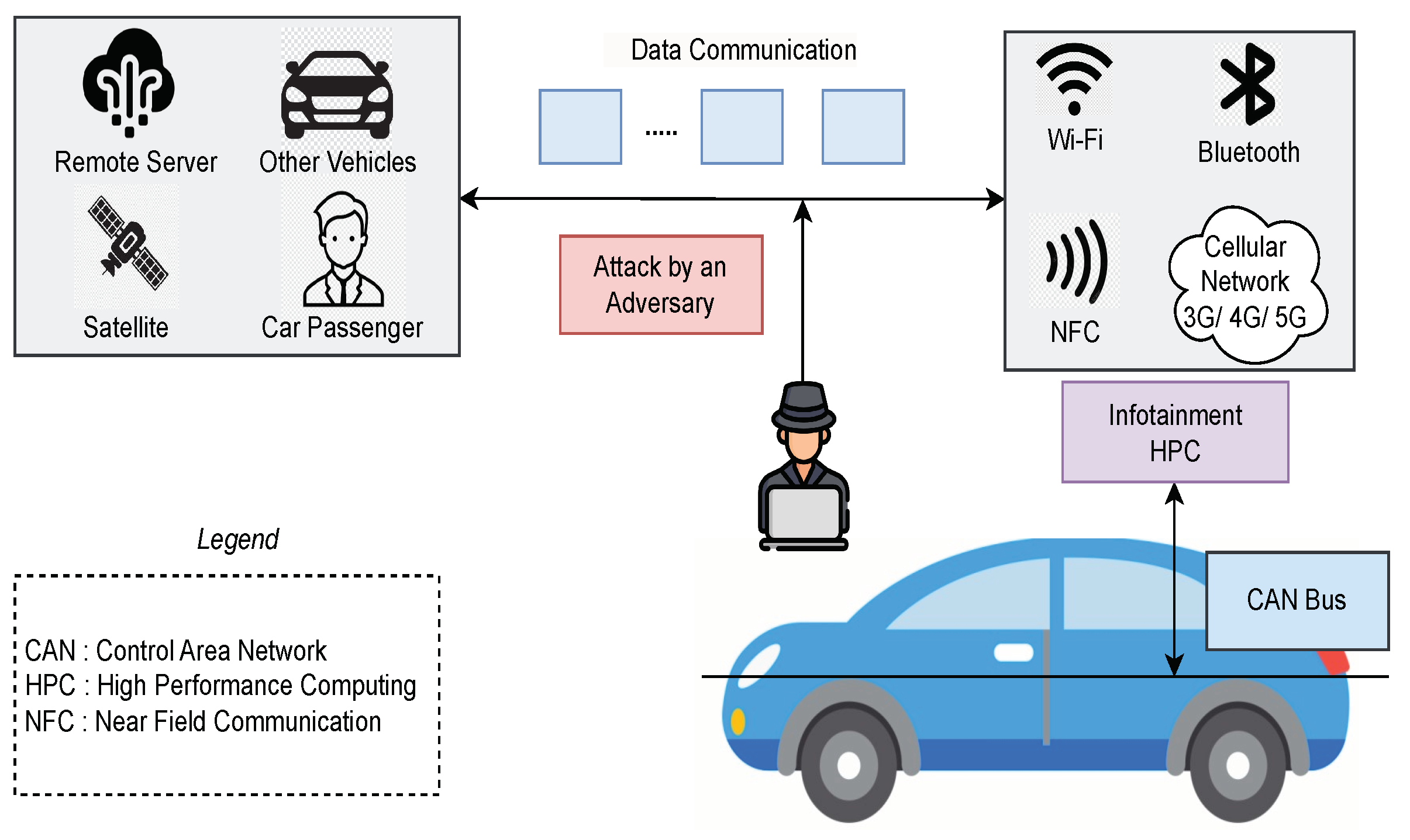
2.1. Use Case Scenario
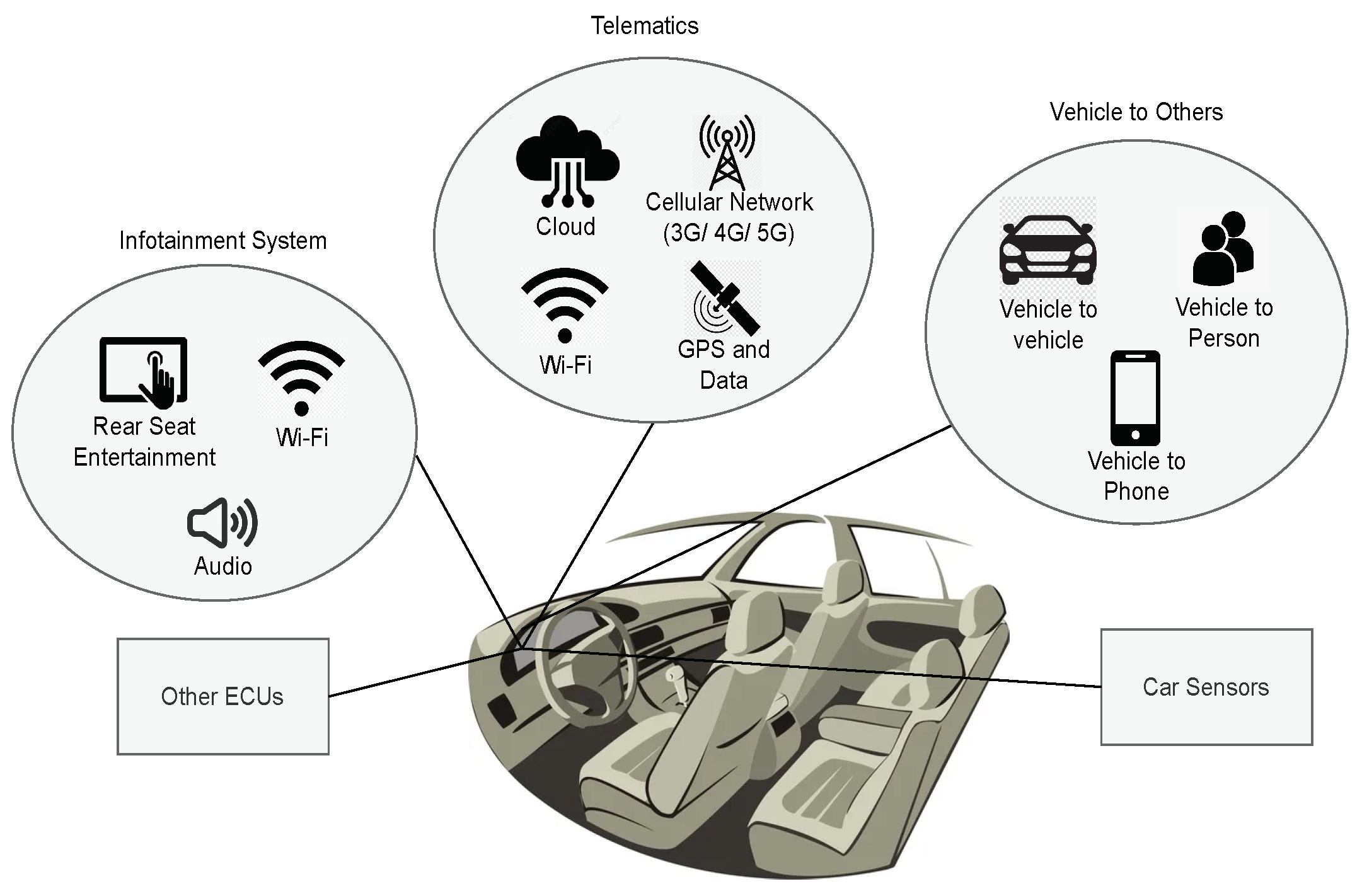
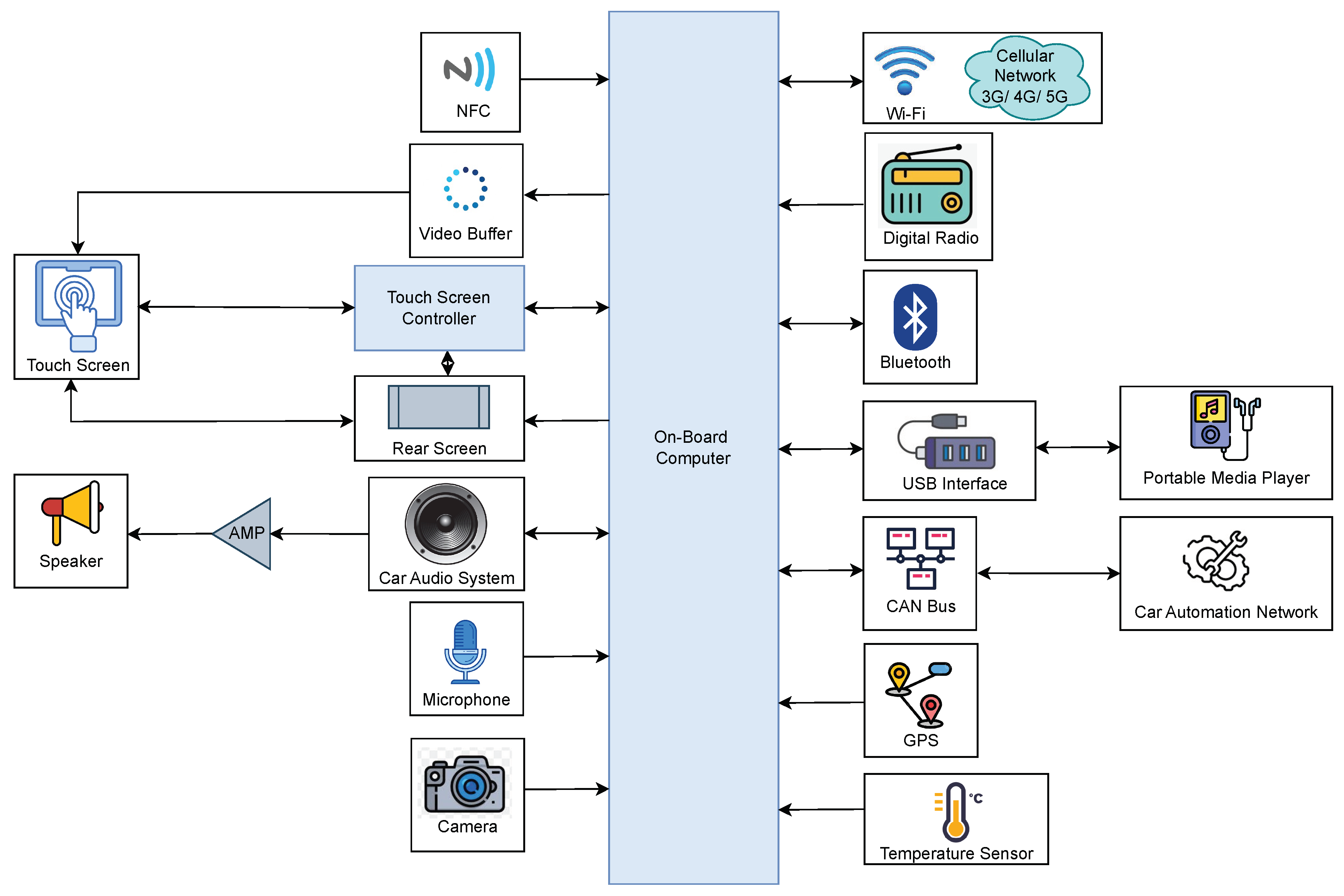
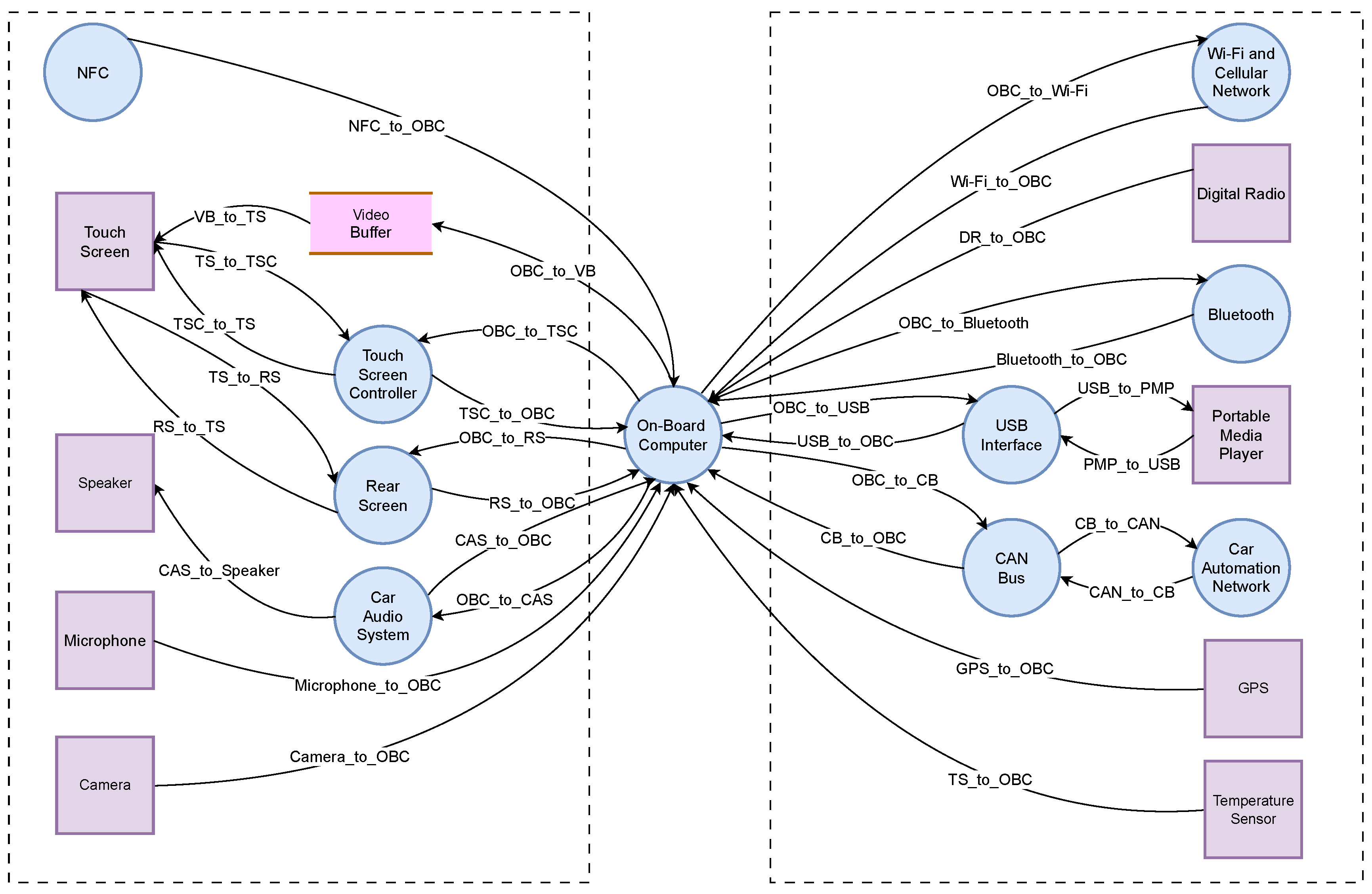
2.2. Proposed System Components
2.3. DFD
2.4. Threat Modeling Using STRIDE
2.5. Risk Assessment Methodologies
2.5.1. SAHARA
2.5.2. DREAD
- Damage (D): Signifying the potential impact of an attack.
- Reproducibility (R): Indicating the ease of replicating the attack.
- Exploitability (E): Assessing the effort required to execute the attack.
- Affected Users (A): The number of individuals who are going to experience the impact.
- Discoverability (D): Measuring the ease of identifying the threat.
3. Evaluation of Threats and Risk Rating
3.1. Analyzing Threats
3.2. Identified Threats
3.3. Rating Threats
4. Results and Discussion
4.1. Resultant Threats and Risks
4.2. Generalized Defense Mechanisms against STRIDE
5. Conclusion
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Watabe, H.; Yamada, H. Efforts toward realization of connected car society. Denso Ten Technical Review, 1, 2017; pp. 3-11.
- Hackers take Remote Control of Tesla’s Brakes and Door locks from 12 Miles Away. Available online: https://thehackernews.com /2016/09/hack-tesla-autopilot.html (accessed on 9 June 2023).
- Vehicle Cybersecurity: The Jeep Hack and Beyond. Available online: https://insights.sei.cmu.edu/blog/vehicle-cybersecurity-the-jeep-hack-and-beyond (accessed on 10 June 2023).
- Choi, J.; Jin, S.I. Security threats in connected car environment and proposal of in-vehicle infotainment-based access control mechanism. In Advanced Multimedia and Ubiquitous Engineering: MUE/FutureTech 2018 12, Springer Singapore, 2019; pp. 383-388.
- Takahashi, J.; Iwamura, M.; Tanaka, M. Security threat analysis of automotive infotainment systems. In 2020 IEEE 92nd Vehicular Technology Conference (VTC2020-Fall), IEEE, November 2020; pp. 1-7.
- Nie, S.; Liu, L.; Du, Y. Free-fall: Hacking tesla from wireless to can bus. Briefing, Black Hat USA, 25(1), 2017; pp. 16.
- Kamkar, S. Drive it like you hacked it: New attacks and tools to wirelessly steal cars. Presentation at DEFCON, 23, 2015; pp. 10.
- Computest. The connected car -Ways to get unauthorized access and potential implications. Research paper, 2018.
- Smith, C. The car hacker’s handbook: A guide for the penetration tester. No Starch Press, 2016.
- Bolz, R.; Kriesten, R. Automotive vulnerability disclosure: Stakeholders, opportunities, challenges. Journal of Cybersecurity and Privacy, 1(2), 2021; pp. 274-288. [CrossRef]
- Renganathan, V.; Yurtsever, E.; Ahmed, Q.; Yener, A. Valet attack on privacy: A cybersecurity threat in automotive Bluetooth infotainment systems. Cybersecurity, 5(1), 2022; pp. 30. [CrossRef]
- Moiz, A.; Alalfi, M.H. An approach for the identification of information leakage in automotive infotainment systems. In 2020 IEEE 20th International Working Conference on Source Code Analysis and Manipulation (SCAM), IEEE, September 2020; pp. 110-114.
- Scalas, M.; Giacinto, G. Automotive cybersecurity: Foundations for next-generation vehicles. In 2019 2nd International Conference on new Trends in Computing Sciences (ICTCS), IEEE, October 2019; pp. 1-6.
- Iorio, M.; Reineri, M.; Risso, F.; Sisto, R.; Valenza, F. Securing SOME/IP for in-vehicle service protection. IEEE Transactions on Vehicular Technology, 69(11), 2020; pp. 3450-13466. [CrossRef]
- Yang, Y.; Duan, Z.; Tehranipoor, M. Identify a spoofing attack on an in-vehicle CAN bus based on the deep features of an ECU fingerprint signal. Smart Cities, 3(1), 2020; pp. 17-30. [CrossRef]
- Koscher, K.; Czeskis, A.; Roesner, F.; Patel, S.; Kohno, T.; Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; Savage, S. Experimental security analysis of a modern automobile. In 2010 IEEE symposium on security and privacy, IEEE, May 2010; pp. 447-462.
- Dang, Q.A.; Khondoker, R.; Wong, K.; Kamijo, S. Threat analysis of an autonomous vehicle architecture. In 2020 2nd International Conference on Sustainable Technologies for Industry 4.0 (STI), IEEE, December 2020; pp. 1-6.
- Pascale, F.; Adinolfi, E.A.; Coppola, S.; Santonicola, E. Cybersecurity in automotive: An intrusion detection system in connected vehicles. Electronics, 10(15), 2021; pp. 1765. [CrossRef]
- Khan, R.; McLaughlin, K.; Laverty, D.; Sezer, S. STRIDE-based threat modeling for cyber-physical systems. In 2017 IEEE PES Innovative Smart Grid Technologies Conference Europe (ISGT-Europe), IEEE, September 2017; pp. 1-6.
- Benyahya, M.; Lenard, T.; Collen, A.; Nijdam, N.A. A Systematic Review of Threat Analysis and Risk Assessment Methodologies for Connected and Automated Vehicles. In Proceedings of the 18th International Conference on Availability, Reliability and Security, August 2023; pp. 1–10. [Google Scholar]
- Al Asif, M.R.; Hasan, K.F.; Islam, M.Z.; Khondoker, R. STRIDE-based cyber security threat modeling for IoT-enabled precision agriculture systems. In 2021 3rd International Conference on Sustainable Technologies for Industry 4.0 (STI), IEEE, December 2021; pp. 1-6.
- Salau, A.; Dantu, R.; Morozov, K.; Upadhyay, K.; Badruddoja, S. Towards a threat model and security analysis for data cooperatives. In Proceedings of the 19th International Conference on Security and Cryptography-SECRYPT, 2022; pp. 707-713.
- Shostack, A. Threat modeling: Designing for security. John Wiley & Sons, 2014.
- Alarcón, J.; Balcázar, I.; Collazos, C.A.; Luna, H.; Moreira, F. User interface design patterns for infotainment systems based on driver distraction: A Colombian case study. Sustainability, 14(13), 2022; pp. 8186. [CrossRef]
- Quintal, F.; Lima, M. HapWheel: In-car infotainment system feedback using haptic and hovering techniques. IEEE Transactions on Haptics, 15(1), 2021; pp. 121-130. [CrossRef]
- Designing infotainment systems that are interactive, not distractive. Automotive Technical Articles - TI E2E Support Forums, 6 June 2019. Available online: https://e2e.ti.com/blog_/b/behind_the_wheel/posts/designing-infotainment-systems-that-are-interactive-not-distractive (accessed on 12 August 2023).
- Meixner, G.; Häcker, C.; Decker, B.; Gerlach, S.; Hess, A.; Holl, K.; Klaus, A.; Lüddecke, D.; Mauser, D.; Orfgen, M.; Poguntke, M. Retrospective and future automotive infotainment systems—100 years of user interface evolution. Automotive user interfaces: Creating interactive experiences in the car, 2017; pp. 3-53.
- Berger, M.; Bernhaupt, R.; Pfleging, B. A tactile interaction concept for in-car passenger infotainment systems. In Proceedings of the 11th International Conference on Automotive User Interfaces and Interactive Vehicular Applications: Adjunct Proceedings, September 2019; pp. 109–114. [Google Scholar]
- Sen, G.; Sener, B. Design for luxury front-seat passenger infotainment systems with experience prototyping through VR. International Journal of Human–Computer Interaction, 36(18), 2020; pp. 1714-1733. [CrossRef]
- Josephlal, E.F.M.; Adepu, S. Vulnerability Analysis of an Automotive Infotainment System’s WIFI Capability. In 2019 IEEE 19th International Symposium on High Assurance Systems Engineering (HASE), IEEE, January 2019; pp. 241-246.
- Tashev, I.; Seltzer, M.; Ju, Y.C.; Wang, Y.Y.; Acero, A. Commute UX: Voice enabled in-car infotainment system. In Mobile HCI’09: Workshop on Speech in Mobile and Pervasive Environments (SiMPE), September 2009.
- Souppaya, M.; Scarfone, K. Guide to enterprise telework, remote access, and bring your own device (BYOD) security. NIST Special Publication, 800, 2016; pp. 46.
- Wolf, A.; Simopoulos, D.; D’Avino, L.; Schwaiger, P. The PASTA threat model implementation in the IoT development life cycle. Informatik 2020, 2021. [Google Scholar] [CrossRef]
- Yu, L.; Chen, K.; Chang, Y.; Chen, A.; Yin, Q.; Zhang, H. A New Correlation Model of IoT Attack Based on Attack Tree. In 2021 IEEE Intl Conf on Dependable, Autonomic and Secure Computing, Intl Conf on Pervasive Intelligence and Computing, Intl Conf on Cloud and Big Data Computing, Intl Conf on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech), IEEE, 2021, October; pp. 930-935.
- Ali, O.; Ishak, M.K.; Bhatti, M.K.L. Internet of things security: Modelling smart industrial thermostat for threat vectors and common vulnerabilities. In Intelligent Manufacturing and Mechatronics: Proceedings of SympoSIMM 2020; Springer: Singapore, 2021; pp. 175–186. [Google Scholar]
- Asif, M.R.A.; Khondoker, R. Cyber Security Threat Modeling of A Telesurgery System. In 2020 2nd International Conference on Sustainable Technologies for Industry, 2020; Vol. 4, pp. 1-6.
- Kim, K.H.; Kim, K.; Kim, H.K. STRIDE-based threat modeling and DREAD evaluation for the distributed control system in the oil refinery. ETRI Journal, 44(6), 2022; pp. 991-1003. [CrossRef]
- Tany, N.S.; Suresh, S.; Sinha, D.N.; Shinde, C.; Stolojescu-Crisan, C.; Khondoker, R. Cybersecurity Comparison of Brain-Based Automotive Electrical and Electronic Architectures. Information, 13(11), 2022; pp. 518. [CrossRef]
- Khan, A.; Bryans, J.; Sabaliauskaite, G. Framework for calculating residual cybersecurity risk of threats to road vehicles in alignment with ISO/SAE 21434. In International Conference on Applied Cryptography and Network Security, Cham: Springer International Publishing, June 2022; pp. 235-247.
- Birch, J.; Rivett, R.; Habli, I.; Bradshaw, B.; Botham, J.; Higham, D.; Jesty, P.; Monkhouse, H.; Palin, R. Safety cases and their role in ISO 26262 functional safety assessment. In Computer Safety, Reliability, and Security: 32nd International Conference, SAFECOMP 2013, Toulouse, France, Proceedings 32, Springer Berlin Heidelberg, 24-27 September 2013; pp. 154-165.
- Dempsey, K.L.; Johnson, L.A.; Scholl, M.A.; Stine, K.M.; Jones, A.C.; Orebaugh, A.; Chawla, N.S.; Johnston, R. Information security continuous monitoring (ISCM) for federal information systems and organizations, 2011.
- Grassi, P.A.; Fenton, J.L.; Garcia, M.E. Digital identity guidelines [including updates as of 12-01-2017], 2017.
- Macher, G.; Armengaud, E.; Brenner, E.; Kreiner, C. Threat and risk assessment methodologies in the automotive domain. Procedia Computer Science, 83, 2016; pp. 1288-1294.
- Macher, G.; Armengaud, E.; Brenner, E.; Kreiner, C. A review of threat analysis and risk assessment methods in the automotive context. In Computer Safety, Reliability, and Security: 35th International Conference, SAFECOMP 2016, Trondheim, Norway, Proceedings 35, Springer International Publishing, 21-23 September 2016.
- Macher, G.; Sporer, H.; Berlach, R.; Armengaud, E.; Kreiner, C. SAHARA: A security-aware hazard and risk analysis method. In 2015 Design, Automation & Test in Europe Conference & Exhibition, IEEE, March 2015; pp. 621-624.
- Available online: https://owasp.org/www-community/Threat_Modeling_Process#subjective-model-dread (accessed on 09 June 2023).
- Cagnazzo, M.; Hertlein, M.; Holz, T.; Pohlmann, N. Threat modeling for mobile health systems. In 2018 IEEE Wireless Communications and Networking Conference Workshops (WCNCW), IEEE, April 2018; pp. 314-319.
- Dang, Q. Recommendation for applications using approved hash algorithms. Gaithersburg, MD, USA: US Department of Commerce, National Institute of Standards and Technology, 2008.
- Macher, G.; Höller, A.; Sporer, H.; Armengaud, E.; Kreiner, C. A combined safety-hazards and security-threat analysis method for automotive systems. In Computer Safety, Reliability, and Security: SAFECOMP 2015 Workshops, ASSURE, DECSoS. ISSE, ReSA4CI, and SASSUR, Delft, The Netherlands, Proceedings 34, Springer International Publishing, 22 September 2015; pp. 237-250.
- Ahmed, A.A.; Ahmed, W.A. An effective multifactor authentication mechanism based on combiners of hash function over internet of things. Sensors, 19(17), 2019; pp. 3663. [CrossRef]
- Modarres, A.M.A.; Sarbishaei, G. An improved lightweight two-factor authentication potocol for IoT applications. IEEE Transactions on Industrial Informatics, 2022. [CrossRef]
- Khalid, H.; Hashim, S.J.; Ahmad, S.M.S.; Hashim, F.; Chaudhary, M.A. SELAMAT: a new secure and lightweight multi-factor authentication scheme for cross-platform industrial IoT systems. Sensors, 21(4), 2021; pp. 1428. [CrossRef]
- Yang, W.; Wang, S.; Sahri, N.M.; Karie, N.M.; Ahmed, M.; Valli, C. Biometrics for internet-of-things security: A review. Sensors, 21(18), 2021; pp. 6163. [CrossRef]
- Tait, B.L. Aspects of biometric security in internet of things devices. Digital Forensic Investigation of Internet of Things (IoT) Devices, 2021; pp. 169-186.
- Bhandari, R.; Kirubanand, V.B. Enhanced encryption technique for secure IoT data transmission. International Journal of Electrical and Computer Engineering, 9(5), 2019; pp. 3732. [CrossRef]
- Alizai, Z.A.; Tareen, N.F.; Jadoon, I. Improved IoT device authentication scheme using device capability and digital signatures. In 2018 International Conference on Applied and Engineering Mathematics (ICAEM), IEEE, September 2018; pp. 1-5.
- Ali, A.; Ahmed, M.; Khan, A. Audit logs management and security- A survey. Kuwait Journal of Science, 48(3), 2021. [CrossRef]
- Zhang, J.; Chen, H.; Gong, L.; Cao, J.; Gu, Z. The current research of IoT security. In 2019 IEEE Fourth International Conference on Data Science in Cyberspace (DSC), IEEE, June 2019; pp. 346-353.
- Mbarek, B.; Ge, M.; Pitner, T. Blockchain-based access control for IoT in smart home systems. In Database and Expert Systems Applications: 31st International Conference, DEXA 2020, Bratislava, Slovakia, September 14–17, 2020, Proceedings, Part II 31, Springer International Publishing, 2020; pp. 17-32.
- Borgiani, V.; Moratori, P.; Kazienko, J.F.; Tubino, E.R.; Quincozes, S.E. Toward a distributed approach for detection and mitigation of denial-of-service attacks within industrial Internet of Things. IEEE Internet of Things Journal, 8(6), 2020; pp. 4569-4578. [CrossRef]
- Tandon, R. A survey of distributed denial of service attacks and defenses. arXiv 2020, arXiv:2008.01345. [Google Scholar]
- Crowther, K.G.; Upadrashta, R.; Ramachandra, G. Securing Over-the-Air Firmware Updates (FOTA) for Industrial Internet of Things (IIOT) Devices. In 2022 IEEE International Symposium on Technologies for Homeland Security (HST), IEEE, November 2022; pp. 1-8.
- Rizvi, S.; Orr, R.J.; Cox, A.; Mehmood, M.; Amin, R.; Muslam, M.M.A.; Xie, J.; Aldabbas, H. Privilege Escalation Attack Detection and Mitigation in Cloud using Machine Learning. IEEE Access, 2023. [CrossRef]
| STRIDE Category | External Entity | Process | Data Flow | Data Store |
|---|---|---|---|---|
| Spoofing | ✓ | ✓ | ||
| Tampering | ✓ | ✓ | ✓ | |
| Repudiation | ✓ | ✓ | ||
| Information Disclosure | ✓ | ✓ | ✓ | |
| Denial of Service | ✓ | ✓ | ✓ | |
| Elevation of Privilege | ✓ |
| Level | Knowledge Example | Resources Example | Threat Criticality Example |
|---|---|---|---|
| 0 | No previous knowledge | No tools required | No impact |
| 1 | Basic knowledge of system | Standard tools, screwdriver | Partial service disruption |
| 2 | Proficient knowledge of internals with focused interests | Simple tools like sniffer, oscilloscope | Significant damage, manipulation of invoice and privacy |
| 3 | Advanced tools like bus communication simulators, flasher | High security impact possible |
| R | K | T | |||
|---|---|---|---|---|---|
| 0 | 1 | 2 | 3 | ||
| 0 | 0 | 0 | 3 | 4 | 4 |
| 1 | 0 | 2 | 3 | 4 | |
| 2 | 0 | 1 | 2 | 3 | |
| 1 | 0 | 0 | 2 | 3 | 4 |
| 1 | 0 | 1 | 2 | 3 | |
| 2 | 0 | 0 | 1 | 2 | |
| 2 | 0 | 0 | 1 | 2 | 3 |
| 1 | 0 | 0 | 1 | 2 | |
| 2 | 0 | 0 | 0 | 1 | |
| 3 | 0 | 0 | 0 | 1 | 2 |
| 1 | 0 | 0 | 0 | 1 | |
| 2 | 0 | 0 | 0 | 1 | |
| Rating | High | Medium | Low |
|---|---|---|---|
| Damage (D) | Extensive data loss, compromise of full system | Moderate data loss, potential compromise of personal or sensitive data | Limited data loss, minor information |
| Reproducibility (R) | Highly unlikely to be reproduced, requires extremely specific and uncommon circumstances | Possible to reproduce, but requires specialized knowledge or specific conditions | Easily reproducible with minimal effort |
| Exploitability (E) | Requires extensive knowledge, sophisticated tools and complex methods | Requires moderate technical skills, advanced tools and some effort | Requires basic technical knowledge and commonly available tools |
| Affected Users (A) | Many users affected, substantial impact on user privacy or security | Some users affected, potential inconvenience or minimal harm | Few users affected, limited impact on individuals |
| Discoverability (D) | Highly hidden, requires specialized expertise, extensive analysis, or insider knowledge | Hidden but discoverable with careful examination or targeted testing | Easily detected |
| Components or Interactions | Threat No. | Threat Details | Threat Category |
|---|---|---|---|
| On-Board Computer | 1 | An adversary can replicate the user actions to impersonate the process of on-board computer. | Spoofing |
| 2 | An adversary may modify any given command and instruction resulting in the modification of the system such as NFC to on-board computer. | Tampering | |
| 3 | Without proper monitoring and control, the on-board computer can be subject to malicious exploitation. | Repudiation | |
| 4 | An adversary may steal or share any personal information with anyone, which may violate the user’s privacy. | Information Disclosure | |
| 5 | In order to deny users of the on-board computer’s services, an adversary may flood it with requests so normal traffic cannot be processed. | Denial of Service | |
| 6 | Without the required authorization, an adversary might obtain access to the on-board computer and carry out privileged operations. | Elevation of Privilege | |
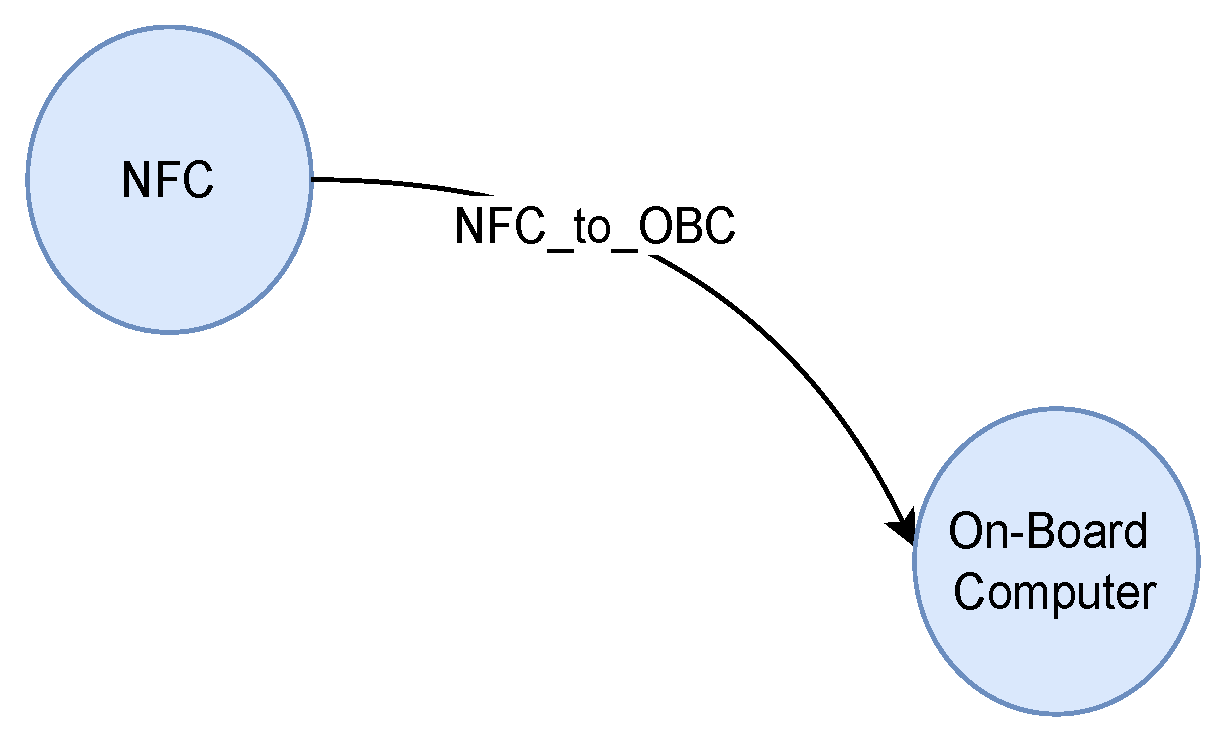
| NFC_to_OBC | 7 | On-Board Computer may crash, halt, stop, or run slowly because of the fake requests sent by the adversary through NFC. | Denial of Service |
| 8 | An adversary may interrupt data flowing across NFC to on-board computer with a snipping device and send a massive volume of data over the communication channel. | Denial of Service | |
| 9 | An adversary can intercept NFC data and use it to attack other parts of the system. | Information Disclosure | |
| 10 | An adversary may tamper the data flow from NFC to on-board computer in order to gain a particular advantage (not unlocking the door). | Tampering | |
| OBC_to_Wi-Fi | 11 | Wi-Fi and cellular network may crash or halt due to the overflow of traffic causing not connecting to the network. | Denial of Service |
| 12 | An adversary may interrupt data flowing across on-board computer to Wi-Fi and cellular network with a snipping device, and session hijacking may occur. | Denial of Service | |
| 13 | The data passing from on-board computer to Wi-Fi and cellular network may sniffed by the adversary causing the leakage of personal information. | Information Disclosure | |
| 14 | An adversary may tamper the data flow from on-board computer to Wi-Fi and cellular network and modify information to take remote control of the device. | Tampering | |
| Wi-Fi_to_OBC | 15 | On-Board Computer may crash, halt, stop, or run slowly due to the adversary making the resources and services unavailable. | Denial of Service |
| 16 | An adversary can disrupt the on-board computer’s performance by overwhelming its communication channels with a high volume of data, interrupting Wi-Fi and cellular network data flow. | Denial of Service | |
| 17 | The data passing from Wi-Fi and cellular network to on-board computer may sniffed by the adversary. This may lead to compliance violations. | Information Disclosure | |
| 18 | An adversary may tamper the data flow from Wi-Fi and cellular network to on-board computer and alter information. | Tampering | |
| OBC_to_Bluetooth | 19 | Bluetooth may crash, halt, stop, or run slowly due to the adversary making the resources and services unavailable. | Denial of Service |
| 20 | An external adversary may interrupt data flowing across a trust boundary by sending a large amount of data over communication channel. | Denial of Service | |
| 21 | The data passing from on-board computer to Bluetooth may sniffed by the adversary and disclose call logs or messages. | Information Disclosure | |
| 22 | An adversary may tamper the data flow from on-board computer to Bluetooth and alter information. | Tampering | |
| Bluetooth_to_OBC | 23 | On-Board Computer may crash, halt, stop, or run slowly because of the fake requests sent by the adversary. | Denial of Service |
| 24 | An external adversary may interrupt data flow and keep the system busy to respond to fake requests. | Denial of Service | |
| 25 | The data passing from on-board computer to Bluetooth may sniffed by the adversary. Based on the type of information disclosure, this may lead to attacks on other parts of the system. | Information Disclosure | |
| 26 | An adversary may tamper with the data flow from Bluetooth to on-board computer and make unauthorized manipulation to the system. | Tampering | |
| OBC_to_CB | 27 | An adversary may tamper the data flow from on-board computer to CAN bus and disclose the system information. | Denial of Service |
| 28 | An adversary may interrupt data flowing across on-board computer to CAN bus in either direction. | Denial of Service | |
| 29 | An adversary may tamper the data flow from on-board computer to CAN bus and disclose the system information. | Information Disclosure | |
| 30 | An adversary can manipulate Bluetooth data to cause a denial of service or elevation of privilege on the CAN bus. | Tampering | |
| CB_to_OBC | 31 | On-Board Computer may crash, halt, stop, or run slowly due to the adversary making the resources and services unavailable. | Denial of Service |
| 32 | An adversary may interrupt data flow across CAN bus to on-board computer in either direction. | Denial of Service | |
| 33 | An adversary can sniff the data flow, potentially enabling attacks on other system components based on the disclosed information. | Information Disclosure | |
| 34 | An adversary may tamper the data flow from CAN bus to on-board computer and alter information. | Tampering |
| Threat No. | SAHARA | DREAD | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| K | R | T | SecL | Priority | D | R | E | A | D | Sum | Priority | |
| 1 | 2 | 2 | 3 | 1 | High | 3 | 3 | 3 | 3 | 2 | 13 | High |
| 2 | 2 | 2 | 2 | 0 | Low | 3 | 2 | 3 | 2 | 2 | 10 | Medium |
| 3 | 2 | 3 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 4 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 5 | 1 | 2 | 2 | 1 | Low | 2 | 2 | 3 | 2 | 2 | 11 | Medium |
| 6 | 2 | 3 | 3 | 1 | High | 3 | 2 | 2 | 2 | 3 | 12 | High |
| 7 | 1 | 2 | 2 | 1 | Low | 2 | 3 | 2 | 3 | 2 | 12 | High |
| 8 | 2 | 3 | 3 | 1 | High | 3 | 3 | 2 | 3 | 1 | 12 | High |
| 9 | 2 | 2 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 10 | 2 | 1 | 3 | 2 | High | 3 | 2 | 3 | 3 | 2 | 13 | High |
| 11 | 1 | 3 | 2 | 0 | Low | 2 | 3 | 1 | 2 | 2 | 10 | Medium |
| 12 | 2 | 3 | 3 | 1 | High | 2 | 2 | 3 | 3 | 2 | 12 | High |
| 13 | 1 | 2 | 3 | 2 | High | 3 | 2 | 3 | 3 | 2 | 13 | High |
| 14 | 2 | 3 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 15 | 2 | 3 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 16 | 2 | 3 | 3 | 1 | High | 2 | 3 | 2 | 3 | 2 | 12 | High |
| 17 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 2 | 3 | 12 | High |
| 18 | 2 | 3 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 19 | 1 | 2 | 2 | 1 | Low | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 20 | 2 | 3 | 3 | 1 | High | 2 | 2 | 3 | 3 | 2 | 12 | High |
| 21 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 22 | 2 | 2 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 23 | 1 | 2 | 3 | 2 | High | 2 | 3 | 2 | 3 | 2 | 12 | High |
| 24 | 2 | 2 | 3 | 1 | High | 2 | 3 | 2 | 3 | 2 | 12 | High |
| 25 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 2 | 2 | 12 | High |
| 26 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 27 | 1 | 2 | 3 | 2 | High | 3 | 2 | 3 | 3 | 2 | 13 | High |
| 28 | 2 | 2 | 3 | 1 | High | 2 | 2 | 3 | 3 | 2 | 12 | High |
| 29 | 2 | 2 | 3 | 1 | High | 3 | 2 | 3 | 2 | 2 | 12 | High |
| 30 | 2 | 3 | 3 | 1 | High | 3 | 2 | 3 | 3 | 2 | 13 | High |
| 31 | 1 | 3 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 32 | 2 | 2 | 3 | 1 | High | 3 | 2 | 3 | 3 | 2 | 13 | High |
| 33 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| 34 | 2 | 2 | 3 | 1 | High | 3 | 2 | 2 | 3 | 2 | 12 | High |
| STRIDE Category | Threat Details | Mitigation |
|---|---|---|
| Spoofing | Adversary pretends to be a legitimate user or system | Multi-factor authentication [50,51,52], Biometric authentication [53,54] |
| Tampering | Adversary modifies data or software without authorization | Encryption [55], Digital signature [56] |
| Repudiation | Adversary denies responsibility for actions they have taken | Logging and auditing mechanisms to track and trace user actions [57] |
| Information Disclosure | Adversary gains access to sensitive information | Access controls and permissions to limit access to sensitive data [58,59] |
| Denial of Service | Adversary prevents legitimate users from accessing a system or service | Rate limiting and load balancing to distribute traffic across multiple servers [60,61] |
| Elevation of Privilege | Adversary gains higher levels of access than they are authorized to have | Secure coding practices [62], User activity monitoring and logging to detect potential privilege escalation attempts [63] |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




