Submitted:
31 January 2023
Posted:
01 February 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Not affecting the visual appearance of Imout to a great extent.
- Making it more difficult to estimate Noisecam from the new processed image.
2. Materials and Methods
2.1. PRNU or “Camera Fingerprint”
2.2. Attacking Methods
- Noise addition (or modification): randomizing least significant components (bits) does not add or reduce noise but it merely modifies it. Nevertheless, it is the first idea that comes up, fingerprints are based on noise and modifying noise might work.
- Geometric distortion: geometric distortions like pixel position scrambling and/or rotating and de-rotating image (with a slight angle error) have had success against other “noise like” patterns like watermarks.
- Noise reduction: if image noise is reduced, the fingerprint will also be erased (at least to some extent).
- Combined methods: methods constructed cascading two or more of the previous ones (may be from the same category or not).
2.2.1. Noise Addition (or modification)
2.2.2. Geometric Distortions
- Scrambling pixels: moving them to a nearby, random position (a maximum radius, r, is defined to maintain the process controlled). Gaussian distribution is used to scramble pixels.
- Rotating and de-rotating: image is rotated a significant angle (say α=15º). Pixel “bicubic” interpolation is forced. Then image is “de-rotated” (rotated again an angle of –α+β, where β is a small error, say 0.50º). Bicubic interpolation is forced again. This operation produces some artifacts on image corners that can be avoided by simple techniques that will become part of processing
- Scaling and de-scaling: image is up-scaled by a significant factor (say sf=3). “Lanczos3” interpolation [15] is forced. Then the first line and the first column are erased. Image is downscaled to its original size, forcing a “non-uniform sampling” and using “Lanczos2” interpolation.
2.2.3. Noise Reduction
2.2.4. Combined Methods
- Combination of simple noise addition and geometric techniques. No Wiener or other noise reduction (n=3, r=2, α=10º, β=0.5º, sf=3).
- Wiener filtering first, rotation and de-rotation (α=10º, β=0.5º), followed by a “deblurring” method for improving image quality, concretely: Lucy-Richardson deconvolution filter [16].
2.3. Design of Tests
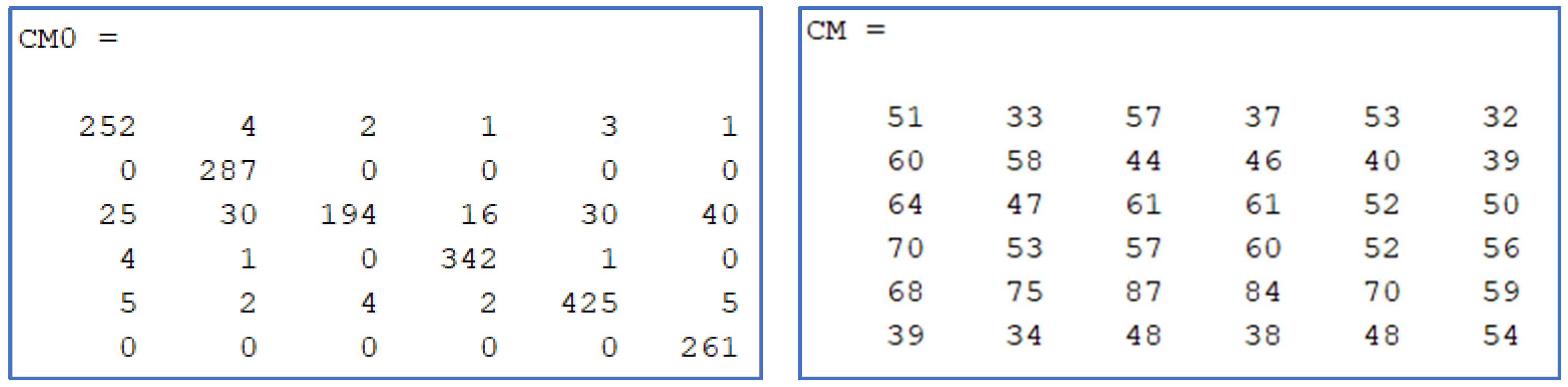
- A confusion matrix for all cameras is computed (understood as the truth table resulting from trying to identify the source camera for all images that are NOT used in computing the PRNU). This allows us measuring the “camera identification error rate” before any attack is applied.
- Each of the attacks defined in section 2.2 is applied re-computing the confusion matrix and error rate.
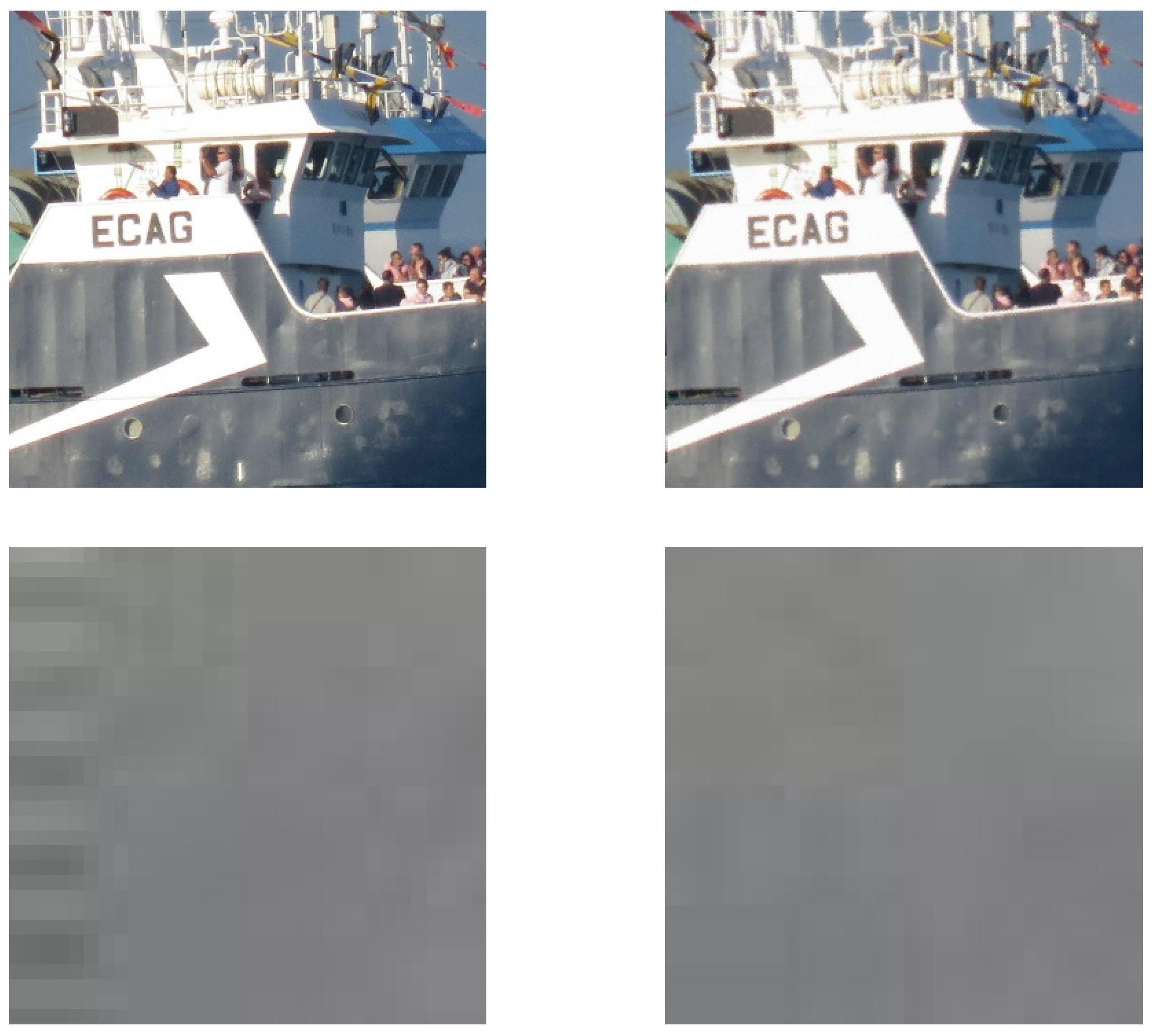
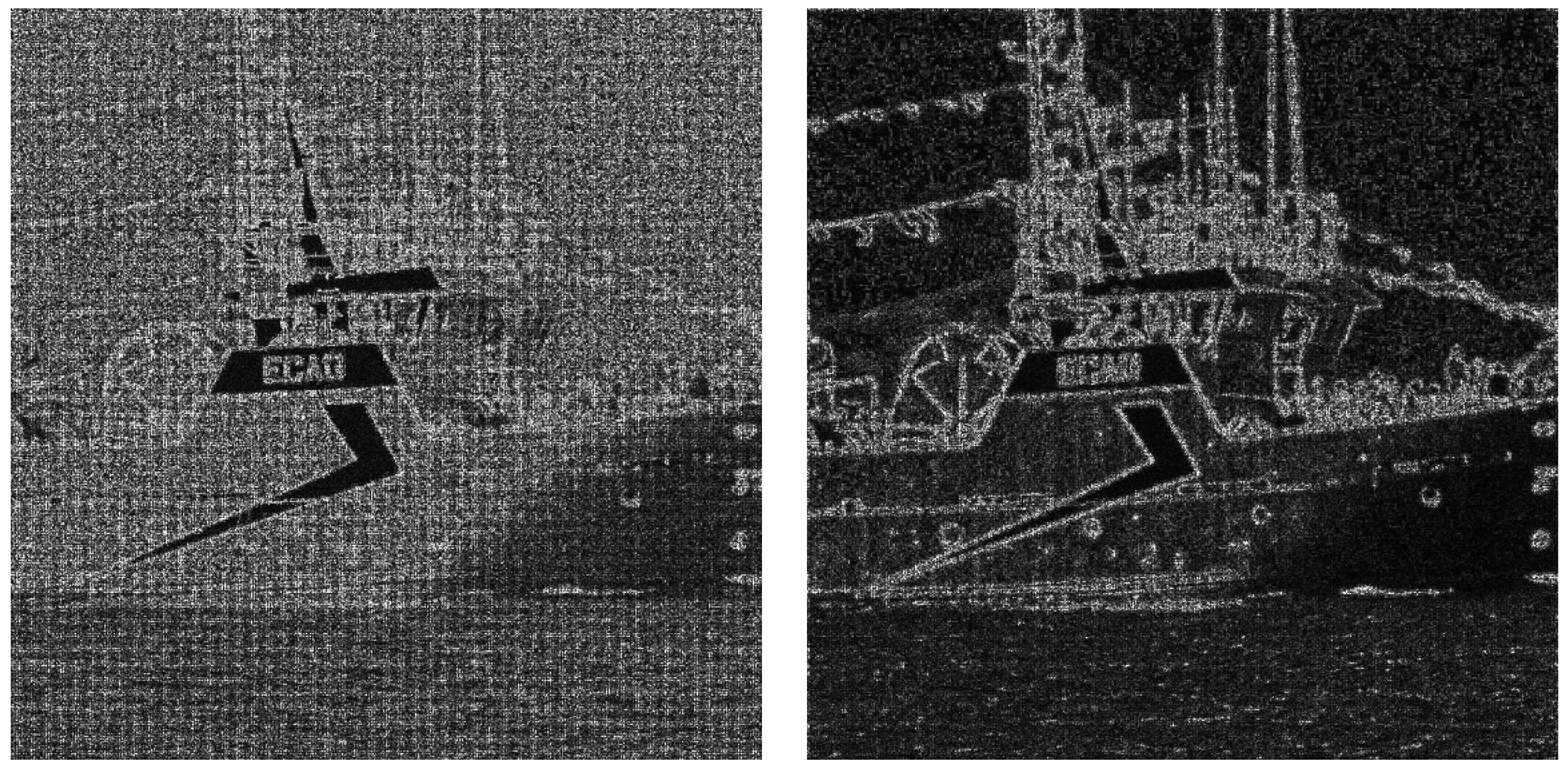
- SNR (Signal to Noise Ratio) after the attack (considering original and attacked, or noisy, images) is also computed as a means for considering image quality degradation. In the next section, average SNR for each method or “attack” is presented, “visual” quality of processed images is also checked via human volunteers.
3. Results
4. Discussion
4.1. Genral Conclusions and Future Lines
4.2. Selecting a Method
- Cropping image to erase “non-defined” border pixels.
- Re-scaling image to original size.
4.3. Future Lines
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- M. Chen et al, “Determining image origin and integrity using sensor noise”, IEEE Transactions on Information Forensics and Security (TIFS), 2008, vo. 3, no. 1, pp. 74-90. [CrossRef]
- A. Pedrouzo-Ulloa et al, “Camera attribution forensic analyzer in the encrypted domain”, in IEEE International Workshop on Information Forensics and Security (WIFS), IEEE (2018). [CrossRef]
- P.M. Pérez-Miguélez and F. Pérez-González, Study and implementation of PRNU-based image clustering algorithms, Master Thesis (University of Vigo, Spain), Vigo (2019).
- J. Bernacki, “A survey on digital camera identification methods”, Forensic Science International: Digital Investigation, 2020, vol. 34. [CrossRef]
- M. Goljan, J. Fridrich and M. Chen, “Defending Against Fingerprint-Copy Attack in Sensor-Based Camera Identification”, IEEE Transactions on Information Forensics and Security, 2011, vol. 6, no. 1, pp 227-236. [CrossRef]
- L.J. García-Villalba, A.L. Sandoval-Orozco, J. Rosales-Corripio, J. Hernández-Castro, “A PRNU-based counter-forensic method to manipulate smartphone image source identification techniques”, Future Generation Computer Systems, 2017, Vol 76, pp 418-427. [CrossRef]
- Available online: https://sourceforge.net/projects/prnudecompare/ (accessed on 25 January 2023).
- G. J. Bloy, “Blind camera fingerprinting and image clustering”, IEEE Transactions on Pattern Analysis and Machine Intelligence (PAMI), 2008, vol. 30, no. 3, pp. 532-534. [CrossRef]
- H. Ogawa and E. Oja, “Projection filter, Wiener filter, and Karhunen-Loève subspaces in digital image restoration”, Journal of Mathematical Analysis and Applications, 1986, vol. 114, no. 1, pp. 37-51. [CrossRef]
- M. Goljan, J. Fridrich and T. Filler, “Large Scale Test of Sensor Fingerprint Camera Identification”, Procceedings of SPIE, Electronic Imaging, Media Forensics and Security XI, 2009, vol. 7254, no. 0I, pp. 01-12. [CrossRef]
- Camera Fingerprint Homepage (from professor Goljan). Available online: http://dde.binghamton.edu/download/camera_fingerprint/ (accessed on 25 January 2023).
- C.K. Chui, An Introduction to Wavelets, Academic Press, San Diego (1992).
- B.V.K.V. Kumar and L.G. Hassebrook, “Performance measures for correlation filters”, Applied Optics, 1990, vol. 29, no. 20, pp. 2997-3006. [CrossRef]
- A.B. Watson, “DCT quantization matrices visually optimized for individual images”, Proceedings of SPIE, 1993, vol. 1913, no. 14, pp. 1-15. [CrossRef]
- P. Getreuer, “Linear Methods for Image Interpolation”, Image Processing On Line, 2011, vol. 1, pp. 238-259. [CrossRef]
- W.H. Richardson, “Bayesian-Based Iterative Method of Image Restoration”, Journal of the Optical Society of America, 1972, vol. 62, no. 1, pp. 55-59. [CrossRef]
- T. Gloe, Rainer Böhme, “The ‘Dresden Image Database’ for Benchmarking Digital Image Forensics”, Proceedings of the 2010 ACM Symposium on Applied Computing, ACM (2010). [CrossRef]
- D. Shullani et al, “VISION: a video and image dataset for source identification”, Eurasip Journal on Information Security, 2017, Vol 15. [CrossRef]
- MATLAB. Available online: https://es.mathworks.com/products/matlab.html (accessed on 25 January 2023).

| ATACKING METHOD: | Key Letter: | Visual Quality: | SNR (av. dB): | Mean exec. time (s): | <<Error Rate>>, Non fooled train set (%). |
<<Error Rate>>, Fooled train set (%). |
|---|---|---|---|---|---|---|
| Aleatorizing least significant bits (n=3). | A | Good, except color degradations (clouds). | 38 | 2.59 | 9.30 | 10.48 |
| Introducing noise on DCT coefficients. | B | Good | 49 | 6.48 | 9.50 | 9.55 |
| Scramble randomly pixels (r=1). | C | Good | 31 | 3.24 | 11.25 | 11.72 |
| Rotating and de-rotating (A=10º,a=0.5º). | D | Good, except artifacts on borders. | 22 | 2.88 | 78.16 | 9.75 |
| Scaling and de-scaling (sf=3). | E | Good | 44 | 3.36 | 9.19 | 9.30 |
| Ordinary wiener filter. | F | Good | 31 | 0.25 | 32.58 | 23.28 |
| Wavelet transform wiener filtered and inverted. | G | Good | 41 | 0.51 | 10.74 | 12.75 |
| Combination of simple noise addition and geometric techniques (n=3, r=2, A=10º, a=0.5º, sf=3). | H | Good, artifacts in some borders, quantification in color degradation areas (sky, clouds). | 23 | 3.68 | 81.72 (*) | 47.23 |
| Wiener + dotating/derotating + deblurring (Lucy) | I | Good | 23 | 2.90 | 78.83 | 25.29 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




