Submitted:
27 April 2026
Posted:
28 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
- 1.
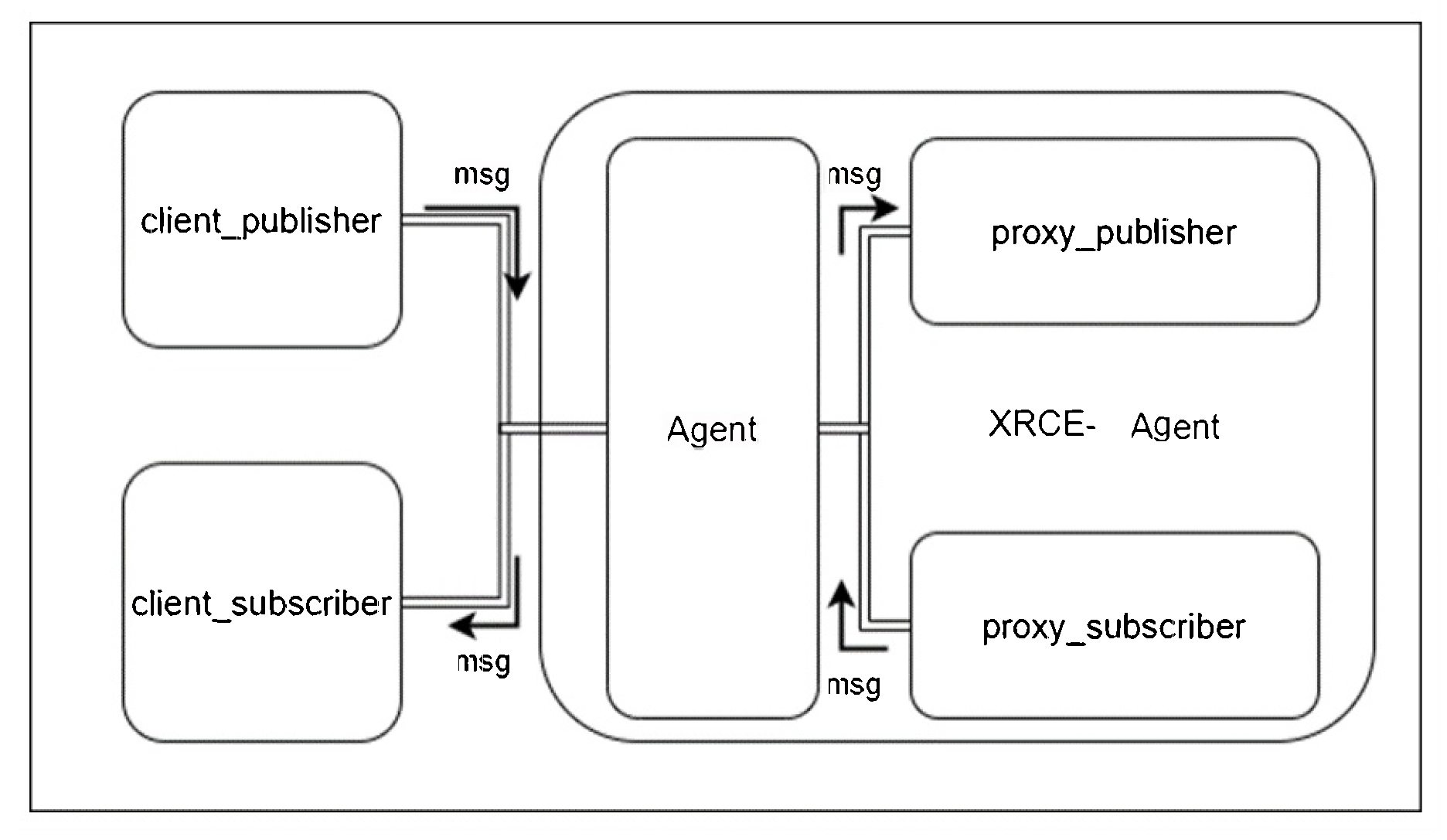
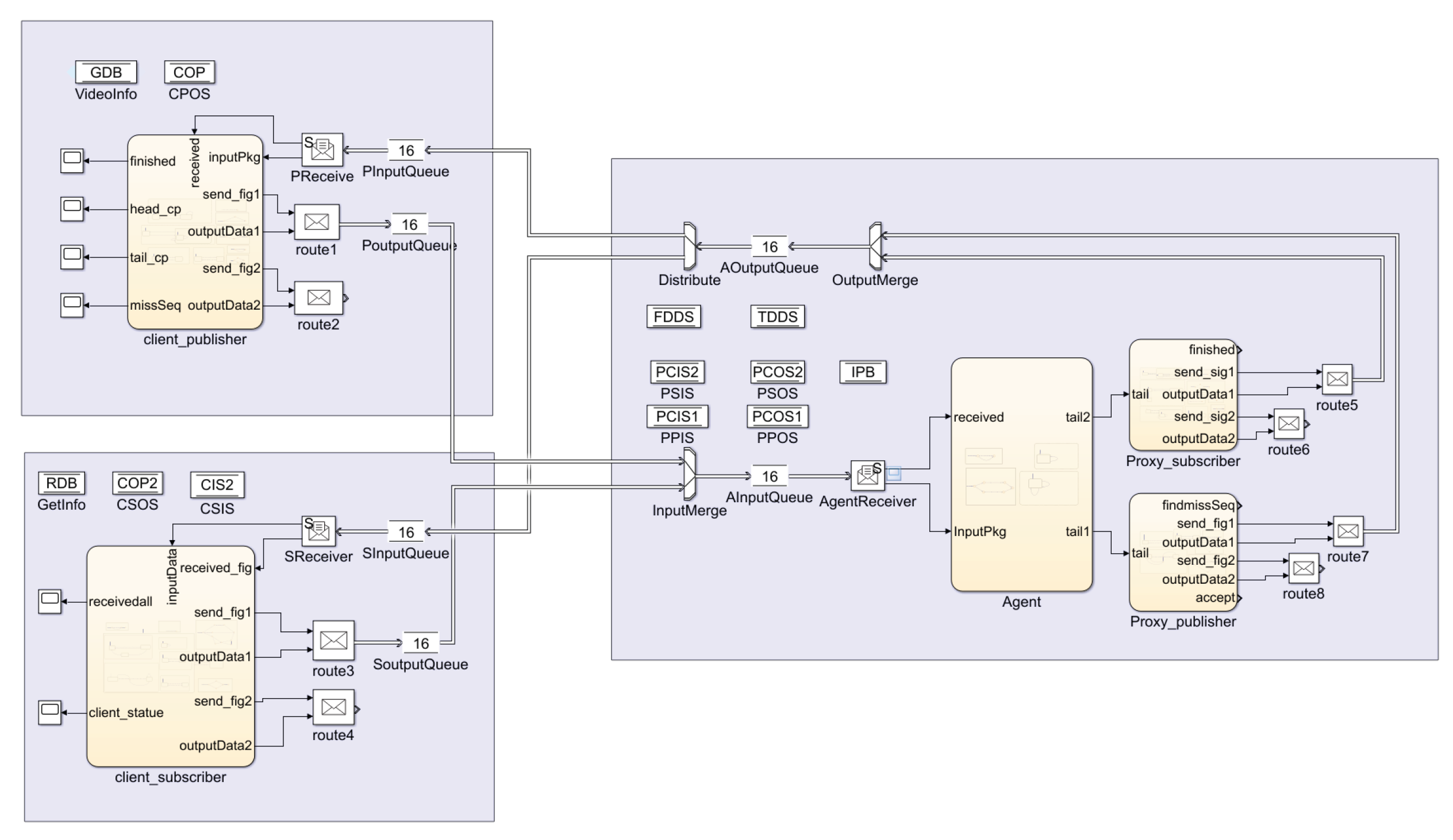
- This study treats the Micro-ROS communication middleware, specifically Micro XRCE-DDS, as a time-critical system and builds abstract modeling. Based on the open-source code of XRCE-DDS, timed automata models are built, including parallel of the client_publisher, client_subscriber, Agent, proxy_publisher, and proxy_subscriber modules.
- 2.
- A constrained signal temporal logic, denoted as , is proposed to describe the properties of the Micro-ROS communication mechanism. Key properties are formally specified by the constrained signal temporal logic. Based on an analysis of the XRCE-DDS protocol, critical properties are extracted from natural language descriptions and subsequently converted into logical formulas.
- 3.
- This paper proposes a co-simulation and runtime verification framework based on models for Micro-ROS. The framework is implemented in Simulink/Stateflow, where simulations are conducted and runtime verification is performed to validate critical system properties.
2. Related Work
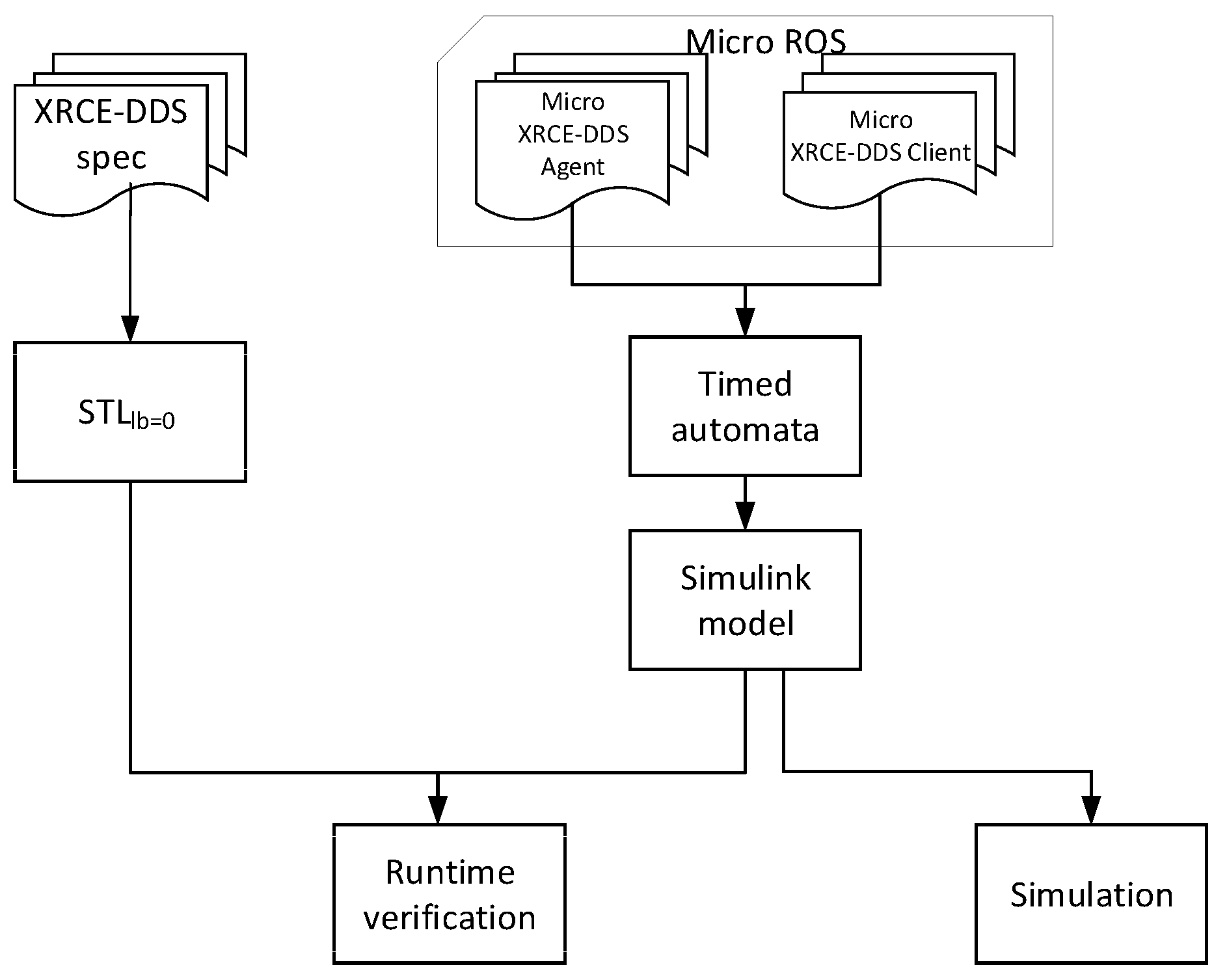
3. Framework of Micro-ROS Modeling and Analysis
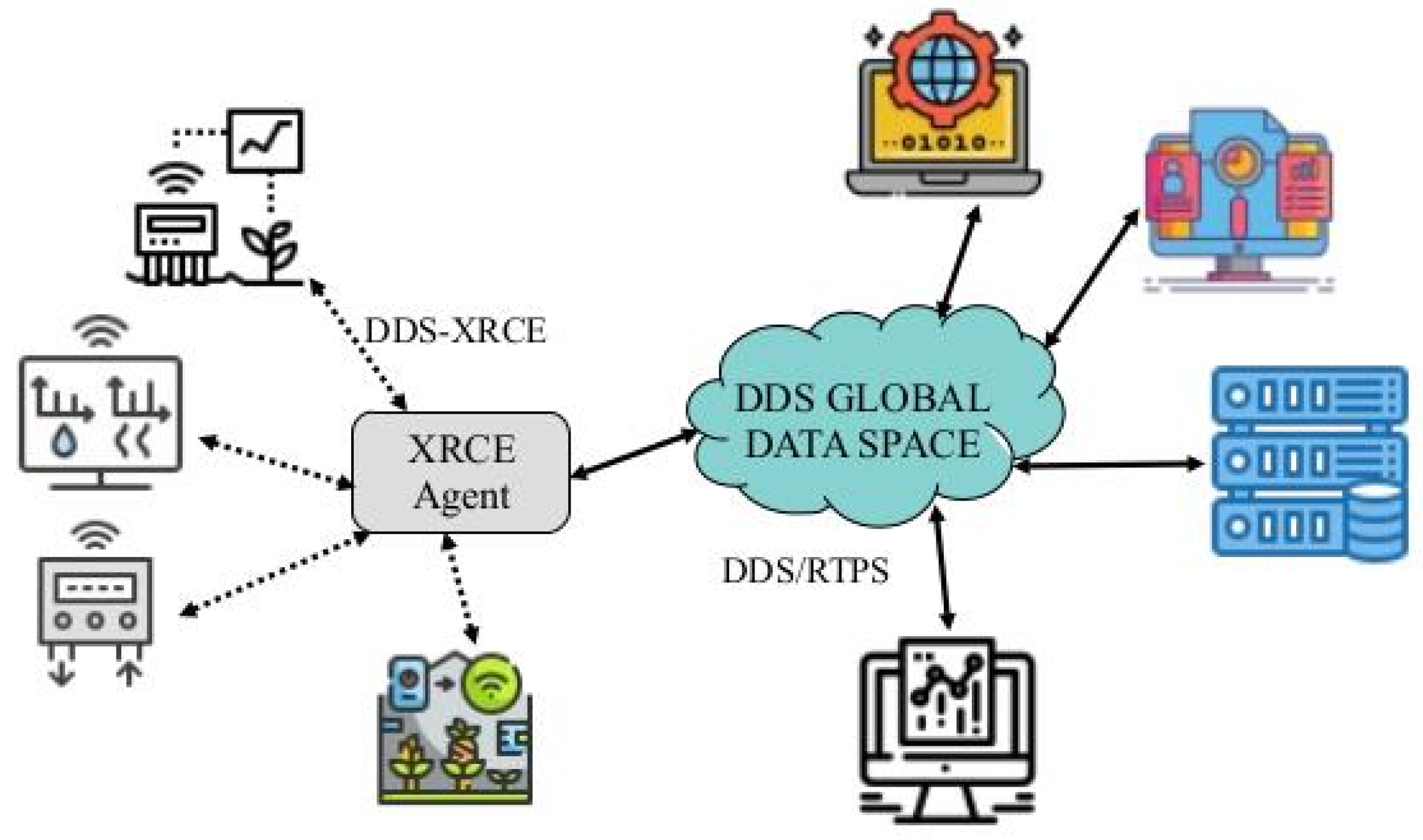
3.1. Micro XRCE-DDS Communication Mechanism
3.2. Time Automata
- : is the set of locations.
- is the initial location set.
- is a finite set of actions or events. Here, actions are divided into two types: general actions and communication actions. Specifically: denotes sending a message through channel c; denotes receiving a message via channel c and storing it in the variable .
- C is the finite set of clocks.
- : is the Invariant Function.
- is the set of transition relation.
3.3. Framework of the Micro-ROS
4. Formal Modeling the Micro-ROS
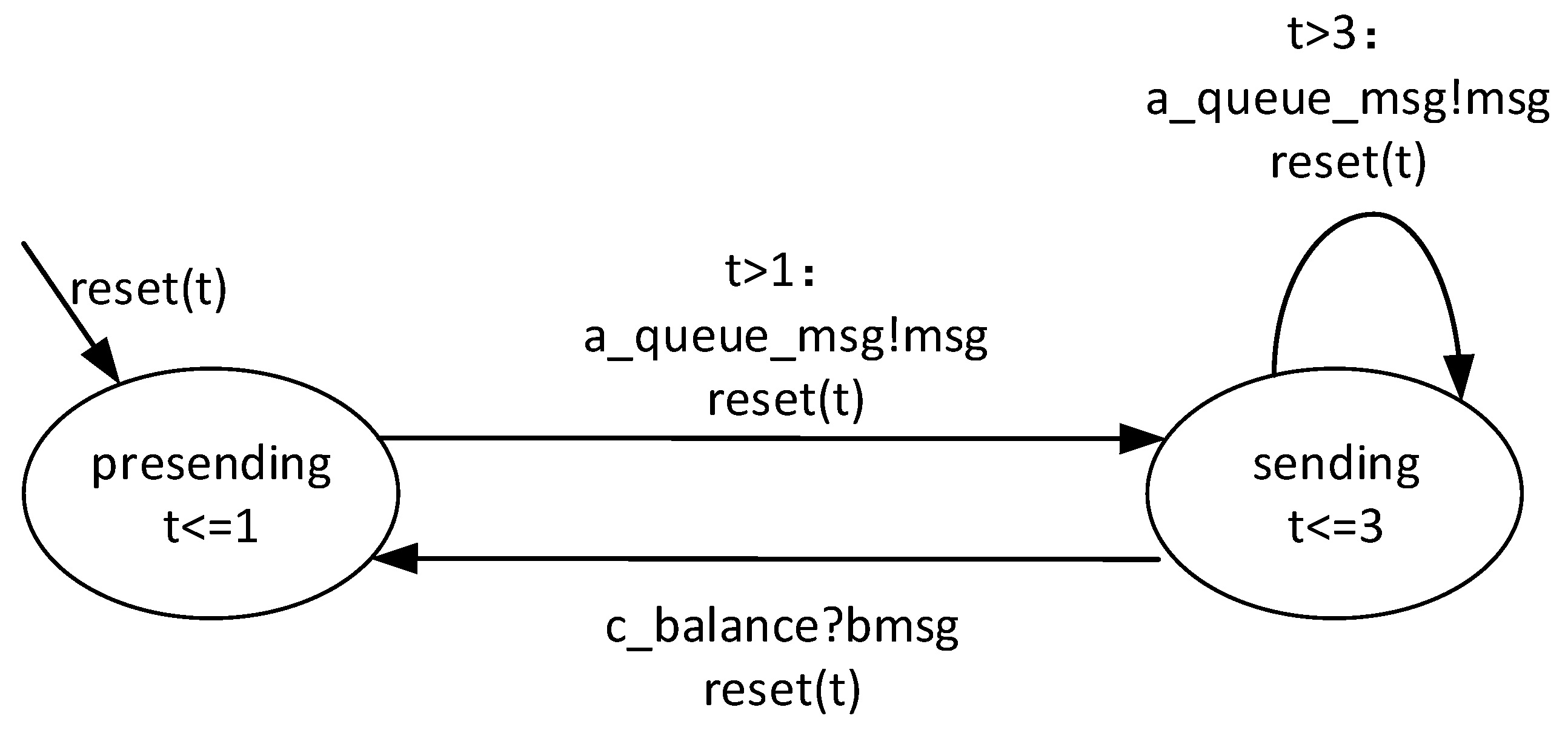
4.1. Client_Publisher Model
- .
- .
- .
- represents the clock set.
- . It is the invariant function in the reliable output stream model.
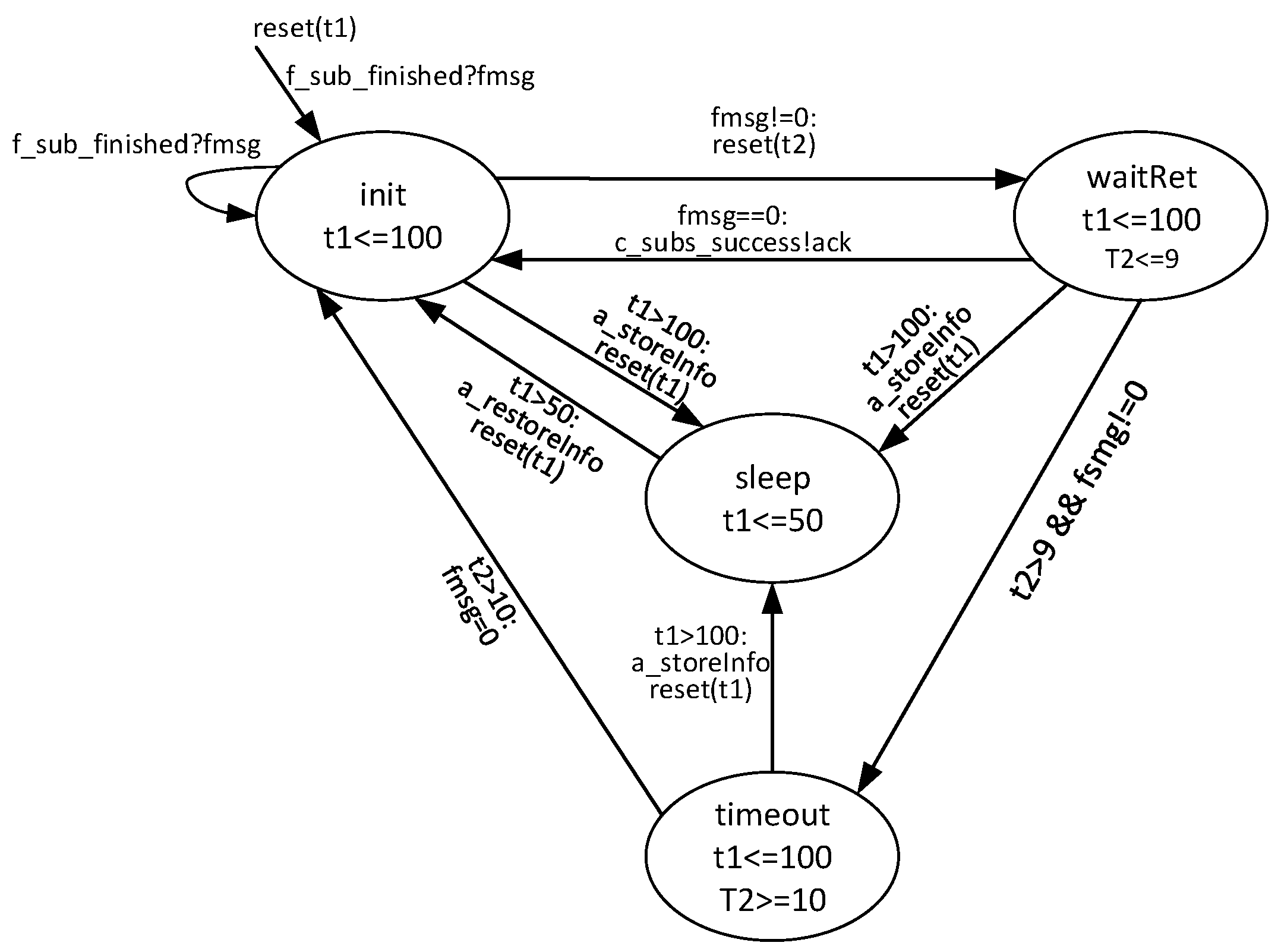
- ↦ is the set of transition relation in , shown as Figure 4.
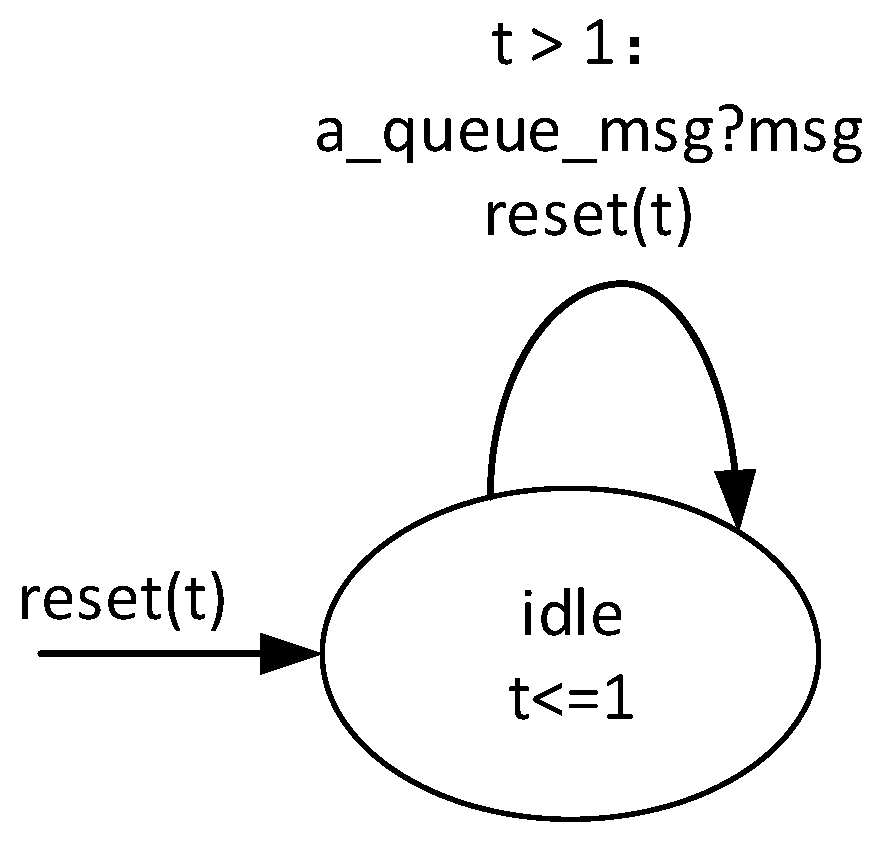
4.2. Client_Subscriber Model
- .
- .
-
.The communication actions are , and . is a channel with a certain capacity, capable of facilitating asynchronous communication.
- represents the clock set. is the clock used to record awake and sleep durations. tracks whether the sending time has exceeded the timeout threshold.
-
, ,, .
- ↦ is the set of transition relation in , shown as Figure 5.
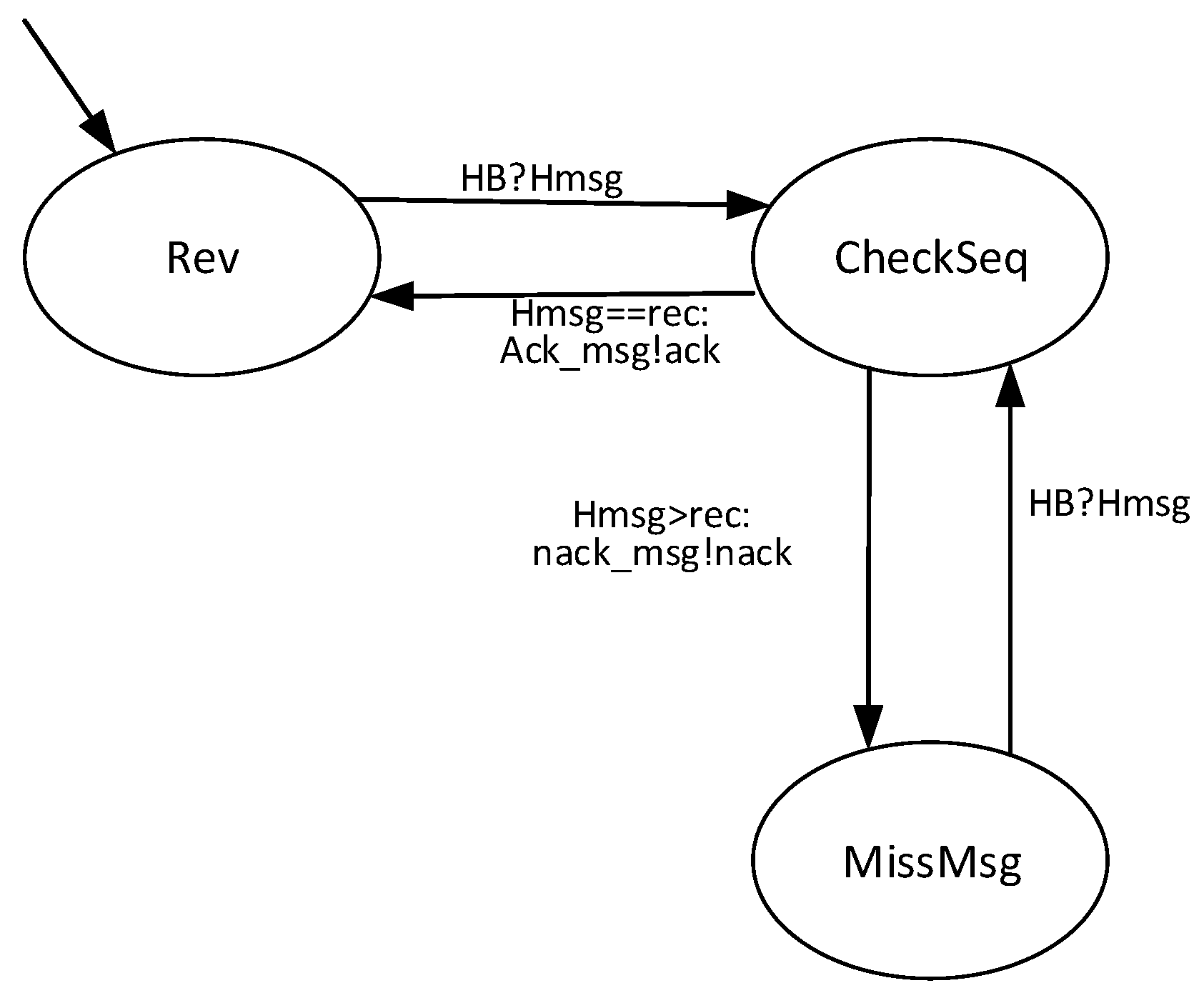
4.3. Agent Model
- .
- .
- .
- .
- The transition relation is shown as Figure 6.
4.4. Proxy_Publisher Model
- .
- .
- .
- .
- .
- ↦ is the set of transition relation in , shown as Figure 7.
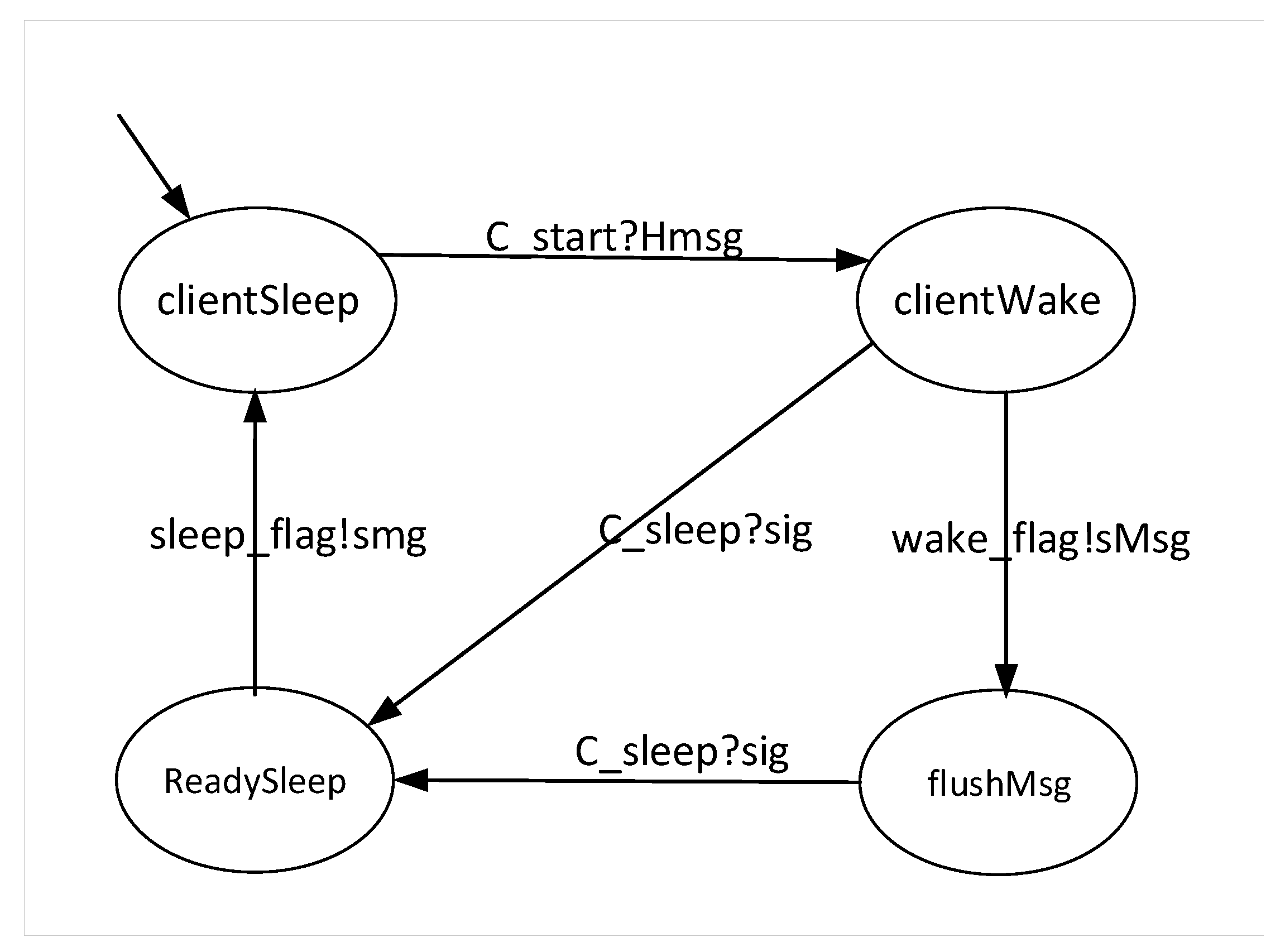
4.5. Proxy_Subscriber Model
- .
- .
- .
- .
- .
- ↦ is the set of transition relation in , shown as Figure 8.
5. Properties of Micro-ROS Model
5.1. Constrained Signal Temporal Logic
5.2. Key Properties Abstraction
- •
-
property ECFS: All messages sent by the client_publisher can be delivered.The property is formulated as follows:In runtime verification, when the proxy_publisher receives all messages sent by the client_publisher, the signal eventually becomes 1, indicating that all messages have been delivered.
- •
-
property ECRA: The client_subscriber can receive all messages to which it has subscribed.This property is formulated as follows:In runtime verification, when the client_subscriber has received all subscribed messages, the signal eventually becomes 1.
- •
-
property NIWS: Once the client_subscriber enters sleep mode, no additional messages will arrive to wake it.This property is formulated as follows:When the client_subscriber enters sleep mode (indicated by the signal changing to 1), it will no longer passively receive messages from the proxy_subscriber. At this point, the value of the signal for message arrivals becomes false and remains so throughout the sleep duration (50 seconds).
- •
-
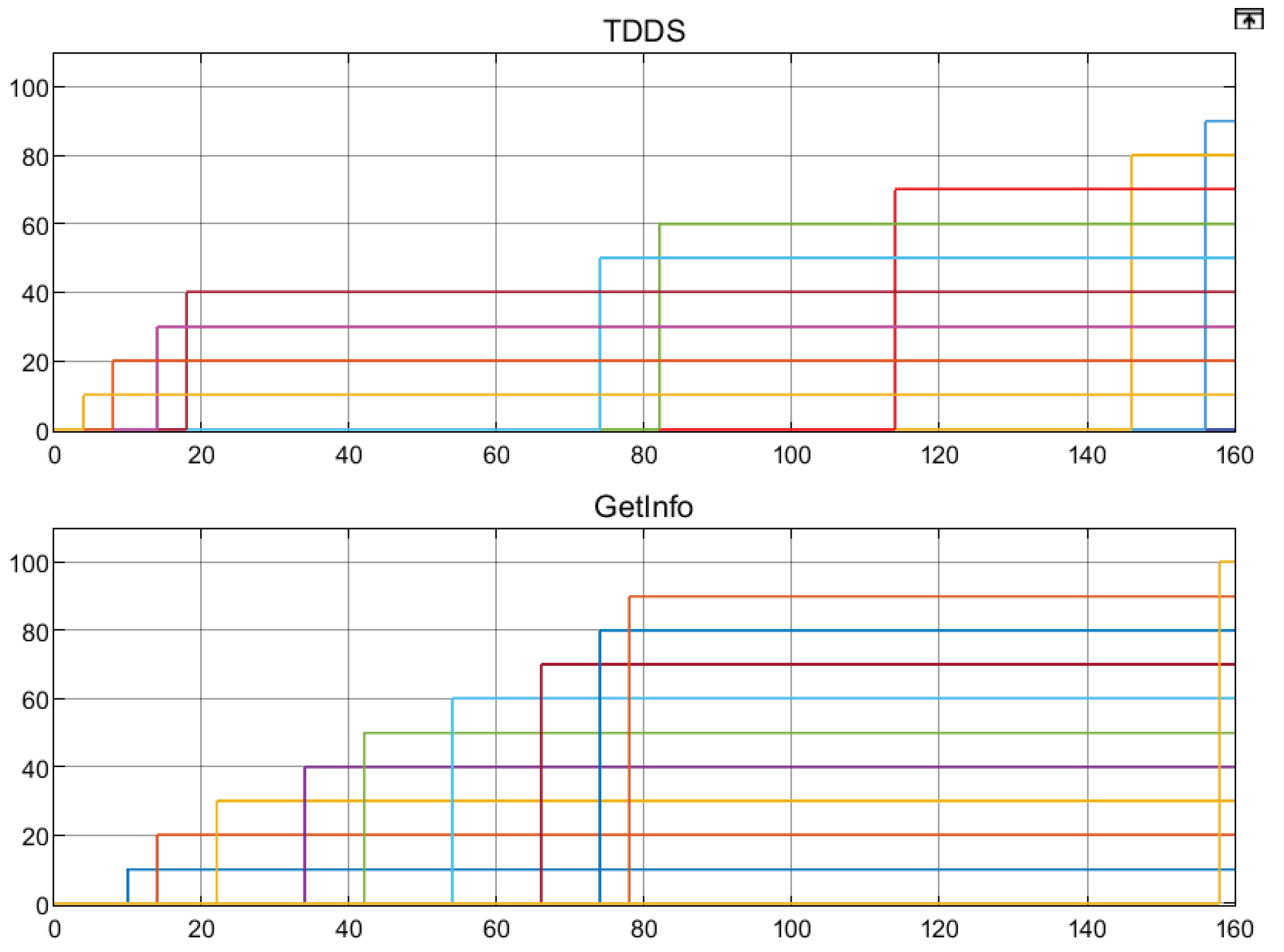
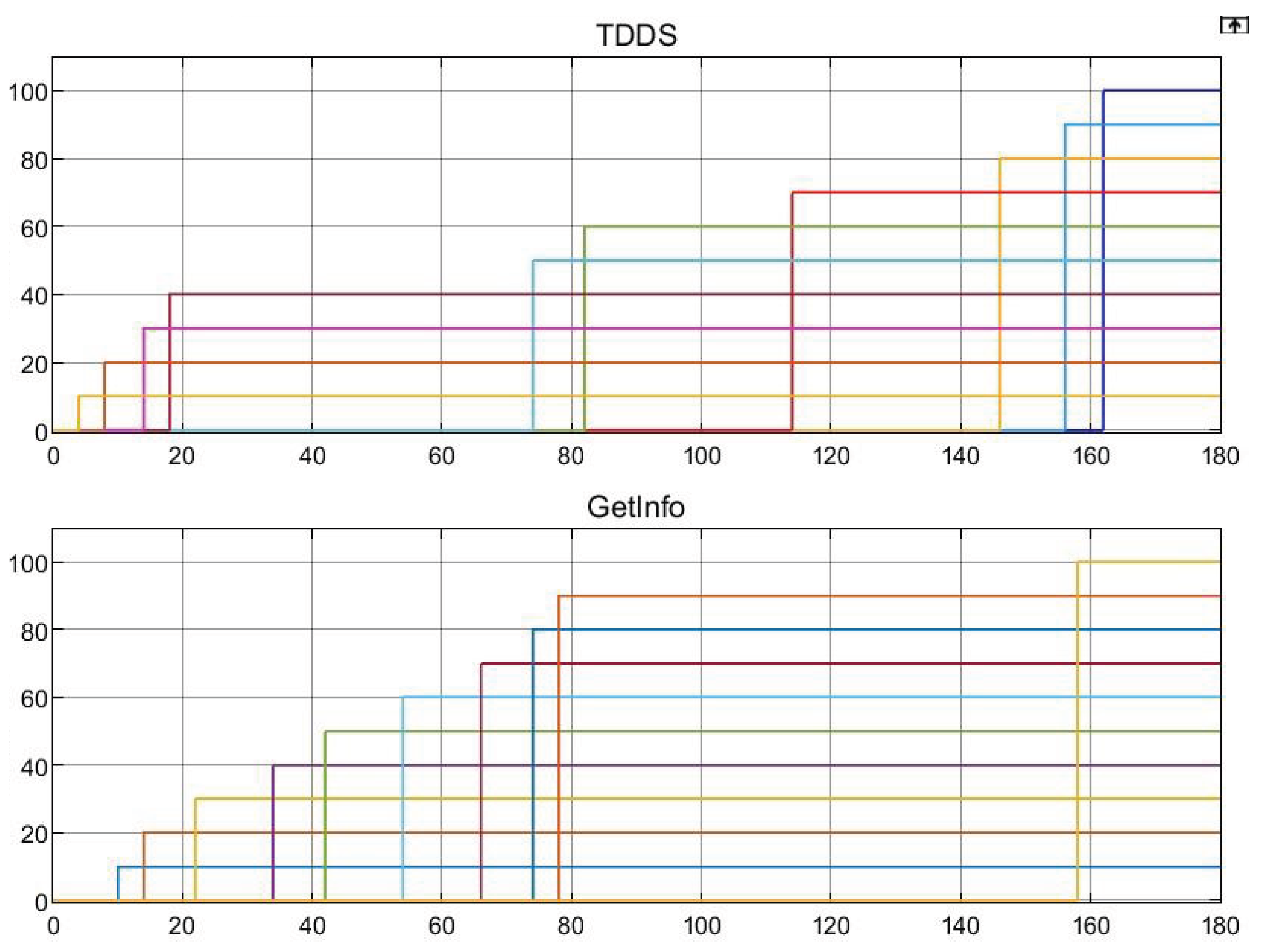
property RMIO: The proxy_publisher always receives messages in the same order as they are sent by the client_publisher.This property is formulated as follows:When the proxy_publisher receives the 10th message (i.e., the final message), the array containing the messages to be sent must be identical to the TDDS array of received messages. Since the array indices correspond to the sequential order of message transmission and reception, identical arrays indicate that the order of message sending and receiving order is consistent.
- •
-
property RMIO2: The client_subscriber always receives messages in the same order as they are sent by the proxy_subscriber.This property is formulated as follows:When the client_subscriber receives the 10th message (i.e., the final message), the array containing the messages to be sent must be identical to the FDDS array of received messages. Since the array indices correspond to the sequential order of message transmission and reception, identical arrays indicate that the order of messages sending and receiving is consistent.
- •
-
property TMRK: When a message is lost, the receiver can detect it in a timely manner.This property is formulated as follows:If a message is not acknowledged by the receiver, the receiver will detect the loss within 20 seconds and notify the sender of the missing sequence number by setting the signal.
- •
-
property FARS: All messages not received by the client_subscriber will be promptly resent by the proxy_subscriber.This property is formulated as follows:When the client_subscriber fails to receive a message, the value of the proxy_subscriber will be greater than the acknowledged value of . The proxy_subscriber attempts to resend the message; upon successful transmission, it adjusts the value to match within 20 seconds.
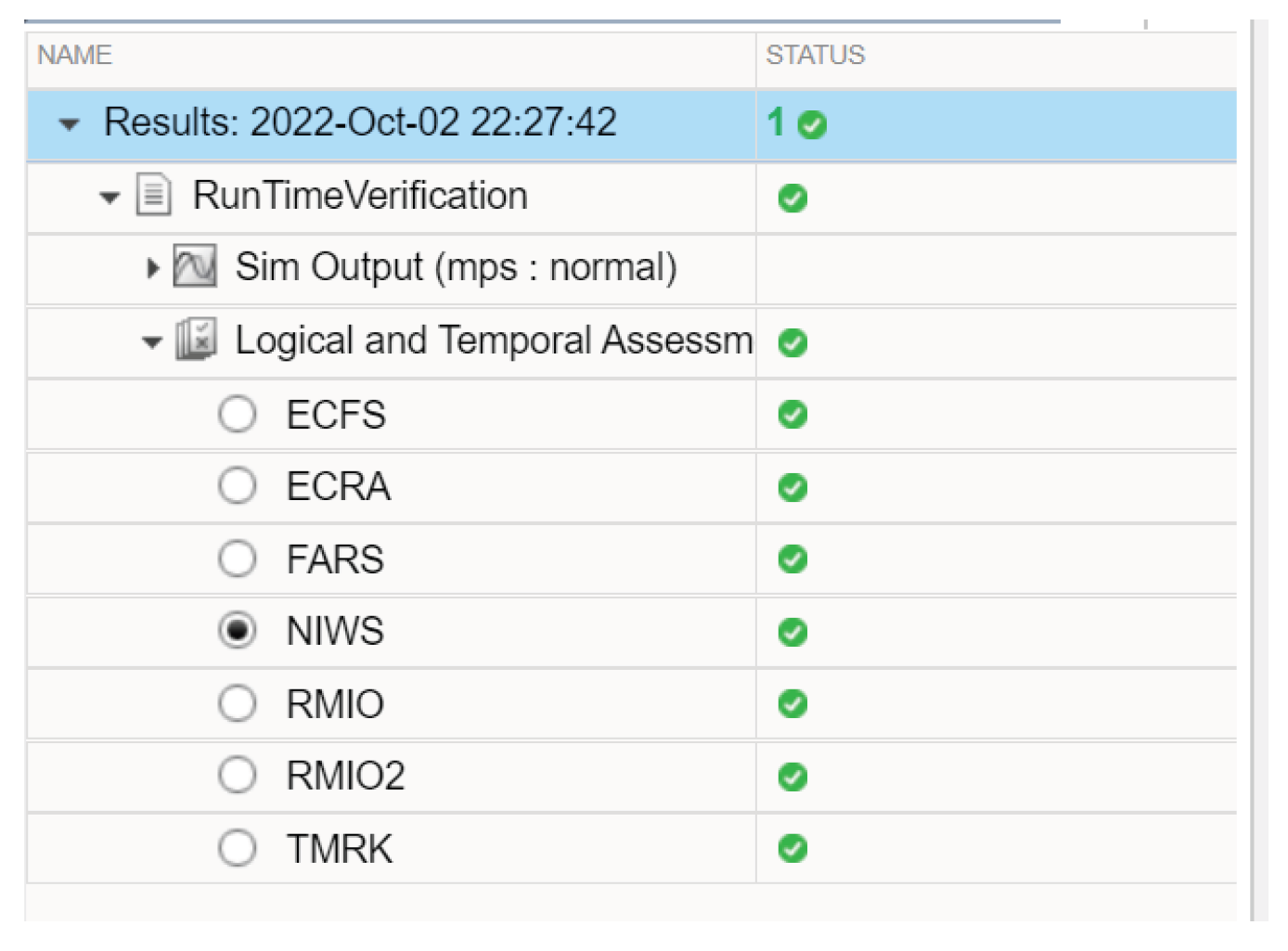
6. Implementation, Simulation and Verification
6.1. Simulation and Result Analysis
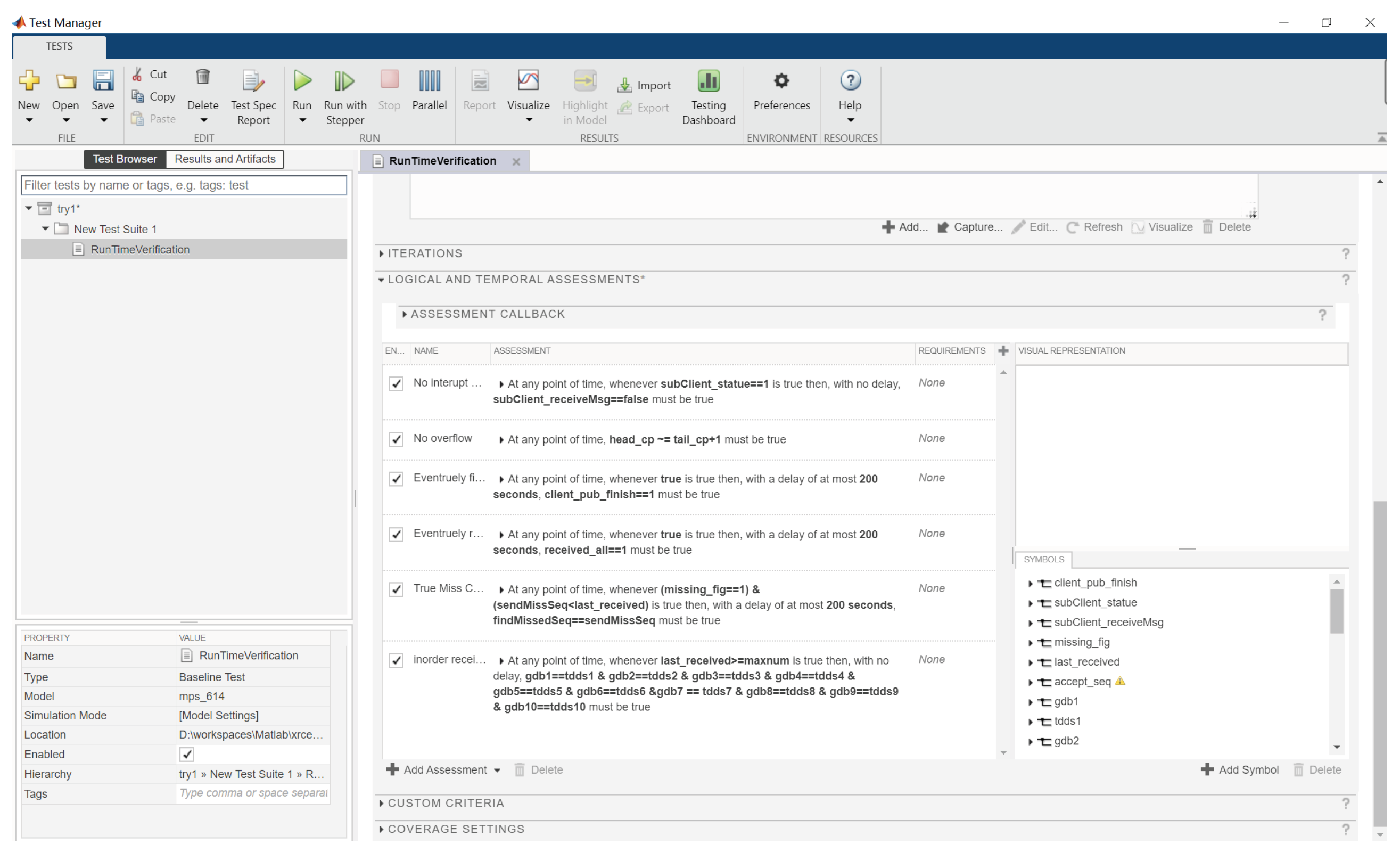
6.2. Runtime Verification and Result Analysis
- ECFS: At any point of time, whenever true is true, with a delay of at most 180 seconds, must be true.
- ECRA: At any point of time, whenever true is true, with a delay of at most 180 seconds, must be true
- NIWS: At any point of time, whenever is true, with a delay between 0 seconds and 50 seconds, must be true
- RMIO: At any point of time, whenever is true, with no delay, must be true
- RMIO2: At any point of time, whenever is true, with no delay, must be true
-
TMRK: At any point of time, whenever is true, with a delay between 0 seconds and 20 seconds,must be true
- FARS: At any point of time, whenever is true, with a delay between 0 seconds and 20 seconds, must be true
7. Conclusion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
References
- Quigley, M.; Conley, K.; Gerkey, B.; et al. ROS: An open-source Robot Operating System//ICRA workshop on open source software. Kobe, 12–17 May 2009, IEEE: Piscataway, 2009; p. 5. [Google Scholar]
- Wang, Z.; Liu, S.; Ji, D.; Yi, W. Improving Real-Time Performance of Micro-ROS with Priority-Driven Chain-Aware Scheduling. Electronics 2024, 13, 1658. [Google Scholar] [CrossRef]
- Micro-ROS - Puts ROS 2 onto Microcontrollers [EB/OL]. 2004. Available online: https://micro.ros.org.
- Lee, H.; Yoon, J.; Jang, M.-S.; Park, K.-J. A robot operating system framework for secure uav communications. Sensors 2021, 21(4), 1369. [Google Scholar] [CrossRef] [PubMed]
- Reke, M.; et al. A Self-Driving Car Architecture in ROS2//2020 International SAUPEC/RobMech/PRASA Conference. Cape Town, Jan 29-31, 2020; IEEE: Piscataway; 2020, pp. 1–6. [Google Scholar]
- Yang, L.G.; Chi, H.F. SLAM Self-Cruise Vehicle Based on ROS Platform/2021 IEEE International Conference on Consumer Electronics and Computer Engineering (ICCECE). Guangzhou, Jan 15-17, 2021; IEEE: Piscataway; 2021, pp. 6–11. [Google Scholar]
- Wang, Z.; Liu, S.; Jiang, X.; Ji, D.; Wang, Y. TIDE: A Timing-Deterministic and Efficient Executor for Micro-ROS. 2023 IEEE International Conferences on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData) and IEEE Congress on Cybermatics (Cybermatics), Danzhou, China, 2023; pp. 487–494. [Google Scholar] [CrossRef]
- Mamani-Saico, A.; Yanyachi, P.R. Implementation and Performance Study of the Micro-ROS/ROS2 Framework to Algorithm Design for Attitude Determination and Control System. IEEE Access 2023, 11, 128451–128460. [Google Scholar] [CrossRef]
- Zahradník, J.; Daňhel, M.; Kubátová, H. Integration of PXROS-HR with Micro-ROS in Robotic Systems. 2024 13th Mediterranean Conference on Embedded Computing (MECO), Budva, Montenegro, 2024; pp. 1–6. [Google Scholar] [CrossRef]
- Dürschmid, T.; Timperley, C.S.; Garlan, D.; et al. Rosinfer: Statically inferring behavioral component models for ros-based robotics systems. In Proceedings of the IEEE/ACM 46th International Conference on Software Engineering, 2024; pp. 1–13. [Google Scholar]
- Terei, N.; Wiemann, R.; Raatz, A. ROS-Based Control of an Industrial Micro-Assembly Robot. Procedia CIRP 2024, 130, 909–914. [Google Scholar] [CrossRef]
- Dehnavi, S.; Goswami, D.; Koedam, M.; et al. Modeling, implementation, and analysis of XRCE-DDS applications in distributed multi-processor real-time embedded systems. In 2021 Design, Automation and Test in Europe Conference and Exhibition (DATE); IEEE; Volume 2021, pp. 1148–1151.
- Park, H.-S.; Lee, S.; Um, D.; Ryu, H.; Park, K.-J. An Analytical Latency Model of the Data Distribution Service in ROS 2. IEEE INFOCOM 2025 - IEEE Conference on Computer Communications, London, United Kingdom; 2025, pp. 1–10. [CrossRef]
- Zanatta, G.; Caiazza, G.; Ferrara, P.; Negrini, L.; White, R. Automating ROS2 Security Policies Extraction through Static Analysis. 2024 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Abu Dhabi, United Arab Emirates; 2024, pp. 3627–3634. [CrossRef]
- Begemann, M.J.; Kallwies, H.; Leucker, M.; Schmitz, M. TeSSLa-ROS-Bridge – Runtime Verification of Robotic Systems. In ICTAC 2023. Lecture Notes in Computer Science; Springer: Cham, 2023; Volume 14446. [Google Scholar] [CrossRef]
- Hu, C.; Dong, W.; Yang, Y.; Shi, H.; Zhou, G. Runtime Verification on Hierarchical Properties of ROS-Based Robot Swarms. IEEE Trans. Reliab. 2020, 69(2), 674–689. [Google Scholar] [CrossRef]
- Li, W.; Ribeiro, P.; Miyazawa, A.; et al. Formal design, verification and implementation of robotic controller software via RoboChart and RoboTool. Auton. Robot 2024, 48, 14. [Google Scholar] [CrossRef]
- Liu, Y.; Guan, Y.; Li, X.; Wang, R.; Zhang, J. Formal Analysis and Verification of DDS in ROS2. 2018 16th ACM/IEEE International Conference on Formal Methods and Models for System Design (MEMOCODE), Beijing, China, 2018; pp. 1–5. [Google Scholar] [CrossRef]
- Carvalho, R.; Cunha, A.; Macedo, N.; Santos, A. Verification of system-wide safety properties of ROS applications. 2020 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), Las Vegas, NV, USA, 2020; pp. 7249–7254. [Google Scholar] [CrossRef]
- Dust, L.; Gu, R.; Mubeen, S.; Ekström, M.; Seceleanu, C. A model-based approach to automation of formal verification of ROS 2 systems. Front. Robot. AI 2025, 12, 1592523. [Google Scholar] [CrossRef] [PubMed]
- Dust, L.; Gu, R.; Seceleanu, C.; et al. Pattern-based verification of ROS 2 applications using UPPAAL. Int. J. Softw. Tools Technol. Transf. 2025, 27, 313–332. [Google Scholar] [CrossRef]
- DDS for eXtremely Resource Constrained Environments. Available online: https://www.omg.org/spec/DDS-XRCE/1.0/PDF.
- Kucuk, K.; Solpan, S. DDS-XRCE Standard Performance Evaluation of Different Communication Scenarios in IoT Technologies. EAI Endorsed Trans. Internet Things 2022, 8, e1. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.



