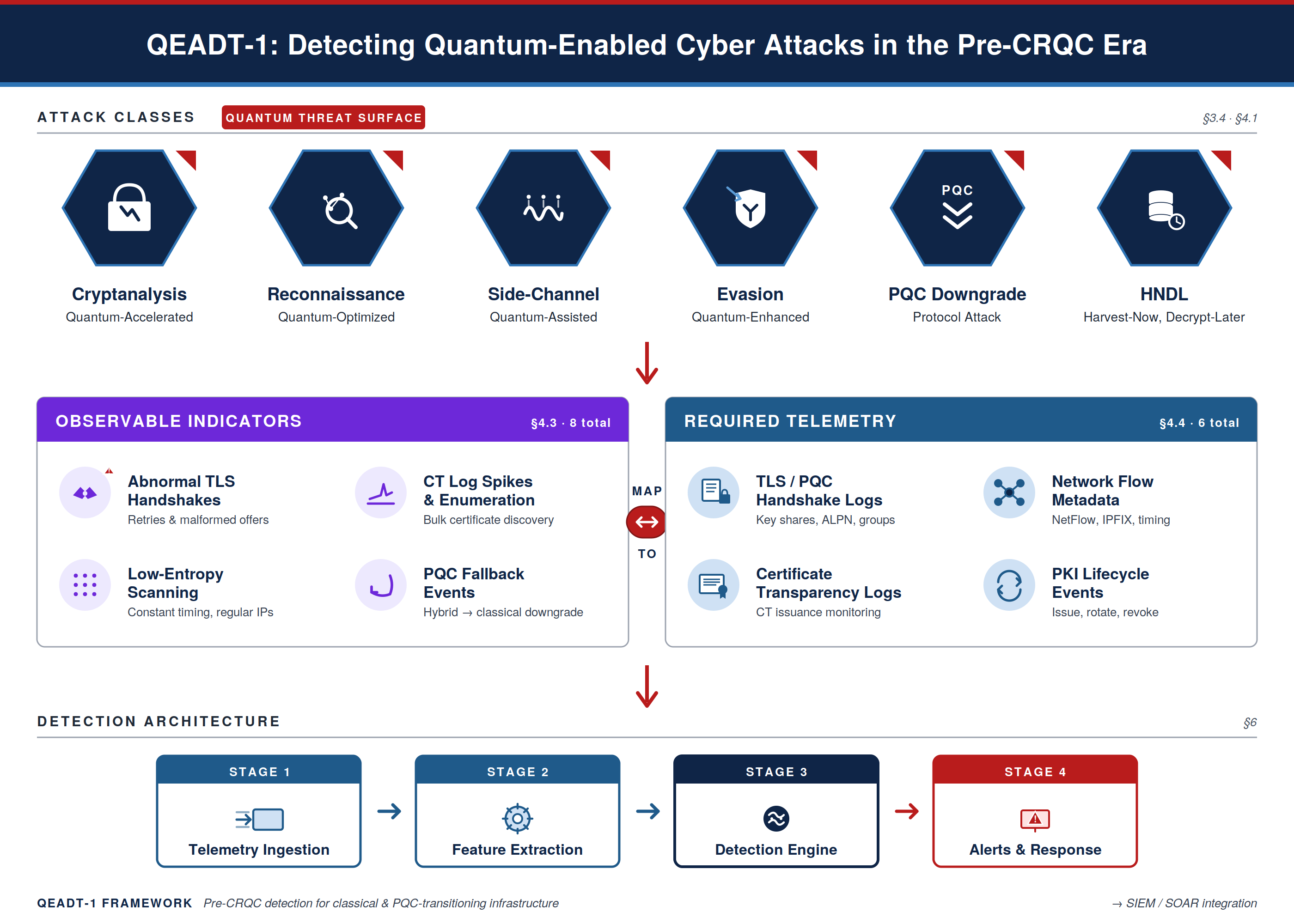
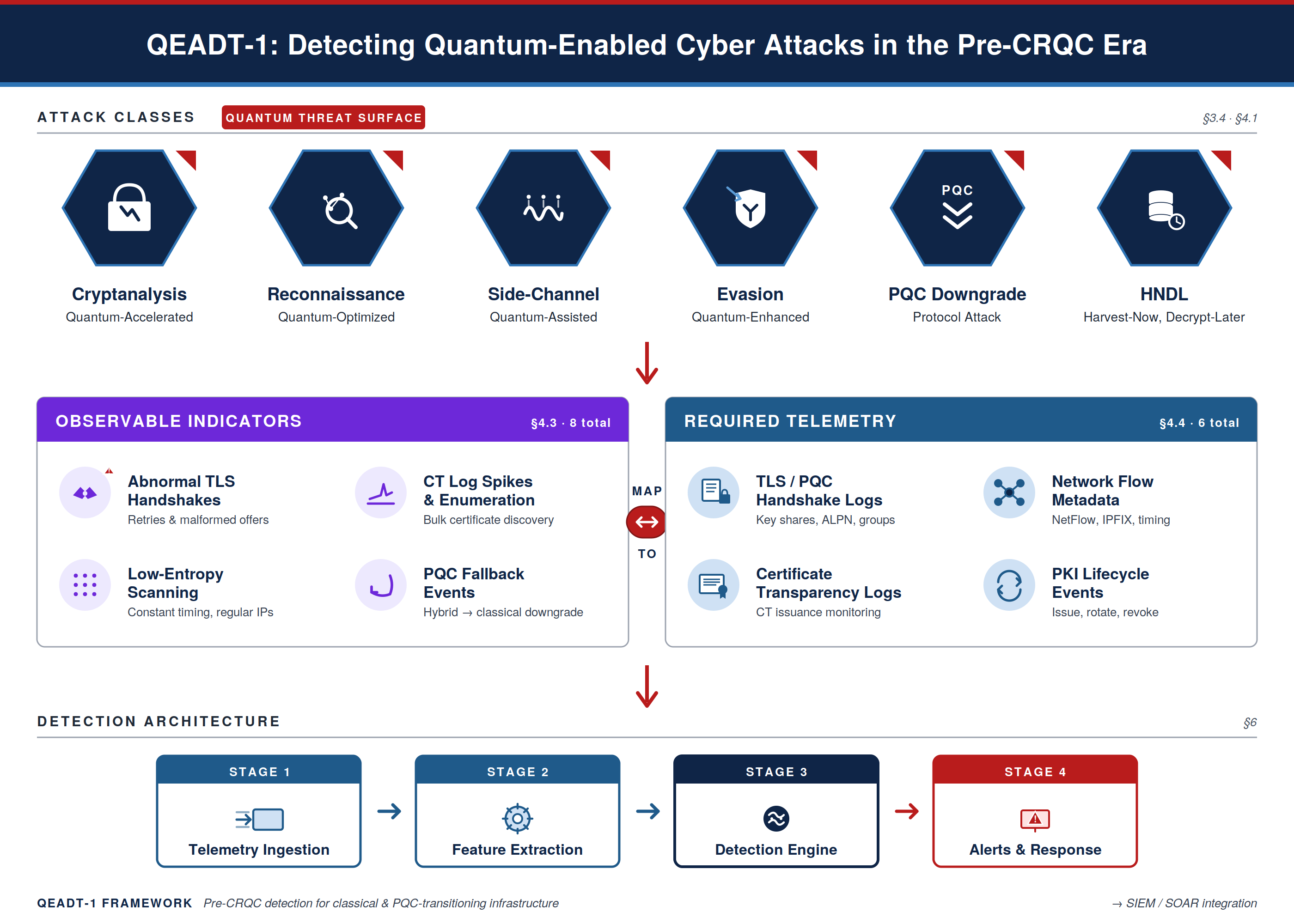
Quantum computing introduces a new class of cyber threats that challenge existing detection paradigms. While significant research has focused on post-quantum cryptography (PQC) and the long-term risk of cryptographic breakage, far less attention has been given to the detection of quantum-enabled attacks during the pre-cryptographically-relevant quantum (pre-CRQC) era. Current intrusion detection systems, network monitors, and cryptographic telemetry tools lack the conceptual models and operational indicators needed to identify adversaries who leverage quantum acceleration, quantum-optimized reconnaissance, or hybrid-mode downgrade strategies. This paper proposes QEADT-1, a systems-level taxonomy for detecting or monitoring quantum-enabled attack patterns against classical and PQC-transitioning infrastructure during the pre-CRQC era, addressing a gap in the literature, which has focused predominantly on prevention through PQC migration and on QKD or quantum-hardware concerns rather than operational detection. We classify six major attack classes, identify their underlying mechanisms, and map each to proposed observable indicators and required telemetry sources. A SOC-oriented detection matrix is introduced to operationalize the taxonomy as a synthesized detection model, followed by a systems architecture for quantum-attack monitoring that is designed to integrate with ongoing PQC migration. This work provides a foundational framework for organizations seeking to detect quantum-enabled threats before cryptographically relevant quantum computers emerge.