Submitted:
14 April 2026
Posted:
15 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Related Works
3. Contributions and Organization
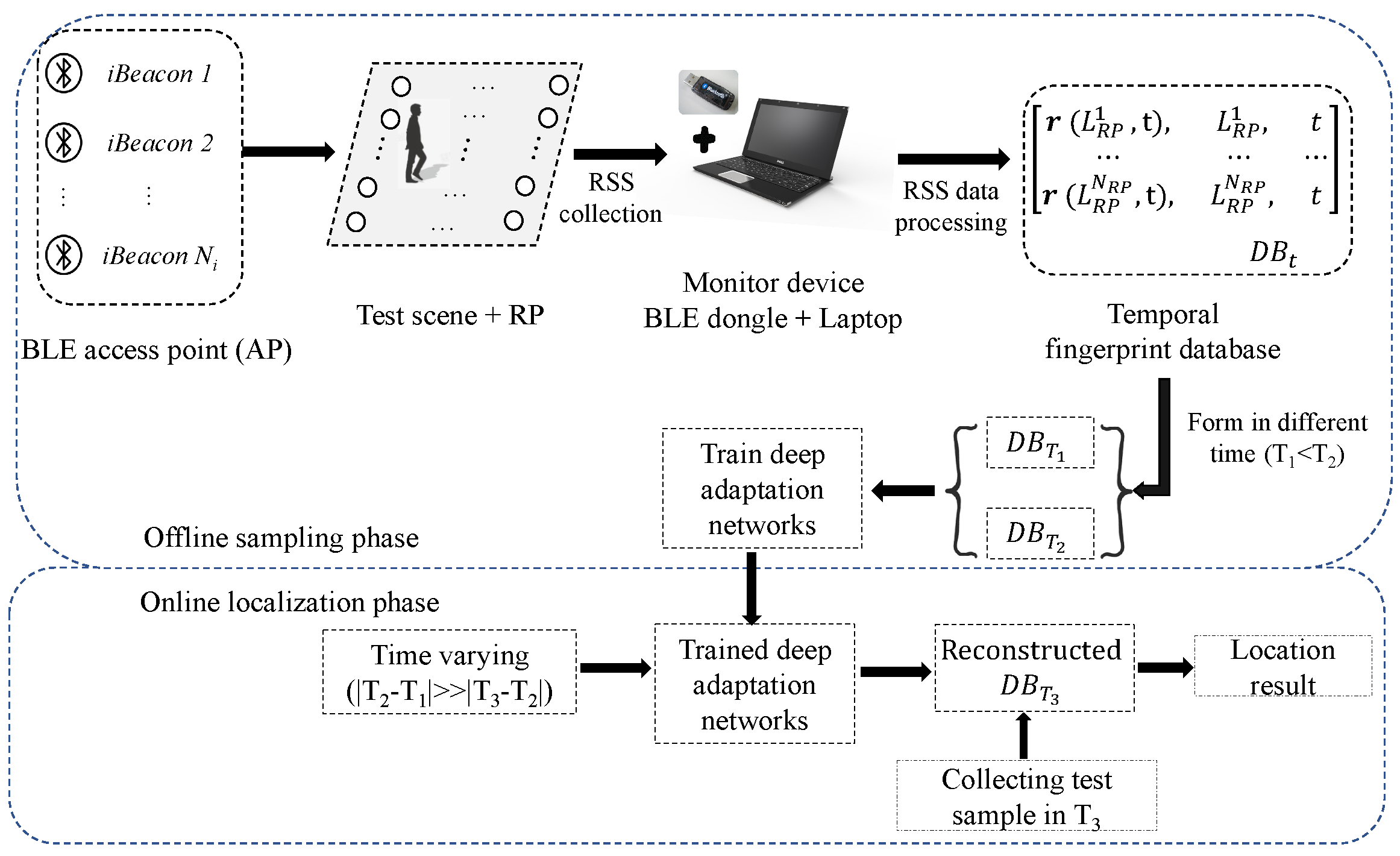
4. System Model
4.1. Topology & BLE Channel Models
4.2. Fingerprint Database
5. Problem Formulation
5.1. MSE Minimization Problem
6. MMD Minimization Problem
7. Proposed MMD Minimization Scheme
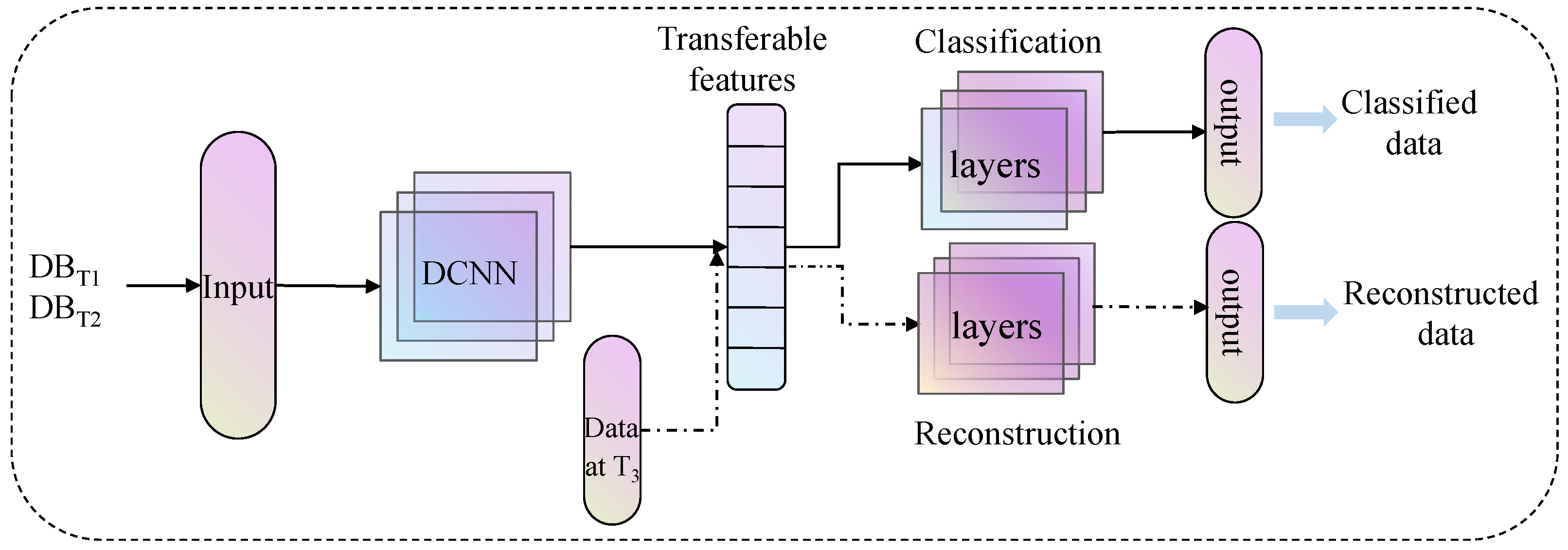
7.1. Deep Domain Adaptation Networks
7.2. Data Collection and Processing
7.3. Training Skills
7.4. Reconstructed Fingerprint
8. Performance Analysis
8.1. CRLB for Location Error
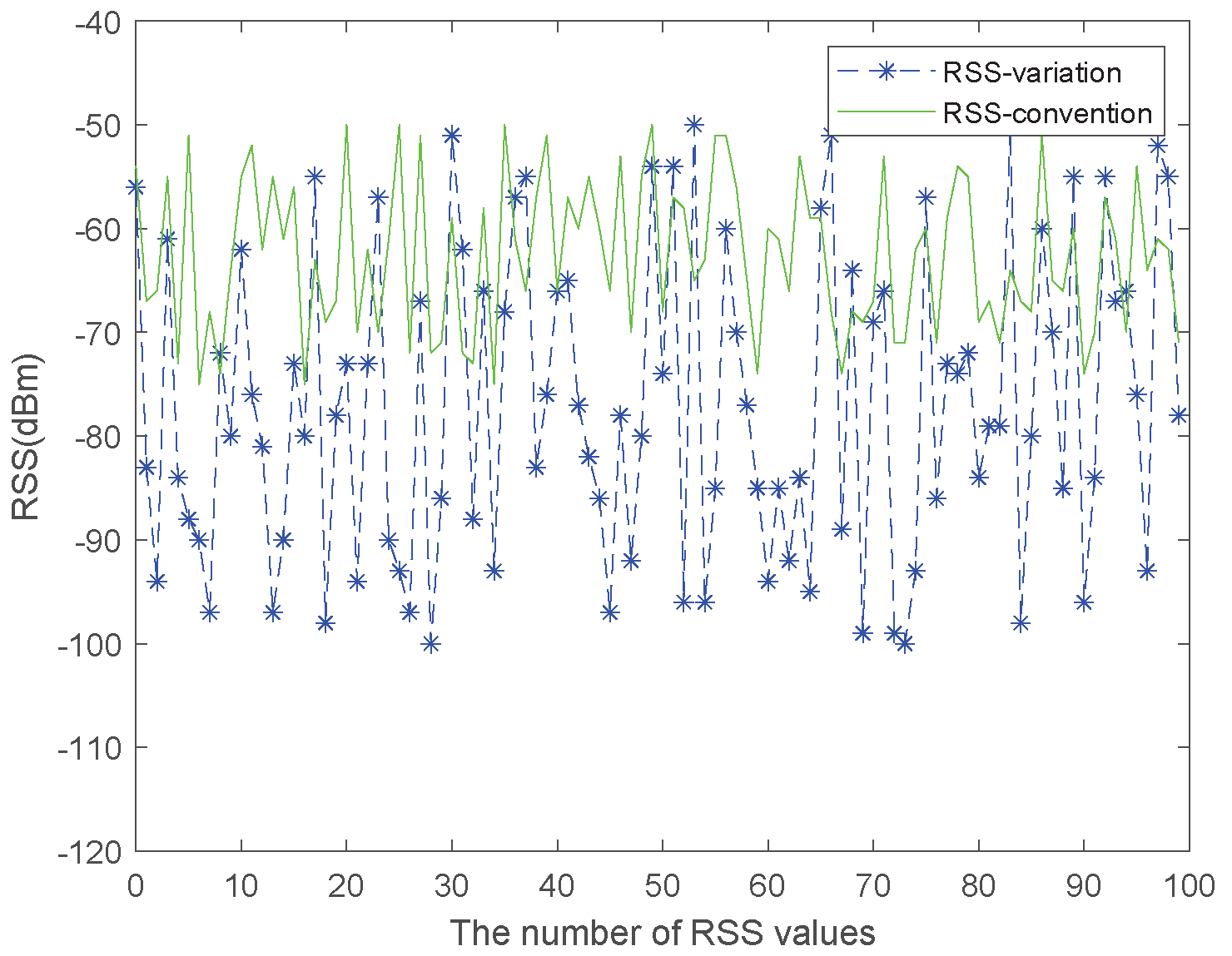
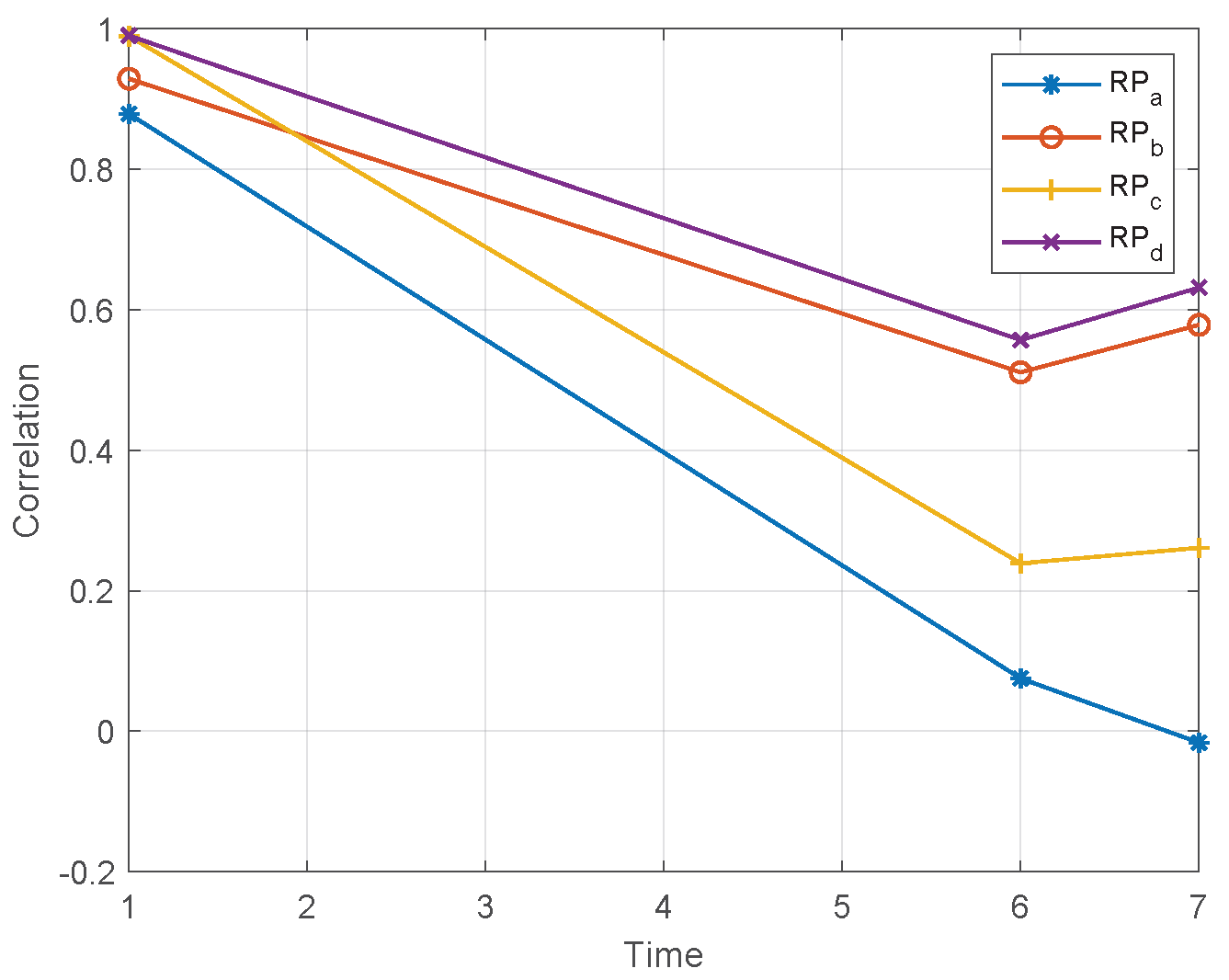
8.2. The Temporal RSS Analysis
9. Results
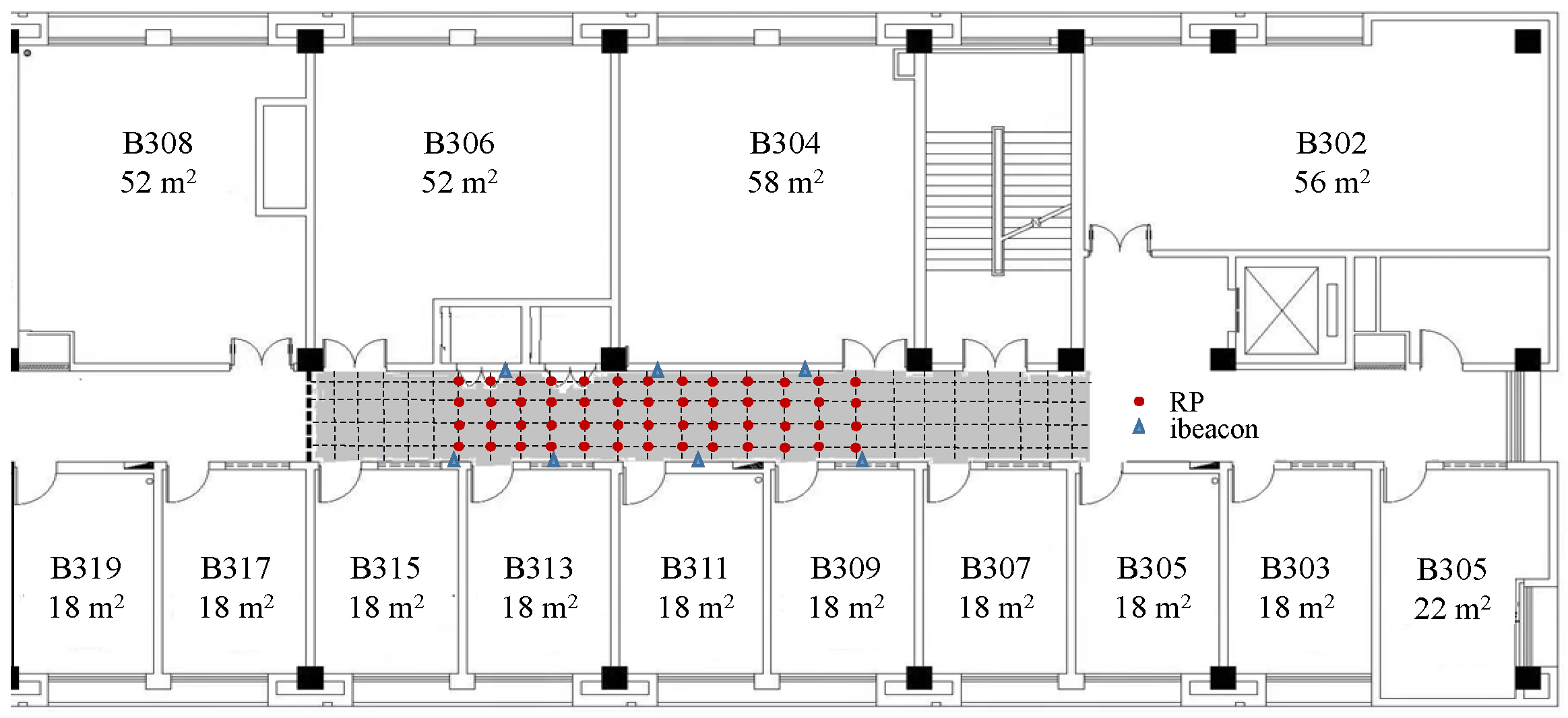
9.1. Test-Bed Description
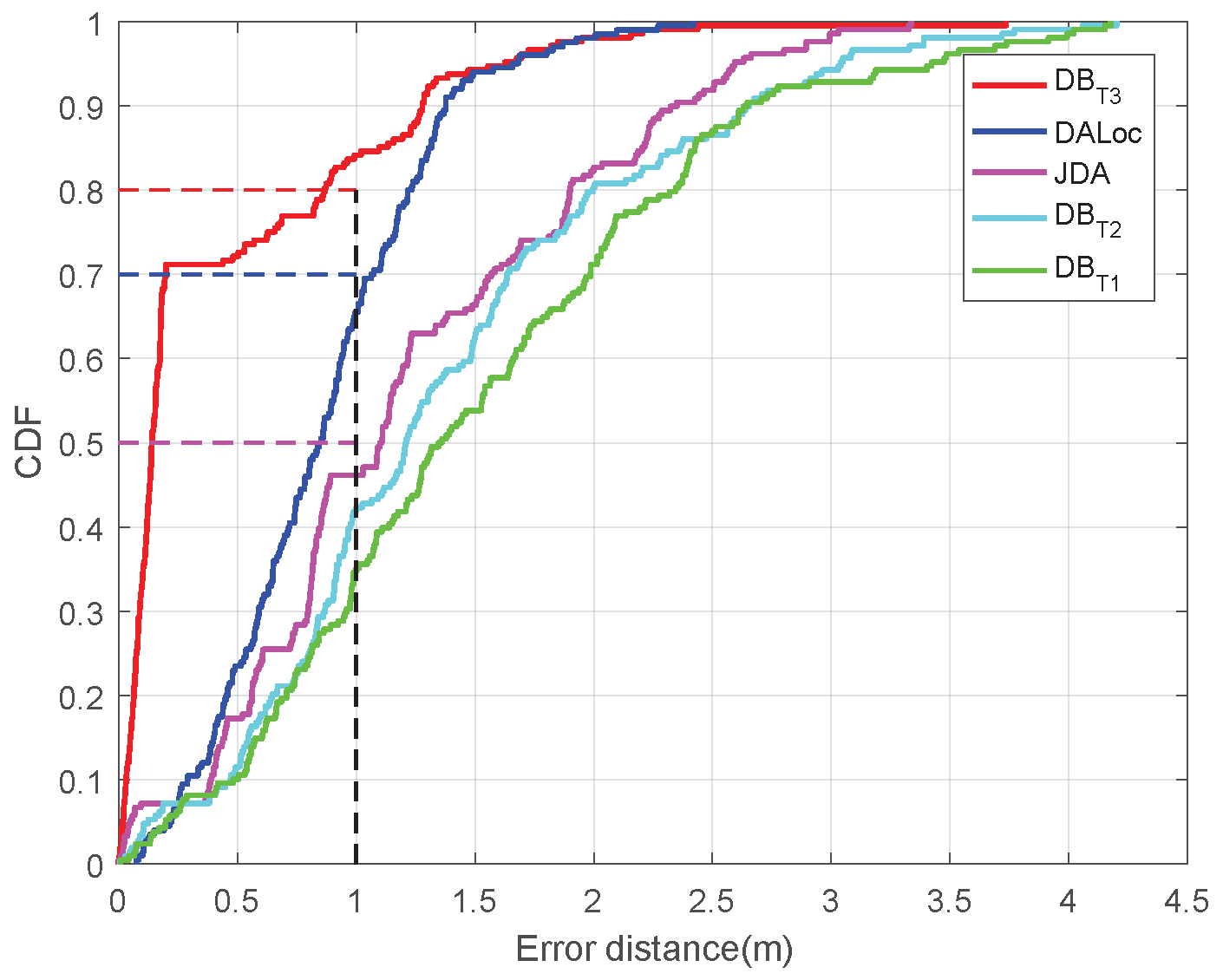
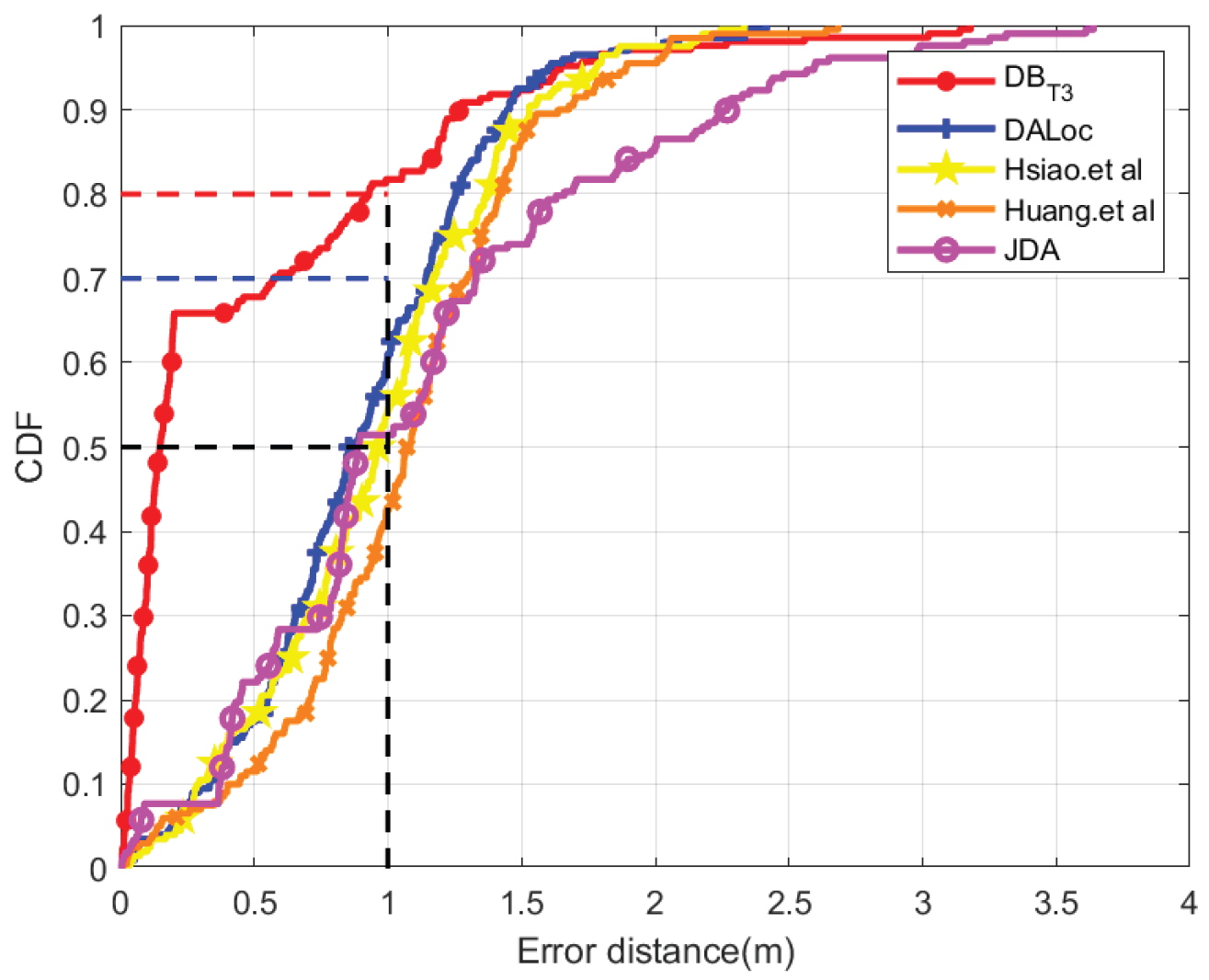
9.2. The Updated Fingerprint Database Evaluation Results
9.2.1. Effect of Reconstructed Fingerprint Database
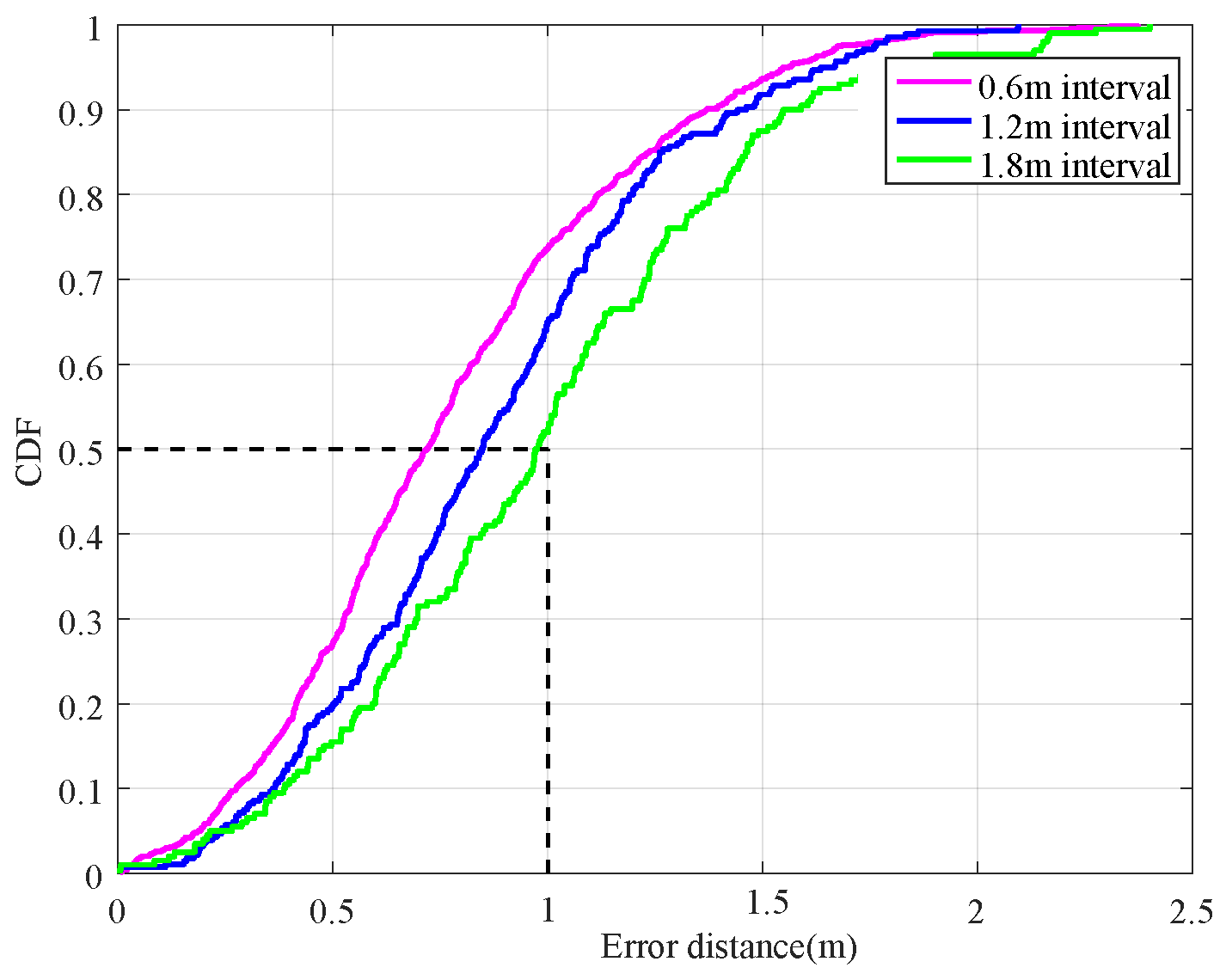
9.2.2. Effect of Different Time Intervals
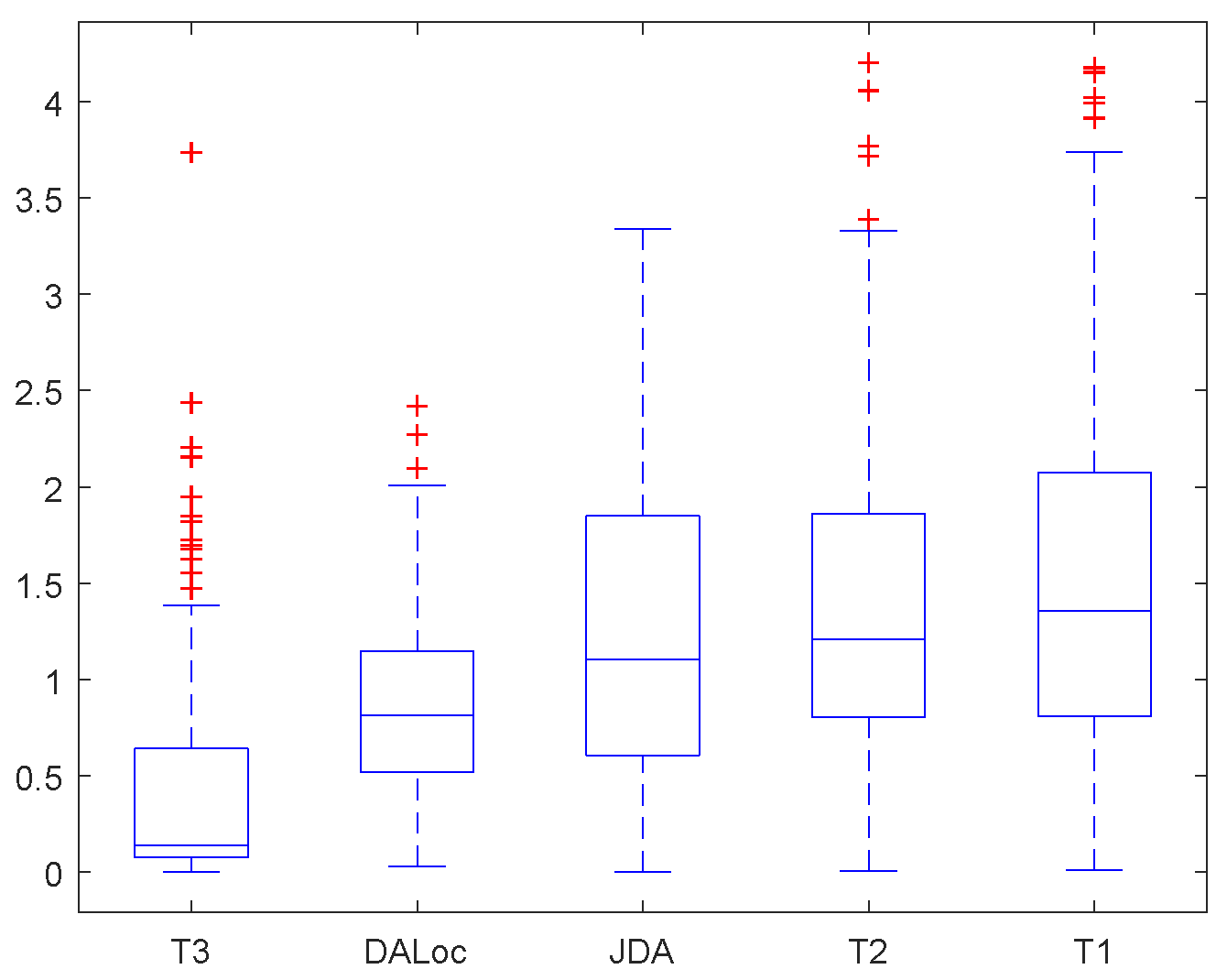
9.2.3. Effect of Outliers
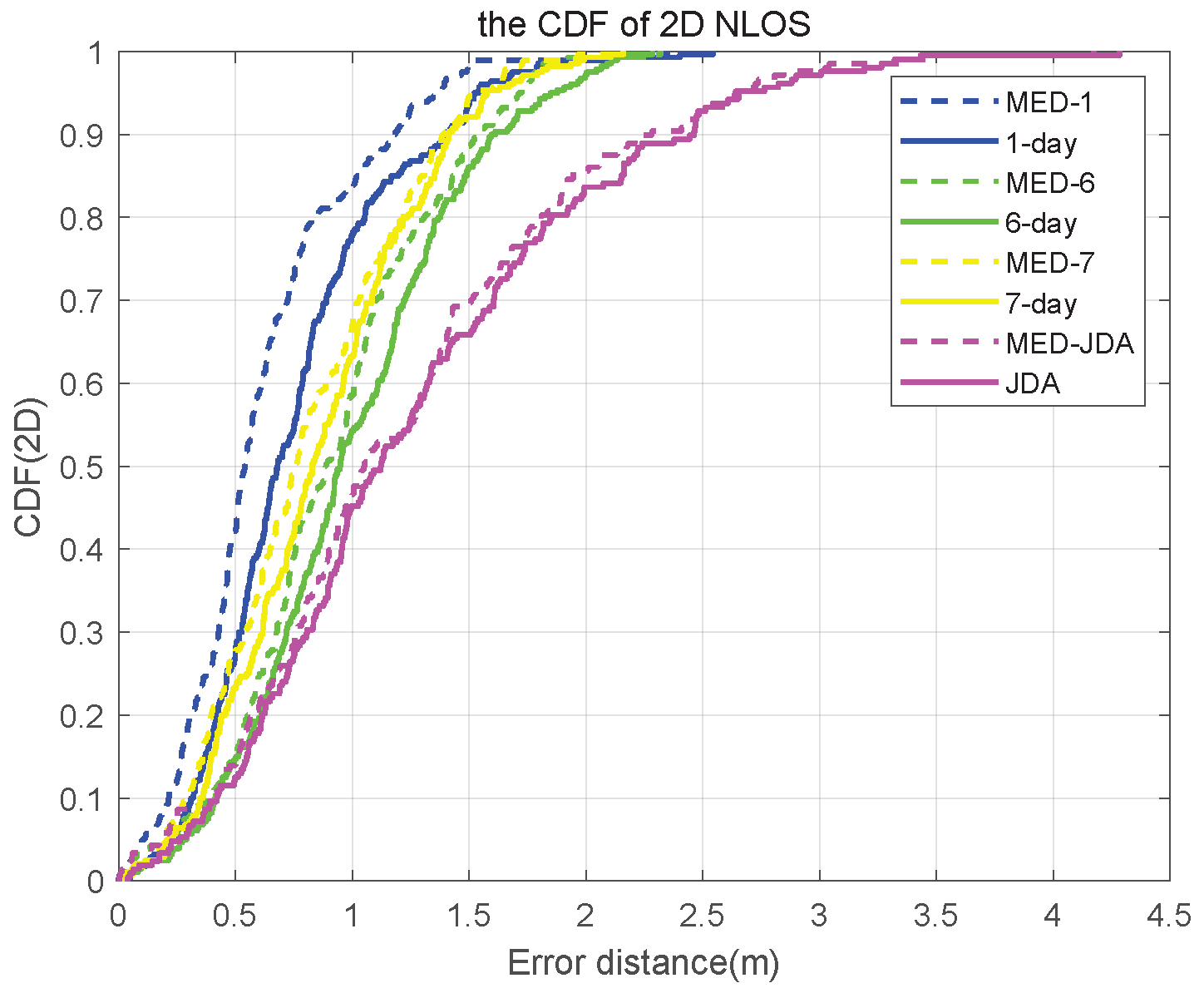
9.2.4. Effect of Eliminating Non-Line of Sight (NLOS) Situation
10. Conclusions
Author Contributions
Funding
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Appendix A. Proof of Lemma 1
Appendix B. Proof of Corollary 1
Appendix C. Derivation of Each Item
Appendix D. Proof of Corollary 2
References
- Zhou, Baoding; et al. Cooperative Indoor Localization Using Mobile Robot Anchors via Factor Graph Optimization. IEEE Internet Things J. 2025. [Google Scholar] [CrossRef]
- Zuo, Yiping; et al. Mobile blockchain-enabled secure and efficient information management for indoor positioning with federated learning. IEEE Trans. Mob. Comput. 2024, 23.12, 12176–12194. [Google Scholar] [CrossRef]
- Fayyad, Jamil; et al. Deep learning sensor fusion for autonomous vehicle perception and localization: A review. Sensors 2020, 20.15, 4220. [Google Scholar] [CrossRef]
- Dauptain, Xavier; et al. Conception of a high-level perception and localization system for autonomous driving. Sensors 2022, 22.24, 9661. [Google Scholar] [CrossRef]
- Ušinskis, Vygantas; et al. Towards autonomous driving: technologies and data for vehicles-to-everything communication. Sensors 2024, 24.11, 3411. [Google Scholar] [CrossRef]
- Ren, Yanbing; et al. DistPreserv: Maintaining user distribution for privacy-preserving location-based services. IEEE Trans. Mob. Comput. 2022, 22.6, 3287–3302. [Google Scholar] [CrossRef]
- Zhu, Lipeng; et al. A tutorial on movable antennas for wireless networks. IEEE Commun. Surv. Tutorials 2025. [Google Scholar] [CrossRef]
- Saunders, Simon R.; Aragón-Zavala, Alejandro A. Antennas and propagation for wireless communication systems; John Wiley & Sons, 2024. [Google Scholar]
- Jiang, Wei; et al. Indoor and outdoor seamless positioning method using UWB enhanced multi-sensor tightly-coupled integration. IEEE Trans. Veh. Technol. 2021, 70.10, 10633–10645. [Google Scholar] [CrossRef]
- Wu, Chong; et al. RF-SLAM: UHF-RFID based simultaneous tags mapping and robot localization algorithm for smart warehouse position service. IEEE Trans. Ind. Inf. 2023, 19.12, 11765–11775. [Google Scholar] [CrossRef]
- Bianchi, V.; Ciampolini, P.; De Munari, I. RSSI-based indoor localization and identification for ZigBee wireless sensor networks in smart homes[J]. IEEE Trans. Instrum. Meas. 2018, 68(2), 566–575. [Google Scholar] [CrossRef]
- Zhang, B.; Sifaou, H.; Li, G. Y. CSI-fingerprinting indoor localization via attention-augmented residual convolutional neural network[J]. IEEE Trans. Wireless Commun. 2023, 22(8), 5583–5597. [Google Scholar] [CrossRef]
- Mackey, Andrew; et al. Improving BLE beacon proximity estimation accuracy through Bayesian filtering. IEEE Internet Things J. 2020, 7.4, 3160–3169. [Google Scholar] [CrossRef]
- Liu, Hui; et al. Survey of wireless indoor positioning techniques and systems. IEEE Trans. Syst. Man Cybern. Part C Appl. Rev. 2007, 37.6, 1067–1080. [Google Scholar] [CrossRef]
- Morar, Anca; et al. A comprehensive survey of indoor localization methods based on computer vision. Sensors 2020, 20.9, 2641. [Google Scholar] [CrossRef]
- Abuhoureyah, Fahd; Wong, Yan Chiew; Isira, Ahmad Sadhiqin Mohd. Trajectory mapping through channel state information by triangulation method and fine-tuning. J. Eng. Appl. Sci. 2024, 71.1, 196. [Google Scholar] [CrossRef]
- Qin, Junping; et al. Indoor trajectory tracking scheme based on Delaunay triangulation and heuristic information in wireless sensor networks. Sensors 2017, 17.6, 1275. [Google Scholar] [CrossRef] [PubMed]
- Li, Ze; et al. TriLoc: Toward accurate indoor localization with assistance of microwave reflections. IEEE Trans. Microwave Theory Tech. 2022, 71.6, 2734–2747. [Google Scholar] [CrossRef]
- Shamaei, Kimia; Kassas, Zaher M. A joint TOA and DOA acquisition and tracking approach for positioning with LTE signals. IEEE Trans. Signal Process. 2021, 69, 2689–2705. [Google Scholar] [CrossRef]
- Hsiao, An-Hung; et al. SALC: Skeleton-Assisted Learning-Based Clustering for Time-Varying Indoor Localization. IEEE Trans. Network Sci. Eng. 2023, 11.1, 439–452. [Google Scholar] [CrossRef]
- Huang, Huakun; et al. Wi-Fi Sensing Based on Deep Supervised Dictionary Learning for Robust Device-Free Localization. IEEE Trans. Veh. Technol. 2025. [Google Scholar] [CrossRef]
- Rafique, Hamaad; et al. A characteristics-based least common multiple algorithm to optimize magnetic field-based indoor localization. IEEE Internet Things J. 2024. [Google Scholar] [CrossRef]
- Farahsari; Shams, Pooyan; et al. A survey on indoor positioning systems for IoT-based applications. IEEE Internet Things J. 2022, 9.10, 7680–7699. [Google Scholar]
- Zhu, Xiaoqiang; et al. Indoor intelligent fingerprint-based localization: Principles, approaches and challenges. IEEE Commun. Surv. Tutorials 2020, 22.4, 2634–2657. [Google Scholar] [CrossRef]
- Zang, Yiming; et al. A novel optical localization method for partial discharge source using ANFIS virtual sensors and simulation fingerprint in GIL. IEEE Trans. Instrum. Meas. 2021, 70, 1–11. [Google Scholar] [CrossRef]
- Wei, Chen; et al. Fingerprint-based localization and channel estimation integration for cell-free massive MIMO IoT systems. IEEE Internet Things J. 2022, 9.24, 25237–25252. [Google Scholar] [CrossRef]
- Li, Qiao; et al. Automatic indoor radio map construction and localization via multipath fingerprint extrapolation. IEEE Trans. Wireless Commun. 2023, 22.9, 5814–5827. [Google Scholar] [CrossRef]
- Liu, Yutong; Kong, Linghe; Chen, Guihai. Data-oriented mobile crowdsensing: A comprehensive survey. IEEE Commun. Surv. Tutorials 2019, 21.3, 2849–2885. [Google Scholar] [CrossRef]
- Gong, Xiaodong; et al. An enhanced indoor positioning solution using dynamic radio fingerprinting spatial context recognition. IEEE Internet Things J. 2022, 10.2, 1297–1309. [Google Scholar] [CrossRef]
- Zhou, Rong; et al. A wi-fi indoor positioning method based on an integration of emdt and wknn. Sensors 2022, 22.14, 5411. [Google Scholar] [CrossRef]
- Tan, Chuanqi; et al. A survey on deep transfer learning. In International conference on artificial neural networks; Springer International Publishing: Cham, 2018. [Google Scholar]
- Pan, Sinno Jialin; et al. Domain adaptation via transfer component analysis. IEEE Trans. Neural Networks 2010, 22.2, 199–210. [Google Scholar] [CrossRef]
- Long, Mingsheng; et al. Transfer feature learning with joint distribution adaptation. In Proceedings of the IEEE international conference on computer vision, 2013. [Google Scholar]
- Long, Mingsheng; et al. Learning transferable features with deep adaptation networks. International conference on machine learning. PMLR 2015. [Google Scholar]
- Redner, Richard A.; Walker, Homer F. Mixture densities, maximum likelihood and the EM algorithm. SIAM review 1984, 26.2, 195–239. [Google Scholar] [CrossRef]
- Xie, Ning; Li, Zhuoyuan; Tan, Haijun. A survey of physical-layer authentication in wireless communications. IEEE Commun. Surv. Tutorials 2020, 23.1, 282–310. [Google Scholar] [CrossRef]
- Zhang, Menglin; et al. Two-stage stochastic optimal operation of integrated electricity and heat system considering reserve of flexible devices and spatial-temporal correlation of wind power. Appl. Energy 2020, 275, 115357. [Google Scholar] [CrossRef]
- Reynolds, Douglas. Gaussian mixture models. In Encyclopedia of biometrics.; Springer: Boston, MA, 2015; pp. 827–832. [Google Scholar]
- Bond, S. R.; Hoeffler, A.; Temple, J. R. W. GMM estimation of empirical growth models[J]. Available at SSRN. 2001, 290522. [Google Scholar]
- Yu, L.; Yang, T.; Chan, A. B. Density-preserving hierarchical EM algorithm: Simplifying Gaussian mixture models for approximate inference. IEEE Trans. Pattern Anal. Mach. Intell. 2018, 41(6), 1323–1337. [Google Scholar] [CrossRef]
- Moon, H. R.; Phillips, P. C. B. GMM estimation of autoregressive roots near unity with panel data[J]. Econometrica 2004, 72(2), 467–522. [Google Scholar] [CrossRef]
- Conley, Timothy G. GMM estimation with cross sectional dependence. Journal of econometrics 1999, 92.1, 1–45. [Google Scholar] [CrossRef]
- Andrews, D. W. K. Consistent moment selection procedures for generalized method of moments estimation[J]. Econometrica 1999, 67(3), 543–563. [Google Scholar] [CrossRef]
- Barni, Mauro; et al. A quasi-Euclidean norm to speed up vector median filtering. IEEE Trans. Image Process. 2000, 9.10, 1704–1709. [Google Scholar] [CrossRef]
- Guo, Gongde; et al. KNN model-based approach in classification. OTM Confederated International Conferences" On the Move to Meaningful Internet Systems", Berlin, Heidelberg, 2003; Springer Berlin Heidelberg. [Google Scholar]
- Krizhevsky, A.; Sutskever, I.; Hinton, G. E. Imagenet classification with deep convolutional neural networks[J]. Advances in neural information processing systems 2012, 25. [Google Scholar] [CrossRef]
- Peleg, S.; Porat, B. The Cramer-Rao lower bound for signals with constant amplitude and polynomial phase. IEEE Trans. Signal Process. 2002, 39(3), 749–752. [Google Scholar] [CrossRef]
- Kay, S. M. Fundamentals of statistical signal processing: estimation theory[M]; Prentice-Hall, lnc., 1993. [Google Scholar]
- Shen, Y.; Win, M. Z. On the accuracy of localization systems using wideband antenna arrays[J]. IEEE Trans. Commun. 2010, 58(1), 270–280. [Google Scholar] [CrossRef]
- Gui, Linqing; et al. A Cramer–Rao lower bound of CSI-based indoor localization. IEEE Trans. Veh. Technol. 2017, 67.3, 2814–2818. [Google Scholar] [CrossRef]
- Patwari, Neal; et al. Locating the nodes: cooperative localization in wireless sensor networks. IEEE Signal Process Mag. 2005, 22.4, 54–69. [Google Scholar] [CrossRef]
- Carrasco, M.; Florens, J. P. On the asymptotic efficiency of GMM[J]. Econom. Theory 2014, 30(2), 372–406. [Google Scholar] [CrossRef]
- Carrasco, M.; Florens, J. P. Generalization of GMM to a continuum of moment conditions[J]. Econom. Theory 2000, 16(6), 797–834. [Google Scholar] [CrossRef]
- Gretton, Arthur; et al. A kernel two-sample test. The journal of machine learning research 2012, 13.1, 723–773. [Google Scholar]
- Borgwardt, Karsten M.; et al. Integrating structured biological data by kernel maximum mean discrepancy. Bioinf. 2006, 22.14, e49–e57. [Google Scholar] [CrossRef]
- Yan, Hongliang; et al. Mind the class weight bias: Weighted maximum mean discrepancy for unsupervised domain adaptation. Proceedings of the IEEE conference on computer vision and pattern recognition 2017. [Google Scholar]
- Jia, Xiaodong; et al. Assessment of data suitability for machine prognosis using maximum mean discrepancy. IEEE Trans. Ind. Electron. 2017, 65.7, 5872–5881. [Google Scholar] [CrossRef]
| 1 | The variations indicate that the range of RSS values under consideration shifts from [-, -] to [-, -]. |
| 2 | Our analysis included examining the wireless signal’s impact from both the signal itself and the temporal correlation [34,35,36] between fingerprint databases. To better represent the stable and instantaneous wireless signal, we used the GMM estimator and analyzed the time domain correlation of RSS-GMM, which can be expressed as an exponential covariance function. We conducted simulations on the positioning results obtained from the constructed fingerprint database and added simulation experiments to verify the impact of long time spans. |
| 3 | In the practical systems, we often apply a time averaging operation to obtain more smooth RSS values, e.g., , and we abuse the notation t here for simplicity. |
| 4 | We analyzed wireless channel propagation, which involves random signal changes and variations in reflective surfaces and reflectors along the path. As a result, the received signal power exhibits both nonlinear and random characteristics. To address this, we approximated the nonlinear wireless signals using the Taylor series. This allowed us to convert the problem into a linear one within the range of and . |
| 5 | The KNN algorithm will compare the measured results with the database to determine K nearest RPs and calculate the location thereby to obtain the estimated location , which is shown to be quite effective for practical systems[44]. |
| 6 | The function is continuous and differentiable on [52]. |
| Algorithm | Location error(m) |
|---|---|
| 0.8041 | |
| 0.9251 | |
| 0.9762 | |
| 1.1175 | |
| 0.9864 | |
| 1.1403 | |
| 1.6490 | |
| 1.6963 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




