Submitted:
01 April 2026
Posted:
03 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Background and Motivation
1.2. Security Challenges in MQTT-Based IoT Systems
1.3. Backpressure and Flow-Control Limitations
- They do not fully regulate QoS 0 traffic, which lacks acknowledgment-based control.
- They operate at a protocol level without awareness of application context or security state.
- They are insufficient under burst workloads, wildcard fan-out, or malicious traffic patterns.
1.4. Wildcard Subscriptions: Scalability vs. Security Risk
- Performance Impact: Wildcards increase subscription matching complexity, resulting in higher CPU utilization and routing overhead at the broker [11].
- Traffic Amplification: A single wildcard subscription can trigger message delivery to a large number of topics, increasing system load.
- Security Risks: Broad subscriptions (e.g., “#”) may lead to unauthorized data access if access control policies are weak or misconfigured.
1.5. Interdependence of Security, Wildcards, and Backpressure
- Security mechanisms increase processing overhead → amplify backpressure.
- Wildcard subscriptions increase message fan-out → increase load and routing complexity.
- Backpressure conditions affect reliability → potentially weaken security monitoring and control.
1.6. Research Gap and Contribution of This Review
- Address security without considering performance impact. or
- Propose flow-control mechanisms without incorporating security context. or
- Analyze wildcards without evaluating system-wide congestion effects.
- A comprehensive synthesis of MQTT security, flow control, and wildcard-related research.
- A critical analysis of their interactions and combined impact on system performance.
- Identification of limitations in current approaches.
- A set of future research directions for building secure, scalable, and adaptive MQTT systems.
1.7. Organization of the Review Article
- Section 2: Background and Fundamentals.
- Section 3: Security Mechanisms in MQTT Systems.
- Section 4: Backpressure and Flow-Control Mechanisms.
- Section 5: Wildcard Subscription Behavior and Optimization.
- Section 6: Integrated Analysis and Literature Gap Discussion.
- Section 7: Future Research Directions.
- Section 8: Conclusions.
2. Background and Fundamentals of MQTT Systems
2.1. Overview of MQTT Architecture
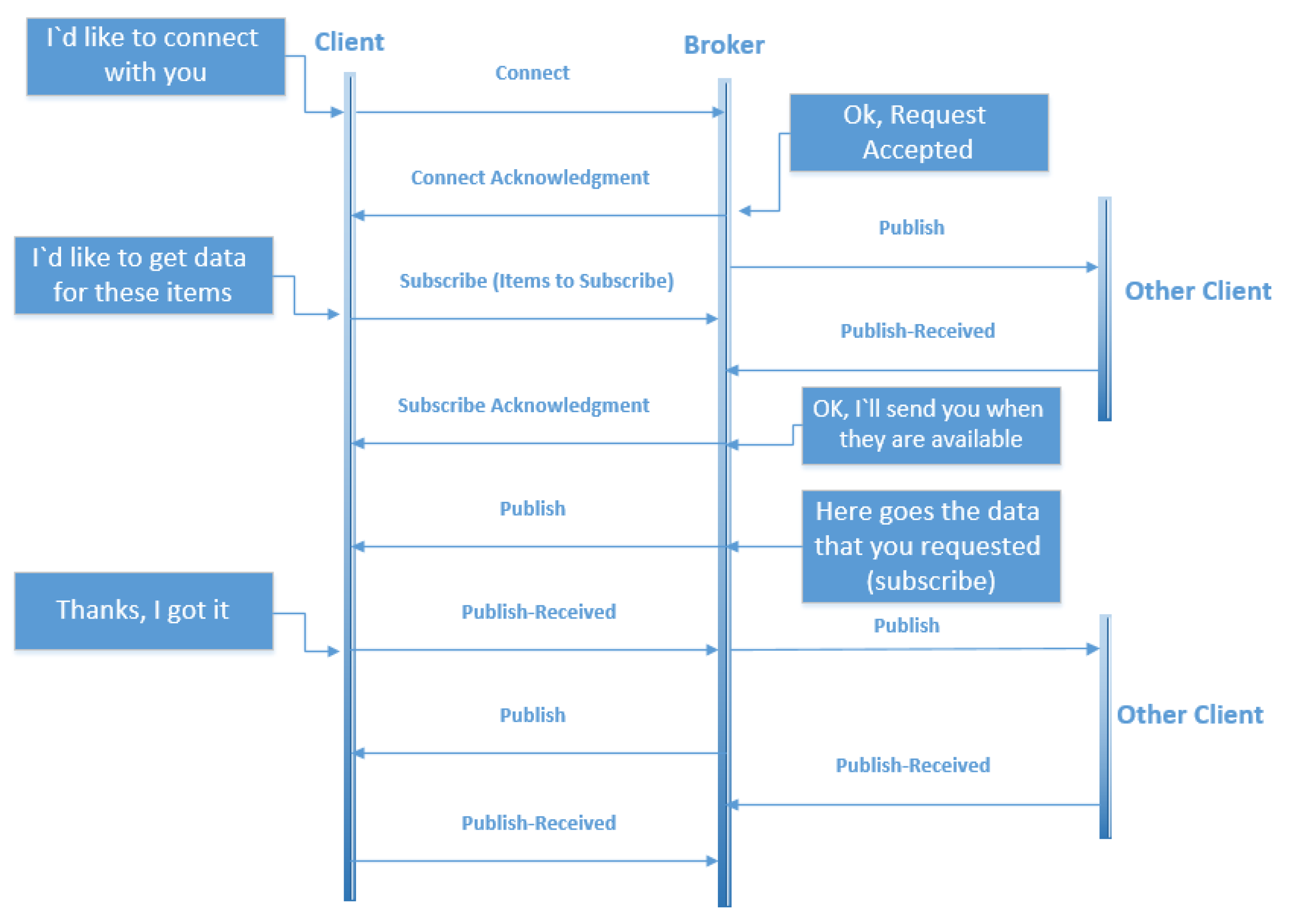
2.1.1. Publish/Subscribe Model
- Space decoupling: publishers and subscribers do not know each other.
- Time decoupling: communication is asynchronous.
- Synchronization decoupling: no blocking between sender and receiver.
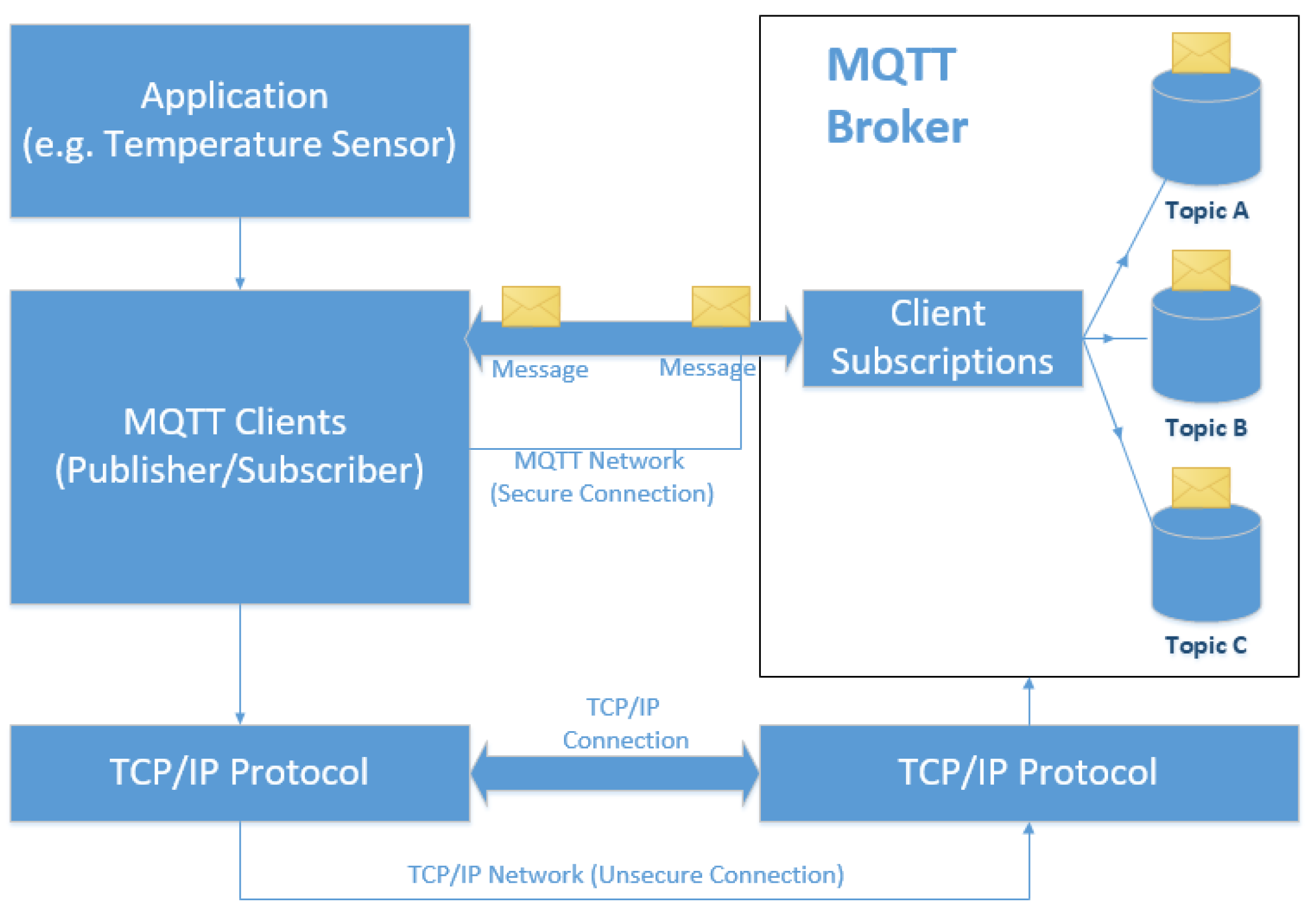
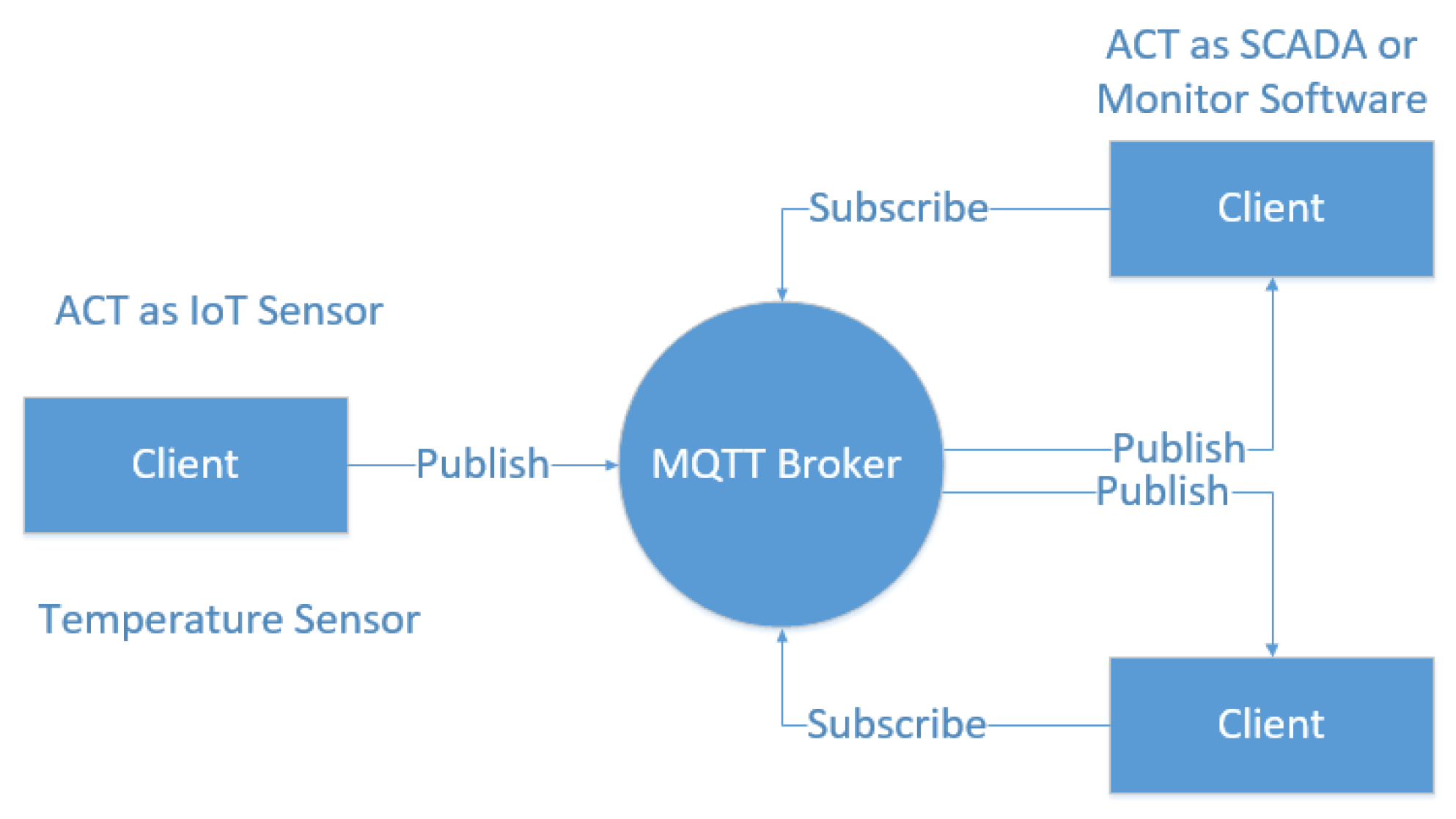
2.1.2. MQTT System Architecture
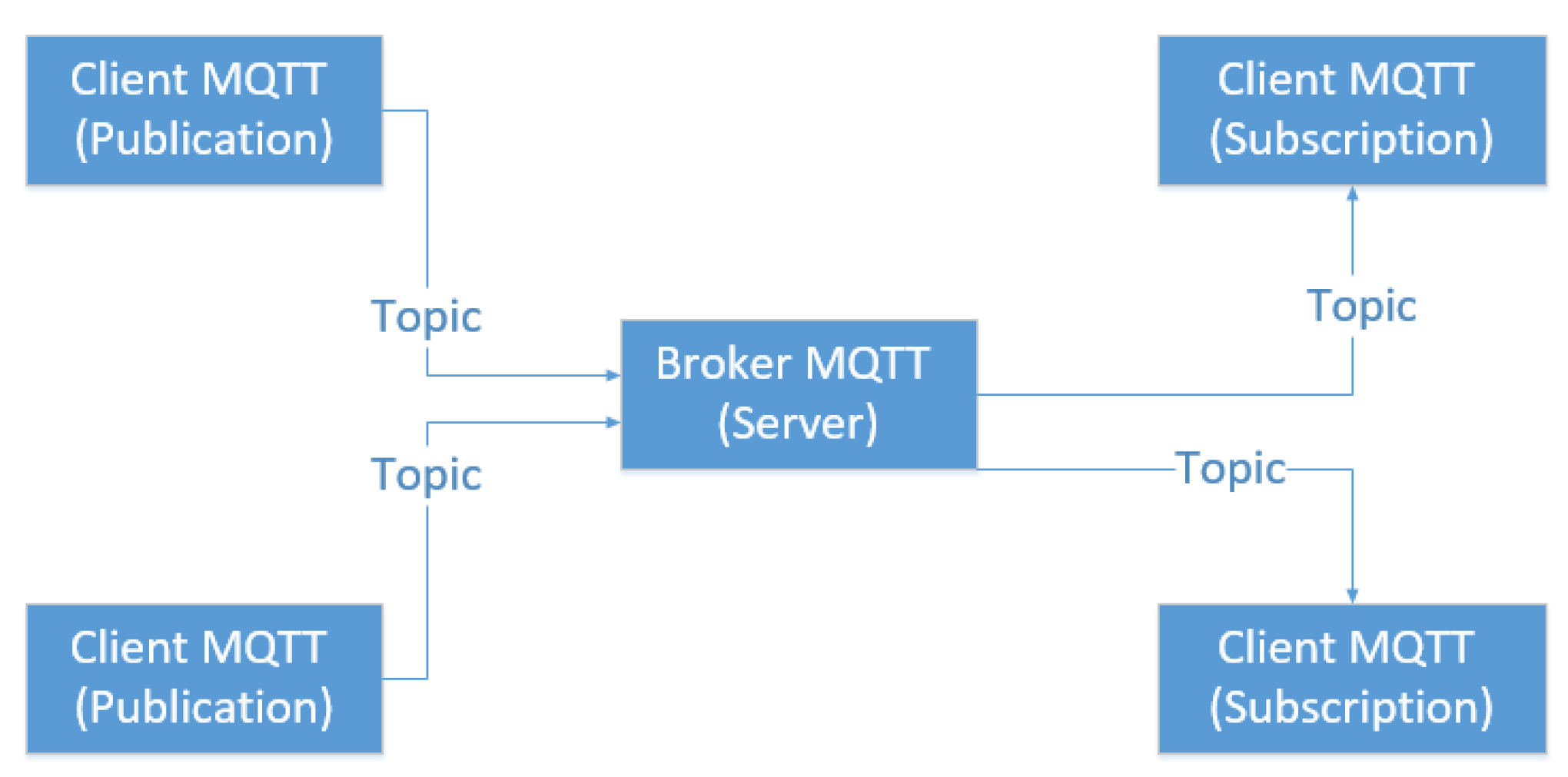
- Publisher: Generates and sends messages to topics.
- Broker: Central server responsible for message routing, filtering, and delivery.
- Subscriber: Receives messages from topics of interest.
- Topic-based filtering.
- Session management.
- Message queuing and delivery.
- Security enforcement (authentication and authorization).
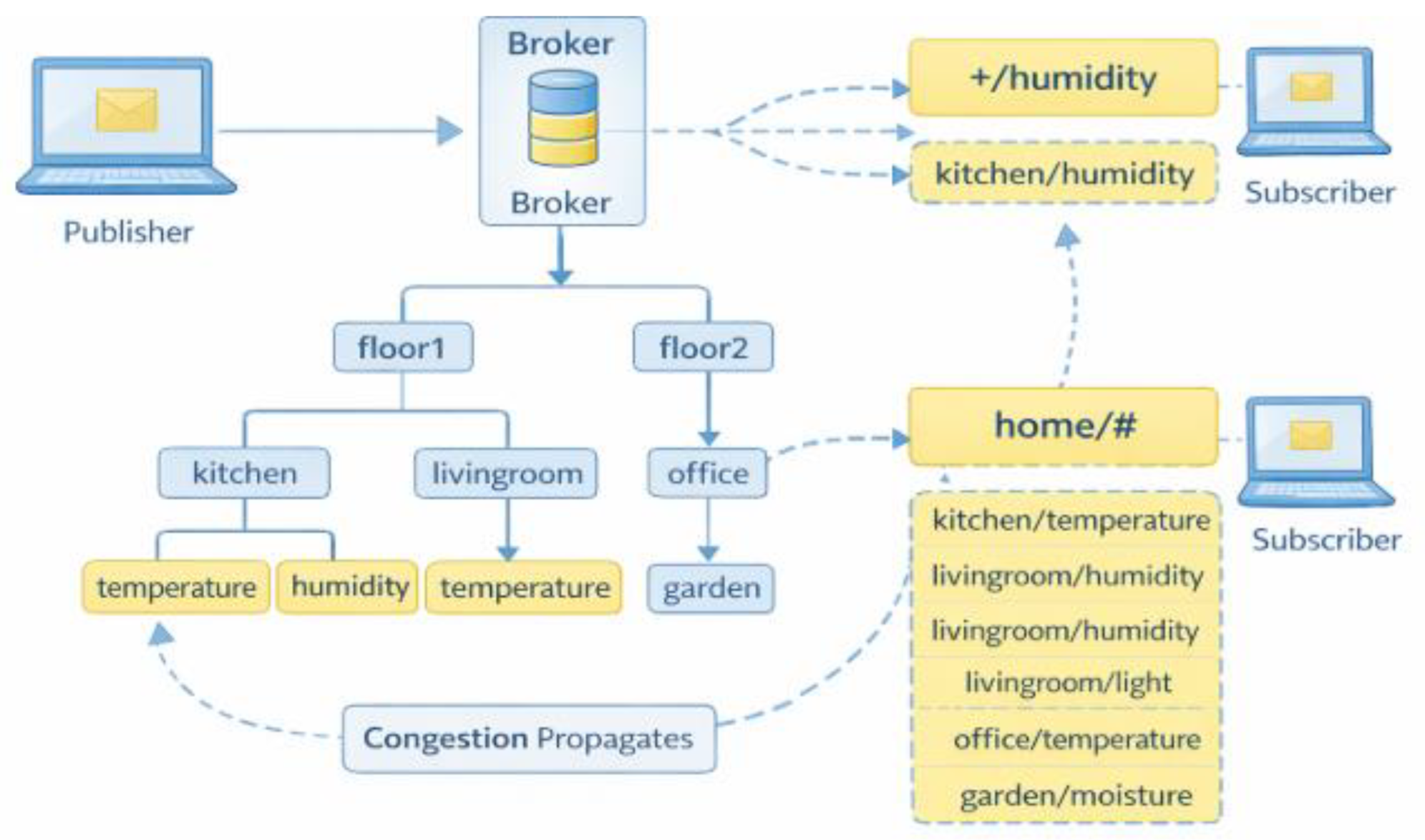
2.2. Topic Hierarchy and Wildcards
- + → single-level wildcard.
- # → multi-level wildcard.
- home/+/temperature → matches one level.
- home/# → matches entire hierarchy.
- Routing complexity.
- Broker CPU load.
- Security exposure.
2.3. Quality of Service (QoS) Levels
2.3.1. QoS Levels Description
| QoS Level | Name | Guarantee | Mechanism | Overhead |
|---|---|---|---|---|
| QoS 0 | At most once | No guarantee | Fire-and-forget | Low |
| QoS 1 | At least once | Possible duplicates | ACK (PUBACK) | Medium |
| QoS 2 | Exactly once | Guaranteed delivery | 4-step handshake | High |
2.3.2. QoS Handshake Mechanisms
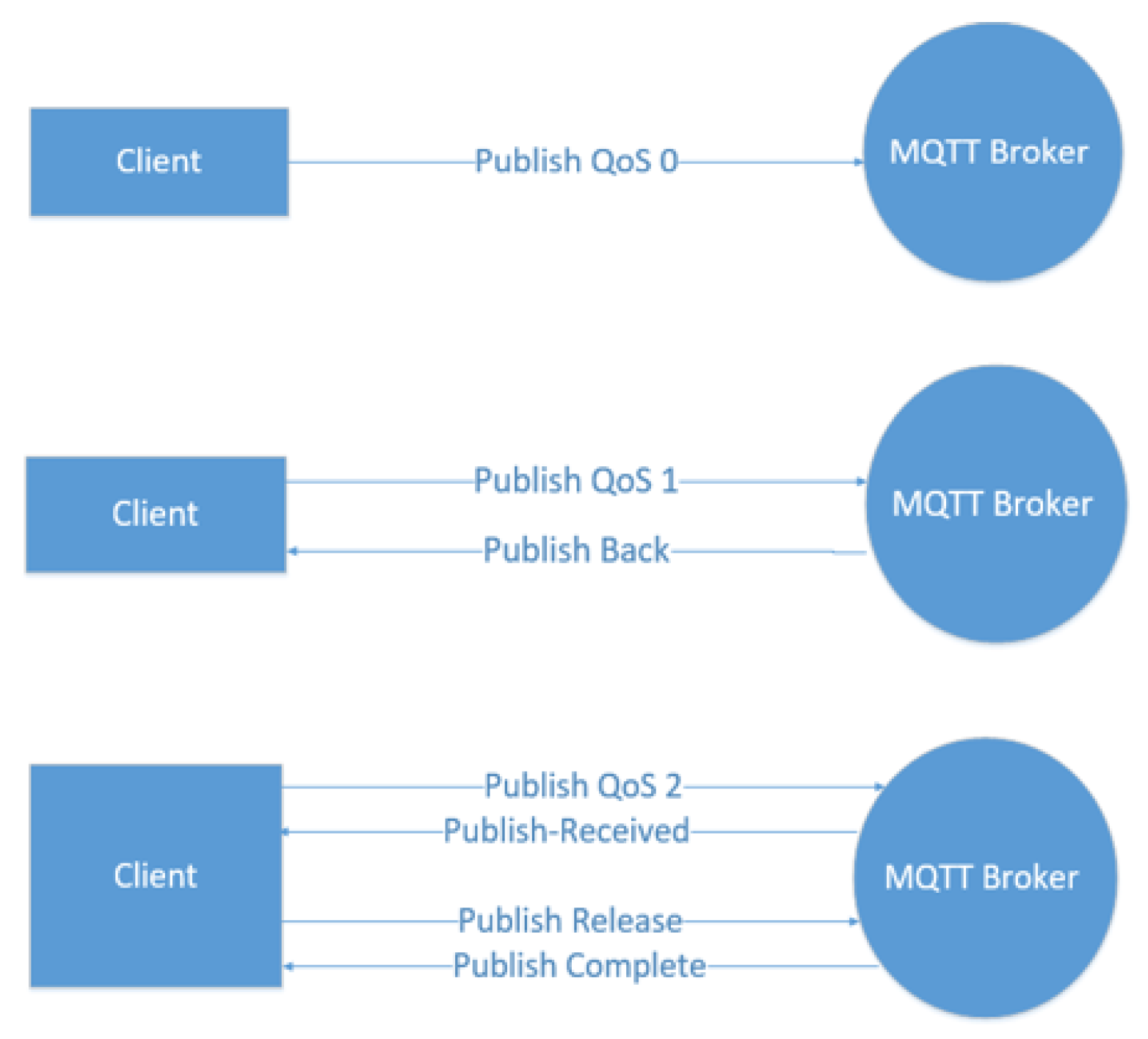
2.3.3. QoS and Performance Trade-Off
- Higher QoS → better reliability but higher latency and overhead.
- Lower QoS → faster delivery but less reliability.
2.4. Backpressure in MQTT Systems
- λin: incoming message rate.
- μservice: processing/service rate.
- Queue length increases.
- Latency grows.
- Message loss may occur.
2.4.1. Queue Growth Model
- (t): queue size at time t.
- (t): arrival rate.
- (t): service rate.
2.4.2. Impact of Backpressure
- Increased latency.
- Message drops.
- Broker instability.
- Reduced QoS effectiveness.
2.5. MQTT v5 Flow-Control Mechanisms
2.5.1. Receive Maximum
- Ninfligℎt: number of in-flight messages.
- Rmax: Receive Maximum.
2.5.2. Send Quota Mechanism
2.5.3. Flow-Control Limitations
- QoS 0 Traffic Not Controlled: No ACK → no feedback mechanism.
- No Security Awareness: Flow control does not consider authentication or trust level.
- Static Thresholds: Not adaptive to dynamic workloads.
- Wildcard Blindness: Does not account for fan-out amplification.
2.6. Interaction Between QoS, Flow Control, and Security
- QoS → increases reliability but adds overhead.
- Security → increases processing cost.
- Flow control → regulates traffic but lacks context awareness.
- Loadsecurity: TLS, authentication, ACL checks.
- LoadQoS: retransmissions, acknowledgments.
2.7. Summary of Background and Key Insights
- MQTT’s lightweight design enables scalability but introduces system-level vulnerabilities under load.
- QoS mechanisms improve reliability but contribute to traffic amplification and latency.
- MQTT v5 flow control provides partial solutions but lacks adaptability and context awareness.
- Wildcard subscriptions significantly increase routing complexity and security risks.
- Backpressure is a system-level phenomenon influenced by multiple interacting factors.
3. Security Mechanisms in MQTT Systems
3.1. Overview of Security Requirements in MQTT-Based IoT
3.2. Authentication Mechanisms in MQTT
3.2.1. Username and Password Authentication
- Lightweight and easy to implement.
- Suitable for constrained devices.
- Vulnerable to brute-force and replay attacks if not encrypted.
- Requires secure transport (TLS).
3.2.2. Certificate-Based Authentication (TLS/X.509)
- Strong identity verification.
- Protection against eavesdropping and MitM attacks.
- High computational overhead.
- Increased latency due to handshake.
3.2.3. Token-Based Authentication (OAuth, JWT)
- Scalable and flexible.
- Suitable for cloud-integrated IoT.
- Token validation overhead.
- Dependency on external identity providers.
3.2.4. Authentication Overhead Model
- Ccrypto: encryption/decryption cost.
- Cℎandsℎake: connection setup cost.
- Cverification: credential validation.
3.3. Authorization and Access Control
3.3.1. Access Control Lists (ACLs)
- Fine-grained control.
- Easy integration with brokers.
- High evaluation overhead.
- Complexity in large-scale systems.
3.3.2. Role-Based Access Control (RBAC)
- Scalable for large systems.
- Easier policy management.
- Less flexible than attribute-based models.
3.3.3. Attribute-Based Access Control (ABAC)
- Highly flexible and dynamic.
- Context-aware decisions.
- High computational complexity.
- Difficult to implement in constrained environments.
- Nrules: number of ACL rules.
- Cmatcℎ: complexity of topic matching.
3.4. Encryption and Data Protection
3.4.1. Transport-Level Security (TLS)
- Confidentiality.
- Integrity.
- Authentication.
- Increased packet size.
- CPU overhead.
- Latency increase.
3.4.2. Payload Encryption
- Protects data beyond broker.
- Enhances privacy.
- Additional processing overhead.
- Key management complexity.
3.5. Security Threats in MQTT Systems
3.5.1. Unauthorized Access
- Publish malicious data.
- Subscribe to sensitive topics.
3.5.2. Wildcard Exploitation
- Expose large data sets.
- Enable data exfiltration.
3.5.3. Denial-of-Service (DoS) Attacks
- Flood broker with messages.
- Exploit QoS retransmissions.
- Trigger backpressure.
3.5.4. Slow Subscriber Attack
- Queue buildup.
- Increased latency.
- System instability.
3.6. Security vs Performance Trade-Off
3.6.1. Combined System Load Model
- Lsecurity = Lautℎ + Lautℎz + Lencryption
- Lrouting: wildcard matching cost
3.6.2. Comparative Analysis
| Mechanism | Security Strength | Performance Impact | Scalability |
|---|---|---|---|
| Username/Password | Low–Medium | Low | High |
| TLS Certificates | High | High | Medium |
| OAuth/JWT | High | Medium | High |
| ACL | Medium | Medium | Medium |
| ABAC | High | High | Low |
3.7. Key Insights and Limitations of Existing Approaches
3.8. Summary
4. Backpressure and Flow-Control Mechanisms in MQTT-Based IoT Systems
4.1. Overview of Backpressure in MQTT Systems
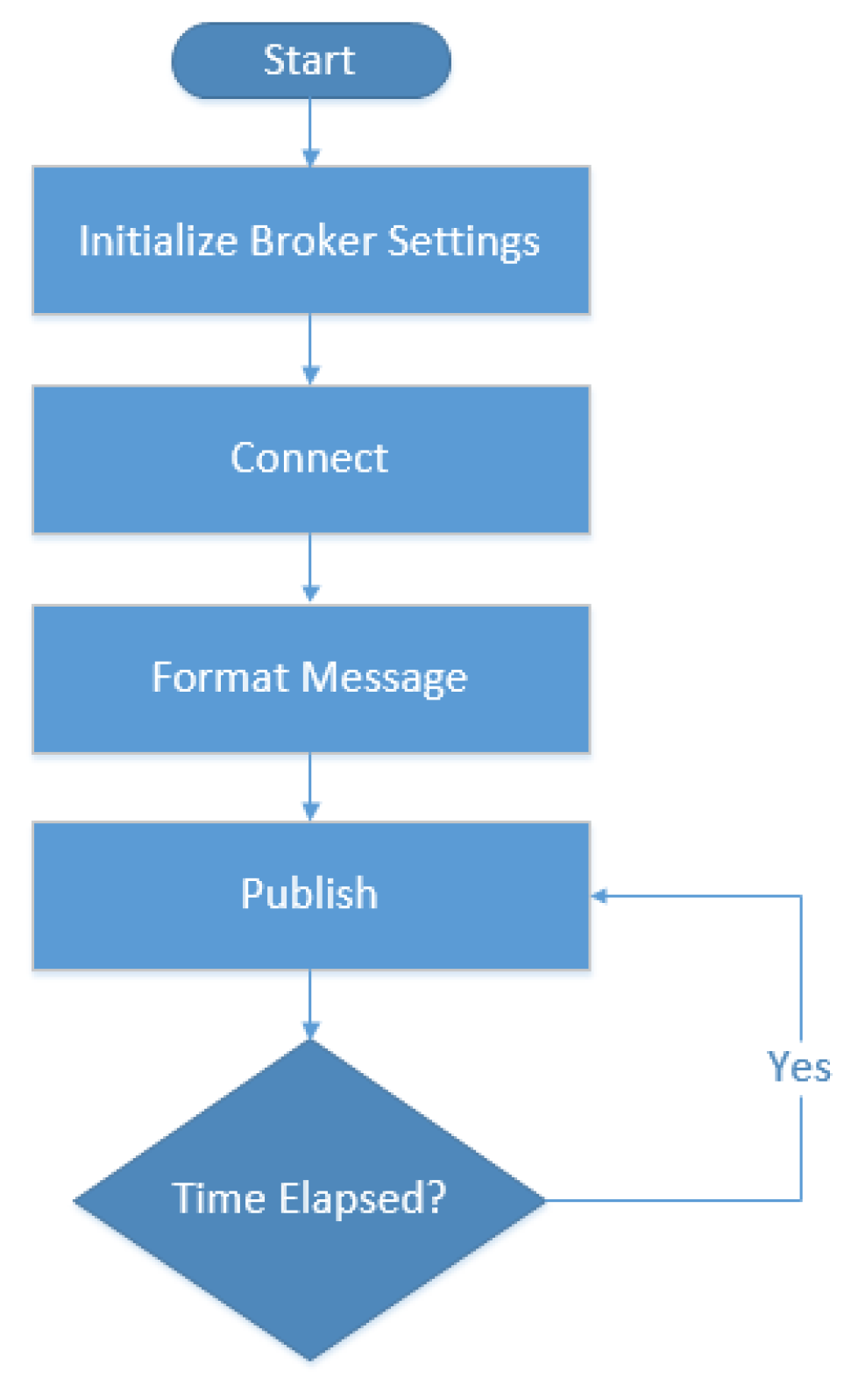
4.1.1. Default MQTT Publishing Behavior (Baseline Scenario)
- (t): incoming message rate.
- μserv(t): broker service rate.
4.2. Sources of Backpressure in MQTT Systems
4.2.1. High Publish Rate and Traffic Bursts
- Rapid data generation from IoT devices.
- Event-driven spikes (e.g., alarms, system updates).
4.2.2. Slow Subscribers (Receiver-Side Bottleneck)
- Limited processing capability.
- Network delays.
- Offline or intermittent clients.
4.2.3. Security Overhead
- TLS encryption/decryption.
- Authentication and authorization checks.
4.2.4. Wildcard Subscription Fan-Out
- Single message → multiple subscribers.
- Increased routing complexity.
4.2.5. QoS Overhead
4.3. Backpressure Propagation Model
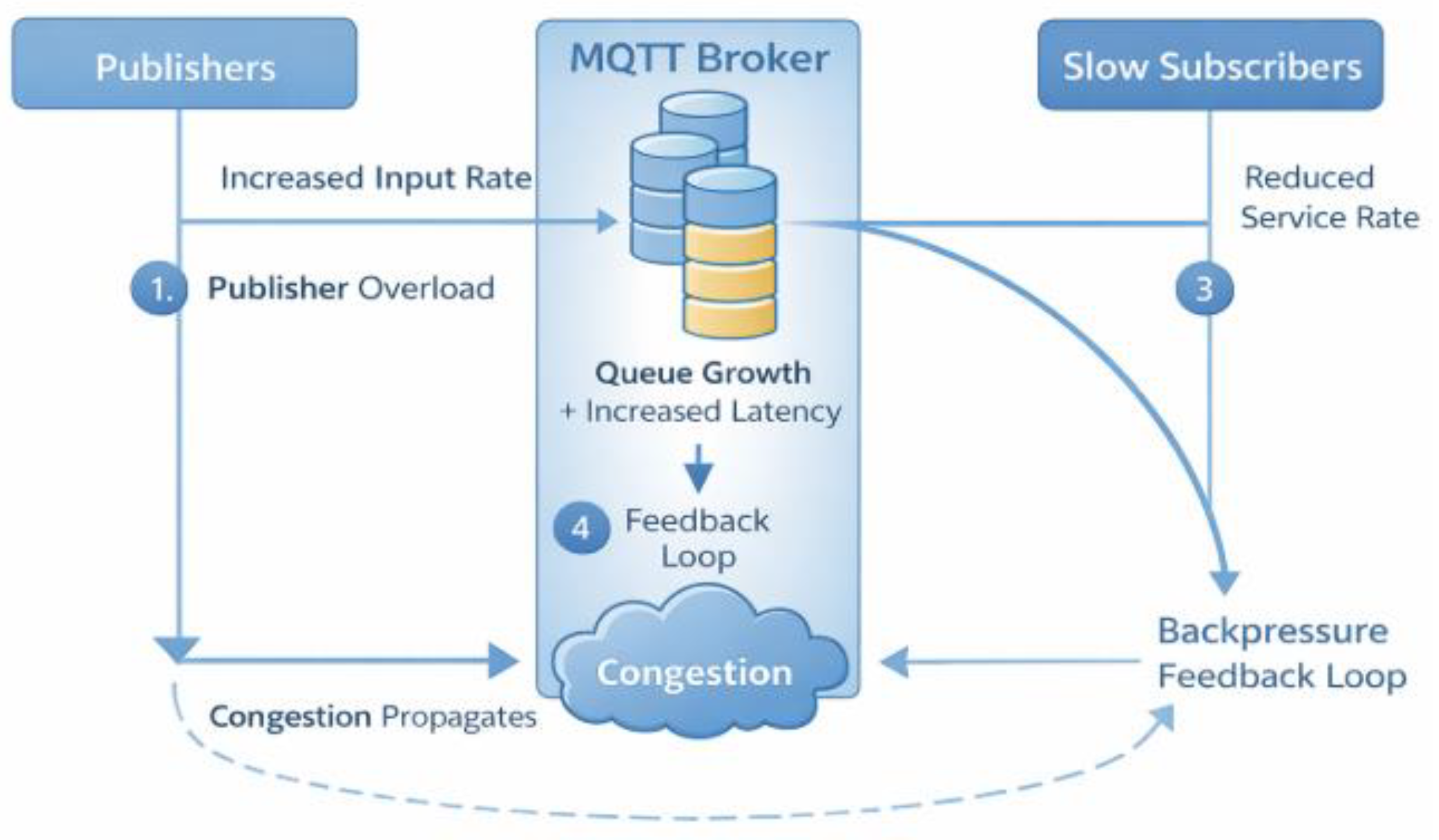
- Publisher overload → increased input rate.
- Broker queue growth → increased latency.
- Subscriber delay → reduced service rate.
- Feedback loop → system-wide congestion.
4.4. Flow-Control Mechanisms in MQTT
4.4.1. TCP-Level Flow Control
- Operates below application layer.
- Cannot control publish rate directly.
- Ineffective for multicast (publish/subscribe) systems.
4.4.2. Broker-Level Flow Control
- Message queue limits.
- Dropping messages.
- Rate limiting.
- Max inflight messages.
- Max queued messages.
- Reactive (not proactive).
- May cause message loss.
- No adaptation to system dynamics.
4.4.3. MQTT v5 Flow-Control Mechanisms
- No control for QoS 0 traffic.
- No awareness of security overhead.
- No adaptation to dynamic workloads.
- No handling of wildcard fan-out effects.
4.5. Adaptive Flow-Control Mechanisms
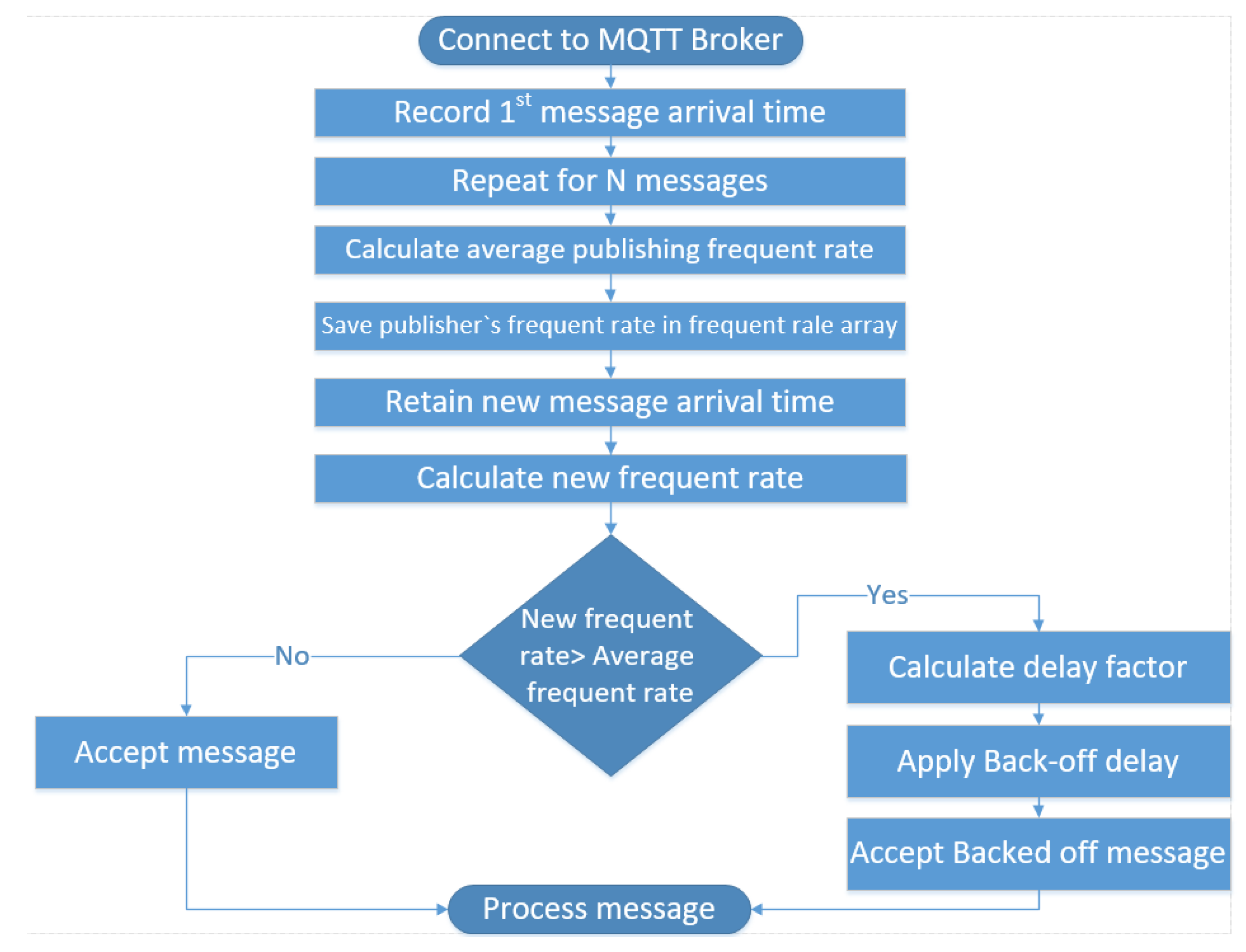
4.5.1. Adaptive Flow-Control Algorithm for Backpressure Mitigation
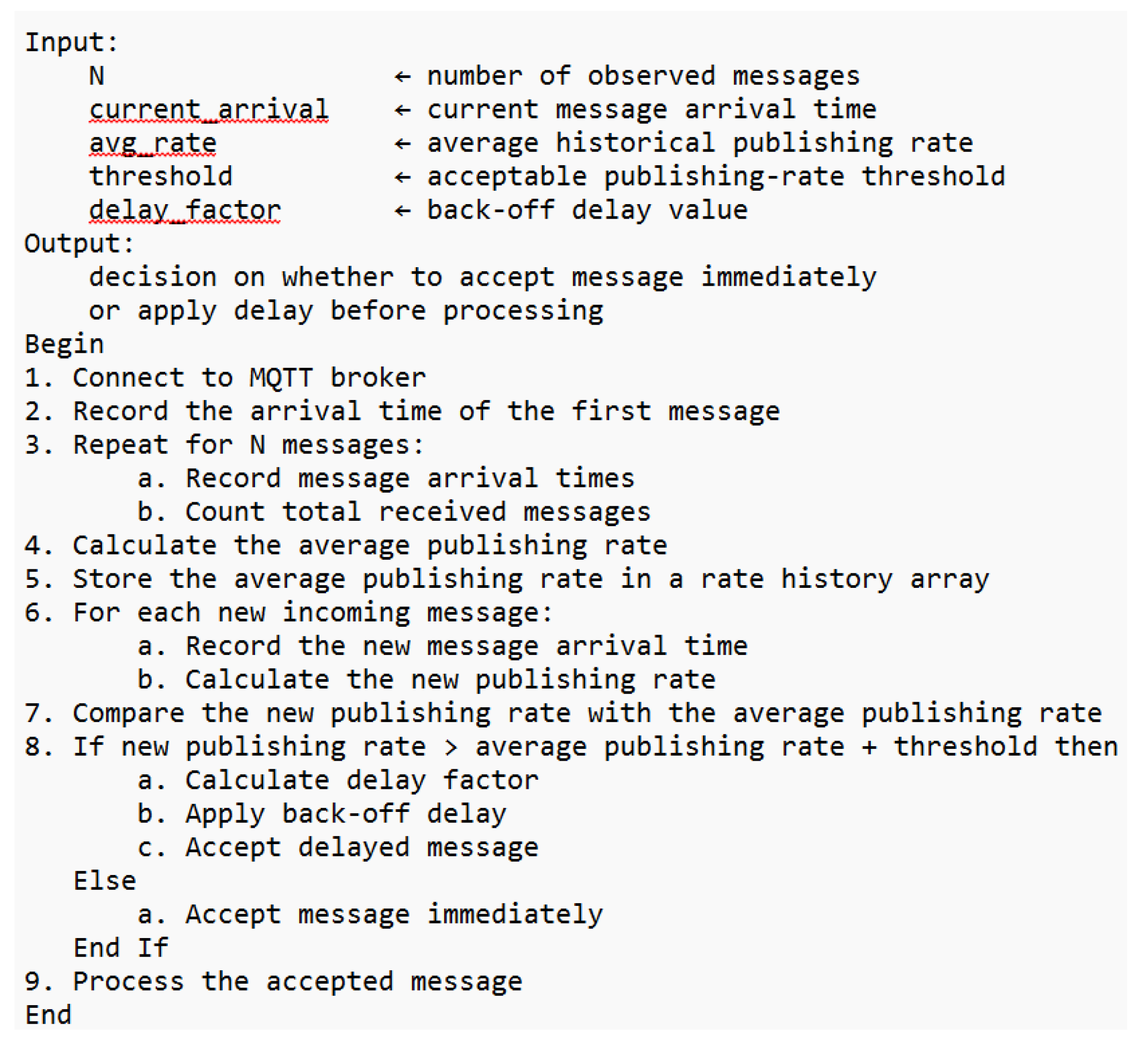
4.5.2. Backpressure-Driven Adaptive Flow Control (Core Concept)
- Rnew: updated publish rate.
- (t): backpressure indicator.
- α < 1: reduction factor.
- β > 0: increase step.
- θ: congestion threshold.
4.5.3. Stability Interpretation
4.5.4. Adaptive Flow-Control Algorithm for Backpressure Mitigation
4.6. Comparison of Flow-Control Approaches
| Approach | Adaptivity | QoS Awareness | Security Awareness | Efficiency |
|---|---|---|---|---|
| TCP Control | Low | No | No | Low |
| Broker Limits | Low | Partial | No | Medium |
| MQTT v5 | Medium | Yes (QoS1/2) | No | Medium |
| Adaptive Flow Control | High | Yes | Partial | High |
4.7. Integration with Security and Wildcards
- Security increases processing delay → increases backpressure.
- Wildcards increase message fan-out → increases load.
- Flow control must consider both.
4.8. Limitations of Existing Flow-Control Mechanisms
- Lack of cross-layer integration.
- No security-aware flow control.
- Limited handling of QoS 0 traffic.
- No optimization for wildcard-heavy systems.
- Absence of standardized adaptive frameworks.
4.9. Summary and Key Insights
- Backpressure is a multi-factor system problem.
- Existing solutions are fragmented and incomplete.
- MQTT v5 improves control but remains insufficient.
- Adaptive flow control provides a promising solution.
- Integration with security and wildcard management is essential.
5. Wildcard Subscription Behavior and Optimization in MQTT Systems
5.1. Overview of Wildcard Subscriptions in MQTT
- Single-level wildcard (+): matches exactly one topic level.
- Multi-level wildcard (#): matches all remaining levels.
5.2. Wildcard Matching Mechanism
5.2.1. Topic Matching Complexity
- T: number of topics.
- S: number of subscriptions.
- Each wildcard requires pattern evaluation.
- Multi-level wildcards increase matching depth.
5.2.2. Wildcard Matching Process
- Trie-based structures.
- Hash tables.
- Tree traversal algorithms.
5.3. Performance Impact of Wildcard Subscriptions
5.3.1. Routing Overhead
- Cforward: cost per message forwarding.
5.3.2. CPU Utilization
- String comparison operations.
- Tree traversal depth.
- Memory access.
5.3.3. Latency Increase
- Matching complexity.
- Queue size.
- Fan-out delivery. Latency = f (Cmatcℎ, Q (t), Fanout)
5.4. Security Risks of Wildcard Subscriptions
5.4.1. Unauthorized Data Access
- Sensitive data.
- System-wide telemetry.
5.4.2. Data Exfiltration Attacks
- Subscribe to #.
- Collect all broker messages.
5.4.3. Traffic Amplification
- Broker overload.
- Denial-of-Service (DoS) conditions.
5.4.4. Interaction with Access Control
- More wildcard rules → higher evaluation cost.
5.5. Mathematical Modeling of Wildcard Overlap
5.5.1. Misrouting Probability Model
- Poverlap: probability of overlap.
- Ntopics: number of topics.
- Nwildcards: number of wildcard subscriptions.
- Duplicate message delivery.
- Increased bandwidth usage.
5.5.2. Optimization Objective
5.6. Optimization Techniques for Wildcard Management
5.6.1. Precise Topic Design
- Reduced overlap.
- Improved security.
- Lower routing cost.
5.6.2. Subscription Partitioning
5.6.3. Broker-Side Optimization
- Trie-based indexing.
- Caching subscription matches.
- Precomputed routing tables.
5.6.4. Adaptive Wildcard Control
- Load-aware subscription handling.
- Reduced congestion.
5.6.5. Access Control Enhancement
- Limit # access.
- Apply strict ACL policies.
- Role-based filtering.
5.7. Integration with Flow Control and Security
5.8. Comparative Analysis of Wildcard Strategies
| Strategy | Performance | Security | Complexity |
|---|---|---|---|
| Broad wildcard (#) | Low | Low | Low |
| Limited wildcard (+) | Medium | Medium | Medium |
| Precise topics | High | High | High |
| Adaptive wildcard control | High | High | High |
5.9. Key Insights and Limitations
5.10. Summary
- Wildcard subscriptions increase routing complexity and system load.
- They introduce critical security risks when improperly controlled.
- Existing solutions fail to integrate wildcard behavior with flow control and security mechanisms.
6. Integrated Analysis and Literature Gap Discussion
6.1. Overview of Integrated System Behavior
- Security mechanisms (authentication, authorization, encryption).
- Flow control and backpressure management.
- Wildcard subscription behavior and routing complexity.
6.2. Cross-Layer Interaction Model
- Loadtraffic: base message rate.
- Loadsecurity: authentication + encryption + authorization overhead.
- Loadwildcard: fan-out and matching complexity.
6.3. Interaction Between Security and Flow Control
- TLS encryption increases packet size and processing cost.
- Authentication adds connection latency.
- Authorization introduces per-message evaluation overhead.
6.4. Interaction Between Wildcards and Flow Control
- Increased routing cost.
- Increased broker load.
- Higher probability of congestion.
6.5. Interaction Between Security and Wildcards
- Wildcards increase authorization complexity.
- ACL evaluation becomes more expensive.
- Misconfigurations increase security risks.
6.6. Combined Effect: System-Level Bottleneck
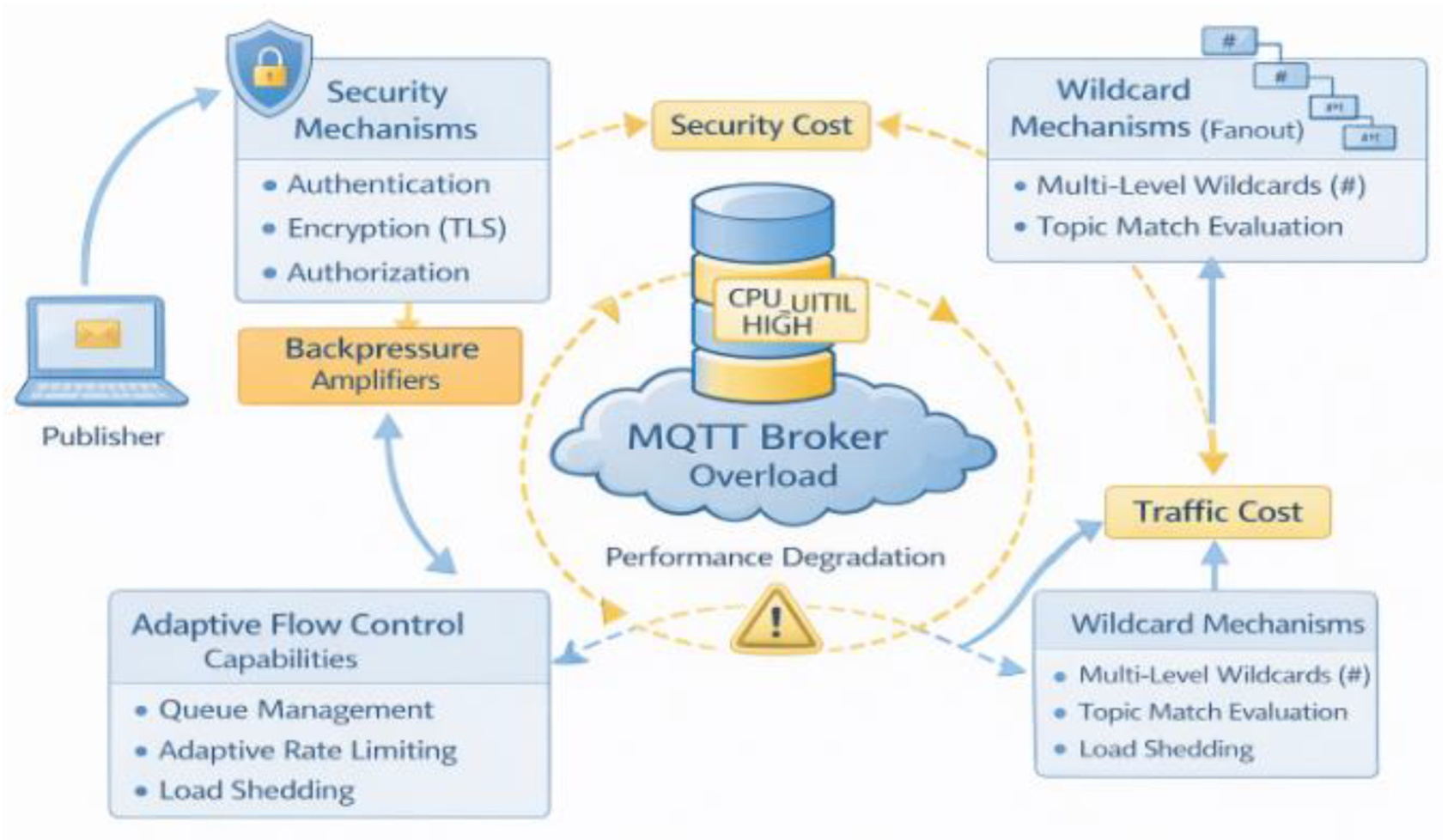
- Increased processing overhead.
- Increased routing complexity.
- Reduced service rate.
- Positive feedback loop of congestion.
6.7. Critical Review of Existing Literature
6.7.1. Security-Focused Studies
- Authentication and encryption.
- Access control.
- Ignore performance impact.
- No integration with flow control.
6.7.2. Flow-Control and Performance Studies
- Backpressure mitigation.
- Rate control.
- Ignore security overhead.
- No wildcard consideration.
6.7.3. Wildcard and Routing Studies
- Topic matching optimization.
- Routing efficiency.
- Ignore security implications.
- No congestion analysis.
6.8. Literature Gap Matrix
| Dimension | Security Studies | Flow-Control Studies | Wildcard Studies | Integrated Approaches |
|---|---|---|---|---|
| Authentication | ✔ | ✘ | ✘ | Partial |
| Authorization | ✔ | ✘ | ✔ | Partial |
| Backpressure | ✘ | ✔ | ✘ | ✘ |
| Adaptive Flow Control | ✘ | ✔ | ✘ | ✘ |
| Wildcard Optimization | ✘ | ✘ | ✔ | ✘ |
| Cross-Layer Integration | ✘ | ✘ | ✘ | ✘ |
6.9. Identified Research Gap
- No security-aware flow control mechanisms.
- No wildcard-aware congestion control.
- No joint evaluation under realistic workloads.
- Lack of adaptive, context-aware broker behavior.
6.10. Positioning of This Review
- Providing a holistic synthesis of MQTT system behavior.
- Highlighting interdependencies between core mechanisms.
- Identifying limitations in existing approaches.
- Establishing the need for:
- o Adaptive flow control.
- o Security-aware optimization.
- o Wildcard-aware routing strategies.
- Backpressure-driven adaptive flow control.
- Experimental validation under security and wildcard conditions.
- Integrated performance analysis.
6.11. Key Insights from Integrated Analysis
6.12. Summary
7. Future Research Directions
7.1. Overview
7.2. Security-Aware Adaptive Flow Control
7.2.1. Motivation
7.2.2. Research Direction
- (t): backpressure indicator (latency, queue size, loss).
- (t): security cost (authentication delay, encryption overhead).
- Reduced congestion under secure communication.
- Improved QoS reliability.
- Balanced trade-off between security and performance.
7.3. Wildcard-Aware Flow Control and Routing Optimization
7.3.1. Motivation
7.3.2. Research Direction
- Fanout: number of matched subscribers.
- Wfactor: wildcard complexity weight.
- Reduced routing overhead.
- Controlled traffic amplification.
- Improved scalability in large topic hierarchies.
7.4. Cross-Layer Optimization Frameworks
7.4.1. Motivation
- Application layer (publish rate).
- Security layer (authentication, ACL).
- Transport layer (TCP).
7.4.2. Research Direction
- Traffic generation.
- Security enforcement.
- Routing decisions.
- Holistic system optimization.
- Improved stability under dynamic workloads.
- Reduced performance-security trade-offs.
7.5. Intelligent and AI-Driven MQTT Management
7.5.1. Motivation
7.5.2. Research Direction
- Congestion prediction.
- Anomaly detection.
- Adaptive rate control.
- Latency.
- Queue size.
- Security events.
- Wildcard usage.
- Predictive congestion avoidance.
- Self-optimizing brokers.
- Improved resilience against attacks.
7.6. Advanced Security Mechanisms for MQTT
7.6.1. Motivation
7.6.2. Research Direction
- Lightweight cryptography.
- Zero-trust architectures.
- Blockchain-based authentication.
- Reduced computational overhead.
- Enhanced trust management.
- Improved scalability.
7.7. Wildcard Optimization and Topic Design Automation
7.7.1. Motivation
7.7.2. Research Direction
- Minimize wildcard overlap.
- Reduce routing complexity.
- Enhance security.
- Reduced broker load.
- Improved routing efficiency.
- Enhanced access control.
7.8. Standardized Benchmarking and Evaluation Frameworks
7.8.1. Motivation
7.8.2. Research Direction
- Security metrics.
- Performance metrics.
- Scalability analysis.
- Latency.
- Throughput.
- Message loss rate.
- Authentication delay.
- CPU utilization.
- Reproducible experiments.
- Fair comparison of solutions.
- Improved research quality.
7.9. Integration with Edge and Fog Computing
7.9.1. Motivation
7.9.2. Research Direction
- Edge-based brokers.
- Fog computing integration.
- Hierarchical messaging systems.
- Reduced latency.
- Improved scalability.
- Enhanced fault tolerance.
7.10. Toward Self-Adaptive and Autonomous MQTT Systems
7.10.1. Vision
- Self-monitoring.
- Self-optimizing.
- Self-healing.
- Detect congestion.
- Adapt flow control.
- Adjust security policies dynamically.
- Fully adaptive IoT communication.
- Minimal human intervention.
- High resilience under dynamic conditions.
7.11. Summary of Future Directions
- Security-aware adaptive flow control.
- Wildcard-aware optimization strategies.
- Cross-layer system design.
- AI-driven intelligent management.
- Lightweight and scalable security mechanisms.
- Standardized benchmarking frameworks.
- Distributed and edge-based architectures.
8. Conclusions
8.1. Summary of the Review
8.2. Key Findings
- Security and performance are inherently coupled
- 2.
- Backpressure is a system-level emergent phenomenon
- 3.
- Wildcard subscriptions act as amplifiers of both load and risk
- 4.
- Existing solutions are fragmented and insufficient
8.3. Contributions of This Review
- Comprehensive Synthesis:
- Critical Gap Identification:
- System-Level Modeling:
- Research Roadmap:
8.4. Practical Implications
- For researchers:
- For system designers:
8.5. Toward Next-Generation MQTT Systems
- Dynamically regulate traffic based on real-time conditions.
- Integrate security awareness into flow-control decisions.
- Optimize subscription behavior to reduce routing overhead.
- Leverage intelligent algorithms for predictive and autonomous management.
8.6. Final Remarks
Acknowledgments
Authors
 |
Nael Radwan is a Ph.D. Candidate, in the Department of Computer Science at the University of Idaho, USA. He received his Bachelor of Science in Computer Science from Philadelphia University (1999), a Higher Diploma in Computer Science from Amman Arab University (2002), and a Master’s degree in Computer Science from Amman Arab University (2005). He began his academic career in 2000 at Al-Balqa Applied University in Jordan as an instructor in the Department of Information Technology. In 2005, he joined Al-Quds Open University and later the Arab Open University in Jeddah, Saudi Arabia, as a lecturer in the Information Systems Department. In 2010, he joined King Abdulaziz University as a lecturer in the Department of Computer Science, where he served until 2021. In 2021, he moved to the United States to pursue his Ph.D. at the University of Idaho, where he is currently working as a Research Assistant. His research interests include computer networks, Internet of Things (IoT) systems, cybersecurity, and secure communication protocols. His academic profile is available at: https://drnaelradwan.academia.edu/ |
 |
Dr. Sheldon is currently a professor of computer science (CS) at the U. Idaho, has 35+ years of experience from academia, non-profit and industry sectors in various roles working on a diverse set of CS, data analytics/AI and cyberspace problems: Challenges related to AI and information security, resilience, deception, cybercrimes exploiting AI, trust and explain ability, OpSec, embedded avionics/vehicular software safety and security (e.g., CPS resiliency, intelligent transportation, IoT/Smart city/Cloud, energy delivery systems, supply chain, and cryptographic key management). His research projects as of late, are sourced from the convergence of software engineering, information assurance, leveraging data science and analytics (ML/DL). He received the Sigma Xi research and UT-Battelle key contributor, R&D 100 and significant event awards and is a life Sr. member of IEEE and ACM (+ASEE member). He has two BS degrees from the UMN Twin Cities and MS/PhD in CS from U. Texas at Arlington. |
References
- Da Xu, L.; He, W.; Li, S. Internet of things in industries: A survey. IEEE Trans. Ind. Inform. 2014, vol. 10(no. 4), 2233–2243. [Google Scholar]
- Al-Fuqaha; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of things: A survey on enabling technologies, protocols, and applications. IEEE Commun. Surv. Tutor. 2015, vol. 17(no. 4), 2347–2376. [Google Scholar] [CrossRef]
- Banks; Gupta, R. “MQTT Version 3.1. 1,”. OASIS Stand. 2014, vol. 29, 89. [Google Scholar]
- Radwan, N. M. A study: The future of the internet of things and its home applications. Int. J. Comput. Sci. Inf. Secur. IJCSIS 2020, vol. 18(no. 1). Available online: https://www.researchgate.net/profile/Nael-Radwan/publication/340451499_A_Study_The_Future_of_the_Internet_of_Things_and_its_Home_Applications/links/6025e91592851c4ed5668a52/A-Study-The-Future-of-the-Internet-of-Things-and-its-Home-Applications.pdf.
- Standard, MQTT Version 5.0. June; vol. 22, no. 2020, p. 1435.
- Sicari, S.; Rizzardi, A.; Grieco, L. A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Comput. Netw. 2015, vol. 76, 146–164. [Google Scholar] [CrossRef]
- Ammar, M.; Russello, G.; Crispo, B. Internet of Things: A survey on the security of IoT frameworks. J. Inf. Secur. Appl. 2018, vol. 38, 8–27. [Google Scholar] [CrossRef]
- Qiu, J.; Tian, Z.; Du, C.; Zuo, Q.; Su, S.; Fang, B. A survey on access control in the age of internet of things. IEEE Internet Things J. 2020, vol. 7(no. 6), 4682–4696. [Google Scholar] [CrossRef]
- Eddy, W. “Rfc 9293: Transmission control protocol (tcp).” RFC Editor, 2022. 01 Apr 2026. Available online: https://ftp.st.ryukoku.ac.jp/pub/internet/rfc/rfc9293.pdf.
- Lundgren; Landin, M. Data Flow Control in IoT: A Study on Throttling Implementations in MQTT. 2025. Available online: https://www.diva-portal.org/smash/record.jsf?pid=diva2:1994519.
- Mishra, A.; Kertesz, A. The use of MQTT in M2M and IoT systems: A survey. Ieee Access 2020, vol. 8, 201071–201086. [Google Scholar] [CrossRef]
- Hintaw, J.; Manickam, S.; Aboalmaaly, M. F.; Karuppayah, S. MQTT Vulnerabilities, Attack Vectors and Solutions in the Internet of Things (IoT). IETE J. Res. 2023, vol. 69(no. 6), 3368–3397. [Google Scholar] [CrossRef]
- Alsabbagh, W. MQTT Protocol in Industrial Internet of Things: Today Challenges and Tomorrow Solutions. Peter Langendoerfers Lab 2021, vol. 14(no. 8), 1–31. [Google Scholar]
- Radwan, N. M.; Alves-Foss, J. MQTT in Focus: Understanding the Protocol and Its Recent Advancements. Int. J. Comput. Sci. Secur. IJCSS 2024, vol. 18(no. 1), 1–14. [Google Scholar]
- Begović, T.; Čabarkapa, V.; Ivković, M.; Popović, B. MQTT Protocol in Smart Home Environments: Principles of Operation and Application. Int. J. Electr. Eng. Comput. 2024, vol. 8(no. 2), 53–61. [Google Scholar] [CrossRef]
- Palmese, F.; Redondi, A. E.; Cesana, M. Adaptive quality of service control for mqtt-sn. Sensors 2022, vol. 22(no. 22), 8852. [Google Scholar] [CrossRef]
- Liu, Y.; Lan, D.; Pang, Z.; Karlsson, M.; Gong, S. Performance evaluation of containerization in edge-cloud computing stacks for industrial applications: A client perspective. IEEE Open J. Ind. Electron. Soc. 2021, vol. 2, 153–168. [Google Scholar] [CrossRef]
- Qurishi, R.; Zhang, Z. “Security Analysis of Popular MQTT Broker Platforms,” 2025, Accessed: Apr. 01, 2026. Available online: https://odr.chalmers.se/bitstreams/f4aad2b4-618a-45cc-99d3-3e0f612e9bfb/download.
- Laaksonen, N. MQTT suitability for performance-critical resource control communication. 2025. Available online: https://www.theseus.fi/handle/10024/905954.
- Mishra; Kertesz, A. The use of MQTT in M2M and IoT systems: A survey. Ieee Access 2020, vol. 8, 201071–201086. [Google Scholar] [CrossRef]
- Algarni, M.; Alkhelaiwi, M.; Karrar, A. Internet of things security: A review of enabled application challenges and solutions. Int. J. Adv. Comput. Sci. Appl. 2021, vol. 12(no. 3). Available online: https://www.researchgate.net/profile/Abdelrahman-Karrar-4/publication/350551718_Internet_of_Things_Security_A_Review_of_Enabled_Application_Challenges_and_Solutions/links/60b09bab299bf13438f009be/Internet-of-Things-Security-A-Review-of-Enabled-Application-Challenges-and-Solutions.pdf. [CrossRef]
- Adam, M.; Hammoudeh, M.; Alrawashdeh, R.; Alsulaimy, B. A survey on security, privacy, trust, and architectural challenges in IoT systems. IEEE Access 2024, vol. 12, 57128–57149. [Google Scholar] [CrossRef]
- Tian, S.; Vassilakis, V. G. On the efficiency of a lightweight authentication and privacy preservation scheme for MQTT. Electronics 2023, vol. 12(no. 14), 3085. [Google Scholar] [CrossRef]
- AL-shammari, M. K. M.; Abead, S. A.; Mahmoud, H. H. Efficiency-Oriented Mutual Authentication Protocol for MCC Using Elliptic Curve Cryptography. J. Internet Serv. Inf. Secur. JISIS 2026, vol. 16(no. 1), 595–611. [Google Scholar] [CrossRef]
- Yang, Y.; Chen, Y.; Chen, F.; Chen, J. Identity-based cloud storage auditing for data sharing with access control of sensitive information. IEEE Internet Things J. 2021, vol. 9(no. 13), 10434–10445. [Google Scholar] [CrossRef]
- Lundgren, A.; Landin, M. Data Flow Control in IoT: A Study on Throttling Implementations in MQTT. 2025. Available online: https://www.diva-portal.org/smash/record.jsf?pid=diva2:1994519.
- Garcia-Macias, J. A. Transport in the IP-based Internet of Things: status report. Procedia Comput. Sci. 2023, vol. 224, 18–25. [Google Scholar] [CrossRef]
- Liu, Y.; Lan, D.; Pang, Z.; Karlsson, M.; Gong, S. Performance evaluation of containerization in edge-cloud computing stacks for industrial applications: A client perspective. IEEE Open J. Ind. Electron. Soc. 2021, vol. 2, 153–168. [Google Scholar] [CrossRef]
- Banno, R.; Watanabe, Y. “Wildcard Topic Management Using Bloom Filter in Distributed MQTT Brokers,” in 2025 IEEE 22nd Consumer Communications & Networking Conference (CCNC). IEEE, Apr. 01, 2026; 2025; pp. 1–6. Available online: https://ieeexplore.ieee.org/abstract/document/10975906/.
- Vardhan, M. M.; Tejdeep, R.; Mishra, P.; Narayanan, V. A. “Secure and efficient communication for MQTT-based IoT systems,” in IoT Security. Elsevier, 2026; pp. 203–217. Available online: https://www.sciencedirect.com/science/chapter/edited-volume/pii/B9780443341250000088.
- Liu, Y. Investigating the Reliability and Security of the MQTT Protocol. PhD Thesis, 2022. Available online: https://digital.lib.washington.edu/researchworks/items/323c1d3f-8b70-4c76-be1c-720d3d46a20d.
- Laghari, S. U. A.; Li, W.; Manickam, S.; Nanda, P.; Al-Ani, A. K.; Karuppayah, S. Securing MQTT ecosystem: Exploring vulnerabilities, mitigations, and future trajectories. IEEE Access 2024, vol. 12, 139273–139289. [Google Scholar] [CrossRef]
- Laghari, S. U. A.; Li, W.; Manickam, S.; Nanda, P.; Al-Ani, A. K.; Karuppayah, S. Securing MQTT ecosystem: Exploring vulnerabilities, mitigations, and future trajectories. IEEE Access 2024, vol. 12, 139273–139289. [Google Scholar] [CrossRef]
- Laghari, S. U. A.; Li, W.; Manickam, S.; Nanda, P.; Al-Ani, A. K.; Karuppayah, S. Securing MQTT ecosystem: Exploring vulnerabilities, mitigations, and future trajectories. IEEE Access 2024, vol. 12, 139273–139289. [Google Scholar] [CrossRef]
- AL-shammari, M. K. M.; Abead, S. A.; Mahmoud, H. H. Efficiency-Oriented Mutual Authentication Protocol for MCC Using Elliptic Curve Cryptography. J. Internet Serv. Inf. Secur. JISIS 2026, vol. 16(no. 1), 595–611. [Google Scholar] [CrossRef]
- Sicari, S.; Rizzardi, A.; Grieco, L. A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Comput. Netw. 2015, vol. 76, 146–164. [Google Scholar] [CrossRef]
- Yang, Y.-S.; Lee, S.-H.; Chen, W.-C.; Yang, C.-S.; Huang, Y.-M.; Hou, T.-W. TTAS: Trusted token authentication service of securing SCADA network in energy management system for industrial Internet of Things. Sensors 2021, vol. 21(no. 8), 2685. [Google Scholar] [CrossRef]
- Liu, Y.; Lan, D.; Pang, Z.; Karlsson, M.; Gong, S. Performance evaluation of containerization in edge-cloud computing stacks for industrial applications: A client perspective. IEEE Open J. Ind. Electron. Soc. 2021, vol. 2, 153–168. [Google Scholar] [CrossRef]
- Wu, J. A Survey on Cloud-Edge-Terminal Collaborative Intelligence in AIoT Networks. arXiv 2025, arXiv:2508.18803. [Google Scholar] [CrossRef]
- Mishra; Kertesz, A. The use of MQTT in M2M and IoT systems: A survey. Ieee Access 2020, vol. 8, 201071–201086. [Google Scholar] [CrossRef]
- Javed; Awais, M.; Shoaib, M.; Khurshid, K. S.; Othman, M. Machine learning and deep learning approaches in IoT. PeerJ Comput. Sci. 2023, vol. 9, e1204. [Google Scholar] [CrossRef] [PubMed]
- Liu, Y.; Wang, J.; Li, J.; Niu, S.; Song, H. Machine learning for the detection and identification of Internet of Things devices: A survey. IEEE Internet Things J. 2021, vol. 9(no. 1), 298–320. [Google Scholar] [CrossRef]
- Hassan, A.; Aslam, J.; Tahir, S.; Rashid, I. Securing the Internet of Things: Exploring MQTT Vulnerabilities and Threats in Pakistan’s IoT Landscape. in 2024 International Conference on Engineering & Computing Technologies (ICECT), Apr. 01, 2026; IEEE, 2024; pp. 1–6. Available online: https://ieeexplore.ieee.org/abstract/document/10581385/.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




