Submitted:
14 March 2026
Posted:
16 March 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background
2.1. PV Inverters as Cyber-Physical DER Components
- Embedded operating systems
- Local data logging and storage
- Wireless and wired communication interfaces
- Remote monitoring and control capabilities
- Cloud-based analytics and firmware updates
2.2. Telemetry Characteristics of Modern Inverters
- Electrical measurements: voltage, current, power, frequency, harmonics
- Operational states: MPPT behaviour, grid-support modes, alarms
- Environmental data: temperature, irradiance (in some models)
- Metadata: serial numbers, firmware versions, commissioning data
- Event logs: faults, restarts, configuration changes
- Cloud-side logs: authentication events, installer access, API calls
2.3. Communication Protocols in DER Ecosystems
SunSpec Modbus (RTU/TCP)
- Exposes structured registers containing electrical measurements and metadata.
- Lacks built-in encryption or authentication in its basic form.
- Often used over RS485 or TCP/IP networks.
Modbus TCP
- Simple, lightweight, but inherently insecure.
- Susceptible to eavesdropping and manipulation.
IEEE 2030.5 (Smart Energy Profile 2.0)
- Supports secure transport (TLS).
- Includes rich metadata and device models.
- Can expose detailed operational information.
Vendor-Specific APIs and Cloud Protocols
- MQTT, HTTPS, WebSockets, proprietary telemetry channels.
- Often undocumented, with varying levels of minimization and retention.
2.4. Cloud Platforms and Installer Portals
- User dashboards for system owners
- Installer portals with privileged access
- Utility or aggregator interfaces for grid-support programs
- APIs for third-party integrations
- Firmware update services (OTA)
- Long-term data retention and analytics
- Retention policies that may exceed operational needs
- Overprivileged installer accounts
- Cross-tenant data exposure risks
- Opaque data-sharing practices
- Metadata accumulation over years of operation
2.5. External Actors and Data Flows
- System owners
- Installers and maintenance providers
- Manufacturers
- Utilities and aggregators
- Third-party service providers
- Overprivileged access
- Unintended data sharing
- Cross-domain inference
- Long-term exposure through cloud retention
3. Methodology
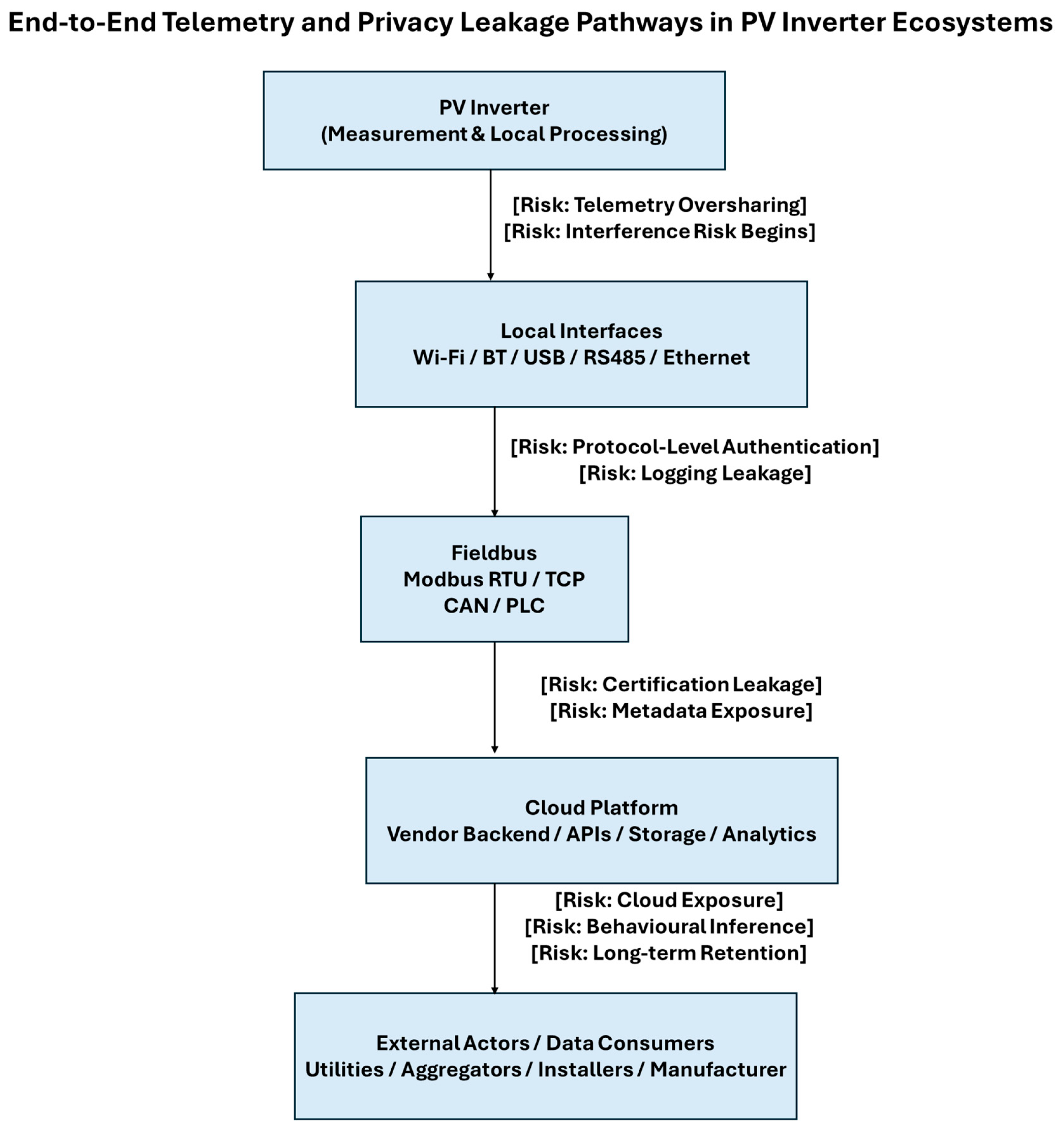
3.1. Scope and Analytical Framework
- Device-level telemetry and local logging
- Local communication interfaces (wired and wireless)
- Fieldbus and DER communication protocols
- Cloud platforms and vendor ecosystems
- External actors with legitimate or delegated access
3.2. Telemetry Inspection and Data Characterization
- Register maps from SunSpec Modbus models
- Sample telemetry payloads from Modbus TCP
- IEEE 2030.5 device models and resource structures
- Vendor-specific API payloads (where publicly documented)
- Metadata fields exposed during commissioning and operation
- Measurement granularity
- Metadata richness
- Temporal resolution
- Contextual information
- Identifiers and cross-linkable fields
- Event and fault logs
3.3. Protocol Analysis
- SunSpec Modbus (RTU and TCP)
- Modbus TCP
- IEEE 2030.5 (Smart Energy Profile 2.0)
- Vendor-specific cloud protocols (MQTT, HTTPS, WebSockets)
- Data exposure (fields, registers, metadata)
- Security properties (encryption, authentication, integrity)
- Default configurations
- Potential for passive or active interception
- Cross-layer interactions (e.g., metadata leakage through TLS certificates or API endpoints)
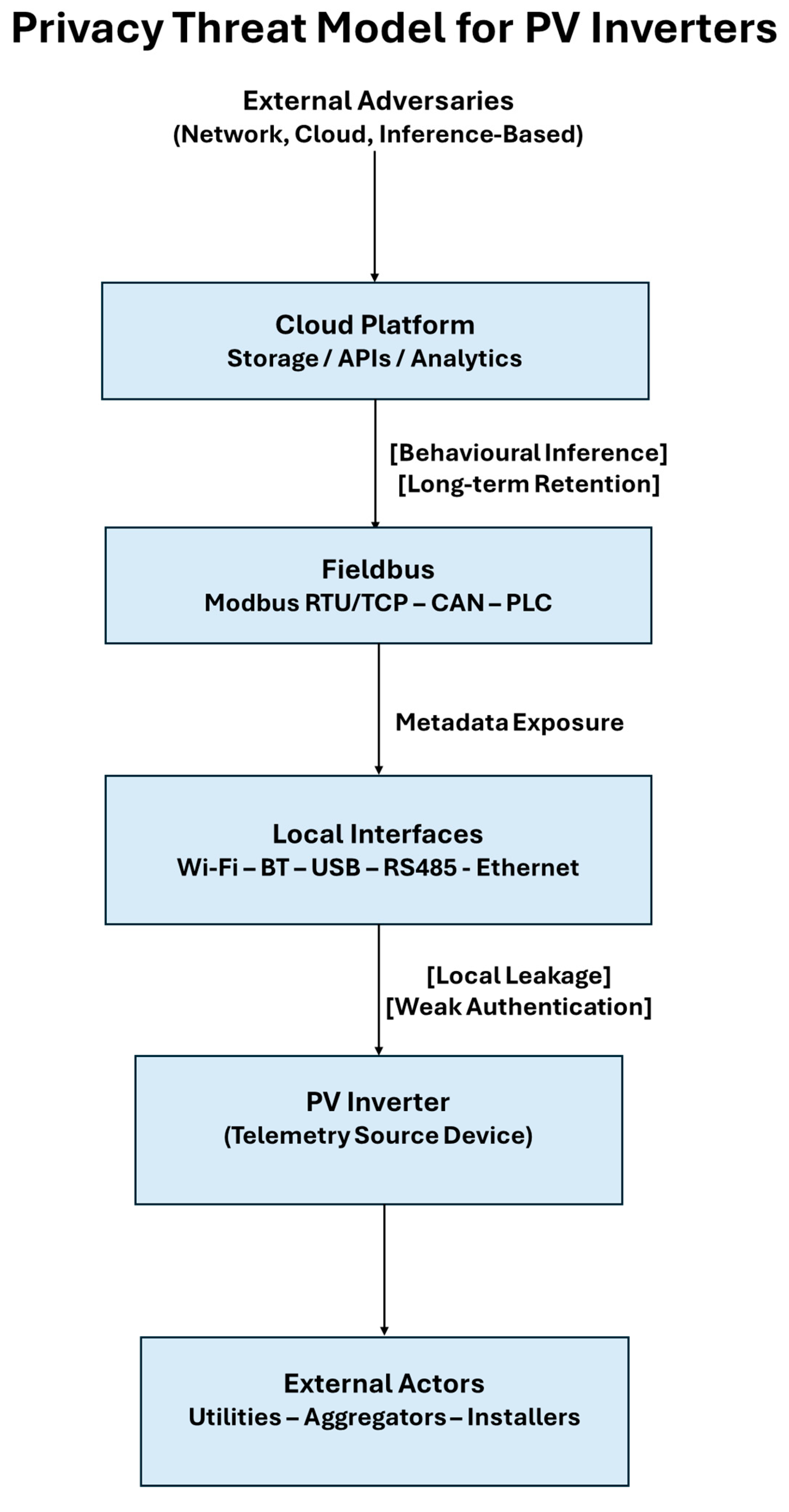
3.4. Actor and Adversary Modelling
- System owners
- Installers and maintenance providers
- Manufacturers
- Utilities and aggregators
- Cloud vendors
- Potential adversaries (network-level, cloud-side, inference-based)
- Access privileges
- Data visibility
- Potential misuse scenarios
- Cross-domain inference capabilities
3.5. Risk Classification and Leakage Taxonomy
- Device-level leakage
- Interface-level leakage
- Fieldbus-level leakage
- Cloud-level leakage
- External-actor leakage
- Data sensitivity
- Inference potential
- Exposure likelihood
- Persistence and retention
- Cross-actor propagation
3.6. Limitations
- publicly available documentation,
- protocol specifications,
- telemetry structures,
- and generalizable architectural patterns.
4. Privacy Leakage Vectors in PV Inverters
4.1. Device-Level Leakage
4.1.1. Fine-Grained Electrical Measurements
- occupancy patterns
- appliance usage
- behavioural routines
- load signatures
4.1.2. Local Logging and Event Histories
- faults
- restarts
- configuration changes
- grid events
- installer interventions
4.1.3. Persistent Identifiers and Metadata
- uniquely identify installations
- correlate data across platforms
- infer device age, maintenance history, or vulnerabilities
4.2. Interface-Level Leakage
4.2.1. Wi-Fi and Bluetooth Interfaces
- SSIDs containing device model or serial number
- Bluetooth identifiers
- Setup or commissioning beacons
- device presence
- installation type
- manufacturer
- commissioning status
4.2.2. USB, RS485, and Service Ports
- raw telemetry
- configuration access
- commissioning data
- installer logs
- passive data extraction
- cloning of device metadata
- unauthorized access to historical logs
4.2.3. Installer Commissioning Apps
- GPS coordinates
- installation photos
- user identifiers
- Wi-Fi credentials
4.3. Fieldbus-Level Leakage
4.3.1. SunSpec Modbus (RTU/TCP)
- electrical measurements
- device metadata
- configuration parameters
- operational states
- eavesdrop on telemetry
- infer behavioural patterns
- extract device identifiers
- correlate installations across networks
4.3.2. Modbus TCP
- real-time telemetry
- fault logs
- configuration registers
4.3.3. IEEE 2030.5 (SEP2)
- DER capabilities
- operational modes
- event histories
- device models
4.4. Cloud-Level Leakage
4.4.1. Telemetry Oversharing
- high-frequency telemetry
- detailed event logs
- commissioning metadata
- installer identifiers
- geolocation data
4.4.2. Long-Term Retention
- years
- indefinitely
- or without clear retention policies
4.4.3. Overprivileged Installer Accounts
- full access to user systems
- historical data
- configuration capabilities
4.4.4. Cross-Tenant Exposure
- multiple customers
- multiple sites
- multiple devices
4.4.5. Vendor Analytics and Third-Party Integrations
- performance analytics
- fleet management
- predictive maintenance
- third-party services
4.5. External-Actor Leakage
4.5.1. Installers and Maintenance Providers
- privileged access
- long-term visibility
- ability to extract logs
- access to commissioning metadata
- unauthorized monitoring
- data misuse
- cross-customer inference
4.5.2. Utilities and Aggregators
- operational states
- grid-support modes
- event histories
- consumption patterns
- occupancy
- system behaviour
4.5.3. Third-Party Service Providers
- telemetry
- metadata
- user identifiers
4.6. Summary of Leakage Categories
5. Behavioural and Occupancy Inference
5.1. Occupancy Detection
- rapid changes in self-consumption
- transitions between grid import and export
- inverter wake-up and sleep cycles
- load-driven fluctuations in PV utilisation
5.2. Behavioural Routines and Daily Patterns
- morning and evening activity peaks
- appliance-driven consumption signatures
- weekend vs weekday routines
- seasonal behavioural changes
5.3. Appliance and Load Inference
- EV charging events
- heat pump operation
- HVAC cycles
- water heater usage
- battery charging/discharging patterns
5.4. Installation Profiling
- system size and configuration
- presence of batteries
- type of inverter (hybrid, string, microinverter)
- commissioning date
- maintenance history
5.5. Long-Term Behavioural Profiling
- lifestyle profiling
- occupancy probability models
- prediction of future behaviour
- correlation with external datasets (weather, tariffs, events)
6. Discussion
6.1. Comparison with Smart Meter Privacy
- data minimization
- retention limits
- access control
- transparency requirements
- collect richer metadata
- transmit data more frequently
- involve more external actors
- rely heavily on cloud platforms
- lack standardized privacy requirements
6.2. Implications for CRA, NIS2, and GDPR
- CRA: inverter vendors must address data protection as part of cybersecurity requirements.
- NIS2: operators of DER fleets must manage telemetry as sensitive operational data.
- GDPR: inverter telemetry qualifies as personal data when linked to identifiable users or behavioural patterns.
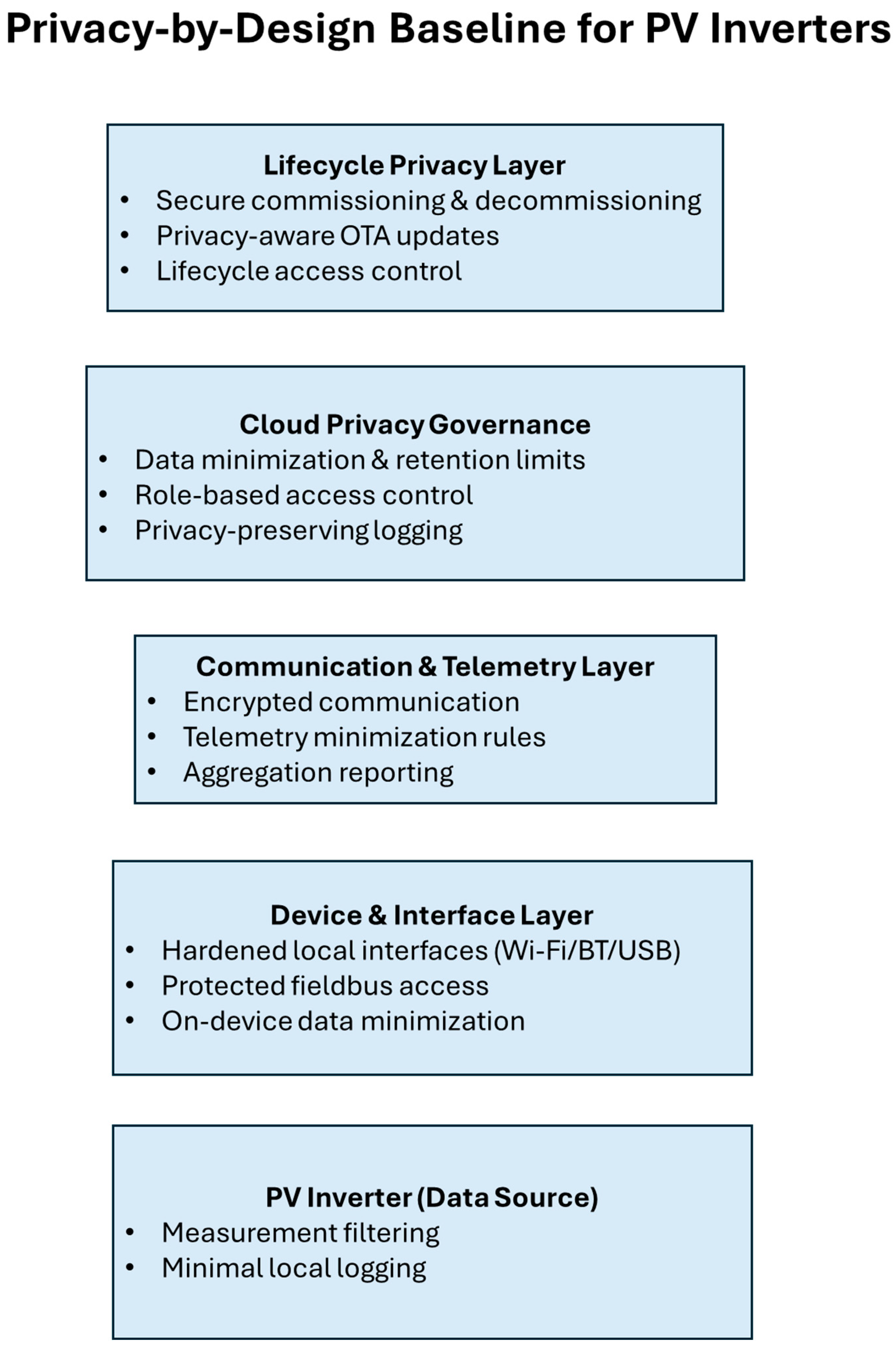
6.3. Need for a Privacy-by-Design Framework
- reduce telemetry granularity
- minimize metadata exposure
- enforce lifecycle-aware access control
- govern cloud retention
- limit installer privileges
- ensure transparency for end users
6.4. Limitations and Generalizability
- publicly documented telemetry structures
- protocol specifications
- common architectural patterns
7. Recommendations
7.1. Telemetry Minimization
- Reduce measurement frequency where possible.
- Limit reporting of high-resolution power data.
- Avoid transmitting redundant or non-essential fields.
7.2. Metadata Reduction
- Remove or hash persistent identifiers.
- Avoid exposing commissioning timestamps or installer IDs.
- Minimize device-specific metadata in cloud payloads.
7.3. Secure and Minimal Interfaces
- Disable Wi-Fi/Bluetooth after commissioning.
- Protect USB/RS485 ports with authentication.
- Restrict local access to essential functions only.
7.4. Protocol Hardening
- Use encrypted and authenticated transport for Modbus TCP.
- Apply privacy-aware profiles for IEEE 2030.5.
- Limit exposure of SunSpec metadata.
7.5. Cloud Governance
- Enforce strict retention limits.
- Implement role-based access control (RBAC/ABAC).
- Remove installer access after commissioning.
- Provide transparency dashboards for users.
7.6. Lifecycle Privacy Controls
- Secure commissioning workflows.
- Privacy-aware OTA updates.
- Secure decommissioning and certificate revocation.
7.7. Multi-Actor Access Management
- Define clear privilege boundaries.
- Audit access by installers, utilities, and third parties.
- Provide user-controlled access revocation.
8. Conclusion
- This preprint has presented the first comprehensive analysis of privacy leakage vectors in modern PV inverter ecosystems. Through a structured examination of device-level telemetry, local interfaces, fieldbus protocols, cloud platforms, and multi-actor access patterns, we have shown that PV inverters expose a significantly broader privacy surface than previously recognized. Unlike smart meters—whose privacy implications have been extensively studied and regulated—PV inverters operate in a fragmented and largely unregulated environment where telemetry oversharing, metadata exposure, long-term retention, and installer overprivilege are common.
- Our findings demonstrate that inverter telemetry can reveal sensitive behavioural information, including occupancy patterns, daily routines, appliance usage, and long-term lifestyle profiles. These risks are amplified by cloud-centric architectures, persistent identifiers, and the involvement of multiple external actors with varying levels of access and visibility. The analysis highlights a clear gap between current industry practices and the privacy expectations established by frameworks such as GDPR, as well as the emerging cybersecurity obligations introduced by CRA and NIS2.
- By mapping privacy leakage across the full telemetry pipeline, this work establishes the analytical foundation for a dedicated privacy-by-design framework for PV inverters and DER systems. The recommendations provided—covering telemetry minimization, metadata reduction, interface hardening, protocol governance, cloud retention policies, and lifecycle-aware access control—outline initial steps toward more privacy-preserving inverter architectures.
- Future work will build on this foundation by proposing a structured Privacy-by-Design Baseline, a reference architecture, and a case study demonstrating practical implementation. Together, these contributions aim to support manufacturers, operators, and policymakers in developing inverter ecosystems that are not only secure and interoperable, but also aligned with modern privacy principles.
| Layer | Leakage Type | Examples |
|---|---|---|
| Device | Measurement & metadata | Power, MPPT, logs, serials |
| Interfaces | Local access | Wi-Fi, BT, USB, RS485 |
| Fieldbus | Protocol exposure | SunSpec, Modbus TCP, IEEE 2030.5 |
| Cloud | Retention & overprivilege | Installer access, analytics |
| External actors | Multi-stakeholder access | Utilities, aggregators |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.




