Submitted:
12 March 2026
Posted:
13 March 2026
You are already at the latest version
Abstract
Keywords:
Overview
Introduction
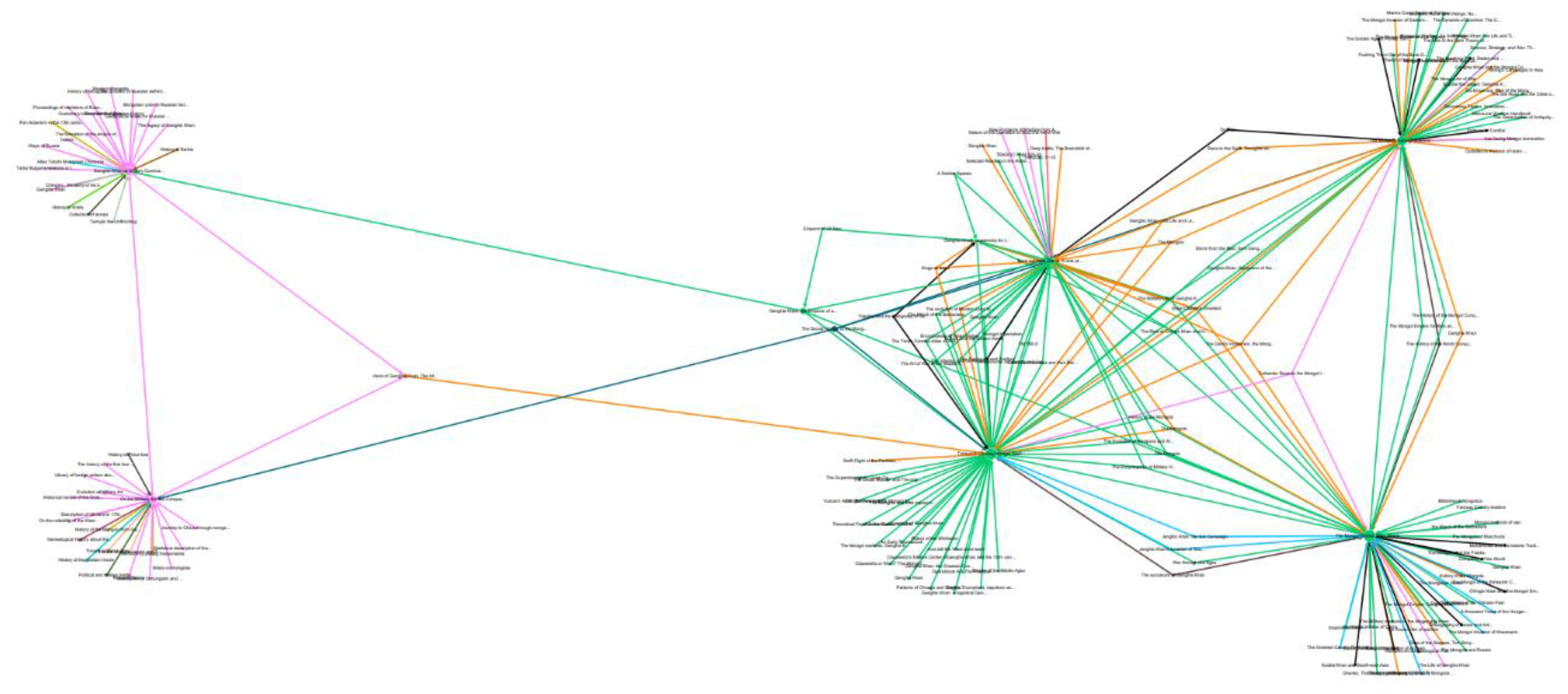
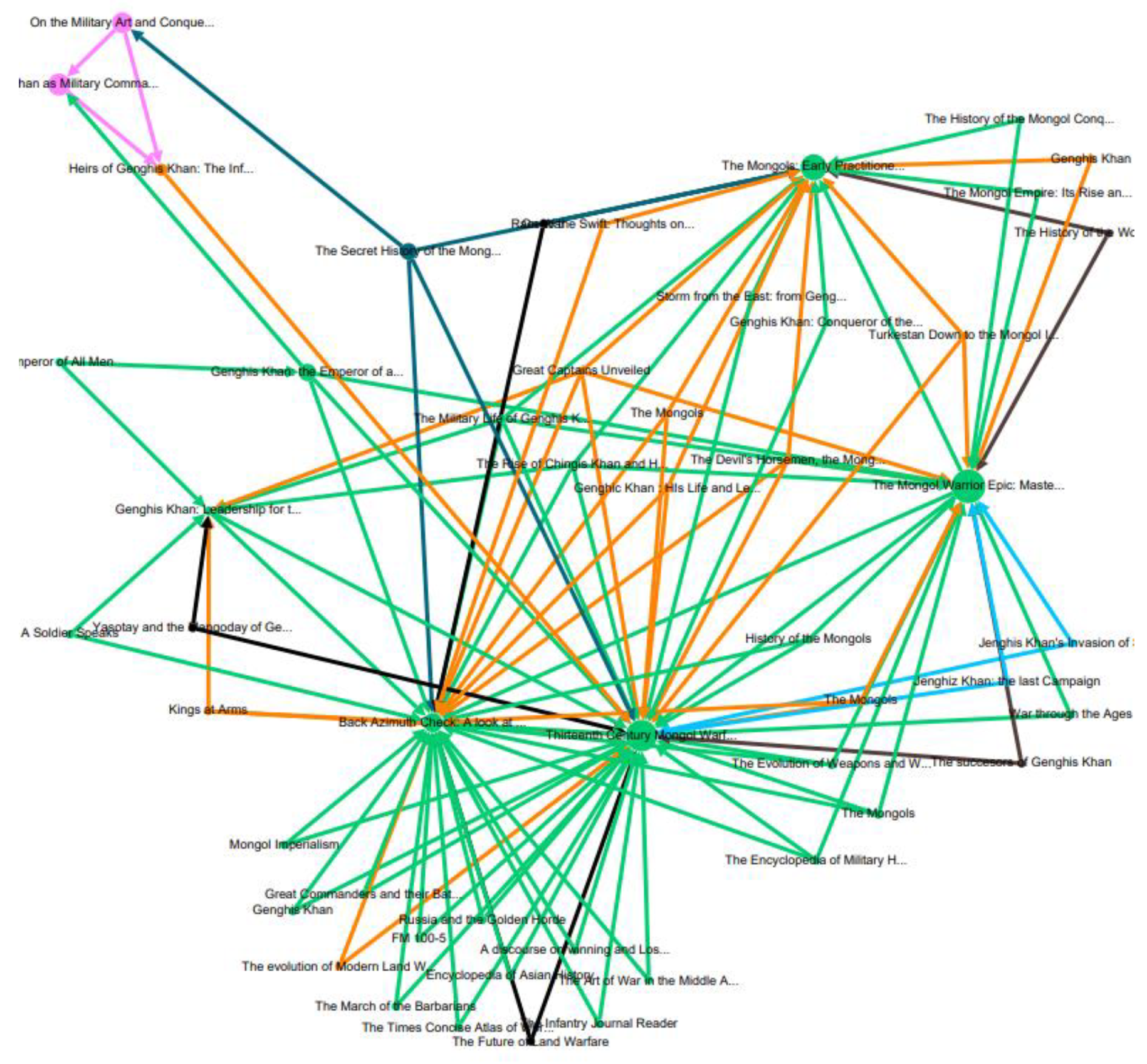
Historiographical Context of the Network
Original Works
Connections
Future Steps
Methodology
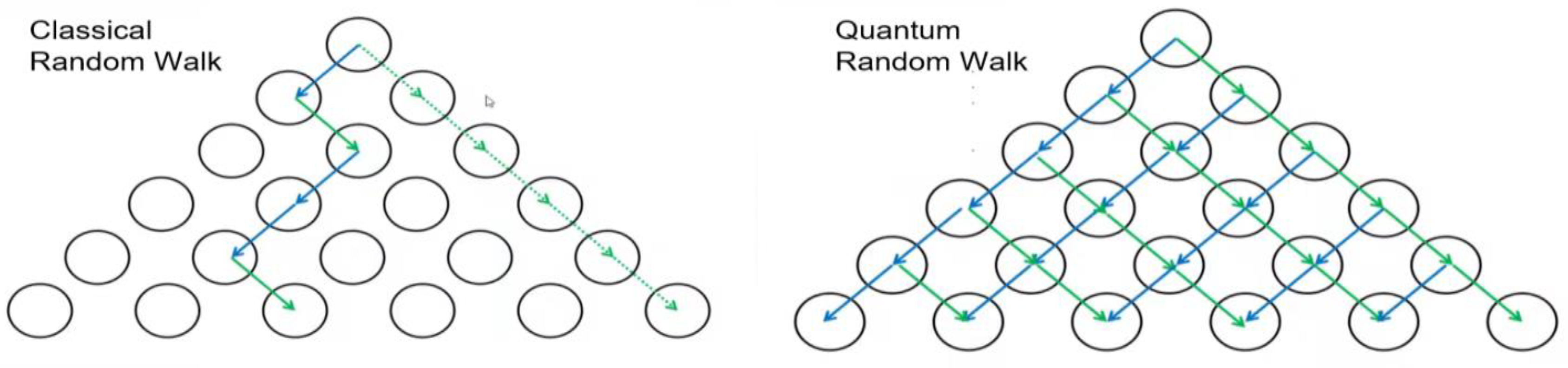
A Primer on Random Walks & Quantum Computing
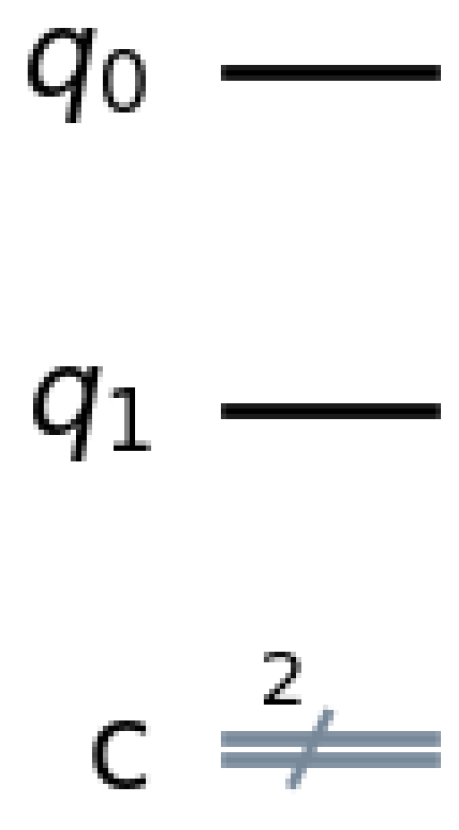
An Introduction to Quantum Circuits & Quantum Link Prediction
| Time | 0-0 | 1-1 | 2-2 | 3-3 |
| 0 | 0.242188 | 0.268555 | 0.240234 | 0.249023 |
| 0-3 | 1-2 | |
| Maximum Probability | 0.241211 | 0.242188 |
| Average Probability | 0.107422 | 0.112109 |
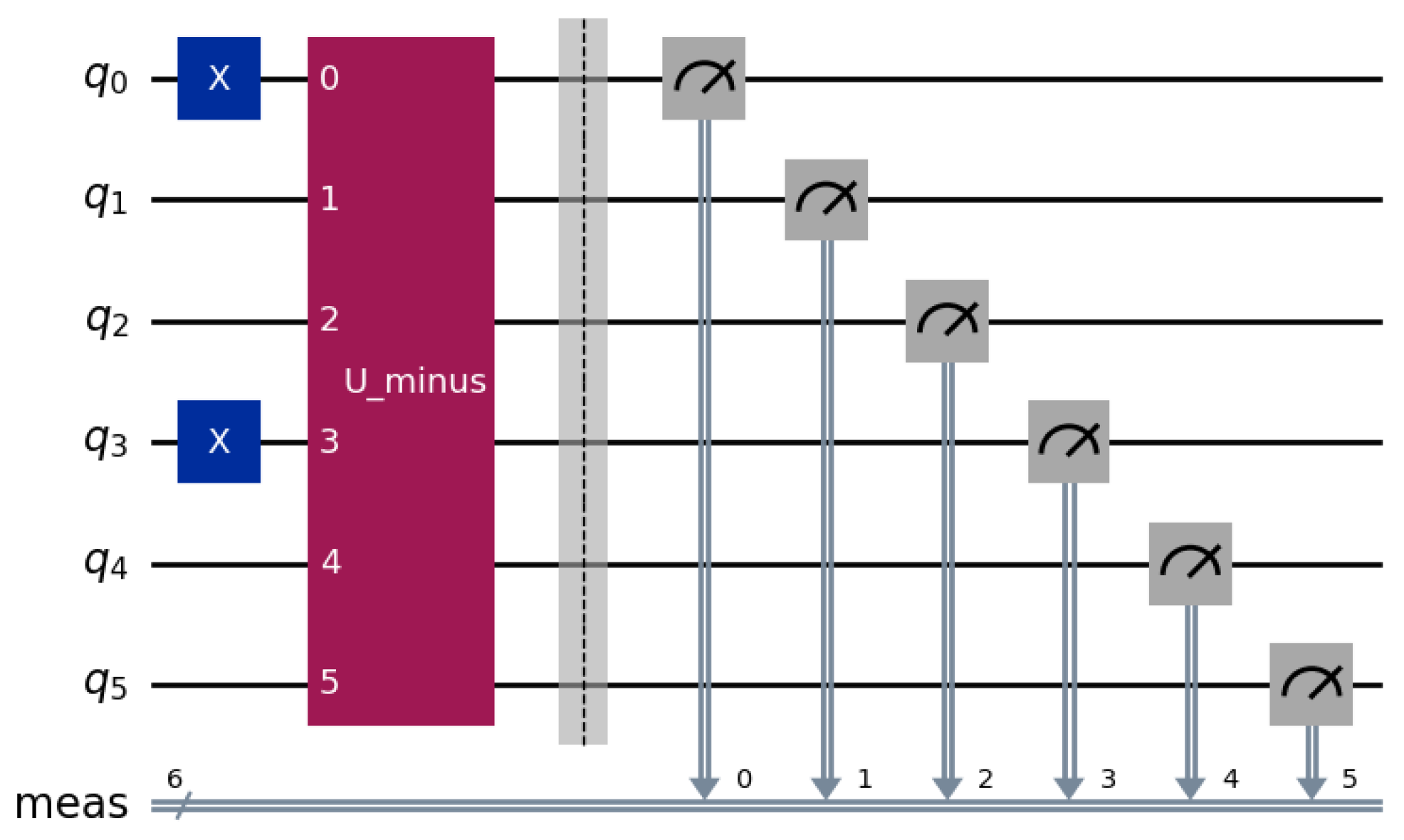
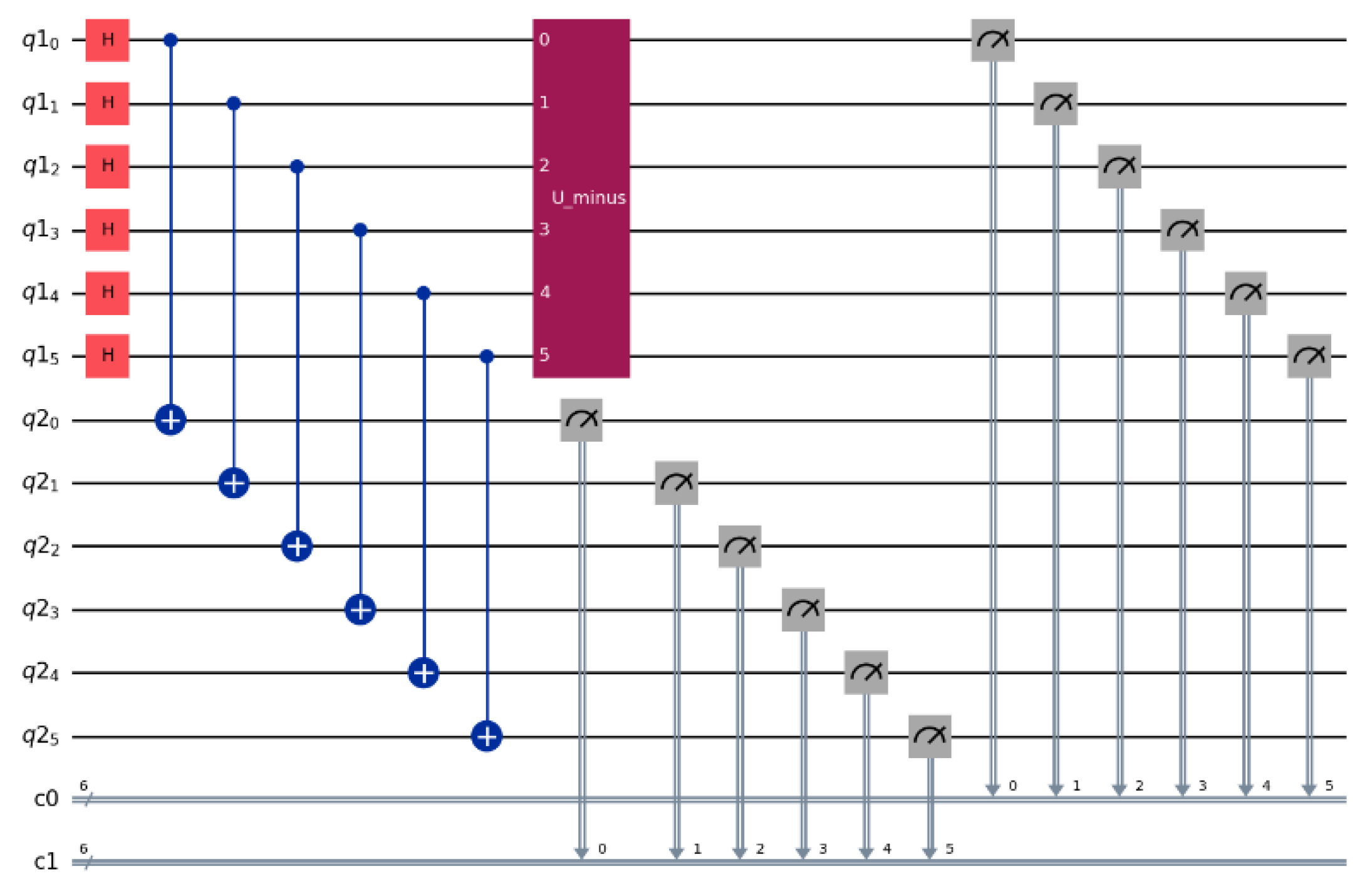
Citation Network Circuits
Results & Historiographical Exploration
Application of Single Node Quantum Random Walk
Application of Superpositioned Quantum Random Walk
Methodological Considerations
- Algorithm Selection
- Required Preprocessing
- Hardware Considerations
- Released Research Software Package
Algorithm Selection
Required Preprocessing
Hardware Considerations
Released Research Software Package
Conclusion & Future Steps
Acknowledgments
References
- Barzen, Johanna. “From Digital Humanities to Quantum Humanities: Potentials and Applications.” In Quantum Computing in the Arts and Humanities, edited by Eduardo Reck Miranda. Cham: Springer, 2022.
- Barthold, W. Turkestan Down to the Mongol Invasion. 2nd ed. Oxford: Clarendon Press, 1928. English translation of V. V. Barthold, Turkestan v epokhu mongolʹskago nashestvija (St. Petersburg, 1898).
- Bellamy, Chris. “Heirs of Genghis Khan: The Influence of the Tartar-Mongols on the Imperial Russian and Soviet Armies.” RUSI Journal 128, no. 1 (1983): 52–60.
- Benfield, D. C. The Mongols: Early Practitioners of Maneuver Warfare. Fort Leavenworth, KS: U.S. Army Command and General Staff College, 2012.
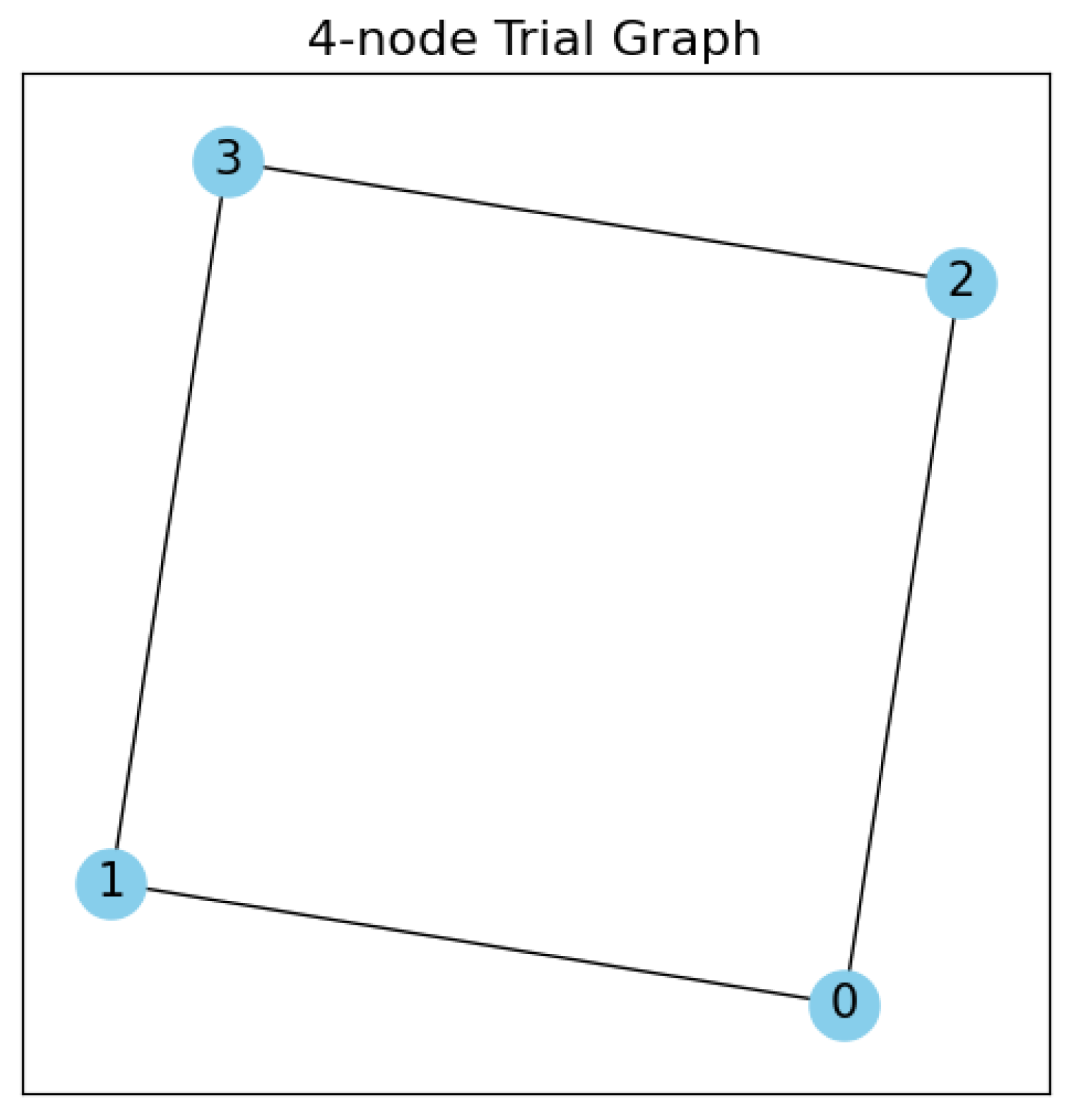
- Bernhardt, Chris. Quantum Computing for Everyone. Cambridge, MA: MIT Press, 2019.
- Hernandez, Jose. “Comparing Russian and American Military Studies on the Lessons of Mongol Military Art Utilizing Network Analysis and Close Readings.” University of Chicago, 2022. [CrossRef]
- Hernandez, Jose. QRW-HistoryCitation: Quantum Random Walks Applied in Qiskit to a Historical Citation Network. GitHub repository. Last modified 2025.
- Hernandez, Jose. QuantumRandomWalks. Python package. PyPI. Last updated September 22, 2025. https://pypi.org/project/QuantumRandomWalks/.
- IBM. “IBM Launches Its Most Advanced Quantum Computers, Fueling New Scientific Value and Progress towards Quantum Advantage.” IBM Newsroom, November 13, 2024. https://newsroom.ibm.com/2024-11-13-ibm-launches-its-most-advanced-quantum-computers,-fueling-new-scientific-value-and-progress-towards-quantum-advantage.
- IBM Quantum, “Fractional Gates,” IBM Quantum Documentation, accessed January 14, 2026, https://quantum.cloud.ibm.com/docs/en/guides/fractional-gates .
- IBM Quantum, “Qiskit,” IBM, accessed January 14, 2026, https://www.ibm.com/quantum/qiskit .
- IBM Quantum, “Bits, Gates, and Circuits,” IBM Quantum Learning, accessed January 14, 2026, https://quantum.cloud.ibm.com/learning/en/courses/utility-scale-quantum-computing/bits-gates-and-circuits.
- Ivanin, M. I. O voennom iskusstve i zavoevaniiakh mongolo-tartar i sredneaziatskikh narodov pri Chingiskhane i Tamerlane [On the Military Art and Conquests of the Tartar-Mongols and Central Asian Peoples under Genghis-Khan and Tamerlane]. Saint Petersburg, 1875.\.
- Juvaynī, ʻAlāʾ al-Dīn ʻAta-Malik. Genghis Khan: The History of the World Conqueror. Translated by Steven Runciman. Seattle: University of Washington Press, 1997.
- Khara-Davan, E. Chingis-Khan kak polkovodet͡s i ego nasledie: Kulʹturno-istoricheskiĭ ocherk Mongolʹskoĭ imperii XII-XIV veka [Genghis Khan: A Military Commander and His Legacy]. Izd. avtora, 1929.
- MacArthur, Douglas. A Soldier Speaks: Public Papers and Speeches of General of the Army Douglas MacArthur. New York: Praeger, 1965.
- McCreight, Richard D. The Mongol Warrior Epic: Masters of Thirteenth Century Maneuver Warfare. Fort Leavenworth, KS: U.S. Army Command and General Staff College, 1983.
- Mikhnevich, N. P. Istorīi︠a︡ voennago iskusstva sʺ drevni︠e︡ĭ shikh vremen do nachala deviatnadtsatago stolietīi︠a︡ [History of Military Art from Ancient Times to the Beginning of the Nineteenth Century]. S.-Peterburg: Leshtukovskai︠a︡ skoropechatni︠a︡ P.O. I︠A︡blonskago, 1895.
- Moutinho, João P., André Melo, Bruno Coutinho, István A. Kovács, and Yasser Omar. “Quantum Link Prediction in Complex Networks.” arXiv, December 9, 2021.
- Moutinho, João P., Duarte Magano, and Bruno Coutinho. “On the Complexity of Quantum Link Prediction in Complex Networks.” Scientific Reports 14 (2024): 1026.
- NetworkX Developers. NetworkX Documentation. Release 3.6.1. Accessed January 14, 2026. https://networkx.org/documentation/stable/index.html.
- P., Radhika Dileep, and Deepthi L. R. “Link Prediction in Citation Networks: A Survey.” In Proceedings of the 2022 Third International Conference on Intelligent Computing Instrumentation and Control Technologies (ICICICT), 1194–1200. Kannur, India, 2022. [CrossRef]
- Pittard, Dana. Thirteenth Century Mongol Warfare: Classical Military Strategy or Operational Art. Fort Leavenworth, KS: U.S. Army Command and General Staff College, 1994.
- Preskill, John. “Quantum Computing in the NISQ Era and Beyond.” Quantum 2 (August 2018): 79. [CrossRef]
- Rachewiltz, Igor de. The Secret History of the Mongols: A Mongolian Epic Chronicle of the Thirteenth Century. Leiden: Brill, 2004.
- Svechin, A. Strategi͡a [Strategy]. Moscow: Gos. voennoe izd-vo, 1926.
- Svechin, A. Evoli͡utsii͡a voennogo iskusstva s drevneĭ shikh vremen do nashikh dneĭ [Evolution of Military Art]. Moscow: Gos. izd-vo, 1927.
- Takemoto, Glenn H. Back Azimuth Check: A Look at Mongol Operational Warfare. Fort Leavenworth, KS: School of Advanced Military Studies, 1992.
- Taylor, W. S. Genghis Khan: Leadership for the Airland Battle. Maxwell AFB, AL: Air Command and Staff College, 1988.
- Vladimirtzov, B. J. Jenghis Khan. Berlin and Moscow, 1922.
- Wang, Peng, Baowen Xu, Yurong Wu, and Xiaoyu Zhou. “Link Prediction in Social Networks: the State-of-the-Art.” arXiv, November 19, 2014. https://arxiv.org/abs/1411.5118.
| 1 | Johanna Barzen, “From Digital Humanities to Quantum Humanities: Potentials and Applications,” in Quantum Computing in the Arts and Humanities, ed. Eduardo Reck Miranda (Cham: Springer, 2022). 1-10 |
| 2 | Douglas MacArthur, A Soldier Speaks: Public Papers and Speeches of General of the Army Douglas MacArthur (New York: Praeger, 1965). |
| 3 | Jose Hernandez, “Comparing Russian and American Military Studies on the Lessons of Mongol Military Art Utilizing Network Analysis and Close Readings” (University of Chicago, 2022). 15-18 |
| 4 | Hernandez, “Comparing Russian and American Military Studies.”5-12 |
| 5 | Hernandez, “Comparing Russian and American Military Studies.”47-48 |
| 6 | Chris Bellamy. “Heirs of Genghis Khan: The Influence of the Tartar-Mongols on the Imperial Russian and Soviet Armies.” RUSI Journal 128, no. 1 (1983): 52–60. |
| 7 | Bellamy, “Heirs of Genghis Khan.” 56-57 |
| 8 | Hernandez, “Comparing Russian and American Military Studies.”5-12 |
| 9 | Radhika Dileep P. and Deepthi L. R., “Link Prediction in Citation Networks: A Survey,” in Proceedings of the 2022 Third International Conference on Intelligent Computing Instrumentation and Control Technologies (ICICICT) (Kannur, India, 2022), 1194–1200. |
| 10 | Radhika and Deepthi, “Link Prediction in Citation Networks” 1195 |
| 11 | Radhika and Deepthi, “Link Prediction in Citation Networks” 1196 |
| 12 | Radhika and Deepthi, “Link Prediction in Citation Networks” 1198 |
| 13 | Peng Wang, Baowen Xu, Yurong Wu, and Xiaoyu Zhou, “Link Prediction in Social Networks: the State-of-the-Art,” arXiv, November 19, 2014. |
| 14 | The initial Russian works in the network: 1)M. I. Ivanin, O voennom iskusstve i zavoevaniiakh mongolo-tartar i sredneaziatskikh narodov pri Chingiskhane i Tamerlane [On the Military Art and Conquests of the Tartar-Mongols and Central Asian Peoples under Genghis-Khan and Tamerlane] (Saint Petersburg, 1875). 2)A. Svechin, Strategi͡a [Strategy] (Moscow: Gos. voennoe izd-vo, 1926). 3) E. Khara-Davan, Chingis-Khan kak polkovodet͡s i ego nasledie: Kulʹturno-istoricheskiĭ ocherk Mongolʹskoĭ imperii XII-XIV veka [Genghis Khan: A Military Commander and His Legacy] (Izd. avtora, 1929). |
| 15 | Ivanin, On the Military Art and Conquests of the Tartar-Mongols. 10-20 |
| 16 | N. P. Mikhnevich, Istorīi︠a︡ voennago iskusstva sʺ drevni︠e︡ĭ shikh vremen do nachala deviatnadtsatago stolietīi︠a︡ [History of Military Art from Ancient Times to the Beginning of the Nineteenth Century] (S.-Peterburg: Leshtukovskai︠a︡ skoropechatni︠a︡ P.O. I︠A︡blonskago, 1895). |
| 17 | Svechin, Strategy.147-149 |
| 18 | Khara-Davan, Genghis Khan: A Military Commander and His Legacy.167-200 |
| 19 | Hernandez, “Comparing Russian and American Military Studies.”36-41 |
| 20 | The initial American works in the network:1) Glenn H. Takemoto, Back Azimuth Check: A Look at Mongol Operational Warfare (Fort Leavenworth, KS: School of Advanced Military Studies, 1992). 2) W. S. Taylor, Genghis Khan: Leadership for the Airland Battle (Maxwell AFB, AL: Air Command and Staff College, 1988). 3) Richard D. McCreight, The Mongol Warrior Epic: Masters of Thirteenth Century Maneuver Warfare (Fort Leavenworth, KS: U.S. Army Command and General Staff College, 1983). 4)D. C. Benfield, The Mongols: Early Practitioners of Maneuver Warfare (Fort Leavenworth, KS: U.S. Army Command and General Staff College, 2012) 5)Dana Pittard, Thirteenth Century Mongol Warfare: Classical Military Strategy or Operational Art (Fort Leavenworth, KS: U.S. Army Command and General Staff College, 1994). |
| 21 | McCreight, The Mongol Warrior Epic.140-148 |
| 22 | Taylor, Genghis Khan: Leadership for the Airland Battle.6-18 |
| 23 | Takemoto, Back Azimuth Check. Benfield, The Mongols: Early Practitioners of Maneuver Warfare.Pittard, Thirteenth Century Mongol Warfare.22-35 |
| 24 | Hernandez, “Comparing Russian and American Military Studies.”15-24 |
| 25 | H. Lamb, Genghis Khan, the Emperor of All Men (New York: R. M. McBride, 1927). |
| 26 | Hernandez, “Comparing Russian and American Military Studies.”Appendix- Diagram 1 |
| 27 | Hernandez, “Comparing Russian and American Military Studies.”23-24 |
| 28 | Hernandez, “Comparing Russian and American Military Studies.”41-43 |
| 29 | Hernandez, “Comparing Russian and American Military Studies.”47-48 |
| 30 | W. Barthold, Turkestan Down to the Mongol Invasion, 2nd ed. (Oxford: Clarendon Press, 1928), English translation of V. V. Barthold, Turkestan v epokhu mongolʹskago nashestvija (St. Petersburg, 1898). |
| 31 | ʻAlāʾ al-Dīn ʻAta-Malik Juvaynī, Genghis Khan: The History of the World Conqueror, trans. Steven Runciman (Seattle: University of Washington Press, 1997).; Igor de Rachewiltz, The Secret History of the Mongols: A Mongolian Epic Chronicle of the Thirteenth Century (Leiden: Brill, 2004). |
| 32 | For a thorough introduction to quantum computing we recommend: Chris Bernhardt, Quantum Computing for Everyone (Cambridge, MA: MIT Press, 2019). |
| 33 | Feng Xia, Jiaying Liu, Hansong Nie, Yonghao Fu, Liangtian Wan, and Xiangjie Kong, “Random Walks: A Review of Algorithms and Applications,” IEEE Transactions on Emerging Topics in Computational Intelligence 4, no. 2 (April 2020): 95–107. |
| 34 | J. Kempe, “Quantum Random Walks: An Introductory Overview,” Contemporary Physics 44, no. 4 (July 2003): 307–327, . |
| 35 | Kempe, “Quantum Random Walks.”312-314 |
| 36 | IBM Quantum, “Qiskit,” IBM, accessed January 14, 2026, https://www.ibm.com/quantum/qiskit . |
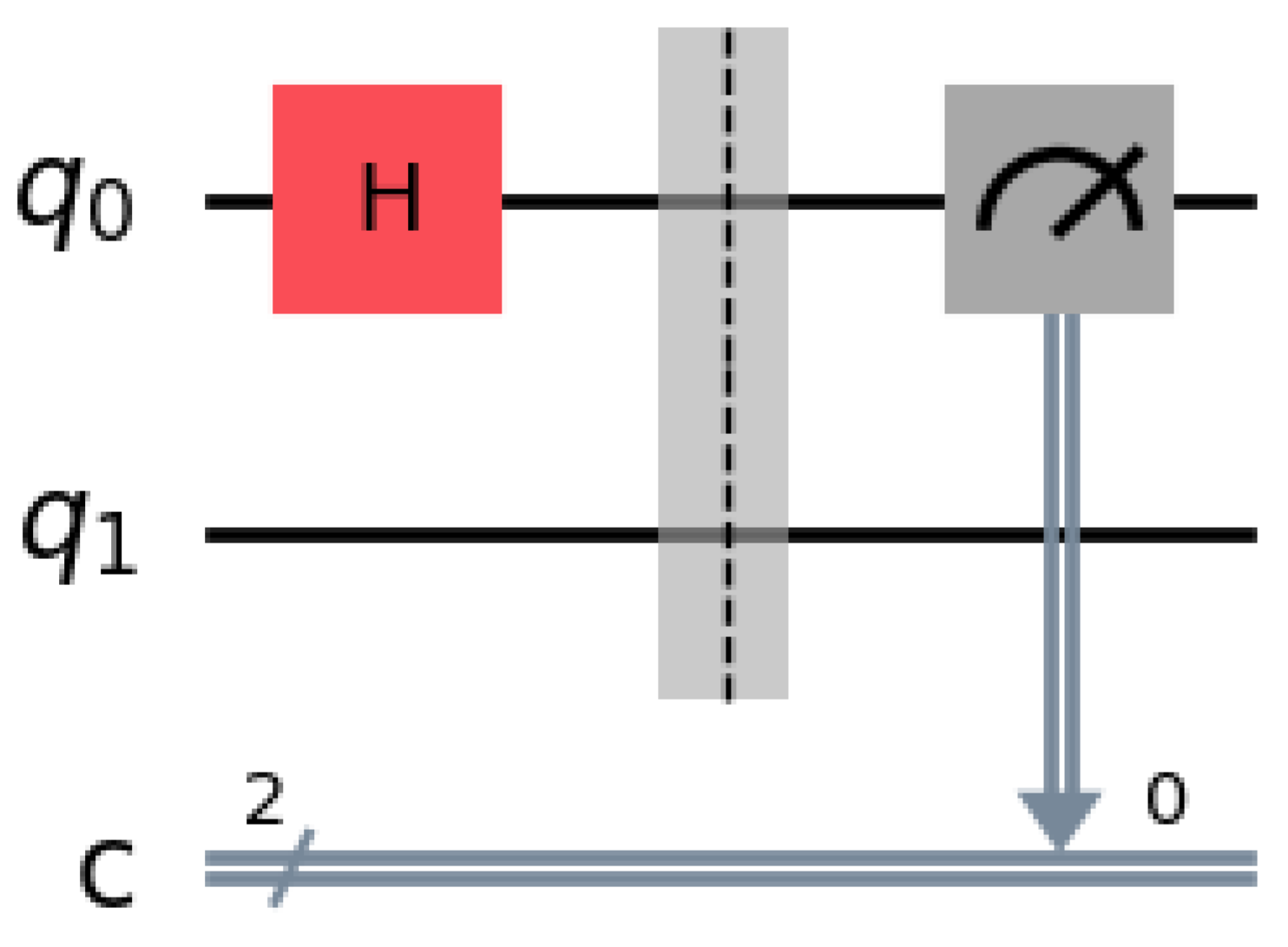
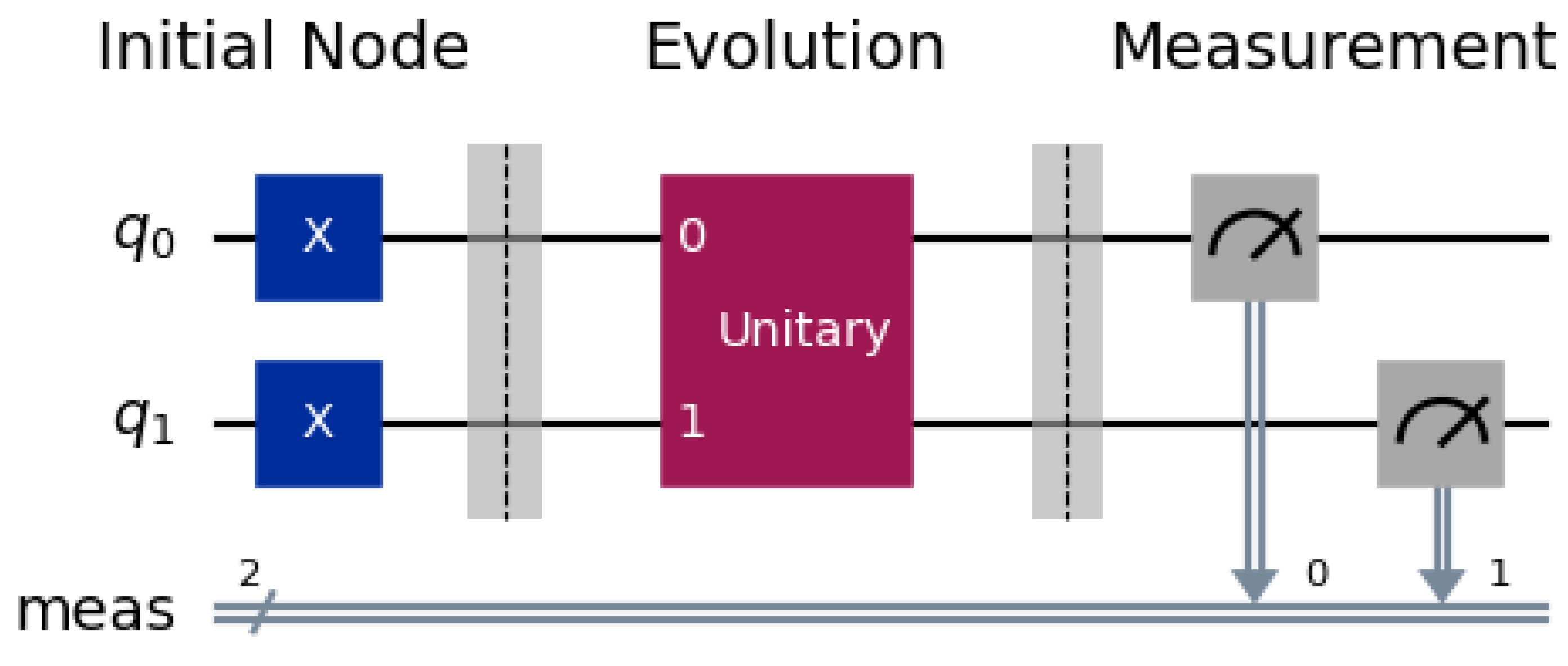
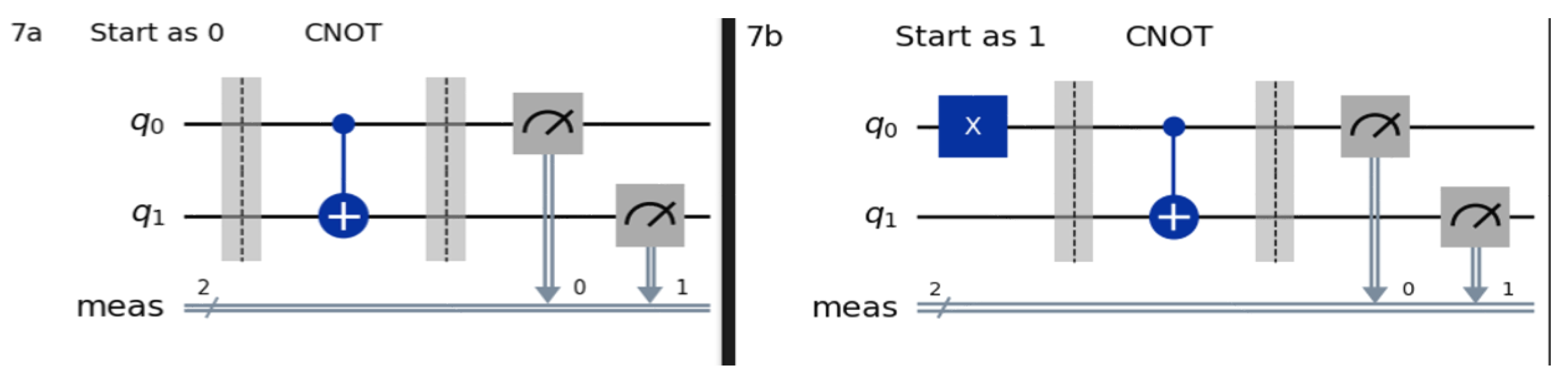
| 37 | IBM Quantum, “Bits, Gates, and Circuits,” IBM Quantum Learning, accessed January 14, 2026, https://quantum.cloud.ibm.com/learning/en/courses/utility-scale-quantum-computing/bits-gates-and-circuits. . |
| 38 | IBM Quantum, “Bits, Gates, and Circuits.” |
| 39 | 310 = 112 |
| 40 | IBM Quantum, “Bits, Gates, and Circuits.” |
| 41 | NetworkX Developers. NetworkX Documentation. Release 3.6.1. Accessed December 21, 2025. https://networkx.org/documentation/stable/index.html. |
| 42 | Ivanin, On the Military Art and Conquests of the Tartar-Mongols. 10-20 |
| 43 | Lamb, Genghis Khan, the Emperor of All Men. 250-256 |
| 44 | B. J. Vladimirtzov, Jenghis Khan (Berlin and Moscow, 1922). |
| 45 | Vladimirtzov, Jenghis Khan.xi-xiii |
| 46 | Barthold, Turkestan at the Time of the Mongol Invasion. |
| 47 | John Preskill, “Quantum Computing in the NISQ Era and Beyond,” Quantum 2 (August 2018): 79, https://doi.org/10.22331/q-2018-08-06-79. |
| 48 | João P. Moutinho, André Melo, Bruno Coutinho, István A. Kovács, and Yasser Omar, “Quantum Link Prediction in Complex Networks,” arXiv, December 9, 2021, . |
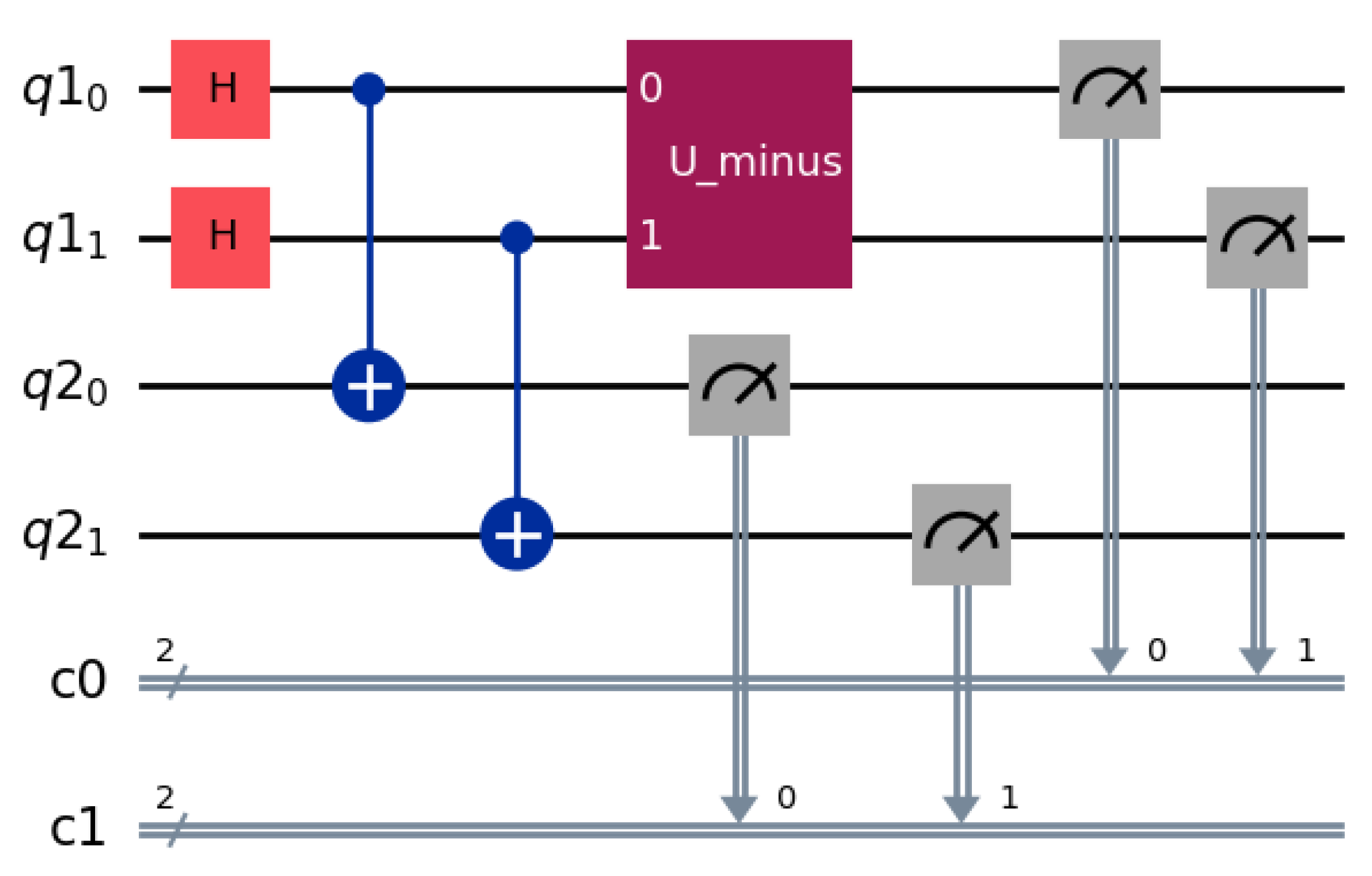
| 49 | Moutinho et al., “Quantum Link Prediction in Complex Networks.”4-7 |
| 50 | João P. Moutinho, Duarte Magano, and Bruno Coutinho, “On the Complexity of Quantum Link Prediction in Complex Networks,” Scientific Reports 14 (2024): 1026. |
| 51 | Moutinho, Magano, and Coutinho, “On the Complexity of Quantum Link Prediction.” 5-8 |
| 52 | Hernandez, Jose, QRW-HistoryCitation: Quantum Random Walks Applied in Qiskit to a Historical Citation Network, GitHub repository, last modified 2025, https://github.com/hernandezj1/QRW-HistoryCitation. |
| 53 | IBM, “IBM Launches Its Most Advanced Quantum Computers, Fueling New Scientific Value and Progress towards Quantum Advantage,” IBM Newsroom, November 13, 2024, |
| 54 | Hernandez, QRW-HistoryCitation. |
| 55 | IBM Quantum, “Fractional Gates,” IBM Quantum Documentation, accessed January 14, 2026, https://quantum.cloud.ibm.com/docs/en/guides/fractional-gates . |
| 56 | Estimated at 1-5 year range depending on manufacturer timeline for quantum hardware and their modalities. |
| 57 | Hernandez, Jose, QuantumRandomWalks, Python package, PyPI, last updated September 22, 2025 |
| 58 | Hernandez, QuantumRandomWalks. |
| 59 | Hernandez, QuantumRandomWalks. |
| Time Step | Node 0 | Node 1 | Node 2 | Node 3 |
| 0 | 0 | 0 | 0 | 1 |
| 0.5 | 0.057617 | 0.164063 | 0.205078 | 0.573242 |
| 1 | 0.511719 | 0.213867 | 0.188477 | 0.085938 |
| 1.5 | 0.988281 | 0.003906 | 0.007813 | 0 |
| 2 | 0.688477 | 0.150391 | 0.139648 | 0.021484 |
| Node 0 | Node 1 | Node 2 | Node 3 | |
| Maximum Probability | 0.988281 | 0.213867 | 0.205078 | 1 |
| Average Probability | 0.449219 | 0.106445 | 0.108203 | 0.336133 |
| Time | 0-3 | 2-1 |
| 0 | 0 | 0 |
| 0.5 | 0.015625 | 0.019531 |
| 1 | 0.117188 | 0.115234 |
| 1.5 | 0.241211 | 0.242188 |
| 2 | 0.163086 | 0.183594 |
| Final node | Maximum Probability | Average Probability |
| 7 | 0.152344 | 0.047705 |
| 8 | 0.307617 | 0.111963 |
| 10 | 0.499023 | 0.170557 |
| 13 | 0.533203 | 0.166846 |
| 25 | 0.282227 | 0.102197 |
| Link | Maximum Probability | Average Probability |
| 7-10 | 0.008789 | 0.001318 |
| 12-14 | 0.007813 | 0.001367 |
| 0-11 | 0.006836 | 0.001123 |
| 13-7 | 0.006836 | 0.001611 |
| 13-46 | 0.006836 | 0.001221 |
| Link | Work 1 | Work 2 |
| 7-10 | “Emperor of All Men” by Harold Lamb |
“Genghis Khan as Military Commander and His Legacy” by Erenzhen Khara Divan |
| 12-14 | “Thirteenth Century Mongol Warfare; Classical Military Strategy or Operational Art?” by Dana Pittard | “The Mongols: Early Practitioners of Maneuver Warfare” by Darrel Benfield |
| 0-11 | “Genghis Khan: Leadership for the Airland Battle” by William Taylor |
“The Mongol Warrior Epic: Masters of thirteenth Centruy Maneuver Warfare” by Richard D. McCreight |
| 13-7 | “Heirs of Genghis Khan: The Influence of the Tartar-Mongols on the Imperial Russian and Soviet Armies” by Christopher Bellamy | “Emperor of All Men” by Harold Lamb |
| 13-46 | “Heirs of Genghis Khan: The Influence of the Tartar-Mongols on the Imperial Russian and Soviet Armies” by Christopher Bellamy | “The Secret History of the Mongols” |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




