Submitted:
27 February 2026
Posted:
28 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Phase1 (Modeling): We develop the conceptual model of the core elements that constitute a CR. This includes translating widely used classifications and design aspects into a unified and computationally interpretable ontology that defines a common language for describing CRs in a consistent and unambiguous manner.
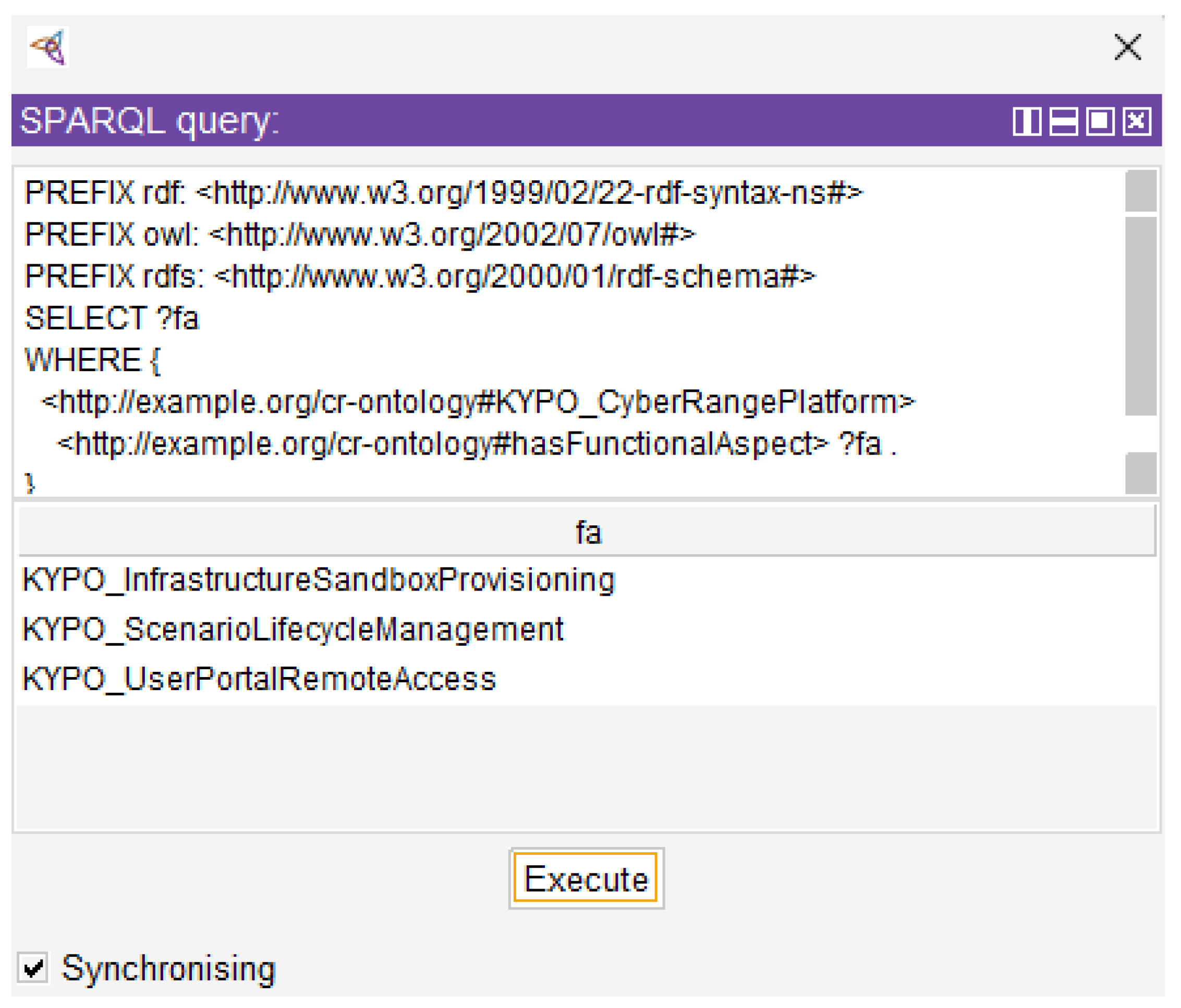
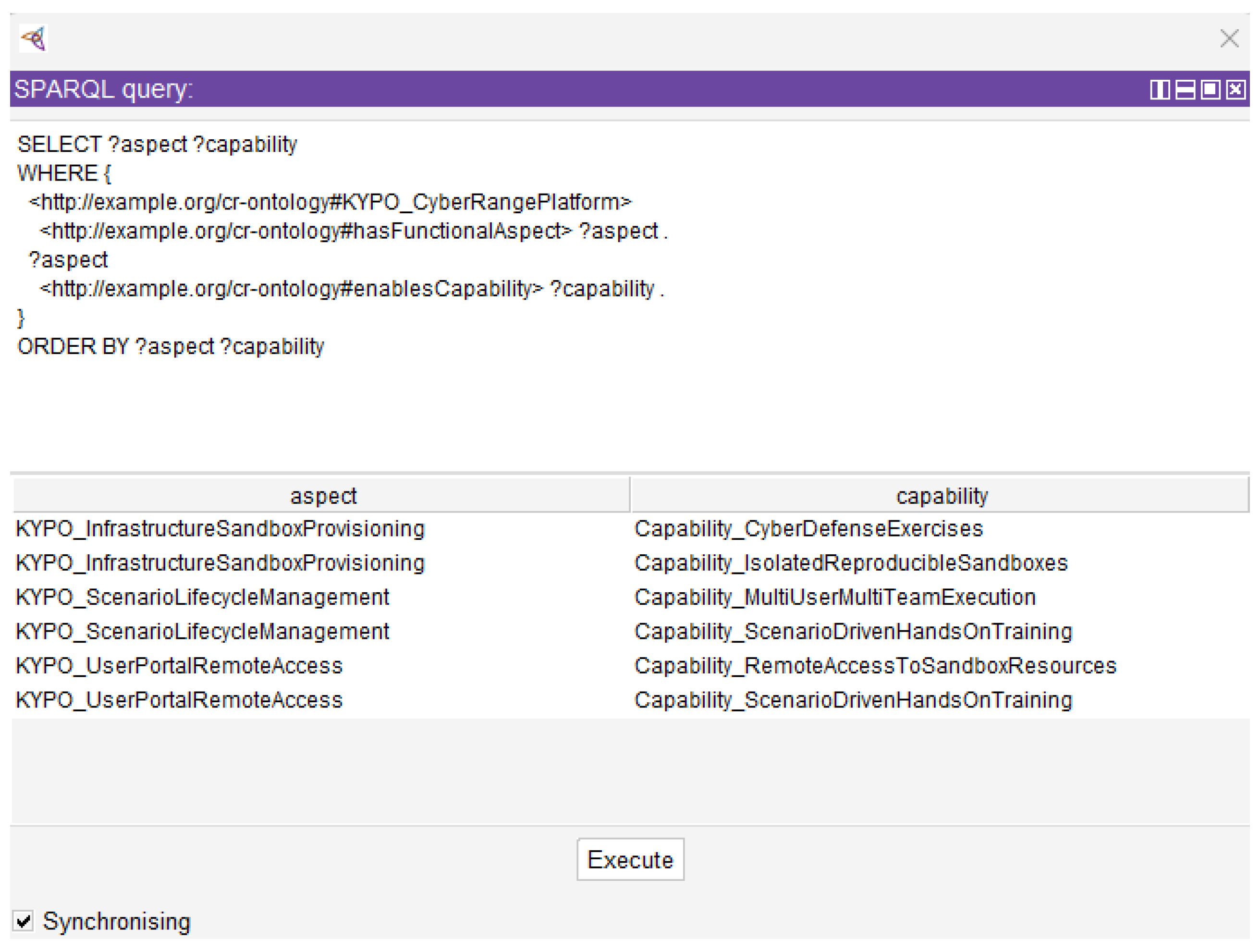
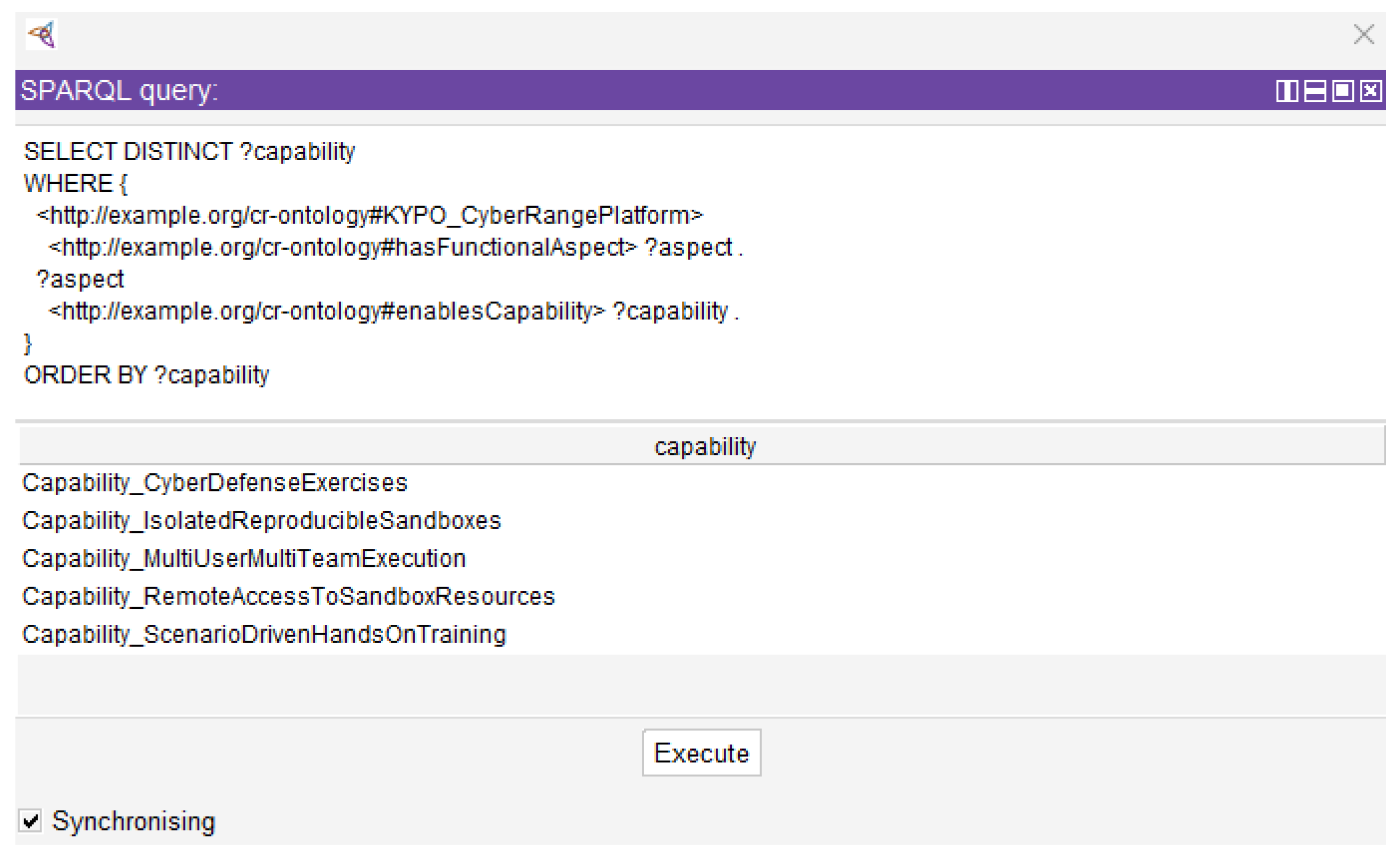
- Phase2 (Implementation): We implement the proposed conceptual model using Protégé [16] and formalize it in Resource Description Framework (RDF) and Extensible Markup Language (XML) formats, thereby producing a structured ontology that captures the relationships, dependencies, and compositional structures among the various design parameters of CRs. This implementation supports structured analysis, enhances transparency, and enables more informed and explainable decision-making during the CR design and evaluation process.
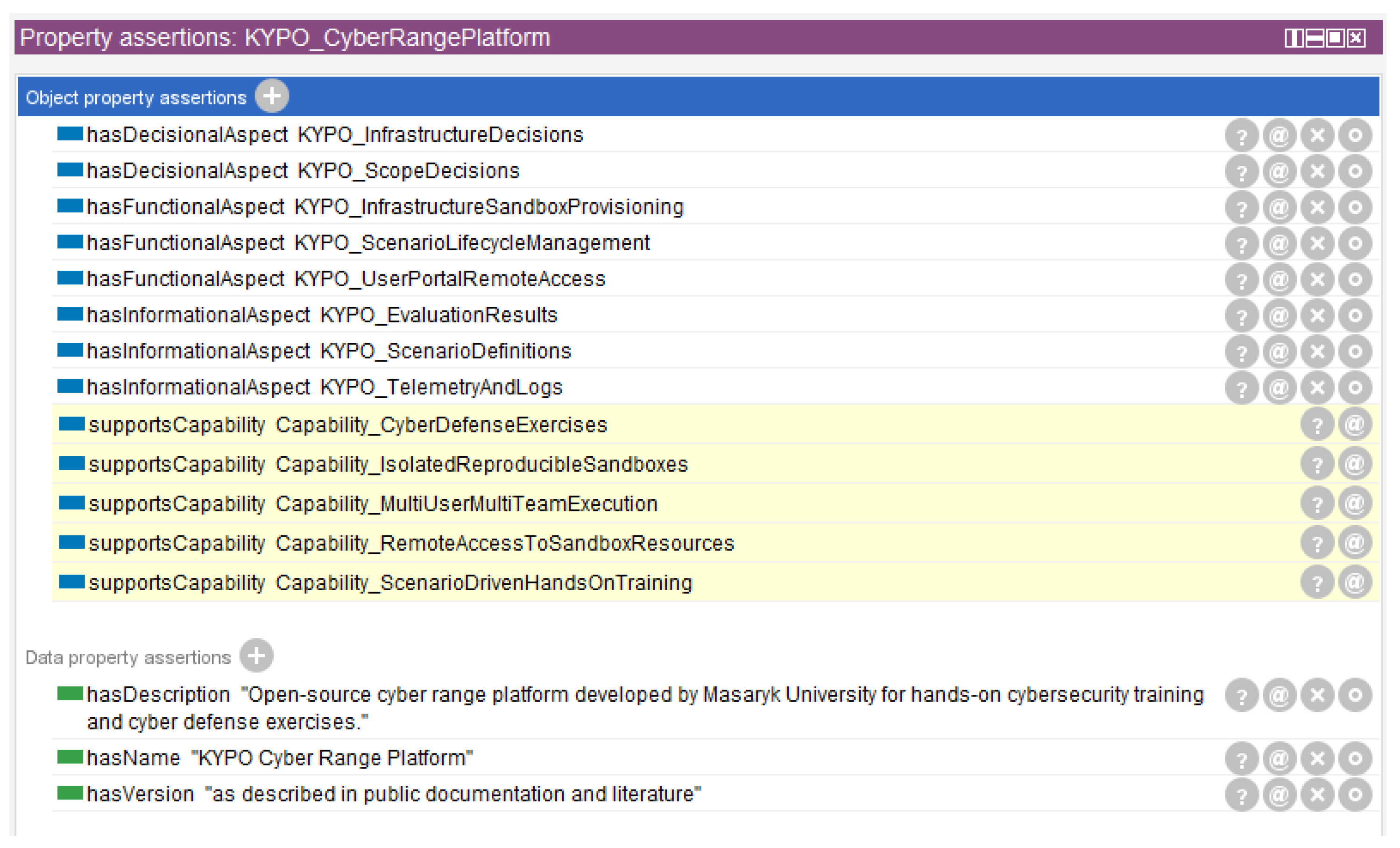
- Phase3 (Validation): We validate the proposed ontology through an indicative CR [17], demonstrating how the multi-layer modeling approach, which distinguishes between descriptive, operational, and capability-related aspects, provides a holistic and interpretable representation of CR ecosystems. This validation highlights the ontology’s ability to facilitate comparability and repeatability across heterogeneous CR platforms and use cases.
2. Related Work
3. Background
3.1. Cyber Ranges
3.2. Ontologies
- Provide a shared and common understanding of structured information among HitL and machines or software agents.
- Support the reuse of domain knowledge across applications and systems.
- Enable interoperability among heterogeneous models and domain-specific vocabularies.
- Facilitate and simplify communication among HitL, computational systems, and between them.
- Offer expressive capabilities for capturing contextual knowledge from diverse and heterogeneous sources.
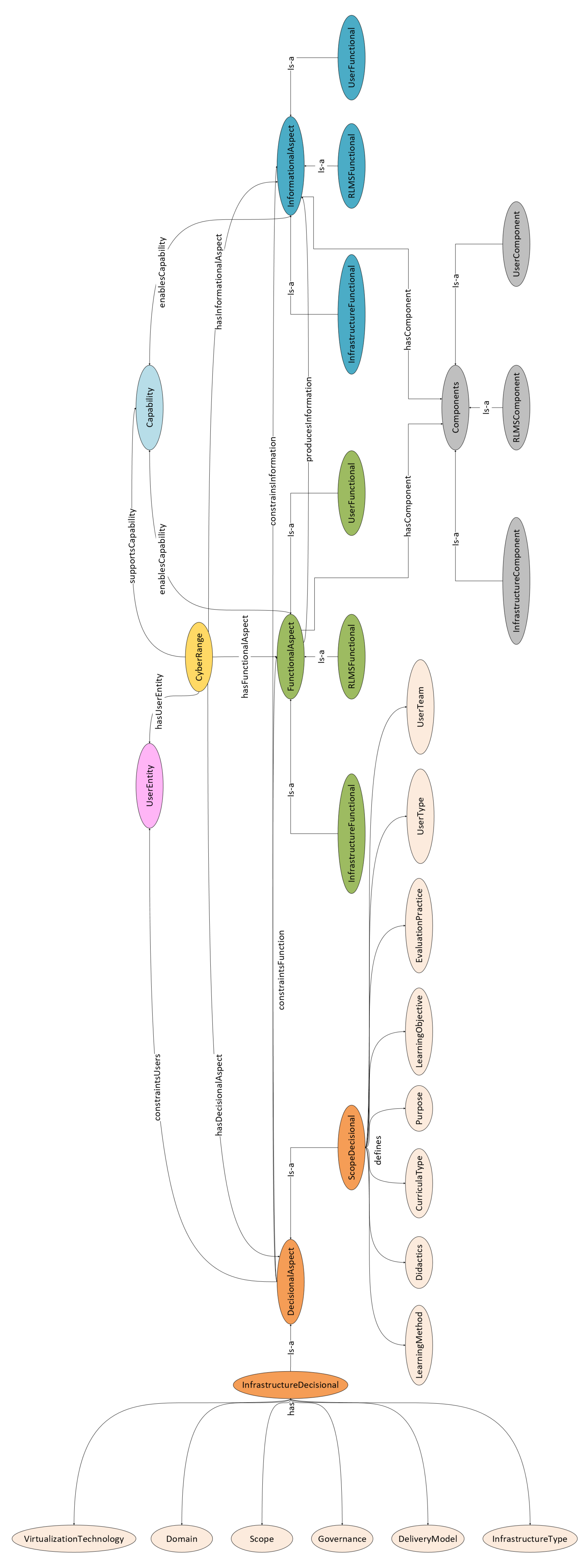
4. Ontology Model
4.1. Modeling Scope
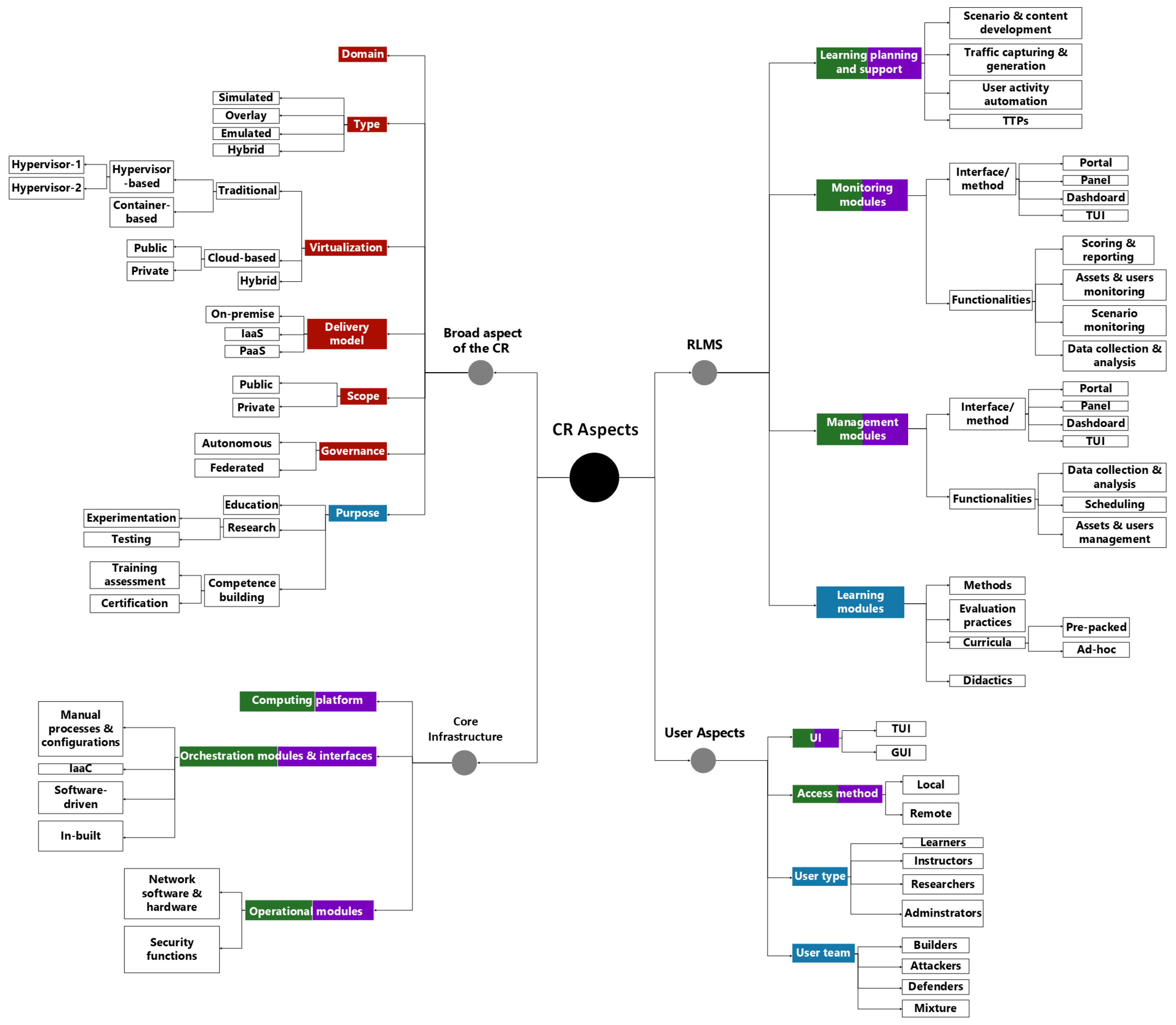
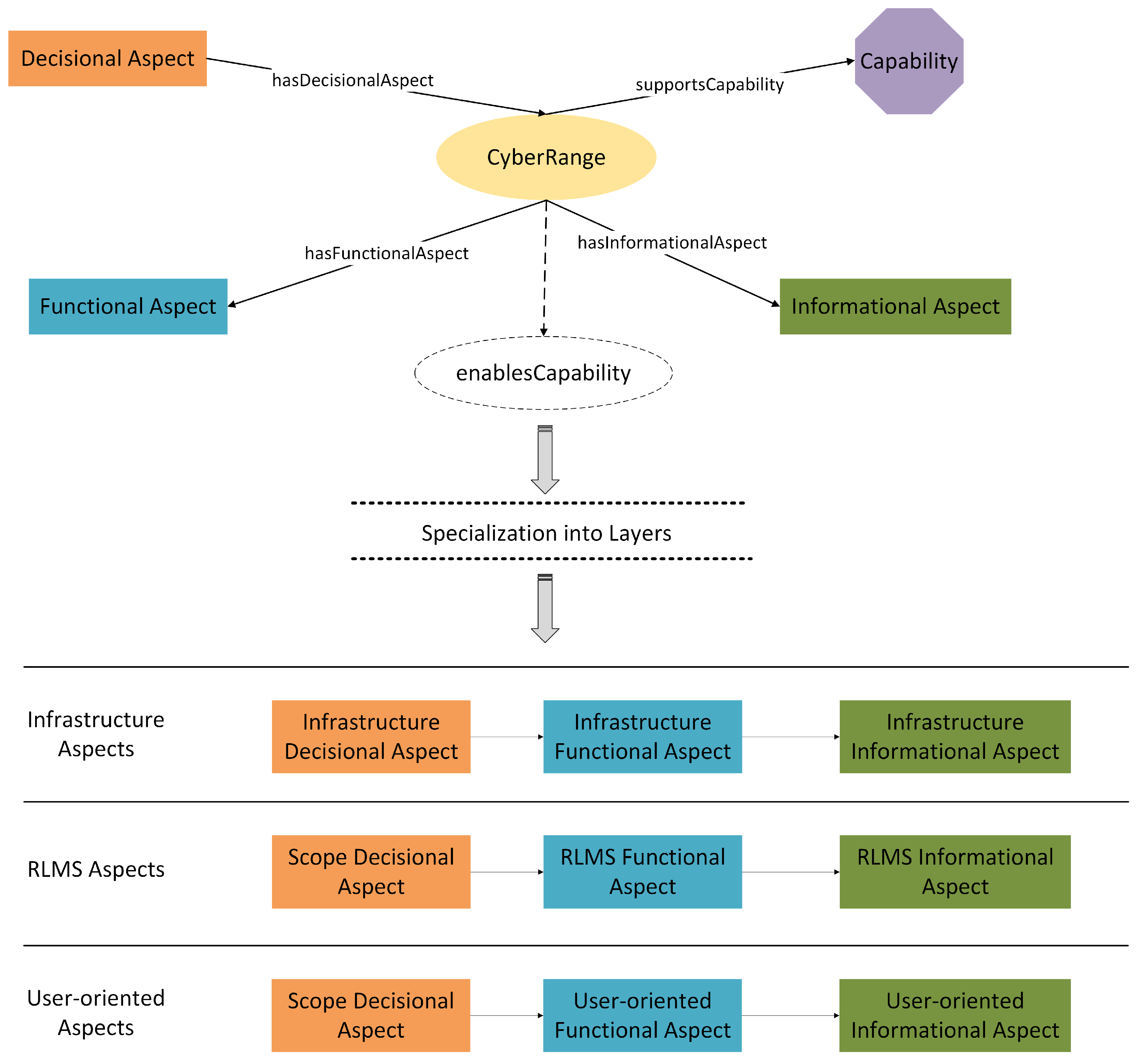
- Decisional aspects: They represent strategic, organizational, and architectural choices made at early CR design stages. In this sense, they define the purpose, scope, and constraints of the CR, including decisions related to infrastructure, including the delivery model, governance, and virtualization technologies, as well as decisions regarding the CR scope, such as target audience, pedagogical objectives, and evaluation practices. Collectively, decisional aspects condition and influence all subsequent functional and informational elements of the CR.
- Functional aspects: They capture the operational behaviors, services, and mechanisms provided by the CR to realize its intended objectives, as defined by the decisional aspects. Specifically, this class of aspects describes what the CR does at runtime, including functionalities such as simulation and emulation, orchestration and automation, monitoring, learning management, and user interaction.
- Informational aspects: They describe the data-centric dimension of the CR, encompassing the information objects that are generated, consumed, processed, or stored during its operation. Typical informational elements include scenarios, configuration artifacts, logs, telemetry data, learning content, and evaluation results. Keep in mind that informational aspects are explicitly linked to the functional aspects that produce or consume them.
- Capabilities: They express higher-level competencies enabled by the CR through the combined realization of decisional, functional, and informational aspects. Rather than referring to individual components or services, capabilities designate what the CR is able to support (e.g., attack simulation, defensive training, or incident response evaluation).
4.2. Model Design
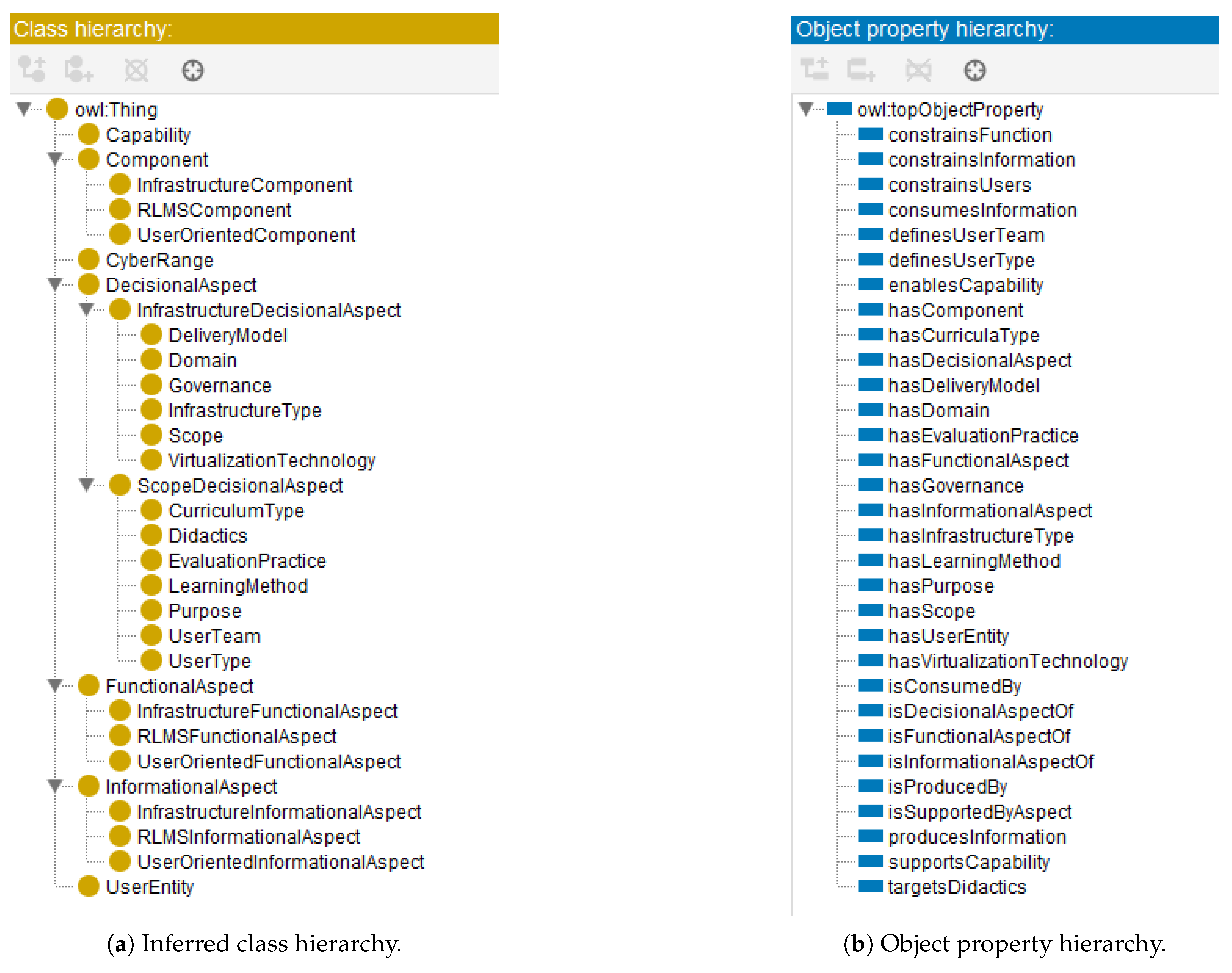
4.2.1. Classes (Concepts)
- DecisionalAspect: Represents high-level architectural and strategic decisions made during CR conception, such as technology selection or CR focus.
- FunctionalAspect: Encapsulates runtime behaviors, services, and technical modules that operationalize the CR’s objectives (e.g., monitoring, automation).
- InformationalAspect: Covers the data-related artifacts involved in the CR, including configurations, telemetry, logs, or learning content.
-
InfrastructureFunctionalAspect, RLMSFunctionalAspect,UserOrientedFunctionalAspect
-
InfrastructureInformationalAspect, RLMSInformationalAspect,UserOrientedInformationalAspect
- InfrastructureDecisionalAspect: Includes choices like virtualization technology, infrastructure type, or delivery model.
- ScopeDecisionalAspect: Covers decisions regarding pedagogical strategies, user types, curricula, and evaluation methods.
-
Component: A generic abstraction for tangible software or infrastructure elements, further specialized as InfrastructureComponent, RLMSComponent, andUserOrientedComponent.
- UserEntity: Represents human actors or groups participating in the CR, with common roles such as Trainee, Instructor, and Team.
4.2.2. Properties (Relationships)
4.2.3. Axioms (Constraints)
4.2.4. Summary of Ontology Elements
5. Implementation
- Consistency checking: The reasoner automatically detects violations of disjointness axioms, domain and range constraints, and cardinality restrictions.
- Structural completeness: The reasoner verifies that each CyberRange instance satisfies minimum cardinality requirements, ensuring the presence of decisional, functional, and informational aspects as mandated by the ontology model introduced in Section 4.
- Implicit classification: The reasoner infers class memberships based on asserted object property relations and their declared domain and range constraints.
- Capability inference: The reasoner applies property-chain axiom 1 to propagate enabled capabilities from functional aspects to the corresponding CyberRange instance.
- Constraint enforcement: The reasoner ensures that decisional aspects semantically constrain admissible functional and informational realizations, maintaining coherence between design-time decisions and runtime behavior.
6. Validation
7. Limitations & Future Work
- Abstraction Level. The ontology is conceptualized and instantiated at a domain abstraction level and does not capture low-level implementation details of specific CR platforms. Namely, it models architectural, functional, informational, and decisional aspects in a technology-agnostic manner. Consequently, highly platform-specific configurations, deployment scripts, infrastructure-as-code artifacts, or detailed runtime orhestration logic are intentionally abstracted. This design choice enhances generalizability and cross-platform comparability, but it limits direct operational automation or platform-level configuration assembly without additional extensions. In this context, future research may focus on extending the ontology with optional implementation-level modules that align CR functional aspects with concrete deployment descriptors (e.g., container orchestration manifests, virtualization templates, or network configuration schemas). Such extensions could facilitate automation of CR deployment workflows while preserving the abstraction principles of the existing ontology.
- Expressiveness Boundaries. Although the ontology conforms to the OWL 2 DL, supporting decidable reasoning, its expressive power is bounded by DL semantics. That is, complex procedural constraints, dynamic workflows, temporal sequencing of CR activities, or conditional logic between events beyond the native representational scope of DL-based ontologies. Such behaviors would require rule-based extensions (e.g., SWRL) or integration with process-oriented formalisms. Future extensions may investigate the integration of rule-based reasoning mechanisms or alignment with process modeling frameworks (e.g., BPMN-derived ontologies or temporal logics) to represent dynamic CR workflows and event-driven behavior.
- Absence of Quantitative Evaluation Modeling. The ontology emphasizes structural and semantic relationships rather than quantitative evaluation metrics. Performance indicators, scalability measurements, resource utilization metrics, or detailed learning analytics are not formally encoded beyond optional datatype annotations. As a result, quantitative assessment of CR effectiveness remains outside the current modeling scope. Future research may incorporate dedicated evaluation and performance modeling modules, potentially through alignment with metric-oriented ontologies, learning analytics vocabularies, or evaluation formulas, such as the ones introduced in [14]. Such extensions would help the formal representation of CR attributes and support maturity assessment and benchmarking across heterogeneous platforms.
- Structural Capability Inference. Capability inference is currently based on structural composition through property-chain axioms, as highlighted in the property-chain axiom 1. This mechanism supports automated classification and traceability, however, it does not evaluate the qualitative adequacy, performance level, or maturity of the supported capability. Therefore, the ontology determines whether a capability is structurally supported, but not the degree to which it is effectively realized. Future work may explore the incorporation of graded or weighted capability models, integrating qualitative assessment criteria or maturity-level ontologies. Such enhancements could allow reasoning not only about capability presence but also about capability quality, effectiveness, or operational readiness.
- Scope of Empirical Validation. While current validation confirms logical consistency and structural integrity through an illustrative case-study instantiation, broader empirical validation across heterogeneous CR deployments would further strengthen the versatility of the proposed model. Although the selected CR platform provides a representative and well-documented example, future validation efforts may involve instantiating the ontology across multiple CR platforms with diverse architectural paradigms and conducting comparative capability analyses.
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| API | Application Programming Interface |
| CI | Critical Infrastructures |
| CPS | Cyber-Physical Systems |
| CR | Cyber Ranges |
| CQ | Competency Questions |
| CtF | Capture-the-Flag |
| CyRIS | Cyber Range Instantiation System |
| DL | Description Logic |
| DSL | Domain-Specific Language |
| HitL | Humans-in-the-Loop |
| IT | Information Technology |
| IaC | Infrastructure-as-Code |
| LLMs | Large Language Models |
| OWL | Web Ontology Language |
| RAG | Retrieval-Augmented Generation |
| RDF | Resource Description Framework |
| RLMS | Range Learning and Management System |
| SDL | Scenario Definition Language |
| SWRL | Semantic Web Rule Language |
| XML | Extensible Markup Language |
References
- Makrakis, G.M.; Kolias, C.; Kambourakis, G.; Rieger, C.; Benjamin, J. Industrial and Critical Infrastructure Security: Technical Analysis of Real-Life Security Incidents. IEEE Access 2021, 9, 165295–165325. [Google Scholar] [CrossRef]
- Kampourakis, V.; Gkioulos, V.; Katsikas, S. A systematic literature review on wireless security testbeds in the cyber-physical realm. Computers & Security 2023, 133, 103383. [Google Scholar] [CrossRef]
- Falliere, N.; Murchu, L.O.; Chien, E.; et al. W32. stuxnet dossier. White paper, symantec corp., security response 2011, 5, 29. [Google Scholar]
- Kozak, P.; Klaban, I.; Šlajs, T. Industroyer cyber-attacks on Ukraine’s critical infrastructure. In Proceedings of the 2023 International Conference on Military Technologies (ICMT), 2023; pp. 1–6. [Google Scholar] [CrossRef]
- Salazar, L.; Castro, S.R.; Lozano, J.; Koneru, K.; Zambon, E.; Huang, B.; Baldick, R.; Krotofil, M.; Rojas, A.; Cardenas, A.A. A Tale of Two Industroyers: It was the Season of Darkness. In Proceedings of the 2024 IEEE Symposium on Security and Privacy (SP), 2024; pp. 312–330. [Google Scholar] [CrossRef]
- Datta, P. Hannibal at the gates: Cyberwarfare & the Solarwinds sunburst hack. Journal of Information Technology Teaching Cases 2022, 12, 115–120. [Google Scholar]
- Kampourakis, V.; Kavallieratos, G.; Gkioulos, V.; Katsikas, S. Cracks in the chain: A technical analysis of real-life supply chain security incidents. Computers & Security 2025, 159, 104673. [Google Scholar] [CrossRef]
- Beerman, J.; Berent, D.; Falter, Z.; Bhunia, S. A Review of Colonial Pipeline Ransomware Attack. In Proceedings of the 2023 IEEE/ACM 23rd International Symposium on Cluster, Cloud and Internet Computing Workshops (CCGridW), 2023; pp. 8–15. [Google Scholar] [CrossRef]
- Kampourakis, V.; Gkioulos, V.; Katsikas, S. A step-by-step definition of a reference architecture for cyber ranges. Journal of Information Security and Applications 2025, 88, 103917. [Google Scholar] [CrossRef]
- Kampourakis, V. Secure Infrastructure for Cyber-Physical Ranges. Proceedings of the Research Challenges in Information Science: Information Science and the Connected World 2023, 622–631. [Google Scholar] [CrossRef]
- Katsantonis, M.N.; Manikas, A.; Mavridis, I.; Gritzalis, D. Cyber range design framework for cyber security education and training. International Journal of Information Security 2023, 22, 1005–1027. [Google Scholar] [CrossRef]
- Yamin, M.M.; Katt, B.; Gkioulos, V. Cyber ranges and security testbeds: Scenarios, functions, tools and architecture. Computers & Security 2020, 88, 101636. [Google Scholar] [CrossRef]
- Ukwandu, E.; Farah, M.A.B.; Hindy, H.; Brosset, D.; Kavallieros, D.; Atkinson, R.; Tachtatzis, C.; Bures, M.; Andonovic, I.; Bellekens, X. A Review of Cyber-Ranges and Test-Beds: Current and Future Trends. Sensors 2020, 20. [Google Scholar] [CrossRef] [PubMed]
- Kampourakis, V.; Kavallieratos, G.; Spathoulas, G.; Gkioulos, V.; Katsikas, S. LLM-Assisted AHP for Explainable Cyber Range Evaluation. arXiv arXiv:2512.10487. [CrossRef]
- Wen, S.F.; Yamin, M.M.; Katt, B. Ontology-Based Scenario Modeling for Cyber Security Exercise. In Proceedings of the 2021 IEEE European Symposium on Security and Privacy Workshops (EuroS&PW), 2021; pp. 249–258. [Google Scholar] [CrossRef]
- University, S. Protégé: A free, open-source ontology editor and framework for building intelligent systems. 2016. Available online: https://protege.stanford.edu/.
- Vykopal, J.; Oslejsek, R.; Celeda, P.; Vizvary, M.; Tovarnak, D. KYPO Cyber Range: Design and Use Cases. In Proceedings of the Proceedings of the 12th International Conference on Software Technologies - ICSOFT. INSTICC, SciTePress, 2017; pp. 310–321. [Google Scholar] [CrossRef]
- Bernardinetti, G.; Iafrate, S.; Bianchi, G. Nautilus: A Tool For Automated Deployment And Sharing Of Cyber Range Scenarios. In Proceedings of the Proceedings of the 16th International Conference on Availability, Reliability and Security, New York, NY, USA, 2021; ARES ’21. [Google Scholar] [CrossRef]
- Pham, C.; Tang, D.; Chinen, K.i.; Beuran, R. CyRIS: a cyber range instantiation system for facilitating security training. In Proceedings of the Proceedings of the 7th Symposium on Information and Communication Technology, New York, NY, USA, 2016; SoICT ’16, pp. 251–258. [Google Scholar] [CrossRef]
- Gallus, P.; Klaban, I.; Františ, P.; Šlajs, T. Modular Cybersecurity Scenario Development and Its Integration into the Cyber Range Platform. Proceedings of the 2025 Communication and Information Technologies (KIT) 2025, 1–6. [Google Scholar] [CrossRef]
- OWASP. OWASP Top Ten 2025. 2025. Available online: https://owasp.org/www-project-top-ten/.
- Russo, E.; Costa, G.; Armando, A. Building next generation Cyber Ranges with CRACK. Computers & Security 2020, 95, 101837. [Google Scholar] [CrossRef]
- OASIS. OASIS Topology and Orchestration Specification for Cloud Applications (TOSCA) TC. 2025. Available online: https://www.oasis-open.org/committees/tc_home.php?wg_abbrev=tosca.
- Gustafsson, T.; Almroth, J. Cyber Range Automation Overview with a Case Study of CRATE. In Proceedings of the Secure IT Systems; Asplund, M., Nadjm-Tehrani, S., Eds.; Cham, 2021; pp. 192–209. [Google Scholar] [CrossRef]
- Yamin, M.M.; Katt, B. Modeling and executing cyber security exercise scenarios in cyber ranges. Computers & Security 2022, 116, 102635. [Google Scholar] [CrossRef]
- Mudassar Yamin, M.; Hashmi, E.; Ullah, M.; Katt, B. Applications of LLMs for Generating Cyber Security Exercise Scenarios. IEEE Access 2024, 12, 143806–143822. [Google Scholar] [CrossRef]
- Gruber, T.R. A translation approach to portable ontology specifications. Knowledge Acquisition 1993, 5, 199–220. [Google Scholar] [CrossRef]
- Wand, Y.; Storey, V.C.; Weber, R. An ontological analysis of the relationship construct in conceptual modeling. ACM Trans. Database Syst. 1999, 24, 494–528. [Google Scholar] [CrossRef]
- Uschold, M.; Gruninger, M. Ontologies: principles, methods and applications. The Knowledge Engineering Review 1996, 11, 93–136. [Google Scholar] [CrossRef]
- Horrocks, I.; Kutz, O.; Sattler, U. The Even More Irresistible SROIQ. Kr 2006, 6, 57–67. [Google Scholar]
- University, M. CyberRangeCZ Platform. 2020. Available online: https://docs.platform.cyberrange.cz/.
- Sapák, T. kypo-crp-tf-deployment. 2020. Available online: https://gitlab.ics.muni.cz/muni-kypo-crp/devops/kypo-crp-tf-deployment.
- Univeristy, M. KYPO CYBER RANGE PLATFORM. 2020. Available online: https://crp.kypo.muni.cz/.
- Švábenský, V.; Vykopal, J.; Seda, P.; Čeleda, P. Dataset of shell commands used by participants of hands-on cybersecurity training. Data in Brief 2021, 38, 107398. [Google Scholar] [CrossRef] [PubMed]
- Vykopal, J.; Vizvary, M.; Oslejsek, R.; Celeda, P.; Tovarnak, D. Lessons learned from complex hands-on defence exercises in a cyber range. In Proceedings of the 2017 IEEE Frontiers in Education Conference (FIE), 2017; pp. 1–8. [Google Scholar] [CrossRef]
- Makhlouf, A.; Percebois, C.; Tran, H.N. Two-Level Reasoning About Graph Transformation Programs. In Proceedings of the Graph Transformation; Guerra, E., Orejas, F., Eds.; Cham, 2019; pp. 111–127. [Google Scholar] [CrossRef]
| Ref. | Year | Focus | Scenario Modeling | Infr. Orch. | Knowledge Model | Coverage |
|---|---|---|---|---|---|---|
| [18] | 2021 | Exercise packaging & deployment | Y | Y | N | Partial |
| [19] | 2016 | CR instantiation automation | Y | Y | N | Partial |
| [20] | 2025 | IaC-based scenario deployment | Y | Y | N | Partial |
| [22] | 2020 | Declarative scenario specification (SDL) | Y | Y | N | Partial |
| [24] | 2021 | Automation survey & orchestration | N | Y | N | Limited |
| [25] | 2022 | Model-driven scenario automation | Y | Y | N | Partial |
| [26] | 2024 | LLM-assisted scenario generation | Y | N | N | Limited |
| [15] | 2021 | Scenario ontology modeling | Y | N | Y | Scenario-only |
| This Work | 2026 | Ontology-based CR engineering | Y | Y | Y | End-to-end |
| Element Type | Name | Description |
|---|---|---|
| Classes (Concepts) | ||
| Class | CyberRange | Root entity representing a complete CR instance |
| Class | DecisionalAspect | Abstract class for design-time decisions |
| Class | FunctionalAspect | Abstract class for runtime behaviors and services |
| Class | InformationalAspect | Abstract class for data artifacts and information objects |
| Class | Capability | Emergent competencies enabled by the CR |
| Class | Component | Abstract technical module implementing functional aspects |
| Class | UserEntity | Human actors participating in CR activities |
| Subclass | InfrastructureDecisionalAspect | Infrastructure-related design decisions |
| Subclass | ScopeDecisionalAspect | Pedagogical and audience-oriented decisions |
| Subclass | InfrastructureFunctionalAspect | Infrastructure-layer functionalities |
| Subclass | RLMSFunctionalAspect | RLMS-layer functionalities |
| Subclass | UserOrientedFunctionalAspect | User-facing services and mechanisms |
| Subclass | InfrastructureInformationalAspect | Infrastructure-generated data artifacts |
| Subclass | RLMSInformationalAspect | RLMS-related informational artifacts |
| Subclass | UserOrientedInformationalAspect | User-facing or user-generated artifacts |
| Subclass | InfrastructureComponent, RLMSComponent, UserOrientedComponent | Layer-specific component implementations |
| Controlled Classes | Governance, DeliveryModel, InfrastructureType, VirtualizationTechnology, Domain, Scope | Infrastructure decisional vocabularies |
| Controlled Classes | LearningMethod, EvaluationPractice, CurriculumType, Purpose, Didactics, UserType, UserTeam | Scope decisional vocabularies |
| Object Properties | ||
| Aggregation | hasDecisionalAspect / isDecisionalAspectOf | Links CR to decisional aspects (inverse defined) |
| Aggregation | hasFunctionalAspect / isFunctionalAspectOf | Links CR to functional aspects (inverse defined) |
| Aggregation | hasInformationalAspect / isInformationalAspectOf | Links CR to informational aspects (inverse defined) |
| Aggregation | supportsCapability | Declares capabilities supported by a CR |
| Dependency | constrainsFunction | DecisionalAspect → FunctionalAspect |
| Dependency | constrainsInformation | DecisionalAspect → InformationalAspect |
| Dependency | constrainsUsers | DecisionalAspect → UserEntity |
| Runtime Flow | producesInformation / consumesInformation | FunctionalAspect → InformationalAspect (inverse defined) |
| Capability Realization | enablesCapability / isSupportedByAspect | Functional/InformationalAspect → Capability (inverse defined) |
| Grounding | hasComponent | Links FunctionalAspect to implementing Component |
| Grounding | hasUserEntity | Associates aspects or CR with UserEntity |
| Specialization | hasGovernance, hasDeliveryModel, hasInfrastructureType, hasVirtualizationTechnology, hasDomain, hasScope | Infrastructure decisional specialization |
| Specialization | hasLearningMethod, hasEvaluationPractice, hasCurriculaType, hasPurpose, targetsLearningObjective, targetsDidactics, definesUserType, definesUserTeam | Scope decisional specialization |
| Datatype Properties | ||
| Metadata | hasName, hasDescription | Human-readable annotations |
| Traceability | hasID, hasVersion | Identification and version control |
| Annotation | hasPriority, hasLevel | Complexity or criticality attributes |
| Optional | hasTimestamp, hasDuration | Temporal annotations when required |
| Axioms and Constraints | ||
| Disjointness | Aspect Classes Disjoint | |
| Disjointness | Layer Subclasses Disjoint | Infrastructure ⊥ RLMS ⊥ UserOriented subclasses |
| Disjointness | Capability Disjointness | Aspect ⊥ Component; Component ⊥ UserEntity |
| Domain/Range | Property Restrictions | Explicit domain and range constraints for all object properties |
| Cardinality | Structural Completeness | Each CR has decisional, functional, informational aspect |
| Cardinality | Capability Support | Each Capability enabled by aspect |
| Inverse Properties | Bidirectional Reasoning | |
| Property Chain | Capability Inference | |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




