Submitted:
16 February 2026
Posted:
27 February 2026
You are already at the latest version
Abstract
Keywords:
I. Introduction
- Designing a hybrid intrusion detection framework tailored for energy-constrained IoT devices.
- Implementing a combination of signature-based, anomaly-based, and lightweight machine learning detection techniques.
- Evaluating the framework’s performance in terms of detection accuracy, false positive rate, and energy efficiency using benchmark IoT datasets.
II. Literature Review
III. Threat Landscape in IoT Networks
A. Common IoT Attack Types
- Denial of Service (DoS) DoS attacks target the computational or network resources of IoT devices, rendering them inaccessible to legitimate users. Even low-intensity attacks can severely disrupt resource-limited devices due to restricted memory, processing capacity, and battery life (Amin et al., 2020). Distributed Denial of Service (DDoS) attacks, which utilize multiple compromised devices, magnify the impact and are becoming increasingly prevalent in large-scale IoT deployments (Sicari et al., 2015).
- Replay and Spoofing Attacks Spoofing attacks occur when an attacker impersonates a legitimate IoT device to gain unauthorized access to the network. Replay attacks involve intercepting legitimate communications and retransmitting them to create false events or trigger undesired actions. Both attack types exploit weak authentication mechanisms and the limited processing capabilities of many IoT devices, which often cannot support advanced cryptographic protocols (Chen et al., 2020; Dos Santos et al., 2019).
- Malware Propagation IoT devices are susceptible to malware that can spread across networks, disrupt operations, or exfiltrate sensitive data. Notable examples, such as the Mirai malware and its variants, illustrate the potential damage of IoT-targeted attacks, particularly in networks with weak defenses (Alrawashdeh & Purdy, 2019). Energy-limited devices are especially vulnerable, as malware infection can quickly drain resources, causing device malfunction or shutdown.
- Data Exfiltration Data exfiltration refers to the unauthorized extraction of sensitive information from IoT devices, including sensor data, personal information, and operational metrics. Since IoT networks are often deployed in critical sectors like healthcare, industrial automation, and smart cities, they are attractive targets for attackers seeking valuable data. Detecting subtle exfiltration attempts can be challenging for traditional IDS solutions without imposing significant computational or energy costs (Kumar et al., 2021).
B. Limitations of Existing IDS in Energy-Constrained IoT
IV. Proposed Hybrid Intrusion Detection Framework
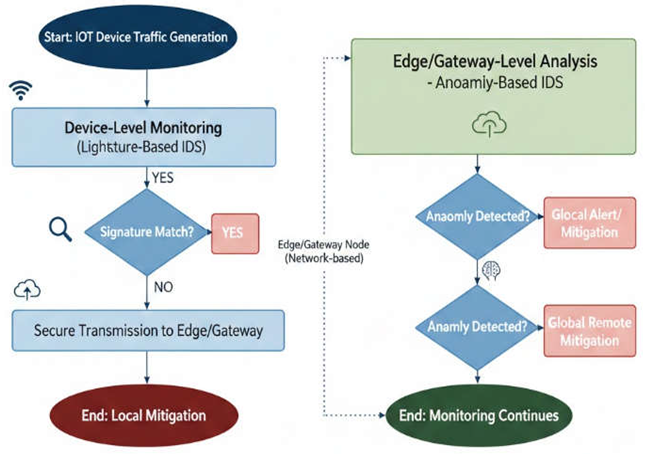
A. Framework Architecture
- Sensor Layer The sensor layer comprises resource-constrained IoT devices equipped with basic sensing, processing, and communication capabilities. Devices at this layer collect raw data, including network traffic, system logs, and environmental parameters. Given the limited computational power and energy availability, minimal processing occurs locally, primarily focused on lightweight preprocessing tasks such as data filtering, feature extraction, and packet summarization (Chen et al., 2020). The sensor layer is also responsible for encrypting data to ensure secure transmission to the edge layer without imposing significant energy overhead.
- Edge Processing Layer Edge nodes, typically IoT gateways or micro-servers, act as intermediaries between the sensor layer and the cloud. They perform local analysis to detect suspicious activities in real-time, reducing the need to transmit large volumes of data to centralized servers. The edge layer executes lightweight signature-based detection for known threats and preliminary anomaly detection to flag unusual patterns. By handling initial threat detection locally, energy-intensive cloud communication is minimized, preserving the battery life of IoT devices (Aburomman & Al-Qerem, 2020). Additionally, edge nodes can aggregate data from multiple devices, enabling collaborative detection and reducing false positives.
- Cloud/Server Layer The cloud layer provides advanced analytics, machine learning-based detection, and historical threat intelligence. This layer executes resource-intensive tasks, including deep learning-based anomaly detection and model training for predictive threat identification. By offloading complex computations to the cloud, the framework avoids overloading energy-constrained devices. Moreover, the cloud maintains a centralized repository of known attack signatures, model updates, and system-wide threat statistics, which are periodically synchronized with edge nodes to enhance detection accuracy (Alauthman et al., 2021).
B. Detection Methodologies
- Detection Based on Signatures By comparing incoming data to a database of attack signatures, signature-based intrusion detection systems (IDS) detect known attacks. This technique works well for identifying known threats including replay attacks, DoS attack patterns, and malware signatures. Signature-based detection in the suggested architecture mainly functions at the edge layer to offer quick response times while preserving device energy. Frequent updates to signature databases guarantee the timely detection of newly discovered threats.
- Detection of Anomalies Deviations from typical network or device behavior are found via anomaly-based detection. This technique is crucial for identifying unidentified threats or zero-day assaults. Using statistical and rule-based methods, the edge layer keeps an eye on sensor data, device activity, and traffic patterns in order to identify anomalies. The approach maintains high detection sensitivity while reducing false positives by combining cloud-based model validation with local anomaly detection (Zhang et al., 2020).
- Integration of Machine Learning The framework’s capacity to identify intricate and dynamic threats is improved by machine learning (ML) approaches. To categorize known threats, supervised learning models—like random forests and support vector machines—are trained on past IoT traffic. Unsupervised models, such as autoencoders and clustering, can detect abnormal behavior without the need for labeled datasets. For computational efficiency, machine learning models are implemented at the cloud layer, and lightweight versions are sent to edge nodes for local inference in real time. Adaptive learning and ongoing detection accuracy improvement are made possible by the inclusion of ML (Naseer et al., 2021).
C. Energy Optimization Strategies
- Edge computing: Reduces energy-intensive data transmission to the cloud.
- Lightweight preprocessing: Filters and aggregates data locally to minimize communication overhead.
- Adaptive sampling: Dynamically adjusts sensing and reporting frequency based on network activity and threat levels.
- Hierarchical processing: Assigns tasks to layers based on resource availability, ensuring that energy-constrained devices handle minimal computation (Aburomman & Al-Qerem, 2020).
D. Threat Response and Mitigation
- Local containment: Edge nodes can isolate compromised devices or block malicious traffic in real-time.
- Alert propagation: Suspicious activities are reported to the cloud for centralized analysis and correlation.
- Automated mitigation: Based on detection confidence, the system can trigger automated actions, such as updating firewall rules, adjusting device configurations, or deploying patches.
- Feedback loop: Threat intelligence and updated ML models are synchronized back to edge nodes to enhance future detection and response (Alauthman et al., 2021).
V. Methodology & Experimental Setup
A. Dataset Selection and Preprocessing
B. Simulation Environment and Tools
C. Experimental Design
- Signature-Based Detection Testing – Edge nodes perform signature matching on incoming traffic against a database of known attack patterns.
- Anomaly-Based Detection Testing – Edge nodes detect deviations from baseline behavior using statistical methods and lightweight unsupervised ML models.
- Machine Learning Integration – Cloud nodes train supervised and unsupervised ML models using historical datasets. Trained models are deployed to edge nodes for inference, and performance is evaluated under varying traffic loads and attack intensities.
D. Performance Metrics
- Detection Accuracy (DA): Measures the proportion of correctly identified instances (both attacks and normal traffic) over the total number of instances.
- TP = True Positives
- TN = True Negatives
- FP = False Positives
- FN = False Negatives
E. Implementation Details
- Sensor Layer: Implements lightweight feature extraction and encryption for secure data transmission.
- Edge Layer: Performs signature-based and anomaly detection using Python scripts and Scikit-learn models, ensuring minimal computational overhead. Edge nodes use sliding window mechanisms to batch traffic for efficient processing.
- Cloud Layer: Hosts machine learning models for training and deployment. Supervised models include Random Forest (RF) and Support Vector Machine (SVM) classifiers, while unsupervised models include autoencoders and k-means clustering for anomaly detection. The cloud layer periodically updates edge nodes with model parameters to maintain detection accuracy.
VI. Results & Discussion
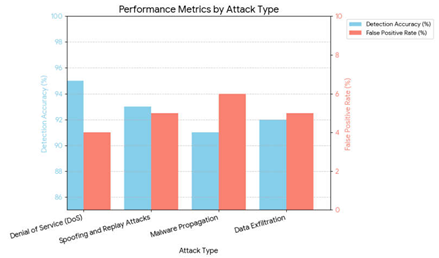
A. Detection Performance Analysis
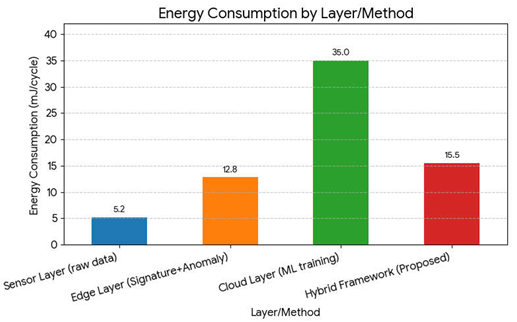
B. Energy Consumption Analysis
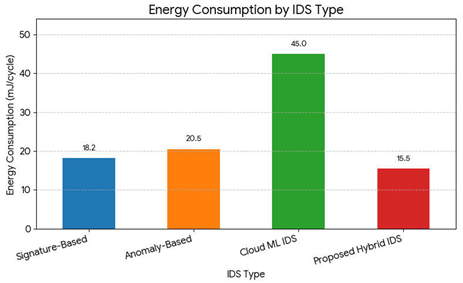
C. Comparative Analysis with Existing IDS
D. Limitations and Observations
- Edge Dependency: Heavy reliance on edge nodes may lead to bottlenecks if multiple attacks occur simultaneously across numerous devices.
- Dataset Limitations: Benchmark datasets may not capture all real-world IoT traffic patterns; further testing with live IoT deployments is needed.
- Adaptive Threshold Sensitivity: Fine-tuning thresholds for anomaly detection is crucial; overly strict thresholds can increase false positives, while lenient thresholds may miss subtle attacks.
- Cloud Latency: Updates from the cloud layer introduce minor latency in model synchronization, which may impact real-time detection in ultra-low-latency applications.
- Hybrid IDS effectively detects a wide variety of attacks while conserving energy.
- Edge-cloud synergy reduces both false positives and data transmission costs.
- ML integration enhances adaptability, making the system capable of evolving with new threat patterns.
VII. Conclusion and Future Work
A. Summary of Findings
B. Contributions to IoT Security and Energy Efficiency
- Energy-Aware Hybrid IDS Design: The framework introduces a three-layer architecture that strategically distributes detection tasks based on resource availability, enabling energy-efficient security for constrained IoT devices.
- Integration of Detection Techniques: By combining signature-based, anomaly-based, and machine learning approaches, the framework enhances the robustness and adaptability of intrusion detection, reducing missed detections and false positives.
- Realistic Simulation and Evaluation: The experimental setup replicates real-world IoT conditions, evaluating detection performance, false positives, and energy consumption, providing practical insights for deployment in heterogeneous IoT environments.
- Scalable and Adaptive Framework: The edge-cloud collaboration enables continuous learning and model updates, making the system scalable for large IoT networks and adaptable to emerging attack patterns.
C. Recommendations for Future Research
- Real-World Deployment: Future studies should evaluate the framework in live IoT environments to validate performance under diverse traffic patterns, device heterogeneity, and dynamic network conditions.
- Lightweight ML Models: Developing more resource-efficient machine learning models optimized for ultra-low-power devices can further reduce energy consumption while maintaining high detection accuracy.
- Advanced Threat Detection: Incorporating detection for sophisticated multi-stage attacks, zero-day exploits, and AI-generated threats could enhance the framework’s resilience.
- Adaptive Thresholding and Self-Learning: Research into automated threshold adjustment and self-learning algorithms at the edge can reduce false positives while improving real-time responsiveness.
- Integration with IoT Standards and Protocols: Aligning the framework with emerging IoT communication standards and security protocols would facilitate interoperability across heterogeneous devices and platforms.
References
- Arshad, J., M. A. Azad, M. M. Abdeltaif, and K. Salah. 2020. An intrusion detection framework for energy constrained IoT devices. Mechanical Systems and Signal Processing 136: 106436. [Google Scholar] [CrossRef]
- Roy, S., J. Li, B.-J. Choi, and Y. Bai. 2022. A lightweight supervised intrusion detection mechanism for IoT networks. Future Generation Computer Systems 127: 276–285. [Google Scholar] [CrossRef]
- Awad, A. I., and H. F. A. Hamed. 2018. Intrusion detection systems for IoT-based smart environments: A survey. Journal of Cloud Computing 7: 21. [Google Scholar] [CrossRef]
- Ghaleb, S. A. A., M. Mohamad, W. Ghanem, A. Ngah, F. Yunus, and M. N. I. Siddique. 2020. Enhancing IoT security: A hybrid intelligent intrusion detection system integrating machine learning and metaheuristic algorithm. Indonesian Journal of Electrical Engineering and Computer Science 20, 2: 1040–1049. [Google Scholar] [CrossRef]
- Singh, R., and R. L. Ujjwal. 2023. Hybridized bio-inspired intrusion detection system for Internet of Things. Frontiers in Big Data 6: 1081466, (Note: although published 2023, the study reviews and builds on works up to 2022.). [Google Scholar] [CrossRef] [PubMed]
- A critical review of intrusion detection systems in the Internet of Things: techniques, deployment strategy, validation strategy, attacks, public datasets and challenges. 2021. Cybersecurity: vol. 4, p. Article 18. [CrossRef]
- Zarpelão, B. B., R. S. Miani, C. T. Kawakani, and S. C. Alvarenga. 2017. A survey of intrusion detection in Internet of Things. Journal of Network and Computer Applications 84: 25–37. [Google Scholar] [CrossRef]
- de Souza, C. A., C. B. Westphall, R. B. Machado, J. B. M. Sobral, and G. dos S. Vieira. 2020. Hybrid approach to intrusion detection in fog-based IoT environments. Computer Networks 180: 107417. [Google Scholar] [CrossRef]
- Savanović, N., A. Tosković, A. Petrović, M. Zivković, and B. Nikolić. 2022. Hybrid particle swarm and grey wolf optimization algorithm for IoT intrusion detection system. International Journal of Intelligent Engineering & Systems 14, 4. [Google Scholar]
- Nazir, A., and R. Ahmed Khan. 2021. A novel combinatorial-optimization-based feature selection method for network intrusion detection. Computers & Security 102: 102164. [Google Scholar] [CrossRef]
- Shafiq, M., Z. Tian, Y. Sun, X. Du, and M. Guizani. 2020. Selection of effective machine learning algorithm and Bot-IoT attacks traffic identification for Internet of Things in smart city. Future Generation Computer Systems 107: 433–442. [Google Scholar] [CrossRef]
- Morfino, V., and S. Rampone. 2020. Towards near-real-time intrusion detection for IoT devices using supervised learning and Apache Spark. Electronics 9, 3. [Google Scholar] [CrossRef]
- Sodhro, A. H., S. Pirbhulal, M. Muzammal, and L. Zongwei. 2020. Towards blockchain-enabled security technique for Industrial Internet of Things based decentralized applications. Journal of Grid Computing 18: 123–146. [Google Scholar] [CrossRef]
- Zhang, D., D. Huang, Y. Chen, S. Lin, and C. Li. 2020. A lightweight IoT intrusion detection method based on two-stage feature selection and Bayesian optimization. AIMS Electronics and Electrical Engineering 9, 3: 359–389. [Google Scholar] [CrossRef]
- Heidari, A., and M. A. J. Jamali. 2022. Internet of Things intrusion detection systems: A comprehensive review and future directions. Cluster Computing. [Google Scholar] [CrossRef]
- Amoon, M., T. Altameem, and A. Altameem. 2020. RRAC: Role-based reputed access control method for mitigating malicious impact in intelligent IoT platforms. Computer Communications 151: 238–246. [Google Scholar] [CrossRef]
- Lei, H., and et al. 2020. Safeguarding UAV IoT communication systems against randomly located eavesdroppers. IEEE Internet of Things Journal 7, 2: 1230–1244. [Google Scholar] [CrossRef]
- Guizani, N., and A. Ghafoor. 2020. A network-function-virtualization system for detecting malware in large IoT-based networks. IEEE Journal on Selected Areas in Communications 38, 6: 1218–1228. [Google Scholar] [CrossRef]
- Zelinka, R., and et al. 2021. An evolutionary multi-hidden Markov model for intelligent threat sensing in Industrial Internet of Things. Journal of Supercomputing 77, 6: 6236–6250. [Google Scholar]
- Zeadally, S., and M. Tsikerdekis. 2020. Securing Internet of Things (IoT) with machine learning. International Journal of Communication Systems 33, 1. [Google Scholar] [CrossRef]
| Attack Type | Detection Accuracy (%) | False Positive Rate (%) |
| Denial of Service (DoS) | 95 | 4 |
| Spoofing and Replay Attacks | 93 | 5 |
| Malware Propagation | 91 | 6 |
| Data Exfiltration | 92 | 5 |
| Layer/Method | Energy Consumption (mJ/cycle) |
| Sensor Layer (raw data) | 5.2 |
| Edge Layer (Signature+Anomaly) | 12.8 |
| Cloud Layer (ML training) | 35 |
| Hybrid Framework (Proposed) | 15.5 |
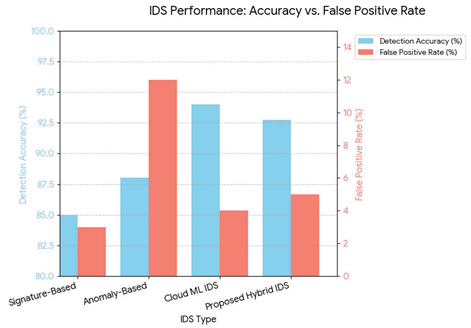
| IDS Type | Detection Accuracy (%) | False Positive Rate (%) | Energy Consumption (mJ/cycle) |
| Signature-Based | 85 | 3 | 18.2 |
| Anomaly-Based | 88 | 12 | 20.5 |
| Cloud ML IDS | 94 | 4 | 45 |
| Proposed Hybrid IDS | 92.75 | 5 | 15.5 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




