Submitted:
13 February 2026
Posted:
27 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background and Related Works
2.1. Background
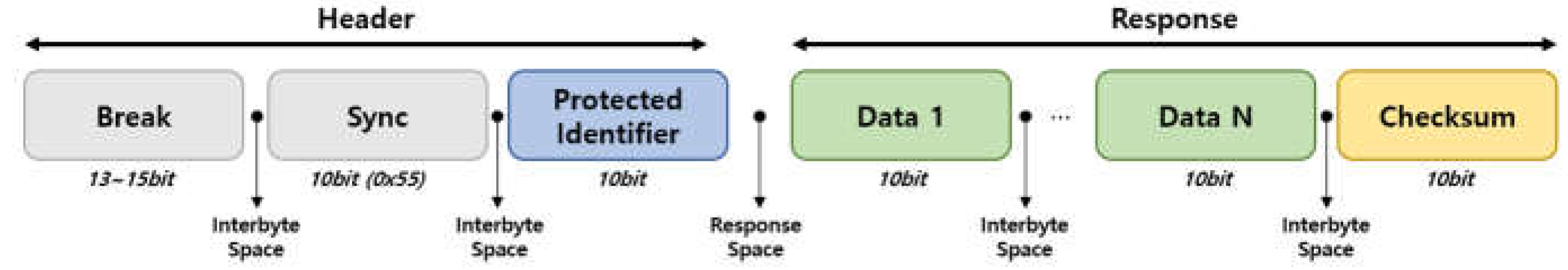
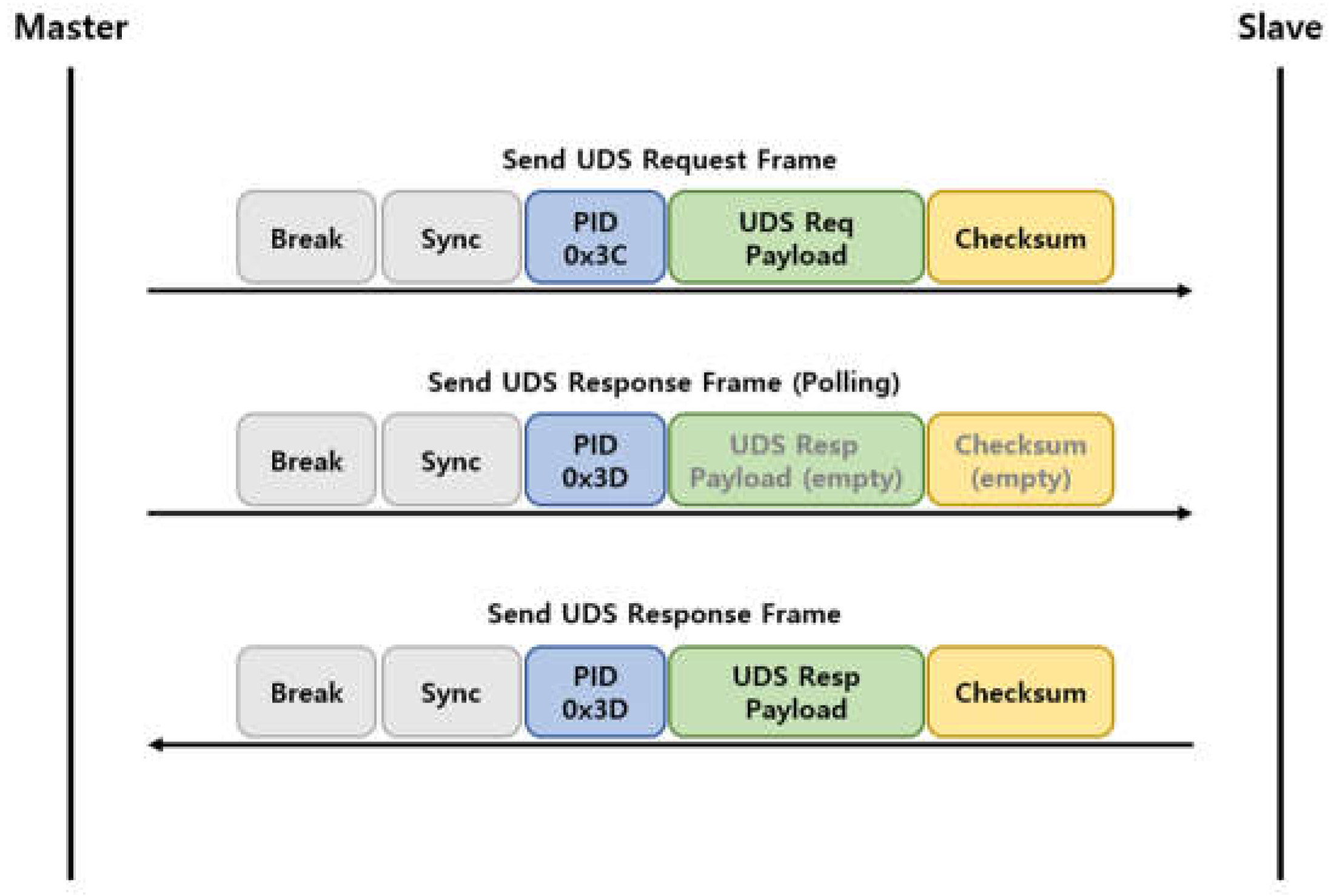
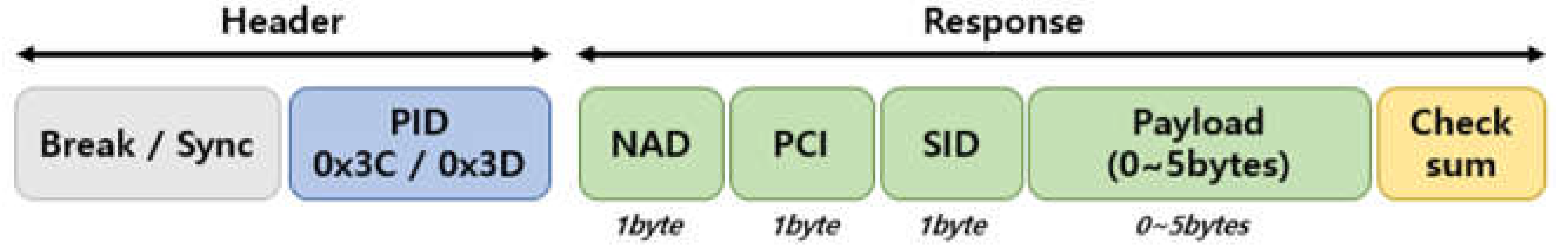
2.1.1. Local Interconnect Network (LIN)
2.1.2. Unified Diagnostic Services (UDS)
2.1.3. Fuzz Testing
- Mutation-based Fuzzing: This approach generates modified data by applying techniques such as bit-flipping or random value injection to existing normal data packets, which serve as seed samples. It can be implemented without an in-depth understanding of complex protocol structures and is mainly utilized for testing simple network packets.
- Generation-based Fuzzing: This method creates new test data from scratch that complies with the rules of the target protocol, such as frame structures and checksums, based on its specification. This approach is particularly effective for testing sophisticated communication protocols and diagnostic services, such as UDS.
2.2. Related Works
2.2.1. Trends in Automotive Network Security Surveys
2.2.2. Fuzzing and Vulnerability Detection for In-vehicle Networks
2.2.3. Efficiency and Optimization in Security Testing
3. Proposed Methodology
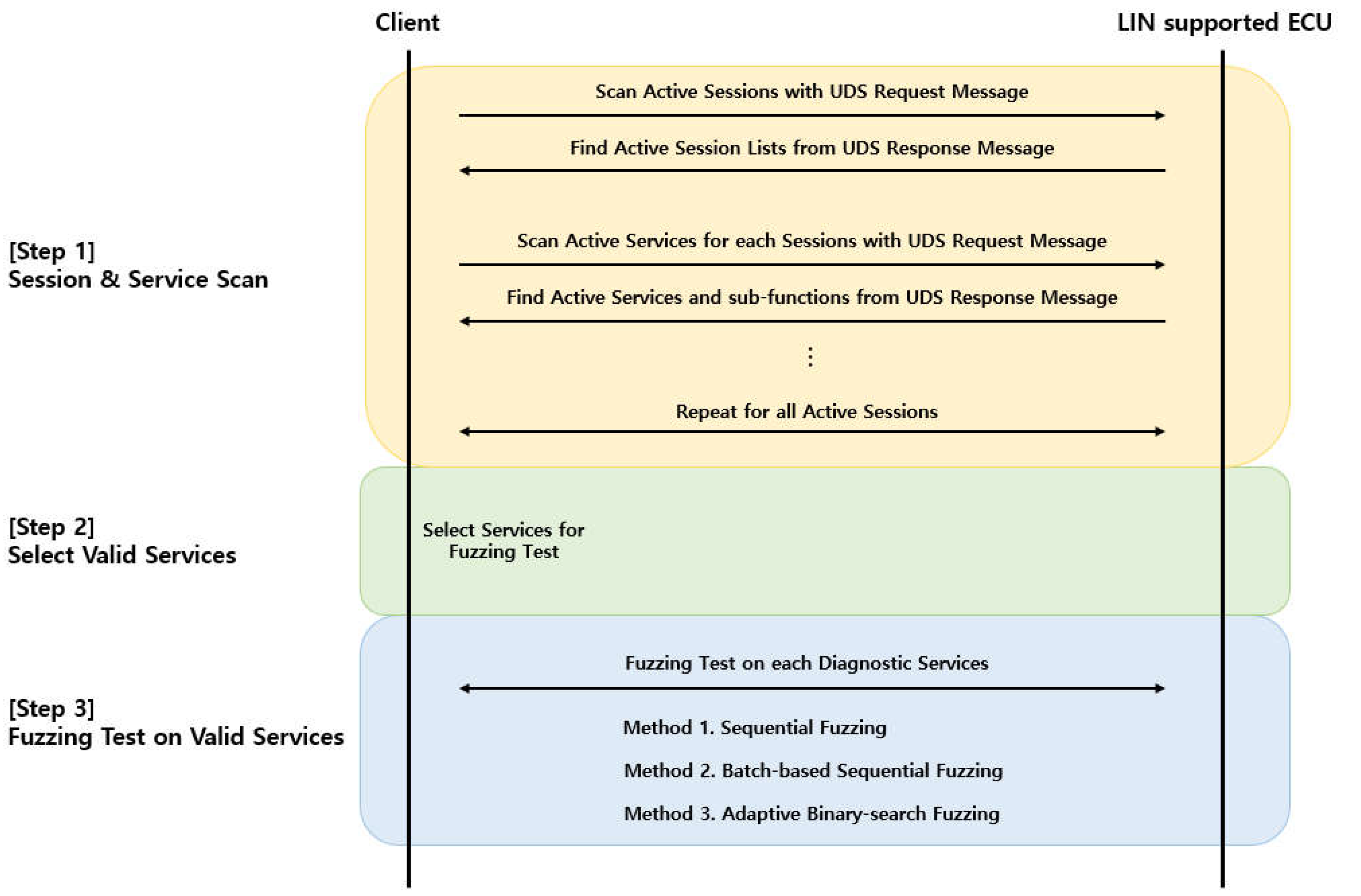
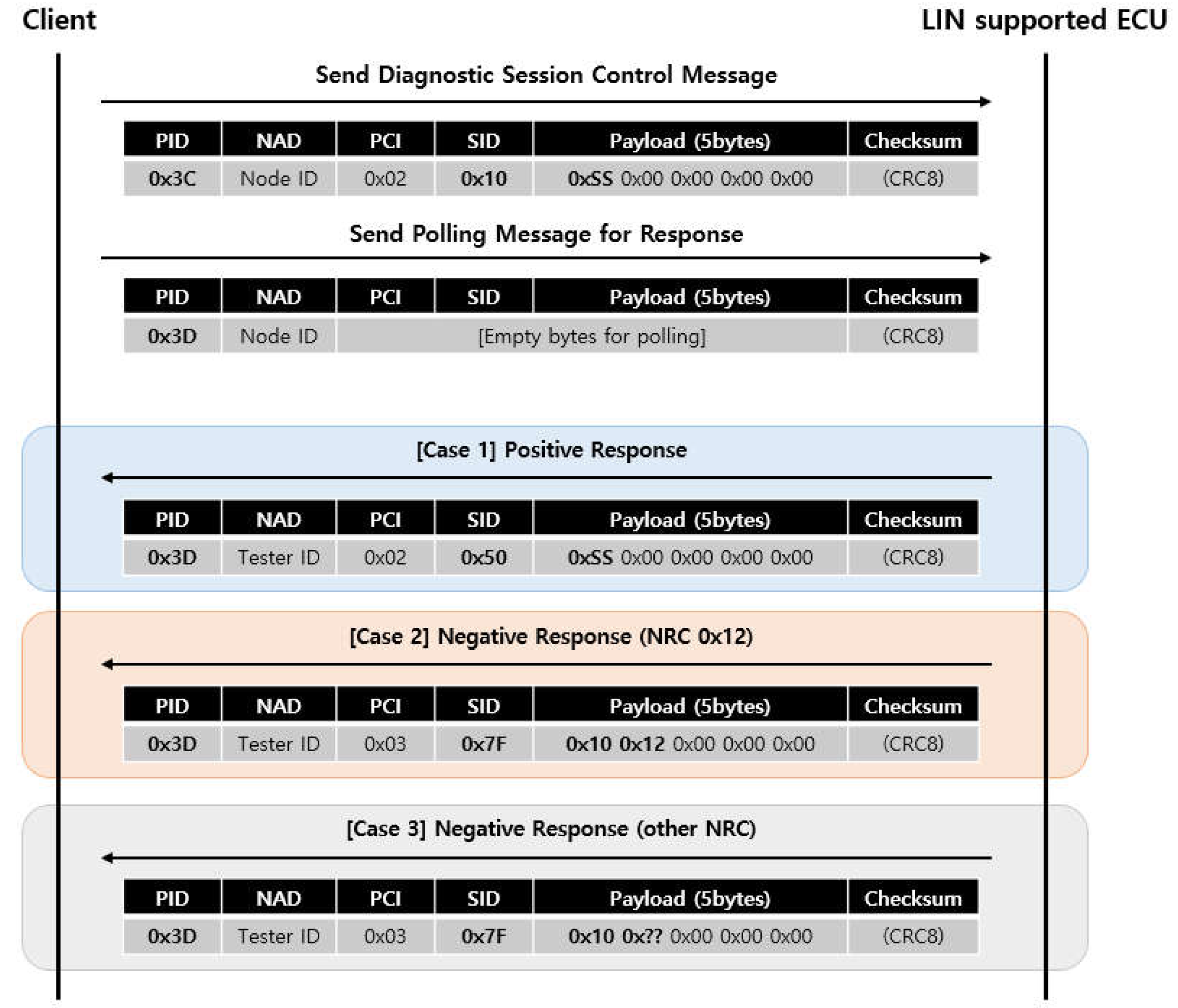
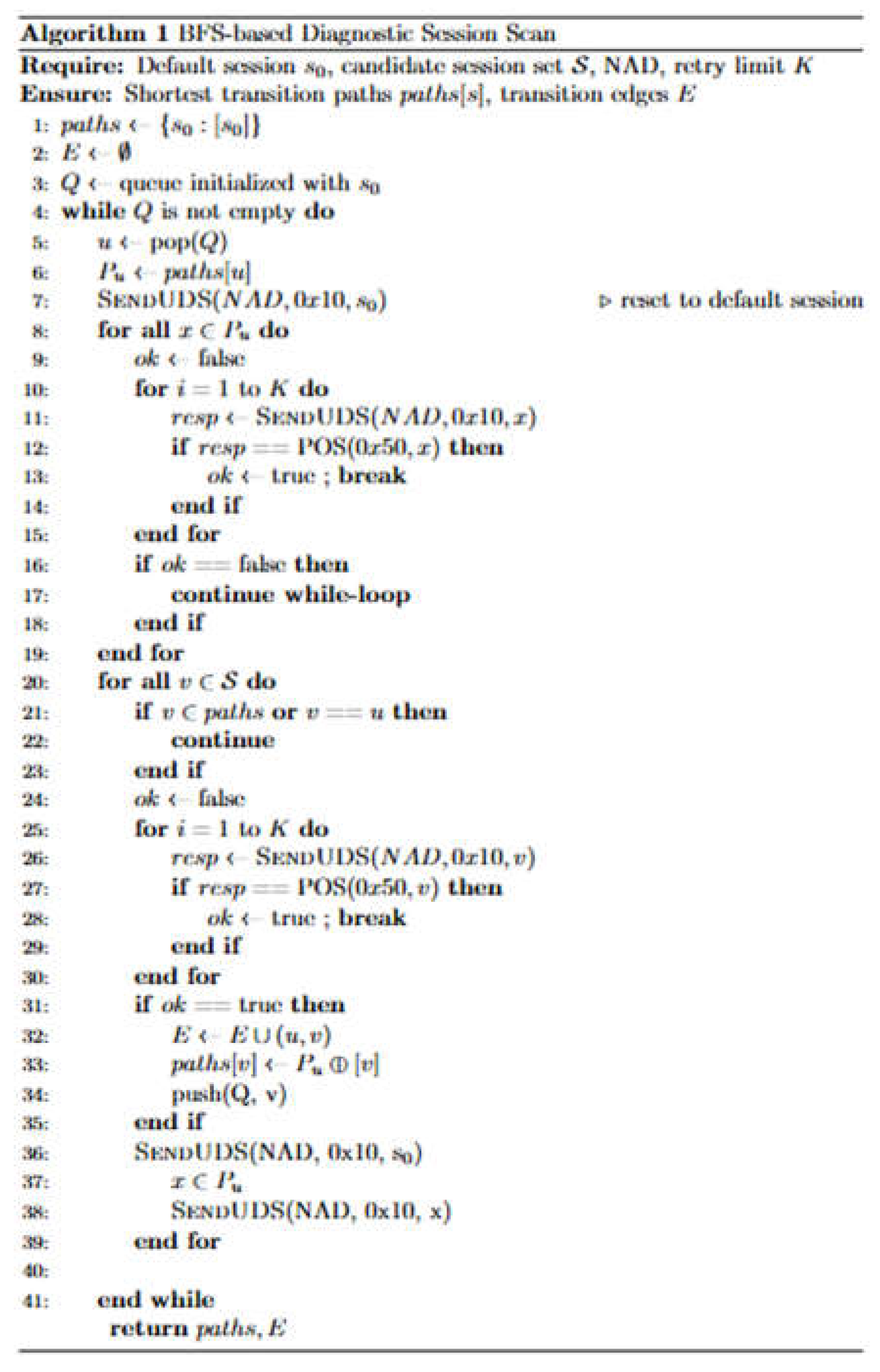
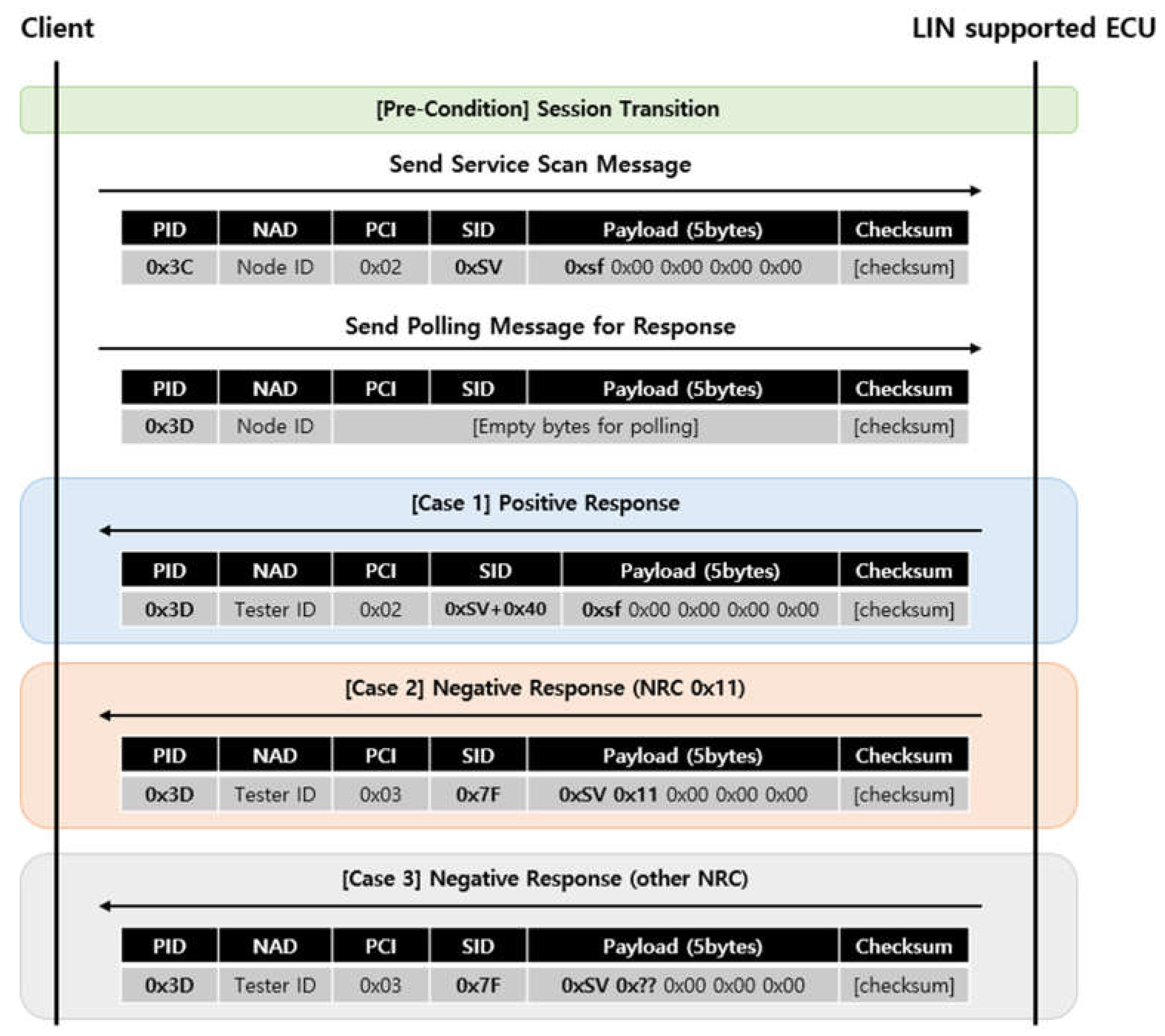
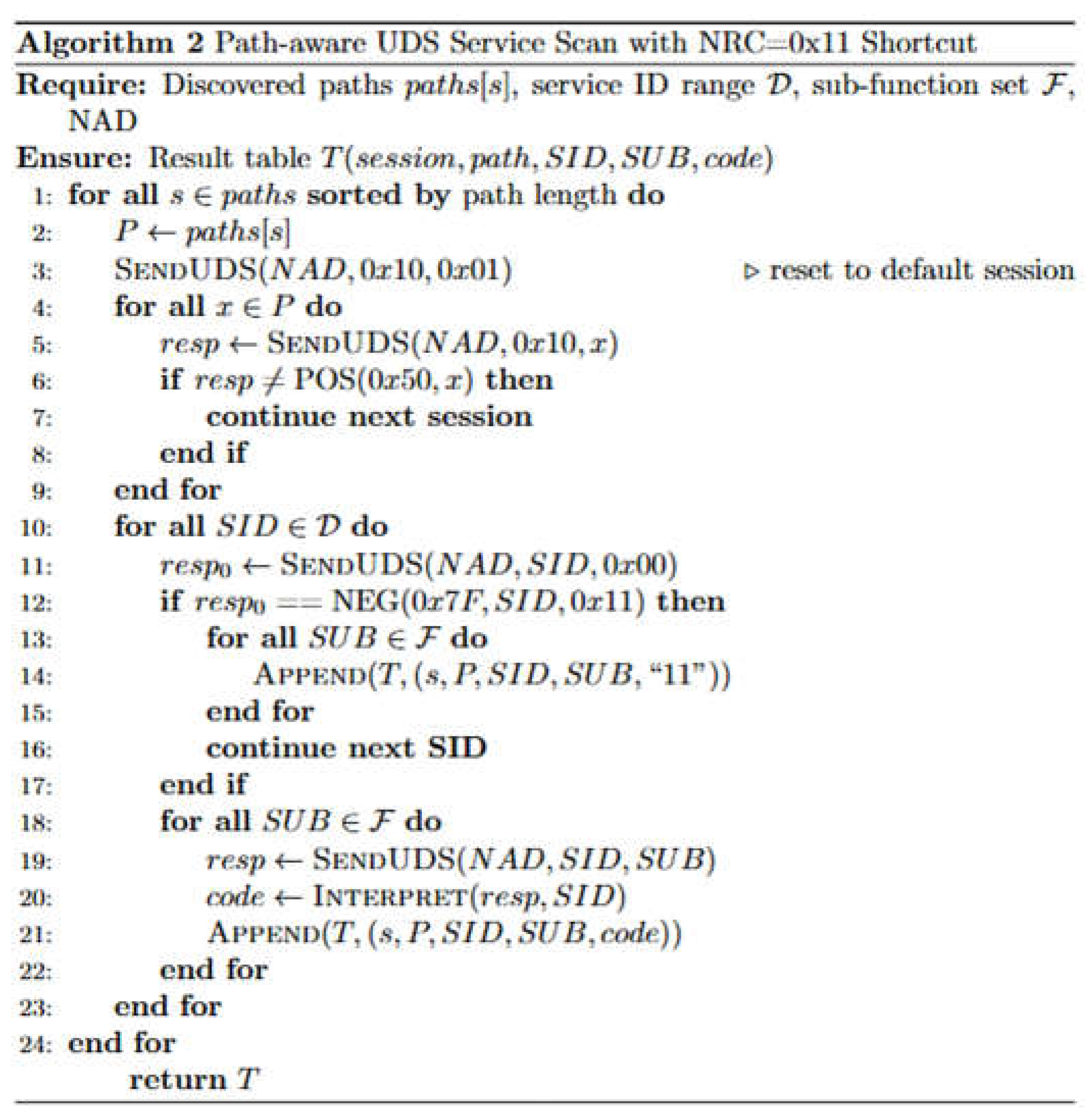
3.1. Session & Service Scan
- Case 1: If a positive response with SID 0x50 is returned for a SID 0x10 request, it is determined that the target session is accessible from the current session.
- Case 2: If a negative response with NRC 0x7F 0x12 (Sub-function Not Supported) is returned for a SID 0x10 request, it is determined that the target session is inaccessible from the current session.
- Case 3: If a negative response with an NRC value other than 0x12 is returned for a SID 0x10 request, the client directly determines the accessibility of the target session based on the specific NRC received.
- Case 1: If a positive response (0xSV + 0x40) is returned for a specific service (0xSV) request, it is determined that the target service exists within the current session.
- Case 2: If a negative response with NRC 0x7F 0x11 (Service Not Supported) is returned for a specific service (0xSV) request, it is concluded that the target service does not exist in the current session. Consequently, the process bypasses any subsequent sub-function discovery for that service and immediately proceeds to the next service ID to optimize scanning efficiency.
- Case 3: If a negative response with an NRC value other than 0x11 is returned for a specific service (0xSV) request, the client directly determines the existence of the target service based on the received NRC.
3.2. Select Valid Services
3.3. Methods for Fuzz Testing
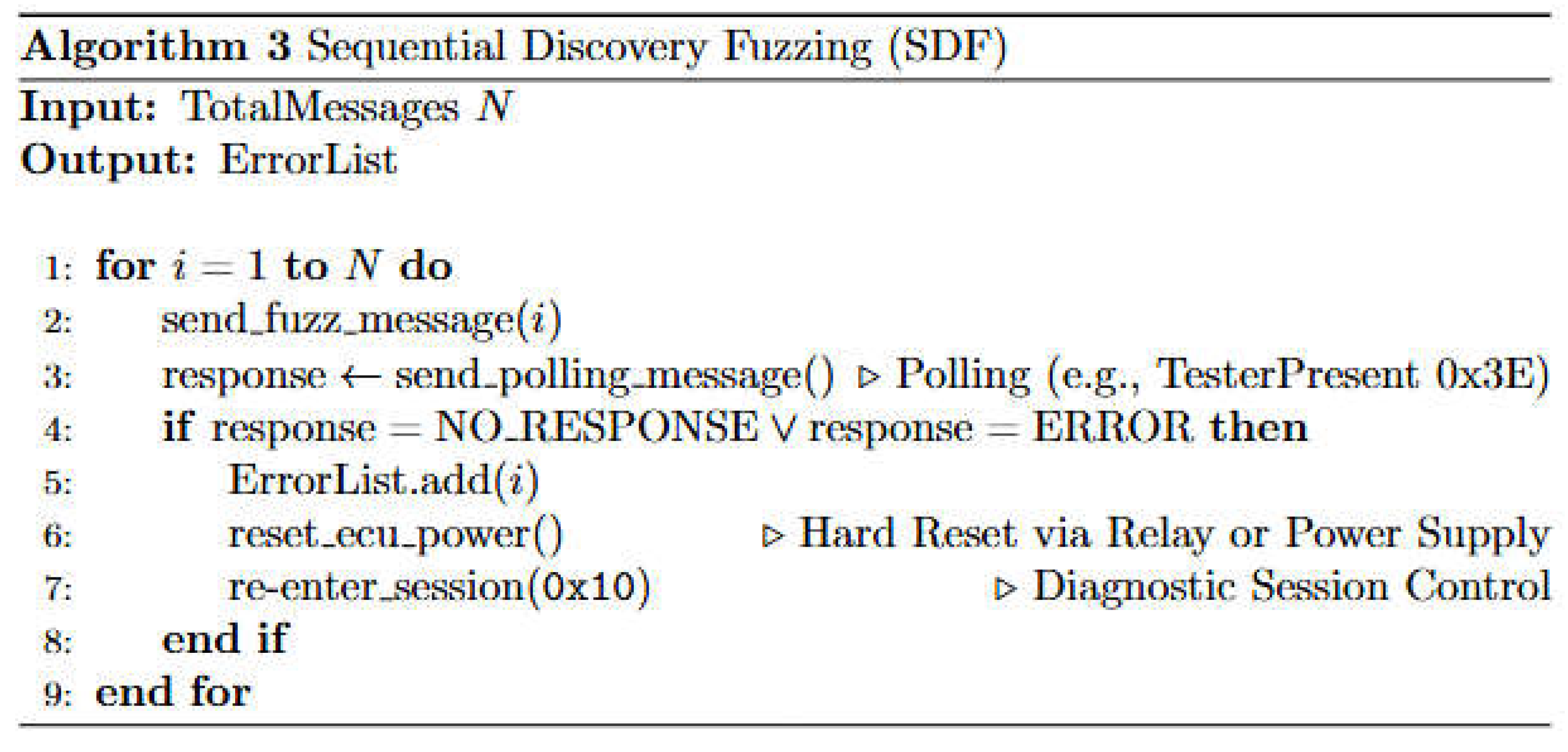
3.3.1. Sequential Discovery Fuzzing (SDF)
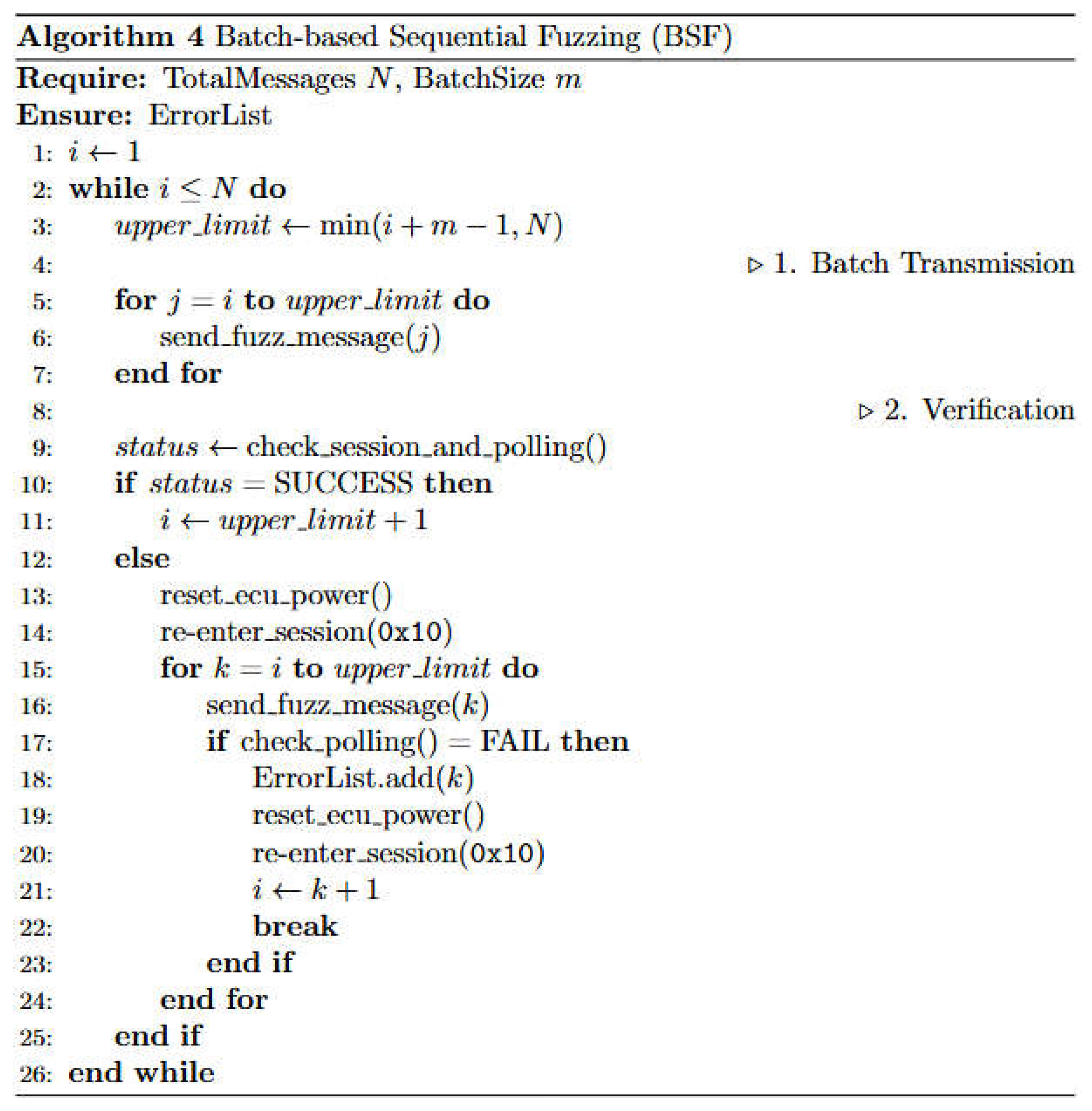
3.3.2. Batch-Based Sequential Fuzzing (BSF)
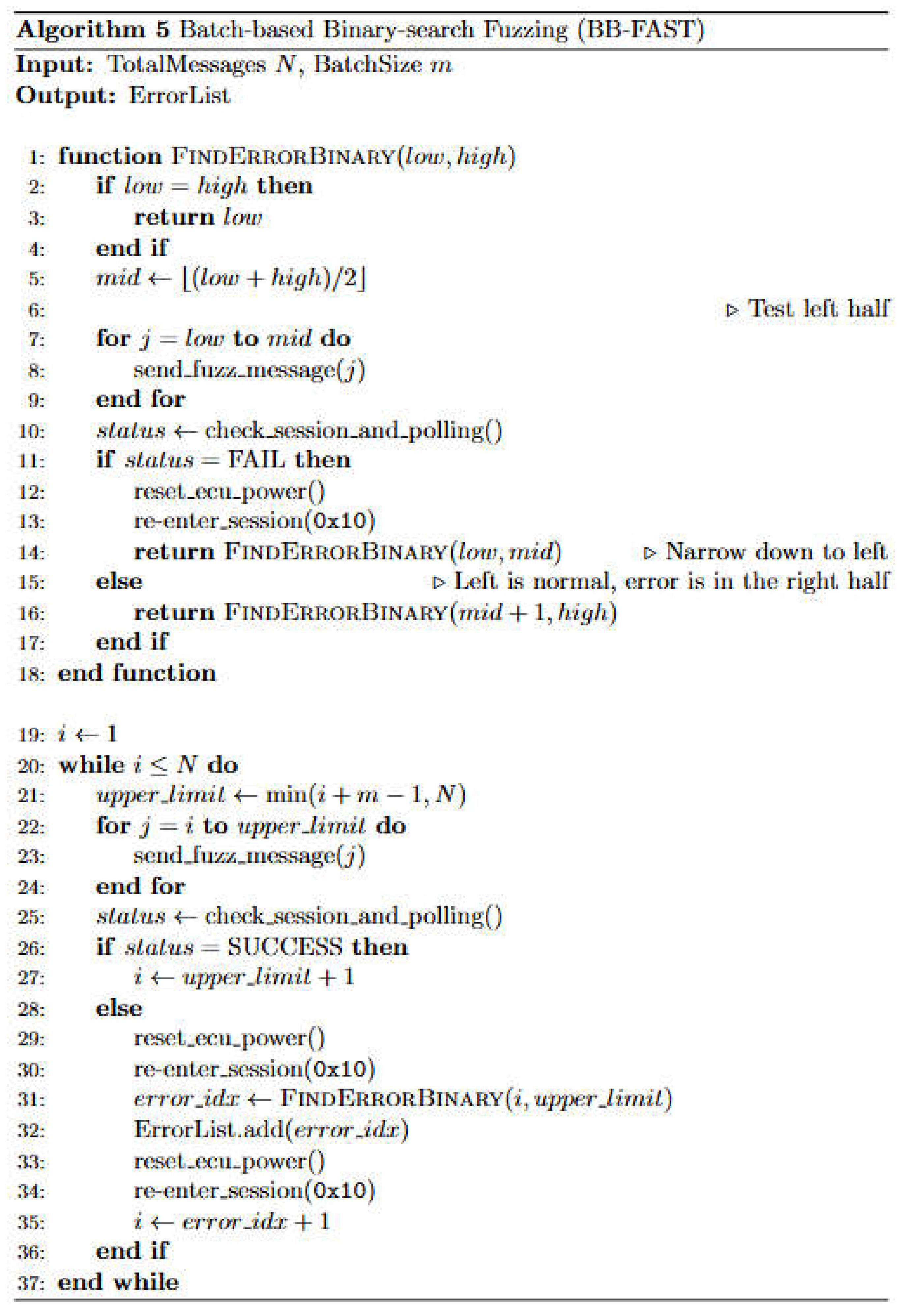
3.3.3. Batch-based Binary-Search Fuzzing and Accelerated Security Testing (BB-FAST)
4. Theoretical Analysis on Proposed Methods
4.1. Time-Complexity Analysis
4.2. Performance Evaluation via Numerical Simulation
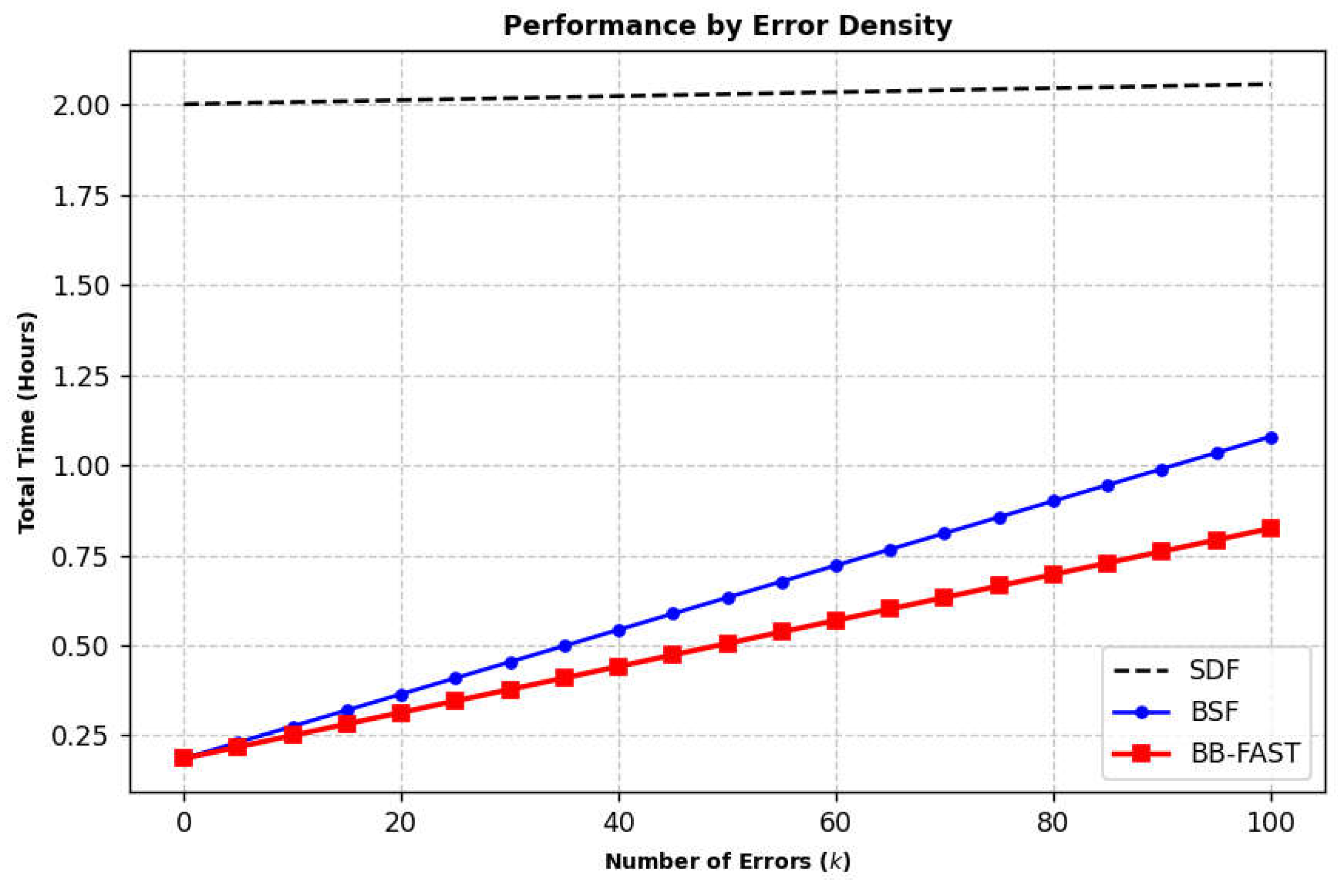
4.2.1. Simulation According to Error Density (k)
- k: 1 to 100 (independent variable)
- m: 512 (fixed value)
- Tr: 2.0 sec (fixed value; reflects the human reaction limit for controllability as specified in ISO 26262-3 [26])
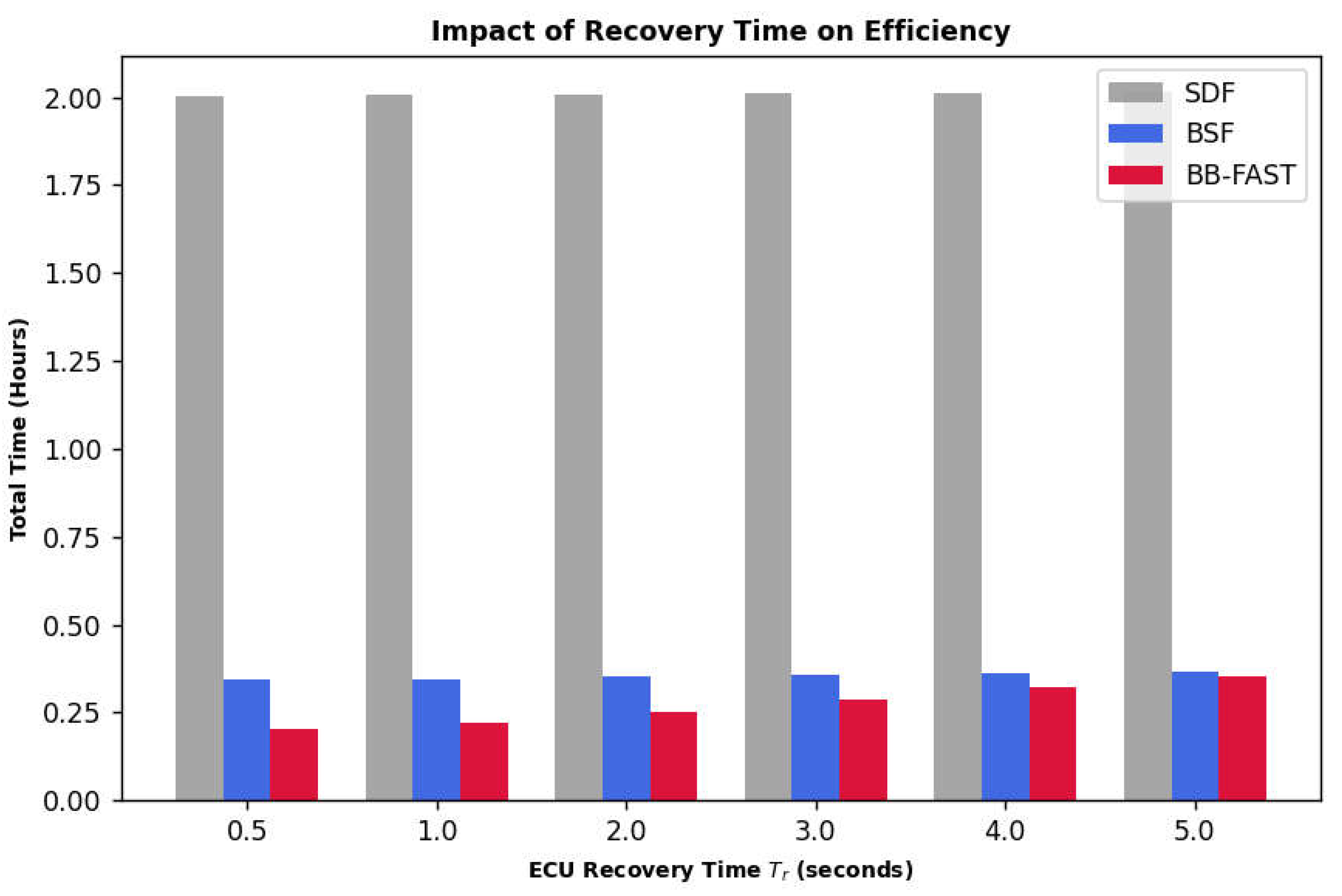
4.2.2. Analysis According to ECU Recovery Time ()
- k: 10 (fixed value)
- m: 512 (fixed value)
- Tr: 0.5 sec to 5.0 sec (independent variable)
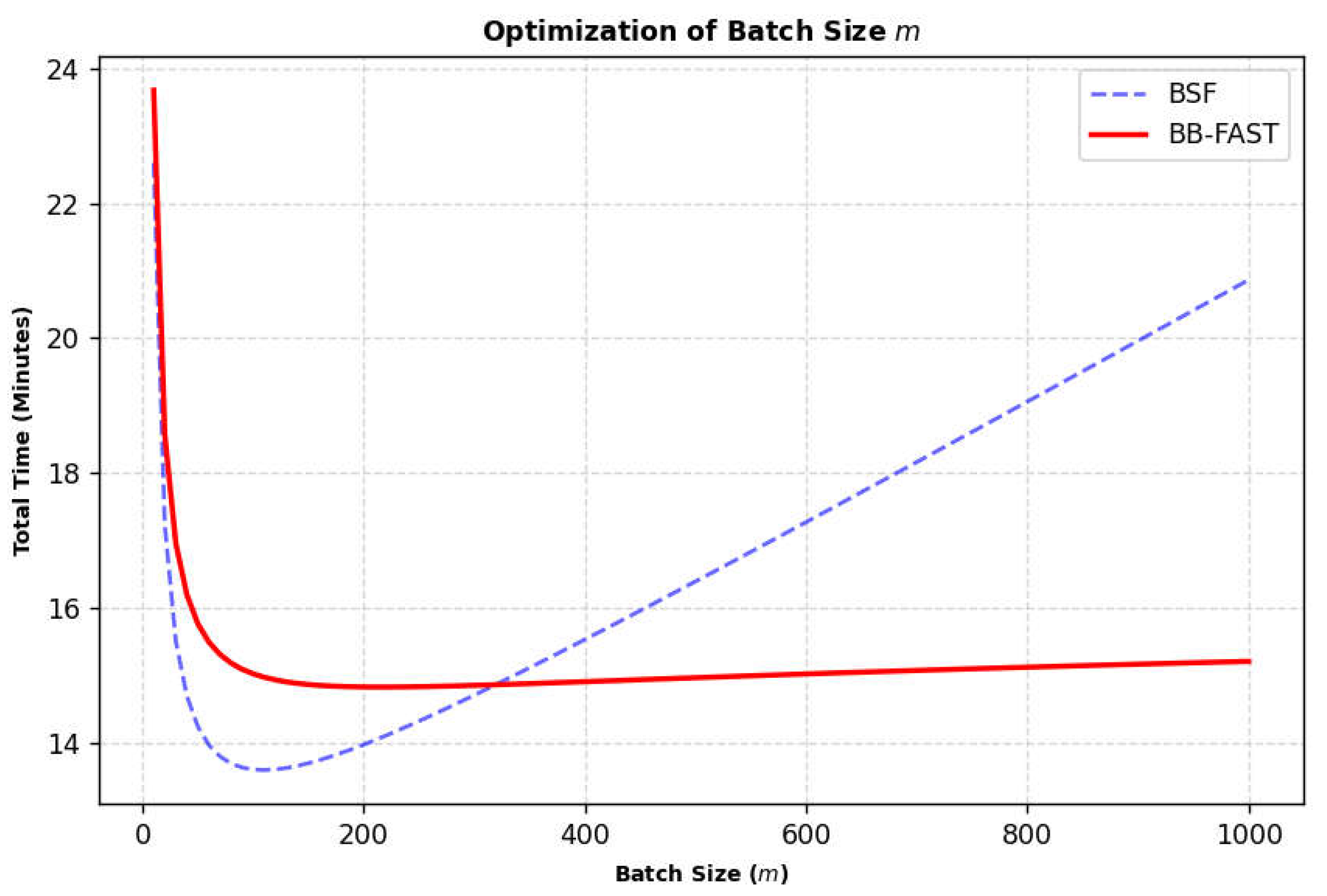
4.2.3. Simulation According to Batch Size ()
- k: 10 (fixed value)
- m: 10 to 1,000 (independent variable)
- Tr: 2.0 s (fixed value; reflects the human reaction limit for controllability as specified in ISO 26262-3 [26])
4.2.4. Summary of Simulation Results
- Strategic Selection of Parameter : As confirmed in Section 4.2.3, the theoretical optimal batch size varies depending on error density () and recovery time (). However, this paper adopts = 512 as a strategic standard, comprehensively considering the scalability for future tests (e.g., 3-byte search spaces), the minimization of polling overhead, and the implementation efficiency of the binary search algorithm. This design ensures universal performance across diverse vehicle network environments rather than seeking a local optimum for a specific scenario.
- Ensuring Feasibility for Large-scale Search Spaces: The simulation results show that an = 512 configuration suppresses the frequency of polling—the dominant bottleneck in total execution time—to 1/512 of the original rate. This minimizes the time delay caused by polling overhead () even in vast search spaces exceeding 2 bytes, thereby guaranteeing deterministic throughput to complete fuzz tests within restricted project schedules.
- Optimization of Search Efficiency Under Physical Constraints: Even in environments with high reset overhead (e.g., =2.0 s), BB-FAST maintains efficient performance in locating error points through binary search. While the linear search cost of BSF increases sharply as the batch size grows, BB-FAST exhibits a gentle logarithmic increase, demonstrating robustness against system instability (presence of multiple errors) or large-scale batch environments.
5. Experimental Results
5.1. Experimental Setup
5.2. Experiment Process
5.3. Experiment Results
5.3.1. Measurement of Execution Time and Analysis of Results
5.3.2. Analysis of Performance in Error-Free Scenarios
5.3.3. Comparison and Discussion with Theoretical Analysis
6. Discussions and Limitations
7. Conclusions
- Solving the LIN Performance Bottleneck: By restructuring fuzzing requests into batch units, BB-FAST achieved a substantial reduction in execution time—specifically by 55.56% and 93.44%—proving that algorithmic optimization can effectively mitigate the physical limitations of low-bandwidth protocols.
- Ensuring Resilience in Error Scenarios: Through the integration of binary search logic, the framework maintains high efficiency under normal conditions while effectively suppressing time delays during error-induced resets to a logarithmic scale, ensuring a robust and uninterrupted testing process.
- Expanding the Scope of Practical Security Testing: This research provides a scalable solution to include LIN-based components, which were previously difficult to test rigorously, into the standard security verification suite. By maximizing test feasibility, BB-FAST ensures that core diagnostic protocols in modern cyber-physical automotive systems are thoroughly verified against potential threats.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- De, M.; Pesé, M.D.; Brooks, R.R.; Hasan, M. Contextualizing Security and Privacy of Software-Defined Vehicles: State of the Art and Industry Perspectives. arXiv 2024. [Google Scholar] [CrossRef]
- Anwar, A.; Anwar, A.; Moukahal, L.; Zulkernine, M. Security Assessment of In-Vehicle Communication Protocols. Vehicular Communications 2023, 44, 100639. [Google Scholar] [CrossRef]
- ISO/SAE 21434; Road Vehicles — Cybersecurity Engineering. ISO: Geneva, Switzerland, 2021.
- UN Regulation No. 155; Cyber Security and Cyber Security Management Syste. UNECE: Geneva, Switzerland, 2021.
- Yekta, A.R.; Loza, N.; Gramm, J.; Schneider, M.P.; Katzenbeisser, S. From ECU to VSOC: UDS Security Monitoring Strategies. The Nineteenth International Conference on Emerging Security Information, Systems and Technologies(SECURWARE 2025), 26-30 October 2025; IARIA, pp. 40–47. [Google Scholar] [CrossRef]
- Kayas, G.; Etas, Z.P.; Etas, D.G.; Etas, T.A.; Payton, J. AI-Assisted Vulnerability Analysis And Classification Framework for UDS on CAN-Bus Fuzzer. In Proceedings of the 10th escar USA - The World’s Leading Automotive Cyber Security Conference, 2023; ESCRYPT: Michigan, USA. [Google Scholar]
- Ruff, M. Evolution of Local Interconnect Network (LIN) Solutions. In 2003 IEEE 58th Vehicular Technology Conference(VTC 2003-Fall); IEEE Cat: Florida, USA, 2003; pp. 3382–3389. [Google Scholar] [CrossRef]
- ISO 17987-1; Road Vehicles — Local Interconnect Network (LIN) — Part 1: General Information and Use Case Definition. ISO: Geneva, Switzerland, 2025.
- ISO 17987-2; Road Vehicles — Local Interconnect Network (LIN) — Part 2: Transport Protocol and Network Layer Services. ISO: Geneva, Switzerland, 2025.
- ISO 17987-3; Road Vehicles — Local Interconnect Network (LIN) — Part 3: Protocol Specification. ISO: Geneva, Switzerland, 2025.
- Navet, N.; Simonot-Lion, F. Automotive Embedded Systems Handbook (Industrial Information Technology); 2008. [Google Scholar]
- ISO 14229-1; Road Vehicles — Unified Diagnostic Services (UDS) — Part 1: Application Layer. ISO: Geneva, Switzerland, 2020.
- ISO 14229-2; Road Vehicles — Unified Diagnostic Services (UDS) — Part 2: Session Layer Services. ISO: Geneva, Switzerland, 2021.
- ISO 14229-7; Road Vehicles — Unified Diagnostic Services (UDS) — Part 7: UDS on Local Interconnect Network (UDSonLIN). ISO: Geneva, Switzerland, 2022.
- Rathore, R.S.; Hewage, C.; Kaiwartya, O.; Lloret, J. In-Vehicle Communication Cyber Security: Challenges and Solutions. Sensors 2022, 22. [Google Scholar] [CrossRef]
- Luo, F.; Zhang, X.; Yang, Z.; Jiang, Y.; Wang, J.; Wu, M.; Feng, W. Cybersecurity Testing for Automotive Domain: A Survey. Sensors 2022, 22. [Google Scholar] [CrossRef] [PubMed]
- Hussain, I.; Reis, M.J.C.S.; Serôdio, C.; Branco, F. A Bibliometric Analysis and Visualization of In-Vehicle Communication Protocols. Future internet 2025, 17. [Google Scholar] [CrossRef]
- Yu, J.; Wagner, S; Wang, B.; Luo, F. A systematic mapping study on security countermeasures of in-vehicle communication systems. SAE International Journal of Transportation Cybersecurity and Privacy 2021, 4. [Google Scholar] [CrossRef]
- Cho, I.; Yoon, J.; Eom, S. Implementation of session and service scanner for UDS security testing. KASE 2023 Annual Spring Conference, 24-27 May 2023; pp. 893–897. [Google Scholar]
- Kim, H.; Jeong, Y.; Choi, W.; Lee, D.H.; Jo, H.J. Efficient ECU Analysis Technology Through Structure-Aware CAN Fuzzing. IEEE Access 2022, 10, 23259–23271. [Google Scholar] [CrossRef]
- Chen, Q.; Zikui, K.; Hu, K.; Peng, X.; Gong, S.; Chen, B.; Kong, Z.; Jiang, H.; Sun, B.; Lu, Y. Structure-Aware, Diagnosis-Guided ECU Firmware Fuzzing. Proc. ACM Softw. Eng 2025, 2, 871–893. [Google Scholar] [CrossRef]
- Faschang, T.; Macher, G. An Open Software-Based Framework for Automotive Cybersecurity Testing. In Communications in Computer and Information Science; Springer: Cham, Switzerland, 2023; Volume 1890, pp. 316–328. [Google Scholar] [CrossRef]
- Zeller, A.; Hildebrandt, R. Simplifying and Isolating Failure-Inducing Input. IEEE Transactions on Software Engineering 2002, 28, 183–200. [Google Scholar] [CrossRef]
- Kapugama, C.G. Extending Delta Debugging Minimization for Spectrum-Based Fault Localization. In 2026 IEEE 16th Annual Computing and Communication Workshop and Conference (CCWC); IEEE SE: Las Vegas, USA, Jan 2026; pp. 5–7. [Google Scholar] [CrossRef]
- McMinn, P. Search-Based Software Test Data Generation: A Survey. STVR 2004, 14, 105–156. [Google Scholar] [CrossRef]
- ISO 26262-3; Road Vehicles — Functional Safety — Part 3: Concept Phase. ISO: Geneva, Switzerland, 2018.
| Request SID | Response SID | Service | Details |
|---|---|---|---|
| 0x10 | 0x50 | Diagnostic Session Control | Control which UDS services are available |
| 0x11 | 0x51 | ECU Reset | Reset the ECU |
| 0x27 | 0x67 | Security Access | Enable use of security-critical services via authentication |
| 0x22 | 0x62 | Read Data By Identifier | Read data from targeted ECU |
| 0x23 | 0x63 | Read Memory By Address | Read data from physical memory |
| 0x2E | 0x6E | Write Data By Identifier | Program specific variables determined by data parameters |
| 0x3D | 0x7D | Write Memory By Address | Write information to the ECU’s memory |
| 0x31 | 0x71 | Routine Control | Initiate/stop routines |
| 0x34 | 0x74 | Request Download | Start request to add software/data to ECU |
| 0x35 | 0x75 | Request Upload | Start request to read software/data from ECU |
| 0x36 | 0x76 | Transfer Data | Perform actual transfer of data |
| 0x7F | Negative Response | Sent with a negative response code when a request cannot handled |
| Request SID | Service | Selection |
|---|---|---|
| 0x10 | DiagnosticSessionControl | ◎ |
| 0x11 | EcuReset | ○ |
| 0x19 | ReadDTCInformation | ○ |
| 0x22 | ReadDataByIdentifier | ◎ |
| 0x23 | ReadMemoryByAddress | ◎ |
| 0x27 | SecurityAccess | ◎ |
| 0x28 | CommunicationControl | ○ |
| 0x2C | DynamicallyDefineDataIdentifier | ◎ |
| 0x2E | WriteDataByIdentifier | ◎ |
| 0x31 | RoutineControl | ◎ |
| 0x34 | RequestDownload | ◎ |
| 0x35 | RequestUpload | ◎ |
| 0x36 | TransferData | ◎ |
| 0x3D | WriteMemoryByAddress | ◎ |
| 0x3E | TesterPresent | ○ |
| 0x83 | AccessTimingParameters | ○ |
| 0x85 | ControlDTCSetting | ○ |
| 0x86 | ResponseonEvent | ○ |
| 0x87 | LinkControl | ○ |
| 0x10 | DiagnosticSessionControl | ○ |
| Symbol | Description | Unit |
|---|---|---|
| Total number of fuzzing messages (packets) | ||
| Batch size | ||
| Transmission time for each fuzzing message | ||
| Session Re-entry and Polling Message Verification Time | ||
| ECU initialization time (power re-application, boot-up, etc.) |
| Method | Time-complexity (Big-O) |
|---|---|
| SDF | |
| BSF | |
| BB-FAST |
| Symbol | Default Value | Notes |
|---|---|---|
| 65,536 | 2-byte range (0x0000~0xFFFF) | |
| 10ms | Frame transmission time at LIN 20kbps | |
| 100ms | 0x10 Service polling latency included |
| Component | Specification | Role |
|---|---|---|
| Laptop | Intel(R) Core(TM) Ultra 7, 32GB RAM | developing tool, controlling fuzz testing scripts |
| PEAK PLIN-USB | supports all LIN specifications | USB to LIN bus converter |
| Automotive ECU | LIN-based Electronic Control Unit | experimental target |
| Power Relay | 12V/5A, 1-Channel Relay | ECU power relay and reset |
| Component | Specification | Role |
|---|---|---|
| Operating System | Windows 11 Pro | |
| Language | Python 3.13.9 | script developing, test controlling |
| Module | PLinApi | LIN communication API |
| numpy, matplotlib | data processing, simulation and result plotting | |
| Monitoring | PLIN-View | real-time LIN monitoring |
| Session | Service ID | Execution Time (SDF) | Execution Time (BSF) | Execution Time (BB-FAST) |
|---|---|---|---|---|
| 0x01 | 0x22 | 121 min 48sec | 7min 53sec | 7min 51sec |
| 0x02 | 0x22 | 17 min 56sec | 7min 50sec | 7min 49sec |
| 0x03 | 0x22 | 121 min 48sec | 7min 53sec | 7min 51sec |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




