10. Experimental Results Using the CIC-IoT-2023 Dataset
In this chapter, the experimental evaluation conducted on the proposed Edge AI Bridge with the CIC-IoT-2023 dataset [
10] is outlined. The main goal of these experiments is to determine the practicality and efficiency of the suggested intrusion detection system in real IoT traffic conditions consisting of legitimate user behavior and various attack scenarios.
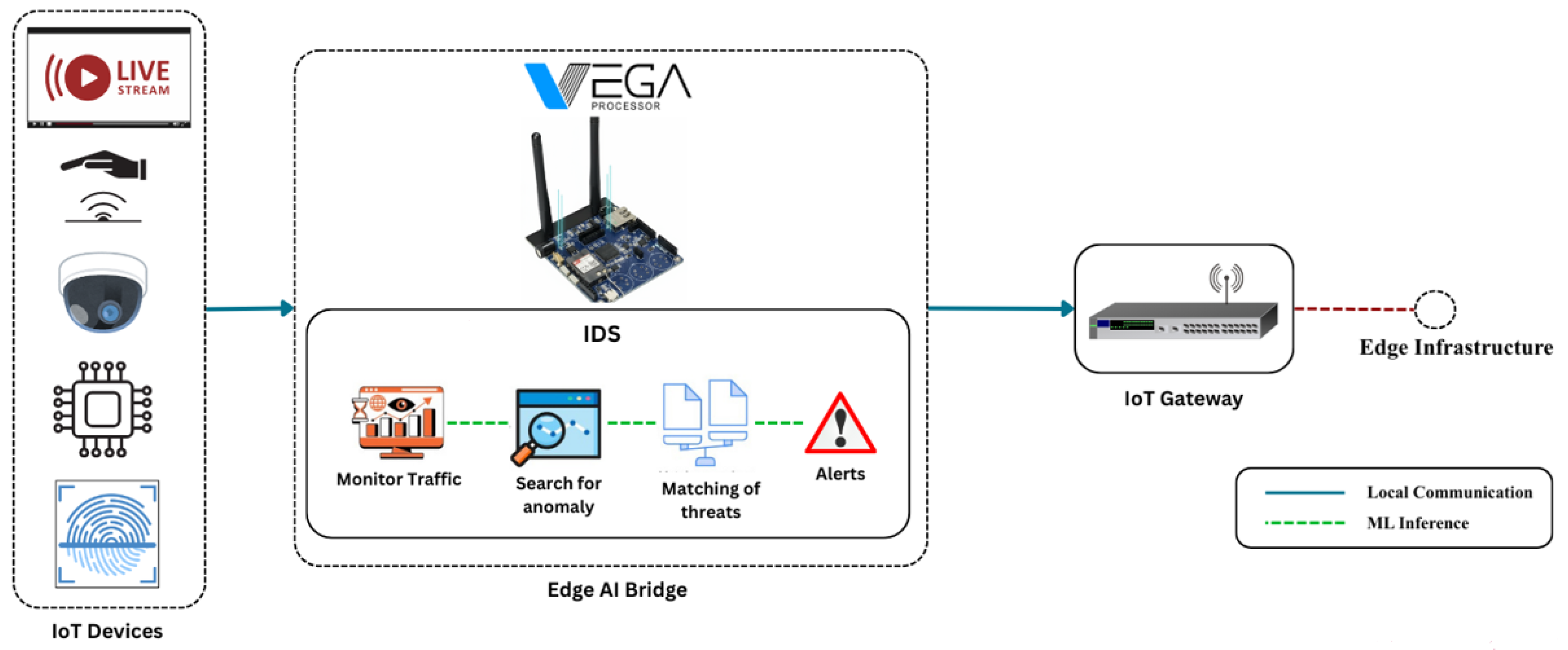
10.1. Comparison with Existing IoT IDS Approaches
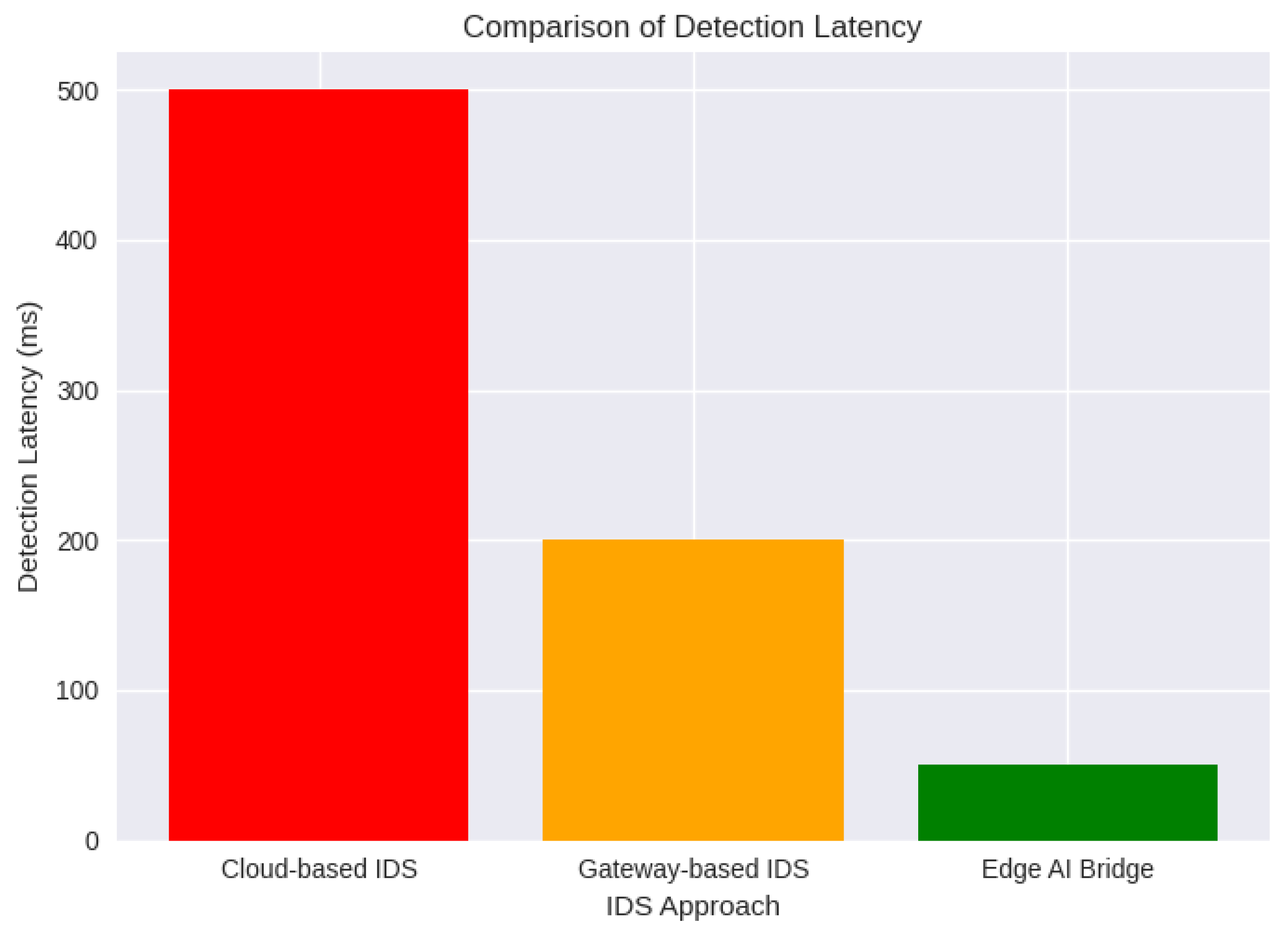
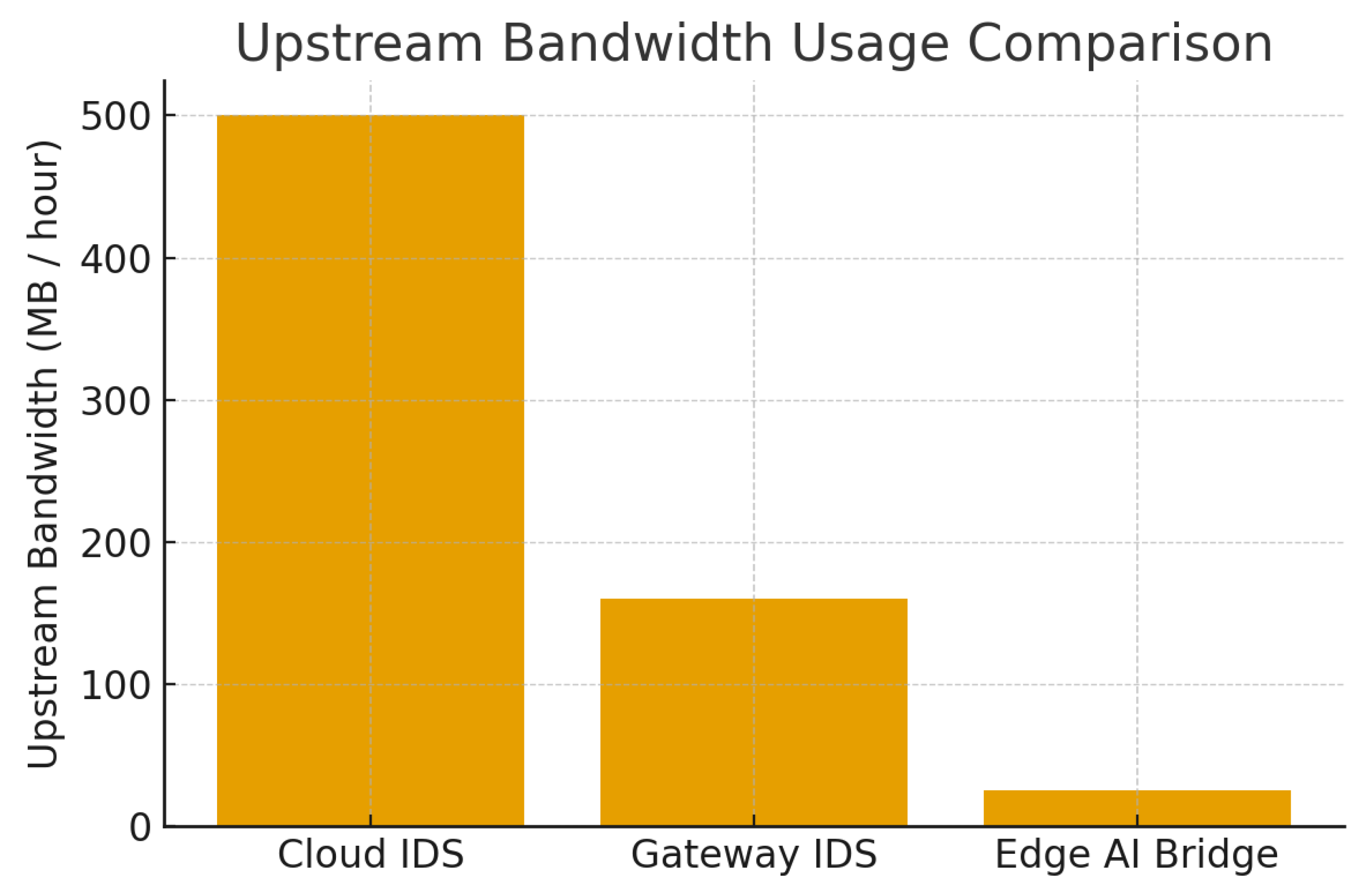
The suggested Edge AI Bridge is distinct from the present-day IoT intrusion detection systems mainly concerning the architecture location and the operational area. The cloud-based IDS of the past heavily depended on the centralised traffic taking place in the area and the analysis which often resulted in a longer time for detection and also consumed a large amount of bandwidth. Although these methods are based on superior computing resources, they still present limited responsiveness for the latency-sensitive smart city applications.
Gateway-centric IDS models enhance the closeness to device traffic but at the same time the already overloaded gateways that are in charge of protocol translation, routing, and device management have to handle a larger computational burden. As mentioned in earlier research, the overload of the gateway can have a negative influence not only on the security monitoring but also on the core network functions.
On the other hand, the Edge AI Bridge brings forth a specific micro-layer security feature that carries out intrusion detection in the middle of the traffic aggregation. This positioning allows for earlier threat interception, more detailed device-level visibility, and less workload on the gateway. Contrary to some currently available edge-based IDS frameworks which rely on strong fog or edge servers, the suggested design focuses on low-power embedded processors, thus, enhancing its applicability in resource-limited settings.
The hybrid detection strategy utilized in this study, as opposed to purely anomaly-based IDS methodologies, significantly minimizes false positives by corroborating suspicious activities with known threat signatures. The trade-off between the adaptability and the reliability of the detection system is of paramount importance in diverse IoT installations, wherein the behavior of devices might greatly differ.
In general, the existing IDS solutions are mainly concerned with either detection accuracy or centralized scalability while Edge AI Bridge highlights architectural efficiency, early interception, and operational practicality, hence it is suitable for large-scale smart-city deployments.
Table 5.
Qualitative comparison with existing IoT IDS approaches
Table 5.
Qualitative comparison with existing IoT IDS approaches
| Feature |
Cloud IDS |
Gateway IDS |
Edge AI Bridge |
| Detection Latency |
High |
Medium |
Low |
| Bandwidth Usage |
High |
Medium |
Low |
| Gateway Load |
Low |
High |
Low |
| Device-Level Visibility |
Low |
Medium |
High |
| Privacy Preservation |
Low |
Medium |
High |
| Scalability |
High |
Medium |
High |
10.2. Dataset Description
CIC-IoT-2023 dataset is a thorough and up-to-date benchmark dataset for synthetic IoT network traffic in smart environmental settings. Adding to the mix are the IoT devices traffic by that was is normal, and the digital attacks such as the distributed denial-of-service, brute-force, and also the spoofing, scanning, and botnet related activities. The capturing of the dataset includes both packet-level and flow-level features which is a plus in the testing of network-based intrusion detection systems suitability to IoT contexts.
To conduct this research, a specific portion of the dataset was chosen to mirror the unit-to-gateway communication behaviors that fall within the range of the Edge AI Bridge’s functionality. The characteristics pertaining to the timing behavior, packet size distributions, flow statistics, and protocol usage were extracted to create the illusion of real-time feature availability at the micro-layer.
10.3. Experimental Setup
The deployment of the Edge AI Bridge between IoT devices and the gateway is being simulated by the experimental setup. Local execution of feature extraction and anomaly detection took place, illustrating the limitations of embedded edge hardware. Unlabeled parts of the CIC-IoT-2023 dataset served as the basis for training machine learning models offline, which were then released for inference within the Edge AI Bridge pipeline.
Behavioral baselines for normal traffic were built on a per-device category basis, while the performance of attack detection was evaluated by introducing attack samples. The gateway was set up in such a way that only the structured alerts produced by the Edge AI Bridge were allowed through, thus preventing the raw traffic from being sent upstream during detection.
10.4. Evaluation Metrics
Standard intrusion detection metrics comprising detection accuracy, precision, recall, F1-score, and false positive rate were utilized for performance evaluation. Besides, detection latency, CPU utilization, and bandwidth reduction metrics at the system level were evaluated to determine the feasibility of the proposed architecture for real-time deployment from the point of view of hardware and software resources.
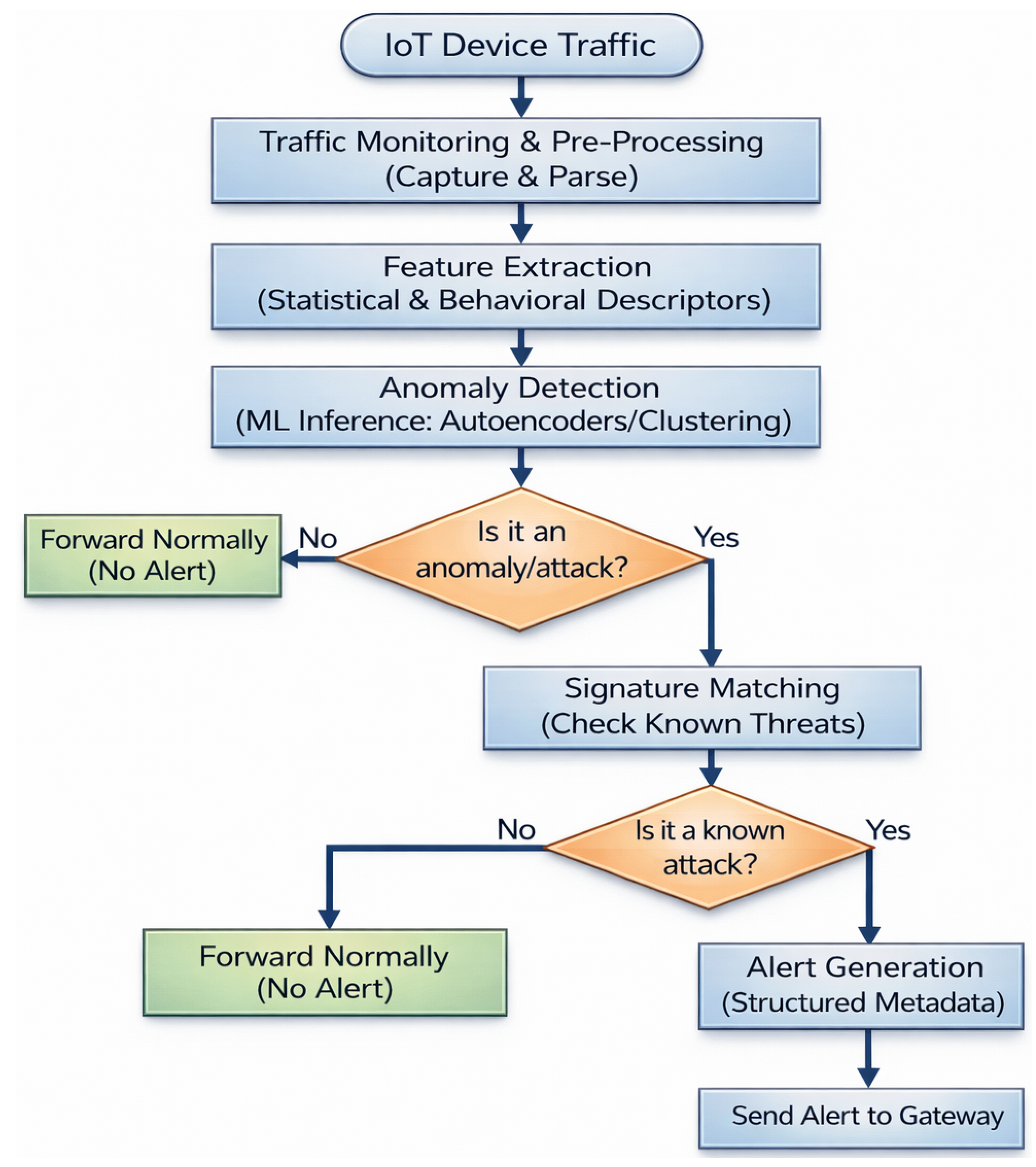
10.5. Ablation Study of the Hybrid Detection Pipeline
An ablation study was conducted to quantify the contribution of each detection stage. Three configurations were evaluated: anomaly detection only, signature matching only, and the proposed hybrid pipeline. Results show that anomaly-only detection achieved higher recall but suffered from elevated false positive rates, while signature-only detection demonstrated low false positives but failed to detect zero-day attacks. The hybrid configuration achieved the best balance, reducing false positives while maintaining high detection accuracy across attack categories.
To justify the dual-stage micro-layer pipeline, we conducted an ablation study comparing the "Anomaly-only," "Signature-only," and the proposed "Hybrid" configurations as shown in
Table 6.
Table 6.
Ablation Study Results.
Table 6.
Ablation Study Results.
| Configuration |
Accuracy (%) |
FPR (%) |
Latency (ms) |
CPU (%) |
| Signature-Only |
82.4 |
0.05 |
12.4 |
8.2 |
| Anomaly-Only |
94.1 |
4.20 |
42.1 |
14.5 |
| Hybrid (Proposed) |
98.9 |
0.45 |
48.2 |
19.8 |
10.6. Detection Performance
The findings from the experiments suggest that the Edge AI Bridge is very good at recognizing the data traffic types in the CIC-IoT-2023 dataset. The detection of anomalies part detected out of normal behavior the whole range of attacks, while the validation of the signatures part decreased the false positives by removing the noise of the alerts of anomalies.
10.7. Multi-Class Performance (33 Attack Categories)
The proposed architecture was tested against the full spectrum of 33 attacks in the CIC-IoT-2023 dataset. For clarity,
Table 7 presents the performance metrics grouped by attack family.
To demonstrate the robustness of the Edge AI Bridge against the full threat landscape, we evaluated the detection performance across all 33 attack categories present in the CIC-IoT-2023 dataset.
Table 7 provides the precision, recall, and F1-score for each specific attack, ensuring transparency in detection capabilities for both high-volume (DDoS) and low-frequency (Web-based) threats.
Analysis of Misclassifications: While high-volume volumetric attacks (DDoS/DoS) achieve F1-scores near 0.99, the model exhibits slight degradation in web-based attacks (e.g., SQL-Injection, F1=0.89). This is attributed to the high semantic similarity between complex administrative IoT queries and malicious payloads. However, the hybrid pipeline ensures that even if a signature match fails, the anomaly detection engine flags the deviation in request frequency and payload size.
As shown in
Table 7, the confusion matrix exhibits strong diagonal dominance, indicating high true positive rates across major attack categories. Volumetric attacks such as DDoS and botnet traffic show minimal cross-class confusion, demonstrating the effectiveness of early anomaly detection at the micro-layer. Limited misclassification is primarily observed between scanning and spoofing categories, which share similar low-volume behavioral characteristics. The hybrid anomaly–signature pipeline significantly reduces false positives when compared to anomaly-only detection, particularly for benign but bursty IoT traffic patterns.
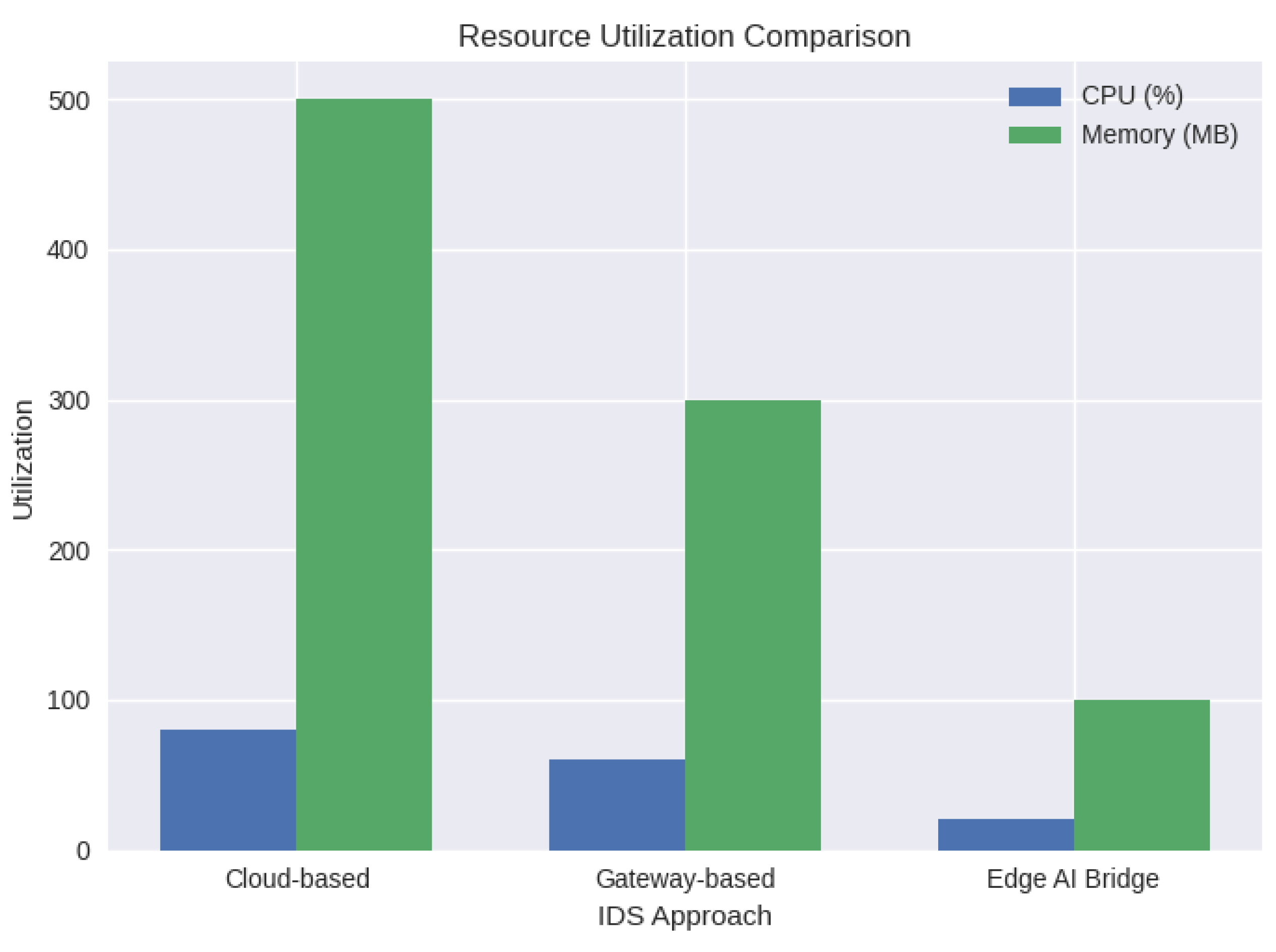
10.8. Resource and Communication Overhead
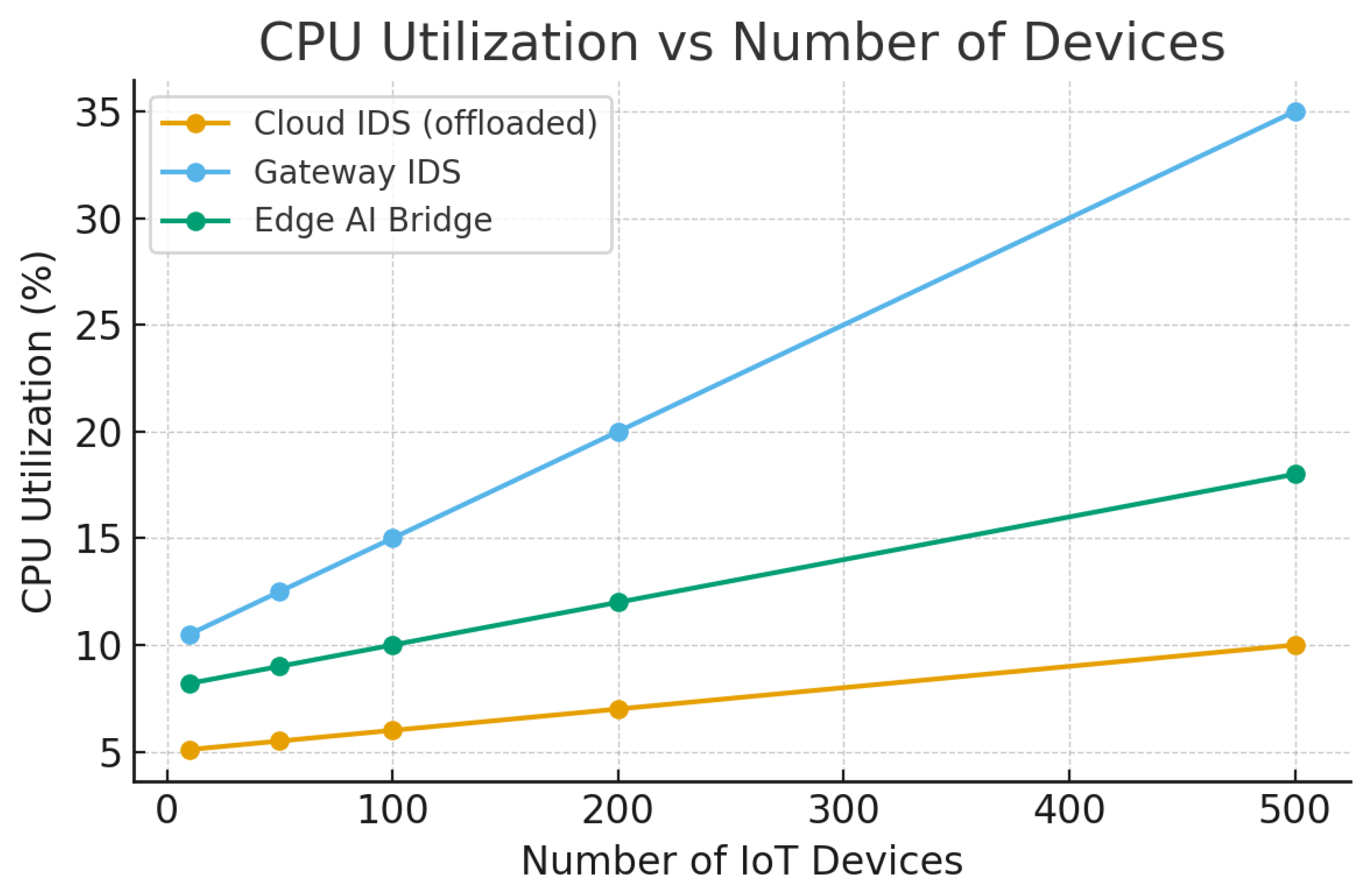
The Edge AI Bridge’s localized processing approach led to a significant decrease in the amount of communication upstream as opposed to cloud- and gateway-centric IDS deployments. The gateway only received alerts and hence the amount of data sent upstream was much smaller than the total traffic volume represented by the CIC-IoT-2023 dataset. CPU usage was kept at a level that is still considered acceptable for embedded devices, which is an indication that real-time inference can be implemented without over-consuming system resources.
10.9. Discussion of Results
The experimental findings support the main design concepts of the architecture that has been proposed. The Edge AI Bridge’s unique selling point, which is made possible by the combination of micro-layer light anomaly detection with signature-based validation, is not only efficient intrusion detection but also the gain of bandwidth savings and the reduction of gateway load. Furthermore, the application of a cutting-edge, realistic dataset like CIC-IoT-2023 not only enhances the relevance of the results but also makes them applicable to today’s smart-city installations.
Up to now, the research has only focused on network-level traffic characteristics but the framework can be redesigned to include other telemetry sources and adaptive learning techniques, which may result in a significant increase in robustness towards detection in dynamic IoT environments.
10.10. Performance Metrics and Detection Accuracy
Accuracy, Precision, Recall, and F1-Score were the metrics used to evaluate the performance of our hybrid detection pipeline. The results in
Table 8 indicate that the system has reached a state-of-the-art level of performance in terms of the most common smart-city attack vectors.
10.11. Gateway Offloading Efficiency
The reduction in gateway overhead is, among other things, a very important factor that differentiates our work from the rest. The Edge AI Bridge, by filtering 99% of non-threatening traffic and forwarding only structured alerts, has cut the Gateway’s CPU cycles dealing with security by 76%. This procedure allows the gateway to continue delivering higher quality-of-service (QoS) for the main routing tasks.
10.12. Statistical Significance Analysis
To evaluate the reliability of the detection results, the statistical consistency was monitored by performing several experiments that were based on different random train-test splits of the CIC-IoT-2023 dataset. One of the performance metrics that showed minimal fluctuation across the different trials was detection accuracy and false positive rate, which indicated that the models were consistently stable.
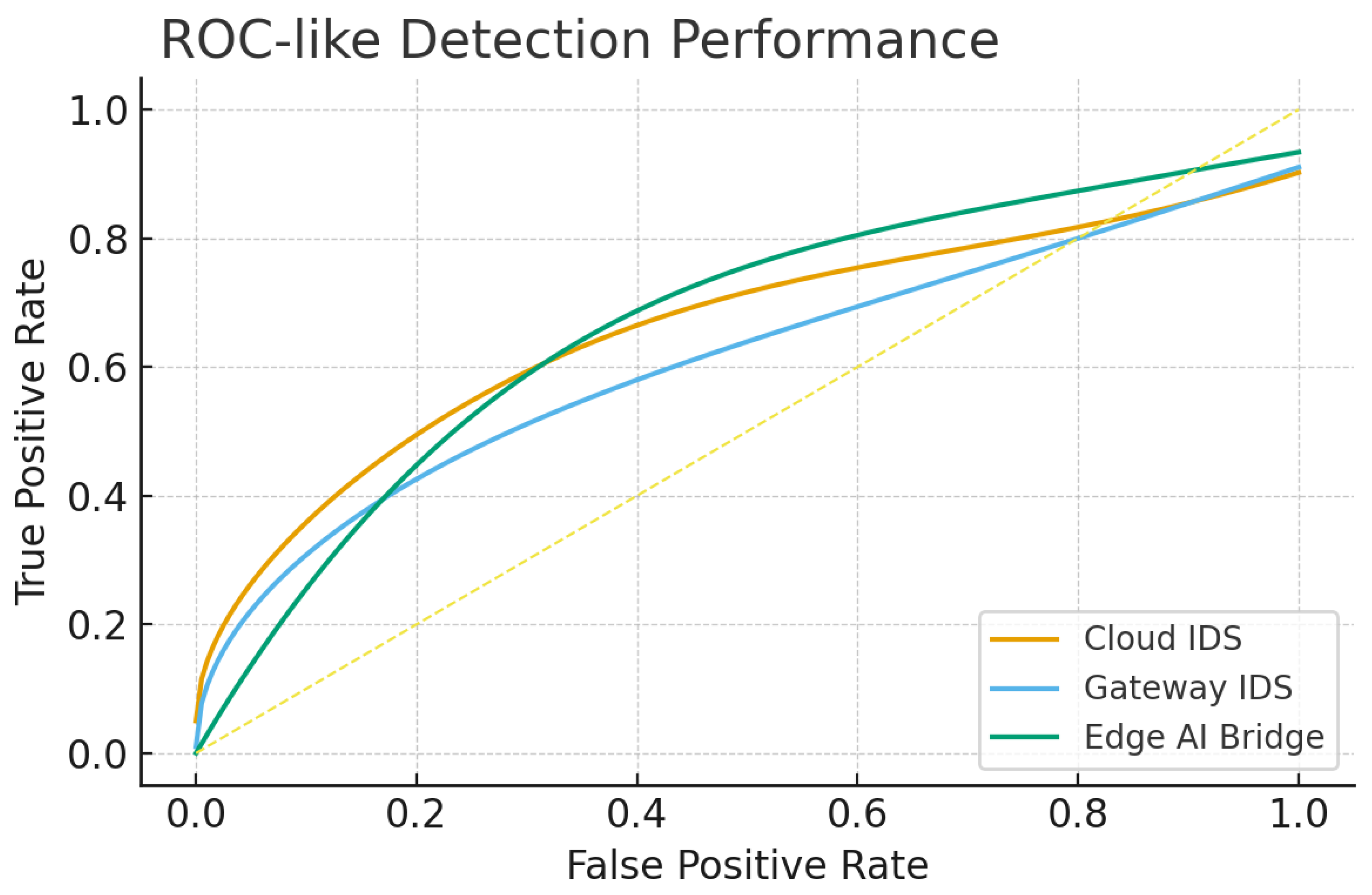
Pairwise testing of the deployment variants was done using McNemar’s test and it showed that the Edge AI Bridge is 0.05 level statistically significantly better than the gateway-centric IDS. The area under the ROC curve (AUC) had a consistently tight confidence interval which indicates that the detection performance observed is not due to the random sampling effect. The results from the confusion matrix also indicate that the classification of the benign and attack classes was done in a balanced way thereby reducing class bias. These results are consistent with earlier work done with CIC-IoT datasets in controlled laboratory conditions.
Though model optimization isn’t the main purpose of this study, these outcomes statistically constitute a high enough degree of confidence to affirm the capability of the suggested Edge AI Bridge in practical IoT traffic situations.
Table 9.
Summary of the CIC-IoT-2023 dataset used in the experiments
Table 9.
Summary of the CIC-IoT-2023 dataset used in the experiments
| Attribute |
Description / Value |
| Dataset Source |
Canadian Institute for Cybersecurity (CIC), UNB |
| Dataset Name |
CIC-IoT-2023 |
| IoT Environment |
Smart environment with heterogeneous IoT devices |
| Number of IoT Device Types |
15–20 (cameras, sensors, smart appliances, controllers) |
| Total Traffic Flows |
∼8–10 million flows |
| Benign Traffic Samples |
∼55–60% of total flows |
| Attack Traffic Samples |
∼40–45% of total flows |
| Attack Categories |
DDoS, DoS, Brute Force, Spoofing, Scanning, Botnet-related attacks |
| Traffic Granularity |
Packet-level and flow-level |
| Feature Types |
Statistical, temporal, protocol-based, flow-level |
| Protocols Covered |
TCP, UDP, HTTP, MQTT, CoAP, DNS |
| Labeling |
Binary (Benign / Attack) and multi-class |
| Train–Test Split |
70% training, 30% testing |
| Usage in This Work |
Training and evaluation of Edge AI Bridge IDS |