Submitted:
30 January 2026
Posted:
02 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Literature Review
3. The Theoretical Foundation of the Zoned Role-Based (ZRB) Model
3.1. Core Formal Definitions
- Zs—the (possibly empty) set of child sub-zones ofz. IfZs = ∅, the zone is a leaf.
- Rz— the non-empty set of roles defined within zone z.
- Az— the set of applications provisioned for use within zone z.
- Uz— the set of users affiliated with zone z. (Users in sub-zones propagate upward—see below.)
- Z is the set of all zones,
- E is the set of directed edges zparent’ zchild representing parent–child relationships.
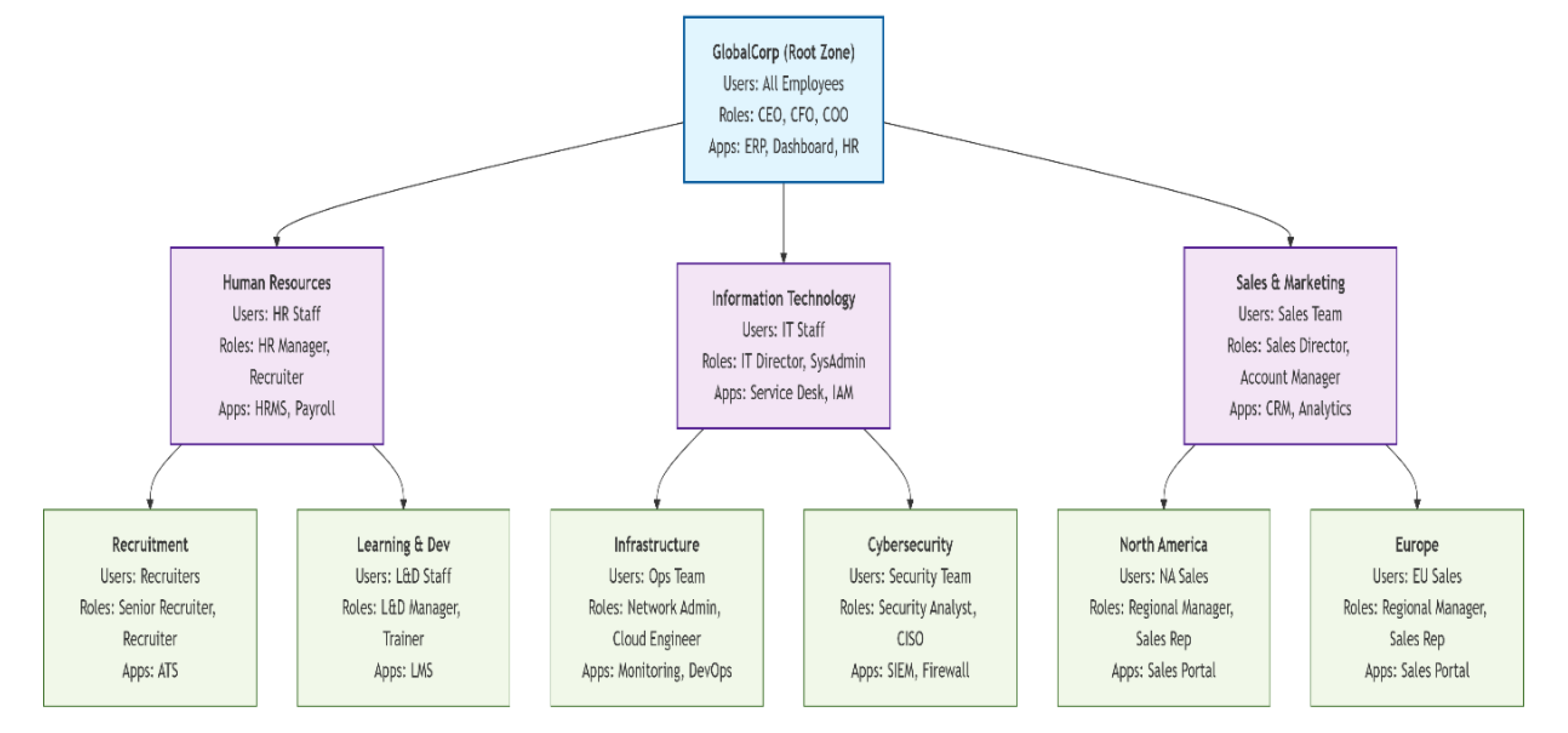
- Represents the entire enterprise.
- Contains all users, high-level roles (CEO, CFO, COO), and enterprise-wide applications (ERP, Dashboard, HR system).
- Parent to all department zones.
- Human Resources (HR): Manages personnel, recruitment, and development.
- Information Technology (IT): Oversees technology infrastructure and security.
- Sales & Marketing (Sales): Handles sales operations and customer engagement.
- HR → Recruitment & Learning & Development teams.
- IT → Infrastructure & Cybersecurity teams.
- Sales → Regional sales teams (North America & Europe).
- Hierarchical Containment: Child zones are contained within parent zones (e.g., Recruitment ⊆ HR ⊆ GlobalCorp).
- User Propagation: Users in child zones are also members of parent zones (e.g., a Recruiter belongs to both Recruitment and HR zones).
- Role Specialization: Roles become more specific at lower levels (e.g., CEO → HR Manager → Senior Recruiter).
- Application Scoping: Applications are provisioned to appropriate zones (e.g., ATS only in Recruitment zone).
- Permission Inheritance: Roles in child zones may inherit relevant permissions from ancestor zones (e.g., HR Manager inherits some permissions from CEO context).
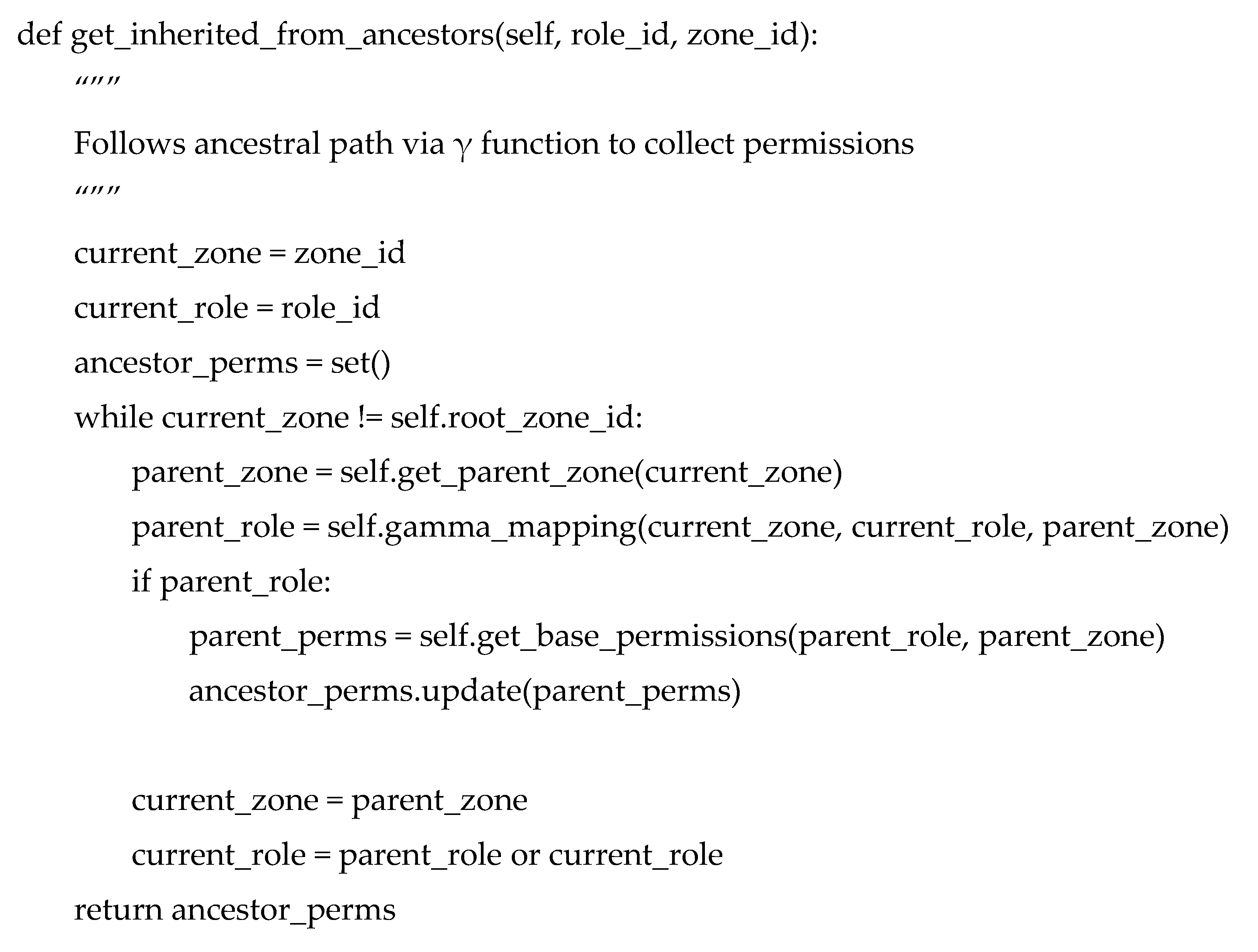
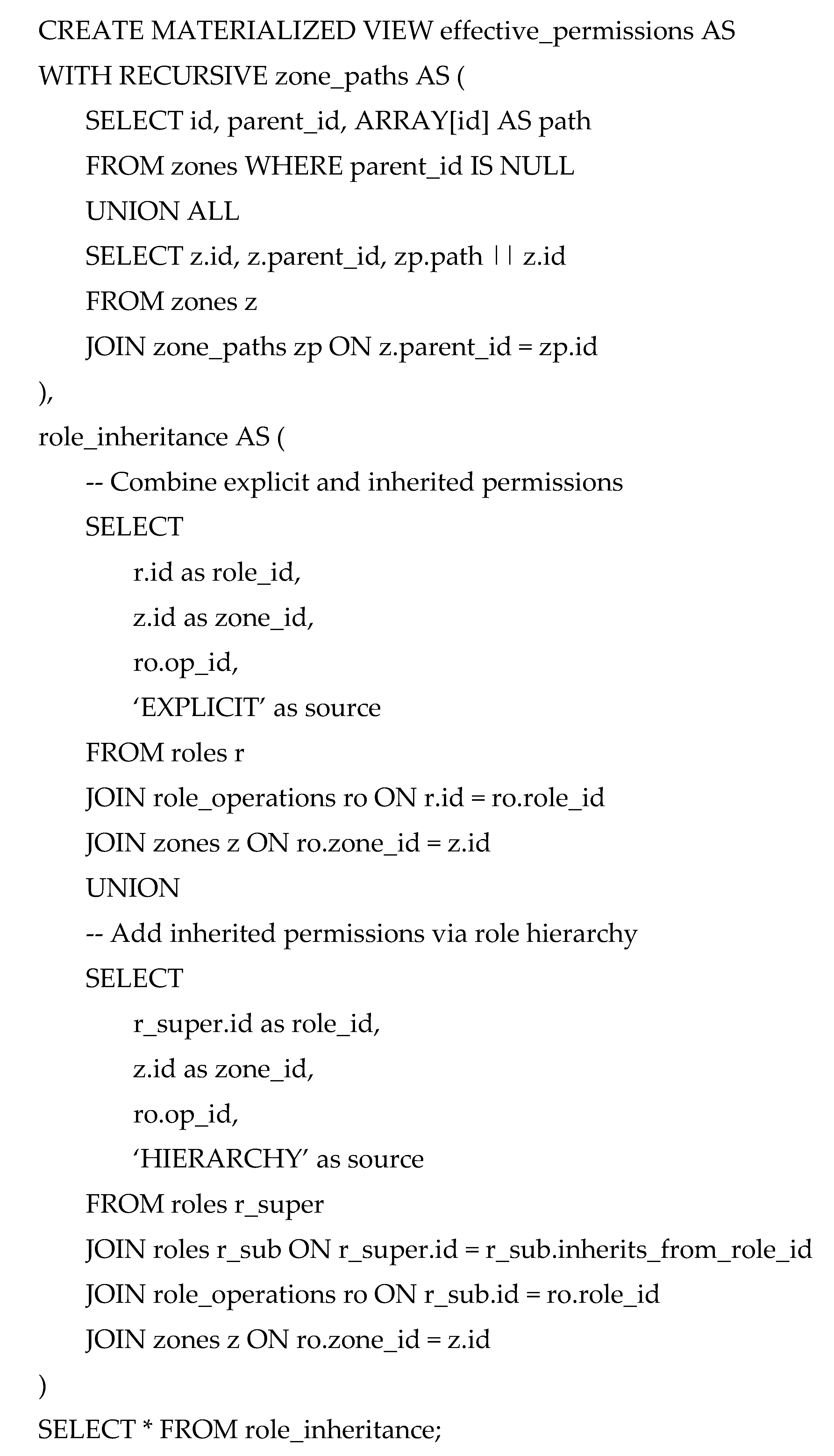
3.2. Hierarchical Permission Inference and the Zone Tree
3.3. Formal Specification of Access Control Matrices
- A 3-dimensional matrix Mψ, or
- A set of tuples (u,z,r)
- A user may have multiple active role-zone pairs simultaneously, supporting cross-functional or multi-zone responsibilities.
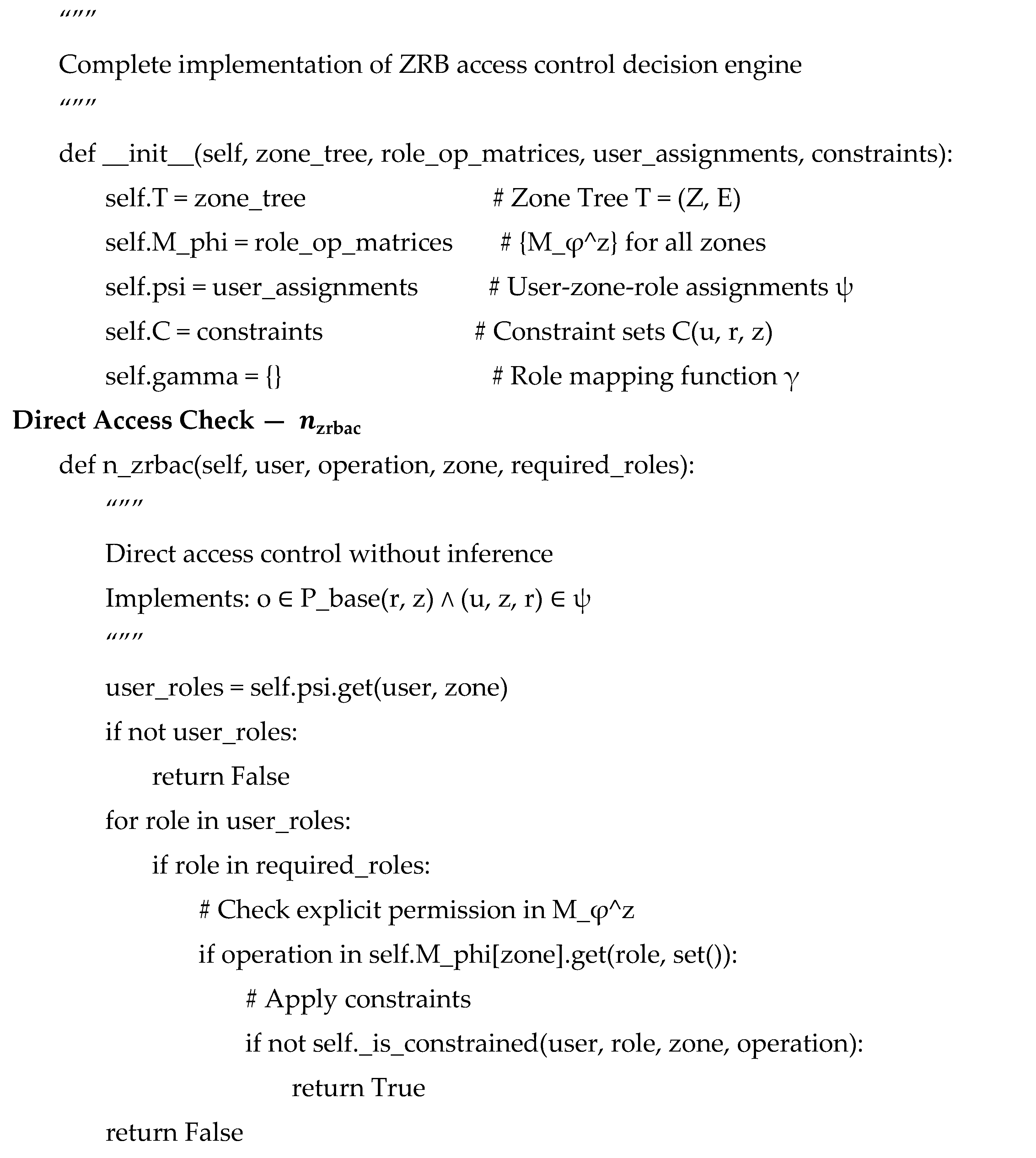
3.4. The Access Control Decision Function
- Zone-scoped roles
- User–zone–role assignments
- Intra- and interzone inheritance
- Explicit constraints
4. The ZRB Methodology for Integrated Enterprise System Design
- Zone lifecycle management (create/modify/deprecate zones in T);
- Role & Operation management (maintain );
- User–Zone–Role assignments (maintain ); and
- Constraint policy management (maintain ). This supports safe evolution as organizations change (e.g., adding a sub-zone affects its subtree and local matrices while preserving global integrity)
- Methodological Flexibility and Evolution
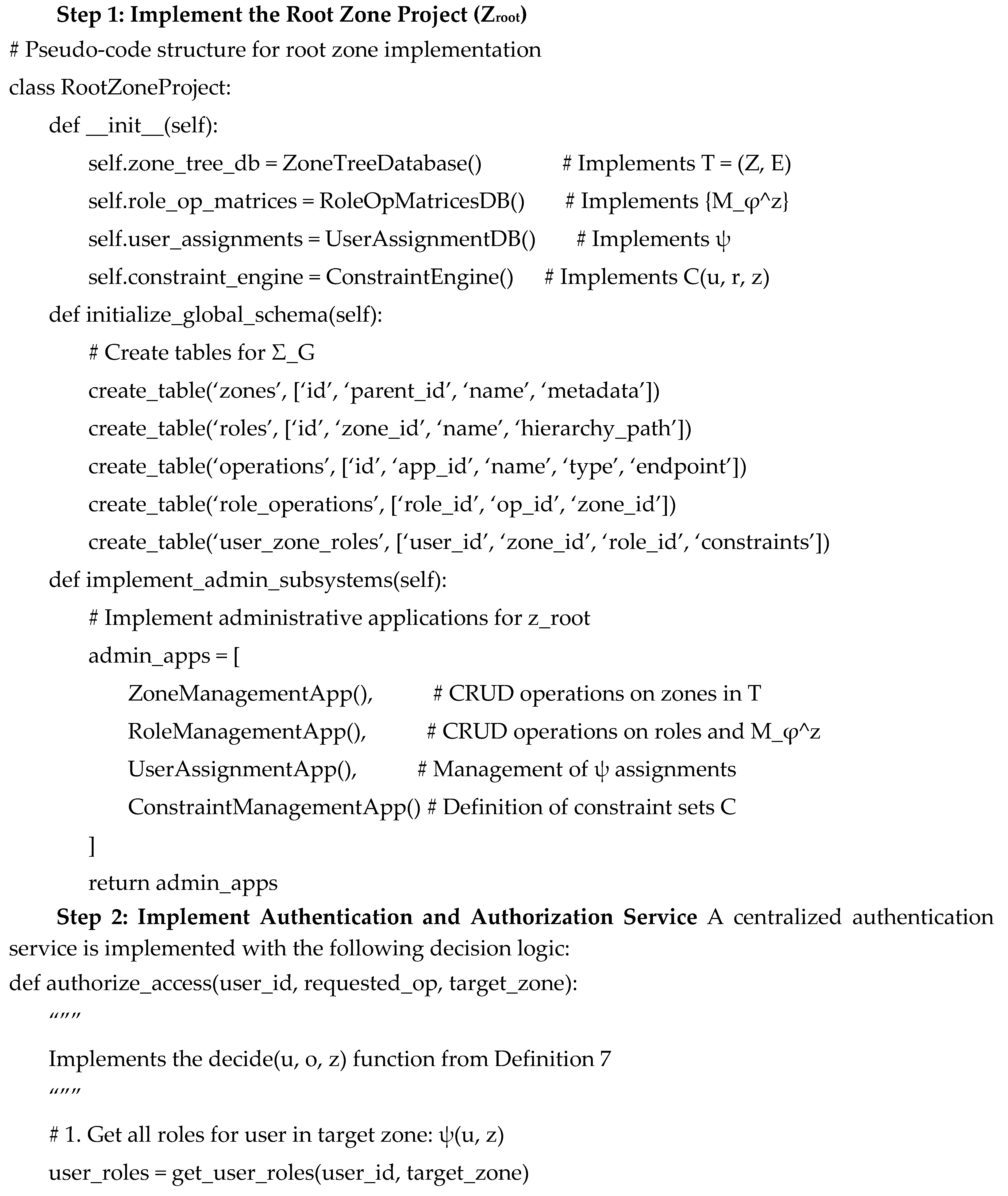
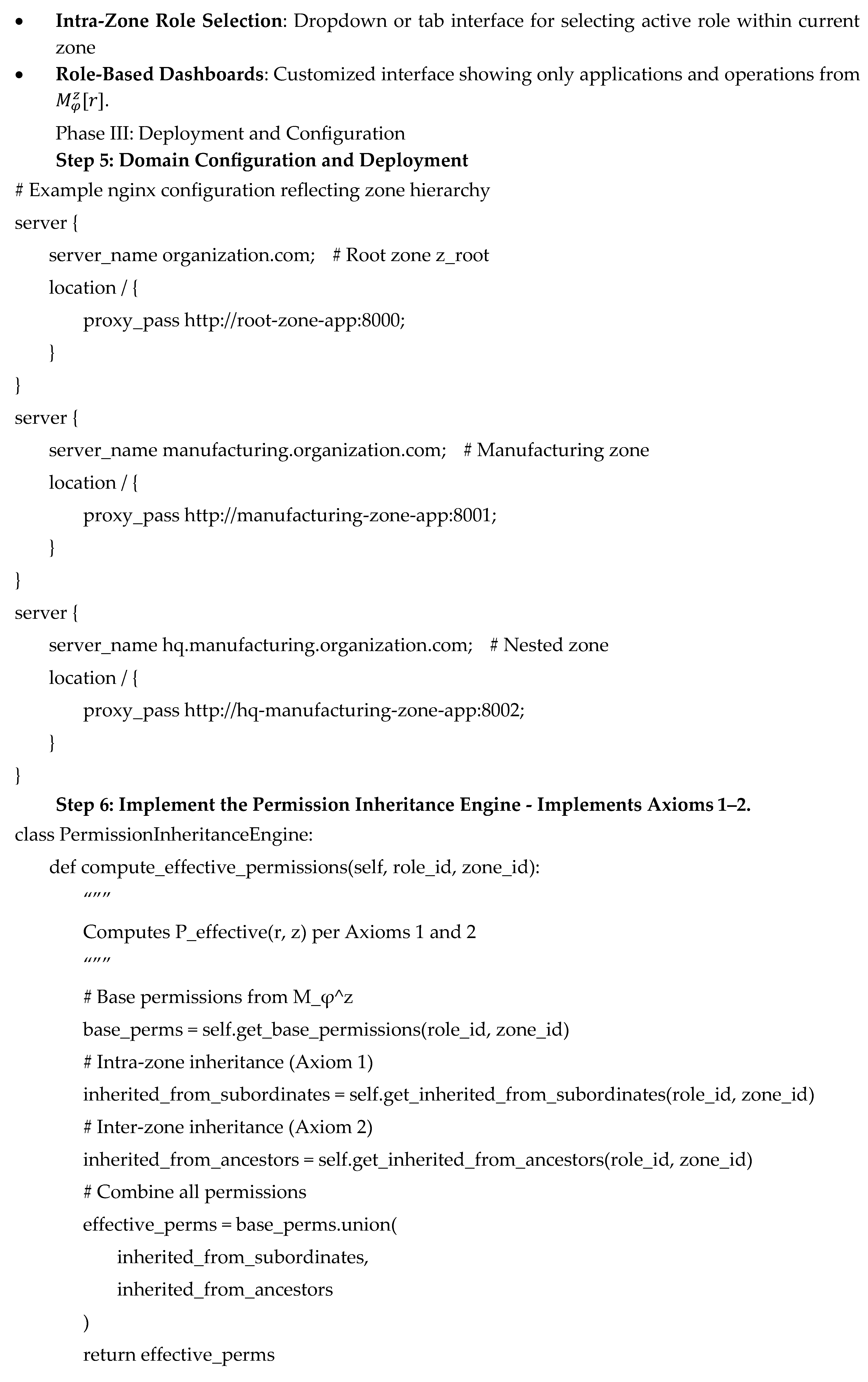
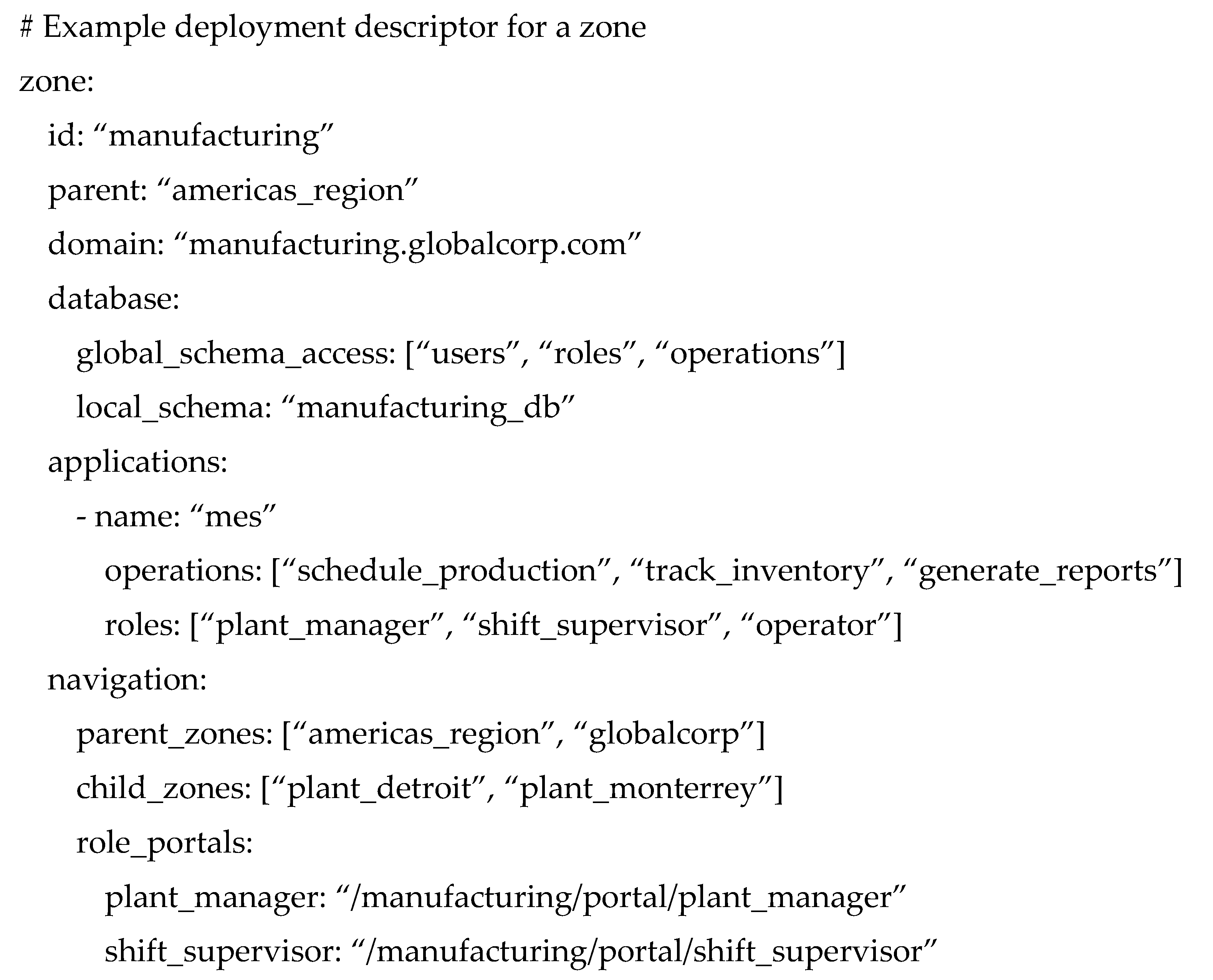
5. Implementation of ZRB-Based Enterprise Systems
5.1. Architectural Mapping: From Organizational Model to Web Infrastructure
- Root zone → primary domain Example: https://organization.com for
- Child zone → subdomain following the containment path Example: https://manufacturing.organization.com for Root → Manufacturing
- Zones (the Zone Tree
- Roles (with hierarchy
- Operations
- Users
- Role–Operation Assignments (matrices )
- User–Zone–Role Assignments (function )
- Constraints (sets
5.2. Implementation Phases and Steps
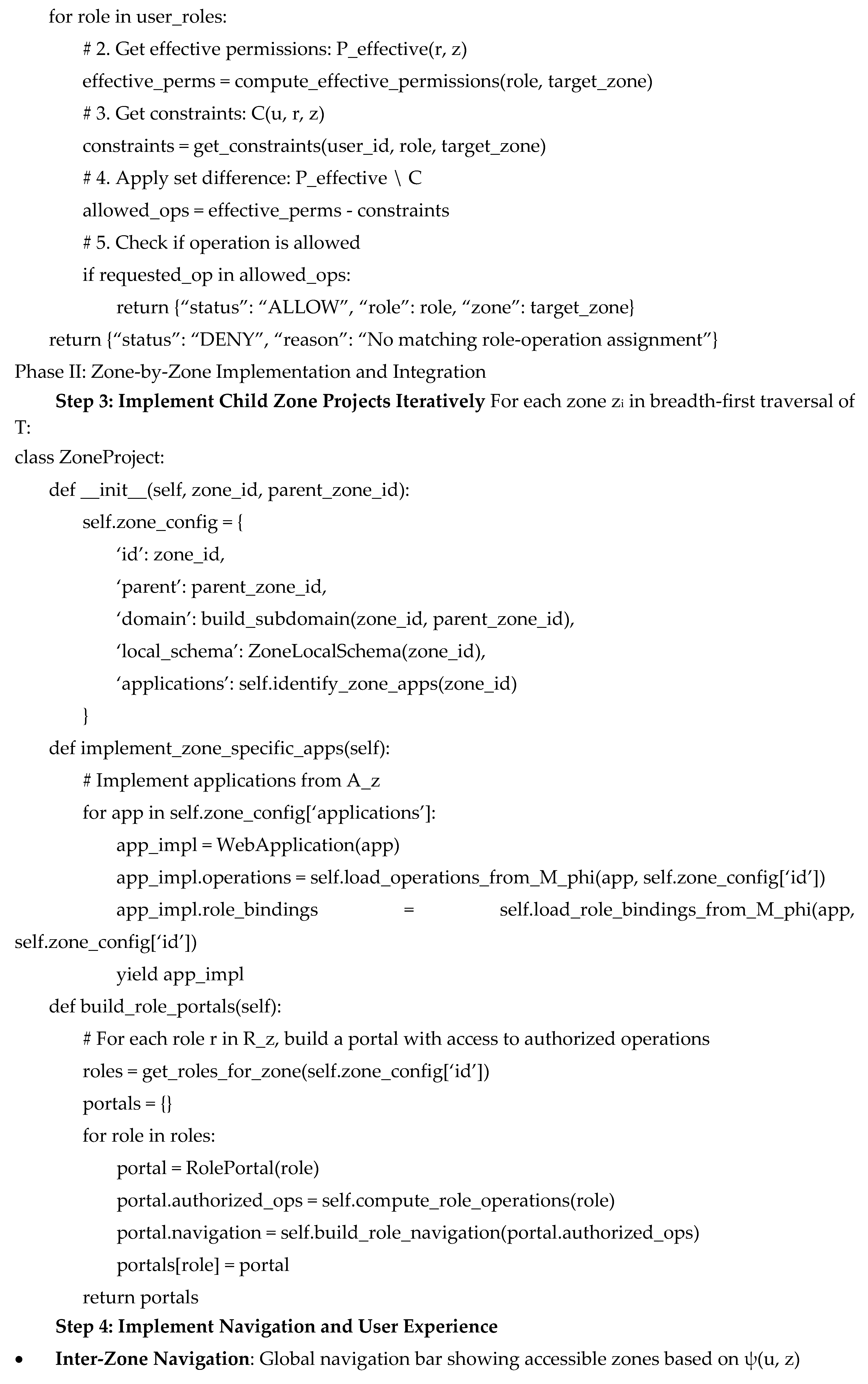
5.3. Deployment Strategy and Lifecycle Management
- Deploy root zone first
- Implement and deploy child zones according to business priority
- Each zone uses independent CI/CD pipelines but integrates with global services
5.4. Benefits for Scalability and Maintenance
- Independent development of zone projects
- Independent deployment of unrelated zones
- Independent scaling based on zone workload
- Security isolation among zones
- Direct mapping of organizational changes to system changes (e.g., new zone → new project + domain; role change → matrix update; policy change → constraint update)
6. Maintenance and System Evolution in ZRB-Based Enterprise Systems
6.1. Zone-Level Structural Maintenance
- creating new departments or project teams,
- restructuring existing units,
- merging or splitting zones, or
- retiring obsolete organizational entities
6.2. Role and Permission Evolution
- adding new specialized roles within a zone,
- modifying the responsibilities of existing roles,
- adjusting hierarchical relationships ,
- updating permission mappings for evolving applications, and
- ensuring consistency with inherited permissions via the mapping function .
6.3. User Lifecycle and Assignment Maintenance
- reassigning users to new roles within the same zone,
- granting temporary roles (e.g., acting manager),
- revoking obsolete roles upon job transitions,
- disabling or reactivating user access, and
- applying temporary or permanent restrictions through constraint sets .
6.4. Application Lifecycle Maintenance
- adding new operations to reflect new business processes,
- refining or renaming existing operations,
- migrating applications between zones as organizational responsibilities shift,
- deprecating outdated functionality, and
- updating operation types or endpoints in response to implementation changes.
6.5. Policy, Security, and Constraint Maintenance
- introducing new separation-of-duty (SoD) constraints,
- applying temporary restrictions for compliance audits,
- blocking inherited permissions for external or contract users,
- adjusting access windows for time-based policies, and
- responding to emerging threats by tightening security boundaries.
6.6. Performance, Monitoring, and Optimization Maintenance
- allowing zone-specific performance tuning (e.g., cache TTLs, load balancing),
- supporting independent scaling of zone applications,
- enabling targeted optimization of frequently accessed permission paths,
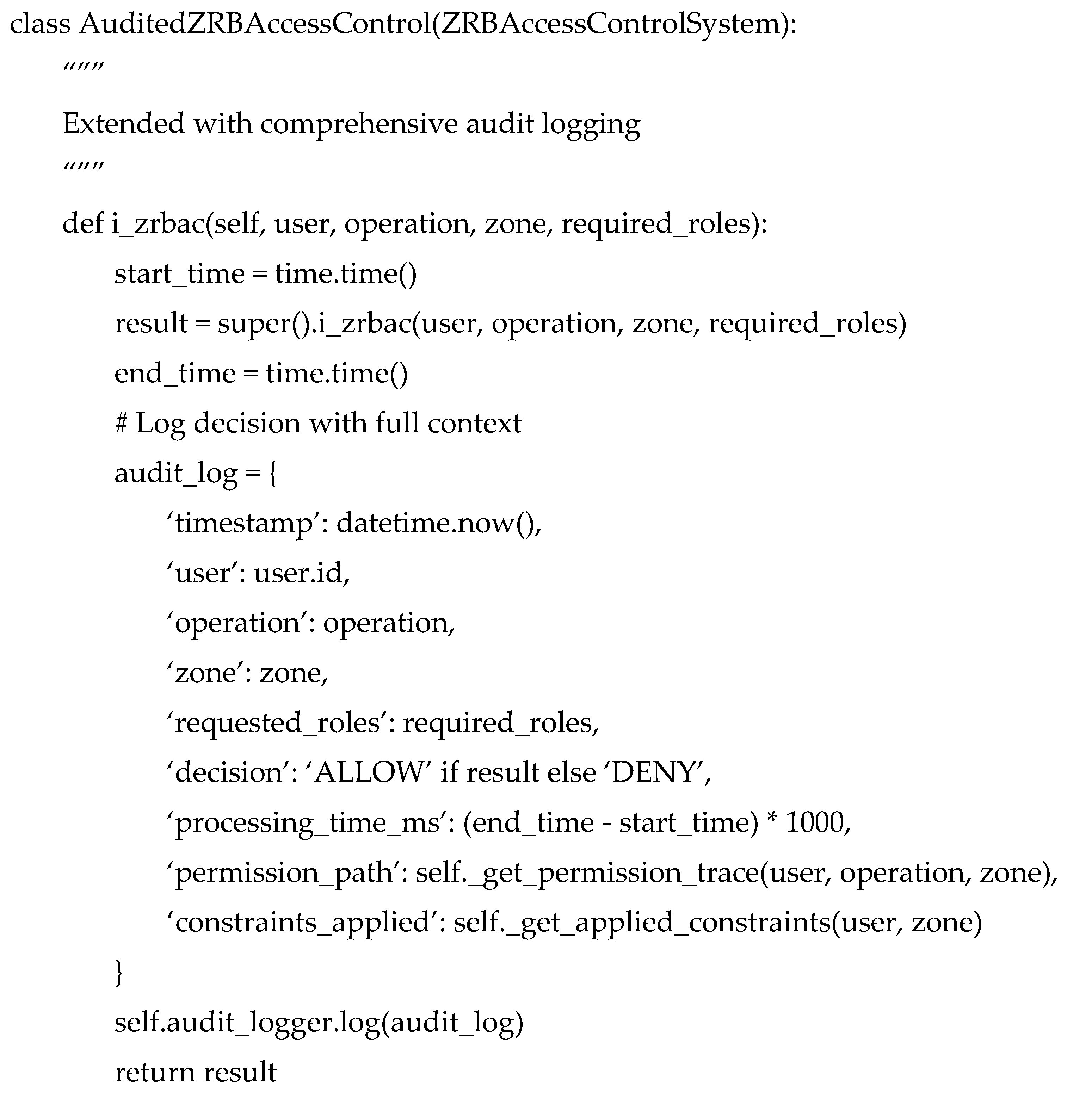
- facilitating fine-grained audit logging for analysis and compliance, and
- providing incremental verification to ensure policy consistency after updates.
- high maintainability,
- minimal unintended side effects during updates,
- clear and predictable propagation of changes,
- improved security governance,
- strong alignment with organizational evolution, and
- reduced administrative overhead.
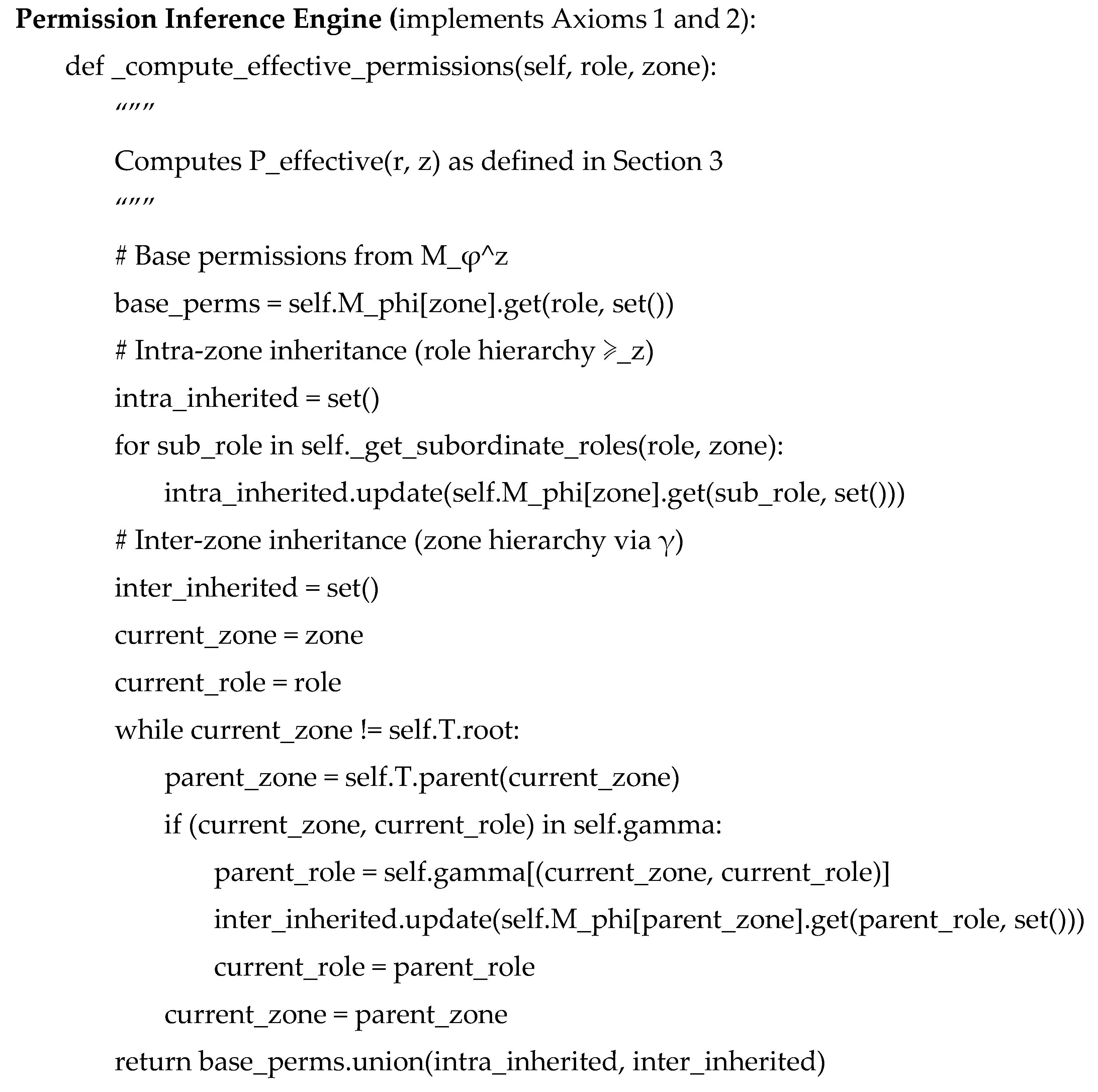
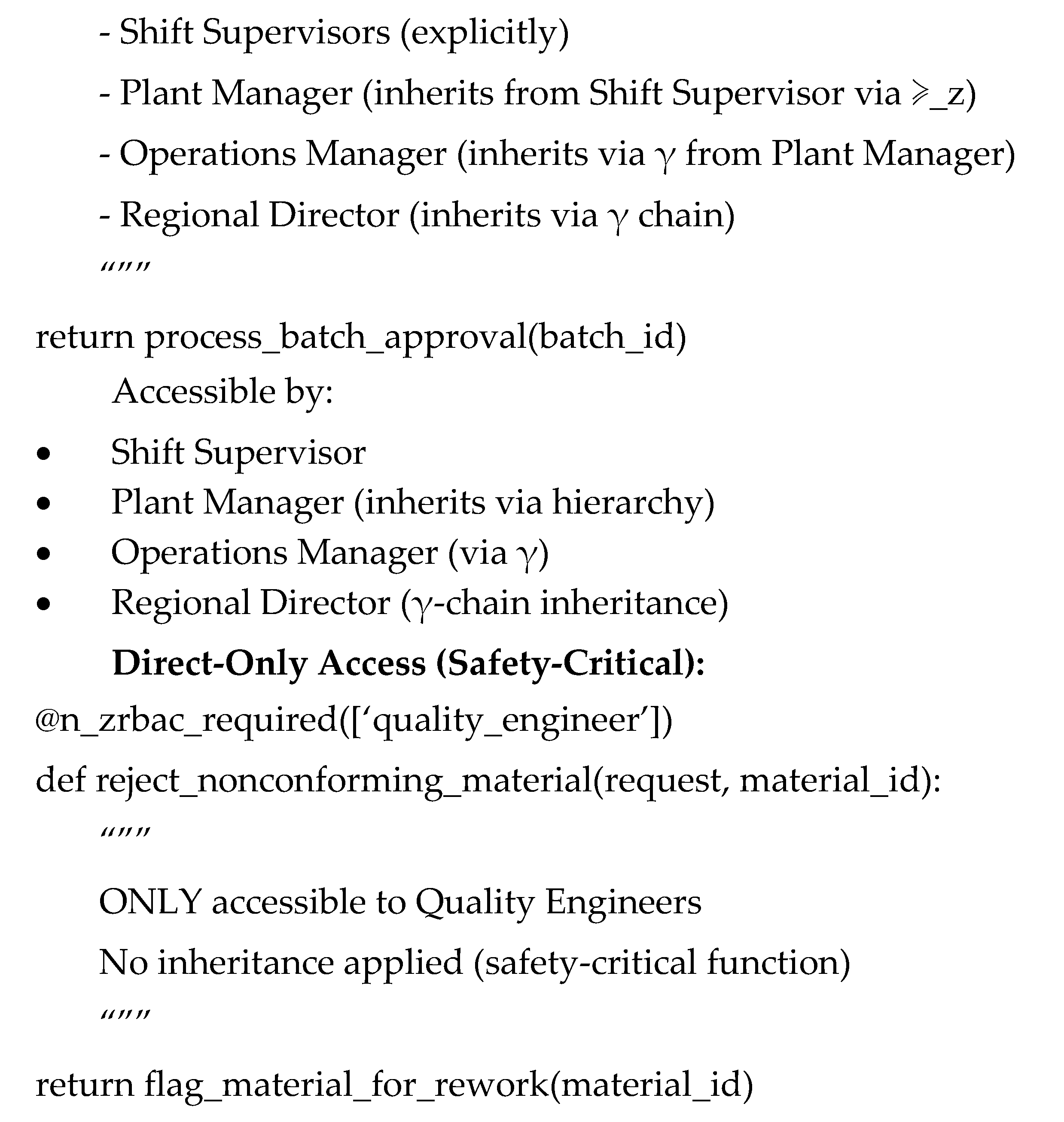
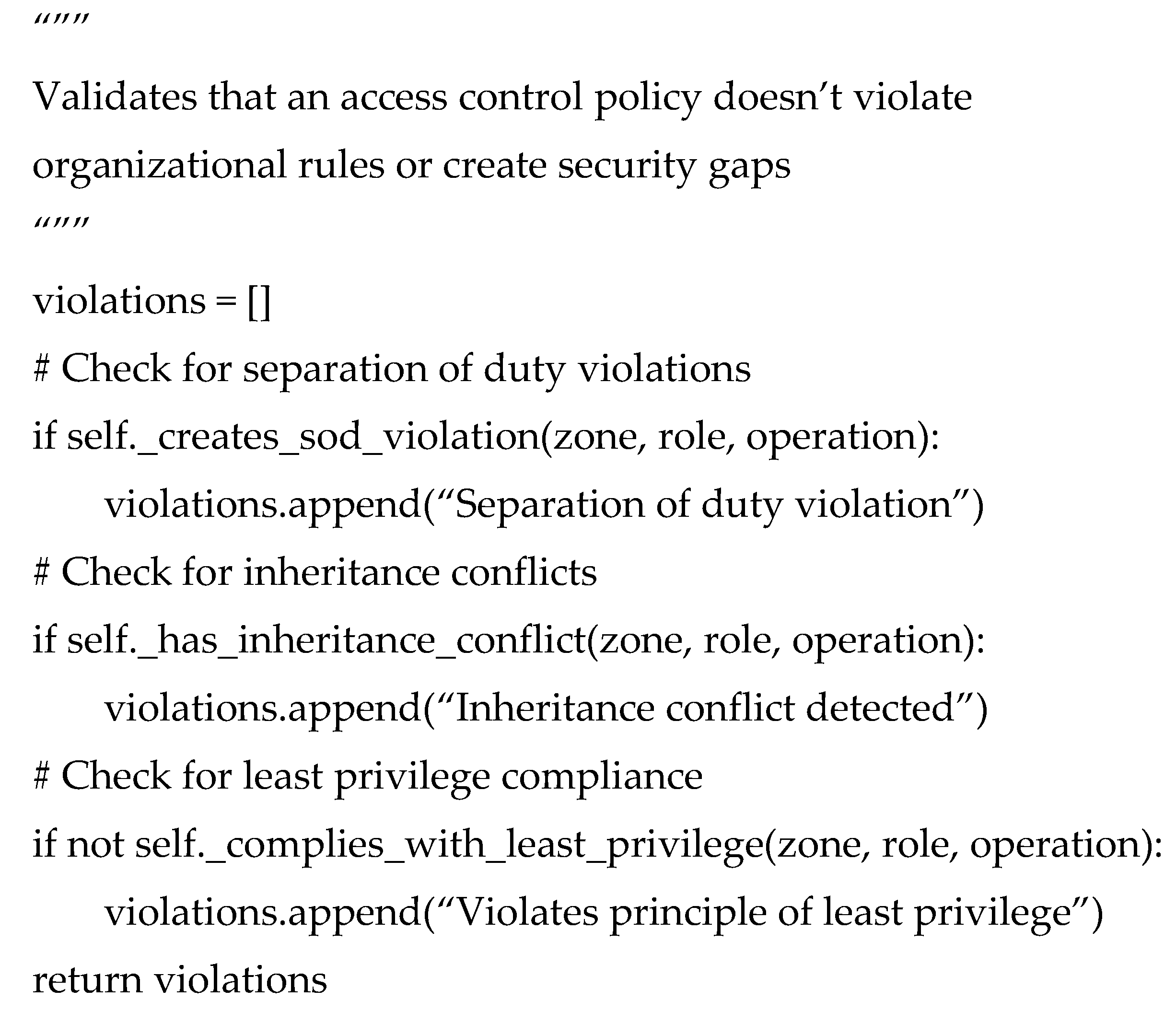
7. ZRB Access Control: Formal Model Implementation and Enforcement
7.1. The Access Control Decision Process Revisited
7.2. Implementation Architecture for ZRB Access Control
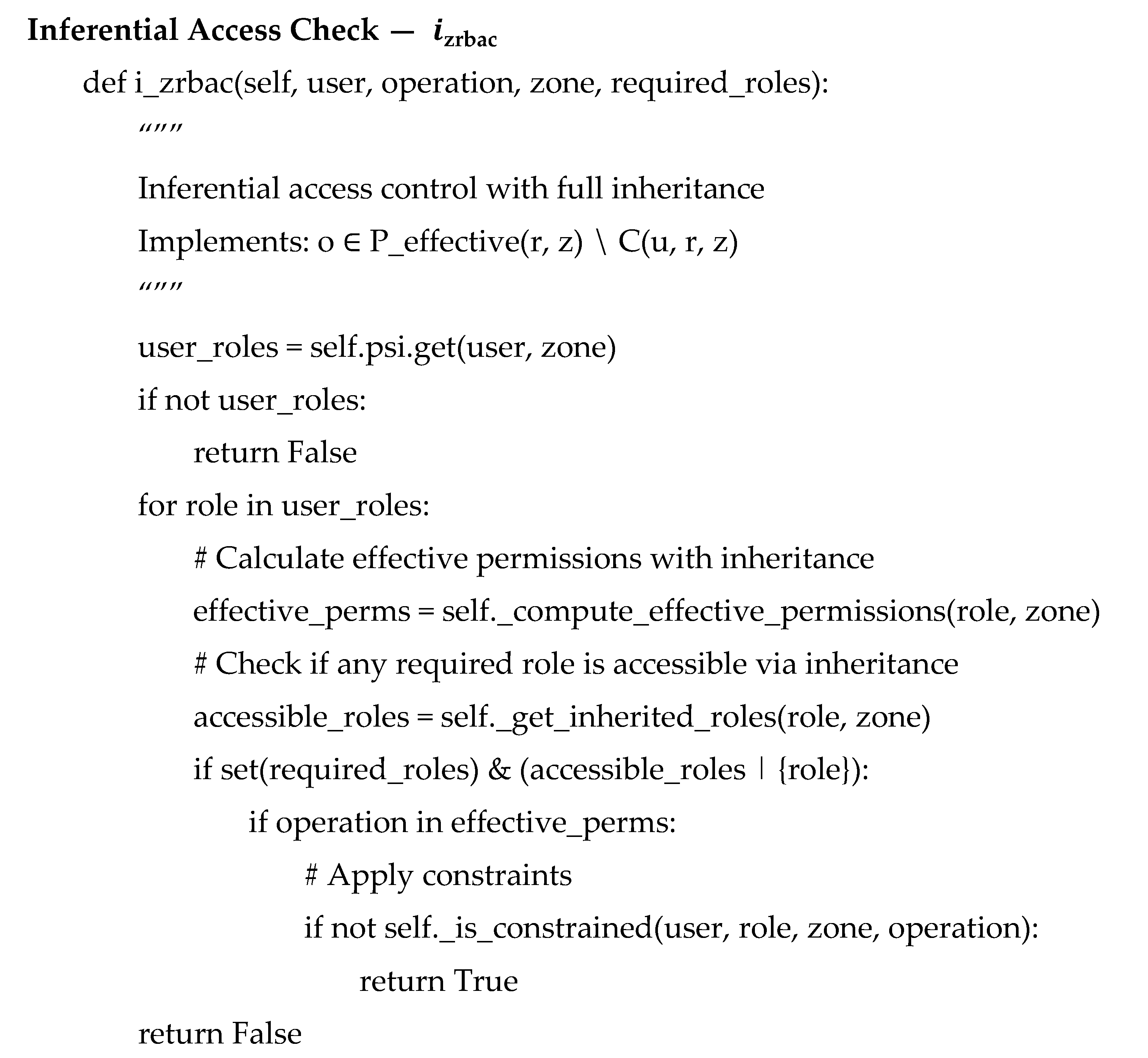
7.3. Integration with MVC Web Frameworks
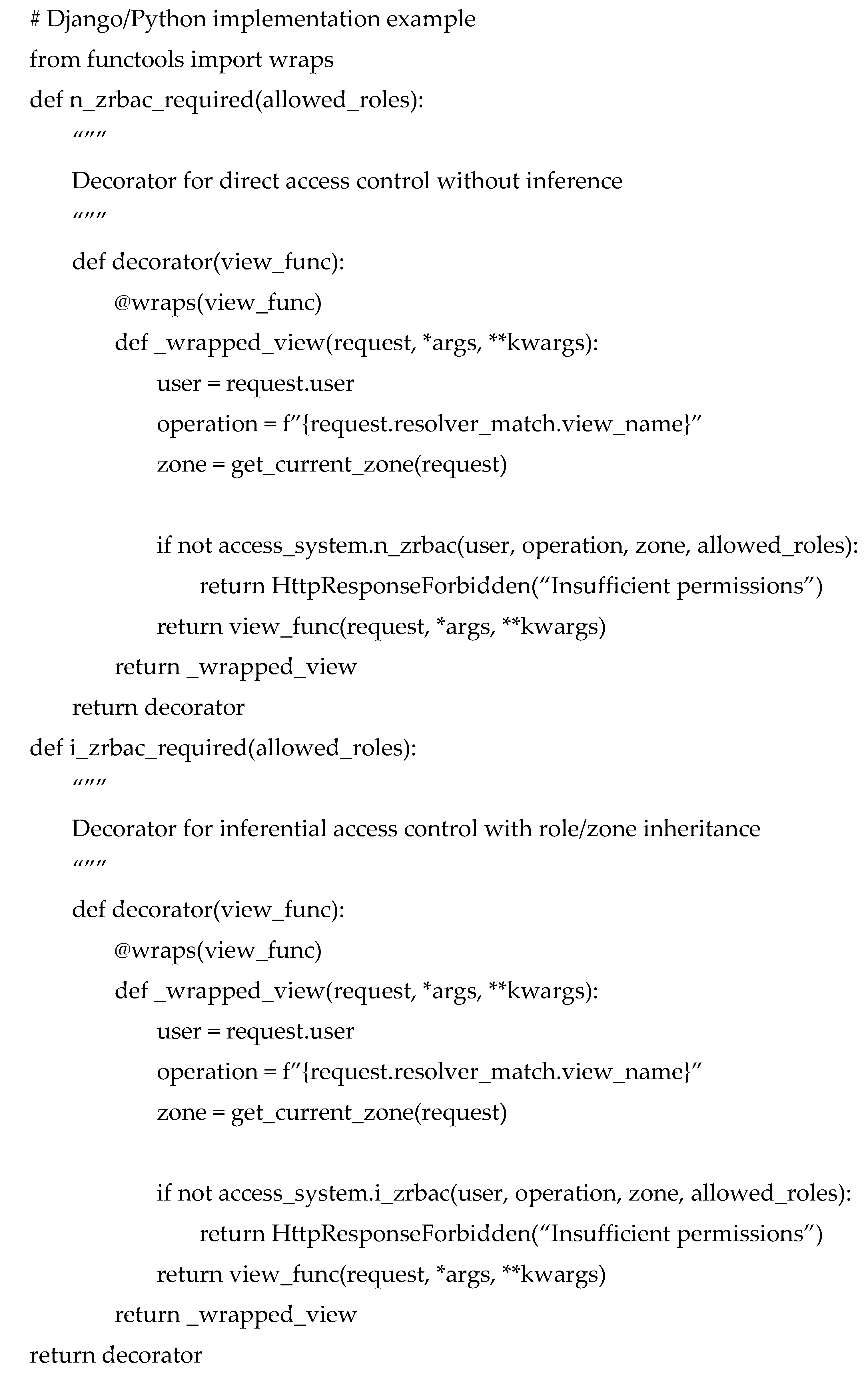
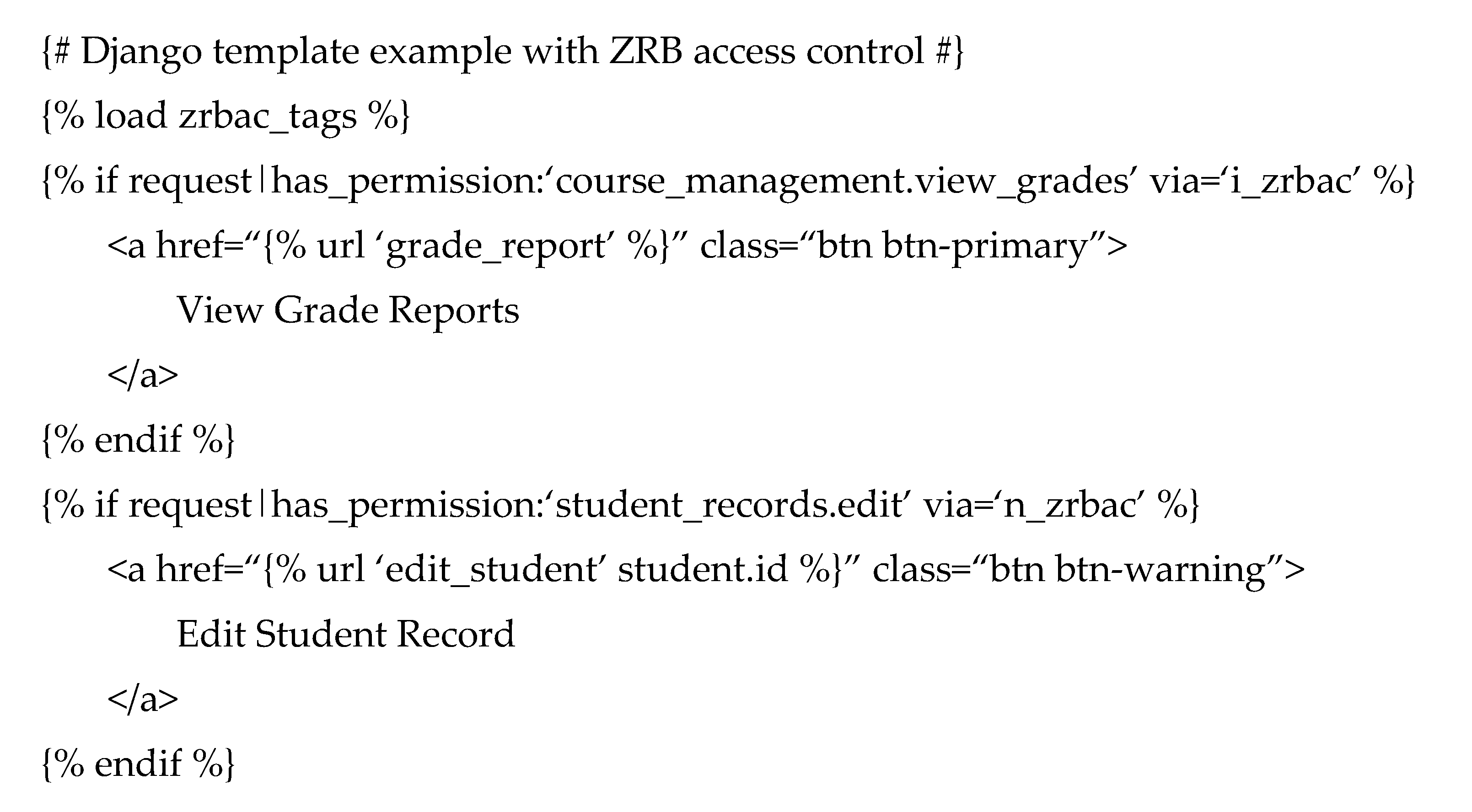
7.4. Practical Examples and Usage Patterns
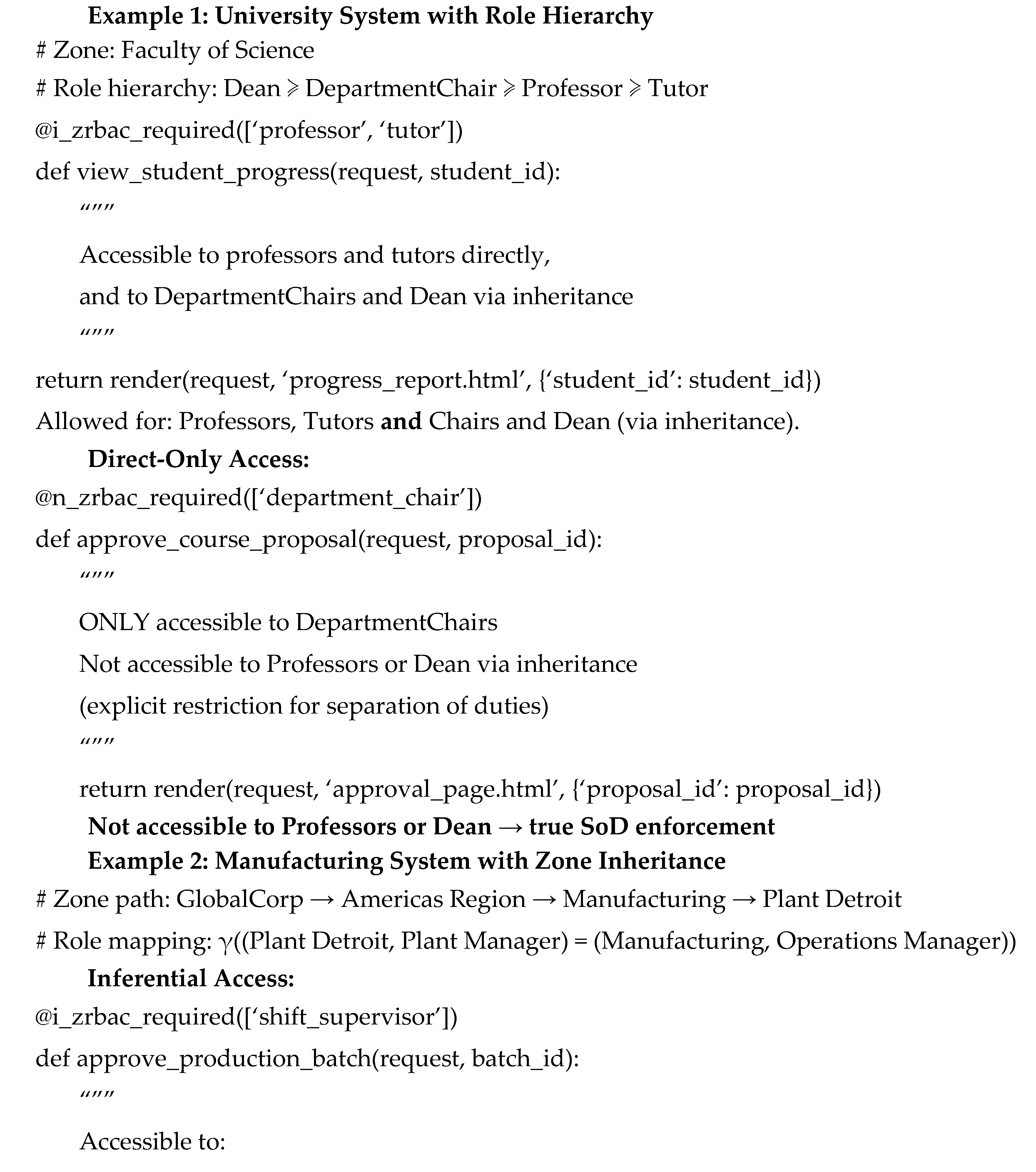
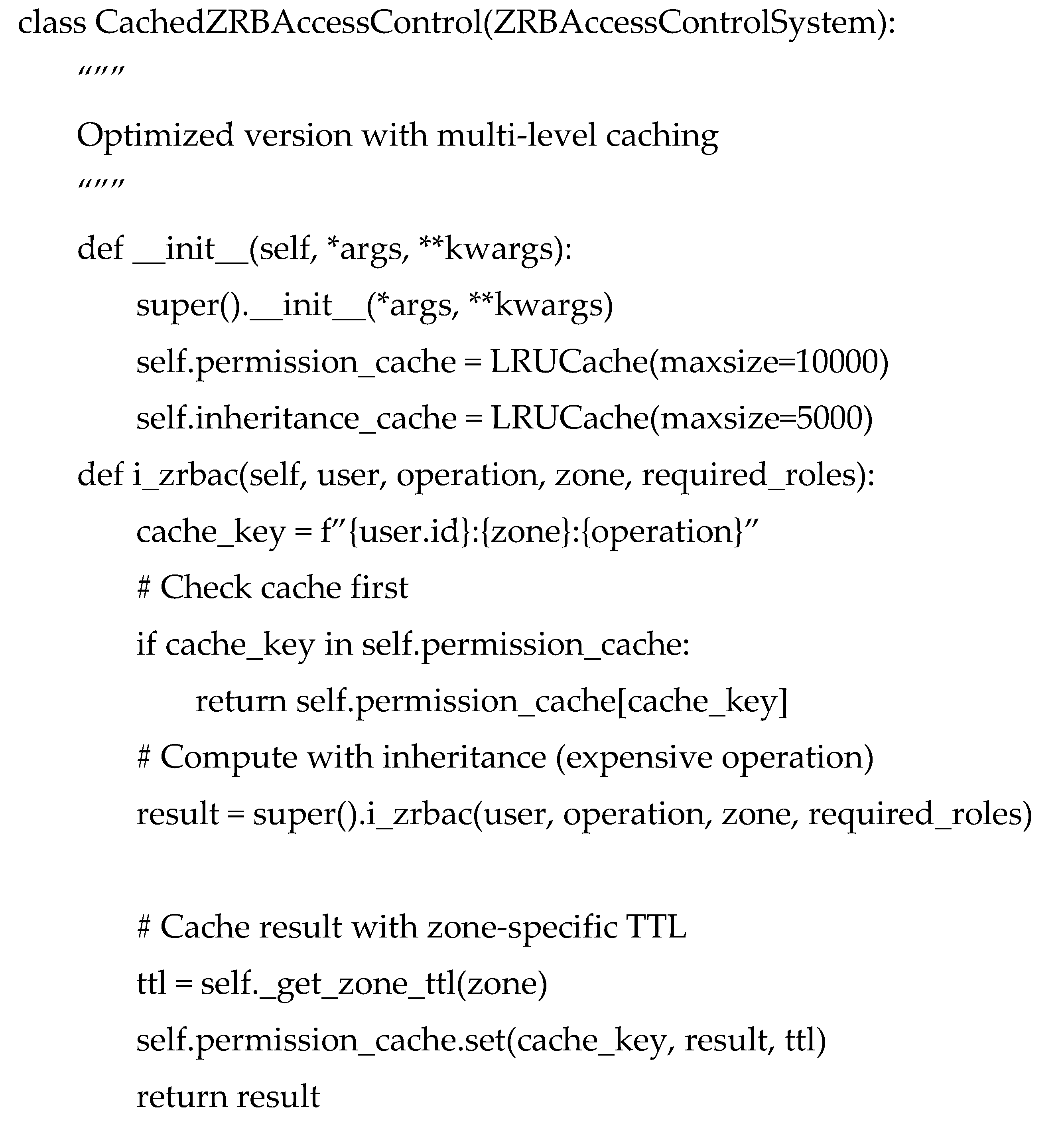
7.5. Performance Considerations and Optimization
7.6. Security and Compliance Features
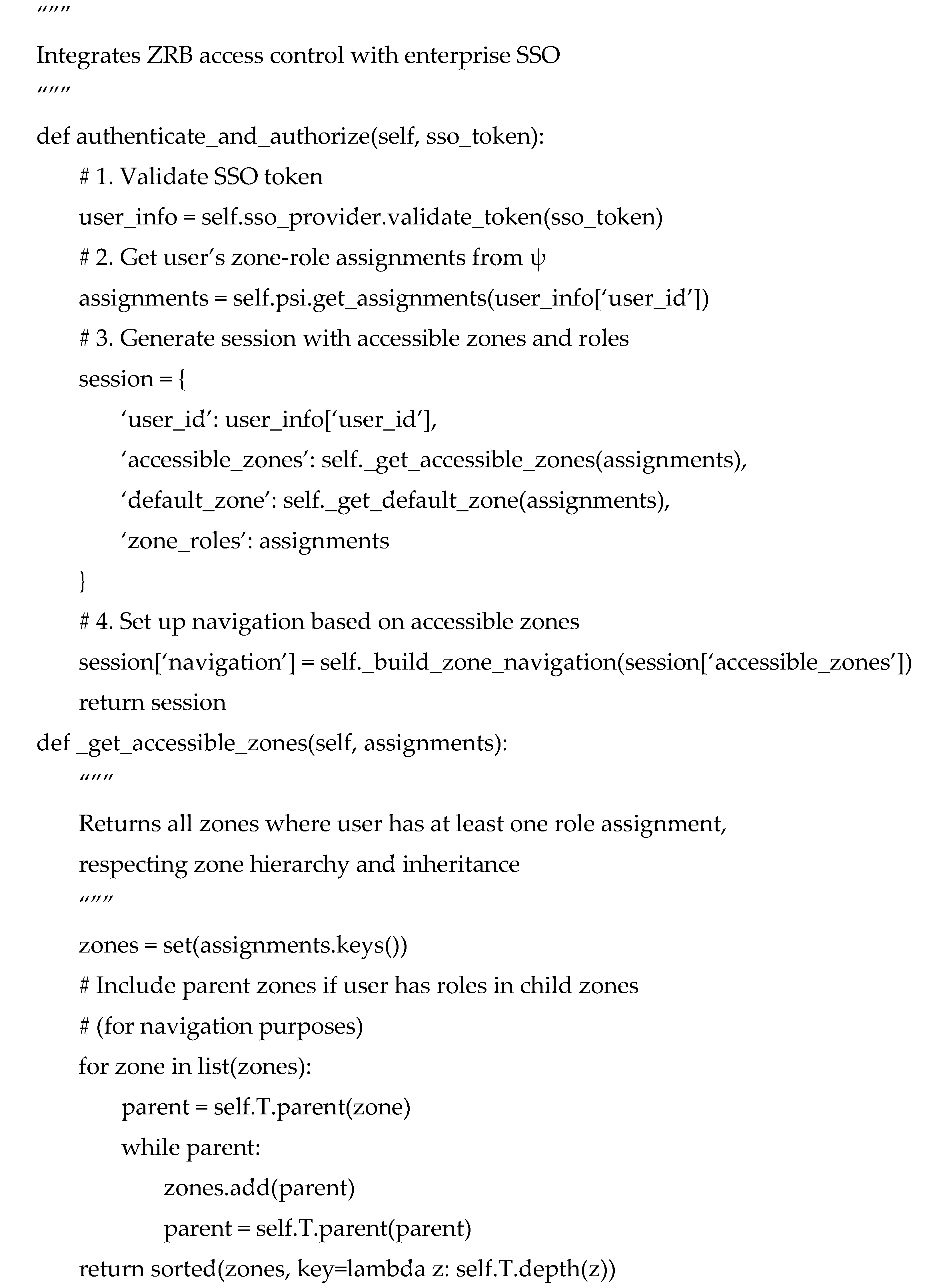
7.7. Integration with Single Sign-On (SSO)
8. Formal Advantages and Theoretical Contributions of the ZRB Model
8.1. Formal Structural Alignment with Organizational Semantics
- the organizational chart, capturing reporting and inclusion relationships, and
- the system blueprint, defining containment of roles, applications, users, and permission hierarchies.
8.2. Provable Security Properties
8.3. Scalability Through Mathematical Decomposition
- d = depth of the intra-zone role hierarchy
- h = height of the zone-ancestry path in
- updates to (roles)
- updates to (applications/operations)
- updates to (permission matrices)
- updates to constraints
- updates to user assignments
8.4. Unified Authentication and Authorization
- zone scope
- role semantics
- inherited permissions via and
- explicit constraints
9. Formal Evaluation and Empirical Validation
9.1. Theoretical Analysis of Advantages
9.2. Limitations and Mitigations
- Automated synchronization with HR systems → keeps ψ updated
- Decentralized zone-level administration → reduces global bottlenecks
- Incremental validation → ensures each satisfies policy constraints for zone only
9.3. Performance Optimization Results
- Permission Cache Hit Rate: 94.3% during typical user sessions
- Inheritance Calculation Reduction: 87.6% fewer recursive computations due to caching
- Memory Efficiency: Average of 2.3 KB per active user for permission-related data
10. Conclusions and Future Research Directions
10.1. Theoretical Contributions
10.2. Empirical Validation
| Domain | Scale | Key Metrics | Result |
| KBIES (Open Education) | 15 zones, 12 roles, 127 apps | Permission accuracy | 99.2% accuracy |
| Open Press | 8 zones, 8 roles, 89 apps | Access violation rate | 0.1% violations |
| Open Research | 5 zones, 7 roles, 56 apps | administrative overhead | 71% overhead reduction |
10.3. Performance and Scalability Considerations
10.4. Future Research Directions
10.5. Concluding Statement
References
- Sandhu, R.S.; Coyne, E.J.; Feinstein, H.L.; Youman, C.E. Role-Based Access Control Models. Computer 1996, 29, 38–47. [CrossRef]
- Ferraiolo, D.F.; Sandhu, R.; Gavrila, S.; Kuhn, D.R.; Chandramouli, R. Proposed NIST Standard for Role-Based Access Control. ACM Trans. Inf. Syst. Secur. 2001, 4, 224–274. [CrossRef]
- Bertino, E.; Bonatti, P.A.; Ferrari, E. TRBAC: A Temporal Role-Based Access Control Model. ACM Trans. Inf. Syst. Secur. 2001, 4, 191–233. [CrossRef]
- Joshi, J.B.D.; Bertino, E.; Latif, U.; Ghafoor, A. A Generalized Temporal Role-Based Access Control Model. IEEE Trans. Knowl. Data Eng. 2005, 17, 4–23. [CrossRef]
- Kuhn, D.R.; Coyne, E.J.; Weil, T.R. Adding Attributes to Role-Based Access Control. Computer 2010, 43, 79–81. [CrossRef]
- Hu, V.C.; Ferraiolo, D.; Kuhn, R.; Schnitzer, A.; Sandlin, K.; Miller, R.; Scarfone, K. Guide to Attribute Based Access Control (ABAC) Definition and Considerations (NIST SP 800-162). NIST, Gaithersburg, MD, USA, 2014. [CrossRef]
- Rose, S.; Borchert, O.; Mitchell, S.; Connelly, S. Zero Trust Architecture (NIST SP 800-207). NIST, 2020. [CrossRef]
- Borchert, O.; Howell, G.; Kerman, A.; Rose, S.; Souppaya, M.; et al. Implementing a Zero Trust Architecture: High-Level Document (NIST SP 1800-35). NIST, 2025. [CrossRef]
- Temoshok, D.; Choong, Y.-Y.; Galluzzo, R.; LaSalle, M.; Regenscheid, A.; Proud-Madruga, D.; Gupta, S.; Lefkovitz, N. Digital Identity Guidelines (NIST SP 800-63-4). NIST, 2025. [CrossRef]
- Souppaya, M.; Scarfone, K.; Dodson, D. Secure Software Development Framework (SSDF) Version 1.1 (NIST SP 800-218). NIST, 2022. [CrossRef]
- Office of Management and Budget. M-23-16: Update to M-22-18, Enhancing the Security of the Software Supply Chain through Secure Software Development Practices. Executive Office of the President, 2023. https://www.whitehouse.gov/wp-content/uploads/2023/06/M-23-16-Update-to-M-22-18-Enhancing-Software-Security.pdf.
- A Systematic Review of Access Control Models: Background, Existing… (IEEE), 2024. (Accessed via IEEE Xplore).
- Marquis, Y.A. From Theory to Practice: Implementing Effective RBAC Strategies to Mitigate Insider Risks. Journal of Engineering Research and Reports 2024, 26(5), 138–154. [CrossRef]
- A Machine Learning Approach for RBAC: Optimizing Role and Permission Management. IEEE 2024. (Accessed via IEEE Xplore).
- Chandramouli, R.; Butcher, Z.; Chetal, A. Attribute-based Access Control for Microservices-based Applications Using a Service Mesh (NIST SP 800-204B). NIST, 2021.
- Venčkauskas, A.; Kukta, D.; Grigaliūnas, Š.; Brūzgienė, R. Enhancing Microservices Security with Token-Based Access Control Method. Sensors 2023, 23, 3363. [CrossRef]
- AWS Architecture Blog. Let’s Architect! Building Multi-Tenant SaaS Systems. 2024. https://aws.amazon.com/blogs/architecture/lets-architect-building-multi-tenant-saas-systems/.
- SANS Institute. 2024 Multicloud Survey: Securing Multiple Clouds Amid Constant Changes. 2024.
- AWS. Introducing Cedar, an Open-Source Language for Access Control. 2023. https://aws.amazon.com/about-aws/whats-new/2023/05/cedar-open-source-language-access-control/.
- Cedar Policy. Cedar Language — Reference & SDK. 2025. https://docs.cedarpolicy.com/.
- Evans, E. Domain-Driven Design: Tackling Complexity in the Heart of Software. Addison-Wesley: Boston, MA, USA, 2003.
- Zachman, J.A. A Framework for Information Systems Architecture. IBM Systems Journal 1987, 26, 276–292.
- Yu, E.S.K. Towards Modelling and Reasoning Support for Early-Phase Requirements Engineering. Proc. 3rd IEEE Int. Symp. Requirements Engineering 1997, 226–235.
- Covington, M.J.; Moyer, M.J.; Ahamad, M. Generalized Role-Based Access Control for Securing Future Applications. Proc. 23rd National Information Systems Security Conference 2001.
- OWASP Foundation. OWASP Top 10: 2021. 2021. https://owasp.org/www-project-top-ten/.
- ASIS International. The Essentials of Access Control: Insights, Benchmarks, and Best Practices (Revised 2025). 2023–2025.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).