Submitted:
23 January 2026
Posted:
26 January 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
- The wall-clock duration of each cryptographic operation (what the user “feels”).
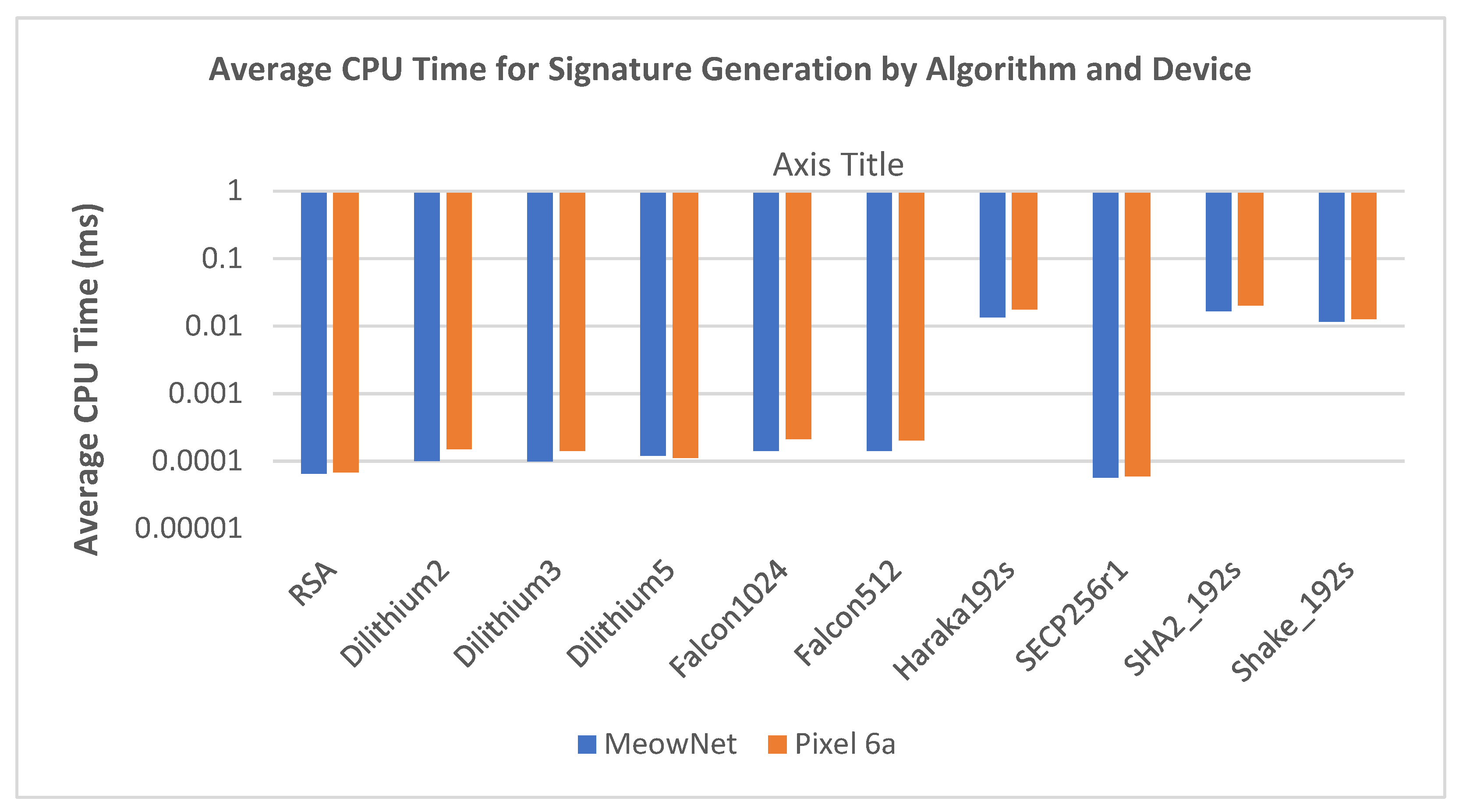
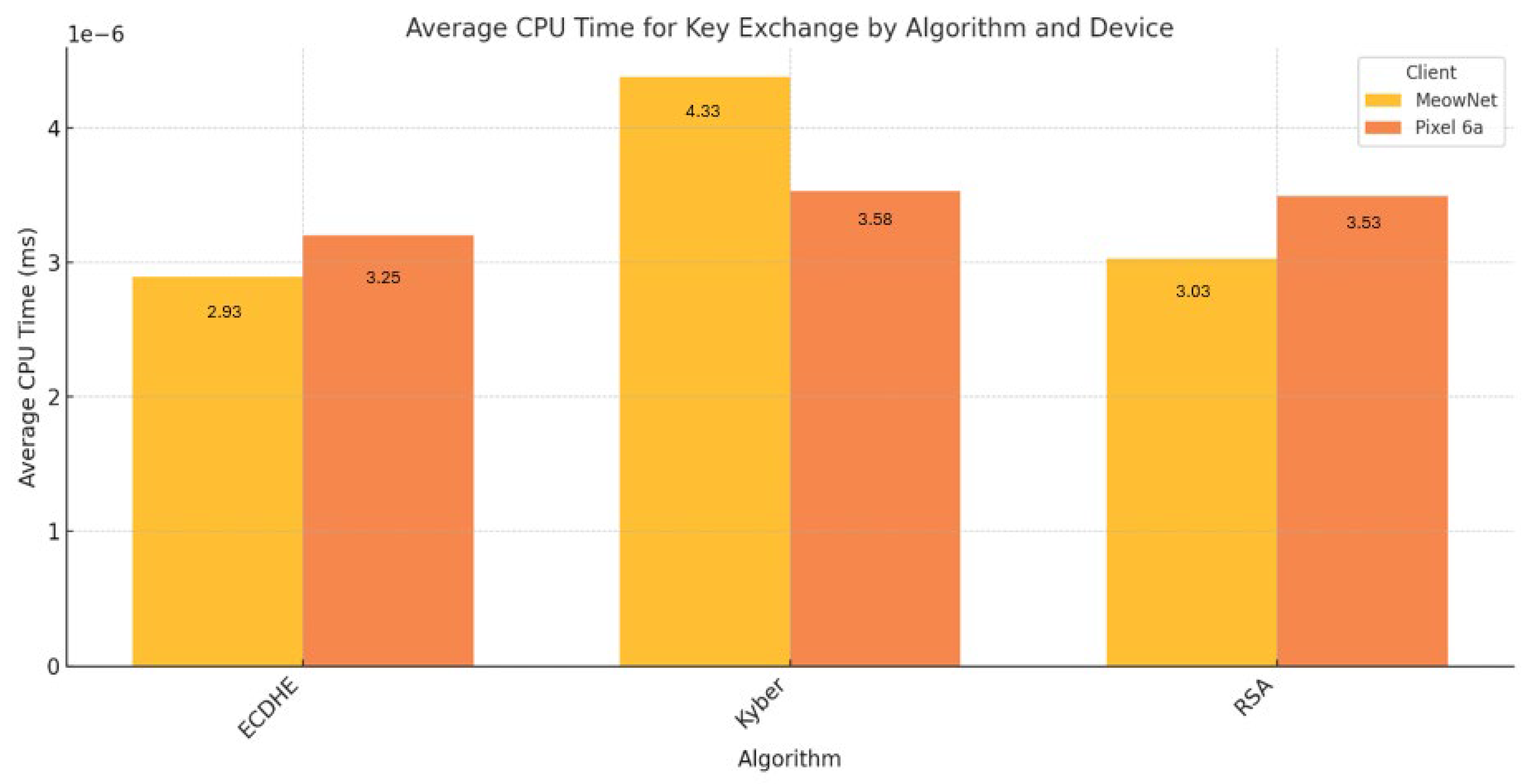
- The CPU time consumed (work done irrespective of scheduling noise).
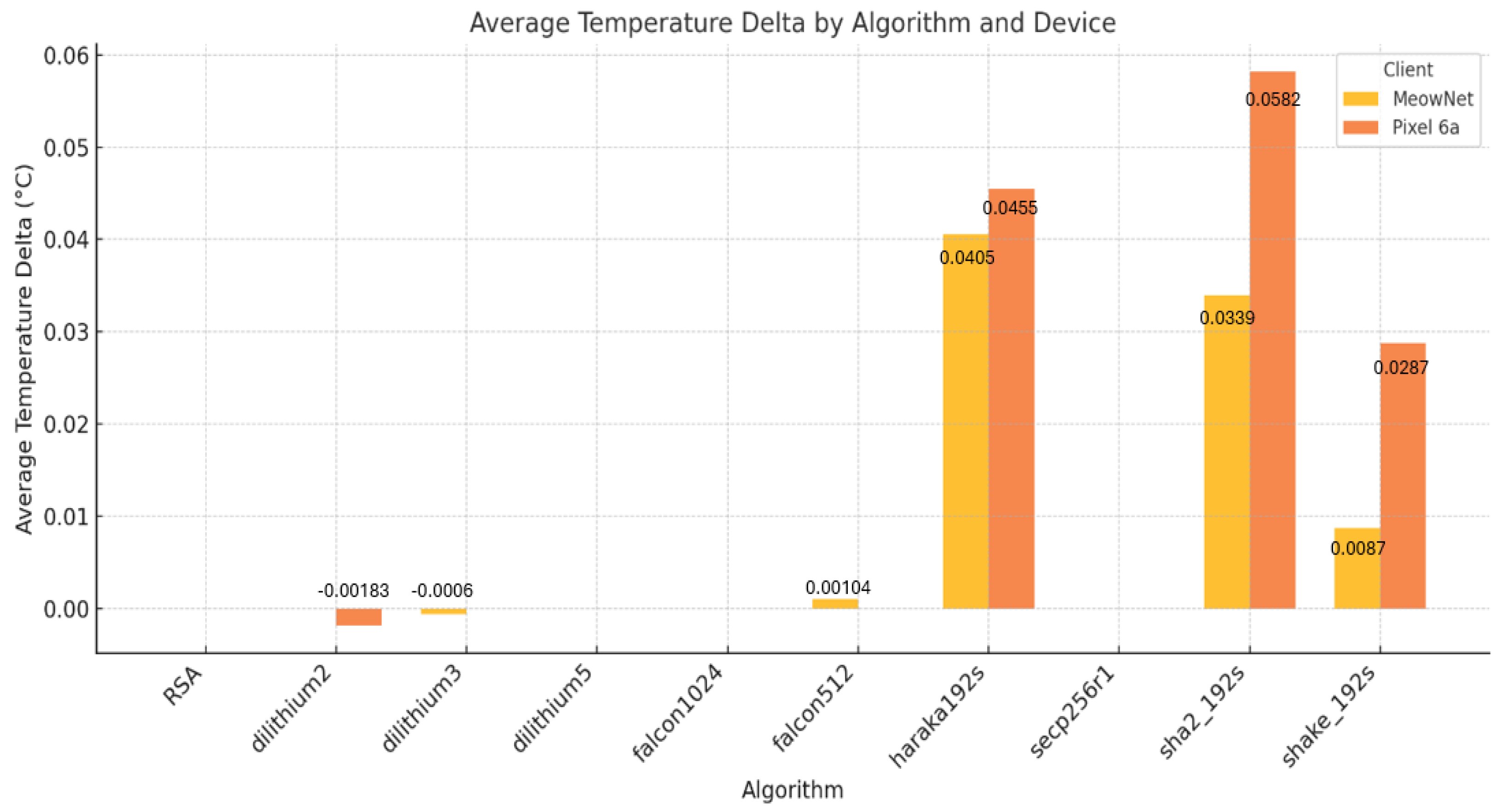
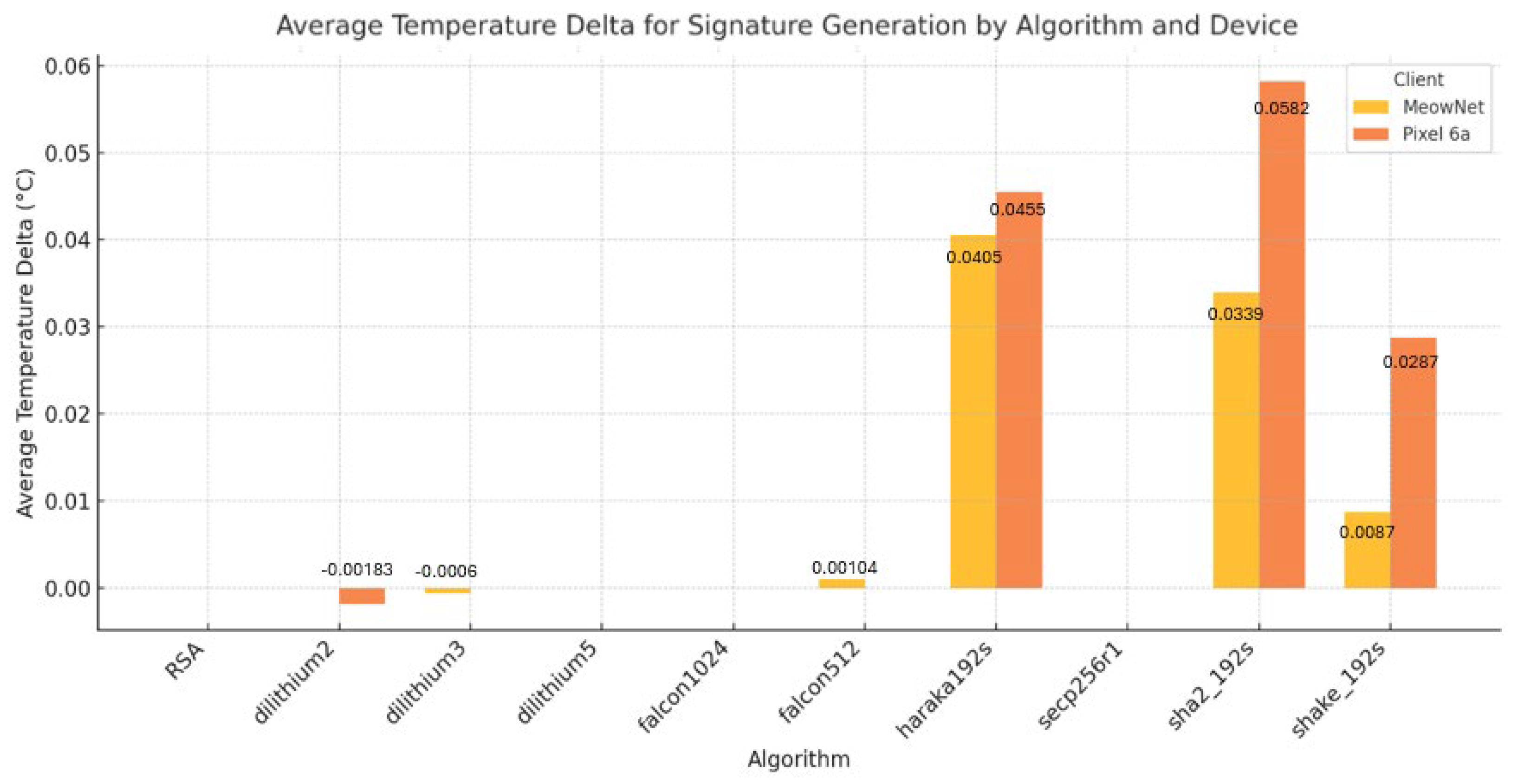
- The temperature delta reported during controlled runs (a proxy for thermal stress and throttling risk)
2. Related Work
2.1. Advancing Quantum Capabilities
2.2. Related Work
2.3. Industry Adoption
3. PQC Algorithm Selection
3.1. Understanding PQC Algorithms Selected
3.1.1. How Kyber Works
- The encryption procedure uses a randomizer polynomial vector and an error polynomial vector . These polynomial vectors are freshly generated for every encryption. Additionally, an error polynomial is needed. Three polynomials , and are completely random and small.
- A Simple Example to Show how Kyber Works
- Because we will multiply and add polynomials, we also need a modulus so that their degree would not become too big for us to handle. We use as the polynomial modulus. It is not important why looks the way it does. The important fact is that by taking a polynomial modulo , we guarantee that their degree (highest exponent) will be smaller than 4. Below all calculations are implicitly done modulo (on coefficients) and (on polynomials).
- From the polynomial modulus , we obtain .
- We use the small parameters as an example to show how Kyber works. For actual implementations, we use the original parameters as above for the strong security as original design.
- i.
- Alice selects a public random matrix A
- ii.
- Alice selects a small noise vector e
- iii.
- Compute t
3.1.2. How CRYSTALS-Dilithium Works
- 1)
-
Key Generation:
- Generate a random secret key s1, s2.
- Compute a public matrix A and a public key t = A· s1+ s2
- 2)
-
Signing:
- Pick a random value y.
- Compute a commitment w = A·y.
- Derive a challenge c using a hash function: c = H(w || message).
- Form the response: z = y + c· s1.
- Output the signature: (z, c).
- 3)
-
Verification:
- Recompute w’ = A·z — c·t.
- Hash w’ || message to recompute c’: c’ = H(w’ || message).
- If c’ == c, the signature is valid.
3.1.3. How Falcon Works
- 1)
-
Key generation
- The public key is a long basis of a q-ary lattice.
- The private key is a short basis of the same lattice.
- 2)
-
SigningIn the signing procedure, the signer:
- generates a random value salt.
- computes a target c = H(message||salt), where H is a hash function sending an input to a random-looking point (on the grid).
- uses the known short basis (his private key) to compute a lattice point v close to the target c.
- outputs (salt, s), where s = c − v.
- 3)
-
VerificationThe verifier accepts the signature (salt, s) if and only if:
- The vector s is short.
- H(message||salt) − s is a point on the lattice generated by his public key.
3.1.4. How SPHINCS+ Works
- • Employ a hypertree with a very large number of leaves.
- • The leaves are signature key pairs for a one-time signature (OTS) scheme.
- • The signer randomly selects one of these key pairs when signing a message.
- • This algorithm has a limit on the total number of messages that can be signed since it needs to ensure that the probability of key reuse is negligibly small.
3.2. Impact of PQC on Mobile Clients
3.3. Security Level and Key Lengths of Selected PQCs
3.4. How a Kyber-Style KEM Session Works
4. Experiment Design
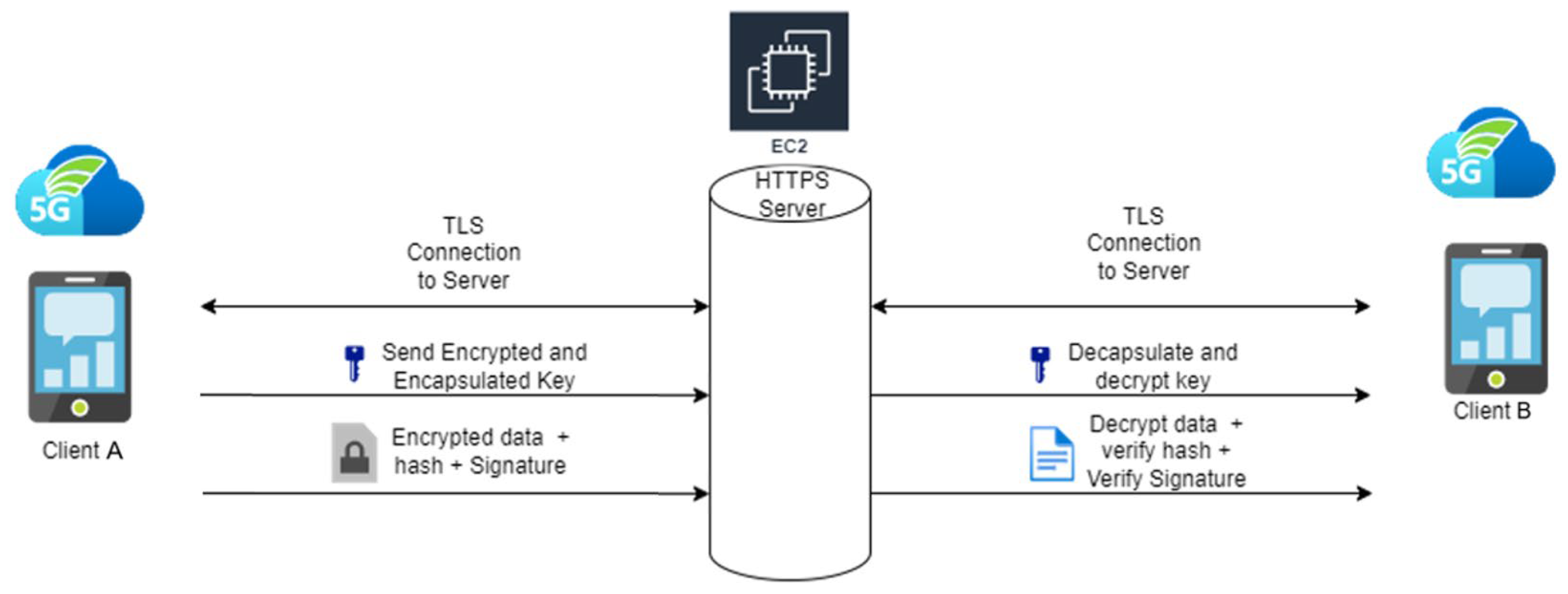
4.1. Setup Overview
4.2. Role of HTTPS Server
4.3. Experiment Workflow
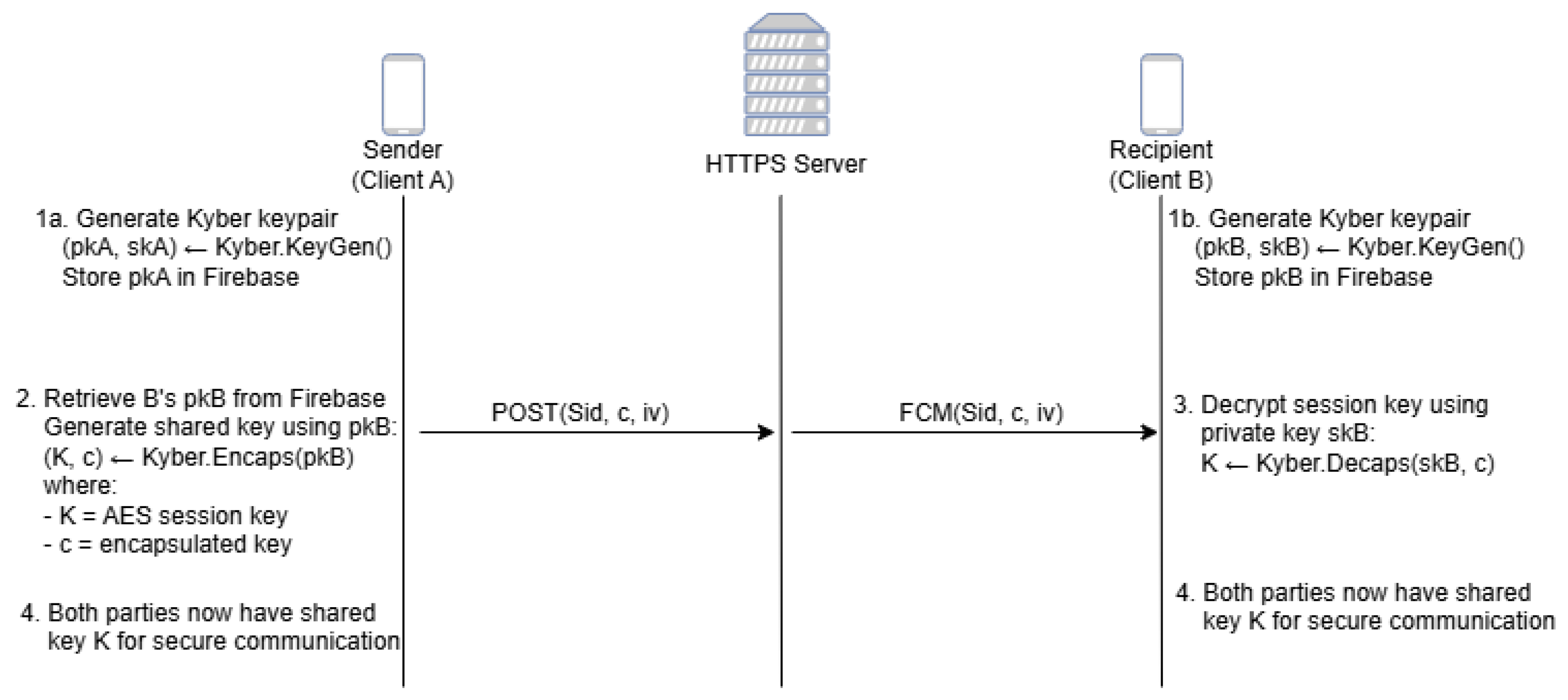
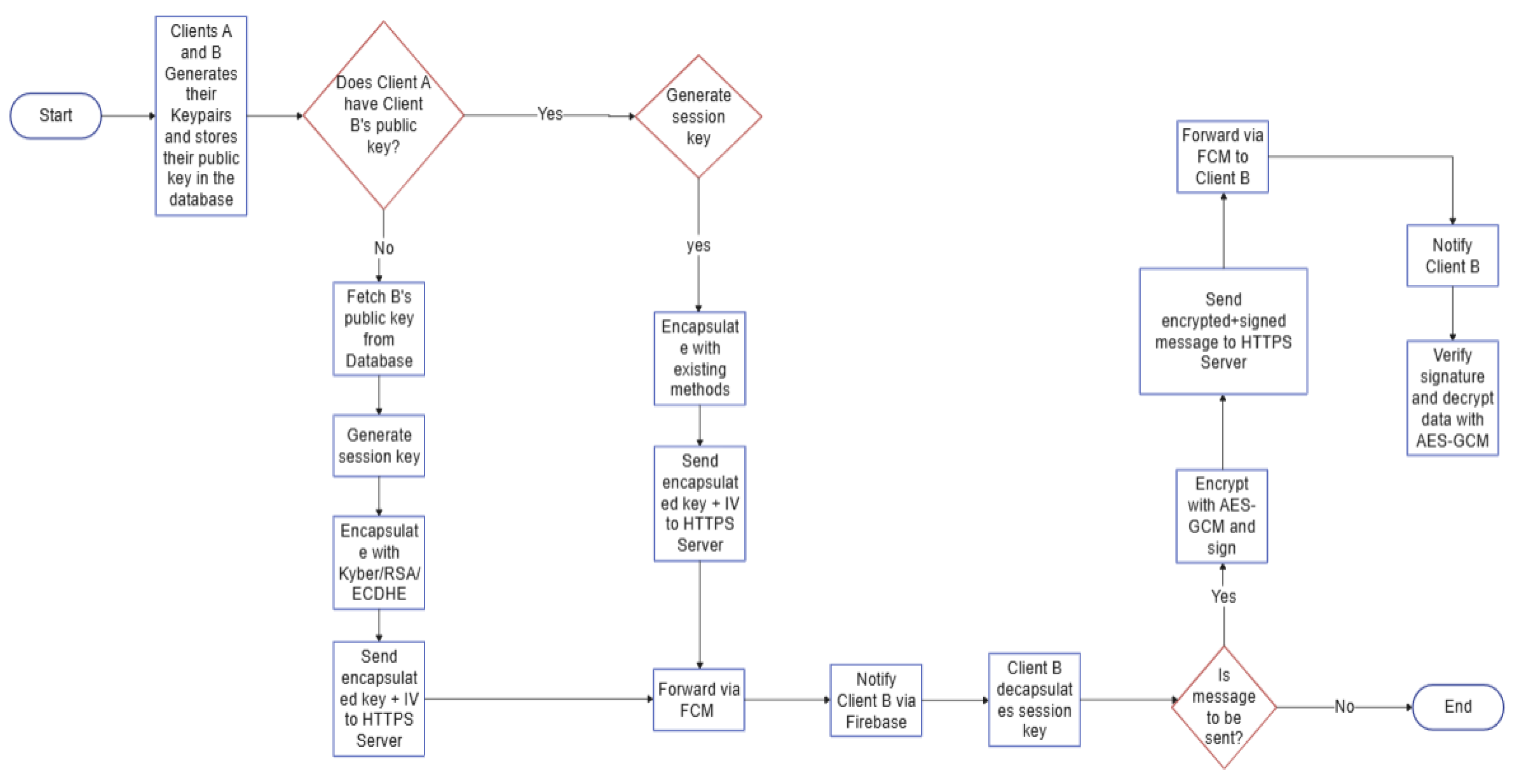
4.4. Client Communication & Handshake
- 1)
- For both clients to initiate communication, both Client A and Client B will generate their Kyber keypairs (pk, sk). The pk of these clients are then stored in the Firebase database.
- 2)
- Client A initiates a key exchange process. Client B’s pk is retrieved from the Firebase database. Client A uses Client B’s public key (pkB) to encapsulate the AES session key. The key exchange message is sent via HTTP POST to the server. The server then uses FCM to route the key exchange message to Client B.
| { |
| "sender": Client A, |
| "encapsulatedKey": c, |
| "iv": IV, |
| "clientId": recipient |
| } |
- 3)
- Client B receives the key exchange message and begins decapsulation the session key using its own private key (skB).
- 4)
- The shared key is now stored and handled by the “SessionData.kt”. Both parties can now use the shared key to encrypt and send data.
- 1)
- With the shared key established in Figure 3, the clients can start to exchange data messages. The defined message (M) by Client A is ready to be sent to the recipient, Client B.
- 2)
- The message (M) will be encrypted to provide confidentiality and integrity. Firstly, the random IV for AES-GCM mode is generated. The message is then encrypted using the shared key K:
- 3)
- The hash value of encrypted message (h) is computed:
| { |
| "sender": Client A, |
| "encryptedMessage": cipher, |
| "iv": IV, |
| "signature": σ, |
| "algorithm": "dilithium" |
| } |
- 4)
- The recipient, Client B, receives the payload and begins processing. Firstly, the hash value h' of the encrypted message (cipher) is computed. Client A’s public key (pkA) is then retrieved from the Firebase database to begin verification of the signature:
- 5)
- If the signature is valid, the message will be decrypted with the shared key (K):
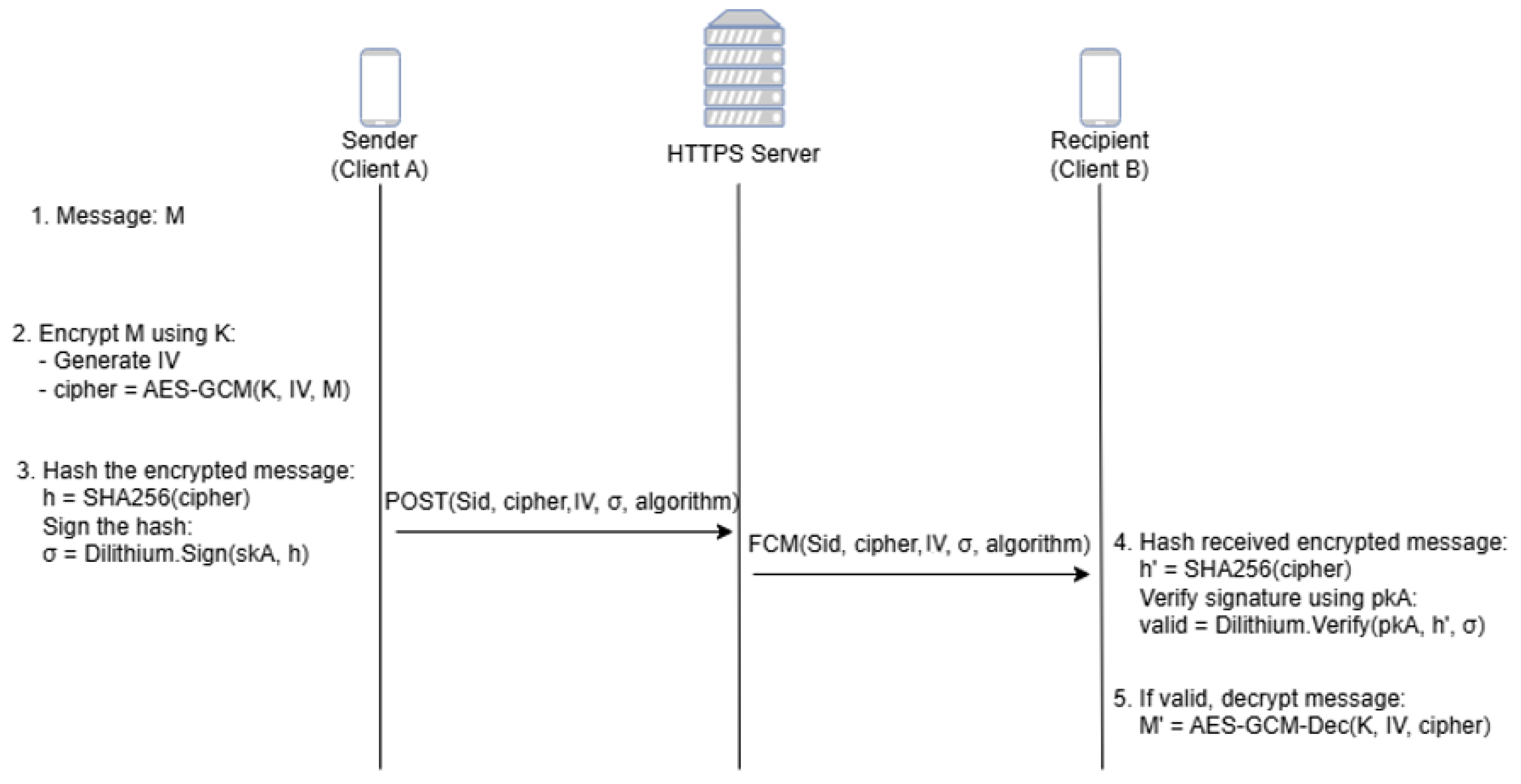
4.5. Exchanging Encrypted Messages
4.6. Data Collection
4.7. Performance Metrics
5. Results
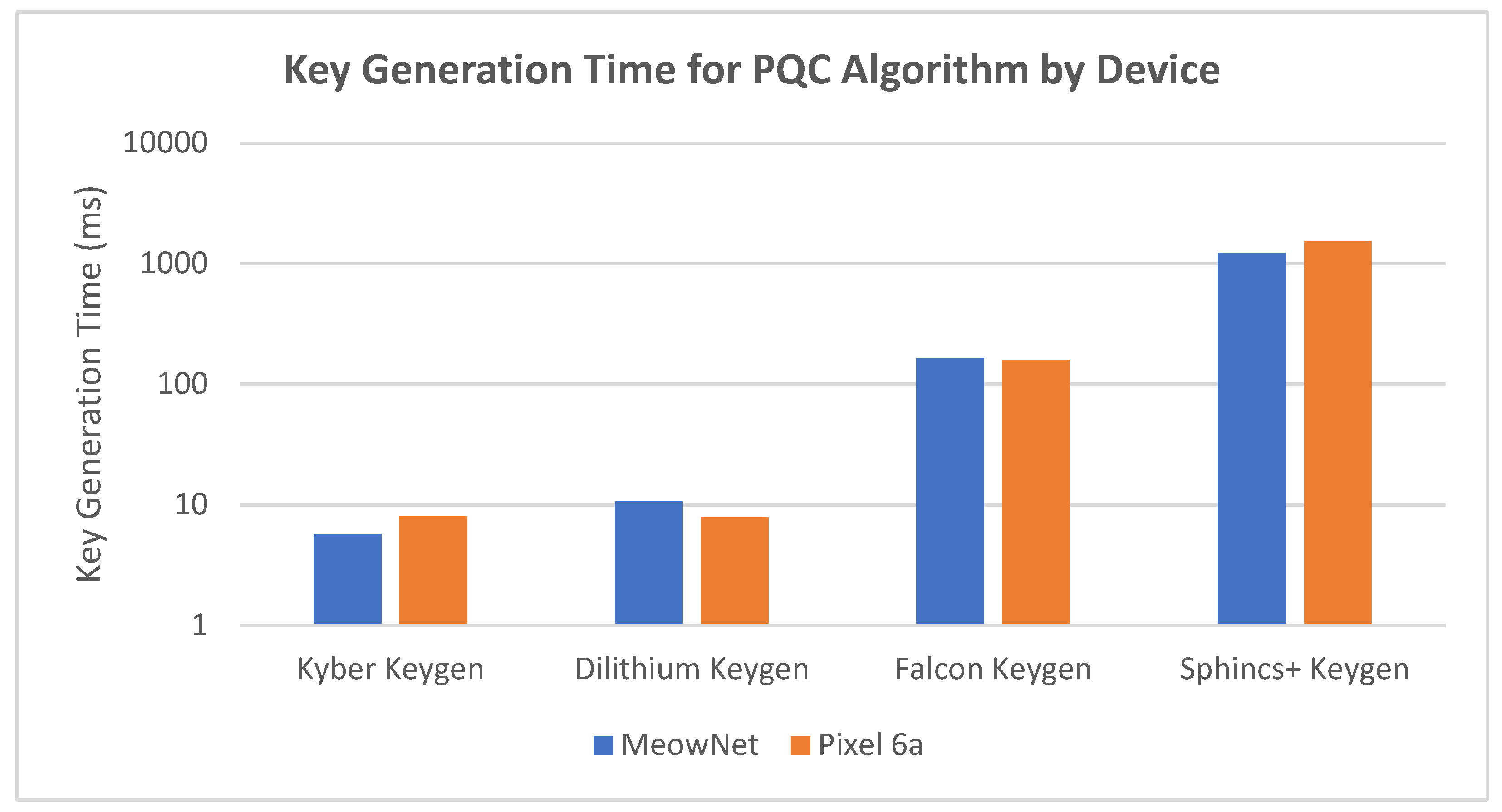
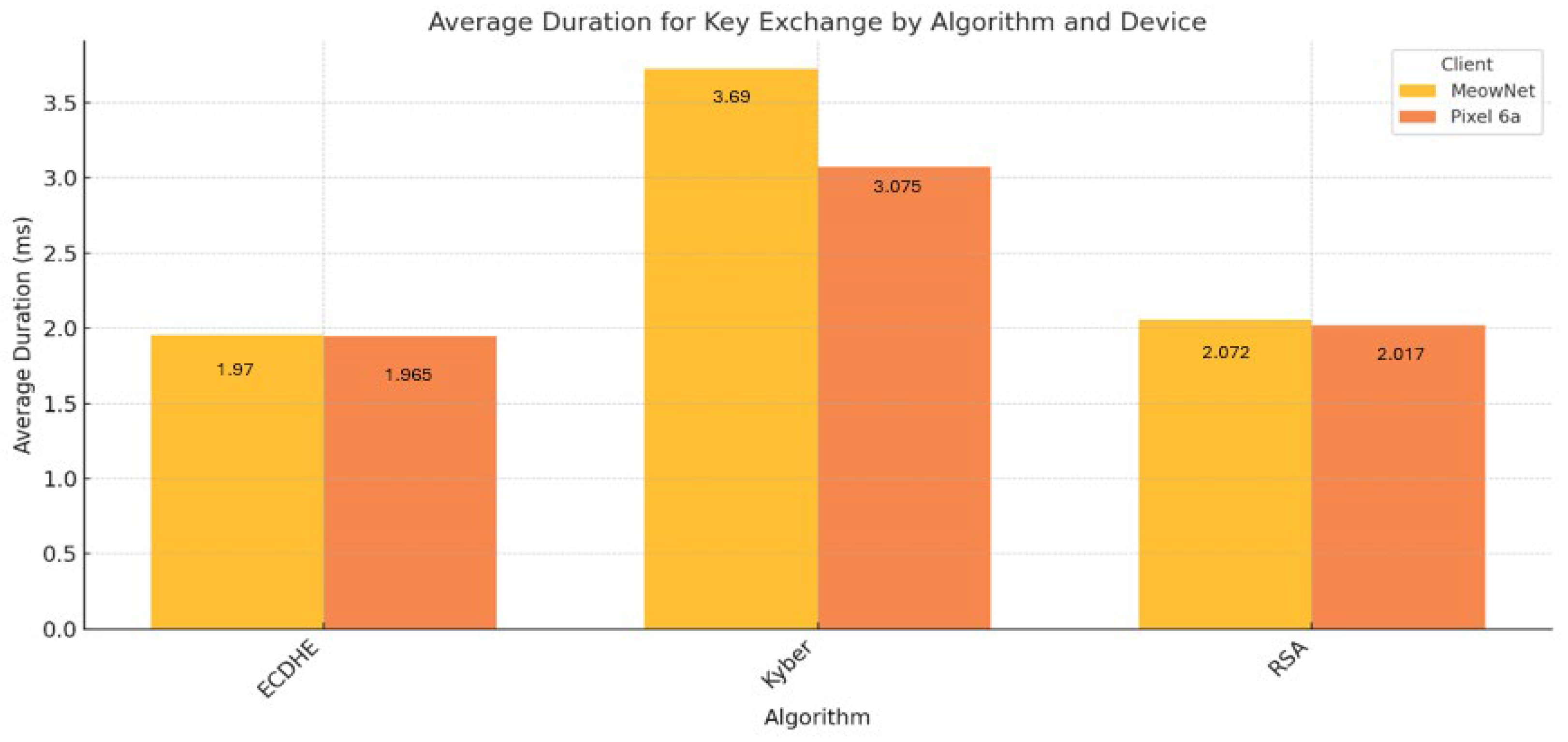
5.1. KEM Performance
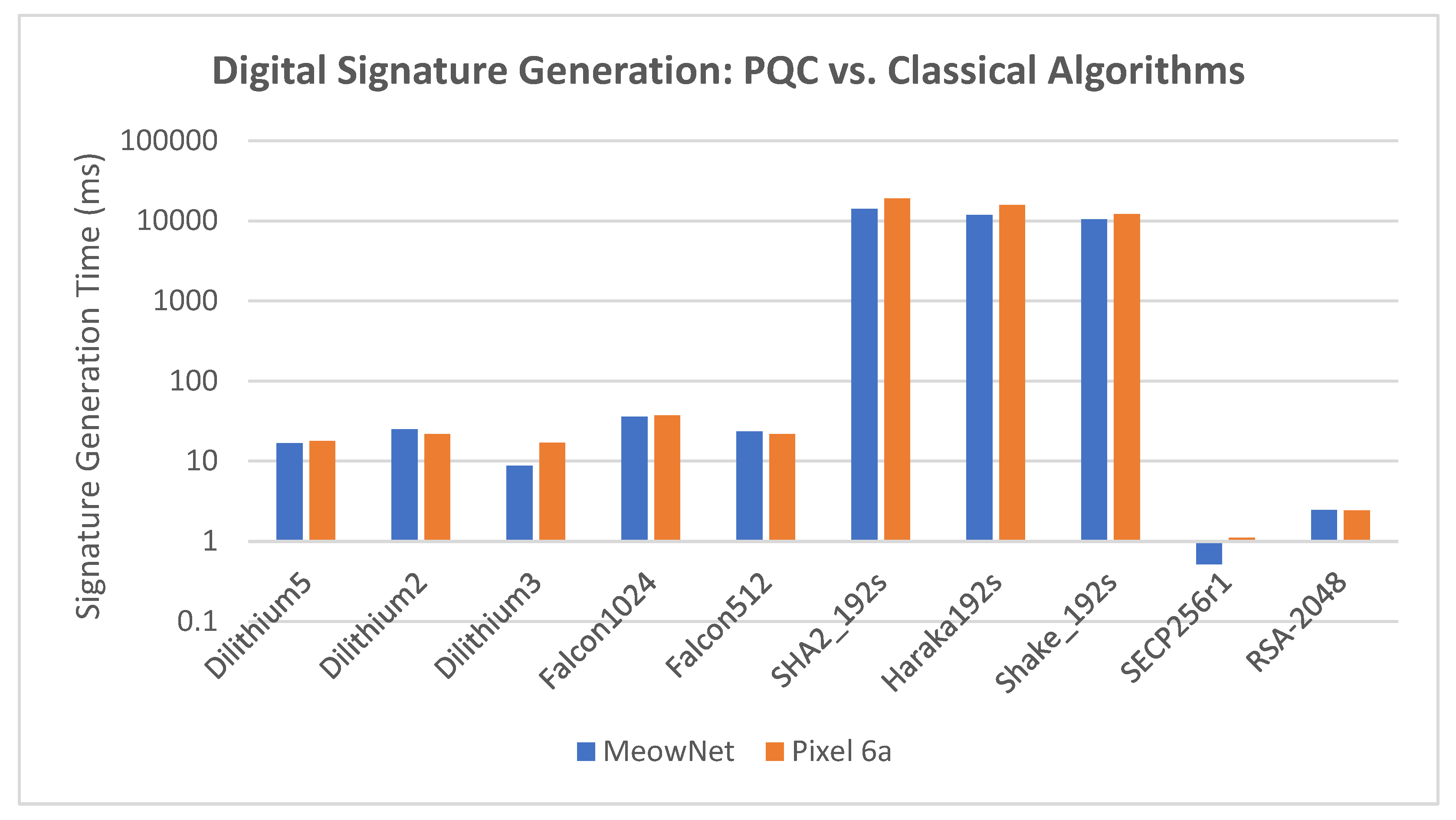
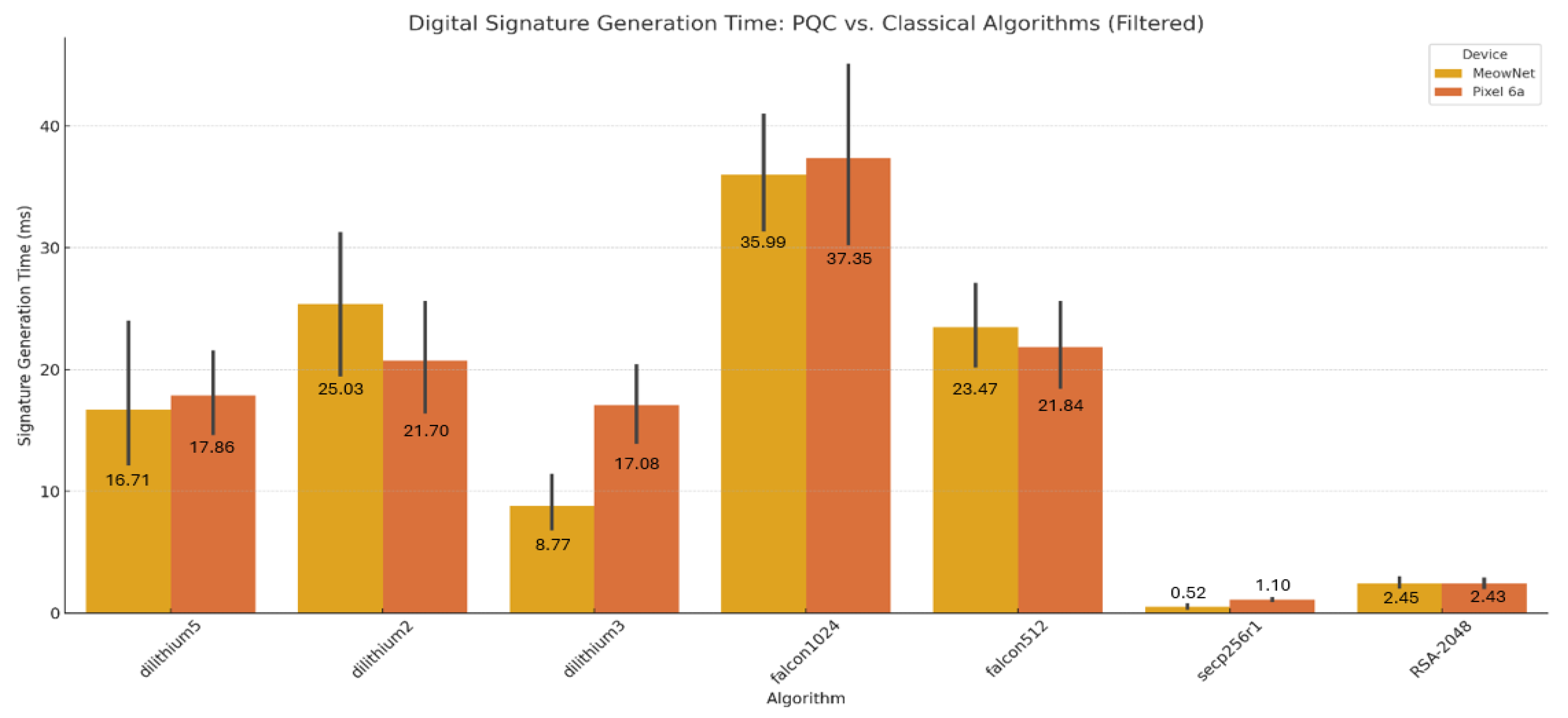
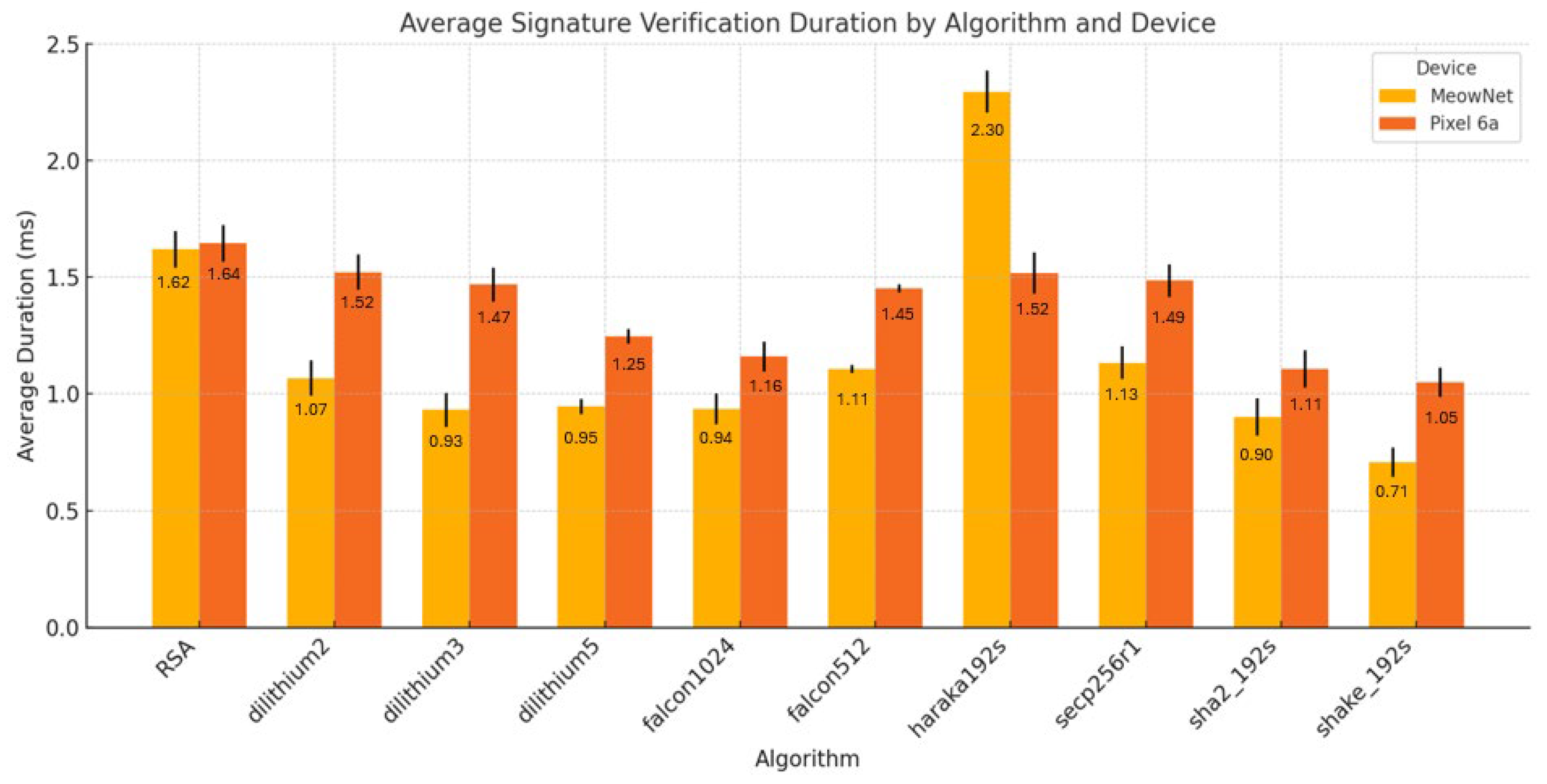
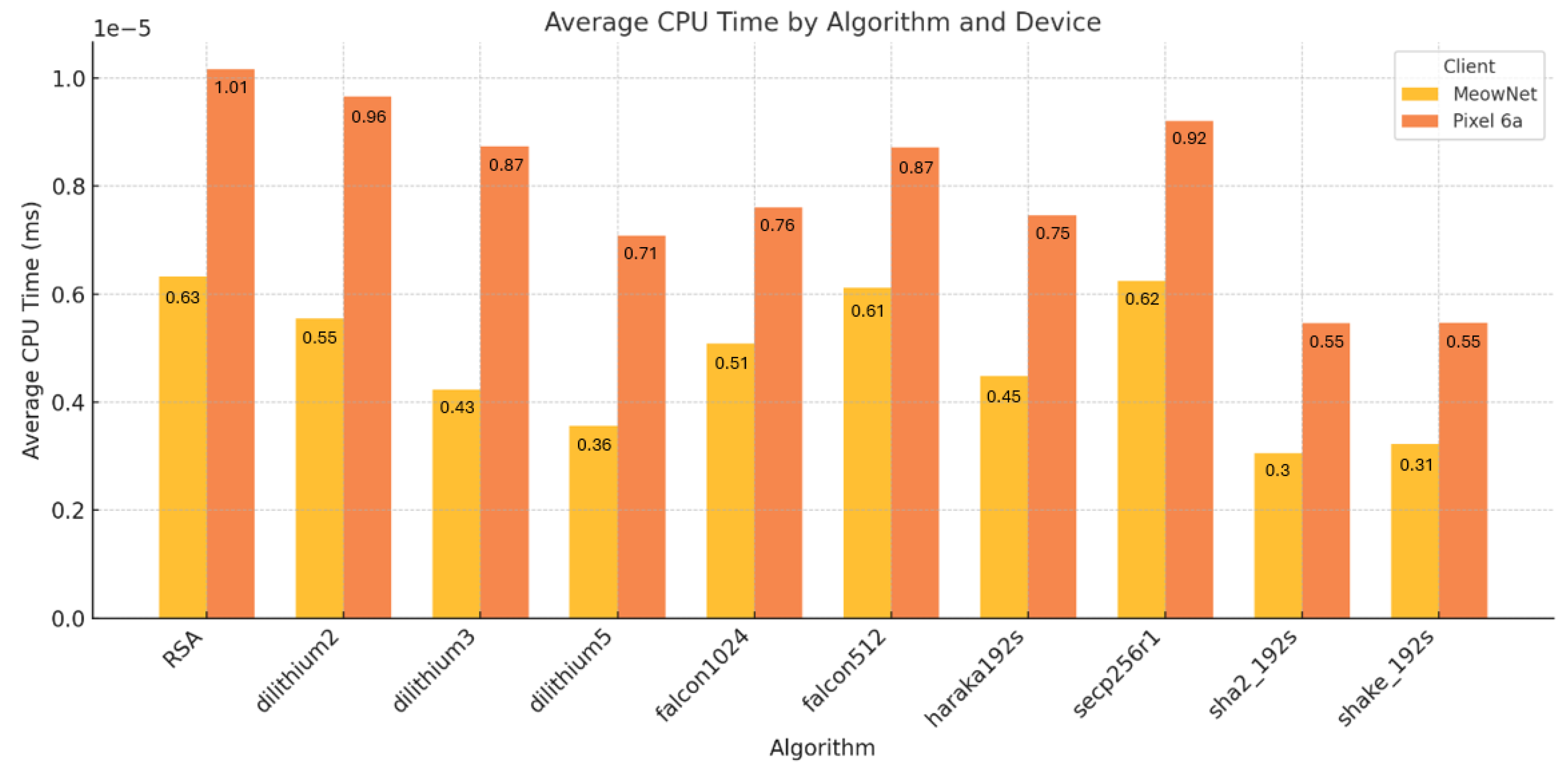
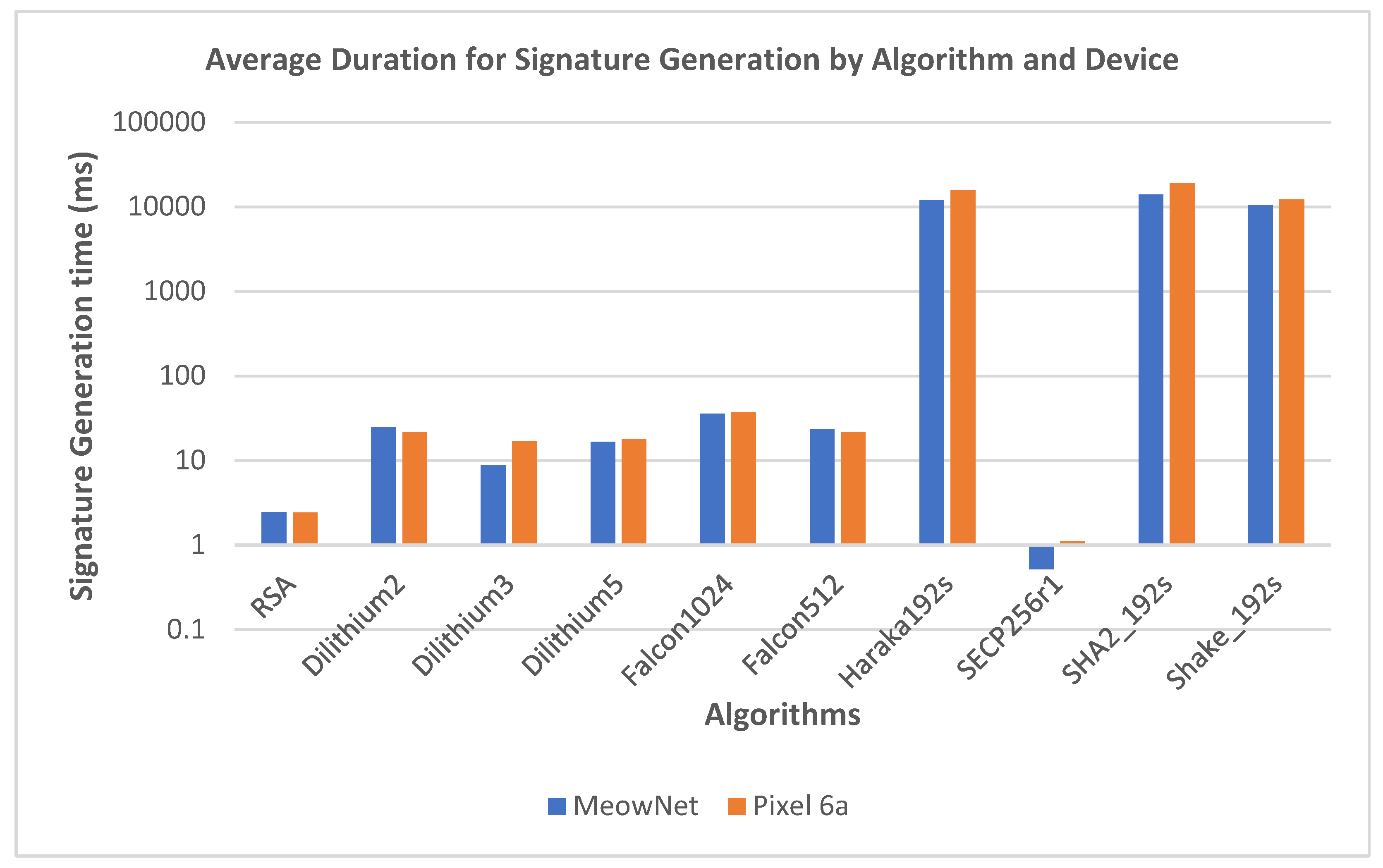
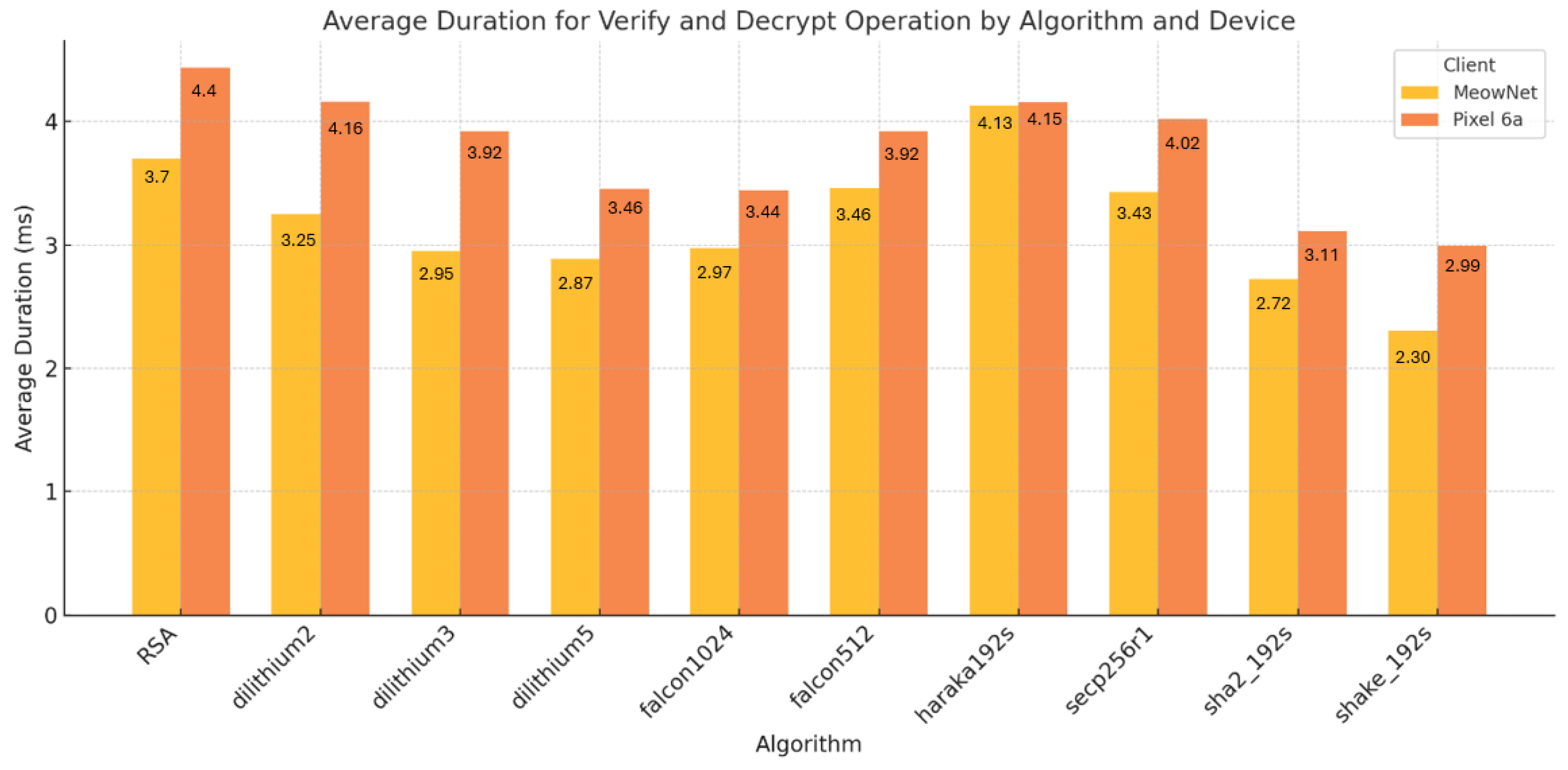
5.2. Digital Signature Performance
5.3. Hardware Impacts to the Performance
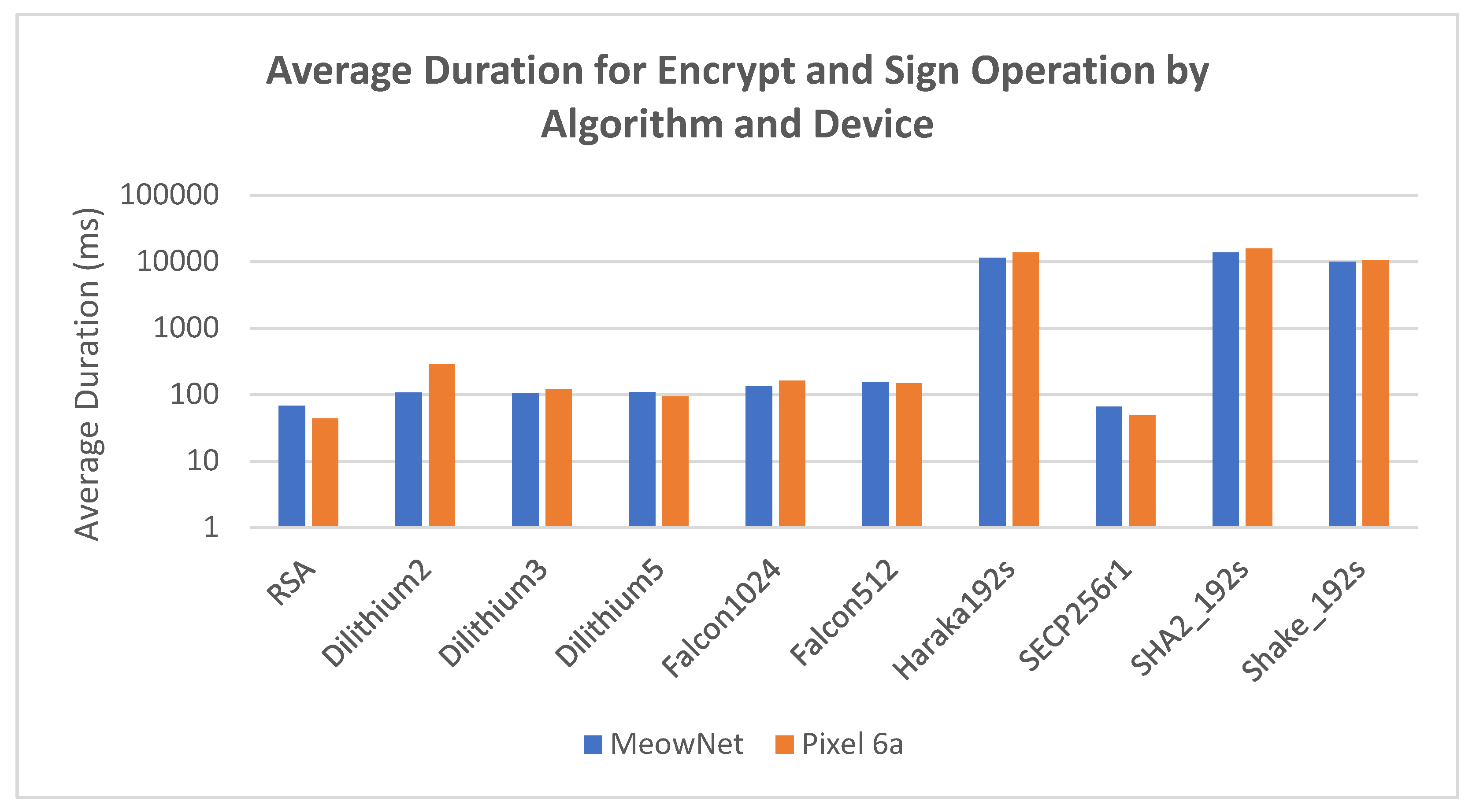
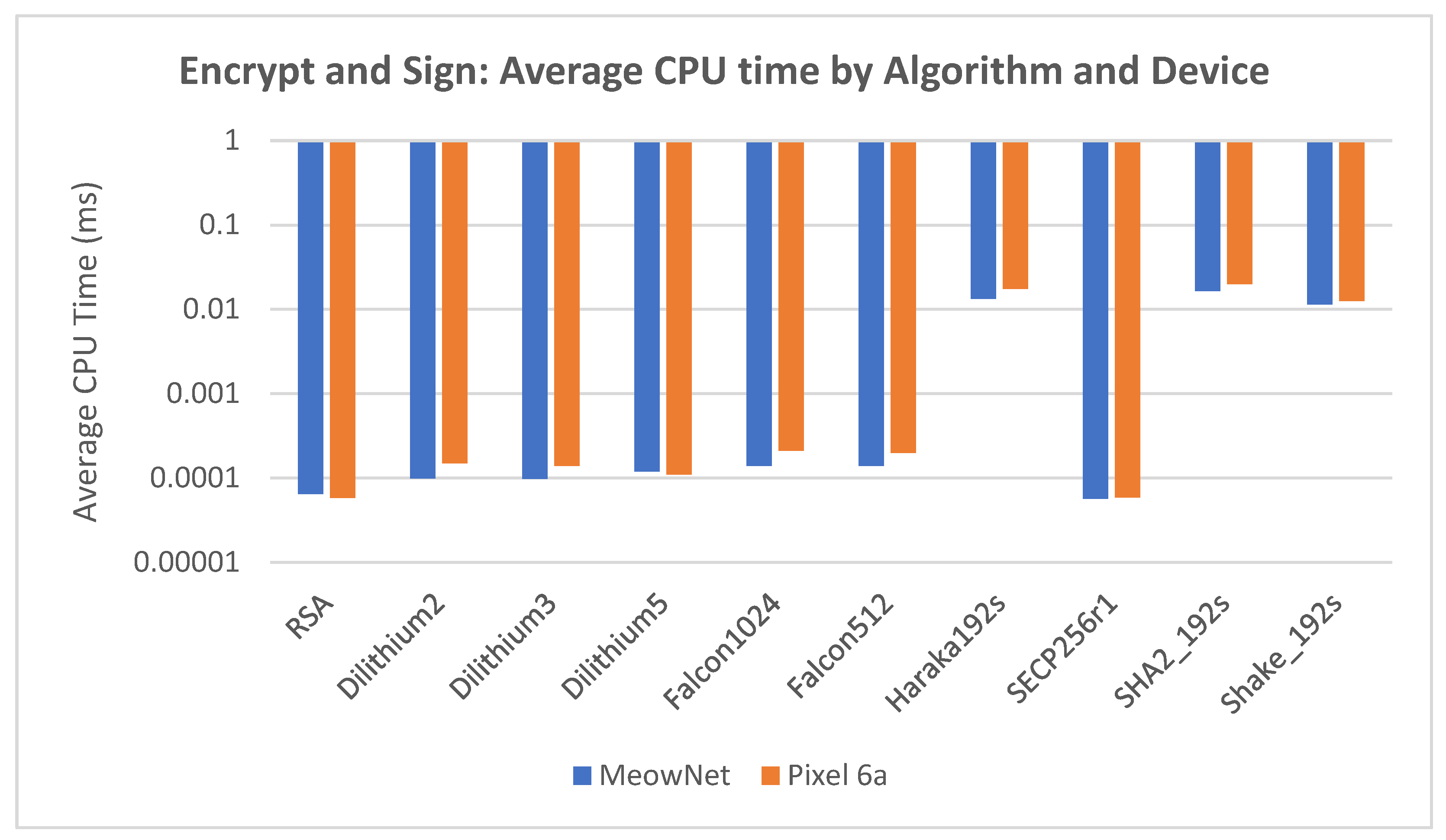
5.4. Performance Results
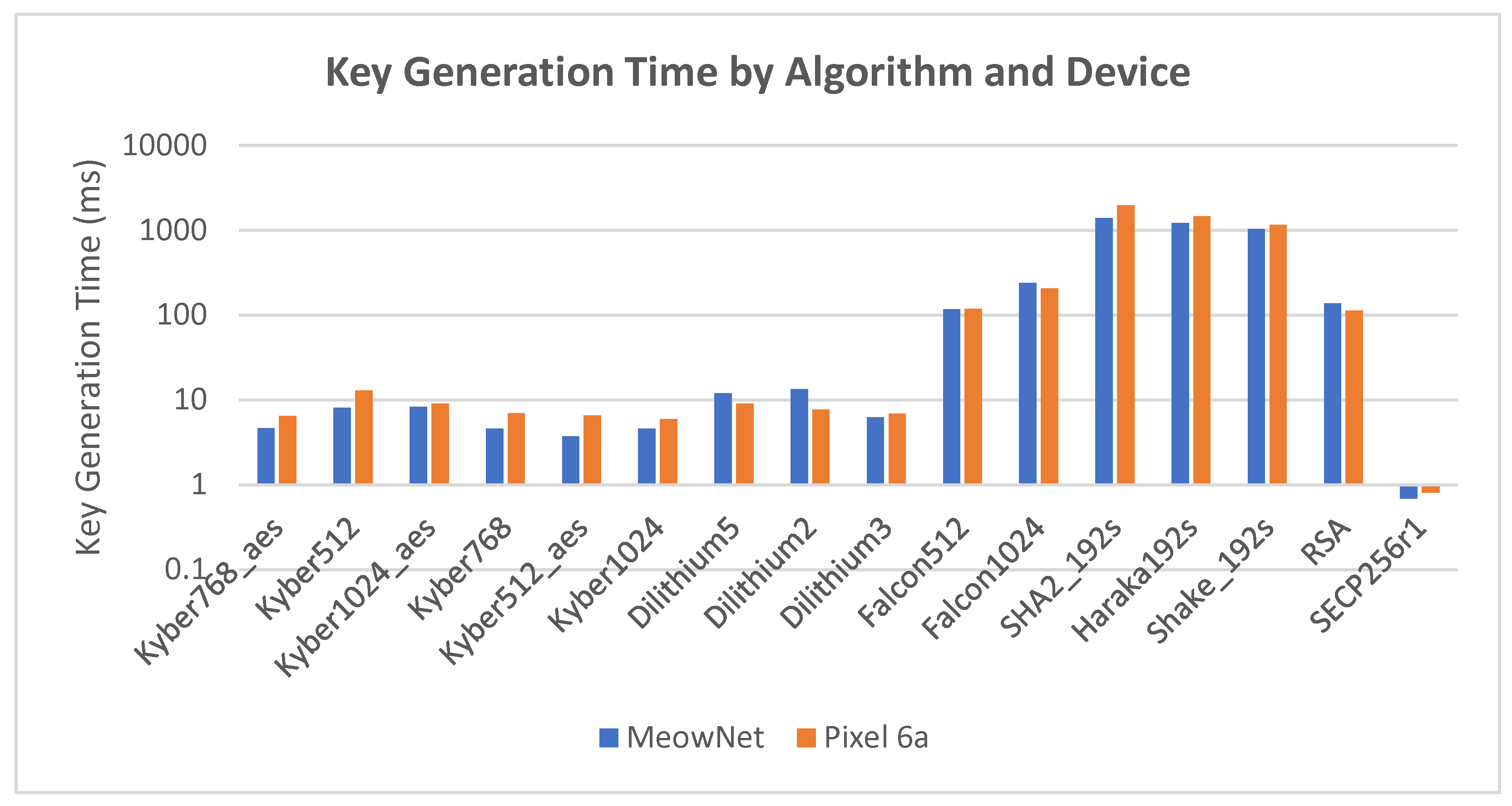
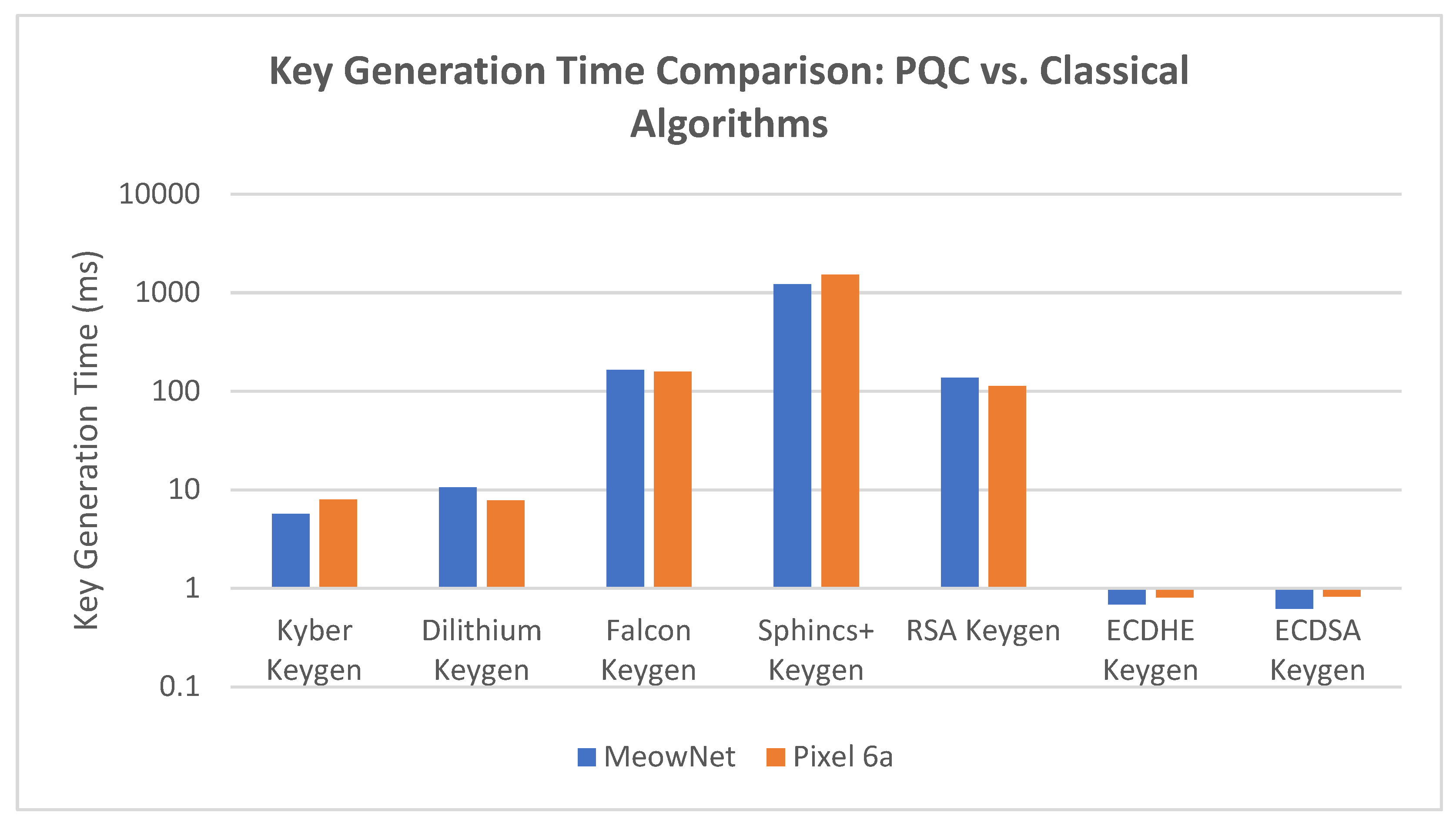
5.4.1. Key Generation Time
5.4.2. Digital Signature Generation Time
5.4.3. Encrypt and Sign Duration, CPU Time and Temperature Delta
5.4.4. Verify and Decrypt Duration, CPU Time and Temperature Delta
5.4.5. Individual Signature Generation Duration, CPU Time and Temperature Delta
5.4.6. Verify and Decrypt Operation Duration in Signature Verification
5.4.7. Key Exchange Duration, CPU Time and Temperature Delta
6. Discussions
6.1. Comparison of PQC Benchmarking Works
6.2. KEM Findings: Kyber on Mobile
6.3. Signature Findings: Dilithium vs Falcon vs SPHINCS+
6.4. Device and Hardware Effects
6.5. QoS Implications in 5G/6G Workloads
6.6. Computational Overheads and Thermal Considerations
7. Future Work
8. Challenges
8.1. Absence of Certificate Authority
8.2. Challenges for Mobile Application Development and PQC Integration
8.3. Message Routing and Payload Limits
8.4. PQC Library Maturity
9. Conclusion
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| ACM | AWS Certificate Manager |
| AEAD | Authenticated encryption with associated data |
| AES | Advanced Encryption Standards |
| AES-GCM | Advanced Encryption Standard - Galois/Counter Mode |
| API | Application Programming Interface |
| AWS | Amazon Web Service |
| CA | Certificate Authority |
| CPU | Central Processing Unit |
| DHE | Diffie-Hellman Ephemeral |
| ECDHE | Elliptic Curve Diffie-Hellman Ephemeral |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| FCM | Firebase Cloud Messaging |
| GCM | Galois/Counter Mode |
| IMDA | Infocomm Media Development Authority |
| IND-CCA | Indistinguishability security under the Chosen Ciphertext Attack |
| IoT | Internet of Things |
| IV | Initialization Vector |
| KDF | Key Derivative Function |
| KEM | Key Encapsulation Mechanism |
| KMS | Key Management Service |
| NIST | National Institute of Standards and Technology |
| PQC | Post Quantum Cryptography |
| QoS | Quality of Service |
| RSA | Rivest-Shamir-Adleman |
| SHA | Secure Hash Algorithm |
| TLS | Transport Layer Security |
References
- IBM. "How SSL and TLS provide identification authentication confidentiality and integrity", IBM MQ 7.5, 30th April 2018. Retrieved October 12, 2023. Available online: https://www.ibm.com/docs/en/ibm-mq/7.5?topic=ssl-how-tls-provide-authentication-confidentiality-integrity.
- Chamola, V.; Jolfaei, A.; Chanana, V.; Parashari, P.; Hassija, V. Information security in the post quantum era for 5G and beyond networks: Threats to existing cryptography, and post-quantum cryptography. Computer Communications 2021, 176, 99–118. [Google Scholar] [CrossRef]
- G. Amponis et al., "Towards Securing Next-Generation Networks: Attacking 5G Core/RAN Testbed," 2022 Panhellenic Conference on Electronics & Telecommunications (PACET), Tripolis, Greece, 2022, pp. 1-4. [CrossRef]
- Yang, H.; et al. Data-Driven Network Slicing From Core to RAN for 5G Broadcasting Services. IEEE Transactions on Broadcasting 2021, vol. 67(no. 1), 23–32. [Google Scholar] [CrossRef]
- M. B. Yassein, S. Aljawarneh, E. Qawasmeh, W. Mardini and Y. Khamayseh, "Comprehensive study of symmetric key and asymmetric key encryption algorithms," 2017 International Conference on Engineering and Technology (ICET), Antalya, Turkey, 2017, pp. 1-7. [CrossRef]
- M. Kim, Y. Shin and T. Shon, "MitM Tool Analysis for TLS Forensics," 2021 International Conference on Platform Technology and Service (PlatCon), Jeju, Korea, Republic of, 2021, pp. 1-4. [CrossRef]
- I. Kotuliak, P. Rybár and P. Trúchly, "Performance comparison of IPsec and TLS based VPN technologies," the 9th International Conference on Emerging eLearning Technologies and Applications (ICETA), Stara Lesna, Slovakia, 2011, pp. 217-221, 2011. [CrossRef]
- D. Mankowski, T. Wiggers and V. Moonsamy, "TLS → Post-Quantum TLS: Inspecting the TLS landscape for PQC adoption on Android," 2023 IEEE European Symposium on Security and Privacy Workshops (EuroS&PW), Delft, Netherlands, 2023, pp. 526-538. [CrossRef]
- J. Arora, K. Saluja, S. Gupta, S. Sharma and G. Kaur, "Handling Secret Key Compromise by Deriving Multiple Asymmetric Keys based on Diffie-Hellman Algorithm," 2023 8th International Conference on Communication and Electronics Systems (ICCES), Coimbatore, India, 2023, pp. 492-498. [CrossRef]
- V. Bhatia and K. R. Ramkumar, "An Efficient Quantum Computing technique for cracking RSA using Shor’s Algorithm," IEEE 5th International Conference on Computing Communication and Automation (ICCCA), Greater Noida, India, 2020, pp. 89-94. [CrossRef]
- Kudelski Security Team. Quantum Attack Resource Estimate: Using Shor’s Algorithm to Break RSA vs DH/DSA VS ECC. 24 August 2021. Available online: https://kudelskisecurity.com/research/quantum-attack-resource-estimate-using-shors-algorithm-to-break-rsa-vs-dh-dsa-vs-ecc.
- Palaganti Venkata Nagendra Sai Sandeep. The Quadratic Leap: How Grover's Algorithm is Redefining Core Problems in Computer Science and Engineering. International Journal of Innovative Science and Research Technology. Volume 10, Issue 7, July– 2025. [CrossRef]
- GSM Association, “The Mobile Economy” Retrieved October 12, 2023. Available online: https://www.gsma.com/mobileeconomy/.
- NIST, “PQC Standardization Process: Announcing Four Candidates to be Standardized, Plus Fourth Round Candidates” Retreived October 17, 2023. Available online: https://csrc.nist.gov/news/2022/pqc-candidates-to-be-standardized-and-round-4.
- Mehic, M.; et al. Quantum Cryptography in 5G Networks: A Comprehensive Overview. IEEE Communications Surveys & Tutorials 2024, vol. 26(no. 1), 302–346. [Google Scholar] [CrossRef]
- NIST. NIST, “NIST Releases First 3 Finalized Post-Quantum Encryption Standards”, Retrieved August 13, 2024. Available online: https://www.nist.gov/news-events/news/2024/08/nist-releases-first-3-finalized-post-quantum-encryption-standards.
- J. Lee, "How Quantum Computers Will Impact Bitcoin". Retrieved October 12, 2024. Available online: https://medium.com/@kyn04138/how-quantum-computers-will-impact-bitcoin-ebac8dae2a4e.
- NIST, “Post-Quantum Cryptography - Post-Quantum Cryptography Standardization” Retrieved October 27, 2023. Available online: https://csrc.nist.gov/Projects/post-quantum-cryptography/post-quantum-cryptography-standardization.
- NIST, “Status Report on the Third Round of the NIST Post-Quantum Cryptography Standardization Process”, Retrieved August 14, 2024. Available online: https://csrc.nist.gov/pubs/ir/8413/upd1/final.
- Google, “Meet Willow, our state-of-the-art quantum chip”, Retrieved December 17, 2024. Available online: https://blog.google/technology/research/google-willow-quantum-chip/.
- IBM. The hardware and software for the era of quantum utility is here. 13 January 2026. Available online: https://www.ibm.com/quantum/blog/quantum-roadmap-2033.
- F. Bene and A. Kiss, "Public Key Infrastructure in the Post-Quantum Era," 2023 IEEE 17th International Symposium on Applied Computational Intelligence and Informatics (SACI), Timisoara, Romania, 2023, pp. 000077-000082. [CrossRef]
- Shor, PW. Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM Journal of Computing 1997, vol. 26(no. 5), 1484–509. [Google Scholar] [CrossRef]
- B. Yan, Z. Tan, S. Wei, H. Jiang, W. Wang, H. Wang, L. Zuo, Q. Duan, Y. Liu, W. Shi, Y. Fei, X. Meng, Y. Han, Z. Shan, J. Chen, X. Zhu, C. Zhang, F. Jin, H. Li, C. Song, Z. Wang, Z. Ma, H. Wang and G. Long, “Factoring integers with sublinear resources on a superconducting quantum processor. arXiv:arxiv:2212.12372v1.
- E. Zeydan, Y. Turk, B. Aksoy and S. B. Ozturk, "Recent Advances in Post-Quantum Cryptography for Networks: A Survey," the Seventh International Conference On Mobile And Secure Services (MobiSecServ), Gainesville, FL, USA, 2022, pp. 1-8. [CrossRef]
- N. Gupta, A. Jati, A. Chattopadhyay and G. Jha, "Lightweight Hardware Accelerator for Post-Quantum Digital Signature CRYSTALS-Dilithium," in IEEE Transactions on Circuits and Systems I: Regular Papers, vol. 70, no. 8, pp. 3234-3243, Aug. 2023. [CrossRef]
- P. Kampanakis, T. Hansen, A. Volanis and G. Ravago, “Post-quantum hybrid SFTP file transfers using AWS Transfer Family”, AWS Security Blog, June 3, 2023. Retrieved October 12, 2023. Available online: https://aws.amazon.com/blogs/security/post-quantum-hybrid-sftp-file-transfers-using-aws-transfer-family/.
- R. Zhou, H. Guo, F. E. C. Teo and S. Bakiras, "A Survey on Post-Quantum Cryptography for 5G/6G Communications," 2023 IEEE International Conference on Service Operations and Logistics, and Informatics (SOLI), Singapore, 2023, pp. 1-6. [CrossRef]
- G. R. Mounica, G. Manimaran, L. B. Jerome and P. Bhattacharjee, "Implementation of 5-Qubit approach-based Shor's Algorithm in IBM Qiskit," 2021 IEEE Pune Section International Conference (PuneCon), Pune, India, 2021, pp. 1-6. [CrossRef]
- B. B. OBE, “Energy Consumption of Post Quantum Cryptography: Dilithium and Kyber Beat Our Existing TLS 1.3 Performance”, ASecuritySite: When Bob Met Alice. Retrieved October 12, 2023. Available online: https://medium.com/asecuritysite-when-bob-met-alice/energy-consumption-of-post-quantum-cryptography-dilithium-and-kyber-beat-our-existing-tls-1-3-ccadd04dd4c7.
- G. Tasopoulos. C. Dimopoulos, A. P. Fournaris, R. K. Zhao, A. Sakzad and R. Steinfeld, “Energy Consumption Evaluation of Post-Quantum TLS 1.3 for Resource-Constrained Embedded Devices,” Cryptology ePrint Archive, Paper 2023/506.
- B. Jarvis, “How to tune TLS for hybrid post-quantum cryptography with Kyber”, AWS Security Blog, July 5, 2022. Retrieved October 12, 2023. Available online: https://aws.amazon.com/blogs/security/how-to-tune-tls-for-hybrid-post-quantum-cryptography-with-kyber/.
- Dames, “Available on IBM z16: Future-Proof Digital Signatures with a Quantum-Safe Algorithm Selected by NIST”, IBM Blog, July 26, 2022. Retrieved October 12, 2023ignatures with a Quantum-Safe Algorithm Selected by NIST”. Available online: https://www.ibm.com/blog/announcement/available-on-ibm-z16-future-proof-digital-signatures-with-a-quantum-safe-algorithm-selected-by-nist/.
- Westerbaan, and C. D. Rubin, “Defending against future threats: Cloudflare goes post-quantum”, The Cloudflare Blog, October 3, 2022. Retrieved October 12, 2023. Available online: https://blog.cloudflare.com/post-quantm-for-all/.
- W. Evans, and B. Westerbaan, “Post-quantum crypto should be free, so we’re including it for free, forever”, The Cloudflare Blog, March 16, 2023. Retrieved October 12, 2023. Available online: https://blog.cloudflare.com/post-quantum-crypto-should-be-free/.
- Ruben Gonzalez. Kyber - How does it work? Approachable Cryptography. September 14, 2021. Retrieved December 13, 2025. Available online: https://cryptopedia.dev/posts/kyber/.
- Alfred Menezes. V2: Kyber PKE and KEM. August 14, 2024. Retrieved December 13, 2025. Available online: https://www.youtube.com/watch?v=nlGjqGdkmfI.
- Popov, Denys. CRYSTALS-Dilithium: The Digital Signature Scheme for the Post-Quantum Era. Medium. 25 August 2025. Available online: https://denispopovengineer.medium.com/crystals-dilithium-the-digital-signature-scheme-for-the-post-quantum-era-d8ba8f0213b9.
- NIST. Module-Lattice-Based Digital Signature Standard. FIPS 204 Federal Information Processing Standards Publication. August 13, 2024. [CrossRef]
- Shi Bai, Léo Ducas, Eike Kiltz, Tancrède Lepoint, Vadim Lyubashevsky, Peter Schwabe, Gregor Seiler and Damien Stehlé. CRYSTALS-Dilithium Algorithm Specifications and Supporting Documentation (Version 3.1). February 8, 2021.
- Falcon – A Post-Quantum Signature Scheme. June 28, 2019. Available online: https://pqshield.com/falcon-a-post-quantum-signature-scheme/.
- Pierre-Alain Fouque, Jeffrey Hoffstein, Paul Kirchner, Vadim Lyubashevsky, Thomas Pornin, Thomas Prest, Thomas Ricosset. Gregor Seiler, William Whyte, Zhenfei Zhang. Falcon: Fast-Fourier Lattice-based Compact Signatures over NTRU. Specification v1.2 — 01/10/2020. Available online: https://falcon-sign.info/falcon.pdf.
- Alfred Menezes. Lecture 6. SPHINCS+ (Hash-Based Signatures). Available online: https://www.youtube.com/watch?v=Z93yiDyPUzE&t=124s.
- NIST. Stateless Hash-Based Digital Signature Standard. FIPS 205 Federal Information Processing Standards Publication. August 13, 2024. https://doi.org/10.6028/NIST.FIPS.205. [CrossRef]
- Udara Pathum, "CRYSTALS Kyber: The Key to Post-Quantum Encryption. Identity Beyond Borders.", Retrieved August 14, 2024. Available online: https://medium.com/identity-beyond-borders/crystals-kyber-the-key-to-post-quantum-encryption-3154b305e7bd.
- F. Lauterbach, P. Burdiak, F. Richter, and M. Voznak, “Performance analysis of post-quantum algorithms,” in Proc. 29th Telecommun. Forum (TELFOR), 2021, pp. 1–4.
- W. J Buchanan, “PQC Key Encapsulation Mechanism (KEM) Speed Tests,” Asecuritysite.com, 2023. Retrieved October 12, 2023. Available online: https://asecuritysite.com/pqc/pqc_kem.
- W. J Buchanan, “PQC Digital Signature Speed Tests,” Asecuritysite.com, 2023. Retrived October 12, 2023. Available online: https://asecuritysite.com/pqc/pqc_sig.
|
Equivalent (classical) bit security |
Minimum qubits needed to attack RSA, DSA | Minimum qubits needed to attack ECDSA and similar ECC schemes |
| 112 | 4098 | 2042 |
| 128 | 6146 | 2330 |
| 192 | 15362 | 3484 |
| Algorithm | PQC - KEM | |||
| Security Level | Private key length | Public key length | Ciphertext length | |
| Kyber512 | 1 | 1632 | 800 | 768 |
| Kyber768 | 3 | 2400 | 1184 | 1088 |
| Kyber1024 | 5 | 3168 | 1568 | 1568 |
| Algorithm | PQC Digital Signature Schemes | |||
|---|---|---|---|---|
| Security Level | Private key length | Public key length | Signature length | |
| Dilithium2 | 2 | 2528 | 1312 | 2420 |
| Dilithium3 | 3 | 4000 | 1952 | 3293 |
| Dilithium5 | 5 | 4864 | 2592 | 4595 |
| Falcon512 | 1 | 1281 | 897 | 690 |
| Falcon1024 | 5 | 2305 | 1793 | 1330 |
| SPHINCS+-Haraka-128f | 1 | 64 | 32 | 17088 |
| SPHINCS+-Haraka-128s | 1 | 64 | 32 | 7856 |
| SPHINCS+-Haraka-192f | 3 | 96 | 48 | 35664 |
| SPHINCS+-Haraka-192s | 3 | 96 | 48 | 16224 |
| SPHINCS+-Haraka-256f | 5 | 128 | 64 | 49856 |
| SPHINCS+-Haraka-256s | 5 | 128 | 64 | 29792 |
| SPHINCS+-SHA256-128f | 1 | 64 | 32 | 17088 |
| SPHINCS+-SHA256-128s | 1 | 64 | 32 | 7856 |
| SPHINCS+-SHA256-192f | 3 | 96 | 48 | 35664 |
| SPHINCS+-SHA256-192s | 3 | 96 | 48 | 16224 |
| SPHINCS+-SHA256-256f | 5 | 128 | 64 | 49856 |
| SPHINCS+-SHA256-256s | 5 | 128 | 64 | 29792 |
| SPHINCS+-SHAKE256-128f | 1 | 64 | 32 | 17088 |
| SPHINCS+-SHAKE256-128s | 1 | 64 | 32 | 7856 |
| SPHINCS+-SHAKE256-192f | 3 | 96 | 48 | 35664 |
| SPHINCS+-SHAKE256-192s | 3 | 96 | 48 | 16224 |
| SPHINCS+-SHAKE256-256f | 5 | 128 | 64 | 49856 |
| SPHINCS+-SHAKE256-256s | 5 | 128 | 64 | 29792 |
| Key Exchange Algorithm | Security Level |
| RSA | Weak against quantum attacks |
| DHE | Moderate (large keys needed) |
| ECDHE | Stronger than DHE with smaller keys |
| Kyber (PQC) | Quantum-resistant |
|
Study / Citation |
Application Domain |
Devices Used | OS |
PQC Algorithms Evaluated |
Performance Items Measured | Libraries / APIs Used | Key Differences vs. Your Study |
| Our Work | Mobile communication workflow; real Android chat-style PQC message exchange |
Consumer smart-phones | Android | Kyber, Dilithium, Falcon, SPHINCS+ |
Key generation, signing, verification, encryption, decryption, CPU-time, temperature delta | BouncyCastle PQC provider, custom Android instrumentation, Firestore logging |
Full PQC workflow implementation inside a mobile app with real device metrics, temperature tracking, and Firebase-based message flow. Fully end-to-end mobile benchmarking, not desktop simulation. |
| Lauterbach [26] | General Internet data protection and secure communication over networks | PC-class platform is used. | Linux (Ubuntu) | Kyber, Dilithium |
Operation duration, CPU cycles | Not Specified | Desktop-only. No mobile OS, no thermal analysis. No mobile workflow or messaging integration. |
| Asecuritysite [30,47,48] | General algorithm speed comparison | Desktop / laptop CPU | Linux | Kyber, BIKE, HQC, FrodoKEM, Dilithium, Falcon, SPHINCS+ |
Basic keygen/sign/verify timing | Not Specified | Not real devices. No temperature or mobile CPU/thermal constraints. Not an application workflow. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




