Submitted:
02 January 2026
Posted:
06 January 2026
You are already at the latest version
Abstract
Keywords:
1. Foundations of Privacy-Preserving Mobile Payments
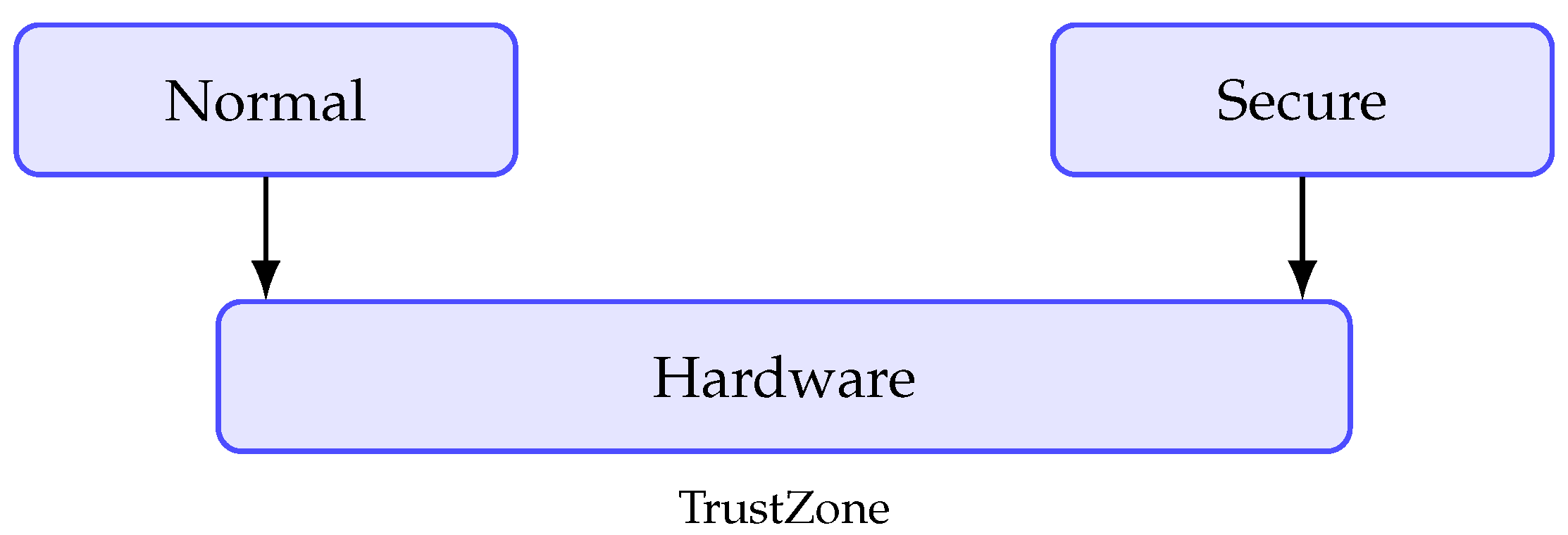
2. ARM Trust Zone and Secure Hardware Integration
3. AI-Enhanced Risk Detection in Anonymous Transactions
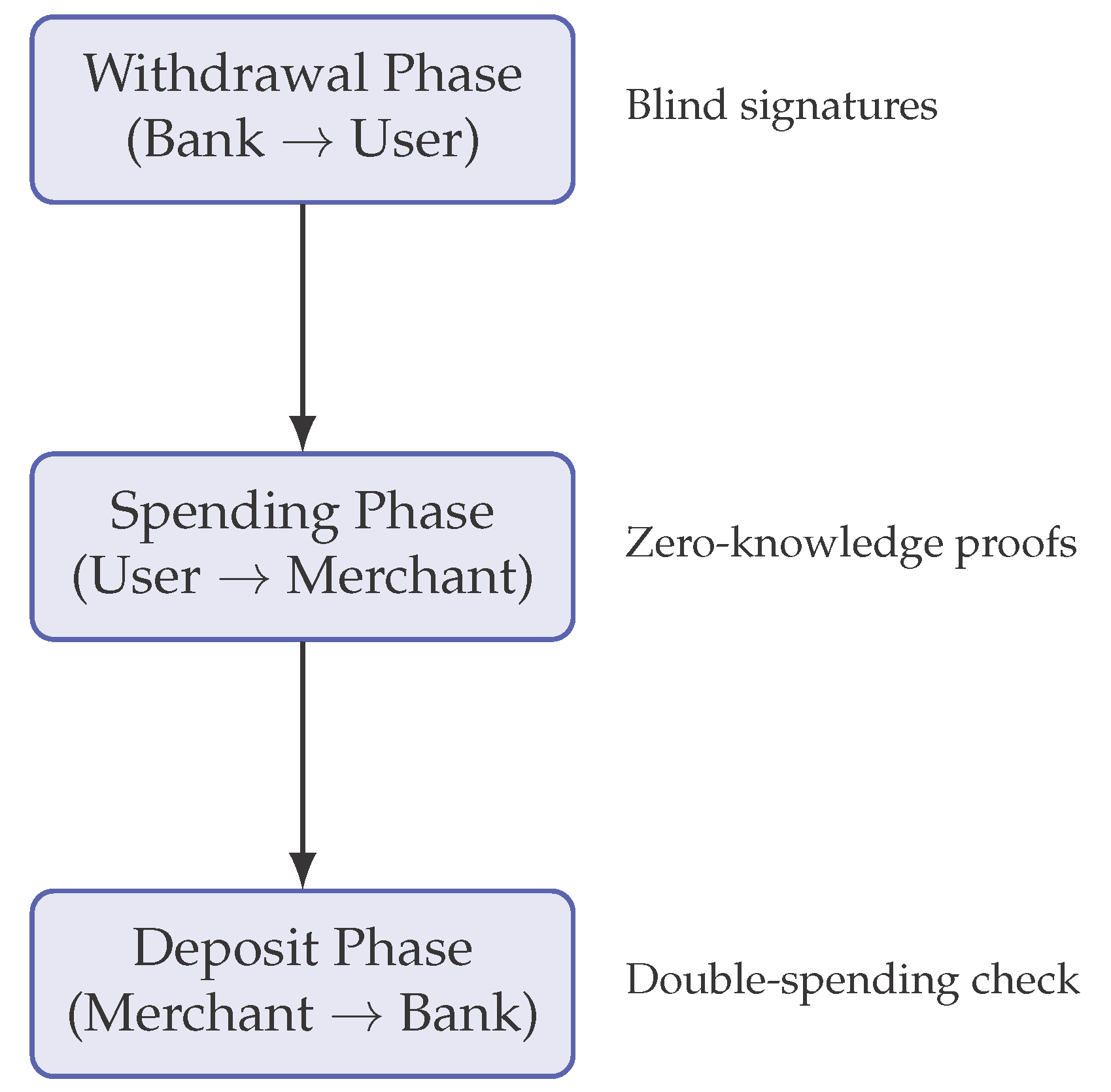
4. System Design and Protocol Specification of AEP-M
- Protocol Sequence Depiction: By providing a visual display of the complex intervening steps for interaction between user, bank and merchant, this figure provides the user more the understanding of the multi-phase protocol.
- Trust Zone Integration Points: The diagram clearly indicates which steps occur within the Trust Zone secure environment (authorization of withdrawal, division of coins, verification of spending). This shows how secure hardware is built into every step of the process.
- Cryptographic Operation Mapping: The mapping of cryptographic functions (blind signature, zero-knowledge proof, accumulator) to their corresponding steps in the protocol allows the reader to correlate theory to practice.
- Artificial Intelligence Utility: The figure gives a picture in which point the AI phase of detection is utilized in conjunction with the withdrawal and spending phases and indicates how this is used to enable machine learning for the cryptographic defense.
- Anonymity: This drawing shows clearly where anonymity is preserved with respect to identity of the user (during withdrawal by way of blind signing) and where that of unlikability is connoted as retained (spending steps by means of zero- knowledge proofs).
5. Security Analysis
5.1. Threat Model
- Malicious Users: Users who are trying to double spend coins, forge digital cash, or de-anonymize other users.
- Malicious Merchants: Merchants who may be trying to replay or reuse the coins or coin tokens or may be trying to de-anonymize users during their transactions.
- Compromised Devices: Attackers who have gained root access to the normal world may be trying to extract keys or re-arrange normal payment operations.
- Outside Attackers: Attackers who eavesdrop on communication channels to trace transactions or inject messages into the channel.
- Malicious Banks or Authorities: Banks and authorities trying to trace transactions to certain users despite the anonymity guarantees.
- AI Model Poisoning: Adversaries may attempt to corrupt federated learning updates to degrade fraud detection accuracy.
5.2. Security Properties
5.2.1. Anonymity and Unlinkability
- Formal Guarantee: Under the Decisional Diffie-Hellman (DDH) assumption and the random oracle model, no probabilistic polynomial-time adversary can distinguish between two honest users’ transactions with non-negligible advantage.
- Informal Argument: Blind signatures during withdrawal ensure the bank cannot link issued coins to specific users. Zero-knowledge proofs during spending prevent merchants from learning coin origins or user identities. The divisible e-cash construction ensures that different spends from the same coin cannot be linked without the secret tracing key.
5.2.2. Double-Spending Prevention
- Formal Guarantee: The probability of successful double-spending is negligible under the strong RSA assumption and the security of the underlying signature scheme.
- Informal Argument: Each coin fragment contains a unique serial number that is revealed during spending. If the same serial number is deposited twice, the bank immediately detects double-spending. The trusted authority can then use the exposed serial number to identify the malicious user through the embedded identity recovery mechanism.
5.2.3. Unforgeability
- Formal Guarantee: The e-cash scheme is existentially unforgeable against adaptive chosen-message attacks under the security of the blind signature scheme and the discrete logarithm assumption.
- Informal Argument: Coin generation requires valid blind signatures from the bank, which cannot be forged without the bank’s private key. The binary tree structure of divisible coins ensures that coin fragments cannot be manipulated to create unauthorized value.
5.2.4. AI Model Integrity
- Formal Guarantee: The federated learning protocol with differential privacy () ensures that individual user data cannot be inferred from model updates.
- Informal Argument: Model updates are cryptographically signed and verified within TrustZone before acceptance. Differential privacy noise prevents reconstruction of training data, while secure aggregation in federated learning protects individual contributions.
5.3. Formal Security Arguments
5.3.1. Anonymity Proof Sketch
- 1.
- generates two legitimate users and and receives a challenge transaction from one of them.
- 2.
- uses zero-knowledge simulator techniques to generate transaction proofs without knowing the user’s identity.
- 3.
- If can determine which user generated the transaction with non-negligible advantage, we can use to break the DDH assumption or the zero-knowledge property of the proof system, leading to a contradiction.
5.3.2. Unforgeability Proof Sketch
- 1.
- Assume an adversary can forge a valid coin with non-negligible probability.
- 2.
- We construct a reduction that uses to break the blind signature security.
- 3.
- intercepts ’s forgery and extracts a valid signature without interacting with the signer, violating the unforgeability of the blind signature scheme.
5.4. TrustZone Security Considerations
- Isolation: Critical operations (key management, coin division, AI inference) execute in the secure world, protected from normal-world malware.
- Secure Storage: Coin fragments and cryptographic keys are encrypted using device-bound keys derived from SRAM PUF, preventing offline extraction.
- Side-Channel Mitigation: Constant-time cryptographic implementations and cache flushing at world boundaries reduce timing and cache side-channel vulnerabilities.
5.5. Limitations and Attack Surface
- Quantum Attack: Like the elliptic curve-based systems, AEP-M is vulnerable to quantum attacks. Such attacks can be eased by going to post-quantum cryptography. Migration to post-quantum cryptography is discussed in Section VI.
- Implementation Bugs in the Trust Zone: Bugs in OP-TEEE or the secure world code could open loopholes for attack. For example, a formal verification of the trusted applications would mitigate this problem.
- Physical Attacks: While SRAM PUF will protect against software generated attacks, there are possible advanced physical attacks.
- AI Evasion Attacks: It is possible to design transactions in a manner that the fraud detection process may not notice them. However, via continuous retraining of the model and adversarial training modes, we can increase robustness.
5.6. Security Comparison
- Better guarantees of privacy because of the cryptographic anonymity
- Better hardware protection because of the Trust Zone isolation
- Adaptive fraud detection without breaking privacy
- Conditional traceability only if fraud is shown
6. Implementation, Evaluation, and Efficiency Metrics
6.0.0.1. Prototype Platform.
6.0.0.2. Cryptographic Primitives.
6.0.0.3. Divisibility and State.
6.0.0.4. AI Inference in the TEE.
6.0.0.5. Training and Updates.
6.0.0.6. Measurement Methodology.
6.0.0.7. Baselines.
6.0.0.8. Latency Results.
6.0.0.9. Throughput and Concurrency.
6.0.0.10. Energy Consumption.
6.0.0.11. Storage Footprint.
6.0.0.12. Scalability and Batching.
6.0.0.13. Security Overheads.
6.0.0.14. Ablation on AI Model Size.
6.0.0.15. Robustness and Updates.
6.0.0.16. Limitations.
6.0.0.17. Summary.
7. Future Outlook in Secure Mobile E-Payment Architectures
References
- Chaum, D. Blind signatures for untraceable payments. Advances in Cryptology 1983, 199–203. [Google Scholar]
- Tang, Q.; Yang, K. Divisible E-cash schemes: constructions, security, and applications. Theoretical Computer Science 2017, 679, 1–15. [Google Scholar]
- Holdings, A. ARM TrustZone Technology Overview Whitepaper, 2019. Available online: https://developer.arm.com/technologies/trustzone.
- Bonneau, J.; Miller, A.; Clark, J.; Narayanan, A.; Kroll, J.A.; Felten, E.W. SoK: Research perspectives and challenges for Bitcoin and cryptocurrencies. In Proceedings of the IEEE Symposium on Security and Privacy, 2015; pp. 104–121. [Google Scholar]
- Li, X.; Zhang, Y. Mobile payments: architectures, security, and user privacy. Journal of Information Security and Applications 2021, 58, 102–120. [Google Scholar]
- Zhang, L.; Huang, Y.; Patel, K. AI for Privacy-Preserving Financial Transactions. IEEE Transactions on Information Forensics and Security 2022, 17, 3412–3426. [Google Scholar]
- Winter, J. Trusted computing building blocks for ARM TrustZone. In Proceedings of the Proceedings of the 1st ACM Workshop on Security and Privacy in Smartphones and Mobile Devices, 2012; pp. 55–64. [Google Scholar]
- Gassend, B.; Clarke, D.; van Dijk, M.; Devadas, S. Silicon physical random functions. In Proceedings of the Proceedings of the 9th ACM Conference on Computer and Communications Security, 2002; pp. 148–160. [Google Scholar]
- Bolton, R.J.; Hand, D.J. Statistical fraud detection: A review. Statistical Science 2002, 17, 235–255. [Google Scholar] [CrossRef]
- Dwork, C.; Roth, A. The algorithmic foundations of differential privacy; Now Publishers Inc, 2014. [Google Scholar]
- Arrieta, A.B.; et al. Explainable artificial intelligence (XAI): Concepts, taxonomies, opportunities and challenges toward responsible AI. Information Fusion 2020, 58, 82–115. [Google Scholar] [CrossRef]
- Linaro. OP-TEE: Open Portable Trusted Execution Environment, 2023. Project documentation and source. Available online: https://www.op-tee.org/.
- Bernstein, D.J.; Duif, N.; Lange, T.; Schwabe, P.; Yang, B.Y. High-speed high-security signatures. In Proceedings of the Proceedings of CHES, 2011; Springer; pp. 124–142. [Google Scholar]
- libsodium: A modern, portable, easy-to-use crypto library; Denis, F., Ed.; 2024; Available online: https://libsodium.org/.
- Dworkin, M. Technical Report SP 800-38D; Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC. NIST, 2007.
- McMahan, H.B.; Moore, E.; Ramage, D.; Hampson, S.; y Arcas, B.A. Communication-efficient learning of deep networks from decentralized data. In Proceedings of the Proceedings of the 20th International Conference on Artificial Intelligence and Statistics, 2017; pp. 1273–1282. [Google Scholar]
- Solutions, M. Monsoon Power Monitor, 2020. Available online: https://www.msoon.com/LabEquipment/PowerMonitor/.
- Pathak, A.; Hu, Y.C.; Zhang, M. PowerTutor: a power monitor for Android-based mobile platforms. In Proceedings of the Proceedings of MobiSys, 2011; pp. 1–5. [Google Scholar]
- NIST. Post-Quantum Cryptography Standardization, Round 3 Finalists, 2022. Available online: https://csrc.nist.gov/projects/post-quantum-cryptography.
- Bindel, N.; Brendel, J.; Fischlin, M.; Gonczarowski, Y. Hybrid key encapsulation mechanisms and authenticated key exchange. In Proceedings of the Proceedings of the ACM SIGSAC Conference on Computer and Communications Security, 2019; pp. 2199–2214. [Google Scholar]
- NIST. NIST Lightweight Cryptography Project, 2023. Available online: https://csrc.nist.gov/projects/lightweight-cryptography.
- Chen, H.; Xu, L.; Patel, D. Reinforcement learning for adaptive anomaly detection in finance. In Proceedings of the Proceedings of the AAAI Conference on Artificial Intelligence, 2021; pp. 1482–1490. [Google Scholar]
| Op. | AEP-M | TEE | SW |
|---|---|---|---|
| Withdraw | 14.8 / 18.9 | 15.1 / 19.6 | 12.7 / 16.2 |
| Spend | 3.6 / 5.1 | 4.7 / 6.4 | 3.1 / 4.2 |
| Deposit | 6.2 / 8.0 | 6.4 / 8.3 | 5.8 / 7.5 |
| Anomaly Inf. | 0.42 / 0.63 | 0.41 / 0.61 | 0.19 / 0.28 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




