Submitted:
10 December 2025
Posted:
29 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background Study
2.1. The Evolving Challenges in Cybersecurity Education
2.2. Game-Based Learning as an innovative solution
2.3. Educational Escape Rooms: Bridging Theory and Practice
- Limited Focus on Governance and Policy: Most cybersecurity games emphasize hands-on technical skills (e.g., cryptography, network defense) while neglecting broader governance, compliance, and policy topics. As a result, learners get little exposure to management-level cybersecurity decision-making and frameworks. This gap is problematic because organizational security relies not only on technical expertise but also on understanding policies, standards, and human factors.
- Minimal Empirical Validation: There is a lack of rigorous evaluation of learning outcomes in many game-based cybersecurity interventions. Few studies go beyond anecdotal evidence or simple pre/post surveys to empirically validate that players of these serious games retain knowledge or perform better in real-world scenarios. Without robust assessments (e.g., controlled studies or long-term follow-ups), it remains unclear how effective these games truly are in building cybersecurity competencies.
- Lack of Industry Alignment: Current cybersecurity games often show minimal alignment with industry practices and needs. Few are developed with direct input from industry professionals or mapped to widely used frameworks and certifications. Consequently, the scenarios and skills practiced in-game may not translate neatly to the challenges faced in the workplace. This gap in industry relevance means students might enjoy the game but still struggle to apply their knowledge on the job. Strengthening ties between game design and cyber industry standards (for example,
- integrating content from frameworks like NIST or ISO 27001) is largely an unmet need.
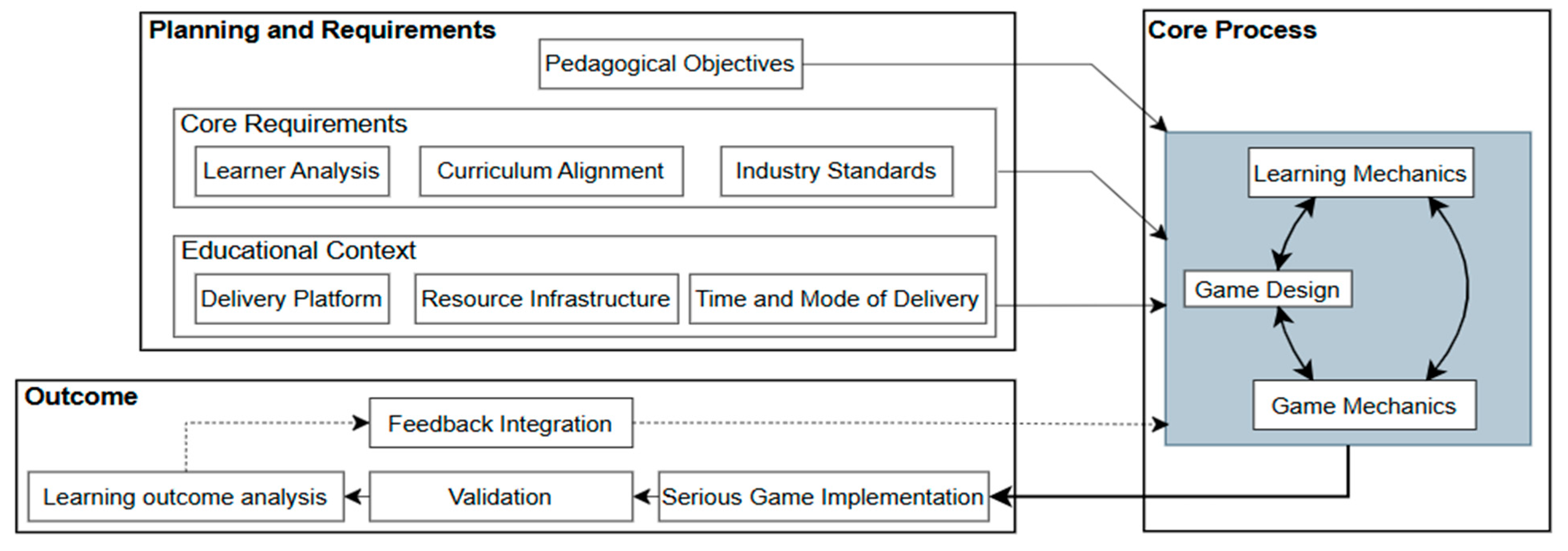
3. Research Methodology and System Development
3.1. Planning & Requirements Phase
3.2. Core Phase: Iterative Design Approach
3.3. Output Phase: Implementation and Validation
3.3.1. Serious Game Implementation and Validation
3.3.2. Iterative refinements
3.3.3. Final deliverables
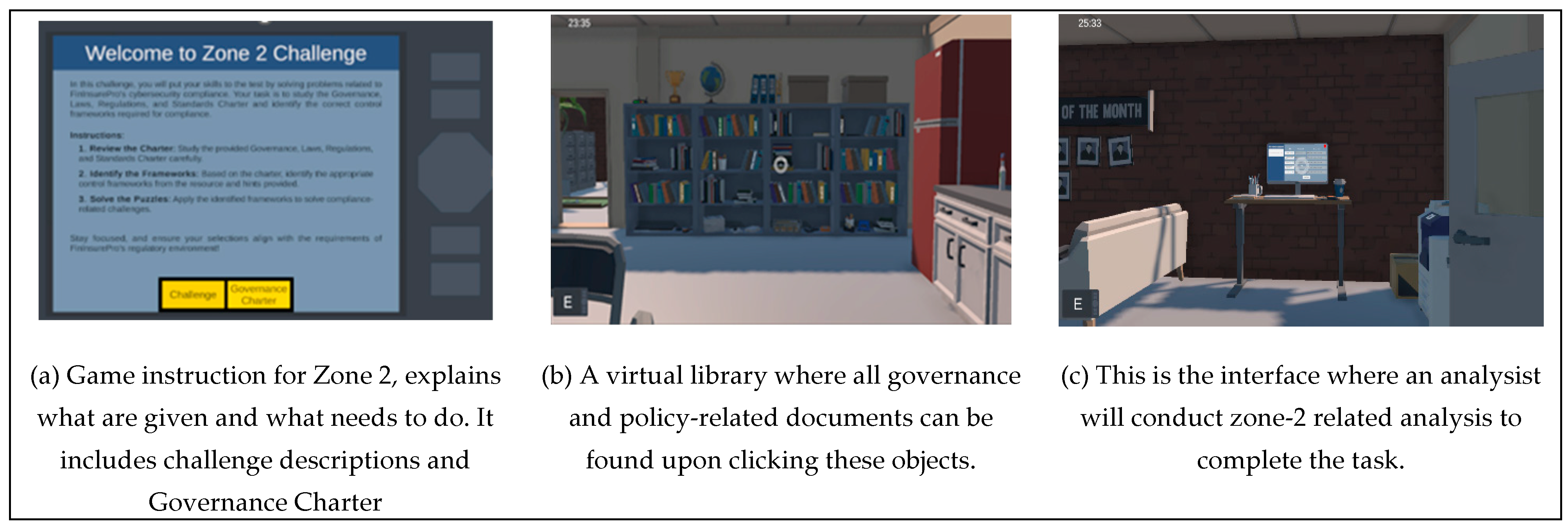
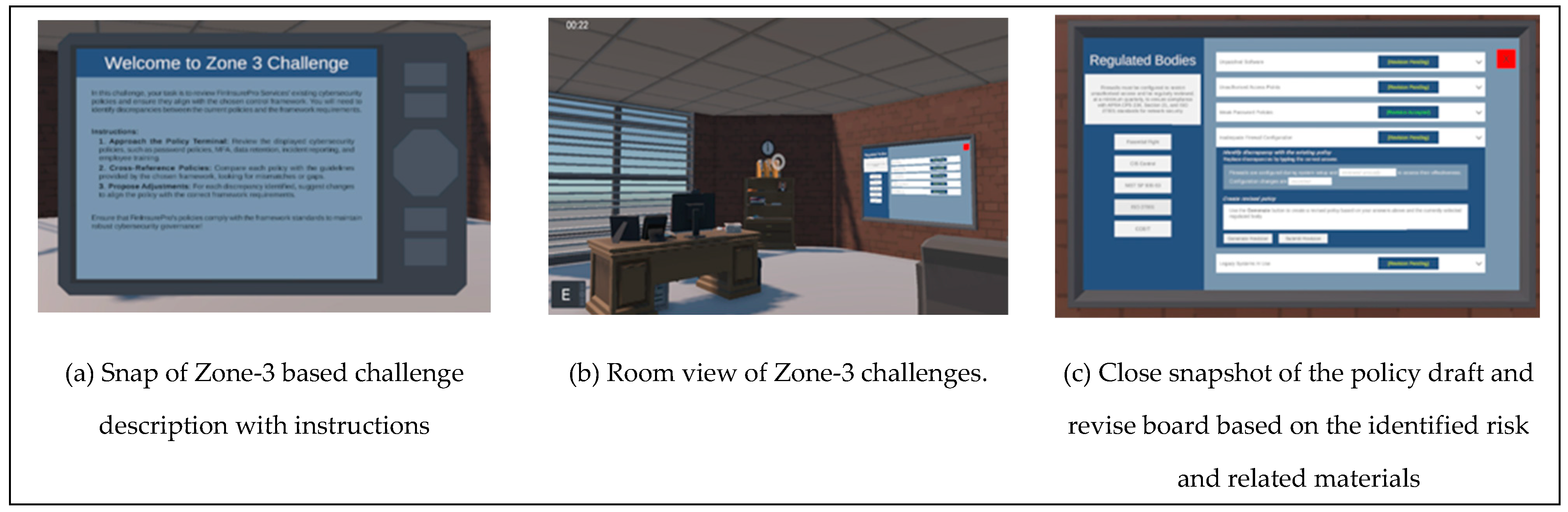
4. Development of UNSW Cyber Escape Room
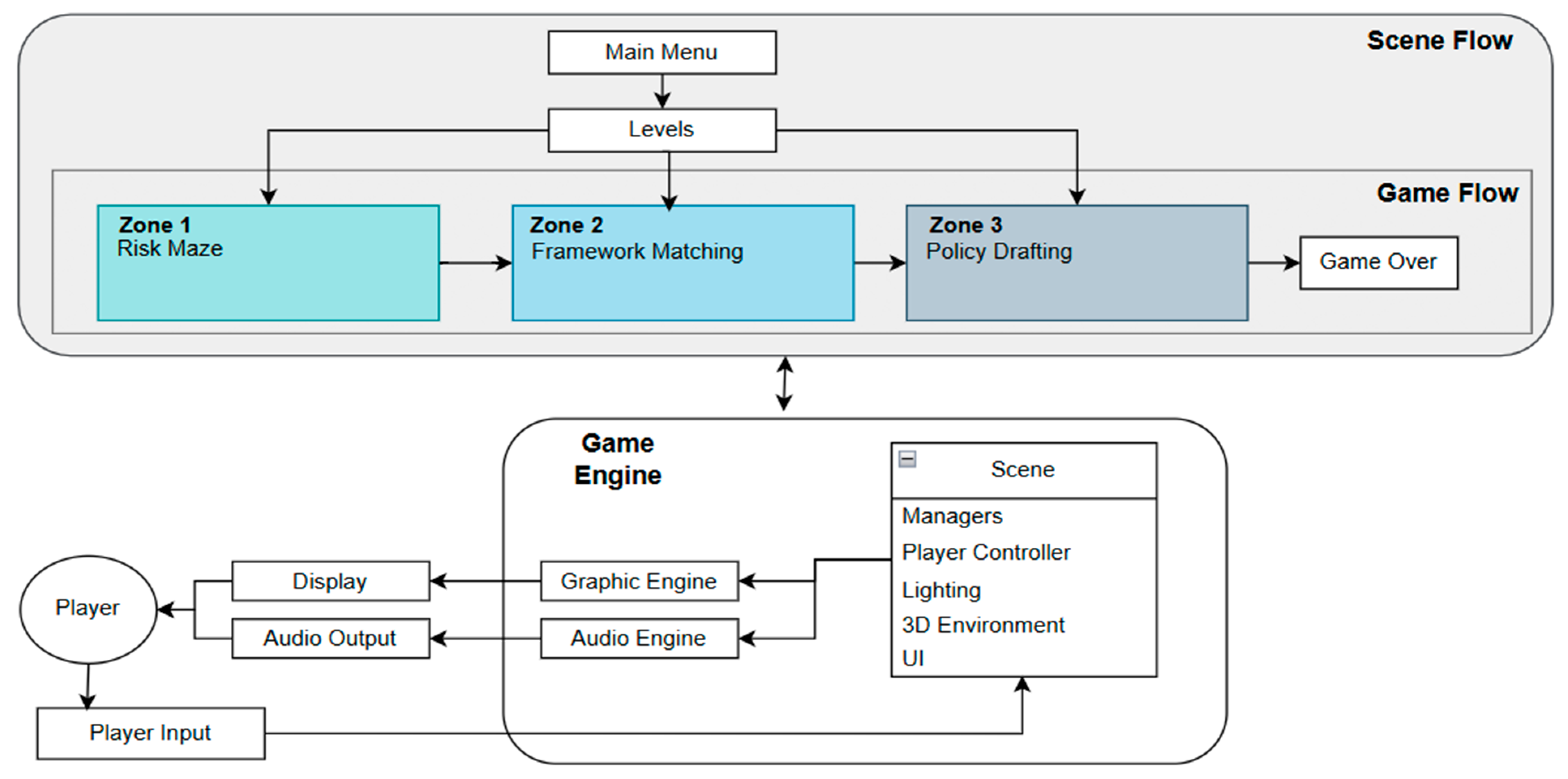
4.1. Game Architecture Overview
- Graphic Engine: Responsible for rendering the virtual environment and visual elements.
- Audio Engine: Manages sound effects and auditory feedback, enhancing engagement.
- Scene Management: Governs different game environments, including player interactions, lighting, and UI components.
- Player Controller: Facilitates user input and interaction, allowing players to navigate the escape room effectively.
4.2. Problem Formulation and Game Mechanics
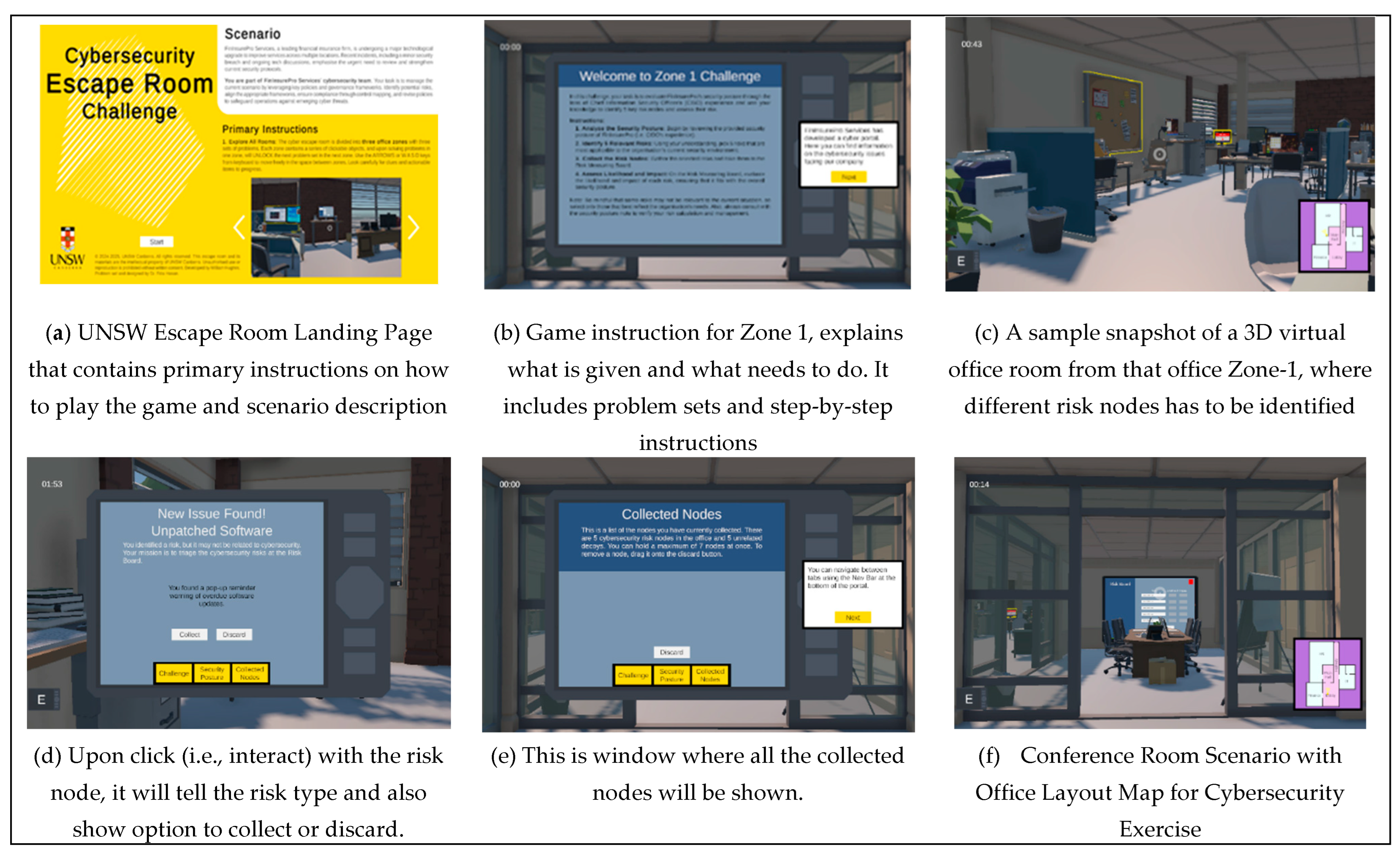
- Problem-based scenarios: Each room section presents context-specific risk scenarios derived from industry case studies, requiring students to apply the NIST Risk Management Framework methodology.
- Progressive complexity structure: Challenges increase in complexity through a scaffolded approach, beginning with straightforward risk identification tasks and advancing to scenarios requiring nuanced trade-off decisions between competing security priorities.
- Interactive decision points: At key junctures, students encounter interactive terminals that require risk classification according to industry standard matrices (likelihood × impact), with immediate feedback mechanisms that explain misalignments.
- Visual metaphor integration: The physical layout of the maze visually reinforces risk management concepts, with path blockages representing security controls and alternative routes demonstrating risk acceptance strategies.
- Sorting and classification mechanics: Interactive panels require students to match security controls to appropriate frameworks (e.g., NIST CSF, ISO 27001, GDPR), with increasing complexity as students’ progress.
- Framework comparison challenges: Advanced puzzles require identifying overlapping requirements across different standards, highlighting commonalities and differences in approaches.
- Contextual application scenarios: Industry-specific vignettes require students to identify which frameworks apply in different regulatory environments, with failure triggering remedial information.
- Terminology recognition exercises: Students must recognize framework-specific terminology and requirements through a series of matching challenges with time constraints.
- Template-based composition system: Students work with interactive policy templates containing mandatory elements (scope, roles, compliance requirements, enforcement mechanisms) that must be populated based on previous zone findings.
- Component selection mechanics: The interface presents policy element options that students must evaluate and select based on organizational context and identified risks.
- Policy evaluation algorithms: The system evaluates drafted policies against multi-dimensional criteria, including completeness, framework alignment, risk coverage, and stakeholder impact.
- Revision and feedback loops: Students receive structured feedback on policy drafts, identifying gaps or inconsistencies that require revision before zone completion.
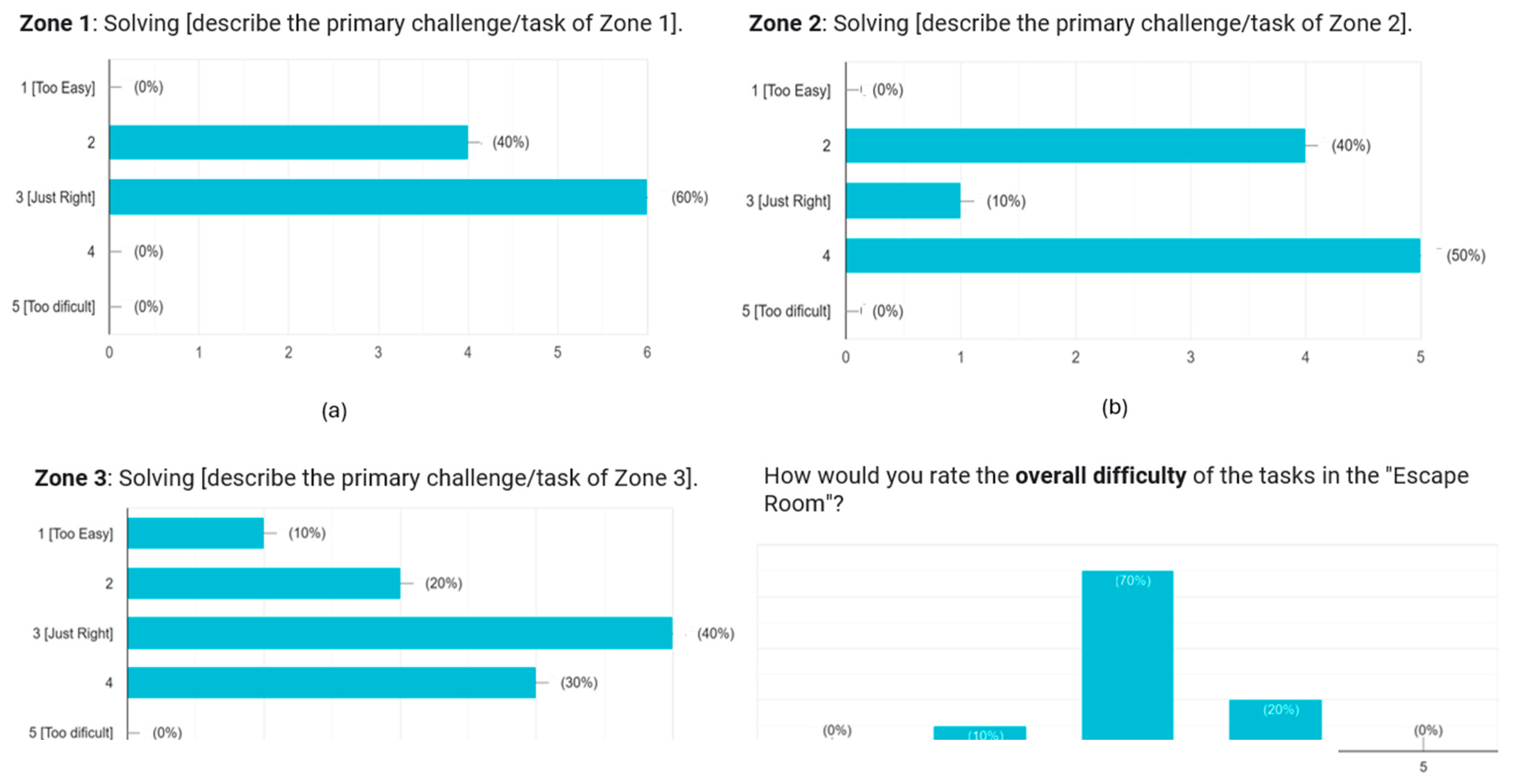
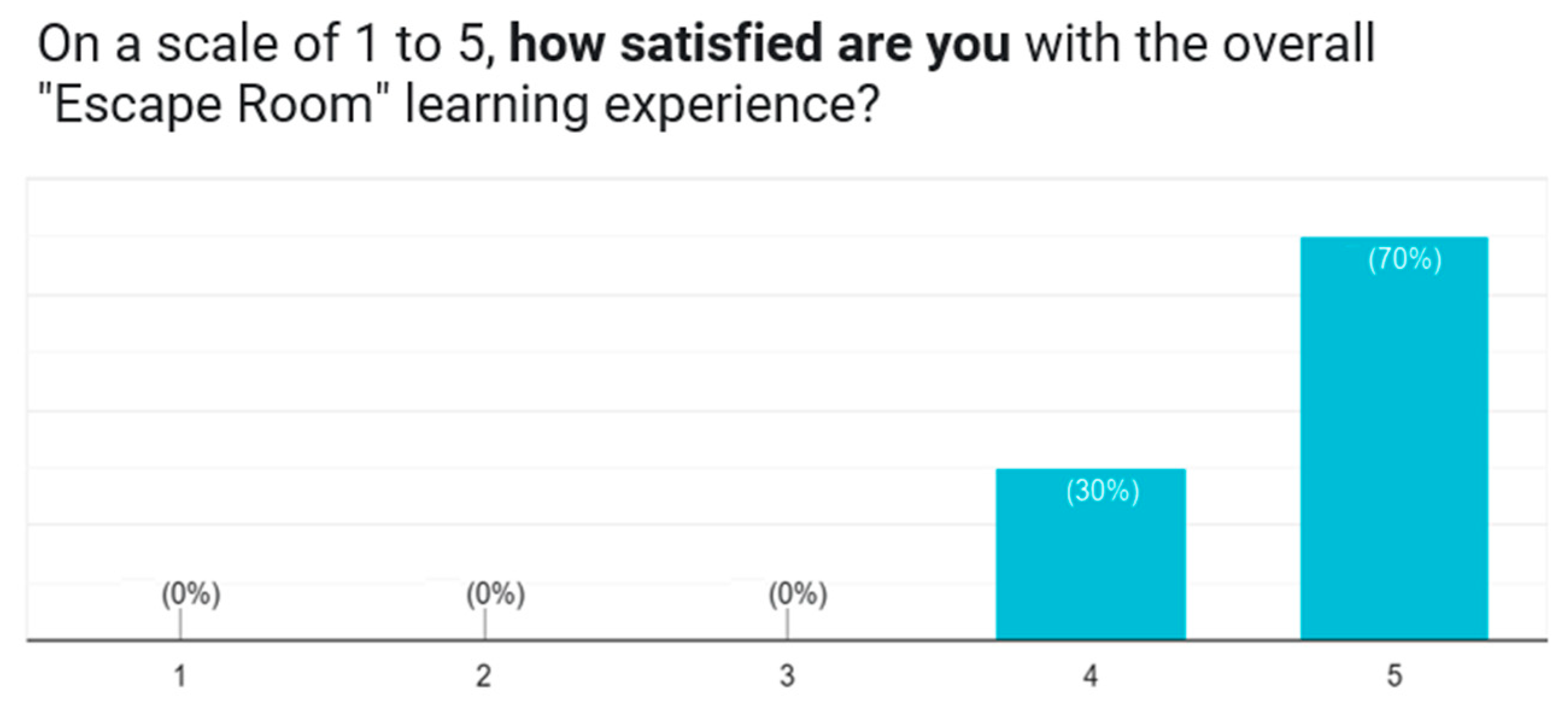
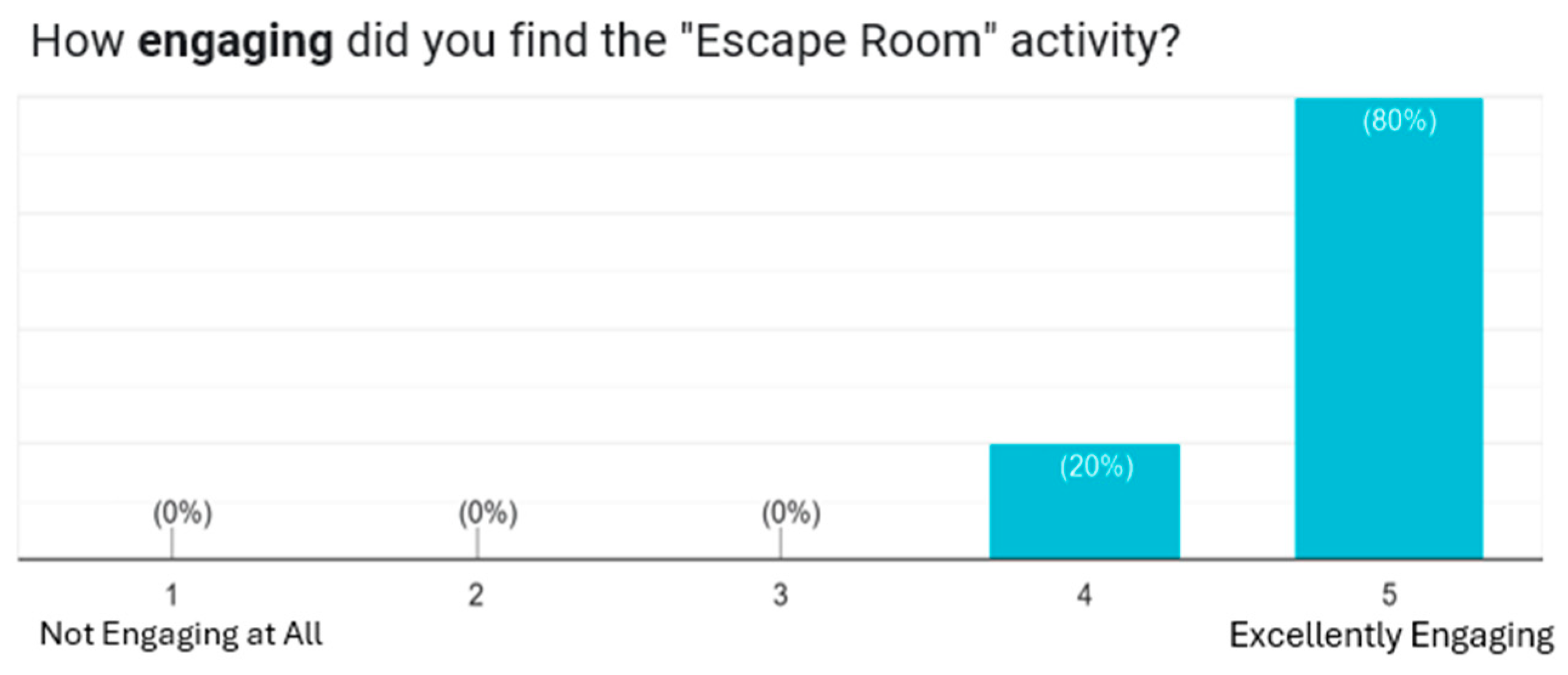
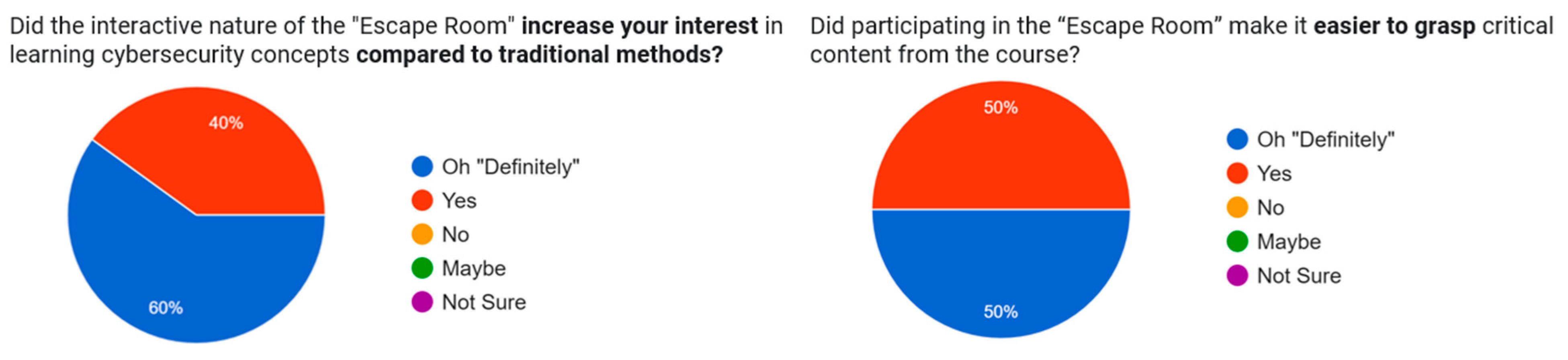
5. Evaluation, Results, and Discussion
6. Conclusion and Future Work
Author Contributions
Informed Consent Statement
Acknowledgments
Conflicts of Interest
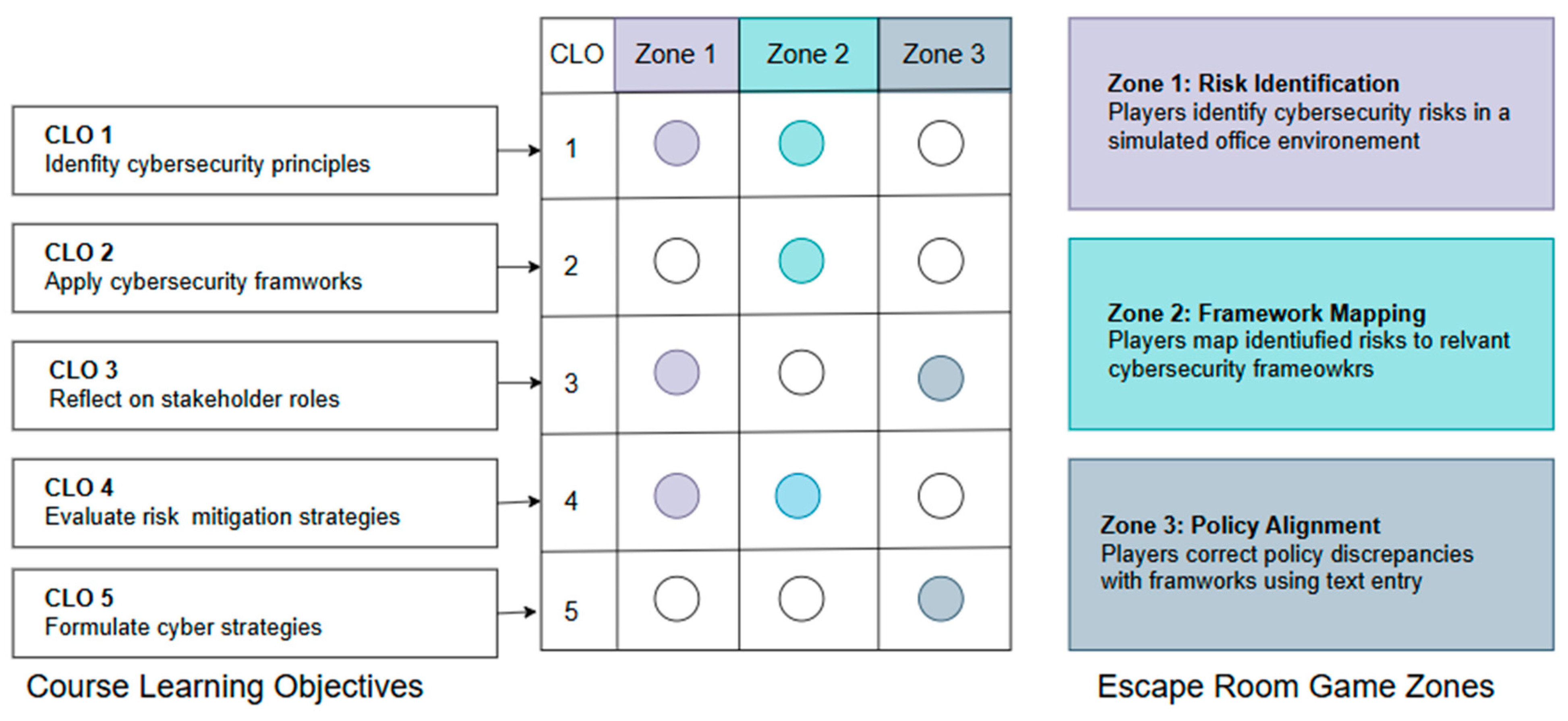
Appendix A. Learning Objectives and Game Mechanics Mapping
Appendix B. Mapping of Game Elements to Learning Theories
| Game Element | Implementation Details | Supporting Learning Theory | Theoretical Principle Applied |
| Progressive Zone Structure | Three sequential zones with increasing complexity (Risk Maze → Framework Mapping → Policy Alignment) | Constructivism | Zone of Proximal Development: Challenges begin with basic governance concepts and gradually progress to more complex problems |
| Bottom-up to Policy Maker Perspective Shift | Zone 1 (employee perspective) to Zone 3 (policy maker perspective) | Constructivism | Cognitive Conflict: Players experience both employee and policy-maker viewpoints, leading to deeper understanding through reconciling different perspectives |
| Interactive Risk Nodes | Clickable elements in Zone 1 requiring classification by impact and likelihood | Learning Mechanics-Game Mechanics model | Explicit mapping of learning objective (risk evaluation) to game mechanics (classification) |
| Framework Description Analysis | Reading and matching frameworks to risks using dropdowns in Zone 2 | Learning Mechanics-Game Mechanics model | Learning mechanics (analyzing frameworks) mapped to game mechanics (selection interface) |
| Calibrated Challenge Progression | Progressive difficulty structure from Zone 1 through Zone 3 | Flow Theory | Challenge-Skill Balance: Maintaining engagement through optimal difficulty calibration |
| Policy Correction Mechanics | Text-entry fields for revising inconsistent policies in Zone 3 | Learning Mechanics-Game Mechanics model | Learning mechanics (policy formulation) mapped to game mechanics (text entry composition) |
| Interactive Risk Nodes | Clickable elements in Zone 1 requiring classification by impact and likelihood | Learning Mechanics-Game Mechanics model | Explicit mapping of learning objective (risk evaluation) to game mechanics (classification) |
References
- Abdelghani, R., Sauzéon, H., & Oudeyer, P.-Y. (2023). Generative AI in the Classroom: Can Students Remain Active Learners? arXiv preprint arXiv:2310.03192.
- Abt, C. C. (1987). Serious games. University press of America.
- Andrew J.A. Seyderhelm and Karen L. Blackmore, P. (2023). How Hard Is It Really? Assessing Game-Task Difficulty Through Real-Time Measures of Performance and Cognitive Load. Sage Journals.
- Arias-Calderón, M., Castro, J., & Gayol, S. (2022). Serious games as a method for enhancing learning engagement: Student perception on online higher education during COVID-19. Frontiers in Psychology, 13, 889975.
- Arnab, S., Lim, T., Carvalho, M. B., Bellotti, F., De Freitas, S., Louchart, S., Suttie, N., Berta, R., & De Gloria, A. (2015). Mapping learning and game mechanics for serious games analysis. British journal of educational technology, 46(2), 391-411.
- Becker, K. (2021). What’s the difference between gamification, serious games, educational games, and game-based learning. Academia Letters, 209(2), 1-4.
- Bond, M., Zawacki-Richter, O., & Nichols, M. (2019). Revisiting five decades of educational technology research: A content and authorship analysis of the British Journal of Educational Technology. British journal of educational technology, 50(1), 12-63.
- Boyle, E. A., Hainey, T., Connolly, T. M., Gray, G., Earp, J., Ott, M., Lim, T., Ninaus, M., Ribeiro, C., & Pereira, J. (2016). An update to the systematic literature review of empirical evidence of the impacts and outcomes of computer games and serious games. Computers & Education, 94, 178-192.
- Calvano, M., Caruso, F., Curci, A., Piccinno, A., & Rossano, V. (2023). A Rapid Review on Serious Games for Cybersecurity Education: Are" Serious" and Gaming Aspects Well Balanced? IS-EUD Workshops,.
- Csikszentmihalyi, M. (1990). Flow: The psychology of optimal experience. Haper and Row.
- Efgivia, M. G., Rinanda, R. A., Hidayat, A., Maulana, I., & Budiarjo, A. (2021). Analysis of constructivism learning theory. 1st UMGESHIC International Seminar on Health, Social Science and Humanities (UMGESHIC-ISHSSH 2020),.
- Forum, W. E. (2025). Global Cybersecurity Outlook 2025. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2025.pdf.
- Fotaris, P., & Mastoras, T. (2019). Escape rooms for learning: A systematic review. Proceedings of the European Conference on Games Based Learning,.
- Gee, J. P. (2003). What video games have to teach us about learning and literacy. Computers in entertainment (CIE), 1(1), 20-20.
- Girard, C., Ecalle, J., & Magnan, A. (2013). Serious games as new educational tools: how effective are they? A meta-analysis of recent studies. Journal of computer assisted learning, 29(3), 207-219.
- Gordillo, A., & López-Fernández, D. (2024). Are educational escape rooms more effective than traditional lectures for teaching software engineering? A randomized controlled trial. IEEE Transactions on Education.
- Hein, G. E. (1991). Constructivist learning theory. Institute for Inquiry, 14.
- Hill Jr, W. A., Fanuel, M., Yuan, X., Zhang, J., & Sajad, S. (2020). A survey of serious games for cybersecurity education and training.
- Hodhod, R., Hardage, H., Abbas, S., & Aldakheel, E. A. (2023). Cyberhero: an adaptive serious game to promote cybersecurity awareness. Electronics, 12(17), 3544.
- Hoernig, S., Ilharco, A., Pereira, P. T., & Pereira, R. (2024). Generative AI and Higher education: Challenges and opportunities. Institute of Public Policy.
- ISC². (2023). Cybersecurity workforce study 2023. https://www.isc2.org/Research/2023-Cybersecurity-Workforce-Study.
- Jaffray, A., Finn, C., & Nurse, J. R. (2021). Sherlocked: A detective-themed serious game for cyber security education. International Symposium on Human Aspects of Information Security and Assurance,.
- Kulshrestha, S., Agrawal, S., Gaurav, D., Chaturvedi, M., Sharma, S., & Bose, R. (2021). Development and validation of serious games for teaching cybersecurity. Serious Games: Joint International Conference, JCSG 2021, Virtual Event, January 12–13, 2022, Proceedings 7,.
- Lim, T., Carvalho, M. B., Bellotti, F., Arnab, S., De Freitas, S., Louchart, S., Suttie, N., Berta, R., & De Gloria, A. (2015). The LM-GM framework for serious games analysis. Pittsburgh: University of Pittsburgh.
- Löffler, E., Schneider, B., Zanwar, T., & Asprion, P. M. (2021). Cysecescape 2.0—a virtual escape room to raise cybersecurity awareness. International Journal of Serious Games, 8(1), 59-70.
- Malcolm Ryan, M. M., Vedant Sansare, Paul Formosa, Deborah Richards, Michael Hitchens. (2020). Design of a Serious Game for Cybersecurity Ethics Training.
- Manuel Arias-Calderón 1, J. C., Silvina Gayol 1. (2022). Serious Games as a Method for Enhancing Learning Engagement: Student Perception on Online Higher Education During COVID-19.
- Michael, D. R., & Chen, S. L. (2005). Serious games: Games that educate, train, and inform. Muska & Lipman/Premier-Trade.
- Nieto-Escamez, F. A., & Roldán-Tapia, M. D. (2021). Gamification as online teaching strategy during COVID-19: A mini-review. Frontiers in Psychology, 12, 648552.
- Nikolic, S., Sandison, C., Haque, R., Daniel, S., Grundy, S., Belkina, M., Lyden, S., Hassan, G. M., & Neal, P. (2024). ChatGPT, Copilot, Gemini, SciSpace and Wolfram versus higher education assessments: an updated multi-institutional study of the academic integrity impacts of Generative Artificial Intelligence (GenAI) on assessment, teaching and learning in engineering. Australasian journal of engineering education, 29(2), 126-153.
- Nkongolo, M. (2024). CyberMoraba: A game-based approach enhancing cybersecurity awareness.
- Pacheco-Velázquez, E., Salinas-Navarro, D. E., & Ramírez-Montoya, M. S. (2023). Serious games and experiential learning: options for engineering education. International Journal of Serious Games, 10(3), 3-21.
- Papaioannou, T., Kokotos, S. E., & Tsohou, A. (2025). Educational escape rooms for raising information privacy competences: An empirical validation. International Journal of Information Security, 24(3), 1-24.
- Piaget, J. (1976). Piaget’s theory. Springer.
- Pramod, D. (2024). Gamification in cybersecurity education; a state of the art review and research agenda. Journal of Applied Research in Higher Education.
- Rawlinson, R. E., & Whitton, N. (2024). Escape rooms as tools for learning through failure. Electronic Journal of e-Learning, 22(4).
- Reddy, M., & Johnson, C. (2024). Games and Gamification: Can Playful Student Engagement Improve Academic Integrity? In Second Handbook of Academic Integrity (pp. 1597-1610). Springer.
- Reigeluth, C. M. (2013). Instructional-design theories and models: A new paradigm of instructional theory, Volume II. Routledge.
- Rieber, L. P. (2005). Multimedia learning in games, simulations, and microworlds. The Cambridge handbook of multimedia learning, 549-567.
- Rodríguez-Rivera, P., Rodríguez-Ferrer, J. M., & Manzano-León, A. (2025). Designing digital escape rooms with generative ai in university contexts: A qualitative study. Multimodal Technologies and Interaction, 9(3), 20.
- Rondon, S., Sassi, F. C., & Furquim de Andrade, C. R. (2013). Computer game-based and traditional learning method: a comparison regarding students’ knowledge retention. BMC medical education, 13, 1-8.
- Scherb, C., Heitz, L. B., Grimberg, F., Grieder, H., & Maurer, M. (2023). A serious game for simulating cyberattacks to teach cybersecurity. arXiv preprint arXiv:2305.03062.
- Spatafora, A., Wagemann, M., Sandoval, C., Leisenberg, M., & Vaz de Carvalho, C. (2024). An Educational Escape Room Game to Develop Cybersecurity Skills. Computers, 13(8), 205.
- Stephen Hart a, A. M. a., Federica Paci b, Vladimiro Sassone a. (2020). Riskio: A Serious Game for Cyber Security Awareness and Education.
- Sweetser, P., & Wyeth, P. (2005). GameFlow: a model for evaluating player enjoyment in games. Computers in entertainment (CIE), 3(3), 3-3.
- Veldkamp, A., Van De Grint, L., Knippels, M.-C. P., & Van Joolingen, W. R. (2020). Escape education: A systematic review on escape rooms in education. Educational Research Review, 31, 100364.
- Vygotsky, L. S. (1978). Mind in society: The development of higher psychological processes (Vol. 86). Harvard university press.
- Wu, W. H., Hsiao, H. C., Wu, P. L., Lin, C. H., & Huang, S. H. (2012). Investigating the learning-theory foundations of game-based learning: a meta-analysis. Journal of computer assisted learning, 28(3), 265-279.
- Zawacki-Richter, O., Marín, V. I., Bond, M., & Gouverneur, F. (2019). Systematic review of research on artificial intelligence applications in higher education–where are the educators? International journal of educational technology in higher education, 16(1), 1-27.
- Zhonggen, Y. (2019). A meta-analysis of use of serious games in education over a decade. International Journal of Computer Games Technology, 2019(1), 4797032.
| Study | Target Audience | Learning Objectives | Game Format | Theoretical Basis | Technology / Platform | Assessment & Feedback Mechanism | Scalability & Accessibility | Key Outcomes | Limitations |
| SherLOCKED (Jaffray et al., 2021) | Undergraduate students | Consolidate foundational security concepts (CIA triad, threats, risk management) | 2D top-down, detective-themed puzzle adventure | Built on the serious-games definition and core gamification principles | Web-based HTML5 interface with simple graphics | Completion-based tracking, post-game debrief discussions | Limited to small group settings | Effective, attractive, and fun; high engagement with lecture content | Pilot only; no formal skill-transfer or long-term retention data |
| CyberHero (Hodhod et al., 2023) | Corporate employees / general workforce | Improve phishing, social-engineering, and password-security awareness | Mobile & web-based adaptive serious game with storytelling | Draws on major learning theories (behaviorism, cognitivism, humanism, connectivism, constructivism) and gamification | Cross-platform (iOS/Android/browser) with adaptive difficulty | Real-time personalized in-game feedback and recommendations | Highly scalable for corporate training programs | 79% learned new things; 84% were engaged by story; 68% had fun; 84% would recommend | Behavioral change and long-term retention were not evaluated |
| CySecEscape 2.0 (Löffler et al., 2021) | SME employees & students | Raise cybersecurity awareness; practice incident-response and risk-identification | Fully virtual escape room with team collaboration | Not explicitly grounded in a learning theory (uses a design-science research framework) | Web-deployed Unity3D prototype (no VR headset required) | Moderator-observed play, performance logs, post-game surveys, and interviews | Scalable but requires setup for VR elements | Virtual format retained immersion; intuitive interface post-refinement | Confusion over interactivity; demographics and sample sizes unclear |
| Privacy-Competence Escape Room (Papaioannou et al., 2025) | Adult Internet users | Develop five privacy competencies (risk perception, data control, etc.) | 2D browser-based digital escape room | Competence-based learning aligned to digital-literacy frameworks | HTML5/JavaScript web interface | Pre-/post-test competence surveys; structured group debriefs | Plans for ongoing improvement with 3D levels | Significant gains in all five competencies (p < .05) | No long-term follow-up; no behavioral metrics beyond self-report |
| Prescott & Krueger (Malcolm Ryan, 2020) |
University-level cybersecurity (or other IT) students | Recognize and apply five cybersecurity ethics principles (beneficence, non-maleficence, autonomy, justice, explicability); ethical focus | Branching narrative with workplace simulation; email and chat interfaces; resource management system | Four Component Model (4CM) of moral intelligence; Morality Play model for serious moral game design | Digital game with simulated workplace interfaces (specific development platform not mentioned) | Reflection reports after decisions; NPC morale system; AI ethics advisor (EthBot) | Limited information in paper; described as classroom-based with no specific scalability features mentioned | Evaluation still underway at time of publication; authors found 4CM useful for designing learning outcomes and game mechanics | Limited cybersecurity system simulation; heavily scripted interactions; difficulty implementing the "moral toy" concept from Morality Play model |
| UNSW Cyber Escape Room (This work) | University students (cybersecurity, business, governance) | Apply risk analysis, align ISO 27001/NIST CSF/GDPR frameworks, and draft policy | Three-zone virtual escape room with sequential, scenario-based challenges | Constructivism; Experiential Learning (Kolb); Flow Theory; LM–GM mapping | Unity3D, web-deployed, standard-hardware remote access | Embedded puzzles, decision evaluations, and performance logging | Designed for remote access, scalable for larger class sizes | 5/5 engagement rating by 71% rated; 57% “Oh definitely” on interest; positive qualitative feedback | No control group; real-world skill transfer not yet measured; single-institution sample |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




