Submitted:
08 December 2025
Posted:
11 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Background and Motivation
- Complex Cross-Service Auditing: Reconstructing a complete, reliable audit trail for a business process that traverses multiple, often ephemeral, microservices is non-trivial.
- Slow Policy Adaptation: Traditional methods for updating compliance rules are too slow for the rapid deployment cycles common in MSA environments.
- Impedance Mismatch: Centralized, heavyweight compliance tools create an impedance mismatch with the lightweight, decentralized paradigm of cloud-native microservices.
1.2. Research Objectives & Approach
- Problem Identification and Motivation (Section 1.1), where we identify the significant challenges traditional BPC approaches face in modern MSA/Cloud settings and motivates the necessity for a new, specialized framework.
- Definition of Objectives for a Solution: Stemming from the identified problem and the acknowledged literature gap concerning established BPC practices in MSA/Cloud, the precise objectives for the BPC4MSA framework were defined through a systematic requirements derivation process. This process, detailed in Section 3, integrates First-Principles Analysis and Constructed Scenario Analysis [10], resulting in a synthesized set of functional and non-functional requirements that constitute the explicit objectives for the artifact.
- Evaluation (Section 5 & 6), which presents a dual-method evaluation of the artifacts. First, in Sections 5, we conduct a Design Evaluation, where the conceptual framework artifact is assessed. Following Polyvyanyy et al. [11], we use a Systematic Literature Review as the method to rigorously validate the framework’s conceptual novelty and its completeness in addressing the identified research gaps. Second, in Section 6, we conduct a Prototype Evaluation, where the instantiated prototype artifact is assessed via a preliminary, non-functional empirical study.
- Communication: This paper serves as the primary vehicle for communicating the entire research process, including the problem context, methodology, artifact design, and findings from both the design and empirical evaluations (DSRM Guideline 7: Communication of Research). Sections 7 (Discussion) and 8 (Conclusion) fulfill this, summarizing findings and outlining future work.
1.3. Contributions
1.4. Paper Structure
2. Background and Related Work
2.1. Business Process Management
2.2. Business Process Compliance
2.3. Microservices Architecture
2.4. Cloud Technologies
2.5. Related Work
2.5.1. Stream 1: Foundational Frameworks and Proactive Assurance
2.5.2. Stream 2: Runtime Monitoring, Adaptation, and Lifecycle Management
2.5.3. Stream 3: Decentralization, Operational Reality, and Next-Generation Challenges
2.6. Formal Foundations for BPC in MSA/Cloud
- is the case identifier, linking the event to a specific process instance.
- is the activity identifier (e.g., ‘Approve Loan’).
- is the timestamp.
- is a partial function representing the data payload. In an MSA/Cloud context, this payload is critical for traceability and typically contains attributes like serviceID (identifying the microservice source) and correlationID (linking distributed events).
- (all events belong to the same case). A trace is considered “distributed” as its constituent events may originate from numerous independent services
- (events are ordered by timestamp).
- is a set of nodes (model elements).
- is a set of control-flow edges.
- is a partial labeling function mapping nodes to activity identifiers.
- is the set of start nodes.
- is the set of end nodes.
3. BPC4MSA Requirements Elicitation and Definition
3.1. Overall Research Methodology Context
3.2. Requirements Elicitation Context and Approach
3.3. Derivation via First-Principles Analysis
3.3.1. Identify Core Characteristics
3.3.2. Analyze Interactions and Conflicts
- The difficulty of managing distributed data consistently across independent microservice databases versus BPC’s need for strong data governance (e.g., privacy, lineage) [48]
- The complexity of monitoring and verifying compliance for complex, potentially asynchronous inter-service communication patterns [47].
- The friction between MSA’s typical lack of centralized control and the need to enforce consistent compliance standards across independently developed services [52].
- The increased overall system complexity inherent in MSA impacting the ability to achieve holistic compliance understanding and verification [14].
- Deficiencies in observability and monitoring capabilities when trying to capture sufficient data for compliance verification across distributed services [47].
- Problems in defining clear boundaries and responsibilities for compliance in processes spanning multiple services or teams, especially in collaborative settings [53].
- The difficulty of maintaining compliance amidst the constantly evolving landscape of frequent microservice updates [19].
- The challenge of formalizing high-level compliance requirements into specific, verifiable rules at the microservice level [14].
- The potential for significant performance overhead when implementing runtime compliance checks [54].
3.3.3. Deduce Necessary Capabilities
- To manage data governance across distributed data management complexities [48], capabilities for policy definition applicable to data handling and mechanisms to trace data flow across services were identified as necessary.
- To ensure traceability despite complex inter-service communication patterns and potential observability gaps [47], the capability for robust context propagation and comprehensive event logging across service boundaries was deemed fundamental.
- To counter the challenge of cloud ephemerality impacting audit trail continuity (related to the evolving landscape discussed by [19], capabilities for decoupled, persistent, and potentially immutable logging services were identified as critical.
- To mitigate performance overhead concerns, the analysis suggested that compliance checking mechanisms should ideally be lightweight, distributable, and potentially operate asynchronously where feasible [56].
- To address the difficulty in formalizing requirements and managing complexity, capabilities supporting expressive yet processable policy languages, potentially leveraging semantic representations, were seen as necessary [14].
- To manage the evolving landscape and issues with defining boundaries, capabilities related to dynamic policy updates and clear association of rules with services/processes were deduced [19].
3.4. Derivation via Constructed Scenario Analysis
3.4.1. Scenario Design
3.4.2. Scenario Analysis
3.5. Synthesized BPC4MSA Requirements
3.5.1. Overview
3.5.2. Core Functional Capabilities
3.5.3. Essential Non-Functional Qualities
3.5.4. Summary of Core Objectives
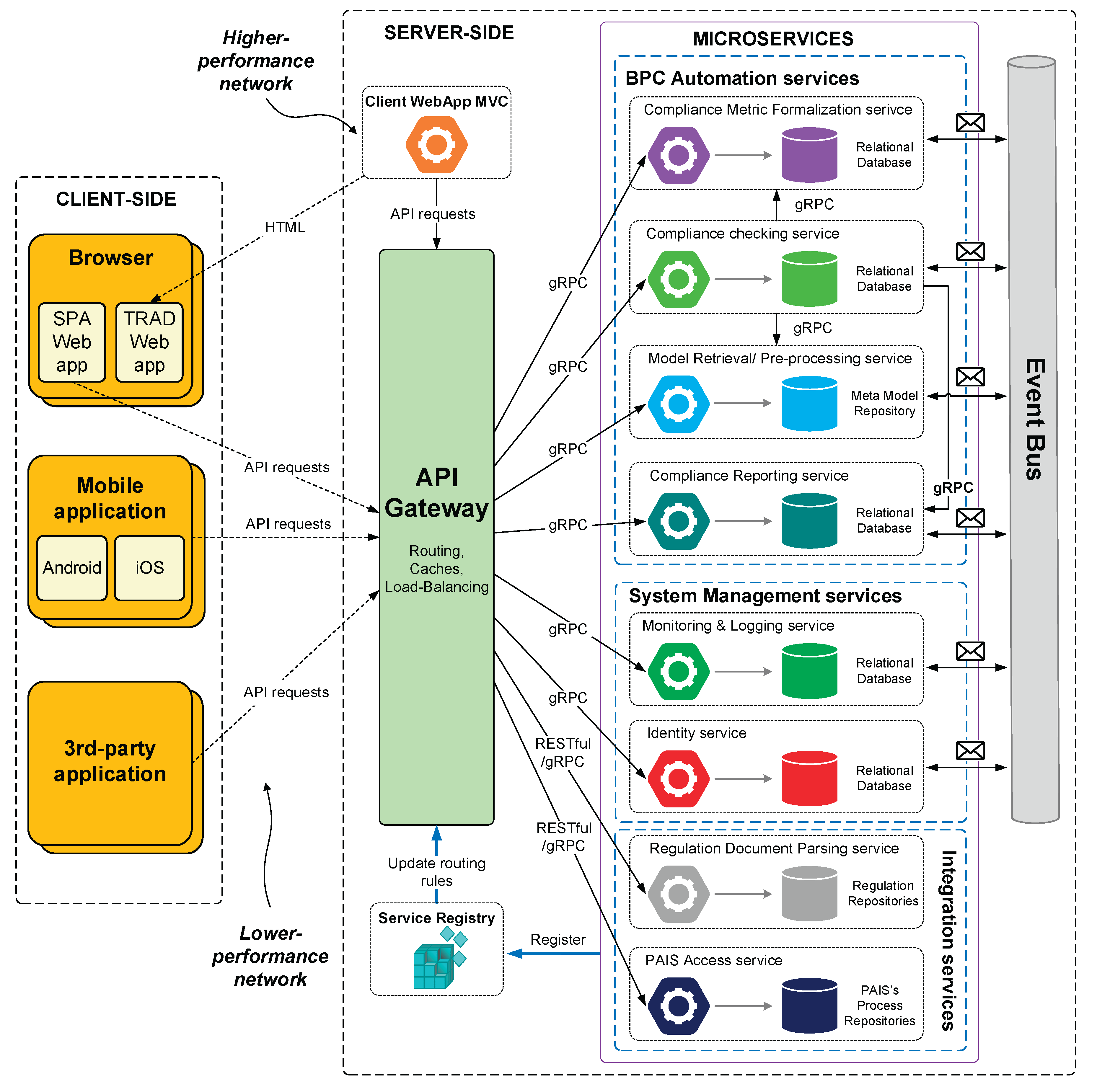
4. The BPC4MSA Framework Design
4.1. Overview and Design Principles
- Decentralization: Aligning with MSA principles, core compliance functionalities are decomposed into independent microservices.
- Event-Driven Communication: An event bus facilitates asynchronous communication and loose coupling between services, enhancing resilience and scalability.
- Separation of Concerns: Services are grouped logically based on their primary function (e.g., BPC Automation, System Management, Integration).
- API-Centricity: An API Gateway manages external communication, providing a unified interface for various client applications.
- Extensibility: The architecture is designed to accommodate future requirements, including potential integration with advanced AI capabilities.
4.2. Architecture and Components
- is the set of BPC Automation services, which instantiate the core compliance functions ().
- is the set of System Management services, which instantiate the operational functions ().
- is the set of Integration services, which provide access to external artifacts (, ).
- is the Event Bus, the mechanism for handling the event stream ().
- is the API Gateway, the unified interface to the framework’s functions.
- The components of this framework are detailed below and illustrated in Figure 1.
4.2.1. Client-Side Applications
- Web Applications (SPA/TRAD): Providing interfaces for compliance officers, auditors, business users, and potentially developers to define policies, monitor status, view reports, and manage violations.
- Mobile Applications: Offering potentially optimized views and interactions for on-the-go monitoring or approvals.
- Third-Party Applications: Allowing external systems (e.g., Governance, Risk, and Compliance (GRC) platforms, external auditing tools) to integrate with BPC4MSA via public APIs.
4.2.2. Infrastructure Components:
- API Gateway: Acts as the single entry point for all client requests. It handles routing, load balancing, caching, and potentially initial authentication/authorization, abstracting the underlying microservice structure from clients.
- Service Registry: Enables dynamic service discovery, allowing services and the API gateway to locate instances of other services in the potentially dynamic cloud environment. Services register themselves upon startup.
- Event Bus: Facilitates asynchronous, publish-subscribe communication between microservices. This decouples services, allowing them to react to events (e.g., policy updates, detected violations, process milestones) without direct dependencies, enhancing resilience and scalability.
4.2.3. Microservice Clusters
- Compliance Metric Formalization Service: (Instantiates ) Responsible for translating compliance requirements (potentially received from the Regulation Document Parsing service or user input via client apps) into the formal representation used by the checking engine (e.g., BhR, PCL). This service could potentially interface with AI models in the future to assist in translating natural language policies (related to C1).
- Model Retrieval/Pre-processing Service: (Retrieves ) Fetches business process models and related metadata from external sources (via the PAIS Access service) and prepares them for compliance analysis (related to C1, C5).
- Compliance Checking Service: (Instantiates ) The core engine that performs compliance verification. It takes formalized rules/metrics and process models/traces as input and evaluates compliance, potentially supporting both design-time checks (C2) and runtime/post-execution analysis (C3, C4) based on events from the Event Bus or data from the Monitoring & Logging service.
- Compliance Reporting Service: (Instantiates ) Aggregates compliance results, generates reports, and provides data for dashboards presented via client applications. It could potentially leverage AI in the future for generating natural language summaries or explanations of compliance status or violations (related to C4).
- Monitoring & Logging Service: (Instantiates ) Collects operational logs and metrics from all microservices for health monitoring and performance analysis. Crucially, it also aggregates and stores the compliance audit trail data (events, check results) generated by other services, potentially via the Event Bus, ensuring data is available for auditing (related to C3, C4).
- Identity Service: (Instantiates ) Manages authentication and authorization for users and potentially services interacting with the framework, ensuring secure access control (related to NQ2).
- Regulation Document Parsing Service: (Retrieves ) Interfaces with external repositories or tools to retrieve and potentially parse regulatory documents or external policy sources, feeding information to the Formalization service (related to C1, C5).
- PAIS Access Service: (Retrieves or from external systems) Provides a dedicated interface for interacting with various Process-Aware Information Systems (PAIS) to retrieve process models and execution data (related to C5).
4.3. Addressing Requirements
4.3.1. Mapping Functional Capabilities
4.3.2. Addressing Non-Functional Qualities
4.4. Technology Stack
- Orchestration: Kubernetes (for deployment, scaling (NFR1), resilience (NFR3)).
- Event Bus: Apache Kafka or RabbitMQ (for scalable (NFR1), resilient (NFR3) asynchronous communication).
- API Gateway: Kong, Traefik, or cloud provider gateways (for managing external access, routing).
- Service Registry: Consul, etcd, or Kubernetes-native discovery (for dynamic discovery).
- Databases: PostgreSQL (for relational data, e.g., Identity, Reporting), Cassandra/MongoDB (for high-volume logs/events, supporting NQ1), Graph Database (potentially for policy/model relationships supporting C1/FR11).
- Monitoring/Logging: Elasticsearch/Fluentd/Kibana (EFK) stack or Prometheus/Grafana (for observability, supporting C4, NQ3).
- Service Implementation: Go, Java (Spring Boot), Python (FastAPI) - chosen based on team expertise and specific service needs (contributing to NQ3/NFR7).
- Communication: gRPC (for efficient internal synchronous calls), RESTful APIs (for external interaction).
4.5. Deployment Considerations
- Deployment Models: Can be deployed on managed Kubernetes services (e.g., EKS, GKE, AKS), self-managed Kubernetes clusters, or potentially adapted for serverless platforms where applicable. Hybrid deployments (part cloud, part on-premise) are feasible but increase complexity.
- Scalability & Resilience: Achieved via Kubernetes auto-scaling based on resource utilization (CPU, memory) or custom metrics (e.g., queue length for the Event Bus), fulfilling NQ1/NFR1. Redundancy across multiple availability zones addresses NQ2/NFR3.
- Security: Relies on cloud provider security features (network policies, IAM), secure configurations (e.g., secrets management), authentication/authorization via the Identity Service, and secure communication protocols (TLS), addressing NQ2/NFR4. Data encryption at rest and in transit is essential.
- Data Management: Strategies for managing distributed data persistence, backups, and potential cross-region replication need careful consideration based on specific compliance requirements (e.g., GDPR data residency).
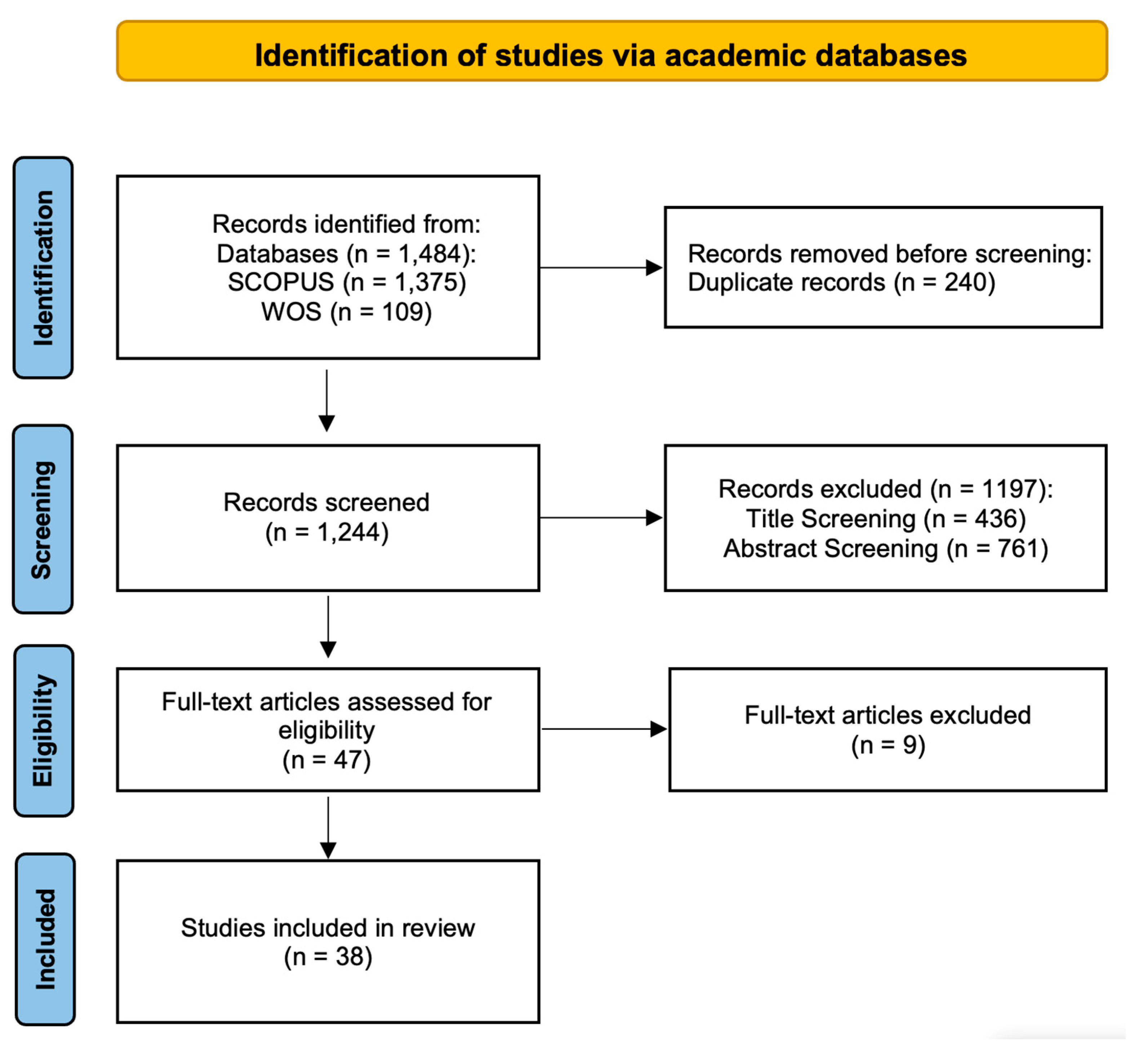
5. Design Evaluation: Systematic Literature Review
5.1. Methodology
5.2. Research Questions (RQs) for SLR
- RQ-SE1: What existing frameworks, architectures, methods, or tools specifically address BPC (including aspects like policy management, monitoring, auditing, enforcement) within MSA, Cloud-native, or closely related Cloud/SOA contexts?
- RQ-SE2: How do these existing approaches address the core functional capabilities (C1-C5) and non-functional qualities (NQ1-NQ3) identified as requirements for BPC4MSA in Section 3.5?
- RQ-SE3: What are the primary limitations or gaps in the current state-of-the-art concerning BPC for MSA/Cloud environments, based on the reviewed literature?
- RQ-SE4: How does the proposed design of BPC4MSA compare to existing approaches, and what are its potential novel contributions towards addressing the identified gaps (RQ-SE3) and requirements (RQ-SE2)?
5.3. Search Strategy
5.4. Study Selection and Screening Process
5.5. Data Extraction
5.6. Synthesis Method
5.7. Literature Analysis & Framework Positioning
- Core Capabilities are Widely Addressed: A vast majority of the analyzed literature addresses the core tenets of compliance management. Policy Lifecycle Management (C1) is considered in 89% of papers (34 out of 38), and Adaptability (NQ3) is a key concern in 89% (34 out of 38), indicating these are foundational research topics.
- Proactive and Reactive Measures are Prevalent: Both “shift-left” and “shift-right” approaches are very common. Proactive Compliance Assurance (C2) is addressed by 84% of papers (32 out of 38), and an equal percentage, 84% (32 out of 38), address Compliance Auditing & Analysis (C4).
- Runtime Monitoring is a key, but not universal, Focus: While still a majority concern, Runtime Monitoring & Enforcement (C3) is the least frequently addressed of the core capabilities, appearing in 63% of papers (24 out of 38). A qualitative look confirms the finding from GAP-3: most of these works focus on monitoring and detection, with true automated enforcement remaining rare.
- The Proactive vs. Reactive Divide: There is a clear pattern of mutual exclusivity between papers strong in Proactive Assurance (C2) and those strong in Compliance Auditing & Analysis (C4). Papers proposing formal, design-time verification methods [16,36,37] rarely include sophisticated post-mortem analysis, and vice-versa for papers focused on BI or process mining [16,68]. This further supports the “Broken Feedback Loop” (GAP-2).
- The Rise of Holistic Frameworks: A noticeable trend in later years (post-2015) is the emergence of more comprehensive frameworks that attempt to address three or more of the core capabilities simultaneously [32,39,43,44,55,69,70]. This indicates a growing maturity in the field and a recognition that a holistic approach is necessary.
- Architectural Drivers: The architectural approach is a strong predictor of focus. Papers based on formal methods (Petri nets, model checking) are almost exclusively focused on C2. Papers based on CEP and event-driven architectures are focused on C3. Papers based on data warehousing and BI are focused on C4. This specialization contributes to the siloing of research and the identified gaps.
- GAP-1: The “Last Mile” Problem: The process of translating ambiguous legal text into precise, machine-readable rules remains a largely manual, error-prone bottleneck, limiting the agility of the entire compliance lifecycle.
- GAP-2: The Broken Feedback Loop: There is a clear disconnect between proactive design-time tools, reactive runtime monitoring systems, and post-mortem analysis platforms, with no automated mechanism to feed insights back into design-time models.
- GAP-3: Weak or Absent Automated Enforcement: The vast majority of research focuses on monitoring and detection. True automated enforcement—actively preventing or correcting violations at runtime without human intervention—is rarely addressed.
- GAP-4: Integrating Internal (Architectural) and External (Regulatory) Compliance: The literature largely treats architectural integrity and regulatory compliance as separate problems, lacking a holistic framework that manages both simultaneously.
- GAP-5: Scalability and Practicality of Advanced Solutions: Many proposed solutions based on formal methods, semantic ontologies, or blockchain face significant practical hurdles, including high modeling overhead and performance bottlenecks.
| ID | Citation | Architectural Approach | C1 | C2 | C3 | C4 | C5 | NQ1 | NQ2 | NQ3 |
|---|---|---|---|---|---|---|---|---|---|---|
| 1 | [71] | Remote auditing, trusted computing, secure logging | - | +/- | +/- | + | - | - | + | - |
| 2 | [36] | Petri nets, formal patterns | +/- | + | - | +/- | - | +/- | + | - |
| 3 | [31] | Blockchain, smart contracts | +/- | +/- | + | + | +/- | +/- | + | +/- |
| 4 | [20] | Service-based, Complex Event Processing (CEP) | + | +/- | + | +/- | + | + | +/- | + |
| 5 | [22] | Self-monitoring, process rewriting | +/- | +/- | + | +/- | +/- | +/- | + | + |
| 6 | [38] | SOA, CEP, DSLs | + | + | + | + | + | + | + | + |
| 7 | [37] | Cloud-based service, model-checking | +/- | + | - | + | + | + | + | + |
| 8 | [32] | Cloud service broker, legal/QoS framework | +/- | +/- | + | +/- | +/- | +/- | +/- | + |
| 9 | [69] | Cloud service broker, autonomic computing (MAPE-K) | + | + | + | +/- | +/- | +/- | +/- | + |
| 10 | [25] | Cloud-based service, model-checking | +/- | + | - | - | + | + | +/- | + |
| 11 | [14] | Semantically-enabled, ontologies, COaaS | + | + | + | + | +/- | +/- | +/- | + |
| 12 | [44] | Model-Driven Architecture (MDA), Compliance Descriptors | + | + | + | +/- | + | +/- | + | + |
| 13 | [45] | Configuration management (Chef), experience report | +/- | - | + | +/- | +/- | + | + | +/- |
| 14 | [19] | Adaptive process (MAPE-K loop) | + | +/- | + | +/- | +/- | +/- | + | + |
| 15 | [72] | Goal-oriented Requirement Language (GRL), MCDA | +/- | +/- | - | - | - | - | +/- | - |
| 16 | [41] | ISC evolution, RETE algorithm | + | +/- | + | - | - | +/- | +/- | + |
| 17 | [23] | Variability Descriptors, Compliance Descriptors | + | + | + | +/- | + | +/- | + | + |
| 18 | [43] | Model-Driven Architecture (MDA), Compliance Descriptors | + | + | + | +/- | + | +/- | + | + |
| 19 | [16] | Process Mining, XES, economic assessment | - | - | - | + | +/- | +/- | +/- | +/- |
| 20 | [73] | Timed Automata, TCTL, UPPAAL model checker | +/- | + | - | - | - | - | + | - |
| 21 | [51] | Model-based, SPIN model checker, LTL | +/- | + | + | +/- | - | - | +/- | +/- |
| 22 | [74] | DSL, Model-Driven Development (MDD), CEP | +/- | - | + | - | +/- | +/- | +/- | + |
| 23 | [18] | User-centered, SPIN model checker, extended patterns | + | + | + | +/- | - | +/- | + | + |
| 24 | [21] | SOA, knowledge-based, BPCL | + | +/- | + | + | + | +/- | + | +/- |
| 25 | [55] | SOA, Deming cycle, KCIs, data warehouse | +/- | + | +/- | + | +/- | +/- | +/- | + |
| 26 | [75] | Integrated compliance graph, decision support | +/- | + | - | +/- | +/- | +/- | + | + |
| 27 | [42] | Integrated graph, interaction analysis | +/- | + | - | +/- | +/- | +/- | + | + |
| 28 | [76] | Integrated graph, process adaptation tool (BCIT) | +/- | + | - | +/- | +/- | +/- | + | + |
| 29 | [70] | State-aware, ROP ontology, Drools | +/- | - | + | +/- | +/- | +/- | + | + |
| 30 | [77] | MTL, rule elicitation, graphical representation | + | + | - | - | - | +/- | + | +/- |
| 31 | [78] | Semantic (OWL/SWRL), ontologies, Drools | + | +/- | - | + | + | +/- | + | + |
| 32 | [39] | End-to-end framework, VbMF, DSLs, CEP | +/- | + | + | + | + | +/- | - | + |
| 33 | [66] | DevSecOps, security checklist methodology | + | + | - | +/- | + | +/- | + | + |
| 34 | [40] | TOSCA, XML nets, CEP, anti-patterns | +/- | + | + | +/- | +/- | +/- | + | +/- |
| 35 | [79] | TOSCA, XML nets, CEP, anti-patterns | +/- | + | + | + | + | + | + | +/- |
| 36 | [46] | Economic assessment, Workflow Patterns, Cost-Benefit Analysis | - | +/- | - | +/- | - | +/- | +/- | +/- |
| 37 | [68] | Business Intelligence, Data Warehouse, OLAP | - | - | - | + | +/- | +/- | + | +/- |
| 38 | [50] | Adaptive SOA, AOP, CEP | +/- | - | + | +/- | +/- | - | +/- | + |
5.8. SLR Summary and Novelty Confirmation
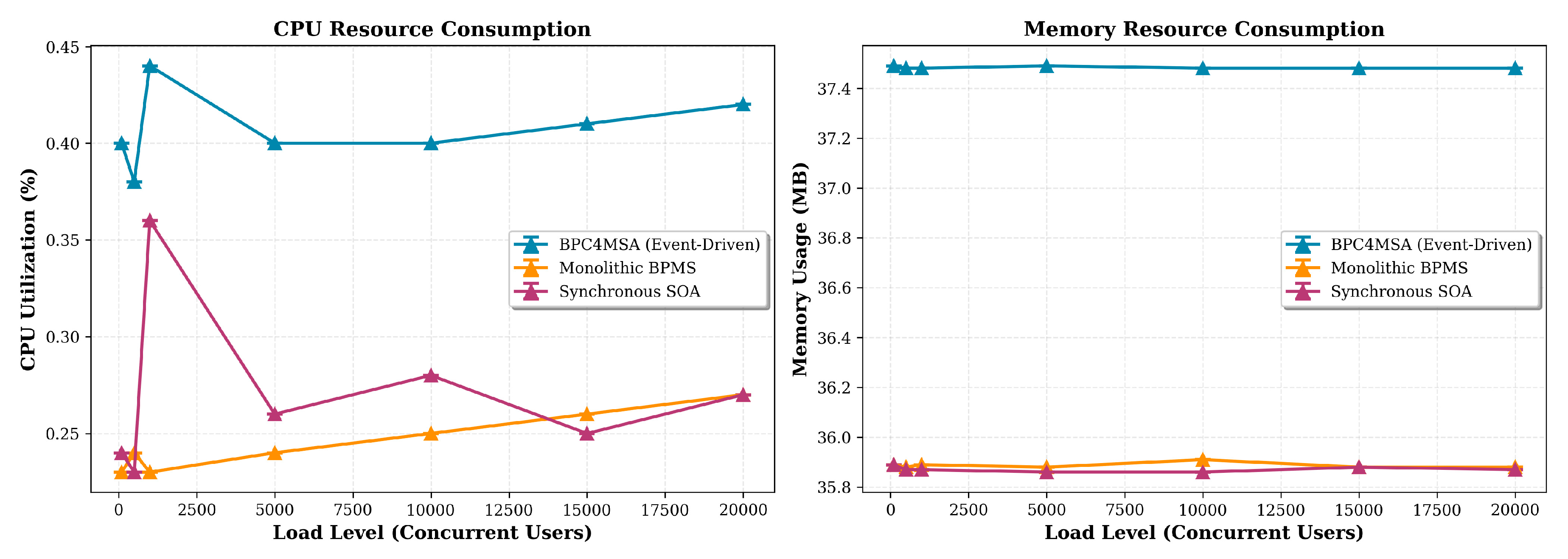
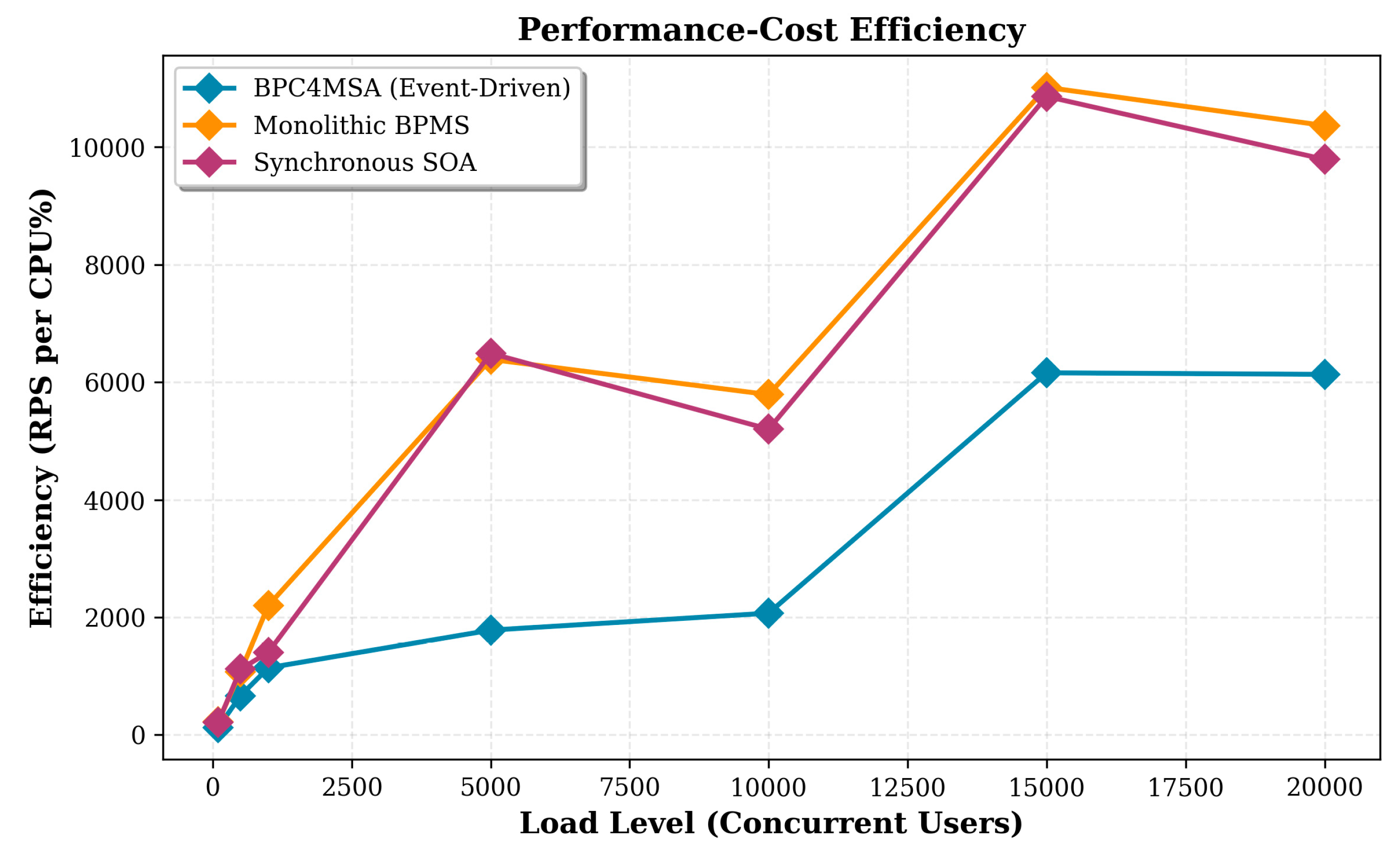
6. BPC4MSA Prototype: Implementation and Preliminary Evaluation
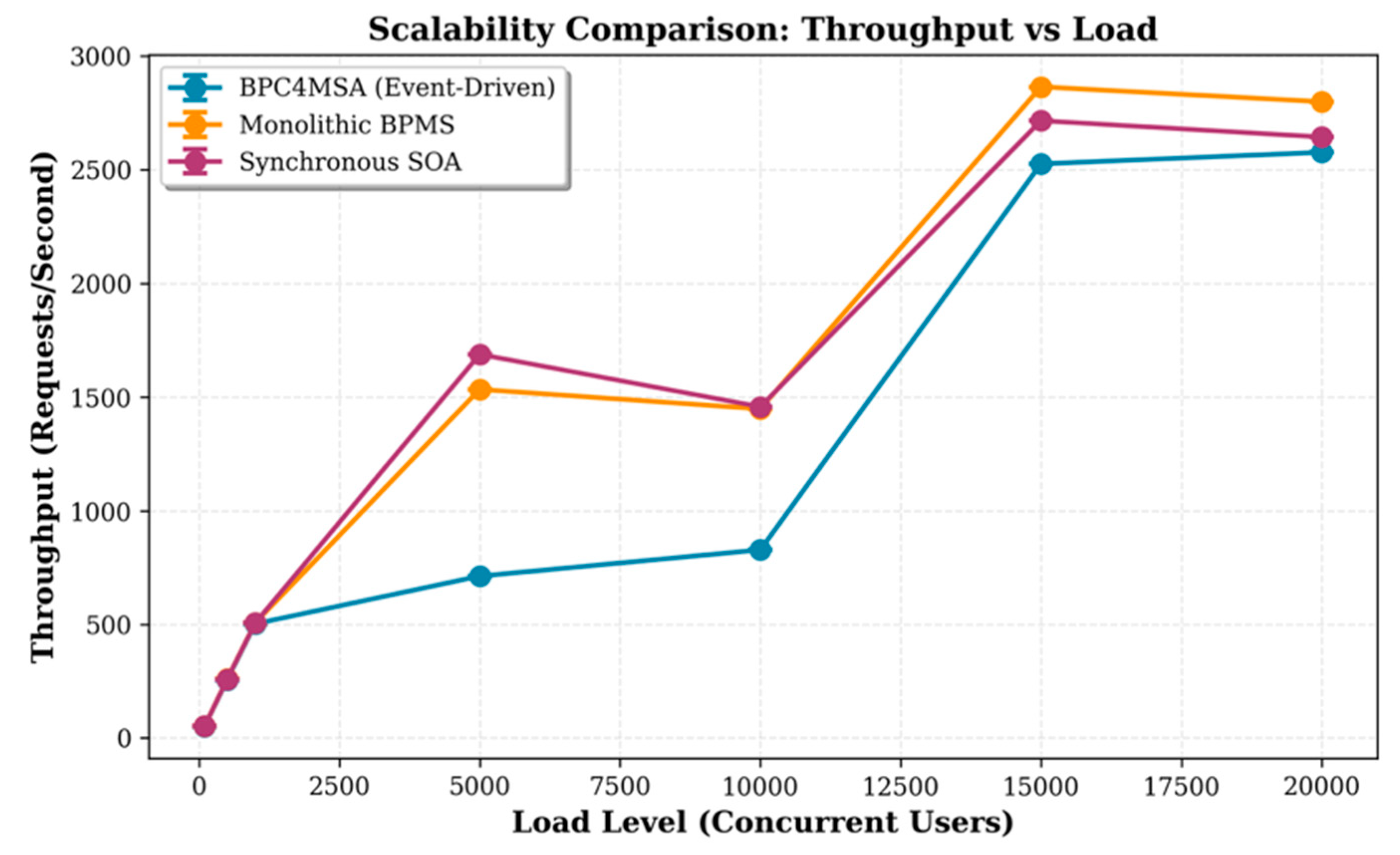
- RQ-AE1: How do the architectures compare in terms of performance and resource efficiency under increasing load? (Evaluates NQ1)
- RQ-AE2: How do the architectures differ in their stability and resilience when pushed to their performance limits? (Evaluates NQ1, NQ3)
6.1. Experimental Setup
- BPC4MSA (Event-Driven): The full prototype implementation of our proposed framework, featuring asynchronous, event-driven communication via a message bus (Kafka) and decoupled microservices for business logic, compliance checking, and auditing.
- Synchronous SOA: A baseline architecture simulating a traditional Service-Oriented Architecture. In this version, the compliance check is a synchronous, blocking HTTP call that must complete before the business process can proceed.
- Monolithic: A baseline representing a traditional all-in-one application. All business logic, compliance checking, and data persistence are handled within a single, tightly-coupled service.
6.2. Experiment Procedures and Data Collection
- Performance Metrics: Throughput (requests per second) and response latency (average and 95th percentile) were captured by the Locust framework.
- Resource Utilization Metrics: The docker stats command was executed concurrently to collect time-series data on CPU and Memory usage for each container.
6.3. Preliminary Empirical Results
6.3.1. The Efficiency Champion: Validating the Cost of Decoupling
6.3.2. Comparative Analysis of System Stability
7. Discussion
7.1. Synthesis of Findings
7.2. Implications of the Conceptual Framework
7.3. Feasibility and Implementation Challenges of the Runtime Pattern
7.4. Limitations and Future Work
8. Conclusion
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Dumas M, La Rosa M, Mendling J, Reijers HA (2018) Fundamentals of Business Process Management. Springer Berlin Heidelberg, Berlin, Heidelberg.
- El Kharbili M, Alves De Medeiros AK, Stein S, Van Der Aalst WMP (2008) Business process compliance checking: Current state and future challenges. In: Lecture Notes in Informatics (LNI), Proceedings - Series of the Gesellschaft fur Informatik (GI). pp 107–113.
- Governatori G (2005) Representing Business Contracts In RuleML. Int J Coop Inf Syst 14:181–216. [CrossRef]
- Governatori G, Sadiq S (2008) The Journey to Business Process Compliance. Handbook of Research on Business Process Modeling 426–454. [CrossRef]
- Dragoni N, Giallorenzo S, Lafuente AL, Mazzara M, Montesi F, Mustafin R, Safina L (2017) Microservices: Yesterday, Today, and Tomorrow. In: Present and Ulterior Software Engineering. Springer International Publishing, Cham, pp 195–216.
- Mustapha AM, Arogundade O ’Tale, Abayomi-Alli A, Adeniran OJ, Adesemowo K, Alonge CY (2020) A Systematic Method for Extracting and Analyzing Cloud-Based Compliance Requirements. In: 2020 International Conference in Mathematics, Computer Engineering and Computer Science (ICMCECS). IEEE, pp 1–7.
- Yimam D, Fernandez EB (2016) A survey of compliance issues in cloud computing. Journal of Internet Services and Applications 7:5. [CrossRef]
- Hevner AR, March ST, Park J, Ram S (2004) Design Science in Information Systems Research. MIS Quarterly 28:75. [CrossRef]
- Peffers K, Tuunanen T, Rothenberger MA, Chatterjee S (2007) A Design Science Research Methodology for Information Systems Research. Journal of Management Information Systems 24:45–77. [CrossRef]
- Sutcliffe A (2003) Scenario-based requirements engineering. In: Proceedings. 11th IEEE International Requirements Engineering Conference, 2003. pp 320–329.
- Polyvyanyy A, Ouyang C, Barros A, van der Aalst WMP (2017) Process querying: Enabling business intelligence through query-based process analytics. Decis Support Syst 100:41–56. [CrossRef]
- Hashmi M, Governatori G, Lam HP, Wynn MT (2018) Are we done with business process compliance: state of the art and challenges ahead. Knowl Inf Syst 57:79–133. [CrossRef]
- Viriyasitavat W, Da Xu L, Dhiman G, Bi Z (2023) Blockchain-as-a-Service for Business Process Management: Survey and Challenges. IEEE Trans Serv Comput 16:2299–2314. [CrossRef]
- Elgammal A, Turetken O (2015) Lifecycle Business Process Compliance Management: A Semantically-Enabled Framework. In: 2015 International Conference on Cloud Computing, ICCC 2015. IEEE, pp 1–8.
- Sackmann S, Kuehnel S, Seyffarth T (2018) Using Business Process Compliance Approaches for Compliance Management with Regard to Digitization: Evidence from a Systematic Literature Review. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). Springer Verlag, pp 409–425.
- Kuehnel S, Sackmann S, Damarowsky J, Boehmer M (2022) EconBPC: A Tool for Activity-based Monetary Assessment and Visualization of Security and Compliance Measures in Business Processes.
- Fellmann M, Zasada A (2014) State-of-the-art of business process compliance approaches: A Survey. ECIS 2014 Proceedings - 22nd European Conference on Information Systems 1–17.
- Mustapha AM, Arogundade O ‘Tale, Abayomi-Alli A, Adesemowo AK, Adeniran OJ (2024) An improved cloud-based business process compliance management system using a user-centered approach. International Journal of System Assurance Engineering and Management 15:5111–5138. [CrossRef]
- García-Galán J, Pasquale L, Grispos G, Nuseibeh B (2016) Towards adaptive compliance. In: Proceedings of the 11th International Symposium on Software Engineering for Adaptive and Self-Managing Systems. ACM, New York, NY, USA, pp 108–114.
- Awad A, Sakr S, Elgammal A (2015) Compliance Monitoring as a Service: Requirements, Architecture and Implementation. In: 2015 International Conference on Cloud Computing (ICCC). IEEE, pp 1–7.
- Orriens B, Heuvel WJ V.D., Papazoglou M (2008) On the risk management and auditing of SOA based business processes. In: Communications in Computer and Information Science. pp 124–138.
- Barnawi A, Awad A, Elgammal A, El Shawi R, Almalaise A, Sakr S (2015) Runtime self-monitoring approach of business process compliance in cloud environments. Cluster Comput 18:1503–1526. [CrossRef]
- Koetter F, Kochanowski M, Renner T, Fehling C, Leymann F (2013) Unifying Compliance Management in Adaptive Environments through Variability Descriptors (Short Paper). In: 2013 IEEE 6th International Conference on Service-Oriented Computing and Applications. IEEE, pp 214–219.
- Mustapha AM, Arogundade OT, Misra S, Damasevicius R, Maskeliunas R (2020) A systematic literature review on compliance requirements management of business processes. International Journal of System Assurance Engineering and Management 11:561–576. [CrossRef]
- Compagna L, Guilleminot P, Brucker AD (2013) Business Process Compliance via Security Validation as a Service. In: 2013 IEEE Sixth International Conference on Software Testing, Verification and Validation. IEEE, pp 455–462.
- Kratzke N, Quint PC (2017) Understanding cloud-native applications after 10 years of cloud computing - A systematic mapping study. Journal of Systems and Software 126:1–16. [CrossRef]
- Richardson C (2018) Microservices patterns: with examples in Java. Simon and Schuster.
- Ortiz J, Torres V, Valderas P (2023) Microservice compositions based on the choreography of BPMN fragments: facing evolution issues. Computing 105:375–416. [CrossRef]
- Alpers S, Becker C, Oberweis A, Schuster T (2015) Microservice Based Tool Support for Business Process Modelling. In: 2015 IEEE 19th International Enterprise Distributed Object Computing Workshop. IEEE, pp 71–78.
- Borkowski M, Fdhila W, Nardelli M, Rinderle-Ma S, Schulte S (2018) Event-based failure prediction in distributed business processes. Inf Syst 0:1–17. [CrossRef]
- Singh Aujla G, Barati M, Rana O, Dustdar S, Noor A, Llanos JT, Carr M, Marikyan D, Papagiannidis S, Ranjan R (2020) COM-PACE: Compliance-Aware Cloud Application Engineering Using Blockchain. IEEE Internet Comput 24:45–53. [CrossRef]
- Casalicchio E, Cardellini V, Interino G, Palmirani M (2018) Research challenges in legal-rule and QoS-aware cloud service brokerage. Future Generation Computer Systems 78:211–223. [CrossRef]
- Fang Z, Yin C (2010) BPM Architecture Design Based on Cloud Computing. Intell Inf Manag 02:329–333. [CrossRef]
- Rimol M (2021) Four Trends Are Shaping the Future of Public Cloud. In: Gartner. gartner.com/en/newsroom/press-releases/2021-08-02-gartner-says-four-trends-are-shaping-the-future-of-public-cloud. Accessed 21 Mar 2022.
- Cloud Native Computing Foundation (2015) Mission of the Cloud Native Computing Foundation. https://github.com/cncf/foundation/blob/main/charter.md. Accessed 21 Mar 2022.
- Accorsi R, Lowis L, Sato Y (2011) Automated certification for compliant cloud-based business processes. Business and Information Systems Engineering 3:145–154. [CrossRef]
- Brucker AD, Compagna L, Guilleminot P (2014) Compliance Validation of Secure Service Compositions. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 136–149.
- Birukou A, Cavalcante AB, Casati F, Chowdhury SR, D’Andrea V, Leymann F, Oberortner E, Serafinski J, Silveira P, Strauch S, Tluczek M (2010) An integrated solution for runtime compliance governance in SOA. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 706–707.
- Tran H, Holmes T, Oberortner E, Mulo E, Cavalcante AB, Serafinski J, Tluczek M, Birukou A, Daniel F, Silveira P, Zdun U, Dustdar S (2010) An End-to-End Framework for Business Compliance in Process-Driven SOAs. In: 2010 12th International Symposium on Symbolic and Numeric Algorithms for Scientific Computing. IEEE, pp 407–414.
- Vetter A (2016) Detecting Operator Errors in Cloud Maintenance Operations. In: 2016 IEEE International Conference on Cloud Computing Technology and Science (CloudCom). IEEE, pp 639–644.
- Indiono C, Fdhila W, Rinderle-Ma S (2018) Evolution of Instance-Spanning Constraints in Process Aware Information Systems. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). Springer Verlag, pp 298–317.
- Seyffarth T, Kuehnel S, Sackmann S (2018) Business process compliance and business process change: An approach to analyze the interactions. In: Lecture Notes in Business Information Processing. Springer Verlag, pp 176–189.
- Koetter F, Kintz M, Kochanowski M, Fehling C, Gildein P, Leymann F, Weisbecker A (2016) Unified Compliance Modeling and Management using Compliance Descriptors. In: Proceedings of the 6th International Conference on Cloud Computing and Services Science. SCITEPRESS - Science and Technology Publications, pp 159–170.
- Koetter F, Kintz M, Kochanowski M, Wiriyarattanakul T, Fehling C, Gildein P, Wagner S, Leymann F, Weisbecker A (2017) An Universal Approach for Compliance Management Using Compliance Descriptors. In: Helfert M, Ferguson D, Méndez Muñoz V, Cardoso J (eds) Communcations in Computer and Information Science. Springer International Publishing, Cham, pp 209–231.
- Filepp R, Adam C, Hernandez M, Vukovic M, Anerousis N, Zhang GQ (2018) Continuous compliance: Experiences, challenges, and opportunities. In: Proceedings - 2018 IEEE World Congress on Services, SERVICES 2018. Institute of Electrical and Electronics Engineers Inc., pp 21–22.
- Kuehnel S, Zasada A (2018) An Approach Toward the Economic Assessment of Business Process Compliance. In: Woo C, Lu J, Li Z, Ling TW, Li G, Lee ML (eds). Springer International Publishing, Cham, pp 228–238.
- Loreti D, Chesani F, Ciampolini A, Mello P (2018) A distributed approach to compliance monitoring of business process event streams. Future Generation Computer Systems 82:104–118. [CrossRef]
- Adams N, Augusto A, Davern M, Rosa M La (2022) Why Do Banks Find Business Process Compliance so Challenging? An Australian Perspective. In: Lecture Notes in Business Information Processing. pp 3–20.
- Ly LT, Göser K, Rinderle-Ma S, Dadam P (2008) Compliance of semantic constraints - A requirements analysis for process management systems. In: CEUR Workshop Proceedings. pp 31–45.
- Scholte T, Kirda E (2010) Achieving Life-Cycle Compliance of Service-Oriented Architectures: Open Issues and Challenges. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 253–267.
- Mustapha AM, Arogundade OT, Vincent OR, Adeniran OJ, Chen X (2017) A model-based business process compliance management architecture for SMSE towards effective adoption of cloud computing. In: 2017 International Conference on Computing Networking and Informatics (ICCNI). IEEE, pp 1–6.
- Ouyang R, Wang J, Xu H, Chen S, Xiong X, Tolba A, Zhang X (2023) A Microservice and Serverless Architecture for Secure IoT System. Sensors 23:4868. [CrossRef]
- Suliman AT, Kadadha M, Mizouni R, Otrok H, Damiani E, Al-Qutayri M (2023) Blockcheck: A consortium blockchain-based conformance checking framework for business processes. Internet of Things 21:100652. [CrossRef]
- Singh P (2022) Designing Observable Microservices for Financial Applications with Built-in Compliance. International Journal of Multidisciplinary Research and Growth Evaluation 3:1163–1168. [CrossRef]
- Rodríguez C, Schleicher D, Daniel F, Casati F, Leymann F, Wagner S (2013) SOA-enabled compliance management: instrumenting, assessing, and analyzing service-based business processes. Service Oriented Computing and Applications 7:275–292. [CrossRef]
- Kellogg M, Schäf M, Tasiran S, Ernst MD (2020) Continuous compliance. In: Proceedings of the 35th IEEE/ACM International Conference on Automated Software Engineering. ACM, New York, NY, USA, pp 511–523.
- Lu R, Sadiq S, Governatori G (2008) Compliance aware business process design. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 120–131.
- Tsakalidis G, Vergidis K, Delias P, Vlachopoulou M (2019) A Conceptual Business Process Entity with Lifecycle and Compliance Alignment. In: Lecture Notes in Business Information Processing. pp 70–82.
- Beckers K (2015) Supporting the Establishment of a Cloud-Specific ISMS According to ISO 27001 Using the Cloud System Analysis Pattern. In: Pattern and Security Requirements. Springer International Publishing, Cham, pp 299–392.
- Silveira P, Rodríguez C, Birukou A, Casati F, Daniel F, D’Andrea V, Worledge C, Taheri Z (2012) Aiding Compliance Governance in Service-Based Business Processes. In: Handbook of Research on Service-Oriented Systems and Non-Functional Properties. IGI Global, pp 524–548.
- Silveira P, Rodríguez C, Casati F, Daniel F, D’Andrea V, Worledge C, Taheri Z (2010) On the design of compliance governance dashboards for effective compliance and audit management. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 208–217.
- Adams N, Augusto A, Davern M, La Rosa M (2024) End-to-end, no-code business process compliance framework for the banking industry. In: CEUR Workshop Proceedings. pp 15–27.
- Namiri K, Stojanovic N (2007) Pattern-based design and validation of business process compliance. In: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics). pp 59–76.
- Yao J, Chen S, Levy D (2014) Accountability-Based Compliance Control of Collaborative Business Processes in Cloud Systems. In: Security, Privacy and Trust in Cloud Systems. Springer Berlin Heidelberg, Berlin, Heidelberg, pp 345–374.
- Kiesel J, Grünewald E (2024) Extending Business Process Management for Regulatory Transparency. In: Business Process Management Forum. pp 337–353.
- Vadlamudi S, Sam J (2021) A Novel Approach to Onboarding Secure Cloud-Native Acquisitions into Enterprise Solutions. In: 2021 International Conference on Disruptive Technologies for Multi-Disciplinary Research and Applications (CENTCON). IEEE, pp 228–233.
- Monteiro D, Maia PHM, Rocha LS, Mendonça NC (2020) Building orchestrated microservice systems using declarative business processes. Service Oriented Computing and Applications 14:243–268. [CrossRef]
- Zarour K, Benmerzoug D (2018) Multicriteria-Based Analysis and Evaluation of Business Processes Executed in Multi-Cloud Environment. In: Advances in Intelligent Systems and Computing. Springer Verlag, pp 315–327.
- Casalicchio E, Palmirani M (2015) A Cloud Service Broker with Legal-Rule Compliance Checking and Quality Assurance Capabilities.
- Solaiman E, Sfyrakis I, Molina-Jimenez C (2016) A State Aware Model and Architecture for the Monitoring and Enforcement of Electronic Contracts. In: Proceedings - CBI 2016: 18th IEEE Conference on Business Informatics. Institute of Electrical and Electronics Engineers Inc., pp 55–63.
- Accorsi R (2011) Business process as a service: Chances for remote auditing. In: Proceedings - International Computer Software and Applications Conference. pp 398–403.
- Garg R, Naudts B, Verbrugge S, Stiller B (2015) Modeling legal and regulative requirements for ranking alternatives of cloud-based services. 8th International Workshop on Requirements Engineering and Law, RELAW 2015 - Proceedings 25–32. [CrossRef]
- Liu X, Xia C, Wang T, Zhong L (2017) CloudSec: A Novel Approach to Verifying Security Conformance at the Bottom of the Cloud. In: 2017 IEEE International Congress on Big Data (BigData Congress). IEEE, pp 569–576.
- Mulo E, Zdun U, Dustdar S (2013) Domain-specific language for event-based compliance monitoring in process-driven SOAs. Service Oriented Computing and Applications 7:59–73. [CrossRef]
- Seyffarth T, Kuehnel S (2022) Maintaining business process compliance despite changes: a decision support approach based on process adaptations. J Decis Syst 31:305–335. [CrossRef]
- Seyffarth T, Raschke K (2020) BCIT: A tool to recommend compliant business processes based on process adaption.
- Stratigaki C, Nikolaidou M, Loucopoulos P, Anagnostopoulos D (2016) Business process elicitation from regulatory compliance documents: An E-government case study.
- Teixeira Filho HM, Guerreiro Azevedo L, Matsui Siqueira SW (2016) IntelliGOV - A semantic approach for compliance validation of service-oriented architectures.
- Vetter A (2019) Online Detection of Operator Errors in Cloud Computing Using Anti-patterns. In: Lecture Notes in Business Information Processing. pp 1–24.
- Tosatto SC, Governatori G, Kelsen P (2015) Business Process Regulatory Compliance is Hard. IEEE Trans Serv Comput 8:958–970. [CrossRef]
| 1 | GitHub Repository: https://github.com/hangoclong/bpc4msa.git
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




