Submitted:
17 March 2026
Posted:
18 March 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Overview
1.2. Hypotheses
- What are the difficulties that people with disabilities face when attempting to authenticate?
- Is the person’s disability the main hindrance to logging onto a system? i.e., is their problem with logging in directly related to their disability?
- What are the tradeoffs between usability and security? i.e., do we need to make authentication easier for disabled users, or more secure, or both?
2. Literature Review
2.1. Systematic Literature Review
2.1. Further Literature Review (Conducted at the Time of Writing)
3. Methods
3.1. Overview
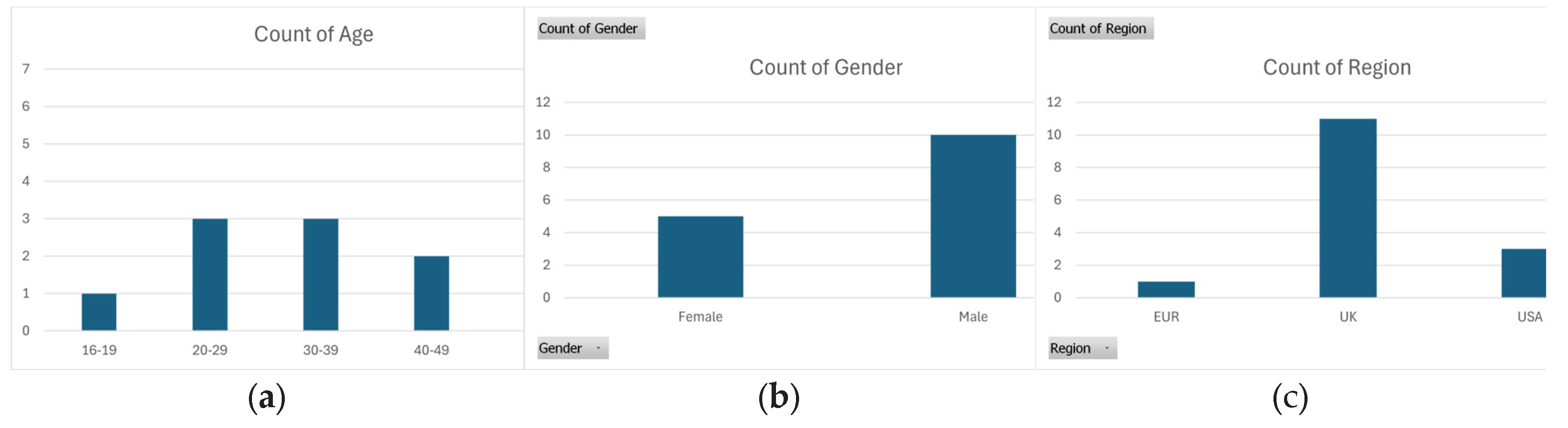
3.2. Participants
3.3. Interview Questions
3.4. Analysis Methodologies
4. Results
4.1. Overview
4.1.1. Categorization
4.1.2. Disability
4.2. Coding Results and Resolution of the Theoretical Framework
| Name of Disability | Degree of effect* | |||
| Physical | Cognitive | |||
| Physical Disability | Learning Disability | Psychological Disability† | Neurodevelopmental Disorder | |
| ADHD1 | N/a | N/a | N/a | Major |
| Anxiety 2 | N/a | N/a | Major | N/a |
| Asthma3 | Major | N/a | Minor | N/a |
| Cerebral Palsy4 | Major | N/a | N/a | Major |
| Dementia5 | N/a | Minor | Minor | N/a |
| Depression6 | N/a | N/a | Major | N/a |
| Dyslexia7 | N/a | Major | N/a | N/a |
| Dyspraxia8 | N/a | N/a | N/a | Major |
| Muscular Dystrophy9 | Major | Minor | Minor | Major |
| Schizophrenia10 | N/a | N/a | Major | Minor |
| Autism / Spectrum Disorder11 | N/a | N/a | Minor | Major |
| Spinal Cord Injury / Malformation12 | Major | N/a | Minor | N/a |
| Stroke13 | Minor | N/a | N/a | Major |
| Williams Syndrome14 | Minor | Major | Minor | N/a |
- Is ADHD a Learning Disability -Understanding Neurodiversity. https://www.skillsforhealth.org.uk/article/is-adhd-a-learning-disability-the-differences-and-co-occurrences/ (accessed on 28/02/2026).
- Your Guide to Anxiety and Disability Benefits. https://www.healthline.com/health/anxiety/is-anxiety-a-disability#qualifications (accessed on 28/02/2026).
- Is Asthma a Mental Illness? https://biologyinsights.com/is-asthma-a-mental-illness-the-physical-mental-connection/ (accessed on 28/02/2026). Note: Asthma can cause difficulty in traversing to reach the authentication device.
- Cerebral Palsy. https://www.ninds.nih.gov/health-information/disorders/cerebral-palsy (accessed on 28/02/2026).
- What is dementia? https://www.alzheimers.org.uk/about-dementia/types-dementia/what-is-dementia (accessed on 28/02/2026). Note: While Dementia technically does not fall into any of the disability characteristics, it does cause cognitive difficulties, and people with learning disabilities are more likely to develop it than others.
- When a mental health condition becomes a disability. https://www.gov.uk/when-mental-health-condition-becomes-disability (accessed on 28/02/2026).
- Dyslexia. https://www.nhs.uk/conditions/dyslexia/ (accessed on 28/02/2026).
- Is Dyspraxia A Disability? https://islts.co.uk/is-dyspraxia-a-disability/ (accessed on 28/02/2026).
- How Does Muscular Dystrophy Affect the Brain? https://biologyinsights.com/how-does-muscular-dystrophy-affect-the-brain/ (accessed on 28/02/2026). Note: It can cause anxiety and depression.
- Quadriplegia. https://continentalhospitals.com/diseases/quadriplegia/ (accessed on 28/02/2026). Generally caused by spinal cord injuries, but also by neurological conditions.
- Schizophrenia. https://www.nhs.uk/mental-health/conditions/schizophrenia/overview/ (accessed on 28/02/2026). Note: Generally accepted to be a psychological disability, but some may question if it is neurodevelopmental: https://psychiatryclinic.org/is-schizophrenia-a-neurodevelopmental-disorder/. (accessed on 28/02/2026).
- Autism Spectrum Disorder. https://www.nimh.nih.gov/health/publications/autism-spectrum-disorder (accessed on 28/02/2026). Note: Not generally classified as a disability, but more as a developmental disorder, as often symptoms appear in the first 2 years of life
- Cognitive Effects of Spinal Cord Injury on the Brain. https://biologyinsights.com/cognitive-effects-of-spinal-cord-injury-on-the-brain/ (accessed on 28/02/2026). Note: Generally caused by spinal cord injuries, but also by neurological conditions. Spinal disabilities can also cause psychological issues.
- Psychological Effects of Stroke. https://www.england.nhs.uk/london/wp-content/uploads/sites/8/2019/09/Psychological-Effects-of-Stroke.pdf (accessed on 28/02/2026). Note: Predominantly a neurological condition that can cause physical disability such as semi-paralysis.
- What is it? https://williams-syndrome.org.uk/what-is-williams-syndrome-6-2/ (accessed on 28/02/2026).
| Name of Disability | Degree of effect* | |||
| Physical | Cognitive | |||
| Physical Disability | Learning Disability | Psychological Disability† | Neurodevelopmental Disorder | |
| Authenticator issues (technical)1 | 6 | 0 | 5 | 1 |
| CAPTCHA issues2 | 2 | 2 | 1 | 4 |
| Character set (not readable)3 | 0 | 2 | 0 | 4 |
| Code retrieval delays4 | 2 | 2 | 1 | 6 |
| Distance from device5 | 8 | 0 | 7 | 3 |
| Environmental distractions6 | 2 | 0 | 1 | 2 |
| Fingerprint scanners7 | 0 | 2 | 0 | 4 |
| Forgotten password8 | 4 | 5 | 4 | 14 |
| Frustrating experience9 | 12 | 4 | 9 | 14 |
| Identification (Authentication)10 | 2 | 0 | 2 | 2 |
| Locked out of service11 | 8 | 1 | 3 | 10 |
| Low difficulty / no issues (control)12 | 11 | 4 | 8 | 13 |
| Number of accounts needed (too many)13 | 3 | 0 | 0 | 4 |
| Password mismatching (on signup)14 | 2 | 3 | 1 | 8 |
| Privacy concerns15 | 10 | 3 | 4 | 12 |
| Repeated login attempts needed16 | 7 | 2 | 2 | 8 |
| Time based codes17 | 4 | 2 | 1 | 6 |
| Time consuming18 | 3 | 3 | 1 | 10 |
| Two-Factor Authentication (2FA)19 | 8 | 0 | 6 | 1 |
- P02 / 34:16.6, 34:36.7 | P05 / 2:40.1 | P15 / 21:39.8
- P01 / 3:13.7 | P02 / 46:03.1, 46:17.3, 46:33.4, 46:39.4, 47:14.4
- P01 / 1:00.3, 3:01.4
- P01 / 10:17.0 | P02 / 16:03.3 | P15 / 21:39.8
- P02 / 5:29.2, 6:25.2, 16.18.2 | P04 / 4:11:0 | P05 / 1:18.2, 1:40.9, 2:31.9, 2.:40.1, 9:06.3 |P06 / 19.11.7 | P15 / 25.02.3
- P02 / 6:25.2, 6:40.0 | P15 / 0:54.8
- P01 / 4:19.9
- P01 / 10:17.0 | P09 / 10:02.9, 5:19.8 | P10 / 0:54.4, 5:05.1 | P12 / 15:38.5 | P13 / 0:39.5, 4:21.2 | P14 / 0:30.5 | P15 / 0:54.8, 16:08.5
- P02 / 47:19.1 | P03 / 11:54.1 | P04 / 4:11.0, 19:55.6, 25:04.6 | P09 / 5:09.2 | P10 / 6:58.8 | P11 / 10:06.6, 11:06.1, 11:24.8, 11:54.5, 12:55.1 | P12 / 1:31.2, 5:18.1, 15:38.5 | P13 / 2:26.5, 4:32.7, 5:24.5 | P14 / 1:21.7, 1:29.6 | P15 / 1:32.4, 3:42.8, 22:12.2
- P02 / 4:58.1, 8:29.1, 9:05.0, 26:42.4, 27:19.8, 32:27.3, 34:04.3, 35:33.8, 49:16.8, 50:56.1, 51:08.4, 51:20.7 | P06 / 10:03.5 | P15 / 8:13.2, 8:53.0, 11:40.8
- P04 / 23:49.7 | P06 / 15:20.7 | P07 / 10:48.8 | P11 / 0:35.3 | P12 / 1:29.9, 5:02.8, 6:23.4 | P13 / 4:23.7 | P15 / 1:32.4, 2:46.6, 22:12.2
- P01 / 6:57.4, 9:25.6 | P02 / 3:22.8 | P03 / 10:29.9 | P04 / 17:48.3, 29:44.9, 30:47.2 | P05 / 15:27.1 | P06 / 0:51.4, 19:54.4 | P08 / 12:02.9 | P12 / 15:14.6
- P11 / 0:54.6 | P13 / 1:16.5, 1:23.5
- P01 / 1:27.5 | P12 / 6:23.4 | P13 / 2:26.5
- P01 / 4:27.3, 4:59.2, 5:28.0, 6:17.0, 7:32.7, 12:31.5 | P02 / 29:40.9, 29:46.6, 29:57.6 | P03 / 7:59.9, 10:37.7 | P04 / 11:24.3, 13:45.8, 31:55.4, 36:25.6 | P07 / 6:11.6, 6:42.0 | P13 / 3:28.8, 7:44.9, 8:29.9 | P14 / 6:10.1 | P15 / 8.53.0, 9:55.0, 9:59.4, 10:20.1
- P01 / 1:45.4 | P02 / 6:54.9, 7:53.2 | P04 / 19:55.6 | P11 / 0:35.3, 11:06.1, 11.37.9, 12:09.8 | P13 / 2:26.5
- P01 / 7:15.5, 7:18.5, 8:53.2 | P02 / 4:29.2, 4:42.4, 4:58.1, 5:29.2, 15:43.0, 16:03.3, 16:16.2, 47:33.8 | P11 / 11:33.2, 11:37.9, 11:54.5
- P01 / 4:22.8, 10.36.3 | P03 / 11.05.1 | P11 / 11:06.1 | P13 / 2:26.5 | P15 / 3:42.8, 21:39.8
- P02 / 47:01.2 | P04 / 4:11.0, 17:48.3 | P05 / 1:18.2, 1:40.9, 2:04.8, 2:31.9, 2:40.1, 15:37.4
| Authentication Challenge | Suggested Solutions | |
| Physical | Cognitive | |
| Privacy concerns | Data control/deletion | Data control/deletion |
| Frustrating experience | Add more support for AT | Add simplified options |
| Identification (Authentication) | Improve accessibility | Improve accessibility |
| Forgotten password | Password managers | Password managers |
| Locked out | Alternative options | Alternative options |
| Distance from device | On-person device/wheelchair support | eID alternatives |
| Repeated attempts needed | Provide alternative options | Provide alternative options |
| Time consuming | Add simplified options | Add simplified options |
| Password mismatching | Password managers | Password managers |
| Environmental distractions | Focused experience | Focused experience |
| Number of accounts | SSO | SSO |
| Character set | Font and color support | Font and color support |
| Time-based codes | Extended access support | Extended access support |
| Two-Factor Authentication (2FA) | Often linked to the distance to the device | Often linked to the distance to the device |
| CAPTCHA issues | Improve accessibility | Improve accessibility |
| Authenticator issues | Develop an Accessible Authenticator | Develop an Accessible Authenticator |
| Code retrieval delays | Linked to time-based codes | Linked to time-based codes |
| Fingerprints | Provide alternative options | Provide alternative options |
| Low difficulty / no issues (control) | Increase awareness of alternatives | Increase awareness of alternatives |
4.2.1. General Findings from Stage 1—Initial Coding
- A
- set of characteristic traits emerged from the participants’ answers. Reasoning for this will be deliberated accordingly in our Stage 3 Final Theory Development, later in this section. The list of seven characteristics identified is as follows:
- 1.
- Disability—There is a wide variety of disabilities that could be addressed by this analysis. Signs of accessibility issues begin to emerge in conversation.
- 2.
- AT Devices—People tend to prefer authenticating themselves with only one device.
- 3.
- Usability versus Security—While people prefer a usable platform, security is still a significant concern. Subsequently, this contradicts earlier theoretical research mentioned in the literature review that suggests usability is a larger problem than security; however, it could be accepted that this is more of a problem in the paradigm of an authentication machine’s functional capability, which contrasts with the user’s value-based and balanced perspective of the situation.
- 4.
- Issues—Time-based codes present the biggest challenge, specifically, physically being able to reach for a 2FA device.
- 5.
- Desirable Features—A simplified login is preferred with optional settings.
- 6.
- Responsibility—The onus for privacy and security should lie with the service provider. A user’s own responsibility is also recognized.
4.2.2. Emerging Characteristics from Stage 2—Focused Coding
- It is difficult to reduce the findings without overlooking small but perhaps relevant information.
- Some topics show much greater support from users than others.
- Some topics reveal an almost 50/50 split in opinions, leading to the assumption that there is no right or wrong answer for these questions.
- Most users identify problems logging in due to their disability.
- Although the research aims to make logging in easier for users, security is still important to them.
- There is considerable interest in a universal login system.
- There is interest in alternative devices to facilitate the log-in process.
- Forgetting passwords is a common theme.
4.2.3. Formulation of Substantive Theory from Stage 3—Final Theory Development
4.3. Preliminary Analysis for Final Theory
- 1.
- Most users identify problems logging in as related to their disability.
- 2.
- The most desired feature is a simplified login, such as an SSO.
- 3.
- Security is of high importance to users and closely matched by the desire for ease of use.
- 4.
- The most common issues appear to be with time-based codes (for 2FA) and the CAPTCHA systems.
- 5.
- Solutions to accessible authentication problems can be found in the data itself.
- 6.
- The option to remain logged in is desirable in certain situations.
- 7.
- Many users feel that privacy and security of the login system are the company’s responsibility, but several acknowledge their own responsibility too.
- 8.
- There is interest in alternative devices to facilitate the log-in process.
- 9.
- Forgetting passwords is a common theme.
4.3.1. Most Users Identify Problems Logging in Related to Their Disability
4.3.2. The Most Desired Feature Is a Simplified Login, Such as an SSO
4.3.3. Security Is of High Importance to Users, but Closely Matched by the Desire for Ease of Use
4.3.4. The Most Common Issues Appear to Be with Time-Based Codes (for 2FA) and the CAPTCHA Systems
4.3.5. Solutions to Accessible Authentication Problems Can Be Found in the Data Itself
4.3.6. The Option to Remain Logged in Is Desirable in Certain Situations
4.3.7. Many Users Feel That Privacy and Security of the Login System Is the Company’s Responsibility, but Several Acknowledge Their Own Responsibility Too
4.3.8. There Is Interest in Alternative Devices to Facilitate the Login Process
- General Device.
- Fingerprints.
- Facial recognition.
- Mobile phone (or tablet).
- USB key.
4.3.9. Forgetting Passwords Is a Common Theme.
4.3.10. Relating Disability Types to Degrees of Effect for the TF
4.4. Final Theory Presented as a Preliminary Framework (TF)
4.5. Qualitative Data Summary
5. Discussion
5.1. General Discussion
5.2. Limitations
6.Conclusions
6.1. Summation
6.2. Theoretical Conclusions to the Initial Hypotheses
6.3. Future Work
Supplementary Materials
Author Contributions
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| 2FA | Two Factor Authentication |
| AA | Accessible Authentication |
| ACS | Access Control Systems |
| ADHD | Attention Deficit Hyperactivity Disorder |
| ASD | Autism Spectrum Disorder |
| AT | Assistive Technology |
| BU | Bournemouth University |
| BURO | Bournemouth University Research Online |
| CA | Certificate Authority |
| CAPTCHA | Completely Automated Public Turing test to tell Computers and Humans Apart |
| CCTV | Closed Circuit Television |
| CP | Cerebral Palsy |
| CT | Constructivist Theory |
| DevSecOps | Development, Security, and Operations |
| eID | Electronic Identification |
| EUR | Europe |
| FHSD | Facioscapulohumeral Muscular Dystrophy |
| FIDO2 | Fast Identity Online 2 |
| GenAI | Generative Artificial Intelligence |
| GT | Grounded Theory |
| HCI | Human Computer Interaction |
| ID | Identification (physical) |
| IoT | Internet of Things |
| JWT | JSON Web Token |
| OCD | Obsessive Compulsive Disorder |
| SEND | Special Education Needs and Disability |
| SSO | Single Sign-On |
| TA | Thematic Analysis |
| TEE | Trusted Execution Environment |
| TF | Theoretical Framework |
| UEI | Upper Extremity Impairment |
| UI | User Interface |
| UK | United Kingdom |
| USA | United States of America |
| USB | Universal Serial Bus |
| WCAG | Web Content Accessibility Guidelines |
| QoS | Quality of Service |
Appendix A
Appendix A.1
| Participant | Age Range | Geographic Location | Gender |
| participant 1 | 40-49 | Southern England, UK | Female |
| participant 2 | 30-39 | Florida, USA | Male |
| participant 3 | 30-39 | Mississippi, USA | Male |
| participant 4 | 30-39 | Philadelphia, USA | Female |
| participant 5 | 40-49 | Southern England, UK | Male |
| participant 6 | 16-19 | Southern England, UK | Male |
| participant 7 | 50+ | Southern England, UK | Female |
| participant 8 | 20-29 | Midlands, UK | Male |
| participant 9 | 20-29 | Southern England, UK | Male |
| participant 10 | 50+ | Southern England, UK | Female |
| participant 11 | 50+ | Southern England, UK | Male |
| participant 12 | 50+ | Southern England, UK | Male |
| participant 13 | 50+ | Southern England, UK | Male |
| participant 14 | 50+ | Southern England, UK | Male |
| participant 15 | 20-29 | France, EUR | Female |
Appendix A.2
| Topic (number of references) | Sub-topic | Description | References |
| AT devices (132) | General Device | Other or alternative devices | 40 |
| Fingerprints | Preference for fingerprint scanning | 17 | |
| Facial recognition | Desirable for login | 15 | |
| Mobile phone (or tablet) | User’s personal smartphone | 14 | |
| USB key | A security key that stores certificates | 11 | |
| Voice recognition | The user would like to see voice recognition | 7 | |
| Fob | An RF (Radio Frequency) device | 6 | |
| Text-to-speech | Text-to-speech conversion to aid login | 6 | |
| Speech to text | Closed captioning or text prompts | 4 | |
| Font change | Adaptations to font style | 4 | |
| Color changes | Adaptations to font color | 4 | |
| Eye tracking | Eye tracking device | 3 | |
| Sip-Puff Device | A device controlled with the user’s mouth | 1 | |
| Desirable features (89) | Universal login | Would want a universal system | 15 |
| Simplified login | Not too many obstacles or options | 15 | |
| Remain logged in | Be logged in when they get back | 11 | |
| Something you know | 2FA (Two Factor Authentication) | 8 | |
| Focused options | Options focused on the disability | 7 | |
| Happy with just a password | Would like to see just a password system only | 6 | |
| Passcode recording | System records time-based code for you | 5 | |
| Easier Recovery | Easier options to recover data | 5 | |
| Faster login | Quickest possible login preferred | 4 | |
| Delete information | Auto-remove old passcodes | 4 | |
| Speak to a person | Would prefer to speak to a real person about login issues | 3 | |
| Show password | Option to show password | 2 | |
| Use of AI | Use of AI once the info is passed to the organization | 2 | |
| Picture-Based Authentication | Selecting pictures to log in | 2 | |
| Disability (131) | Nature of disability | Name of Disability in question | 32 |
| Due to disability | User feels the issue is due to disability | 29 | |
| Pass information | Happy to pass information to third parties | 22 | |
| Reluctant to divulge | Reluctance to divulge disability | 20 | |
| Not because of disability | User feels the issue is not due to disability | 11 | |
| Deterioration | Concerns about a deteriorating or degenerative disability | 5 | |
| Issues[1] (180, 127 G, 41 V, 12 L) | Privacy concerns G | Concerns about information or permissions | 27 |
| Frustrating G | Feelings of frustration due to authentication | 23 | |
| Identification G | Issues with being identifiable | 17 | |
| Forgotten password G | Unable to recall password | 11 | |
| Locked out G | No way to verify own account | 11 | |
| Distance from device G | Being far away/having to reach a 2FA device. | 11 | |
| Repeated attempts needed G | Repeated attempts needed to log in or tired from repeatedly having to do it | 9 | |
| Time-consuming G | Logging in is time-consuming | 7 | |
| Password mismatching G | Inability to match passwords | 3 | |
| Distractions G | Environmental disabilities | 3 | |
| Number of accounts G | Extra complexity caused by the quantity of different logins needed | 3 | |
| Character set G | Issues with the character set | 2 | |
| Time-based codes V | Two-step authentication issues | 17 | |
| 2FA V | Two-step authentication issues | 9 | |
| CAPTCHA issues V | Issues with Google (or other) image recognition test—characterized by the use of traffic lights and stairs | 6 | |
| Authenticator issues V | Authenticator issues or delays | 4 | |
| Code retrieval delays V | Issues with biometric | 3 | |
| Fingerprints V | Time delays in emails or 2FA codes coming through | 1 | |
| Low difficulty L | Minor or no issues with authentication | 12 | |
| Responsibility (27) | Companies’ responsibility | The company is more responsible | 14 |
| Both responsible | Users and companies are equally responsible | 10 | |
| Users’ responsibility | The user is more responsible | 3 | |
| Usability v Security (85) | Security important | User feels security is important | 34 |
| Usability (and speed of access) is important | User feels usability is important | 20 | |
| Balanced System | Users need a balance between security and usability | 18 | |
| Security Sacrifices | Willing to sacrifice security to make it easier to log in | 13 |
Appendix B
Appendix B.1
- The interview questions are listed in Table B1.
| Index | Question | Format | Relevance / Reasoning | Category |
| 01 | Name | Text | Indexing/Storage | DE1 |
| 02 | Age Range * |
|
Age verification, categorization | DE2 |
| 03 | Gender |
|
Demographic | DE3 |
| 04 | Geographic Location | Text | Classification / Diversity | DE4 |
| 05 | Disability * | Text | Classification / Relevance / Application options | DR1 |
| 06 | Do you find authentication (i.e., logging into websites or applications) difficult because of your disability? | Yes / No / Maybe | Perception of an issue | DR2/U2 |
| 07 | In what ways (if any) does your disability make authentication hard for you to do? What are the main difficulties that you face when you log in to systems that do not take your disability into account? |
Text | Context on current issues. Difficulty related to disability. |
U3/DR3 |
| 08 | How important is it for you to get logged in quickly? | Scalar value 1-5
|
Need for speed / ease of use. | U4 |
| 09 | How highly do you rate the importance of security? | Scalar value 1-5
|
Need for security. | S1 |
| 10 | How often do you sacrifice security to make logging in easier? E.g., easy passwords, password reuse, no 2-Factor Authentication (2FA), etc. | Scalar value 1-5
|
Willingness to sacrifice security. | DR4/S2 |
| 11 | Do you sacrifice security because it’s too difficult to authenticate with your disability? Is there anything that could make this easier? | Text | Does lack of usability bar security? | DR5/S3/U5 |
| 12 | If you had to choose, would you prefer more security or an easier or faster login? | Scalar value 1-5
|
Preferences. | S4/U6 |
| 13 | Would you like to have one system that you could use to log into most of your websites and applications? | Yes / No / Maybe | Is it wanted? Single sign on (SSO) needed? | U7 |
| 14 | When you log in to a site or service, would you like to have details of your disability passed across so that they can automatically adapt their user experience for you? | Yes / No / Maybe | Need for passing data parameters to third party. | DR6 |
| 15 | Would you like to have the options to choose which elements of your disability are revealed to each third party that you log into? | Yes / No / Maybe | Level of disclosure to third party. | DR7/P1 |
| 16 | How do you feel about trusting a company with information about your disability, and what benefits or negative side effects do you think it could have? | Text | Trust, privacy, and confidence. | DR8/P2 |
| 17 | Would you like to see a login system that could work with a variety of inputs, including paddles, sip/puff, audio/text-to-speech devices, optical/head movement, or other assistive technologies? | Yes / No / Maybe | Application hardware interfacing. | U8 |
| 18 | In relation to the above question, which alternative or assistive technologies would you like to be able to do this with? | Text | Classify hardware options. | U9 |
| 19 | Would you like to or currently use assistive technology (AT) such as a paddle or switch to authenticate with? Please specify which AT device you would use. | Text | Use of AT for verification/ 2FA. | U10/DR9 |
| 20 | Would you say that you are currently happy with the way you have to log in to sites currently? | Text | Overall satisfaction with current technology. | E1 |
| 21 | Do you find it frustrating or have any reservations when logging into systems (e.g., Loss of data, privacy, access denial, difficulty logging in)? | Text | Negative Emotional States. | P3 |
| 22 | What strengths do you think a good login system should have, and how would you feel if you could use a system like this? | Text | Positive Emotional states. | E2 |
| 23 | Do you sometimes think that a company should automatically know who you are, or do you welcome the fact that there is a layer of security always protecting your data? Do you think authentication systems need to be more intelligent? | Text | Security levels, individual recognition, and AI detection. | P4/S5 |
| 24 | Do you feel that security is an organization’s responsibility, that of the user, or a bit of both? | Text | Placement of responsibilities | S6/P5 |
| 25 | Would you consider using an on-person device for verification, and if so, which would you prefer? E.g. Key fob, USB key, Bluetooth switch, biometric device, or maybe just a mobile phone | Text | Would they be prepared to carry a device with them for verification? | U11 |
| 26 | Would you like the opportunity to be included in any future research questions in relation to this PhD? | Yes / No Please fill out the separate contact questionnaire if ‘Yes’ |
Opportunity to participate in further testing systems, reviews or general questionnaires. | DE5 |
| 27 | Any further comments | Text | Qualitative / vocalization of ideas. | All |
References
- How to Meet WCAG (Quick Reference). Available online: https://www.w3.org/WAI/WCAG22/quickref/ (accessed on 29th May 2025).
- Meet the requirements of equality and accessibility regulations. Available online: https://www.gov.uk/guidance/meet-the-requirements-of-equality-and-accessibility-regulations (accessed on 29th May 2025).
- Equality Act 2010. Available online: https://www.legislation.gov.uk/ukpga/2010/15/contents (accessed on 29th May 2025).
- Cropley, D.; Whittington, P.; Dogan, H. A Systematic Literature Review for Facilitating Authentication for the Disabled. In Proceedings of the IEEE International Conference on e-Business Engineering (ICEBE), Fudan University, Shanghai, China, 11th-13th October 2024; pp. 218–225. [Google Scholar] [CrossRef]
- Furnell, S.; Helkala, K; Woods, N. Accessible authentication: assessing the applicability for users with disabilities. Computers & Security 2022, Volume 113, 102561. [Google Scholar]
- Üstün, T. B.; Kostanjsek, N.; Chatterji, S.; Rehm, J. Measuring Health and Disability, Manual for WHO Disability Assessment Schedule (WHODAS 2.0), World Health Organization. 2010; p.4. ISBN: 9789241547598.
- Laamanen, M.; Ladonlahti, T; Uotinen, S; Okada, A.; Bañeres, D.; Koçdar, S. Acceptability of the e-authentication in higher education studies: views of students with special needs and disabilities. Int J Educ Technol High Educ 2021, Volume 18. [CrossRef]
- Di Campi, A.M.; Luccio, F.L. Accessible authentication methods for persons with diverse cognitive abilities. Univ Access Inf Soc 2025. [CrossRef]
- Andrew, S.; Watson, D.; Oh, T.; Tigwell, G. W. A review of literature on accessibility and authentication techniques. ACM Assets ’20 2020, 55, 1–4. [Google Scholar] [CrossRef]
- Alnfiai, M.; Sampalli, S. BraillePassword: accessible web authentication technique on touchscreen devices. J Ambient Intell Human Comput 2019, Volume 10, 2375–2391. [CrossRef]
- Lewis, B.; Kirupaharan, P.; Ranalli, T-M.; Venkatasubramanian, K. A3C: An Image-Association-Based Computing Device Authentication Framework for People with Upper Extremity Impairments. ACM Trans. Access. Comput. 2024, Volume 17(2), 6. [Google Scholar] [CrossRef]
- NVivo (#1 qualitative analysis software for 30 years). Available online: https://lumivero.com/products/nvivo/ (accessed on 17th June 2025).
- Grimes, R. Introduction. In Hacking Multifactor Authentication; John Wiley & Sons: Indiana, USA, 2021; p. xxvii.
- Gibson, P. Thought (Chapter 8). In Philosophy; Arcturus: London, UK, 2021; p. 126.
- Mohajan, D; Mohajan, H. Memo Writing Procedures in Grounded Theory Research Methodology. Studies in Social Science & Humanities 2022, Vol. 1(No. 4), 10–18. [Google Scholar] [CrossRef]
- Braun, V; Clarke, V. Can I use TA? Should I use TA? Should I not use TA? Comparing reflexive thematic analysis and other pattern-based qualitative analytic approaches. Couns Psychother Res 2021, Vol. 21, 37–47. [Google Scholar] [CrossRef]
- Mathematical Induction. Available online: https://www.math.wustl.edu/~freiwald/310induction1.pdf (accessed on 1st October 2025).
- Chun Tie, Y.; Birks, M.; Francis, K. Grounded theory research: A design framework for novice researchers. SAGE Open Medicine 2019. [CrossRef]
- Charmaz, K. An Invitation to Grounded Theory (Chapter 1). In Constructing grounded theory. A practical guide through qualitative analysis; Sage Publications: London, UK, 2006; pp. 1-12, ISBN: 978-0-7619-7353-9.
- Thompson, G. Products—assistive and accessible technologies. In Digital Assistive Technology; Awde, N.; Banes, D.; Banes, K., Eds.; Millennium Community Solutions: King’s Lynn, UK, 2022; pp. 74-235.
- Bhandari, G.; Lyth, A.; Shalaginov, A.; Grønli, T.-M. Distributed Deep Neural-Network-Based Middleware for Cyber-Attacks Detection in Smart IoT Ecosystem: A Novel Framework and Performance Evaluation Approach. Electronics 2023, 12, 298. [Google Scholar] [CrossRef]
- Rich, E.; Knight, K. Connectionist Models (Chapter 18). In Artificial Intelligence, 2nd ed.; Shapiro, D. M.; Murphy, J. F., Eds.; McGraw-Hill: New York, USA, 1991; p. 492.
- The future of artificial intelligence. Available online: https://www.ibm.com/think/insights/artificial-intelligence-future (accessed on 12th November 2025).
- MacKenzie, I. S. Modelling Interaction (Chapter 8). In Human-Computer Interaction, 1st ed.; Morgan Kaufmann: Massachusetts, USA, 2013; pp. 249-255.
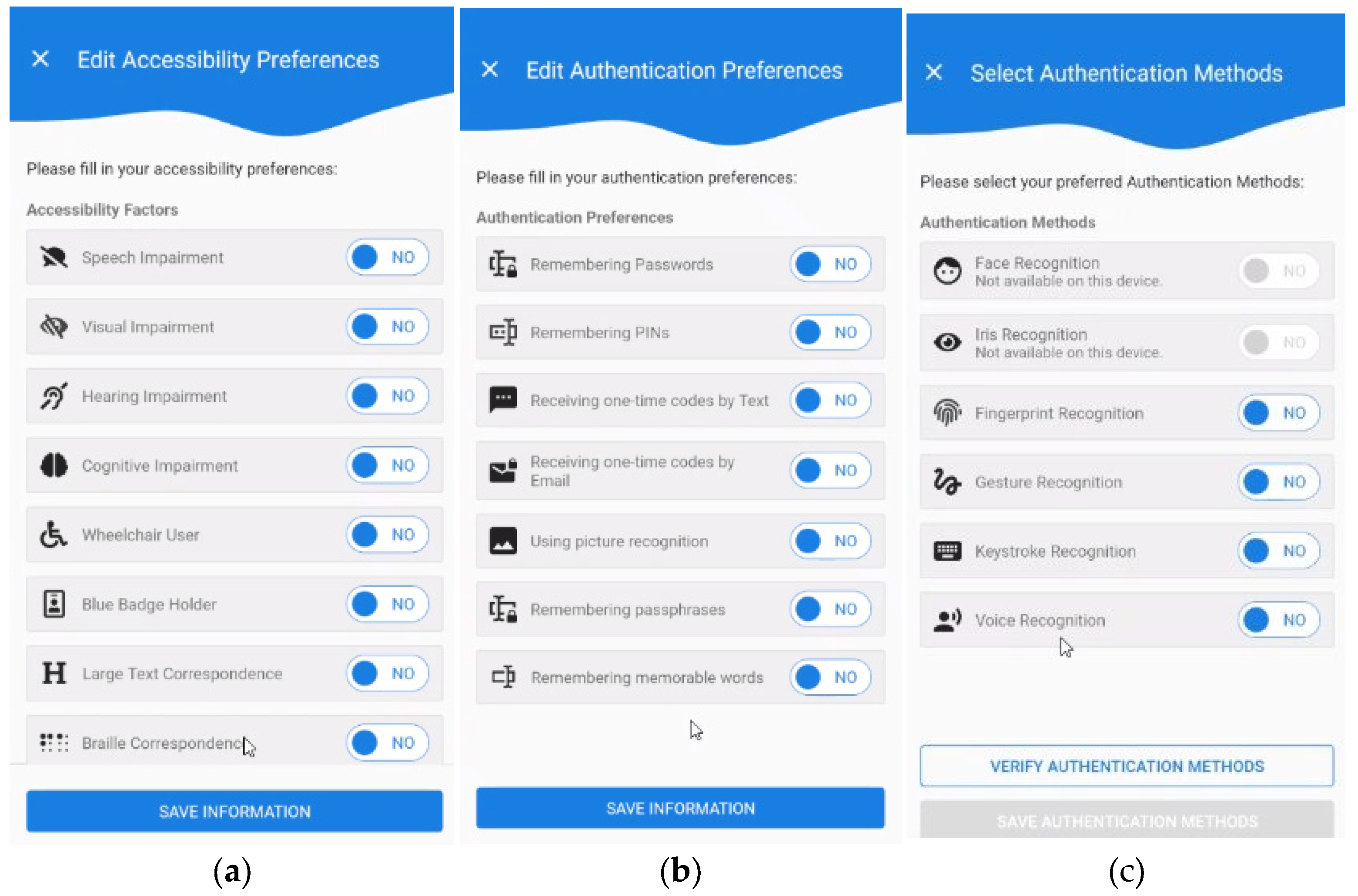
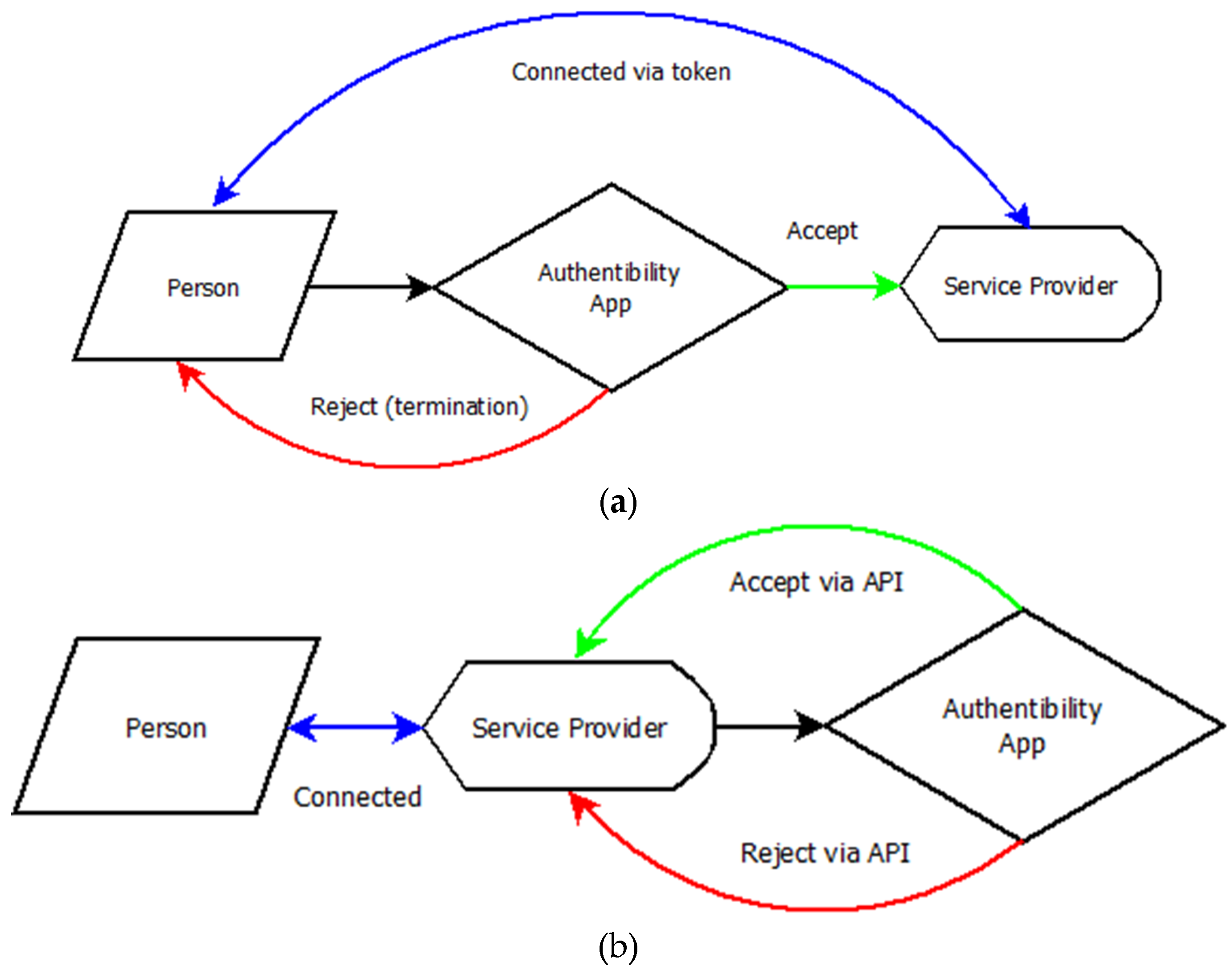
- Whittington, P.; Dogan, H. Authentibility Pass: An accessible authentication gateway for people with reduced abilities. In Proceedings of the IEEE International Conference on e-Business Engineering (ICEBE), Sydney, Australia, 4th-6th November 2023; pp. 155–162. [Google Scholar] [CrossRef]
- Schwartz, S.; Maciej, M. SAML (Chapter 3). In Securing the Perimeter: Deploying Identity and Access Management with Free Open Source Software; Apress: Berkeley, CA, 2020; p. 65. [CrossRef]
- Dash, S. K. Federated Authentication-II (Chapter 5). In Web Authentication Handbook; Orange Education: Delhi, India, 2023; pp. 167-169.
- Barker, J. Why physical space matters in cybersecurity (Chapter 7). In Confident Cyber Security; Kogan Page: London, UK, 2018; pp. 121-130.
- Firouzi, A.; Dadkhah, S.; Maret, S.A.; Ghorbani, A.A. DataSense: A Real-Time Sensor-Based Benchmark Dataset for Attack Analysis in IIoT with Multi-Objective Feature Selection. Electronics 2025, 14, 4095. [Google Scholar] [CrossRef]
- Intrusion detection evaluation dataset (CIC-IDS2017). Available online: https://www.unb.ca/cic/datasets/ids-2017.html (accessed on 4th November 2025).
- Li, Y.; Li, Y.; Wang, G.; Hu, H. An Adaptive Dynamic Defense Strategy for Microservices Based on Deep Reinforcement Learning. Electronics 2025, 14, 4096. [Google Scholar] [CrossRef]
- Zawadzki, P.; Dziwoki, G.; Kucharczyk, M.; Machniewski, J.; Sułek, W.; Izydorczyk, J.; Izydorczyk, W.; Kłosowski, P.; Dustor, A.; Filipowski, W.; et al. Quantum Enabled Data Authentication Without Classical Control Interaction. Electronics 2025, 188, 104810. [Google Scholar] [CrossRef]
- Disability. Available online: https://www.who.int/health-topics/disability#tab=tab_1 (accessed on 6th November 2025).
- Designing Remote Keyless Entry (RKE) Systems. Available online: https://www.analog.com/en/resources/technical-articles/designing-remote-keyless-entry-rke-systems.html (accessed on 14th November 2025).
- Battey, H.S.; Cox, D. R. Some aspects of non-standard multivariate analysis. Journal of Multivariate Analysis 2022, 14, 4096. [Google Scholar] [CrossRef]
- Ghorbani Lyastani, S; Schilling, M.; Neumayr, M.; Backes, M.; Bugiel, S. Is FIDO2 the Kingslayer of User Authentication? A Comparative Usability Study of FIDO2 Passwordless Authentication. IEEE Symposium on Security and Privacy (SP) 2020, pp. 268-285. [CrossRef]
| 1 | Legend: G = General issues. V = Verification issues. L = Lack of issues. |
| 2 |
Questions marked with a * are mandatory, failing to complete this will invalidate your submission. Other questions are optional, but if all are completed this will aid the research more. Categorization key for the questions is as follows:
DE - Demographics
U - Usability
S - Security
DR - Disability Related
E - Effectiveness (of Authentication System)
P - Privacy
All - All categories
|
| Disability Category | Nature of Disability |
| Physical | C6 Tetraplegia (Quadriplegia); Spinal Cord Injury; Muscular Dystrophy; Hand Dexterity1; Curved Spine1; Asthma; Spinal Problems1; Dyspraxia; Cerebral Palsy; Williams Syndrome2; Stroke2. |
| Cognitive | Dyslexia; Dyspraxia2; ADHD; Attention Issues1; Obsessive Compulsive Disorder (OCD) 1; Schizophrenia; Learning Disabilities1; Autism; Spectrum Disorder; Depression; Anxiety, Williams Syndrome2; Dementia; Stroke2. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




