Submitted:
20 November 2025
Posted:
20 November 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
Do large (2MB) pages amplify or mitigate side-channel leakage, particularly at the page-number granularity, and can they improve performance without degrading security?
2. Related Work
3. Background
3.1. Side-Channel Attacks
3.2. PMU-Based Side Channels
3.3. Huge Pages
3.4. Translation Lookaside Buffers (TLBs)
3.5. Cryptographic Workloads
3.6. Machine Learning (ML) Inference
4. Experimental Setup
4.1. Rationale of the Experimental Leakage Model
4.2. Mappings and Page Sizes
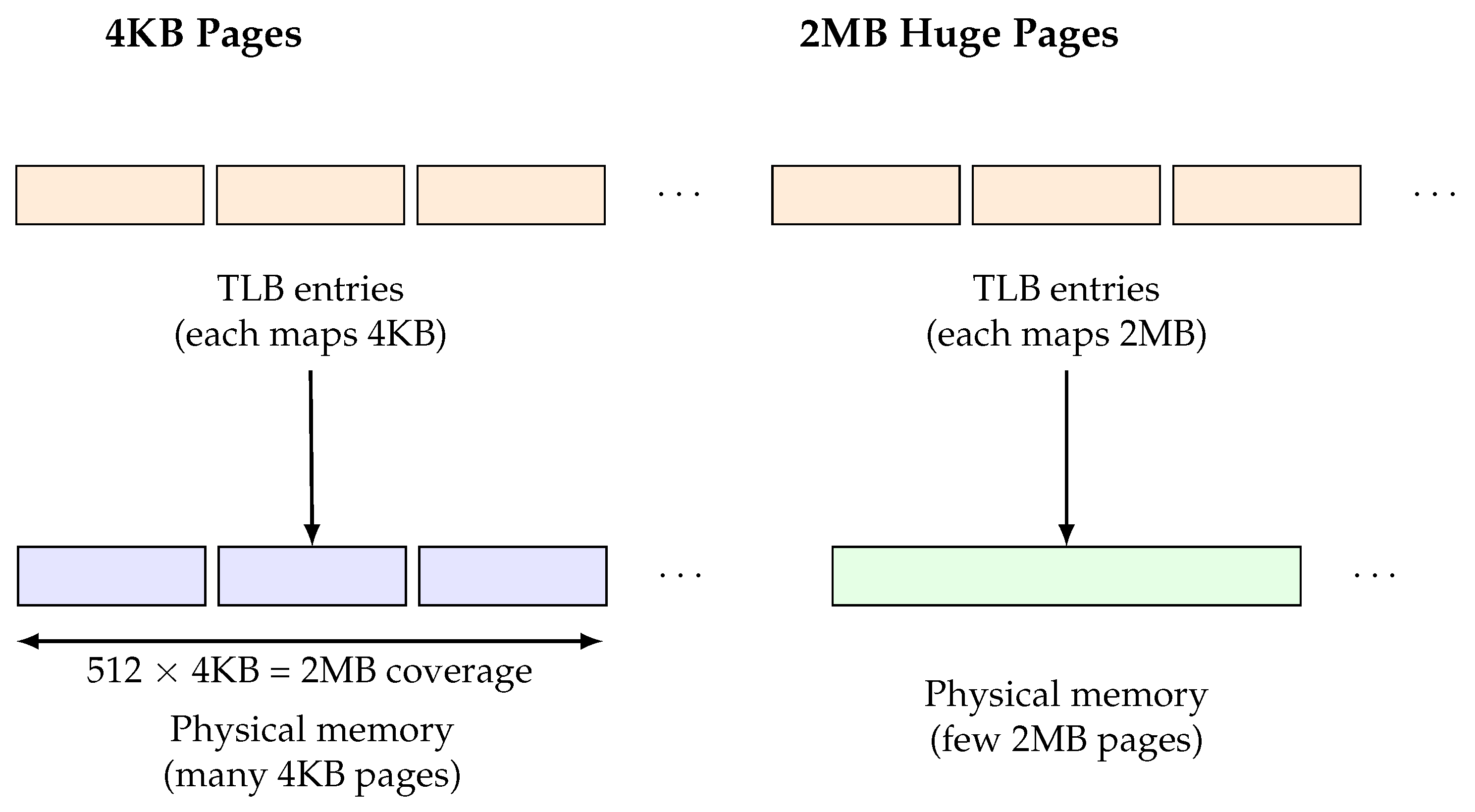
- 4KB (standard pages): the file is mapped using a normal mmap (no MAP_HUGETLB) so the kernel backs the region with 512 independent 4KB Page Table Entries (PTEs). This is our baseline: attacker and victim touch identical byte offsets, but the kernel/hardware treat each 4KB page separately (TLB entries, page-walks, etc.).
- 2MB (huge pages): the file is mapped so it is backed by true 2MB hugepage PTE (each hugepage covers entire 512×4KB region). This is done by reserving and mounting hugepages on the host. In this configuration, a single TLB entry covers the entire 2MB region.
4.2.1. How We Provision Hugepages (Host Commands)
4.2.2. Why We Use the Same 2MB Shared File for Both Page-Size Configurations
4.3. Victim Behavior
- (1)
- reads the plaintext from the mapped page starting at TARGET_OFFSET (full 4KB for page-sized modes; first 256 B for small-block modes);
- (2)
- executes the cryptographic kernel over that buffer (e.g., AES/ChaCha20 on 4KB; RSA-2048 hybrid or ECC-P256 hybrid on 4KB; RSA-RAW-256 or ECIES-256 on 256 B);
- (3)
- writes the result to a temporary file and drops a “/tmp/victim_ready” flag to synchronize with the attacker.
4.4. Attacker Measurement
4.4.1. PMU-Based Measurements
4.4.2. Timing-Based Measurements
4.4.2.1. Data Aggregation and Feature Construction
- (1)
- Group raw samples by (key_id, page_offset).
- (2)
- For each (key, page) grouping, we compute the mean across the 25 repetitions of each recorded measurement counter. This yields an 8-dimensional feature vector for the PMU-based setting, and a 1-dimensional feature vector when using timing-based (rdtscp) measurements.
4.4.2.2. Cryptographic Workloads and Keys
- AES: CBC, ECB, GCM (key lengths: 128/256 bits as used);
- ChaCha20 (typical 256-bit key);
- Elliptic-curve-based: ECIES-256 and P-256 signature/decryption flows;
- RSA: 2048-bit (standard) and a RAW-256 variant used as an experimental short-key workload.
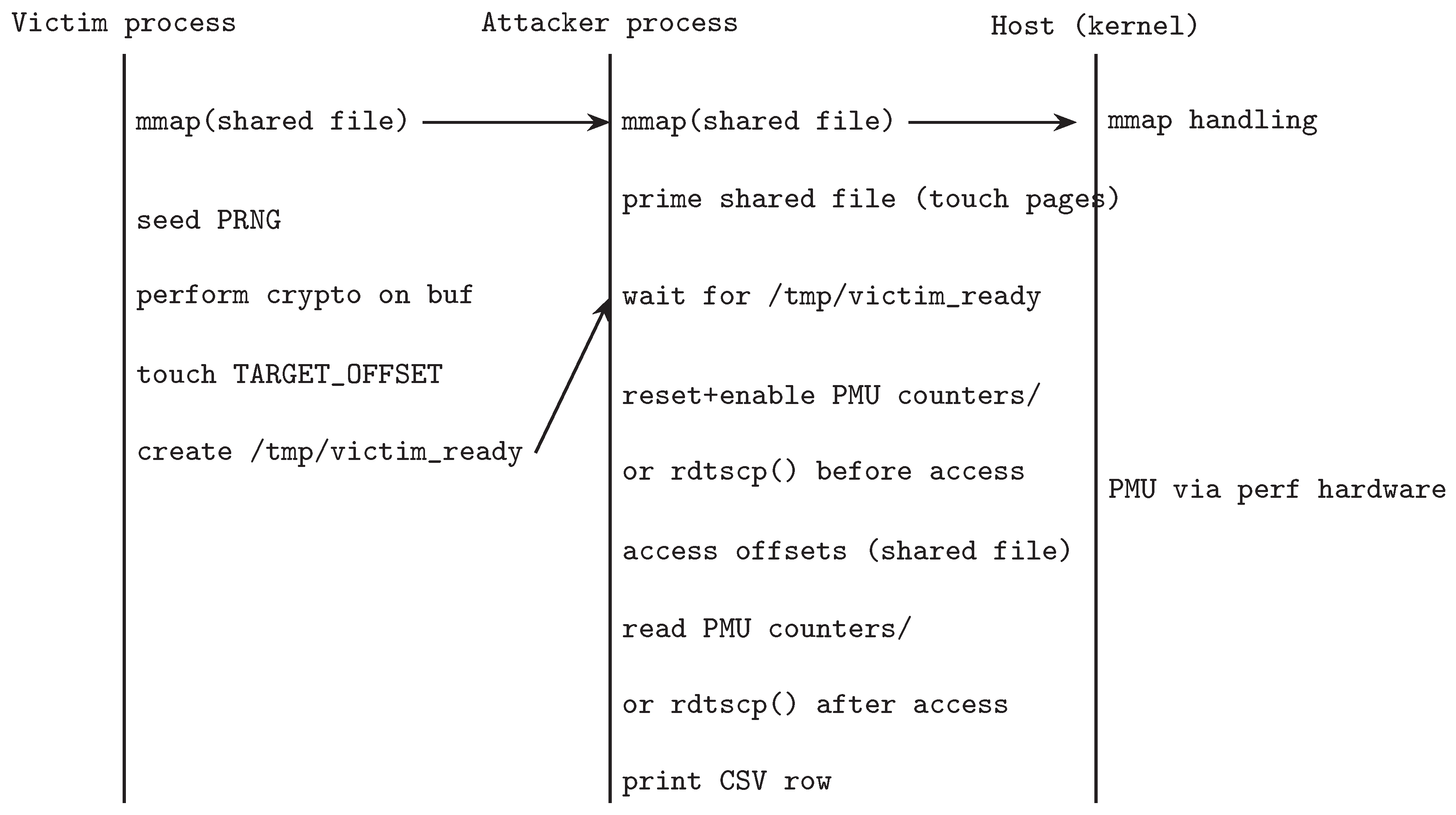
4.5. Machine Learning Pipeline and Classification
4.6. Page-Level Leakage Experiments
- (1)
- Primes all pages in the shared region.
- (2)
- Waits for the victim to perform a page access.
- (3)
- Probes each page again and records its measured access latency using PMU or rdtscp().
4.6.1. PMU-Based Leakage (Coarse-Grained Analysis)
- 4KB mapping: the victim operates on standard 4KB pages, issuing a single 4KB access for each example.
- 2MB mapping with 4KB offsets: the victim maps a 2MB hugepage-backed region but still performs accesses at 4KB granularity inside this region.
- 2MB mapping with 2MB offsets: the victim performs accesses at 2MB granularity across multiple 2MB regions. The attacker maps and measures one 2MB region at a time, then advances to the next.
4.6.2. Timing-Based Leakage (Fine-Grained Prime+Probe Analogue)
4.6.3. Objective
5. Results
5.1. Key-Class Classification (PMU-Based)
5.2. Key-Class Classification (Time-Based)
5.3. Page-Level Leakage
5.3.0.1. PMU-based leakage (coarse-grained analysis).
- 4KB configuration (predict 4KB page index): accuracy = 3.6%.
- 2MB mapping, 4KB offset (predict 4KB page index): accuracy = 3.7%.
- 2MB mapping (predict 2MB page number across 20 regions): accuracy = 3.6%.
5.3.0.2. Timing-based leakage (fine-grained Prime+Probe analogue).
- 4KB configuration (predict 4KB page index): trimmed-mean accuracy = 2.1%.
- 2MB mapping, 4KB offset (predict 4KB page index): trimmed-mean accuracy = 1.6%.
- 2MB mapping (predict 2MB page number across regions): estimated accuracy = 1.5%, consistent with 1-in-20 chance.
5.3.0.3. Interpretation.
5.4. Runtime/Overhead Snapshot
6. Discussion & Conclusion
6.1. Performance Gain Without Additional Leakage
6.2. Why Huge Pages Do Not Increase Leakage
6.3. Rationale and Motivation of the Cryptographic Access Pattern Model
6.4. Security–Performance Balance
6.5. Broader Implications
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Li, X.; Tyagi, A. Cross-world covert channel on arm trustzone through pmu. Sensors 2022, 22, 7354. [Google Scholar] [CrossRef] [PubMed]
- Xu, Y.; Qi, W.; Lin, Z. Controlled-Channel Attacks: Deterministic Side Channels for Untrusted Operating Systems. In Proceedings of the IEEE Symposium on Security and Privacy; 2015; pp. 640–656. [Google Scholar]
- Zhu, W. Exploring superpage promotion policies for efficient address translation. Master’s thesis, Rice University, 2019.
- Yarom, Y.; Falkner, K. Flush+ Reload: a High Resolution, Low Noise, L3 Cache Side-Channel Attack. In Proceedings of the 23rd USENIX Security Symposium (USENIX Security 14); 2014; pp. 719–732. [Google Scholar]
- Gruss, D.; Maurice, C.; Mangard, S. Flush+ Flush: A Fast and Stealthy Cache Attack. In Proceedings of the Detection of Intrusions and Malware, and Vulnerability Assessment. Springer; 2016; pp. 279–299. [Google Scholar]
- Kocher, P.; Horn, J.; Fogh, A.; Genkin, D.; Gruss, D.; Haas, W.; Hamburg, M.; Lipp, M.; Mangard, S.; Prescher, T.; et al. Spectre attacks: Exploiting speculative execution. Communications of the ACM 2020, 63, 93–101. [Google Scholar] [CrossRef]
- Lipp, M.; Schwarz, M.; Gruss, D.; Prescher, T.; Haas, W.; Horn, J.; Mangard, S.; Kocher, P.; Genkin, D.; Yarom, Y.; et al. Meltdown: Reading kernel memory from user space. Communications of the ACM 2020, 63, 46–56. [Google Scholar] [CrossRef]
- Xiao, Y.; Zhang, X.; Zhang, Y.; Teodorescu, R. One bit flips, one cloud flops:{Cross-VM} row hammer attacks and privilege escalation. In Proceedings of the 25th USENIX security symposium (USENIX Security 16); 2016; pp. 19–35. [Google Scholar]
- Bepary, M.K.; Basu, A.; Mohammad, S.; Hassan, R.; Farahmandi, F.; Tehranipoor, M. SPY-PMU: Side-Channel Profiling of Your Performance Monitoring Unit to Leak Remote User Activity. Cryptology ePrint Archive 2025. [Google Scholar]
- Whyman, E.K.; Somers, H.L. Evaluation metrics for a translation memory system. Software: Practice and Experience 1999, 29, 1265–1284. [Google Scholar] [CrossRef]
- Wang, W.; Chen, G.; Pan, X.; Zhang, Y.; Wang, X.; Bindschaedler, V.; Tang, H.; Gunter, C.A. Leaky cauldron on the dark land: Understanding memory side-channel hazards in SGX. In Proceedings of the Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, 2017, pp.
- Wei, J.; Zhang, Y.; Zhou, Z.; Li, Z.; Al Faruque, M.A. Leaky dnn: Stealing deep-learning model secret with gpu context-switching side-channel. In Proceedings of the 2020 50th Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN). IEEE; 2020; pp. 125–137. [Google Scholar]
- Hua, W.; Zhang, Z.; Suh, G.E. Reverse engineering convolutional neural networks through side-channel information leaks. In Proceedings of the Proceedings of the 55th Annual Design Automation Conference, 2018, pp.
- Shokri, R.; Stronati, M.; Song, C.; Shmatikov, V. Membership inference attacks against machine learning models. In Proceedings of the 2017 IEEE symposium on security and privacy (SP). IEEE; 2017; pp. 3–18. [Google Scholar]
- Zhang, Y.; Jia, R.; Pei, H.; Wang, W.; Li, B.; Song, D. The secret revealer: Generative model-inversion attacks against deep neural networks. In Proceedings of the Proceedings of the IEEE/CVF conference on computer vision and pattern recognition, 2020, pp.
- Engler, D.R.; Kaashoek, M.F.; O’Toole Jr, J. Exokernel: An operating system architecture for application-level resource management. ACM SIGOPS Operating Systems Review 1995, 29, 251–266. [Google Scholar] [CrossRef]
- Gupta, A.; Faraboschi, P.; Gioachin, F.; Kale, L.V.; Kaufmann, R.; Lee, B.S.; March, V.; Milojicic, D.; Suen, C.H. Evaluating and improving the performance and scheduling of HPC applications in cloud. IEEE Transactions on Cloud Computing 2014, 4, 307–321. [Google Scholar] [CrossRef]
- Michailidis, T.; Delis, A.; Roussopoulos, M. management. In Proceedings of the Proceedings of the 12th ACM International Conference on Systems and Storage, 2019, pp.
- Osvik, D.A.; Shamir, A.; Tromer, E. Cache attacks and countermeasures: the case of AES. In Proceedings of the Proceedings of the 2006 The Cryptographers’ Track at the RSA Conference on Topics in Cryptology, Berlin, Heidelberg, 2006. [CrossRef]
- Wang, W.; Chen, G.; Pan, X.; Zhang, Y.; Wang, X.; Bindschaedler, V.; Tang, H.; Gunter, C.A. Leaky Cauldron on the Dark Land: Understanding Memory Side-Channel Hazards in SGX. In Proceedings of the Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, New York, NY, USA, 2017. [CrossRef]
- Wang, A.; Chen, B.; Wang, Y.; Fletcher, C.W.; Genkin, D.; Kohlbrenner, D.; Paccagnella, R. Peek-a-Walk: Leaking Secrets via Page Walk Side Channels. In Proceedings of the 2025 IEEE Symposium on Security and Privacy (SP). IEEE; 2025; pp. 3534–3548. [Google Scholar]
- Gao, T.; Huo, X.; Liu, H.; Gao, H. Wide neural networks as gaussian processes: Lessons from deep equilibrium models. Advances in Neural Information Processing Systems 2023, 36, 54918–54951. [Google Scholar]
- Javed, Y.; Rajabi, N. Multi-layer perceptron artificial neural network based IoT botnet traffic classification. In Proceedings of the Proceedings of the Future Technologies Conference.
- Gao, T.; Sun, S.; Liu, H.; Gao, H. Exploring the Impact of Activation Functions in Training Neural ODEs. In Proceedings of the The Thirteenth International Conference on Learning Representations; 2025. [Google Scholar]
| Mode | Key Size | 2MB Avg | 4KB Avg |
|---|---|---|---|
| AES-CBC | 128 bit | 0.809 | 0.758 |
| AES-ECB | 128 bit | 0.751 | 0.756 |
| AES-GCM | 128 bit | 0.826 | 0.757 |
| ChaCha20 | 256 bit | 0.762 | 0.766 |
| ECC-ECIES | 256 bit | 0.744 | 0.751 |
| ECC-P256 | 256 bit | 0.812 | 0.813 |
| RSA-2048 | 2048 bit | 0.802 | 0.791 |
| RSA-RAW | 256 bit | 0.821 | 0.766 |
| Mode | Key Size | 2MB Avg | 4KB Avg |
|---|---|---|---|
| AES-CBC | 128 bit | 0.750 | 0.750 |
| AES-ECB | 128 bit | 0.737 | 0.783 |
| AES-GCM | 128 bit | 0.790 | 0.752 |
| ChaCha20 | 256 bit | 0.763 | 0.755 |
| ECC-ECIES | 256 bit | 0.777 | 0.770 |
| ECC-P256 | 256 bit | 0.772 | 0.730 |
| RSA-2048 | 2048 bit | 0.749 | 0.750 |
| RSA-RAW | 256 bit | 0.750 | 0.750 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 1996 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




